IoT-Based Multi-Sensor Healthcare Architectures and a Lightweight-Based Privacy Scheme
Abstract
1. Introduction
- A formal lightweight cryptographic primitive which can encrypt and decrypt the inputted messages with a considerable-sized key, thus ensuring the confidentiality, data privacy and authentication while deeming the decomposition of the algorithm through key search attacks to be difficult. The success of other known attacks will also be eliminated as each device will effectively secure the collected data before transmission.
- High speed in key generation and encryption/decryption processes for quick transmissions and the management of the significant IoT network load. Therefore, the constant availability of the architecture will be ensured because the communication system will be able to handle multiple messages that are rapidly transmitted.
- Flexible design with multiple options for key size and performance speed for various circumstances depending on the user preferences. The scalability of the IoT can thus be confronted by constantly adapting to the current needs of the system.
- Minimal resource utilization of the employed security scheme for efficient implementation in hardware-constrained IoT devices. This way, all devices in the healthcare structure can employ a level of security and hence ensure their integrity. Proper balance between the resources and the performance throughput must also be ensured. The performance flow of the security scheme must be considered when minimizing the resources of the design. The throughput must remain sufficiently high in order to correspond to high-speed transmissions.
- First, the employed cryptographic primitive, as presented in [17], ensures the maintenance of the main security concepts while being lightweight and having the ability to utilize various sized keys, from 32-bit to 256-bit length. The width of the key is a general parameter of the security level for symmetric encryption, deeming the 256-bit key highly effective for the proposed environment. The LEAIoT algorithm also utilizes asymmetric encryption, which further enhances the security and confidentiality of the system.
- Second, the high computation speed achieved by the hardware-based implementation ensures the quick network management of the IoT’s heavy communication load. The performance results of the proposed FPGA-based architecture are compared to the original LEAIoT design [17], which was implemented in a central processing unit (CPU), with a significant improvement of the key generation speed up to 99.9% and the encryption/decryption speed up to 96.2%.
- Third, in the same architecture, four different key sizes are integrated, providing four diverse performance speeds and security efficiencies that the applications can instantly choose from depending on the current network and the computational needs of the application. Therefore, the system offers flexibility and can easily adapt to various circumstances.
- Finally, the cryptographic scheme is properly implemented through innovative design optimizations and achieves novel implementational results that indicate its resource efficiency without an excessive reduction in throughput. Thus, the proposed scheme effectively fulfills the performance requirements for smart health and it can be easily employed to the various devices of the IoT network, providing global security to the healthcare structure while maintaining performance balance between resources, throughput and security. For further proving the architecture’s efficiency, the proposed hardware-based scheme is compared to other relative FPGA-based research. Specifically, it was concluded that the proposed implementation utilizes up to 87.9% and 76.9% fewer resources than the lightweight versions of Advance Encryption Standard (AES). It also decreases the resource consumption up to 65.7% and 12.2% compared to SNOW 3G and ZUC ciphers, respectively. Lastly, it achieves an almost double throughput compared to RC4 cipher and overall similar performance results with PRESENT and CLEFIA, even with a significantly lower frequency.
2. IoT-Based Multi-Sensor Healthcare Applications
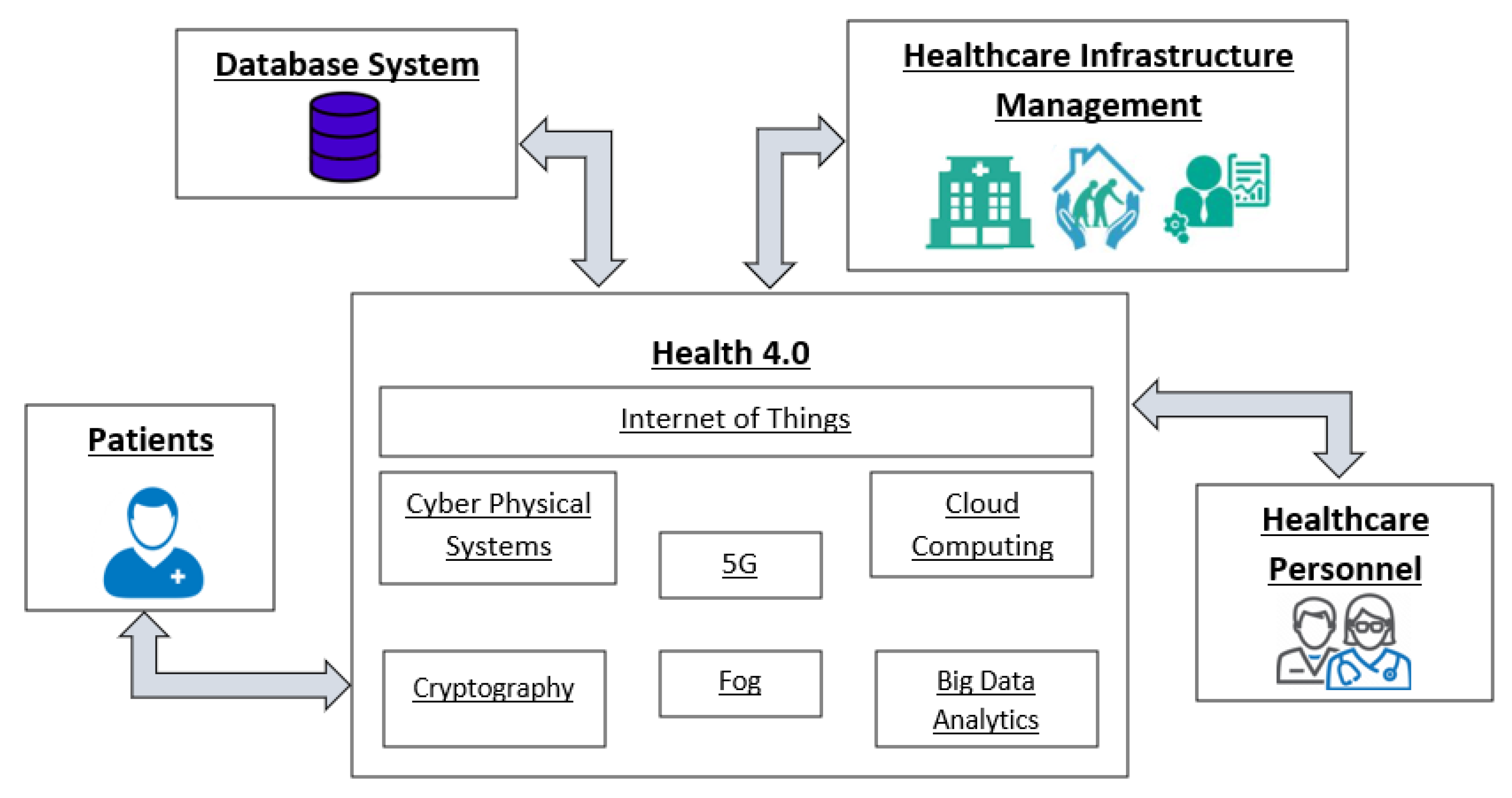
2.1. Health 4.0 Objectives
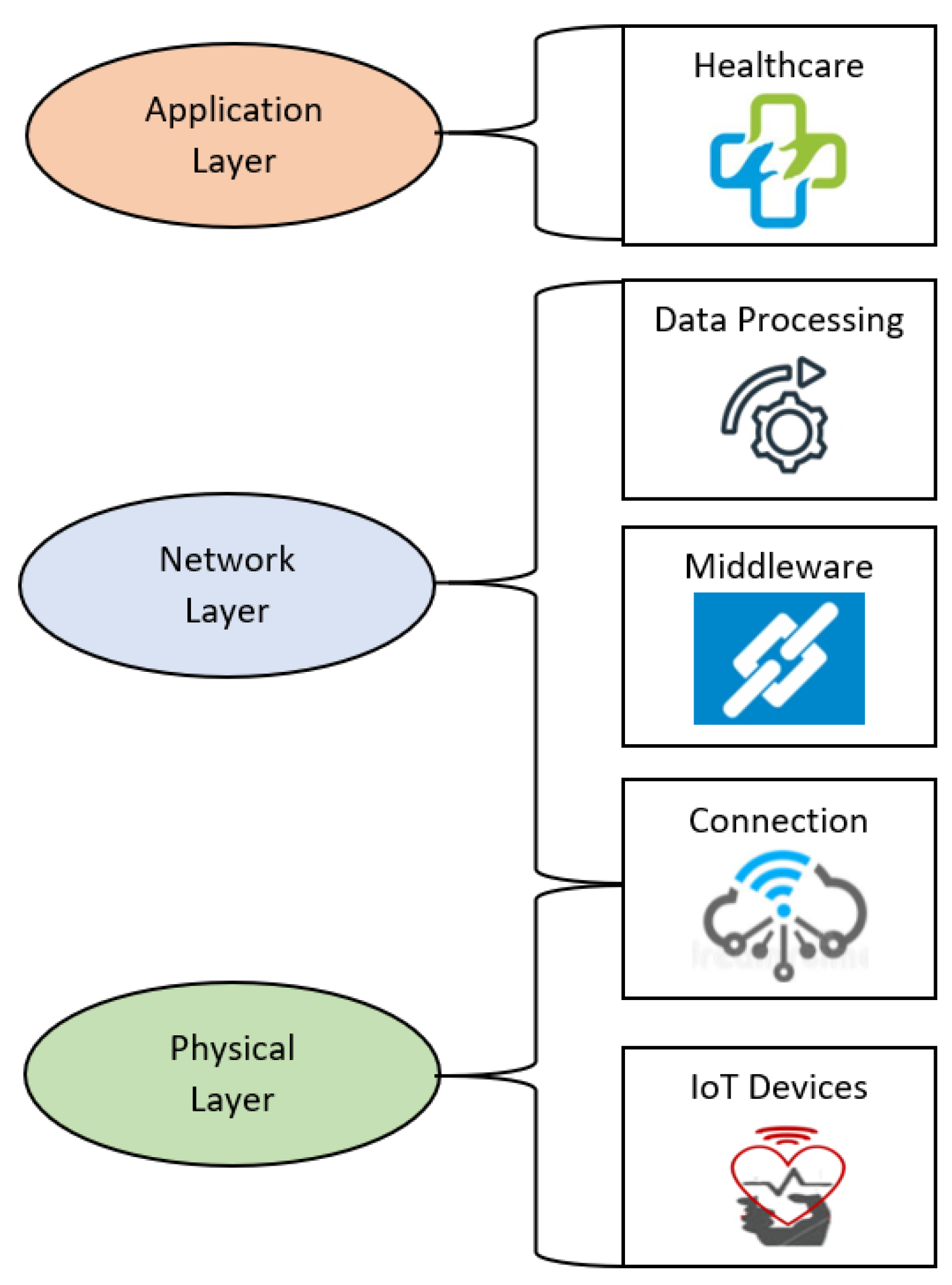
2.2. IoT Architecture
2.3. Smart Health Multi-Sensors Designs from Literature
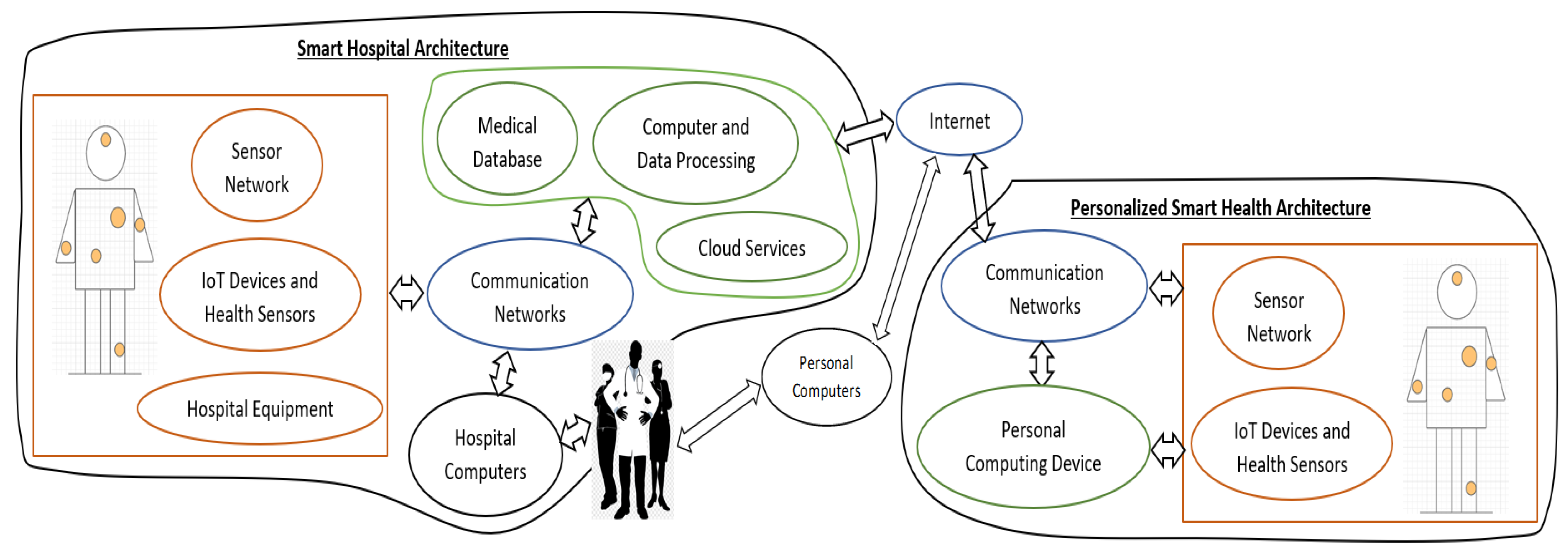
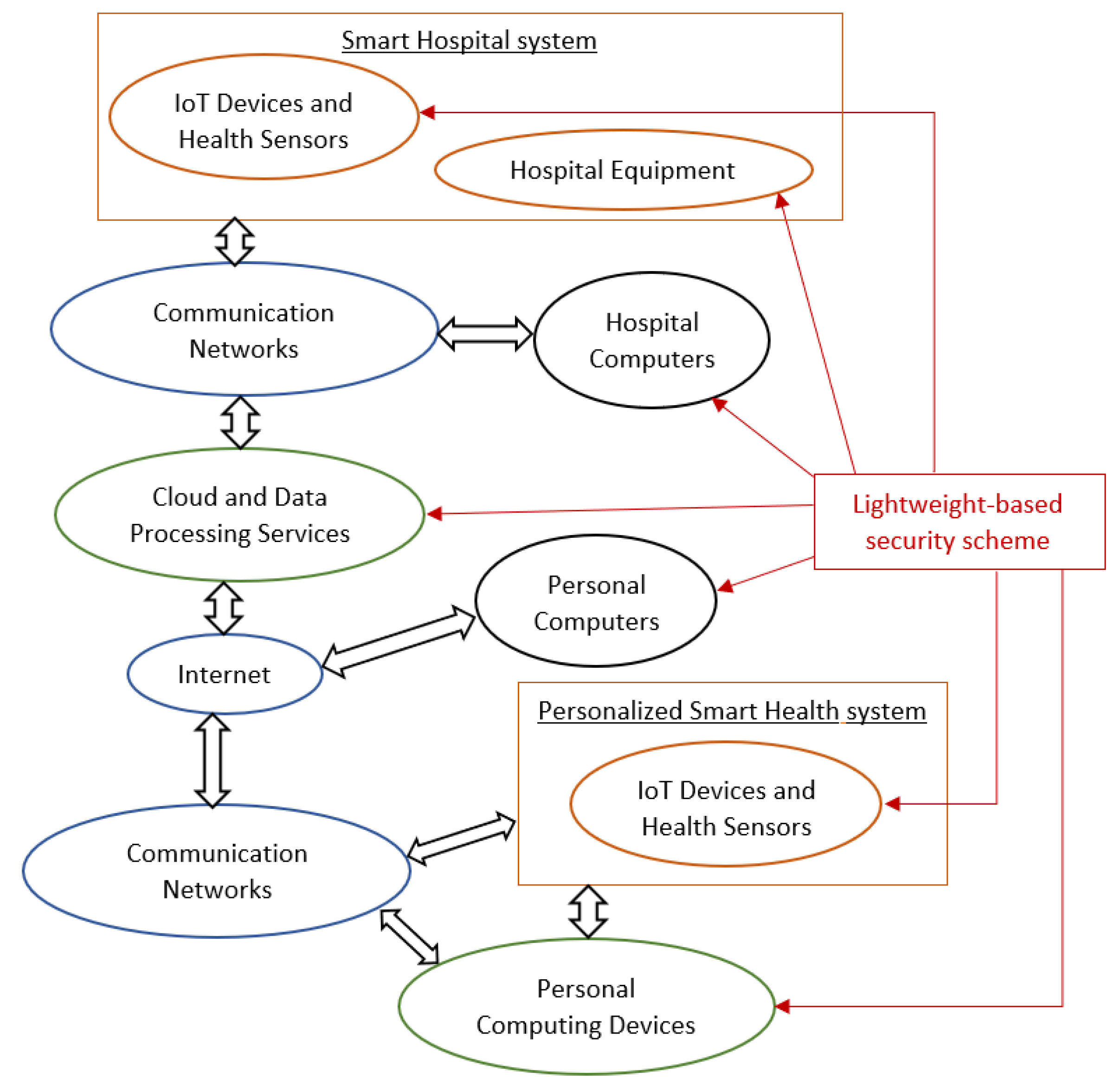
2.4. IoT-Based Multi-Sensor Healthcare Infrastructure
3. Security Requirements
4. Lightweight-Based Security Scheme
4.1. LEAIoT: Lightweight Encryption/Decryption Algorithm
- The synthetic values of the plaintext are multiplied with the private key n. Then, modulo 37 is used;
- A 3 × 3 matrix is created as the private key k. Additionally, the length of the key n is calculated and utilized as the key n1;
- The produced text from step 1 is segregated into blocks bi matching the key k. Specifically, it is divided to multiple arrays of length equal to 3;
- Each block bi is multiplied with the keys k and n1. Modulo 37 is subsequently applied;
- The result is the secure ciphertext of the original plaintext;
- The modular inverse of the keys n1 and k with modulo 37 is utilized;
- The received ciphertext is divided to blocks bi, as with step 3 of the encryption sequence;
- Each block is multiplied with the two keys k′ and n1(−1). Modulo 37 is then applied;
- The produced text is afterwards multiplied with the key SSK and modulo 37 is once again used;
- The result is the original plaintext.
- First, the inputted values are multiplied with key n:
- Finally, the result of the previous calculation is multiplied with key k and the length of key n to produce the encrypted message:
- First, the SSK, k′ and n1(−1) are calculated:
- Then, the encrypted message is multiplied with k′ and n1(−1):
- Finally, the original message is revealed by multiplying the previous result with the SSK key:
4.2. Implementation of the Proposed Lightweight-Based Security Scheme
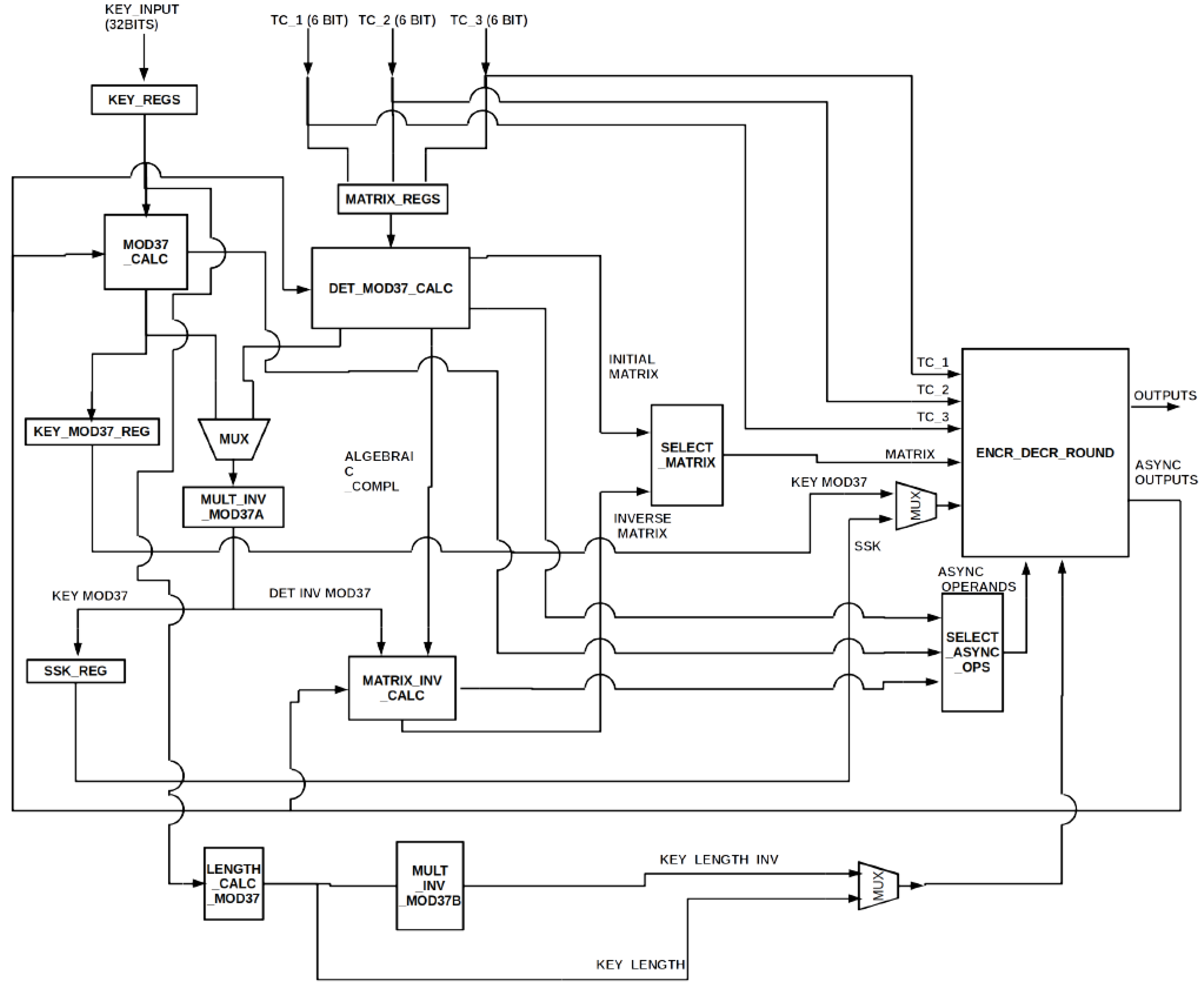
- ENCR_DECR_ROUND unit contains the necessary resources for the encryption and decryption of the input text. It also executes the additions and multiplications of finite elements and sends the results into the appropriate units.
- The MOD37_CALC unit calculates modulo 37 of symmetric key n.
- DET_MOD37_CALC unit’s input is a 3 × 3 matrix, namely key k, and its outputs are modulo 37 of the matrix’s determinant and table I, which is an intermediate step for computing the modular inverse of the matrix. Each element of table I, namely iab, is calculated by the following equation:where is the determinant of a 2 × 2 matrix created after erasing row a and column b of the input matrix.
- MULT_INV_MOD37 unit computes the modular inverse of the input. The input can either be module 37 of the symmetric key n or the determinant’s module 37 of key k, which was calculated by DET_MOD37_CALC. The input is selected by a multiplexer.
- MATRIX_INV_CALC unit receives the determinant’s modular inverse of key k as input, as computed by MULT_INV_MOD37, and receives the intermediate table I as input, as calculated by DET_MOD37_CALC. The output is the modular inverse of key k.
- LENGTH_CALC_MOD37 unit calculates the length of symmetric key n, namely generating key n1. The modular inverse of this key can be produced by the MULT_INV_MOD37 unit. The procedure is the same as with the modular inverse computation of symmetric key n.
4.2.1. Modulo 37 Calculation Module
4.2.2. Three-Dimensional Matrix’s Determinant Calculation Module
4.2.3. Modular Inverse Calculation Module and Three-Dimensional Matrix’s Modular Inverse Calculation Module
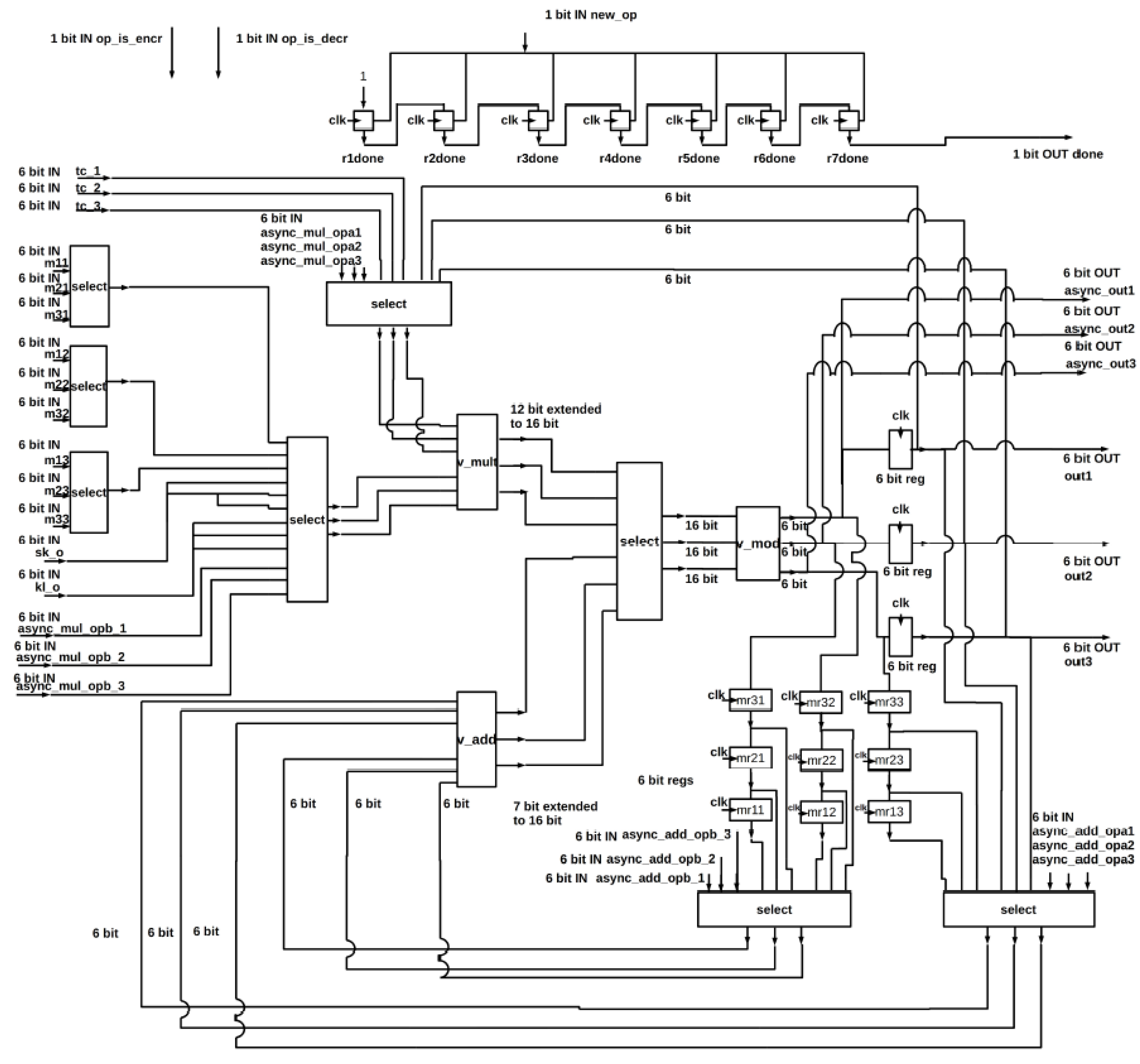
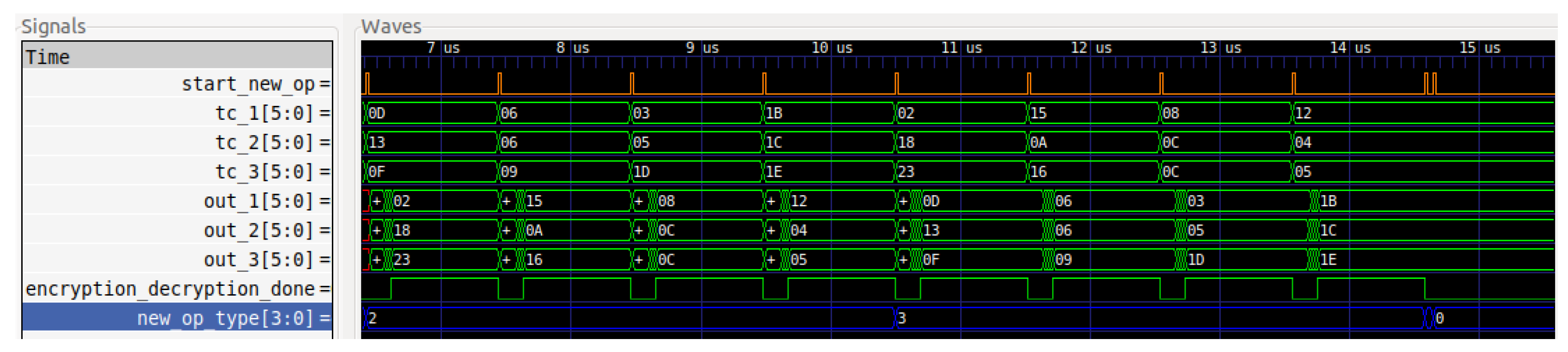
4.2.4. Encryption and Decryption Unit
- A 3 × 3 matrix with 6-bit elements (m11, m12, …, m33);
- Three 6-bit characters (tc_1, tc_2, tc_3) from the text which will be encrypted or decrypted;
- A 6-bit key (sk_o);
- A 6-bit signal (kl_o), which is modulo 37 of the key length or its modular inverse;
- Three single bit signals that indicate the start of a new operation or the applied process, namely encryption or decryption;
- Twelve different data for the generation of the keys, six of them (async_add_opa1, async_add_opa2, async_add_opa3, async_add_opb1, async_add_opb2, async_add_opb3) are added together while the other six (async_mul_opa1, async_mul_opa2, async_mul_opa3, async_mul_opb1, async_mul_opb2, async_mul_opb3) are multiplied with each other;
- A signal (async_op_is_add) which selects whether the operation for the keys’ generation is addition or multiplication.
5. Synthesis Implementation Results
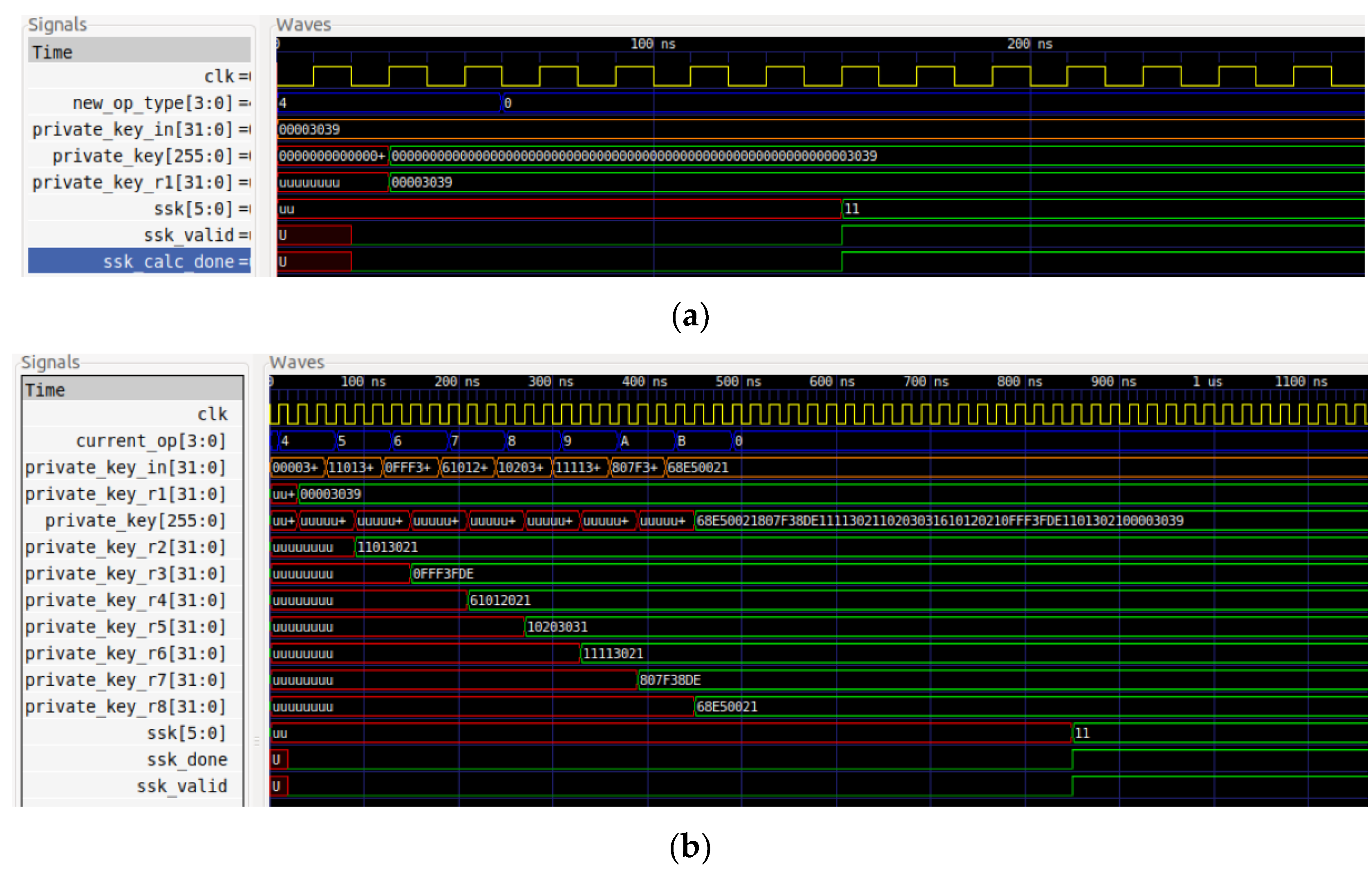
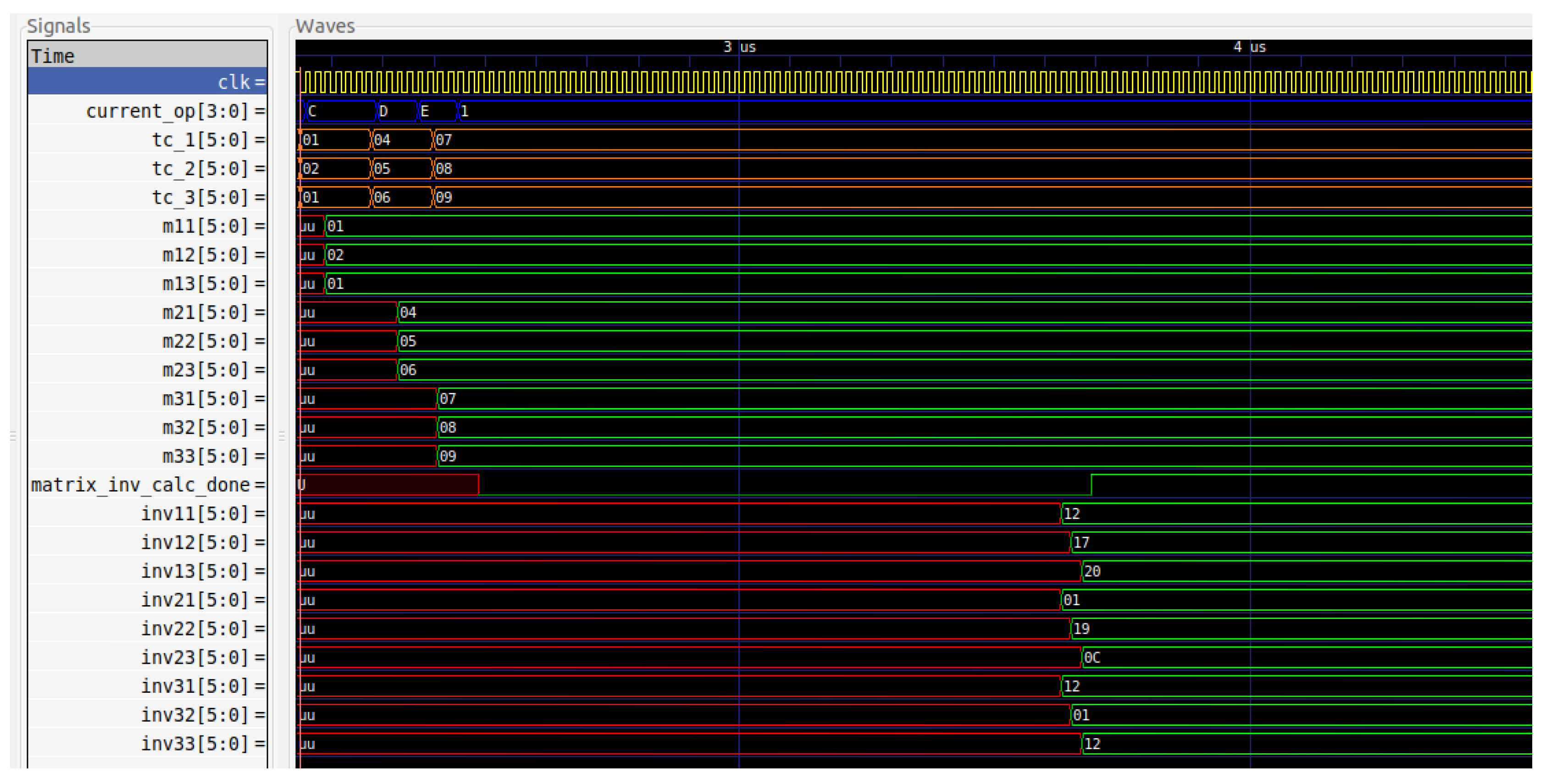
5.1. Simulations
5.2. Implementation
6. Performance Results
7. Conclusions
Author Contributions
Funding
Institutional Review Board Statement
Informed Consent Statement
Data Availability Statement
Conflicts of Interest
References
- Fei, H. Security and Privacy in Internet of Things (IoTs): Models, Algorithms, and Implemenations; CRC Press: Boca Raton, FL, USA, 2016; ISBN 9781498723183. [Google Scholar]
- Stellios, I.; Kotzanikolaou, P.; Psarakis, M.; Alcaraz, C.; Lopez, J. A survey of IoT-Enabled cyberattacks: Assessing attack paths to critical infrastructures and services. IEEE Commun. Surv. Tutor. 2018, 20, 3453–3495. [Google Scholar] [CrossRef]
- Baker, S.B.; Xiang, W.; Atkinson, I. Internet of things for smart healthcare: Technologies, challenges, and opportunities. IEEE Access 2017, 5, 26521–26544. [Google Scholar] [CrossRef]
- Al-Jaroodi, J.; Mohamed, N.; Abukhousa, E. Health 4.0: On the way to realizing the healthcare of the future. IEEE Access 2020, 8, 211189–211210. [Google Scholar] [CrossRef] [PubMed]
- Mohamed, N.; Al-Jaroodi, J. The Impact of Industry 4.0 on healthcare system engineering. In Proceedings of the 2019 IEEE International Systems Conference (SysCon), Orlando, FL, USA, 8–11 April 2019; pp. 1–7. [Google Scholar]
- Tsantikidou, K.; Sklavos, N. Vulnerabilities of Internet of Things, for Healthcare Devices and Applications. In Proceedings of the 2021 8th NAFOSTED Conference on Information and Computer Science (NICS), Hanoi, Vietnam, 21–22 December 2021. [Google Scholar]
- Simplicio, M.A., Jr.; Silva, M.V.M.; Alves, R.C.A.; Shibata, T.K.C. Lightweight and escrow-less authenticated key agreement for the internet of things. Comput. Commun. 2017, 98, 43–51. [Google Scholar] [CrossRef]
- Makhdoom, I.; Abolhasan, M.; Lipman, J.; Liu, R.P.; Ni, W. Anatomy of Threats to the Internet of Things. IEEE Commun. Surv. Tutor. 2019, 21, 1636–1675. [Google Scholar] [CrossRef]
- Lounis, K.; Zulkernine, M. Attacks and defenses in short-range wireless technologies for IoT. IEEE Access 2020, 8, 88892–88932. [Google Scholar] [CrossRef]
- Butun, I.; Österberg, P.; Song, H. Security of the Internet of Things: Vulnerabilities, attacks, and countermeasures. IEEE Commun. Surv. Tutor. 2020, 22, 616–644. [Google Scholar] [CrossRef]
- Khanam, S.; Ahmedy, I.B.; Idna Idris, M.Y.; Jaward, M.H.; Bin Md Sabri, A.Q. A survey of security challenges, attacks taxonomy and advanced countermeasures in the Internet of Things. IEEE Access 2020, 8, 219709–219743. [Google Scholar] [CrossRef]
- Burg, A.; Chattopadhyay, A.; Lam, K.Y. Wireless communication and security issues for cyber–Physical systems and the internet-of-things. Proc. IEEE 2018, 106, 38–60. [Google Scholar] [CrossRef]
- Tsantikidou, K.; Sklavos, N. Hardware security for IoT-based, healthcare applications. In Proceedings of the New England Hardware Security Day 2021 Workshop, Virtual, 9 April 2021. [Google Scholar]
- Bikos, A.N.; Sklavos, N. The future of privacy and trust on the internet of Things (IoT) for healthcare: Concepts, Challenges, and Security Threat Mitigations. In Recent Advances in Security, Privacy, and Trust for Internet of Things (IoT) and Cyber-Physical Systems (CPS); CRC Press: Boca Raton, FL, USA, 2020. [Google Scholar]
- Panagiotou, P.; Sklavos, N.; Zaharakis, I.D. Design and implementation of a privacy framework for the internet of things (IoT). In Proceedings of the 2018 21st Euromicro Conference on Digital System Design (DSD), Prague, Czech Republic, 29–31 August 2018. [Google Scholar]
- Tsavos, M.; Sklavos, N.; Alexiou, G.P. Lightweight security data streaming, based on reconfigurable logic, for FPGA platform. In Proceedings of the 2020 23rd Euromicro Conference on Digital System Design (DSD), Kranj, Slovenia,, 26–28 August 2020. [Google Scholar]
- Habib, M.A.; Ahmad, M.; Jabbar, S.; Ahmed, S.H.; Rodrigues, J.J.P.C. Speeding up the Internet of Things: LEAIoT: A lightweight encryption algorithm toward low-latency communication for the Internet of Things. IEEE Consum. Electron. Mag. 2018, 7, 31–37. [Google Scholar] [CrossRef]
- Kocakulak, M.; Butun, I. An overview of wireless sensor networks towards Internet of Things. In Proceedings of the 2017 IEEE 7th Annual Computing and Communication Workshop and Conference (CCWC), Las Vegas, NV, USA, 9–11 January 2017. [Google Scholar]
- Al-Garadi, M.A.; Mohamed, A.; Al-Ali, A.K.; Du, X.; Ali, I.; Guizani, M. A Survey of Machine and Deep Learning Methods for Internet of Things (IoT) Security. IEEE Commun. Surv. Tutor. 2020, 22, 1646–1685. [Google Scholar] [CrossRef]
- Rodrigues, J.J.; Segundo DB, D.R.; Junqueira, H.A.; Sabino, M.H.; Prince, R.M.; Al-Muhtadi, J.; De Albuquerque, V.H.C. Enabling Technologies for the Internet of Health Things. IEEE Access 2018, 6, 13129–13141. [Google Scholar] [CrossRef]
- Egala, B.S.; Pradhan, A.K.; Badarla, V.; Mohanty, S.P. Fortified-Chain: A blockchain-based framework for security and privacy-assured Internet of medical things with effective access control. IEEE Internet Things J. 2021, 8, 11717–11731. [Google Scholar] [CrossRef]
- Firouzi, F.; Farahani, B.; Barzegari, M.; Daneshmand, M. AI-Driven Data Monetization: The other Face of Data in IoT-based Smart and Connected Health. IEEE Internet Things J. 2020, 9, 5581–5599. [Google Scholar] [CrossRef]
- Ma, Y.; Wang, Y.; Yang, J.; Miao, Y.; Li, W. Big health application system based on health Internet of Things and big data. IEEE Access 2017, 5, 7885–7897. [Google Scholar] [CrossRef]
- Kamal, N.; Ghosal, P. Three tier architecture for IoT driven health monitoring system using raspberry Pi. In Proceedings of the 2018 IEEE International Symposium on Smart Electronic Systems (iSES) (Formerly iNiS), Hyderabad, India, 17–19 December 2018. [Google Scholar]
- Zhang, H.; Li, J.; Wen, B.; Xun, Y.; Liu, J. Connecting intelligent things in smart hospitals using NB-IoT. IEEE Internet Things J. 2018, 5, 1550–1560. [Google Scholar] [CrossRef]
- Cabra, J.; Castro, D.; Colorado, J.; Mendez, D.; Trujillo, L. An IoT approach for wireless sensor networks applied to e-health environmental monitoring. In Proceedings of the 2017 IEEE International Conference on Internet of Things (iThings) and IEEE Green Computing and Communications (GreenCom) and IEEE Cyber, Physical and Social Computing (CPSCom) and IEEE Smart Data (SmartData), Exeter, UK, 21–23 June 2017. [Google Scholar]
- Wu, F.; Wu, T.; Zarate, D.C.; Morfuni, R.; Kerley, B.; Hinds, J.; Taniar, D.; Armstrong, M.; Yuce, M.R. An autonomous hand hygiene tracking sensor system for prevention of hospital associated infections. IEEE Sens. J. 2021, 21, 14308–14319. [Google Scholar] [CrossRef]
- Neshenko, N.; Bou-Harb, E.; Crichigno, J.; Kaddoum, G.; Ghani, N. Demystifying IoT security: An exhaustive survey on IoT vulnerabilities and a first empirical look on internet-scale IoT exploitations. IEEE Commun. Surv. Tutor. 2019, 21, 2702–2733. [Google Scholar] [CrossRef]
- Sklavos, N.; Zaharakis, I.D.; Kameas, A.; Kalapodi, A. Security & trusted devices in the context of Internet of Things (IoT). In Proceedings of the 2017 Euromicro Conference on Digital System Design (DSD), Vienna, Austria, 30 August–1 September 2017. [Google Scholar]
- Ioannidou, I.; Sklavos, N. On general data protection regulation vulnerabilities and privacy issues, for wearable devices and fitness tracking applications. Cryptography 2021, 5, 29. [Google Scholar] [CrossRef]
- Stallings, W. Cryptography and Network Security, 6th ed.; Pearson: Upper Saddle River, NJ, USA, 2014. [Google Scholar]
- Barrett, P. Implementing the rivest shamir and adleman public key encryption algorithm on a standard digital signal processor. In Advances in Cryptology—CRYPTO’ 86; Springer: Berlin/Heidelberg, Germany, 1987; pp. 311–323. [Google Scholar]
- Wallace, C.S. A Suggestion for a Fast Multiplier. IEEE Trans. Electron. Comput. 1964, EC-13, 14–17. [Google Scholar] [CrossRef]
- Xilinx. Zynq-7000 SoC Data Sheet: Overview; DS190 datasheet; Xilinx: San Jose, CA, USA, 2018. [Google Scholar]
- Xilinx. Vivado Design Suite User Guide: Release Notes, Installation, and Licensing; UG973 datasheet; Xilinx: San Jose, CA, USA, 2018. [Google Scholar]
- GHDL Documentation. Release 1.0-dev Datasheet. Available online: https://ghdl-rad.readthedocs.io/_/downloads/en/latest/pdf/ (accessed on 29 April 2022).
- Madani, M.; Benkhaddra, I.; Tanougast, C.; Chitroub, S.; Sieler, L. FPGA implementation of an enhanced SNOW-3G stream cipher based on a hyperchaotic system. In Proceedings of the 2017 4th International Conference on Control, Decision and Information Technologies (CoDIT), Barcelona, Spain, 5–7 April 2017. [Google Scholar]
- Lata, K.; Saini, S. Hardware Software Co-Simulation of an AES-128 based data encryption in image processing systems for the internet of things environment. In Proceedings of the 2020 IEEE International Symposium on Smart Electronic Systems (iSES) (Formerly iNiS), Chennai, India, 14–16 December 2020. [Google Scholar]
- Kumar, T.; Reddy, K.; Rinaldi, S.; Parameshachari, B.; Arunachalam, K. A Low area high speed FPGA implementation of AES architecture for cryptography application. Electronics 2021, 10, 2023. [Google Scholar] [CrossRef]
- Lara-Nino, C.A.; Diaz-Perez, A.; Morales-Sandoval, M. Lightweight Hardware Architectures for the Present Cipher in FPGA. IEEE Trans. Circuits Syst. I Regul. Pap. 2017, 64, 2544–2555. [Google Scholar] [CrossRef]
- Yang, Y.; Zhao, W.; Xiong, L.; Wang, N.; Ma, Y. Optimized implementations for ZUC-256 on FPGA. Wirel. Pers. Commun. 2021, 116, 2615–2632. [Google Scholar] [CrossRef]
- Cheng, X.; Zhu, H.; Xu, Y.; Zhang, Y.; Xiao, H.; Zhang, Z. A reconfigurable and compact hardware architecture of CLEFIA block cipher with multi-configuration. Microelectron. J. 2021, 114, 105144. [Google Scholar] [CrossRef]
- Taqieddin, E.; Abu-Rjei, O.; Mhaidat, K.; Bani-Hani, R. Efficient FPGA Implementation of the RC4 Stream Cipher using Block RAM and Pipelining. Procedia Comput. Sci. 2015, 63, 8–15. [Google Scholar] [CrossRef][Green Version]
| LUTs | Flip-Flops | F7-Muxes | F8-Muxes | Execution Time | Frequency | Throughput | Throughput/Slices |
|---|---|---|---|---|---|---|---|
| 2700 | 815 | 67 | 24 | 261 ns | 34.483 MHz | 68.965 Mbps | 0.0191 |
| S.K. * Size (bit) | Insertion of S.K. * | Modular Inverse of S.K. * | Insertion of A.K. ** | Modular Inverse of A.K. ** | Total |
|---|---|---|---|---|---|
| 32 | 2 | 5 | 6 | 61 | 74 |
| 64 | 4 | 8 | 6 | 61 | 79 |
| 128 | 8 | 12 | 6 | 61 | 87 |
| 256 | 16 | 19 | 6 | 61 | 102 |
| Operation | Original CPU-Based LEAIoT [17] (ms) | The Proposed FPGA-Based Architecture (ms) |
|---|---|---|
| 32-bit key generation | 4 | 0.002146 |
| 64-bit key generation | 10 | 0.002291 |
| 128-bit key generation | 16 | 0.002523 |
| 256-bit key generation | 22 | 0.002958 |
| Encr/Decr * of 100 kilobits | 210 | 1.45 |
| Encr/Decr * of 300 kilobits | 275 | 4.35 |
| Encr/Decr * of 500 kilobits | 290 | 7.25 |
| Encr/Decr * of 1000 kilobits | 386 | 14.5 |
| Algorithm | Key Size | LUTs | FFs | Frequency (MHz) | Throughput (Mbps) |
|---|---|---|---|---|---|
| SNOW 3G [37] | 128 | 7881 | 2391 | 28.84 | 922.88 |
| AES-128 [38] | 128 | 20402/14798 | 8704/1345 | 332.34/272.33 | 4342/3485 |
| AES-MPPRM [39] | 128 | 8129 | 7119 | 81.328 | 42.92 |
| PRESENT [40] | 80/128 | 215/264 | 153/201 | 213.81/194.63 | 102.89/91.59 |
| ZUC [41] | 256 | 2494 | 1512 | 209.346 | 6540 |
| CLEFIA [42] | 128/192/256 | 1725 | 663 | 147 | 990/818/696 |
| RC4 [43] | - | 277 | 197 | 123.64 | 41.21 |
| Proposed design | 32/64/128/256 | 2700 | 815 | 34.483 | 68.965 |
Publisher’s Note: MDPI stays neutral with regard to jurisdictional claims in published maps and institutional affiliations. |
© 2022 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).
Share and Cite
Aivaliotis, V.; Tsantikidou, K.; Sklavos, N. IoT-Based Multi-Sensor Healthcare Architectures and a Lightweight-Based Privacy Scheme. Sensors 2022, 22, 4269. https://doi.org/10.3390/s22114269
Aivaliotis V, Tsantikidou K, Sklavos N. IoT-Based Multi-Sensor Healthcare Architectures and a Lightweight-Based Privacy Scheme. Sensors. 2022; 22(11):4269. https://doi.org/10.3390/s22114269
Chicago/Turabian StyleAivaliotis, Vassileios, Kyriaki Tsantikidou, and Nicolas Sklavos. 2022. "IoT-Based Multi-Sensor Healthcare Architectures and a Lightweight-Based Privacy Scheme" Sensors 22, no. 11: 4269. https://doi.org/10.3390/s22114269
APA StyleAivaliotis, V., Tsantikidou, K., & Sklavos, N. (2022). IoT-Based Multi-Sensor Healthcare Architectures and a Lightweight-Based Privacy Scheme. Sensors, 22(11), 4269. https://doi.org/10.3390/s22114269







