Towards Scalable and Efficient Architecture for Modeling Trust in IoT Environments
Abstract
1. Introduction
Motivation and Contributions
“A system-level horizontal architecture that distributes resources and services of computing, storage, control, and networking anywhere along the continuum from Cloud to Things”.
- We propose a horizontal architecture for Fog environments utilizing the Chord protocol.
- We show how trust modeling can be mapped into our proposed architecture.
- We verify the scalability and efficiency of our proposed architecture.
2. Related Work
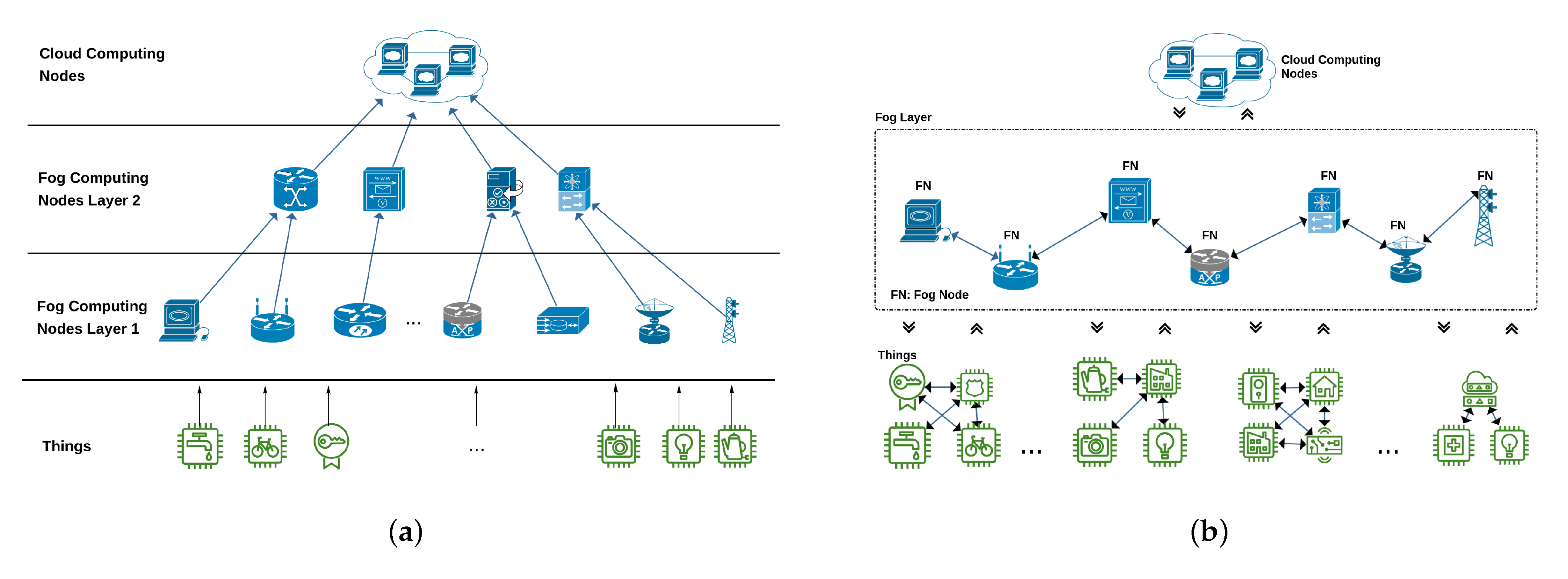
2.1. Vertical Fog Architectures
2.2. Horizontal Fog Architectures
2.3. Summary
- Enables Fog sites to complement each other in order to satisfy the needs between user’s devices and Cloud Computing centers.
- Each Fog node needs to know the location of other nodes. Therefore, it scales well with the number of Fog nodes.
- Efficient location solution since lookups take messages.
- Lookup information is maintained as Fog nodes join and leave the system.
3. Proposed Chord-based Fog Architecture
3.1. Functional Architecture
- Where shall a data item be stored.
- How does a requester find the actual location of a data item.
- How to limit the complexity for communication and storage.
- How to ensure robustness and resilience in case of faults and frequent changes.
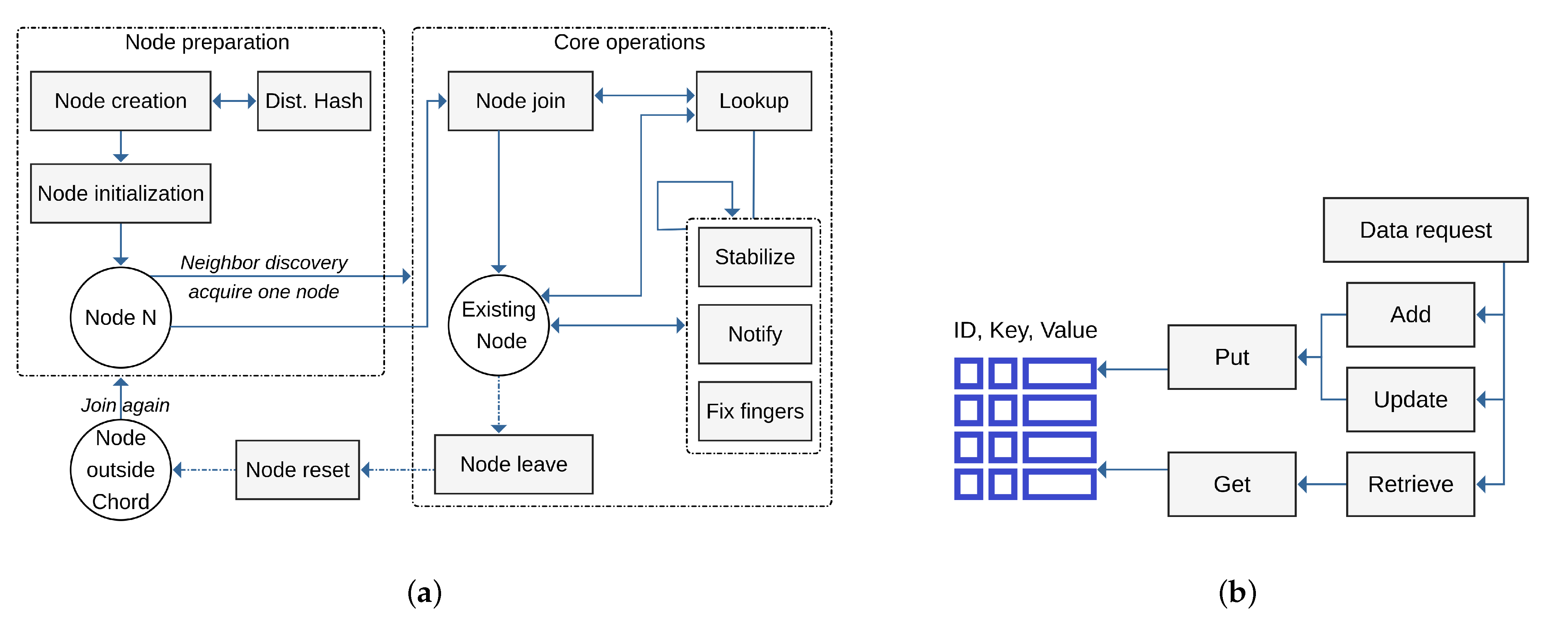
3.2. Operational Architecture
3.2.1. Node Management
3.2.2. Data Management
4. Trust Model Mapping
4.1. Overview
4.2. Inter-Fog Trust Representation and Usage
4.3. Intra-Fog Trust Representation and Usage
4.4. Trust Transaction Example
- The SC coordinator updates its experience as described in Section 4.5.
- The SC coordinator also sends this experience to the SP coordinator so that the trustworthiness of SP is updated (i.e., updating the ITT).
- The SC coordinator disseminates this experience through Chord so that the reputation of SP coordinator is updated. This information is basically aggregated with previously stored reputation using consensus operator as described in Section 4.5.
4.5. Evolving Trust Using Subjective Logic
5. Performance Evaluation
5.1. Experimental Environment
5.1.1. Contiki Operating System
- Supporting various platforms such as Z1, Wismote, MicaZ, and SKY motes; microcontrollers such as Atmel AVR family, TI MSP430 family, and ST STM32w; and radios such as the Texas Instruments CC1020, CC2420, and CC2520, and RFM TR1001.
- Supporting dynamic and efficient memory management and runs utilizing small memory sizes, i.e., RAM (10 Kbytes) and ROM (30 Kbytes).
- Providing two kinds of networking: non-IP networking and IP networking. The former is enabled through Rime stack and the latter is enabled through uIPv4 and uIPv6 stacks.
- Implementing the adaptation layer, 6LoWPAN, to support uIPv6 seamless operations.
- Providing various implementations of RDC and MAC protocols.
- Comes with Cooja, a built-in flexible hardware-level emulator.
5.1.2. Cooja Simulator
- It mimics the same instruction sets of IoT nodes and this facilitates modeling of the fine-grained node behavior.
- It runs a simulation at the hardware-level utilizing genuine hardware profiles. As a result, the compiled code can be uploaded into real platform.
- It evaluates the proposed solutions under real conditions by exploiting the available network models such as topology, radio propagation, medium interference, and link quality models.
- It eases the development and evaluation of IoT network protocols and supports both command line and graphical interfaces.
5.2. Experimental Methodology
- select a radio medium model such as distance/constant loss Unit Disk Graph Model (UDGM), Directed Graph Radio Medium (DGRM), or Multi-path Ray-tracer Medium (MRM);
- select a mote type from the supported motes such as Z1, Wismote, MicaZ, or SKY mote and select the number of motes;
- select a network topology such as uniformed 2D-Grid or random positioning; and
- select the transmission range for the populated nodes.
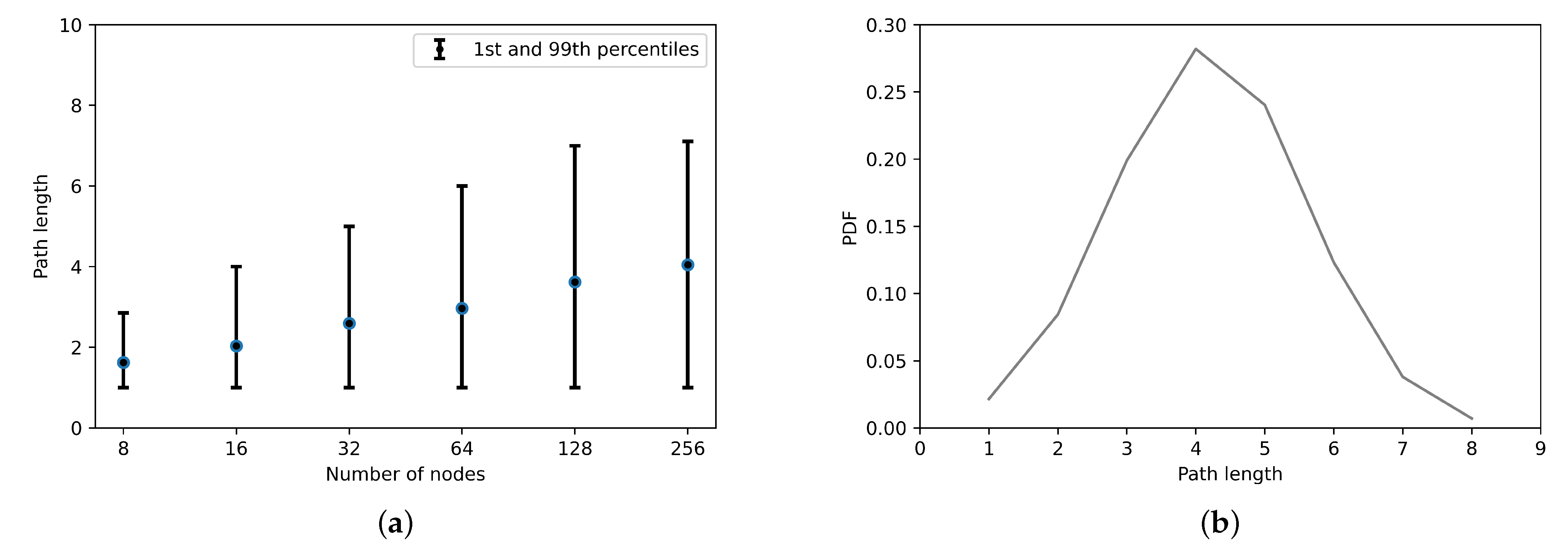
5.3. Verification of the Proposed Model
5.3.1. Load Balancing
5.3.2. Path Length
5.3.3. Simultaneous Node Failures
5.3.4. Lookups during Stabilization
5.3.5. Lookup Latency
5.4. Mobility Effect on Packets Delivery
5.5. Energy Consumption
6. Proposed Architecture Realism and limitations
7. Conclusions and Future Work
Author Contributions
Funding
Institutional Review Board Statement
Informed Consent Statement
Data Availability Statement
Acknowledgments
Conflicts of Interest
Abbreviations
| IoS | Internet of Services |
| CPS | Cyber Physical Systems |
| FCD | Fog Computing Domain |
| IoT | Internet of Things |
| DHT | Distributed Hash Table |
References
- Fortino, G.; Savaglio, C.; Spezzano, G.; Zhou, M. Internet of Things as System of Systems: A Review of Methodologies, Frameworks, Platforms, and Tools. IEEE Trans. Syst. Man Cybern. Syst. 2021, 51, 223–236. [Google Scholar] [CrossRef]
- Zahra, S.R.; Chishti, M.A. Smart Cities Pilot Projects: An IoT Perspective. In Smart Cities: A Data Analytics Perspective. Lecture Notes in Intelligent Transportation and Infrastructure; Khan, M.A., Algarni, F., Quasim, M.T., Eds.; Springer International Publishing: Cham, Switzerland, 2021; pp. 1–9. [Google Scholar] [CrossRef]
- Confais, B.; Lebre, A.; Parrein, B. A Fog storage software architecture for the Internet of Things. Adv. Edge Comput. Massive Parallel Process. Appl. 2020, 35, 61–105. [Google Scholar]
- Kapitonov, A.; Lonshakov, S.; Berman, I.; Ferrer, E.C.; Bonsignorio, F.P.; Bulatov, V.; Svistov, A. Robotic Services for New Paradigm Smart Cities Based on Decentralized Technologies. Ledger 2019, 4, 56–66. [Google Scholar] [CrossRef]
- Schwandt, F. Internet of Things (IoT) connected devices installed base worldwide from 2015 to 2025 (in billions). Statista. 2018. Available online: https://www.statista.com/statistics/471264/iot-number-of-connected-devices-worldwide/ (accessed on 20 January 2021).
- Atlam, H.F.; Hemdan, E.E.D.; Alenezi, A.; Alassafi, M.O.; Wills, G.B. Internet of Things Forensics: A Review. Internet Things 2020, 100220. [Google Scholar] [CrossRef]
- Li, Y.; Orgerie, A.C.; Rodero, I.; Amersho, B.L.; Parashar, M.; Menaud, J.M. End-to-end energy models for Edge Cloud-based IoT platforms: Application to data stream analysis in IoT. Future Gener. Comput. Syst. 2018, 87, 667–678. [Google Scholar] [CrossRef]
- Wu, F.; Wu, T.; Yuce, M.R. An internet-of-things (IoT) network system for connected safety and health monitoring applications. Sensors 2019, 19, 21. [Google Scholar] [CrossRef]
- Varadharajan, V.; Bansal, S. Data security and privacy in the internet of things (IoT) environment. In Connectivity Frameworks for Smart Devices; Springer: Berlin, Germany, 2016; pp. 261–281. [Google Scholar]
- Kandasamy, K.; Srinivas, S.; Achuthan, K.; Rangan, V.P. IoT cyber risk: A holistic analysis of cyber risk assessment frameworks, risk vectors, and risk ranking process. EURASIP J. Inf. Secur. 2020, 2020, 1–18. [Google Scholar] [CrossRef]
- Abdul-Ghani, H.A.; Konstantas, D. A comprehensive study of security and privacy guidelines, threats, and countermeasures: An IoT perspective. J. Sens. Actuator Netw. 2019, 8, 22. [Google Scholar] [CrossRef]
- Karagiannis, V.; Schulte, S. Comparison of alternative architectures in fog computing. In Proceedings of the 2020 IEEE 4th International Conference on Fog and Edge Computing (ICFEC), Melbourne, Australia, 14 May 2020; pp. 19–28. [Google Scholar]
- Al-Khafajiy, M.; Baker, T.; Al-Libawy, H.; Maamar, Z.; Aloqaily, M.; Jararweh, Y. Improving fog computing performance via fog-2-fog collaboration. Future Gener. Comput. Syst. 2019, 100, 266–280. [Google Scholar] [CrossRef]
- Lu, X.; Liu, J.; Zhao, H. Collaborative target tracking of IoT heterogeneous nodes. Measurement 2019, 147, 106872. [Google Scholar] [CrossRef]
- Palade, A.; Clarke, S. Collaborative agent communities for resilient service composition in mobile environments. IEEE Trans. Serv. Comput. (Early Access) 2020. [Google Scholar] [CrossRef]
- Ali, B.; Awad, A.I. Cyber and Physical Security Vulnerability Assessment for IoT-Based Smart Homes. Sensors 2018, 18, 817. [Google Scholar] [CrossRef]
- Cui, J.; Xu, W.; Zhong, H.; Zhang, J.; Xu, Y.; Liu, L. Privacy-preserving authentication using a double pseudonym for internet of vehicles. Sensors 2018, 18, 1453. [Google Scholar] [CrossRef]
- Suárez-Albela, M.; Fernández-Caramés, T.M.; Fraga-Lamas, P.; Castedo, L. A practical evaluation of a high-security energy-efficient gateway for IoT fog computing applications. Sensors 2017, 17, 1978. [Google Scholar] [CrossRef]
- Azzedin, F.; Ghaleb, M. Internet-of-Things and Information Fusion: Trust Perspective Survey. Sensors 2019, 19, 1929. [Google Scholar] [CrossRef] [PubMed]
- Liang, C.; Wen, F.; Wang, Z. Trust-based distributed Kalman filtering for target tracking under malicious cyber attacks. Inf. Fusion 2019, 46, 44–50. [Google Scholar] [CrossRef]
- Kouicem, D.E.; Bouabdallah, A.; Lakhlef, H. An Efficient Architecture for Trust Management in IoE Based Systems of Systems. In Proceedings of the IEEE 2018 13th Annual Conference on System of Systems Engineering (SoSE), Paris, France, 19–22 June 2018; pp. 138–143. [Google Scholar]
- Souissi, I.; Azzouna, N.B.; Said, L.B. A Multi-Level Study of Information Trust Models in WSN-assisted IoT. Comput. Netw. 2019, 151, 12–30. [Google Scholar] [CrossRef]
- Lin, Z.; Dong, L. Clarifying trust in social internet of things. IEEE Trans. Knowl. Data Eng. 2018, 30, 234–248. [Google Scholar] [CrossRef]
- Gai, F.; Zhang, J.; Zhu, P.; Jiang, X. Multidimensional Trust-Based Anomaly Detection System in Internet of Things. In International Conference on Wireless Algorithms, Systems, and Applications; Springer: Berlin, Germany, 2017; pp. 302–313. [Google Scholar]
- Khani, M.; Wang, Y.; Orgun, M.A.; Zhu, F. Context-Aware Trustworthy Service Evaluation in Social Internet of Things. In International Conference on Service-Oriented Computing; Springer: Berlin, Germany, 2018; pp. 129–145. [Google Scholar]
- Nkomo, M.; Hancke, G.; Abu-Mahfouz, A.; Sinha, S.; Onumanyi, A. Overlay Virtualized Wireless Sensor Networks for Application in Industrial Internet of Things: A Review. Sensors 2018, 18, 3215. [Google Scholar] [CrossRef] [PubMed]
- Koo, D.; Hur, J. Privacy-preserving deduplication of encrypted data with dynamic ownership management in fog computing. Future Gener. Comput. Syst. 2018, 78, 739–752. [Google Scholar] [CrossRef]
- Qi, Q.; Tao, F. A smart manufacturing service system based on edge computing, fog computing, and cloud computing. IEEE Access 2019, 7, 86769–86777. [Google Scholar] [CrossRef]
- Pramanik, P.K.D.; Pal, S.; Brahmachari, A.; Choudhury, P. Processing IoT Data: From Cloud to Fog—It’s Time to Be Down to Earth. In Applications of Security, Mobile, Analytic, and Cloud (SMAC) Technologies for Effective Information Processing and Management; IGI Global: Hershey, PA, USA, 2018; pp. 124–148. [Google Scholar]
- Sengan, S.; Subramaniyaswamy, V.; Nair, S.K.; Indragandhi, V.; Manikandan, J.; Ravi, L. Enhancing cyber-physical systems with hybrid smart city cyber security architecture for secure public data-smart network. Future Gener. Comput. Syst. 2020, 112, 724–737. [Google Scholar] [CrossRef]
- Zhang, C. Design and application of fog computing and Internet of Things service platform for smart city. Future Gener. Comput. Syst. 2020, 112, 630–640. [Google Scholar] [CrossRef]
- Vasileios, M.; Panagiotis, S.; Ioannis, M. Towards Distributed Data Management in Fog Computing. Wirel. Commun. Mob. Comput. 2018, 14. [Google Scholar] [CrossRef]
- Kunal, S.; Saha, A.; Amin, R. An overview of cloud-fog computing: Architectures, applications with security challenges. Secur. Priv. 2019, 2, e72. [Google Scholar] [CrossRef]
- Couto, R.d.S.; Secci, S.; Campista, M.E.M.; Costa, L.H.M.K. Network design requirements for disaster resilience in IaaS clouds. IEEE Commun. Mag. 2014, 52, 52–58. [Google Scholar] [CrossRef]
- OpenFog Reference Architecture for Fog Computing; Tech. Rep; OPFRA001.020817; OpenFog consortium—Architecture Working Group: Fremont, CA, USA, 2017.
- Karagiannis, V.; Borkowski, M.; Venito, A.; Coelho, R.; Fohler, G. Edge Computing with Peer to Peer Interactions: Use Cases and Impact. In Workshop on Fog Computing and the IoT (IoT-Fog); IoT-Fog ’19; Association for Computing Machinery: New York, NY, USA, 2019; pp. 46–50. [Google Scholar] [CrossRef]
- Karagiannis, V.; Schulte, S.; Leitao, J.; Preguiça, N. Enabling fog computing using self-organizing compute nodes. In Proceedings of the 2019 IEEE 3rd International Conference on Fog and Edge Computing (ICFEC), Larnaca, Cyprus, 14–17 May 2019; pp. 1–10. [Google Scholar]
- Association, I.S. IEEE Standard for Adoption of OpenFog Reference Architecture for Fog Computing. IEEE Std 1934–2018 2018, 1–176. [Google Scholar] [CrossRef]
- Peng, M.; Zhao, Z.; Sun, Y. Brief Introduction of Fog Radio Access Networks. In Fog Radio Access Networks (F-RAN); Springer: Berlin, Germany, 2020; pp. 1–19. [Google Scholar]
- Ren, Z.; Lu, T.; Wang, X.; Guo, W.; Liu, G.; Chang, S. Resource scheduling for delay-sensitive application in three-layer fog-to-cloud architecture. Peer-to-Peer Netw. Appl. 2020, 13, 1474–1485. [Google Scholar] [CrossRef]
- Tang, B.; Chen, Z.; Hefferman, G.; Wei, T.; He, H.; Yang, Q. A hierarchical distributed fog computing architecture for big data analysis in smart cities. Proc. Ase Bigdata Soc. 2015, 2015, 1–6. [Google Scholar]
- Guo, Y.; Oma, R.; Nakamura, S.; Duolikun, D.; Enokido, T.; Takizawa, M. Evaluation of a two-way tree-based fog computing (TWTBFC) model. In Advances in Intelligent Systems and Computing, Proceedings of the International Conference on Innovative Mobile and Internet Services in Ubiquitous Computing, Sydney, Australia, 3–5 July 2019; Springer: Berlin, Germany, 2019; pp. 72–81. [Google Scholar]
- Oma, R.; Nakamura, S.; Enokido, T.; Takizawa, M. A Dynamic Tree-Based Fog Computing (DTBFC) Model for the Energy-Efficient IoT. In International Conference on Emerging Internetworking, Data & Web Technologies; Springer: Berlin, Germany, 2020; pp. 24–34. [Google Scholar]
- Guo, Y.; Saito, T.; Oma, R.; Nakamura, S.; Enokido, T.; Takizawa, M. Subtree-Based Fog Computing in the TWTBFC Model. In International Conference on Emerging Internetworking, Data & Web Technologies; Springer: Berlin, Germany, 2020; pp. 46–52. [Google Scholar]
- Edgex Foundry Architecture. Available online: https://docs.edgexfoundry.org/1.3/ (accessed on 11 August 2020).
- Salaht, F.A.; Desprez, F.; Lebre, A. An overview of service placement problem in fog and edge computing. ACM Comput. Surv. (CSUR) 2020, 53, 1–35. [Google Scholar] [CrossRef]
- Raghavendra, M.S.; Chawla, P.; Rana, A. A Survey of Optimization Algorithms for Fog Computing Service Placement. In Proceedings of the 2020 8th International Conference on Reliability, Infocom Technologies and Optimization, Noida, India, 4–5 June 2020; pp. 259–262. [Google Scholar]
- Souza, V.B.; Masip-Bruin, X.; Marín-Tordera, E.; Sànchez-López, S.; Garcia, J.; Ren, G.J.; Jukan, A.; Ferrer, A.J. Towards a proper service placement in combined Fog-to-Cloud (F2C) architectures. Future Gener. Comput. Syst. 2018, 87, 1–15. [Google Scholar] [CrossRef]
- Bellavista, P.; Zanni, A.; Solimando, M. A migration-enhanced edge computing support for mobile devices in hostile environments. In Proceedings of the 2017 13th International Wireless Communications and Mobile Computing Conference (IWCMC), Valencia, Spain, 26–30 June 2017; pp. 957–962. [Google Scholar]
- Deng, S.; Xiang, Z.; Yin, J.; Taheri, J.; Zomaya, A.Y. Composition-driven IoT service provisioning in distributed edges. IEEE Access 2018, 6, 54258–54269. [Google Scholar] [CrossRef]
- Stantchev, V.; Barnawi, A.; Ghulam, S.; Schubert, J.; Tamm, G. Smart items, fog and cloud computing as enablers of servitization in healthcare. Sens. Transducers 2015, 185, 121–128. [Google Scholar]
- Masri, W.; Al Ridhawi, I.; Mostafa, N.; Pourghomi, P. Minimizing delay in IoT systems through collaborative fog-to-fog (F2F) communication. In Proceedings of the 2017 Ninth International Conference on Ubiquitous and Future Networks (ICUFN), Milan, Italy, 4–7 July 2017; pp. 1005–1010. [Google Scholar]
- Zhang, W.; Zhang, Z.; Chao, H.C. Cooperative fog computing for dealing with big data in the internet of vehicles: Architecture and hierarchical resource management. IEEE Commun. Mag. 2017, 55, 60–67. [Google Scholar] [CrossRef]
- Nguyen, D.; Shen, Z.; Jin, J.; Tagami, A. ICN-Fog: An information-centric fog-to-fog architecture for data communications. In GLOBECOM 2017–2017 IEEE Global Communications Conference; IEEE: New York, NY, USA, 2017; pp. 1–6. [Google Scholar]
- Naranjo, P.G.V.; Pooranian, Z.; Shojafar, M.; Conti, M.; Buyya, R. FOCAN: A Fog-supported smart city network architecture for management of applications in the Internet of Everything environments. J. Parallel Distrib. Comput. 2019, 132, 274–283. [Google Scholar] [CrossRef]
- Oma, R.; Nakamura, S.; Enokido, T.; Takizawa, M. An energy-efficient model of fog and device nodes in IoT. In Proceedings of the IEEE 2018 32nd International Conference on Advanced Information Networking and Applications Workshops (WAINA), Krakow, Poland, 16–18 May 2018; pp. 301–306. [Google Scholar]
- Naranjo, P.G.V.; Baccarelli, E.; Scarpiniti, M. Design and energy-efficient resource management of virtualized networked Fog architectures for the real-time support of IoT applications. J. Supercomput. 2018, 74, 2470–2507. [Google Scholar] [CrossRef]
- Wang, T.; Zeng, J.; Lai, Y.; Cai, Y.; Tian, H.; Chen, Y.; Wang, B. Data collection from WSNs to the cloud based on mobile Fog elements. Future Gener. Comput. Syst. 2020, 105, 864–872. [Google Scholar] [CrossRef]
- Haseeb, K.; Islam, N.; Javed, Y.; Tariq, U.A. A Lightweight Secure and Energy-Efficient Fog-Based Routing Protocol for Constraint Sensors Network. Energies 2021, 14, 89. [Google Scholar] [CrossRef]
- Stoica, I.; Morris, R.; Liben-Nowell, D.; Karger, D.R.; Kaashoek, M.F.; Dabek, F.; Balakrishnan, H. Chord: A scalable peer-to-peer lookup protocol for internet applications. IEEE/ACM Trans. Netw. (TON) 2003, 11, 17–32. [Google Scholar] [CrossRef]
- Lua, E.K.; Crowcroft, J.; Pias, M.; Sharma, R.; Lim, S. A survey and comparison of peer-to-peer overlay network schemes. IEEE Commun. Surv. Tutor. 2005, 7, 72–93. [Google Scholar]
- Jøsang, A.; Marsh, S.; Pope, S. Exploring different types of trust propagation. In International Conference on Trust Management; Springer: Berlin, Germany, 2006; pp. 179–192. [Google Scholar]
- Jøsang, A. Decision making under vagueness and uncertainty. In Subjective Logic; Springer: Berlin, Germany, 2016; pp. 51–82. [Google Scholar]
- Dybedokken, T.S. Trust Management in Fog Computing. Master’s Thesis, NTNU, Trondheim, Norway, 2017. [Google Scholar]
- Alemneh, E.; Senouci, S.M.; Brunet, P.; Tegegne, T. A two-way trust management system for fog computing. Future Gener. Comput. Syst. 2020, 106, 206–220. [Google Scholar] [CrossRef]
- Dunkels, A.; Gronvall, B.; Voigt, T. Contiki-a lightweight and flexible operating system for tiny networked sensors. In Proceedings of the 29th Annual IEEE International Conference on Local Computer Networks, Tampa, FL, USA, 16–18 November 2004; pp. 455–462. [Google Scholar]
- Hahm, O.; Baccelli, E.; Petersen, H.; Tsiftes, N. Operating systems for low-end devices in the internet of things: A survey. IEEE Internet Things J. 2015, 3, 720–734. [Google Scholar] [CrossRef]
- Zikria, Y.B.; Afzal, M.K.; Ishmanov, F.; Kim, S.W.; Yu, H. A survey on routing protocols supported by the Contiki Internet of things operating system. Future Gener. Comput. Syst. 2018, 82, 200–219. [Google Scholar] [CrossRef]
- Kritsis, K.; Papadopoulos, G.Z.; Gallais, A.; Chatzimisios, P.; Theoleyre, F. A tutorial on performance evaluation and validation methodology for low-power and lossy networks. IEEE Commun. Surv. Tutor. 2018, 20, 1799–1825. [Google Scholar] [CrossRef]
- Karagiannis, V.; Desai, N.; Schulte, S.; Punnekkat, S. Addressing the node discovery problem in fog computing. In 2nd Workshop on Fog Computing and the IoT (Fog-IoT 2020); Schloss Dagstuhl-Leibniz-Zentrum für Informatik: Wadern, Germany, 2020. [Google Scholar]
- Tom, R.J.; Sankaranarayanan, S.; de Albuquerque, V.H.C.; Rodrigues, J.J. Aggregator based RPL for an IoT-fog based power distribution system with 6LoWPAN. China Commun. 2020, 17, 104–117. [Google Scholar] [CrossRef]
- Sheltami, T.R.; Shahra, E.Q.; Shakshuki, E.M. Fog computing: Data streaming services for mobile end-users. Procedia Comput. Sci. 2018, 134, 289–296. [Google Scholar] [CrossRef]
- Silva, R.; Silva, J.S.; Boavida, F. Opportunistic fog computing: Feasibility assessment and architectural proposal. In Proceedings of the 2017 IFIP/IEEE Symposium on Integrated Network and Service Management (IM), Lisbon, Portugal, 8–12 May 2017; pp. 510–516. [Google Scholar]
- Zahra, S.R.; Chishti, M.A. Fuzzy logic and Fog based Secure Architecture for Internet of Things (FLFSIoT). J. Ambient. Intell. Humaniz. Comput. 2020. [Google Scholar] [CrossRef]
- Kavitha, B.; Vallikannu, R.; Sankaran, K.S. Delay-aware concurrent data management method for IoT collaborative mobile edge computing environment. Microprocess. Microsyst. 2020, 74, 103021. [Google Scholar] [CrossRef]
- Esmaeilyfard, R.; Naderi, M. Distributed composition of complex event services in IoT network. J. Supercomput. 2020, 1–22. [Google Scholar] [CrossRef]
- Pardeshi, M.S.; Yuan, S.M. SMAP fog/edge: A secure mutual authentication protocol for fog/edge. IEEE Access 2019, 7, 101327–101335. [Google Scholar] [CrossRef]
- Surati, S.; Jinwala, D.C.; Garg, S. A survey of simulators for P2P overlay networks with a case study of the P2P tree overlay using an event-driven simulator. Eng. Sci. Technol. Int. J. 2017, 20, 705–720. [Google Scholar] [CrossRef]
- Al-Kashoash, H.A.; Amer, H.M.; Mihaylova, L.; Kemp, A.H. Optimization-based hybrid congestion alleviation for 6LoWPAN networks. IEEE Internet Things J. 2017, 4, 2070–2081. [Google Scholar] [CrossRef]
- Mahyoub, M.; Mahmoud, A.; Abu-Amara, M.; Sheltami, T. An Efficient RPL-based Mechanism for Node-to-Node Communications in IoT. IEEE Internet Things J. (Early Access) 2020. [Google Scholar] [CrossRef]
- Ruckebusch, P.; Devloo, J.; Carels, D.; De Poorter, E.; Moerman, I. An evaluation of link estimation algorithms for RPL in dynamic wireless sensor networks. In Lecture Notes of the Institute for Computer Sciences, Social Informatics and Telecommunications Engineering, Proceedings of the International Internet of Things Summit, Rome, Italy, 27–29, October 2015; Springer: Berlin, Germany, 2015; pp. 349–361. [Google Scholar]
- Aschenbruck, N.; Ernst, R.; Gerhards-Padilla, E.; Schwamborn, M. BonnMotion: A mobility scenario generation and analysis tool. In Proceedings of the 3rd International ICST Conference on Simulation Tools and Techniques, Malaga, Spain, 15–19 March 2010; pp. 1–10. [Google Scholar]
- Dunkels, A.; Osterlind, F.; Tsiftes, N.; He, Z. Software-based on-line energy estimation for sensor nodes. In Proceedings of the 4th Workshop on Embedded Networked Sensors, Cork, Ireland, 25–26 June 2007; pp. 28–32. [Google Scholar]
- Mahmoud, A.; Mahyoub, M.; Sheltami, T.; Abu-Amara, M. Traffic-aware auto-configuration protocol for service oriented low-power and lossy networks in IoT. Wirel. Netw. 2019, 25, 4231–4246. [Google Scholar] [CrossRef]
- Instruments, T. MSP430F543x, MSP430F541x Mixed-Signal Microcontrollers. Available online: https://www.ti.com/lit/ds/symlink/msp430f5437.pdf (accessed on 11 August 2020).
- He, D. A Novel Methodology for Planning Reliable Wireless Sensor Networks. Ph.D. Thesis, Universidad Politécnica de Madrid, Madrid, Spain, 2014. [Google Scholar]
- Sharma, H.; Haque, A.; Jaffery, Z.A. Maximization of wireless sensor network lifetime using solar energy harvesting for smart agriculture monitoring. Ad Hoc Netw. 2019, 94, 101966. [Google Scholar] [CrossRef]
- Perez Abreu, D.; Velasquez, K.; Curado, M.; Monteiro, E. A comparative analysis of simulators for the Cloud to Fog continuum. Simul. Model. Pract. Theory 2020, 101, 102029. [Google Scholar] [CrossRef]














| Parameter | Value |
|---|---|
| Platform | Contiki v with Cooja simulator |
| Network topology | Random |
| Mote type | Wismote with 16 KB RAM and 128 KB ROM |
| Network scale | Variable (8, 16, 32, 64, 128 and 256 nodes) |
| Network layer | RPL + uIPv6 + 6LoWPAN |
| Radio environment | Unit Disk Graph Medium (UDGM) |
| Transmission range | 60 m |
| MAC & PHY | Carrier Sense Multiple Access (CSMA) /Collision Avoidance (CA) & IEEE |
| RDC/ CCR | ContikiMAC/64 Hz and NullRDC/128Hz |
| Number of iterations | 10 iterations |
Publisher’s Note: MDPI stays neutral with regard to jurisdictional claims in published maps and institutional affiliations. |
© 2021 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).
Share and Cite
Ghaleb, M.; Azzedin, F. Towards Scalable and Efficient Architecture for Modeling Trust in IoT Environments. Sensors 2021, 21, 2986. https://doi.org/10.3390/s21092986
Ghaleb M, Azzedin F. Towards Scalable and Efficient Architecture for Modeling Trust in IoT Environments. Sensors. 2021; 21(9):2986. https://doi.org/10.3390/s21092986
Chicago/Turabian StyleGhaleb, Mustafa, and Farag Azzedin. 2021. "Towards Scalable and Efficient Architecture for Modeling Trust in IoT Environments" Sensors 21, no. 9: 2986. https://doi.org/10.3390/s21092986
APA StyleGhaleb, M., & Azzedin, F. (2021). Towards Scalable and Efficient Architecture for Modeling Trust in IoT Environments. Sensors, 21(9), 2986. https://doi.org/10.3390/s21092986







