Modeling Time Requirements of CPS in Wireless Networks
Abstract
1. Introduction
- A Schedulability and Scalability algorithm capable of determining whether a subscription can be handled by a given network topology considering the CPS time constraints;
- The introduction of a network unreliability abstraction factor (modeled as a margin of safety) that impacts the scalability and schedulability analysis by applying a time reservation restraint to the acceptance of subscriptions while enabling the achievement of higher network loads (and therefore use) when compared to the conservative worst-case analysis;
- An Evaluation of the proposed algorithm against simulations considering a wide-range network load with three case studies;
- A discussion about the use of the simulations to adjust the margin of safety to fit the network capacity, thus improving utility.
2. Network Model
- Publish-Subscribe: nodes and gateways interact using a publish-subscribe policy, with gateways sending interest messages to express interest on a given of data, produced in a given of space, during a given time . Nodes matching these criteria periodically send reply messages every units of time. Data is assumed to be valid from the perspective of applications until they expire at time instant . Response messages carry the requested data along with information about its , , a , and an (the concept of message expiry is discussed below).
- Periodic Behavior: all traffic in the network originates from periodic responses to known interest messages. Event-driven applications are not allowed and control messages are either known beforehand and can be accounted for, or are modeled as a reservation of network capacity. The periodic responses respect the Interest during the Interest time .
- Expiry: data carried by the network is only valid during a given time period, expressed by the expiry of the containing response message (). Messages on routing queues are kept ordered by , so messages closer to expiration are routed first. Expired messages are discarded.
3. Algorithm
| Algorithm 1 Network Load |
| 1: procedure (, , , , ) |
| 2: ordered by ascendant, where |
| 3: ordered by descendent, where |
| 4: |
| 5: = 0 |
| 6: = true |
| 7: |
| 8: for each do |
| 9: = |
| 10: for each do |
| 11: = = = 0 |
| 12: = 0 |
| 13: for each | <= do |
| 14: if and then |
| 15: += |
| 16: if = then |
| 17: += |
| 18: end if |
| 19: end if |
| 20: end for |
| 21: end for |
| 22: for each do |
| 23: = + |
| 24: += + |
| 25: if then |
| 26: |
| 27: += n. |
| 28: += |
| 29: end if |
| 30: for each do |
| 31: += |
| 32: end for |
| 33: end for |
| 34: = |
| 35: = - |
| 36: = / |
| 37: if (/) < or > then |
| 38: = false |
| 39: |
| 40: end if |
| 41: end for |
| 42: return |
| 43: end procedure |
4. Case Study
4.1. SmartData and Trustful Space-Time Protocol
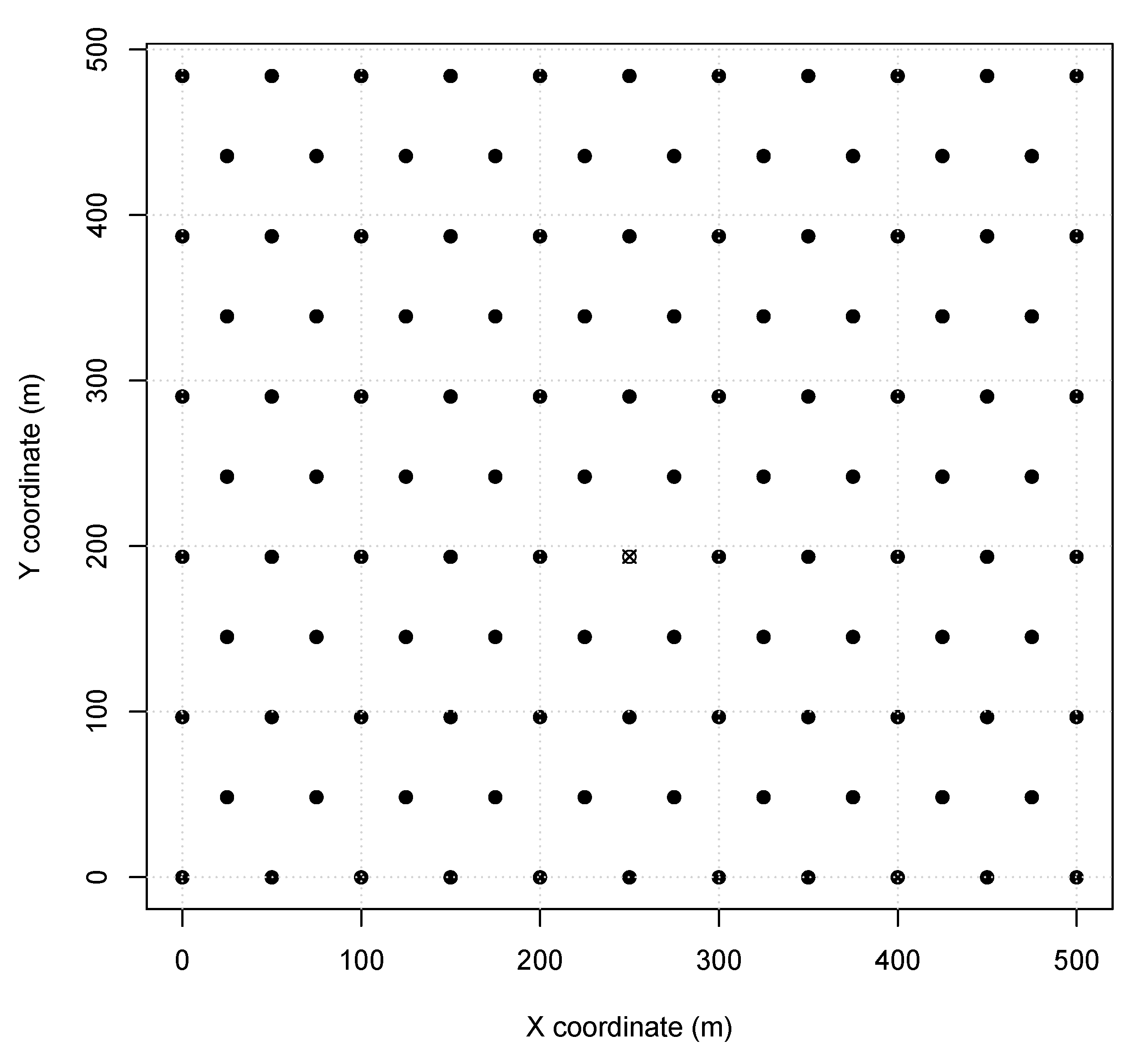
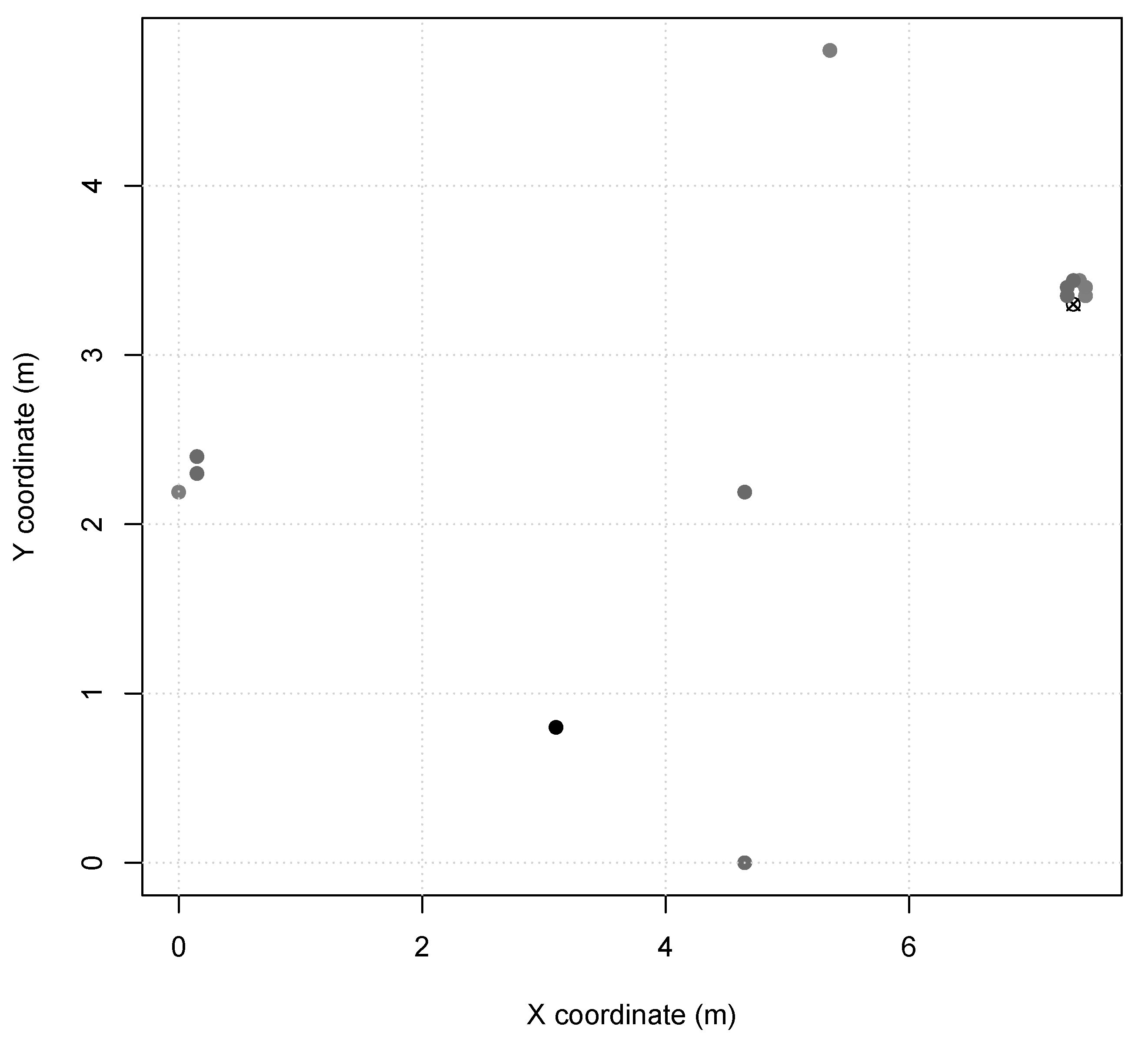
4.2. Experimental Setup
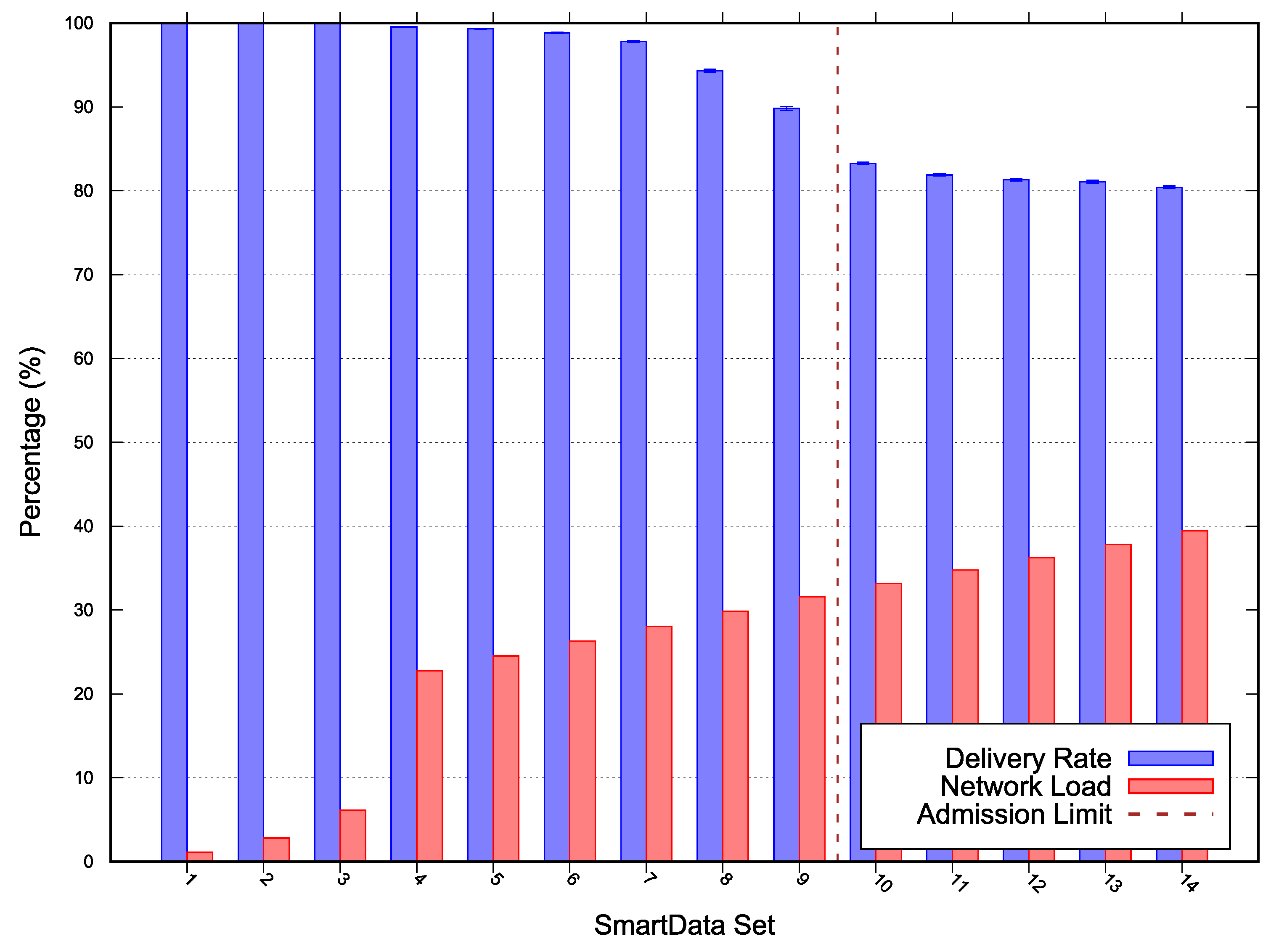
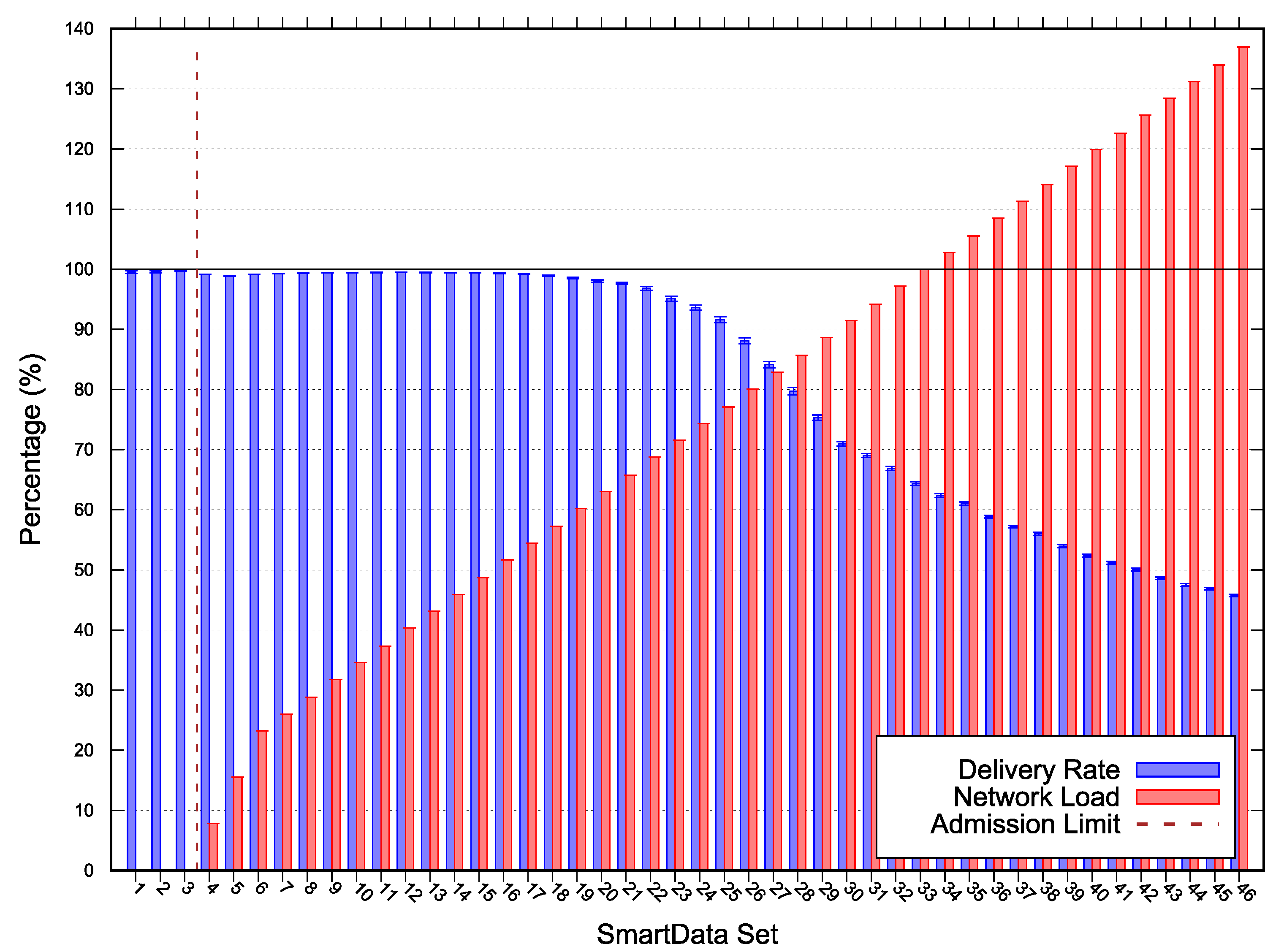
4.3. Results
5. Discussion
6. Related Works
6.1. Schedulability
6.2. Scalability
7. Conclusions
Author Contributions
Funding
Conflicts of Interest
References
- Derler, P.; Lee, E.; Sangiovanni-Vincentelli, A. Modeling Cyber-Physical Systems. Proc. IEEE 2012, 100, 13–28. [Google Scholar] [CrossRef]
- Hu, L.; Xie, N.; Kuang, Z.; Zhao, K. Review of Cyber-Physical System Architecture. In Proceedings of the 15th International Symposium on Object/Component/Service-Oriented Real-Time Distributed Computing Workshops, Shenzhen, China, 11 April 2012. [Google Scholar] [CrossRef]
- Mo, L.; You, P.; Cao, X.; Song, Y.; Kritikakou, A. Event-Driven Joint Mobile Actuators Scheduling and Control in Cyber-Physical Systems. IEEE Trans. Ind. Inf. 2019, 15, 5877–5891. [Google Scholar] [CrossRef]
- Khan, M.U.; Li, S.; Wang, Q.; Shao, Z. CPS Oriented Control Design for Networked Surveillance Robots With Multiple Physical Constraints. IEEE Trans. Comput. Aided Des. Integr. Circuits Syst. 2016, 35, 778–791. [Google Scholar] [CrossRef]
- Kannengiesser, U.; Müller, H. Multi-level, Viewpoint-Oriented Engineering of Cyber-Physical Production Systems: An Approach Based on Industry 4.0, System Architecture and Semantic Web Standards. In Proceedings of the 2018 44th Euromicro Conference on Software Engineering and Advanced Applications (SEAA), Prague, Czech Republic, 29–31 August 2018; pp. 331–334. [Google Scholar] [CrossRef]
- Wang, Z.; Song, H.; Watkins, D.W.; Ong, K.G.; Xue, P.; Yang, Q.; Shi, X. Cyber-physical systems for water sustainability: challenges and opportunities. IEEE Commun. Mag. 2015, 53, 216–222. [Google Scholar] [CrossRef]
- Iyer, G.; Agrawal, P.; Cardozo, R.S. Analytic model and simulation study for network scalability in smart utility networks. In Proceedings of the 2013 IEEE Innovative Smart Grid Technologies-Asia (ISGT Asia), Bangalore, India, 10–13 November 2013. [Google Scholar] [CrossRef]
- Lee, E. The Past, Present and Future of Cyber-Physical Systems: A Focus on Models. Sensors 2015, 15, 4837–4869. [Google Scholar] [CrossRef] [PubMed]
- Benhai, Z.; Yuan, Y.; Hongyan, M.; Dapeng, Y.; Libo, X. Research on optimal ELSF real-time scheduling algorithm for CPS. In Proceedings of the 2016 Chinese Control and Decision Conference (CCDC), Yinchuan, China, 28–30 May 2016; pp. 6867–6871. [Google Scholar] [CrossRef]
- Li, F.; Liu, C.; Yu, G.; Chen, Z. A Scheduling Algorithm of Events with Uncertain Timestamps for CPS. In Proceedings of the 2017 3rd International Conference on Big Data Computing and Communications (BIGCOM), Chengdu, China, 10–11 August 2017; pp. 313–319. [Google Scholar] [CrossRef]
- Prieto, M.; Pernía, A.; Nuño, F.; Díaz, J.; Villegas, P. Development of a Wireless Sensor Network for Individual Monitoring of Panels in a Photovoltaic Plant. Sensors 2014, 14, 2379–2396. [Google Scholar] [CrossRef] [PubMed]
- Boussard, M.; Bui, D.T.; Douville, R.; Justen, P.; Sauze, N.L.; Peloso, P.; Vandeputte, F.; Verdot, V. Future Spaces: Reinventing the Home Network for Better Security and Automation in the IoT Era. Sensors 2018, 18, 2986. [Google Scholar] [CrossRef] [PubMed]
- Horvath, P.; Yampolskiy, M.; Koutsoukos, X. Efficient Evaluation of Wireless Real-Time Control Networks. Sensors 2015, 15, 4134–4153. [Google Scholar] [CrossRef] [PubMed]
- Frohlich, A.A.; Resner, D. Data-Centric Cyber-Physical Systems Design with Smartdata. In Proceedings of the 2018 Winter Simulation Conference (WSC), Gothenburg, Sweden, 9–12 December 2018. [Google Scholar] [CrossRef]
- Resner, D.; Fröhlich, A.A. TSTP MAC: A Foundation for the Trustful Space-Time Protocol. In Proceedings of the 14th IEEE/IFIP International Conference on Embedded and Ubiquitous Computing (EUC 2016), Paris, France, 24 August 2016. [Google Scholar]
- Ozen, S.; Oktug, S. Adaptive sink selection for WSNs using forwarder set based dynamic duty cycling. In Proceedings of the 2014 Eleventh Annual IEEE International Conference on Sensing, Communication, and Networking Workshops (SECON Workshops), Singapore, 30 June–4 July 2014; pp. 7–12. [Google Scholar] [CrossRef]
- Zhang, D.; Dong, E. A Virtual Coordinate-Based Bypassing Void Routing for Wireless Sensor Networks. IEEE Sens. J. 2015, 15, 3853–3862. [Google Scholar] [CrossRef]
- Fröhlich, A.A.; Scheffel, R.M.; Kozhaya, D.; Veríssimo, P.E. Byzantine Resilient Protocol for the IoT. IEEE Internet Things J. 2019, 6, 2506–2517. [Google Scholar] [CrossRef]
- Harbin, J.; Burns, A.; Davis, R.I.; Indrusiak, L.S.; Bate, I.; Griffin, D. The AirTight Protocol for Mixed Criticality Wireless CPS. ACM Trans. Cyber-Phys. Syst. 2020, 4, 1–28. [Google Scholar] [CrossRef]
- Burns, A.; Harbin, J.; Indrusiak, L.; Bate, I.; Davis, R.; Griffin, D. AirTight: A Resilient Wireless Communication Protocol for Mixed-Criticality Systems. In Proceedings of the 2018 IEEE 24th International Conference on Embedded and Real-Time Computing Systems and Applications (RTCSA), Hakodate, Japan, 28–31 August 2018; pp. 65–75. [Google Scholar] [CrossRef]
- Nayak, N.G.; Dürr, F.; Rothermel, K. Time-sensitive Software-defined Network (TSSDN) for Real-time Applications. In Proceedings of the 24th International Conference on Real-Time Networks and Systems, New York, NY, USA, 19–21 October 2016; pp. 193–202. [Google Scholar] [CrossRef]
- Ting, K.; Liu, T.; Tibbets, L.; Figueira, S. CapPlan—A Network Capacity Planning Tool for LambdaGrids. In Proceedings of the International conference on Networking and Services (ICNS’06), Silicon Valley, CA, USA, 16–21 July 2006; p. 65. [Google Scholar] [CrossRef]
- Zats, S.; Su, R.; Watteyne, T.; Pister, K.S. Scalability of Time Synchronized wireless sensor networking. In Proceedings of the IECON 2011—37th Annual Conference of the IEEE Industrial Electronics Society, Melbourne, Victoria, Australia, 7–10 November 2011. [Google Scholar] [CrossRef]
- Agamy, A.F.; Mohamed, A.M. Performance Modeling of WSN with Bursty Delivery Mode. CoRR 2017, abs/1702.03907. [Google Scholar]
- Younis, M.; Akkaya, K. Strategies and Techniques for Node Placement in Wireless Sensor Networks: A Survey. Ad Hoc Netw. 2008, 6, 621–655. [Google Scholar] [CrossRef]


| Scenario 1 | |
|---|---|
| Interest | selected nodes/period |
| 115 nodes w/ | |
| 115 nodes w/ | |
| 115 nodes w/ | |
| 115 nodes w/ | |
| [11..115] nodes w/ | |
| Set | Period | Set | Period |
|---|---|---|---|
| 900 s | 0.4×60 s, | ||
| 600 s, | 0.5×60 s, | ||
| 300 s, | 0.6×60 s, | ||
| 60 s, | 0.7×60 s, | ||
| 0.1×60 s, | 0.8×60 s, | ||
| 0.2×60 s, | 0.9×60 s, | ||
| 0.3×60 s, | 1.0×60 s, |
| Scenario 2 | Scenario 3 | ||
|---|---|---|---|
| Interest | selected nodes/period | Interest | selected nodes/period |
| 1 node w/60 s/0.3 s | 3 nodes w/60 s/0.3 s | ||
| 1 node w/0.3 s/0.3 s | 3 nodes w/0.3 s/0.3 s | ||
| 4 nodes w/1 s/1 s | [4..40] nodes w/1 s/1 s | ||
| 7 nodes w/10 s/10 s | [4..40] nodes w/10 s/10 s | ||
| [1..13] nodes w/1 s/1 s | - | - | |
| Set | Period | Set | Period |
|---|---|---|---|
| 0.3 s | 0.2×{1 s}, | ||
| 60 s, | 0.3×{1 s}, | ||
| 60 s, | 0.4×{1 s}, | ||
| 1 s, | 0.5×{1 s}, | ||
| 1 s, | 0.6×{1 s}, | ||
| 1 s, | 0.7×{1 s}, | ||
| 10 s, | 0.8×{1 s}, | ||
| 10 s, | 0.9×{1 s}, | ||
| 10 s, | 1.0×{1 s}, | ||
| 10 s, | 1.1×{1 s}, | ||
| 10 s, | 1.2×{1 s}, | ||
| 10 s, | 1.3×{1 s}, | ||
| 10 s, | 1.4×{1 s} | ||
| 0.1×{1 s}, | 1.5×{1 s}, |
| Set | Period | Set | Period | Set | Period |
|---|---|---|---|---|---|
| 60 s | 0.3 s, 1.1×{1 s, 10 s}, | 0.3 s, 2.7×{1 s, 10 s}, | |||
| 60 s, | 0.3 s, 1.2×{1 s, 10 s}, | 0.3 s, 2.8×{1 s, 10 s}, | |||
| 60 s, | 0.3 s, 1.3×{1 s, 10 s}, | 0.3 s, 2.9×{1 s, 10 s}, | |||
| 0.3 s, | 0.3 s, 1.4×{1 s, 10 s}, | 0.3 s, 3.0×{1 s, 10 s}, | |||
| 0.3 s, | 0.3 s, 1.5×{1 s, 10 s}, | 0.3 s, 3.1×{1 s, 10 s}, | |||
| 0.3 s, | 0.3 s, 1.6×{1 s, 10 s}, | 0.3 s, 3.2×{1 s, 10 s}, | |||
| 0.3 s, 0.1×{1s, 10 s}, | 0.3 s, 1.7×{1 s, 10 s}, | 0.3 s, 3.3×{1s, 10 s}, | |||
| 0.3 s, 0.2×{1s, 10 s}, | 0.3 s, 1.8×{1 s, 10 s}, | 0.3 s, 3.4×{1s, 10 s}, | |||
| 0.3 s, 0.3×{1s, 10 s}, | 0.3 s, 1.9×{1 s, 10 s}, | 0.3 s, 3.5×{1s, 10 s}, | |||
| 0.3 s, 0.4×{1s, 10 s}, | 0.3 s, 2.0×{1 s, 10 s}, | 0.3 s, 3.6×{1s, 10 s}, | |||
| 0.3 s, 0.5×{1s, 10 s}, | 0.3 s, 2.1×{1 s, 10 s}, | 0.3 s, 3.7×{1s, 10 s}, | |||
| 0.3 s, 0.6×{1s, 10 s}, | 0.3 s, 2.2×{1 s, 10 s}, | 0.3 s, 3.8×{1s, 10 s}, | |||
| 0.3 s, 0.7×{1s, 10 s}, | 0.3 s, 2.3×{1 s, 10 s}, | 0.3 s, 3.9×{1s, 10 s}, | |||
| 0.3 s, 0.8×{1s, 10 s}, | 0.3 s, 2.4×{1 s, 10 s}, | 0.3 s, 4.0×{1s, 10 s}, | |||
| 0.3 s, 0.9×{1s, 10 s}, | 0.3 s, 2.5×{1 s, 10 s}, | - | - | ||
| 0.3 s, 1.0×{1s, 10 s}, | 0.3 s, 2.6×{1 s, 10 s}, | - | - |
© 2020 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Huegel Richa, C.; M. de Lucena, M.; Passig Horstmann, L.; Conradi Hoffmann, J.L.; Fröhlich, A.A. Modeling Time Requirements of CPS in Wireless Networks. Sensors 2020, 20, 1818. https://doi.org/10.3390/s20071818
Huegel Richa C, M. de Lucena M, Passig Horstmann L, Conradi Hoffmann JL, Fröhlich AA. Modeling Time Requirements of CPS in Wireless Networks. Sensors. 2020; 20(7):1818. https://doi.org/10.3390/s20071818
Chicago/Turabian StyleHuegel Richa, César, Mateus M. de Lucena, Leonardo Passig Horstmann, José Luis Conradi Hoffmann, and Antônio Augusto Fröhlich. 2020. "Modeling Time Requirements of CPS in Wireless Networks" Sensors 20, no. 7: 1818. https://doi.org/10.3390/s20071818
APA StyleHuegel Richa, C., M. de Lucena, M., Passig Horstmann, L., Conradi Hoffmann, J. L., & Fröhlich, A. A. (2020). Modeling Time Requirements of CPS in Wireless Networks. Sensors, 20(7), 1818. https://doi.org/10.3390/s20071818





