Enhancements and Challenges in CoAP—A Survey
Abstract
1. Introduction
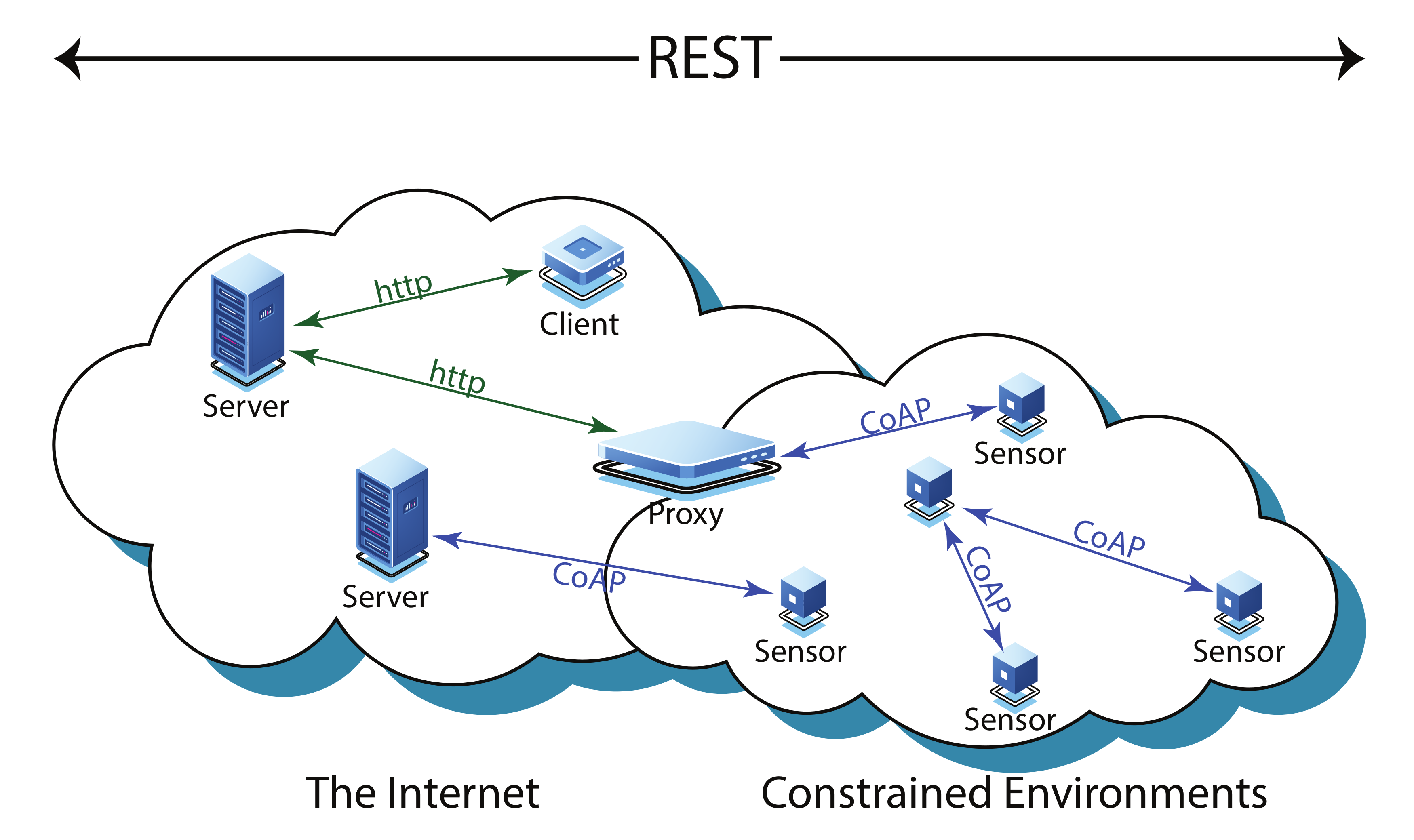
2. Constrained Application Protocol (CoAP)
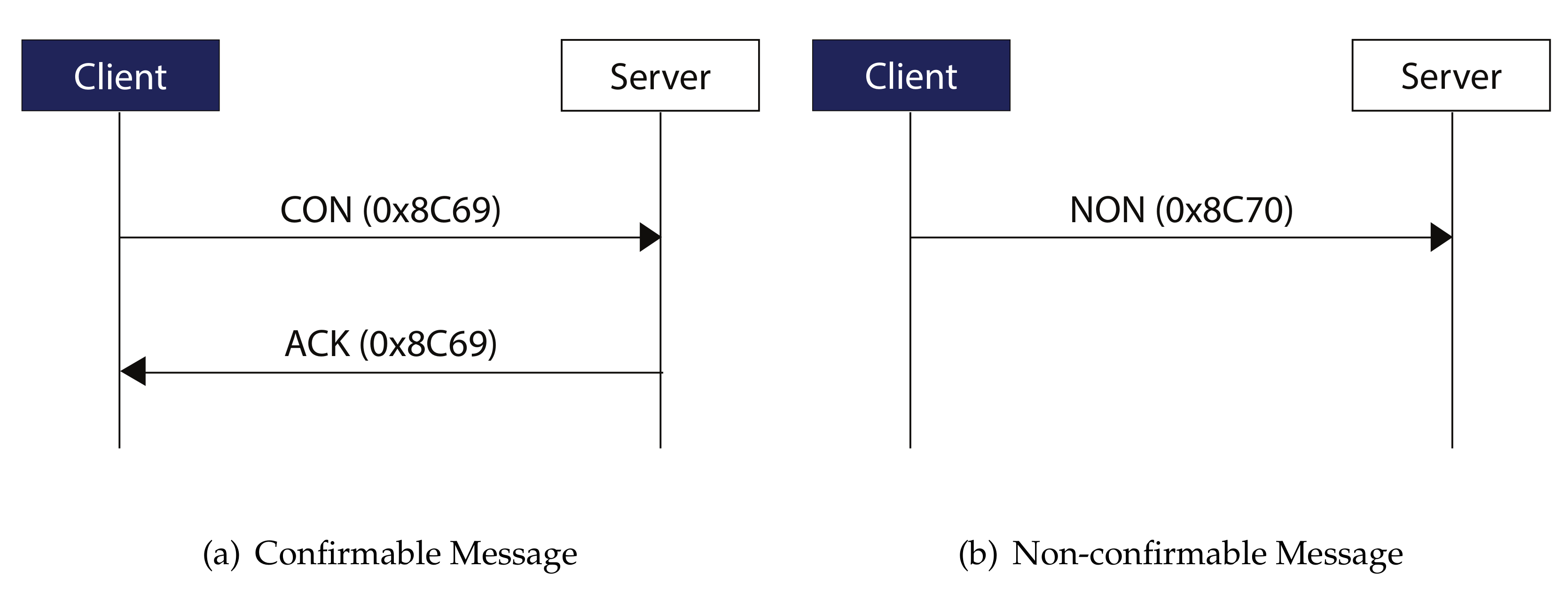
- Confirmable (CON)
- Non-confirmable (NON)
- Acknowledgement (ACK)
- Reset
3. Applications of CoAP
3.1. Interoperability and Integration
3.1.1. Interoperability with HTTP
3.1.2. CoAP Interoperability with MQTT for Healthcare
3.1.3. Interoperability with Healthcare Platform
3.1.4. Integration of Healthcare Standards
3.1.5. Integration with OSGP
3.2. Security
3.2.1. Authentication and Authorization
3.2.2. Authentication and Access Control
3.3. Streaming Services
3.3.1. Media Streaming
3.3.2. Video Streaming Services
3.4. Cloud Computing Services
CoAP Integration with Cloud
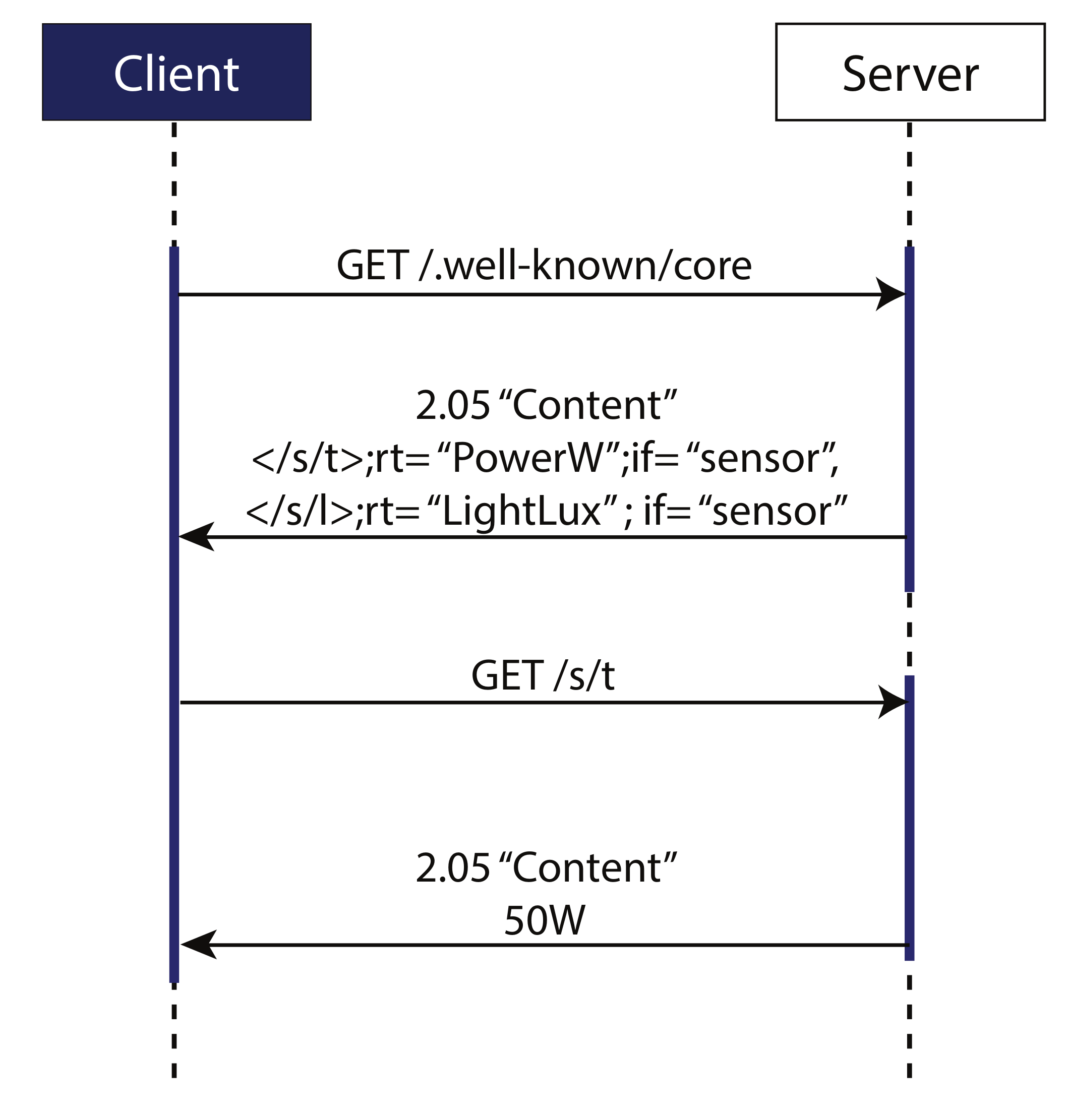
3.5. Resource Observation and Discovery
3.5.1. Resource Observation
3.5.2. Resource Discovery
3.6. Real-Time Remote Monitoring
Remote Monitoring and Real-Time Display in Healthcare
4. Enhancements in CoAP
4.1. Congestion Control Mechanisms in CoAP
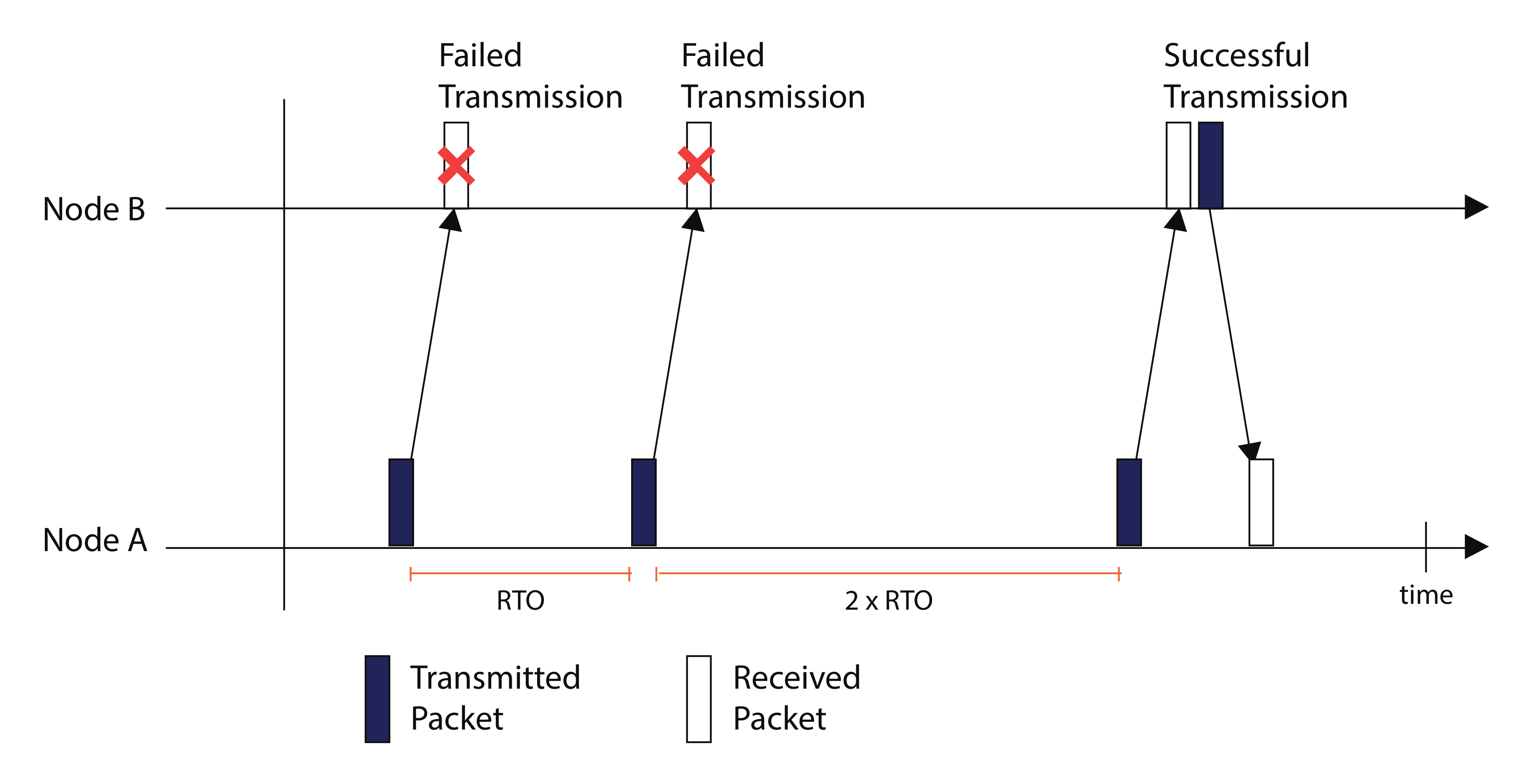
4.1.1. Default CoAP
4.1.2. CoCo-RED
- Determination and calculation of RTO timer
- Management using Revised Random Early Detection (RevRED) algorithm for avoiding congestion
- Fibonacci Pre-Increment Backoff (FPB) algorithm for implementing backoff timer
- If AvgQ < Min threshold, arriving packet is placed in queue
- If Min threshold < AvgQ < Max threshold, arriving packet is dropped based on the dropping probability formula presented by the proposed method
- If AvgQ > Max threshold, arriving packet is dropped based on the exponentially dropping probability formula presented by the proposed method
4.1.3. CoCoA
4.1.4. Four-State Estimator Scheme
4.1.5. Adaptive Congestion Control
4.1.6. CoCoA+
4.1.7. Improved Adaptive Congestion Control
4.1.8. CACC
4.1.9. FASOR
4.1.10. pCoCoA
- A method for linking requests to responses precisely even in case of retransmissions
- Several modifications to the estimation algorithm of RTO
4.1.11. CoCoA++
4.1.12. Genetic CoCoA++
4.1.13. Message Loss Feedback based
4.1.14. Content Freshness Based
4.1.15. BDP-CoAP
4.1.16. CoAP-R
4.2. Enhanced CoAP for Interoperability
4.3. Enhancement in CoAP Security
4.3.1. Enhanced DTLS Protocol
4.3.2. Enhanced Security with Hashing
4.4. Enhanced CoAP for Streaming Services
5. Qualitative and Quantitative Analysis of Congestion Control Schemes
5.1. Qualitative Analysis
5.2. Quantitative Analysis
6. Open Challenges
6.1. Energy Efficiency of CoAP-Enabled Nodes
6.2. Interoperability
6.3. Congestion Control
6.4. Security of CoAP
7. Conclusions
Author Contributions
Funding
Acknowledgments
Conflicts of Interest
Abbreviations
| IETF | Internet of Engineering Task |
| CoAP | Constrained Application Protocol |
| IoT | Internet of Things |
| IoUT | Internet of Underwater Things |
| IoE | Internet of Everything |
| WSN | Wireless Sensor Networks |
| REST | Representational State Transfer |
| UDP | User Datagram Protocol |
| TCP | Transmission Control Protocol |
| BEB | Binary Exponential Backoff |
| CoCoA | Congestion Control/Advance |
| RTT | Round Trip Time |
| CON | Confirmable |
| NON | Non-confirmable |
| RTO | Retransmission Timeout |
| DTLS | Datagram Transport Layer Security |
| MQTT | Message Queuing Telemetry Transport |
| OSGP | Open Smart Grid Protocol |
| SG | Smart Grids |
| COIIoT | CoAP and OSGP Integration for the Internet of Things |
| PED | Pending Event Descriptor |
| AAA | Authentication, Authorization and Accounting |
| EAP | Extensible Authentication Protocol |
| LP-WAN | Low-Power Wide Area Networks |
| LO-CoAP-EAP | Low-Overhead CoAP-EAP |
| DASCo | Dynamic Streaming over CoAP |
| DASH | Dynamic Streaming over HTTP |
| JSON | JavaScript Object Notation |
| RD | Resource Directory |
| PRD | Proactive RD Discovery |
| FDR | Fully distributed push-pull Resource Discovery |
| CoCo-RED | Congestion Control Random Early Detection |
| RevRED | Revised Random Early Detection |
| FPB | Fibonacci Pre-Increment Backoff |
| BMT | Buffer Management Technique |
| VBF | Variable Backoff Factor |
| CACC | Context-Aware Congestion Control |
| RC | Retransmission Count |
| FASOR | Fast-Slow RTO |
| TC | Transmission Counter |
| CDG | CAIA Delay Gradient |
| PBF | Probabilistic Backoff Factor |
| GA | Genetic Algorithm |
| CR | Congestion Ratio |
| WRTT | Weak RTT |
| SRTT | Strong RTT |
| BBR | Bottleneck Bandwidth and Round-trip propagation time |
| BW | Bandwidth |
| HDAA | HTTP Digest Access Authentication |
| AESCCM | Advanced Encryption Standard-Counter with Cipher Block Chaining-Message Authentication Code |
| ECDSA | Elliptic Curve Digital Signature Algorithm |
| MAC | Message Authentication Code |
| AES | Advanced Encryption Standard |
| RC6 | Rivest Cipher 6 |
| LEA | Lightweight Encryption Algorithm |
| GCM | Galois/counter mode |
| DRD | Distributed Resource Discovery |
| CRD | Centralized Resource Directory |
| OCSP | Online Certification Status Protocol |
| PFR | Packet Failure Rate |
| QoN | Quality of Network |
References
- Lee, J.J.; Chung, S.M.; Lee, B.; Kim, K.T.; Youn, H.Y. Round Trip Time Based Adaptive Congestion Control with CoAP for Sensor Network. In Proceedings of the 2016 International Conference on Distributed Computing in Sensor Systems (DCOSS), Washington, DC, USA, 26–28 May 2016; pp. 113–115. [Google Scholar] [CrossRef]
- Shelby, Z.; Hartke, K.; Bormann, C. The constrained application protocol (CoAP). 2014. Available online: https://iottestware.readthedocs.io/en/master/coap_rfc.html (accessed on 9 November 2020). [CrossRef]
- Pramanik, A.; Luhach, A.K.; Batra, I.; Singh, U. A systematic survey on congestion mechanisms of CoAP based Internet of Things. In Proceedings of the International Conference on Advanced Informatics for Computing Research, Jalandhar, India, 17–18 March 2017; pp. 306–317. [Google Scholar] [CrossRef]
- Meng, H.; HongBing, H.; WeiPing, L. An Adaptive Congestion Control Algorithm with CoAP for the Internet of Thing. Int. J. Comput. Tech. 2017, 4, 46–51. [Google Scholar]
- Raitahila, I. Congestion Control Algorithms for the Constrained Application Protocol (CoAP). Master’s Thesis, University of Helsinki, Helsinki, Finland, 2019. [Google Scholar]
- Betzler, A.; Gomez, C.; Demirkol, I.; Paradells, J. CoAP congestion control for the internet of things. IEEE Commun. Mag. 2016, 54, 154–160. [Google Scholar] [CrossRef]
- Betzler, A.; Gomez, C.; Demirkol, I.; Paradells, J. CoCoA+: An advanced congestion control mechanism for CoAP. Ad Hoc Netw. 2015, 33, 126–139. [Google Scholar] [CrossRef]
- Bolettieri, S.; Tanganelli, G.; Vallati, C.; Mingozzi, E. pCoCoA: A precise congestion control algorithm for CoAP. Ad Hoc Netw. 2018, 80, 116–129. [Google Scholar] [CrossRef]
- Mi, Z.; Wei, G. A CoAP-Based Smartphone Proxy for Healthcare with IoT Technologies. In Proceedings of the 2018 IEEE 9th International Conference on Software Engineering and Service Science (ICSESS), Beijing, China, 23–25 November 2018; pp. 271–278. [Google Scholar] [CrossRef]
- Oryema, B.; Kim, H.; Li, W.; Park, J.T. Design and implementation of an interoperable messaging system for IoT healthcare services. In Proceedings of the 2017 14th IEEE Annual Consumer Communications Networking Conference (CCNC), Las Vegas, NV, USA, 8–11 January 2017; pp. 45–52. [Google Scholar] [CrossRef]
- Ge, S.; Chun, S.; Kim, H.; Park, J. Design and implementation of interoperable IoT healthcare system based on international standards. In Proceedings of the 2016 13th IEEE Annual Consumer Communications Networking Conference (CCNC), Las Vegas, NV, USA, 9–12 January 2016; pp. 119–124. [Google Scholar] [CrossRef]
- Li, W.; Jung, C.; Park, J. IoT Healthcare Communication System for IEEE 11073 PHD and IHE PCD-01 Integration Using CoAP. KSII Trans. Internet Inf. Syst. 2018, 12. [Google Scholar] [CrossRef]
- Viel, F.; Augusto-Silva, L.; Leithardt, V.R.Q.; de Paz-Santana, J.F.; Celeste-Ghizoni-Teive, R.; Albenes-Zeferino, C. An Efficient Interface for the Integration of IoT Devices with Smart Grids. Sensors 2020, 20, 2849. [Google Scholar] [CrossRef]
- Garcia-Carrillo, D.; Marin-Lopez, R.; Kandasamy, A.; Pelov, A. A CoAP-based network access authentication service for low-power wide area networks: LO-CoAP-EAP. Sensors 2017, 17, 2646. [Google Scholar] [CrossRef]
- Tamboli, M.B.; Dambawade, D. Secure and efficient CoAP based authentication and access control for Internet of Things (IoT). In Proceedings of the 2016 IEEE International Conference on Recent Trends in Electronics, Information Communication Technology (RTEICT), Bangalore, India, 20–21 May 2016; pp. 1245–1250. [Google Scholar] [CrossRef]
- Krawiec, P.; Sosnowski, M.; Batalla, J.M.; Mavromoustakis, C.X.; Mastorakis, G. DASCo: Dynamic adaptive streaming over CoAP. Multimed. Tools Appl. 2018, 77, 4641–4660. [Google Scholar] [CrossRef]
- Rahman, W.U.; Choi, Y.; Chung, K. Quality Adaptation Algorithm for Streaming over CoAP. In Proceedings of the 2018 International Conference on Information and Communication Technology Convergence (ICTC), Jeju Island, Korea, 17–19 October 2018; pp. 1015–1018. [Google Scholar] [CrossRef]
- Scott, T.L.; Eleyan, A. CoAP based IoT data transfer from a Raspberry Pi to Cloud. In Proceedings of the 2019 International Symposium on Networks, Computers and Communications (ISNCC), Istanbul, Turkey, 18–20 June 2019; pp. 1–6. [Google Scholar] [CrossRef]
- Jan, S.R.; Khan, F.; Ullah, F.; Azim, N.; Tahir, M. Using CoAP protocol for resource observation in IoT. Int. J. Emerg. Technol. Comput. Sci. Electron. 2016, 21, 385–388. [Google Scholar]
- Djamaa, B.; Yachir, A.; Richardson, M. Hybrid CoAP-based resource discovery for the Internet of Things. J. Ambient Intell. Humaniz. Comput. 2017, 8, 357–372. [Google Scholar] [CrossRef]
- Ugrenovic, D.; Gardasevic, G. CoAP protocol for Web-based monitoring in IoT healthcare applications. In Proceedings of the 2015 23rd Telecommunications Forum Telfor (TELFOR), Belgrade, Serbia, 24–26 November 2015; pp. 79–82. [Google Scholar] [CrossRef]
- Suwannapong, C.; Khunboa, C. Congestion Control in CoAP Observe Group Communication. Sensors 2019, 19, 3433. [Google Scholar] [CrossRef]
- Bhalerao, R.; Subramanian, S.S.; Pasquale, J. An analysis and improvement of congestion control in the CoAP Internet-of-Things protocol. In Proceedings of the 2016 13th IEEE Annual Consumer Communications Networking Conference (CCNC), Las Vegas, NV, USA, 9–12 January 2016; pp. 889–894. [Google Scholar] [CrossRef]
- Ouakasse, F.; Rakrak, S. An Improved Adaptive CoAP Congestion Control Algorithm. Int. J. Online Biomed. Eng. 2019, 15, 96–109. [Google Scholar] [CrossRef]
- Akpakwu, G.A.; Hancke, G.P.; Abu-Mahfouz, A.M. CACC: Context-aware congestion control approach for lightweight CoAP/UDP-based Internet of Things traffic. Trans. Emerg. Telecommun. Technol. 2020, 31, e3822. [Google Scholar] [CrossRef]
- Jarvinen, I.; Raitahila, I.; Cao, Z.; Kojo, M. FASOR Retransmission Timeout and Congestion Control Mechanism for CoAP. In Proceedings of the 2018 IEEE Global Communications Conference (GLOBECOM), Abu Dhabi, UAE, 9–13 December 2018; pp. 1–7. [Google Scholar] [CrossRef]
- Rathod, V.; Jeppu, N.; Sastry, S.; Singala, S.; Tahiliani, M.P. CoCoA++: Delay gradient based congestion control for Internet of Things. Future Gener. Comput. Syst. 2019, 100, 1053–1072. [Google Scholar] [CrossRef]
- Yadav, R.K.; Singh, N.; Piyush, P. Genetic CoCoA++: Genetic Algorithm based Congestion Control in CoAP. In Proceedings of the 2020 4th International Conference on Intelligent Computing and Control Systems (ICICCS), Madurai, India, 13–15 May 2020; pp. 808–813. [Google Scholar] [CrossRef]
- Kim, M.; Lee, S.; Khan, M.T.R.; Seo, J.; Bae, Y.; Jeong, Y.; Kim, D. A new CoAP congestion control scheme using message loss feedback for IoUT. In Proceedings of the 34th ACM/SIGAPP Symposium on Applied Computing, Limassol, Cyprus, 8–12 April 2019; pp. 2385–2390. [Google Scholar] [CrossRef]
- Seo, J.; Lee, S.; Khan, M.T.R.; Kim, D. A New CoAP Congestion Control Scheme Considering Strong and Weak RTT for IoUT. In Proceedings of the 35th Annual ACM Symposium on Applied Computing, Brno, Czech Republic, 30 March–3 April 2020; Association for Computing Machinery: New York, NY, USA, 2020; pp. 2158–2162. [Google Scholar] [CrossRef]
- Ancillotti, E.; Bruno, R. BDP-CoAP: Leveraging Bandwidth-Delay Product for Congestion Control in CoAP. In Proceedings of the 2019 IEEE 5th World Forum on Internet of Things (WF-IoT), Limerick, Ireland, 5–18 April 2019; pp. 656–661. [Google Scholar] [CrossRef]
- Ancillotti, E.; Bruno, R.; Vallati, C.; Mingozzi, E. Design and Evaluation of a Rate-Based Congestion Control Mechanism in CoAP for IoT Applications. In Proceedings of the 2018 IEEE 19th International Symposium on “A World of Wireless, Mobile and Multimedia Networks” (WoWMoM), Chania, Greece, 12–15 June 2018; pp. 14–15. [Google Scholar] [CrossRef]
- Shelby, Z.; Hartke, K.; Bormann, C. Observing resources in CoAP. Available online: https://tools.ietf.org/html/draft-ietf-core-observe-04 (accessed on 9 November 2020).
- Jaffey, T. MQTT and CoAP, IoT Protocols. Available online: https://www.eclipse.org/community/eclipse_newsletter/2014/february/article2.php (accessed on 9 November 2020).
- Bormann, C.; Shelby, Z. Block-Wise Transfers in the Constrained Application Protocol (CoAP). Available online: https://www.hjp.at/doc/rfc/rfc7959.html (accessed on 9 November 2020).
- Standard for Health Informatics—Personal Health Device Communication—Application profile—Optimized Exchange Protocol; Standard; IEEE: New York, NY, USA, 2008.
- Djamaa, B.; Yachir, A. A Proactive Trickle-Based Mechanism for Discovering CoRE Resource Directories. Procedia Comput. Sci. 2016, 83, 115–122. [Google Scholar] [CrossRef][Green Version]
- Djamaa, B.; Richardson, M.; Aouf, N.; Walters, B. Towards efficient distributed service discovery in low-power and lossy networks. Wirel. Netw. 2014, 20, 2437–2453. [Google Scholar] [CrossRef]
- Ancillotti, E.; Bruno, R. Comparison of CoAP and CoCoA+ congestion control mechanisms for different IoT application scenarios. In Proceedings of the 2017 IEEE Symposium on Computers and Communications (ISCC), Heraklion, Greece, 3–6 July 2017; pp. 1186–1192. [Google Scholar] [CrossRef]
- Hayes, D.A.; Armitage, G. Revisiting TCP congestion control using delay gradients. In Proceedings of the International Conference on Research in Networking, Espoo, Finland, 14–17 June 2011; Springer: Berlin/Heidelberg, Germany, 2011; pp. 328–341. [Google Scholar] [CrossRef]
- Buschsieweke, M.; Güneş, M. Authentication for the web of things: Secure end-to-end authentication between CoAP and HTTP. In Proceedings of the 2017 IEEE 28th Annual International Symposium on Personal, Indoor and Mobile Radio Communications (PIMRC), Montreal, QC, Canada, 8–13 October 2017; pp. 1–5. [Google Scholar] [CrossRef]
- Kumar, P.M.; Gandhi, U.D. Enhanced DTLS with CoAP-based authentication scheme for the internet of things in healthcare application. J. Supercomput. 2020, 1–21. [Google Scholar] [CrossRef]
- Halabi, D.; Hamdan, S.; Almajali, S. Enhance the security in smart home applications based on IOT-CoAP protocol. In Proceedings of the 2018 Sixth International Conference on Digital Information, Networking, and Wireless Communications (DINWC), Beirut, Lebanon, 25–27 April 2018; pp. 81–85. [Google Scholar] [CrossRef]
- Rogaway, P.; Shrimpton, T. Cryptographic hash-function basics: Definitions, implications, and separations for preimage resistance, second-preimage resistance, and collision resistance. In International Workshop on Fast Software Encryption; Springer: Berlin/Heidelberg, Germany, 2004; pp. 371–388. [Google Scholar] [CrossRef]
- Bellare, M.; Canetti, R.; Krawczyk, H. Keying hash functions for message authentication. In Proceedings of the Annual International Cryptology Conference, Barbara, CA, USA, 18–22 August 1996; Springer: Berlin/Heidelberg, Germany, 1996; pp. 1–15. [Google Scholar] [CrossRef]
- Saraiva, D.A.; Leithardt, V.R.Q.; de Paula, D.; Sales-Mendes, A.; González, G.V.; Crocker, P. Prisec: Comparison of symmetric key algorithms for iot devices. Sensors 2019, 19, 4312. [Google Scholar] [CrossRef]
- Choi, G.; Kim, D.; Yeom, I. Efficient streaming over CoAP. In Proceedings of the 2016 International Conference on Information Networking (ICOIN), Kota Kinabalu, Malaysia, 13–15 January 2016; pp. 476–478. [Google Scholar] [CrossRef]
- Yassein, M.B.; Hmeidi, I.; Meqdadi, O.; Alghazo, F.; Odat, B.; AlZoubi, O.; Smairat, A. Challenges and Techniques of Constrained Application Protocol (CoAP) for Efficient Energy Consumption. In Proceedings of the 2020 11th International Conference on Information and Communication Systems (ICICS), Irbid, Jordan, 7–9 April 2020; pp. 373–377. [Google Scholar] [CrossRef]
- Bormann, C.; Castellani, A.P.; Shelby, Z. CoAP: An Application Protocol for Billions of Tiny Internet Nodes. IEEE Internet Comput. 2012, 16, 62–67. [Google Scholar] [CrossRef]
- Chen, N.; Viho, C.; Baire, A.; Huang, X.; Zha, J. Ensuring interoperability for the Internet of Things: Experience with CoAP protocol testing. Automatika 2013, 54, 448–458. [Google Scholar] [CrossRef]
- Rahman, R.A.; Shah, B. Security analysis of IoT protocols: A focus in CoAP. In Proceedings of the 2016 3rd MEC International Conference on Big Data and Smart City (ICBDSC), Muscat, Oman, 15–16 March 2016; pp. 1–7. [Google Scholar] [CrossRef]
- Capossele, A.; Cervo, V.; de Cicco, G.; Petrioli, C. Security as a CoAP resource: An optimized DTLS implementation for the IoT. In Proceedings of the 2015 IEEE international conference on communications (ICC), London, UK, 8–12 June 2015; IEEE: New York, NY, USA, 2015; pp. 549–554. [Google Scholar] [CrossRef]
- Palattella, M.R.; Accettura, N.; Vilajosana, X.; Watteyne, T.; Grieco, L.A.; Boggia, G.; Dohler, M. Standardized Protocol Stack for the Internet of (Important) Things. IEEE Commun. Surv. Tutor. 2013, 15, 1389–1406. [Google Scholar] [CrossRef]
- Hartke, K. Practical Issues with Datagram Transport Layer Security in Constrained Environments. Draft-Hartke-Dice-Practical-Issues-01. Available online: https://tools.ietf.org/html/draft-hartke-dice-practical-issues-01 (accessed on 9 November 2020).
- Kohlweiss, M.; Maurer, U.; Onete, C.; Tackmann, B.; Venturi, D. (De-) constructing TLS 1.3. In Proceedings of the International Conference on Cryptology in India, Jaipur, India, 3–7 October 2015; Springer: Berlin/Heidelberg, Germany, 2015; pp. 85–102. [Google Scholar] [CrossRef]
- Krawczyk, H.; Wee, H. The OPTLS Protocol and TLS 1.3. In Proceedings of the 2016 IEEE European Symposium on Security and Privacy (EuroS P), Saarbrucken, Germany, 21–24 March 2016; pp. 81–96. [Google Scholar] [CrossRef]
- Nastase, L. Security in the Internet of Things: A Survey on Application Layer Protocols. In Proceedings of the 2017 21st International Conference on Control Systems and Computer Science (CSCS), Bucharest, Romania, 29–31 May 2017; pp. 659–666. [Google Scholar] [CrossRef]
- Myers, M.; Ankney, R.; Malpani, A.; Galperin, S.; Adams, C.X. 509 Internet Public Key Infrastructure Online Certificate Status Protocol-OCSP. Available online: https://dl.acm.org/doi/pdf/10.17487/RFC2560 (accessed on 9 November 2020).
- Eastlake, D. Transport Layer Security (TLS) Extensions: Extension Definitions. Available online: https://www.hjp.at/doc/rfc/rfc6066.html (accessed on 9 November 2020).
- Granjal, J.; Monteiro, E.; Sá-Silva, J. Security for the Internet of Things: A Survey of Existing Protocols and Open Research Issues. IEEE Commun. Surv. Tutor. 2015, 17, 1294–1312. [Google Scholar] [CrossRef]
- Raza, S.; Trabalza, D.; Voigt, T. 6LoWPAN Compressed DTLS for CoAP. In Proceedings of the 2012 IEEE 8th International Conference on Distributed Computing in Sensor Systems, Hangzhou, China, 16–18 May 2012; pp. 287–289. [Google Scholar] [CrossRef]
- Butun, I.; Morgera, S.D.; Sankar, R. A Survey of Intrusion Detection Systems in Wireless Sensor Networks. IEEE Commun. Surv. Tutor. 2014, 16, 266–282. [Google Scholar] [CrossRef]
- Young, M.; Boutaba, R. Overcoming Adversaries in Sensor Networks: A Survey of Theoretical Models and Algorithmic Approaches for Tolerating Malicious Interference. IEEE Commun. Surv. Tutor. 2011, 13, 617–641. [Google Scholar] [CrossRef]
- Abduvaliyev, A.; Pathan, A.K.; Zhou, J.; Roman, R.; Wong, W. On the Vital Areas of Intrusion Detection Systems in Wireless Sensor Networks. IEEE Commun. Surv. Tutor. 2013, 15, 1223–1237. [Google Scholar] [CrossRef]

| Paper | Role of CoAP | Application |
|---|---|---|
| Z. Mi et al. [9] | Direct compatibility of medical sensors with internet + interaction of sensors with other nodes using RESTful communication | Interoperability |
| B. Oryema et al. [10] | Implementation of messaging system with MQTT model using CoAP | Interoperability |
| S.-y. Ge at al. [11] | Design and implementation of healthcare platform with IEEEE 11073 PHD | Interoperability |
| W. Li et al. [12] | Integration of two healthcare standards ISO/IEEE 11073 and IHE PCD-01 for communicating between medical IoT devices | Integration |
| Viel et al. [13] | Integration of CoAP with Open Smart Grid Protocol (OSGP) for information exchange between devices in smart grids (SG) | Integration |
| D. Garcia-Carrillo et al. [14] | Integration between AAA infrastructures and EAP | Authentication and Authorization |
| M. B. Tamboli et al. [15] | To provide communication with packets having low overhead in CoAP-based authentication and access control framework for IoT | Authentication and Access Control |
| P. Krawiec et al. [16] | For delivering the media segments to consumers in implementing dynamic streaming over CoAP | Streaming Services |
| W. ur Rahman et al. [17] | To perform adaptive streaming for constrained wireless environments | Video Streaming |
| T. L. Scott et al. [18] | Transfer of data from IoT nodes to cloud | Cloud Computing Services |
| S. R. Jan et al. [19] | Observing resources (temperature values) in IoT environment and WSNs | Resource Observation |
| B. Djama et al. [20] | For advertising and demanding of resource directories using CoAP REST methods | Resource Discovery |
| D. Ugrenovic et al. [21] | Implementation of a remote healthcare monitoring system using CoAP client/server model | Real-time Remote Monitoring |
| Scheme Name | Adopted Mechanism | Comm. Type | Burst Traffic Support | Complexity Level | Issues Countered | Shortcomings |
|---|---|---|---|---|---|---|
| Default CoAP [2] | Binary Exponential Backoff (BEB) | Reliable | No | Low | Basic Congestion Control | Idle delays between retransmissions, does not consider dynamic network |
| CoCo-RED [22] | Buffer management using Revised Random Early Detection | Reliable | Yes | Low | Reduced packet loss and response time of network | Fixed backoff values, does not consider dynamic network conditions |
| CoCoA [6] | RTT measurements + Variable Backoff | Reliable | No | Low | Basic congestion control issues + RTO aging | Ambiguity in weak RTT estimator |
| 4-state Estimator [23] | State0based Variable Backoff | Reliable | No | Medium | Idle delays between successive (re)transmissions in CoCoA | Not included |
| Adaptive Congestion Control [4] | Transmission count-based | Reliable | No | Low | Ambiguity in weak estimator values | More bandwidth, and energy is consumed in solving ambiguity of weak estimator especially for wireless communication |
| CoCoA+ [7] | Modifications in CoCoA RTO calculations | Reliable | No | High | Ambiguity in weak estimator values of CoCoA | Inaccurate measurement of retransmitted RTT in burst traffic |
| Improved Adaptive Congestion Control [24] | Packet loss ratio-based RTO calculations | Reliable | Yes | Low | Congestion Control in burst traffic, elimination of RTO aging mechanism | Additional overhead in calculating RTO in each transmission, poor adaptability in RTO |
| CACC [25] | RTT Estimators + Retransmission Count based | Reliable | No | High | Differentiating the scenario of packet loss due bit error rate and congestion | Poor RTO aging mechanism, vanishing of RTTVAR variable for similar consecutive RTT samples, lack of aging mechanism for weak RTO causing steep RTO increment |
| FASOR [26] | RTO Estimators + State-based backoff logic | Reliable | No | Medium | Bufferbloat condition, high link error rates | No special logic for senders remaining idle |
| pCoCoA [8] | Transmission Count + Modifications in RTO Estimation + Estimation of Max mean deviation of RTO | Reliable | Yes | High | Spurious retransmissions, vanishing RTTVAR due to similar RTT sampling | Not included |
| CoCoA++ [27] | Delay Gradient based calculation + probabilistic backoff | Reliable | No | High | Shortcomings of default CoAP, CoCoA, CoCoA+ | Sender runs out of retransmissions due to quick retransmissions caused by increased packet sending rate |
| Genetic CoCoA++ [28] | CoCoA++-based + Genetic algorithm | Reliable | No | High | Issues of CoCoA+ including: (i) Accurate retransmission RTO measurement (ii) Large changes in RTO estimates | RTT observation time is limited, burst traffic is not considered |
| Message Loss Feedback-based [29] | Message Loss Feedback-based | Reliable/Unreliable | No | Low | Congestion detection in default CoAP | Loss rate of transmission cannot be found if number of CON and NON messages are equal |
| Content Freshness based [30] | Congestion window size control | Reliable/Unreliable | No | Medium | Congestion Control in default CoAP | Loss rate of transmission cannot be found if number of CON and NON messages are equals |
| BDP-CoAP [31] | Estimation of bottleneck bandwidth | Reliable | Yes | Medium | Issues of lossy links + short term unfairness of channel | Not included |
| CoAP-R [32] | Rate-based | Reliable | Yes | Medium | Performance issues of CoCoA in light and burst traffic + unfair bandwidth allocation | Scenario of inactive/malfunctioned node is not considered |
| Scheme Name | Performance Metrics | Topology | Traffic Scenarios | Avg Percentage Improvement |
|---|---|---|---|---|
| CoCo-RED [22] | Settling time, response time, packet loss | Chain, grid, cross, dumbbell, random | Continuous, burst | Settling time: 2%, Response time: 8%, Packet loss: 21% |
| CoCoA [6] | Throughput, settling time | Not mentioned | Continuous, burst | Throughput: 19Settling time: 26.67% |
| 4-state Estimator [23] | Throughput, goodput | Not mentioned | Continuous | Throughput: 19% Goodput: 40% |
| Adaptive Congestion Control [4] | Throughput | Not mentioned | Continuous | Throughput: 56% |
| CoCoA+ [7] | packet delivery ratio, end-to-end delay, settling time | Chain, dumbbell, grid | Periodic, burst, mixed | Packet delivery ratio: 4.4% End-to-end delay: 18.5% Settling time: 27.5% |
| Improved Adaptive Congestion Control [24] | number of dropped packets, number of successful transactions | Point to multipoint | Constant | Dropped packets: 40.8% Successful transactions: 7.5% |
| CACC [25] | Throughput, end-to-end delay, energy consumption | Grid, chain, dumbbell | Constant | Throughput: 21.8% End-to-end delay: 47.8% Energy consumption: 41% |
| CoCoA++ [27] | Number of packets transmitted, average packet sending rate | Grid, flower, dumbbell, chain | Periodic | Number of packets transmitted: 15% Avg packet sending rate: 5.2% |
| Genetic CoCoA++ [28] | Packet failure rate | Grid, dumbbell | Continuous | Packet failure rate: 32.14% |
| Message Loss Feedback-based [29] | Average packet reception ratio, throughput | Random | Constant | Packet reception ratio: 3.215% Throughput: 18.54% |
| Content Freshness based [30] | Throughput, number of message transmissions | Random | Constant | Throughput: 23.46% Number of transmissions: 31.95% |
Publisher’s Note: MDPI stays neutral with regard to jurisdictional claims in published maps and institutional affiliations. |
© 2020 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Tariq, M.A.; Khan, M.; Raza Khan, M.T.; Kim, D. Enhancements and Challenges in CoAP—A Survey. Sensors 2020, 20, 6391. https://doi.org/10.3390/s20216391
Tariq MA, Khan M, Raza Khan MT, Kim D. Enhancements and Challenges in CoAP—A Survey. Sensors. 2020; 20(21):6391. https://doi.org/10.3390/s20216391
Chicago/Turabian StyleTariq, Muhammad Ashar, Murad Khan, Muhammad Toaha Raza Khan, and Dongkyun Kim. 2020. "Enhancements and Challenges in CoAP—A Survey" Sensors 20, no. 21: 6391. https://doi.org/10.3390/s20216391
APA StyleTariq, M. A., Khan, M., Raza Khan, M. T., & Kim, D. (2020). Enhancements and Challenges in CoAP—A Survey. Sensors, 20(21), 6391. https://doi.org/10.3390/s20216391








