Physical Unclonable Function and Hashing Are All You Need to Mutually Authenticate IoT Devices
Abstract
1. Introduction
- A novel two-factor mutual authentication approach for IoT devices in which a hashing algorithm is utilized for the IoT device and the server to authenticate each other,
- Use of two PUFs in the IoT device for two-factor authentication for stronger security against cyberattacks,
- Low power consumption during the authentication, which is very appealing to resource-constrained applications of the IoT.
2. Authentication Techniques in IoT Devices
2.1. Authentication via Encryption/Decryption
2.2. Authentication via Localization and Device Environmental Data
2.3. Authentication via Physical Unclonable Functions (PUFs)
2.3.1. Weak PUFs
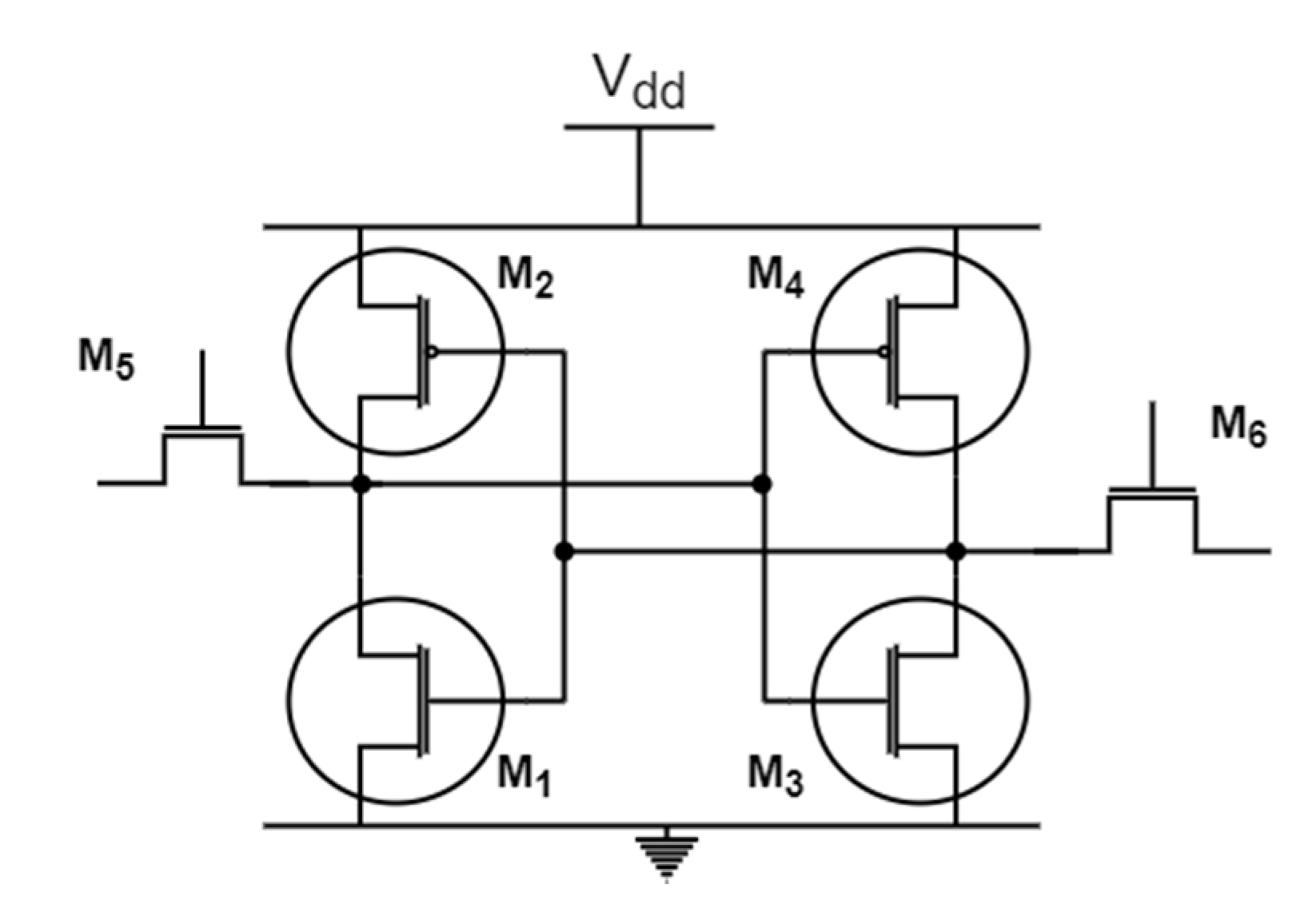
- SRAM PUF
- Ring Oscillator (RO) PUF
2.3.2. Strong PUFs
- Arbiter PUF
- Optical PUF
3. Literature Review
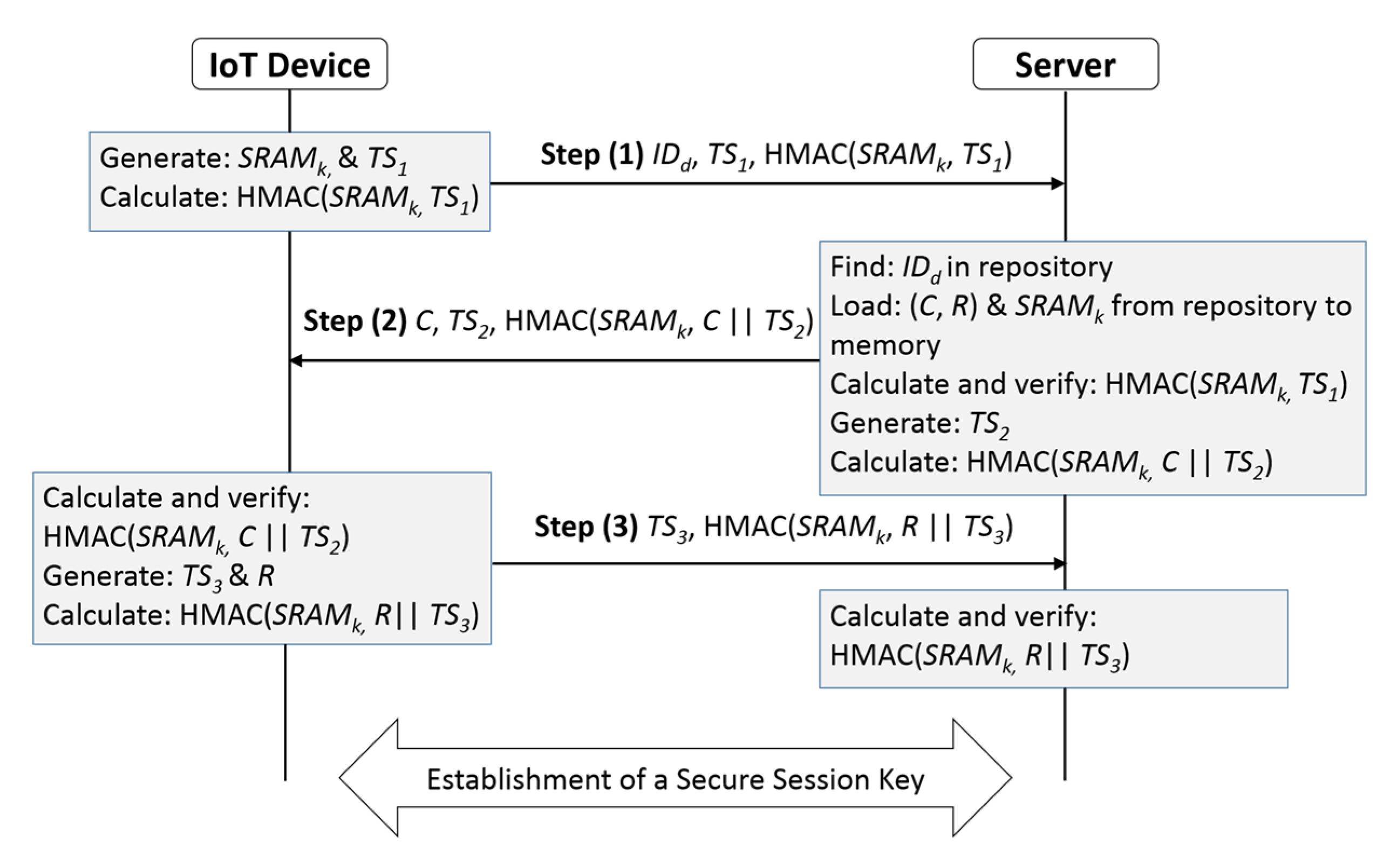
4. Proposed Authentication Mechanism
4.1. Mutual Authentication Mechanism
| Algorithm 1 The mutual authentication between IoT device and server. |
| Input: An IoT device with identity IDd, and server that stores the IoT device’s information (SRAMk, CRP, and IDd); |
| Output: A mutual authentication between the IoT device and the server; |
| Begin |
| 1: The IoT device generates a SRAM PUF cryptography key SRAMk, a timestamp TS1, and HMAC(SRAMk, TS1) message; |
| 2: IoT device sends its IDd, TS1, and HMAC(SRAMk, TS1) message to the server; |
| 3: If (the server finds IDd in its repository) then |
| 4: The server loads the SRAMk, and CRP (C, R) that belongs to the IDd from its repository to its memory; |
| 5: The server calculates HMAC(SRAMk, TS1) message; |
| 6: If (the calculated hash message in step 5 matches the hash message that was sent in step 2) |
| then |
| 7: The server generates a timestamp TS2, calculates (C ‖ TS2), and generates HMAC(SRAMk, C ‖ TS2) message; |
| 8: The server sends C, TS2, and HMAC(SRAMk, C ‖ TS2) message to the IoT device; |
| 9: else |
| Go to step 21; |
| end if |
| 10: else |
| Go to step 21; |
| end if |
| 11: The IoT device calculates (C ‖ TS2), and generates HMAC(SRAMk, C ‖ TS2) message; |
| 12: If (the calculated hash message in step 11 matches the hash message that was sent in step 8) |
| then |
| The authenticity of the server is verified; |
| 13: The IoT device passes the challenge C to its Arbiter PUF, and generates a response R; |
| 14: The IoT device generates a timestamp TS3, calculates (R ‖ TS3), and generates HMAC(SRAMk, R ‖ TS3) message; |
| 15: The IoT device sends TS3, and HMAC(SRAMk, R ‖ TS3) message to the server; |
| 16: else |
| Go to step 21; |
| end if |
| 17: The server calculates (R ‖ TS3), and generates HMAC(SRAMk, R ‖ TS3) message; |
| 18: If (the calculated hash message in step 17 matches the hash message that was sent in step 15) |
| then |
| The authenticity of the IoT device is verified; |
| 19: A mutual authentication between the IoT device and the server is established; |
| 20: else |
| Go to step 21; |
| then |
| 21: Stop (terminates the connection); |
| End |
4.2. Secure Session Key Establishment
- The server generates a 128-bit random number which will be the session key Sk and timestamp (TS4) to ensure the freshness of the message.
- The server encrypts {Sk, TS4} using the IoT device cryptographic key SRAMk and a strong symmetric encryption algorithm such as the AES block cipher encryption algorithm (128-bit block size); M = .
- The server generates HMAC (SRAMk, M ‖ TS4) and sends it alongside the message M and the timestamp TS4 to the IoT device.
- The IoT device generates (M ‖ TS4), and calculates HMAC (SRAMk, M ‖ TS4), and compares the received and the calculated hash messages for the purpose of verifying the message integrity. If the two hashes do not match, the IoT device terminates the connection. Otherwise, the IoT device decrypts the message M using its SRAMk and AES encryption algorithm and retrieves the secured session key Sk.
- The session key Sk will be used by the IoT device and the server to encrypt and decrypt the exchanged data between the IoT device and the server.
5. Protocol Analysis
5.1. Cyberattack Scenarios
5.2. Cyber Defense Assessment
- The IoT device and the server use timestamps in their communications which helps to prevent replay attack attempts.
- Machine learning attack to predict the Arbiter PUF’s responses is not feasible in our mutual authentication. This type of attack is based on capturing PUF’s CRPs. In our mechanism, we do not exchange the PUF response in plaintext, we utilize only one pair of the Arbiter PUF’s CRP for each IoT device in the system. Therefore, launching a machine learning attack on our proposed protocol is not applicable (N/A). Machine learning or modeling attack requires capturing several CRPs of the PUF in order to train the model and predict the PUF response. Furthermore, if an attacker intercepted our exchanged PUF information, they will see only the PUF’s challenge which will be useless for the ML algorithms. The PUF’s CRP in our proposed scheme is similar to the user account’s password in any system, changing the user account’s password regularly is a good security practice. Similarly, the PUF’s CRP in our scheme can be changed to another CRP on a regular basis throughout the IoT device’s life cycle, which presents a strong security measure in the system. Note that changing the PUF’s CRP regularly does not require storing all the PUF’s CRPs in the production server. The PUF’s CRPs can be stored in backup storage for the future use.
- In our authentication mechanism, the IoT device and the server do not exchange sensitive data (such as SRAMk, PUF response R, or the session key Sk) in plaintext over the unsecure communication channel. This supports the data confidentiality. In fact, in the proposed scheme SRAMk and PUF response R are not exchanged in encrypted form either. No encryption takes place before the session key establishment. The only exchanged data in plaintext during authentication are the IoT device identity IDd, timestamps (TS1, TS2, TS3), PUF’s challenge C, and hashed messages. In such a setting a man-in-the-middle attack will not benefit from any captured data. Furthermore, if the man in the middle alters the transferred data, the intended receiver will detect the alteration by matching the hashed messages and drop the connection.
- A silicon PUF cannot be duplicated due to its unique characteristics [19]. An invasive attack on the IoT device PUF to discover its structure will not succeed as duplicating the discovered structure is infeasible. Because the initial secret key is not stored on a chip in the IoT device, there is no useful information on the IoT device for an invasive attack technique to benefit from.
- As we are utilizing a SRAM PUF in our authentication scheme, we do not store the secret key in memory in the IoT device. Therefore, launching a firmware attack on the IoT device will fail to reveal any useful information.
- In our proposed authentication mechanism, although we do not exchange the Arbiter PUF response with any device, it is possible that a side channel attack could succeed in recovering the Arbiter PUF response. However, in our authentication mechanism, revealing the Arbiter response will be useless because: (1) we do not use the Arbiter response to generate the session key and (2) there are no sensitive data that can be recovered by knowing the Arbiter response. Therefore, an attacker would have to launch a successful side channel attack on the SRAM PUF to recover its key SRAMK to compromise the session key. It is possible to have the SRAM PUF key highly secured as there have been attempts in research for improving the security level of the SRAM PUF. One successful study in this field is presented in [32], where researchers present a highly efficient and secure mechanism for extracting and securing the SRAM PUF key against side channel attacks. Such a solution increases the reliability of using SRAM PUF in IoT device security systems. Our approach of utilizing two PUFs in the IoT device and server authentication reduces the effectiveness of side channel attacks against the authentication of the devices, compared to authentication mechanisms that deploy one PUF.
- Assume that an attacker somehow gets hold of the SRAM key SRAMk of the IoT device. To launch a successful spoofing attack, they need to also know the Arbiter PUF responses. Since we do not exchange the PUF response R in plaintext and the Arbiter PUF practically cannot be duplicated, a spoofing attack against our mutual authentication mechanism is impractical.
- As we mentioned above in point number 3, our mutual authentication mechanism does not exchange sensitive data in plaintext. Therefore, if an attacker sniffs out the communication link between the IoT device and the server, they will fail to reveal any useful information that might help to obtain any sensitive data.
5.3. Formal Analysis
5.3.1. BAN Logic Assumption and Postulates
Assumptions
- P| ≡ X: Principal P believes that X is true. Principal P represents the IoT device or the server in our protocol, whereas X represents an exchanged message between the IoT device and the server.
- P X: Principal P sees, can read and repeat X.
- P|~ X: Principal P believed X and sent it once.
- PX: Principal P has the authority to generate X, and P should be trusted for that.
- ♯(X): Represents the freshness of the message X.
- P Q: The key K is good for the communication between the principals P and Q, where no one can compromise the key K.
- P Q: The message X is a shared secret, which is known only to the principals P, Q, and any other principals that are trusted by them.
- : This represents X and Y as a compound, where Y is a secret, and the presence of Y proves the identity of the principal that sent .
Logical Postulates
5.3.2. Proposed protocol Detailed Analysis
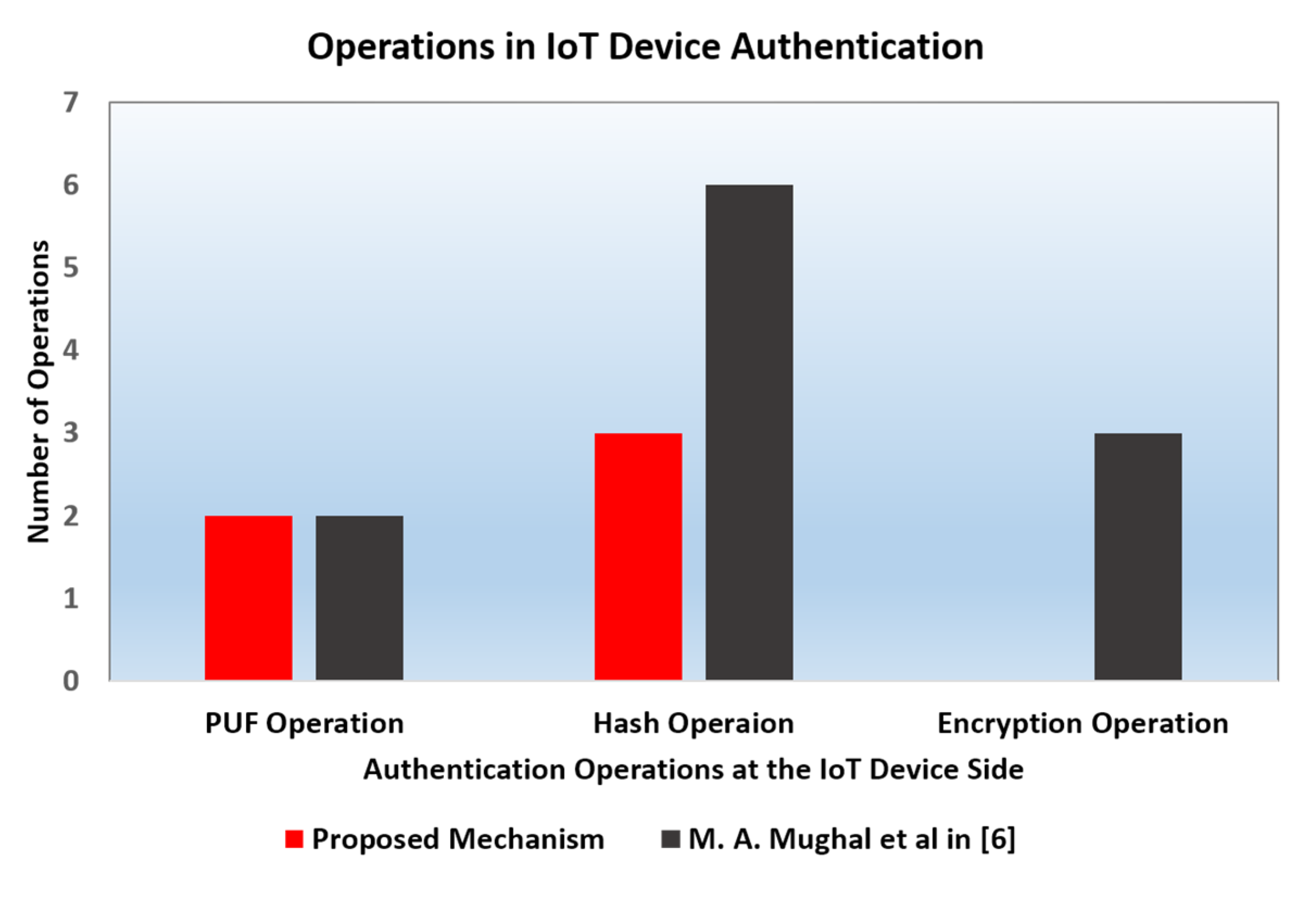
6. Performance Evaluation
6.1. Computational Complexity
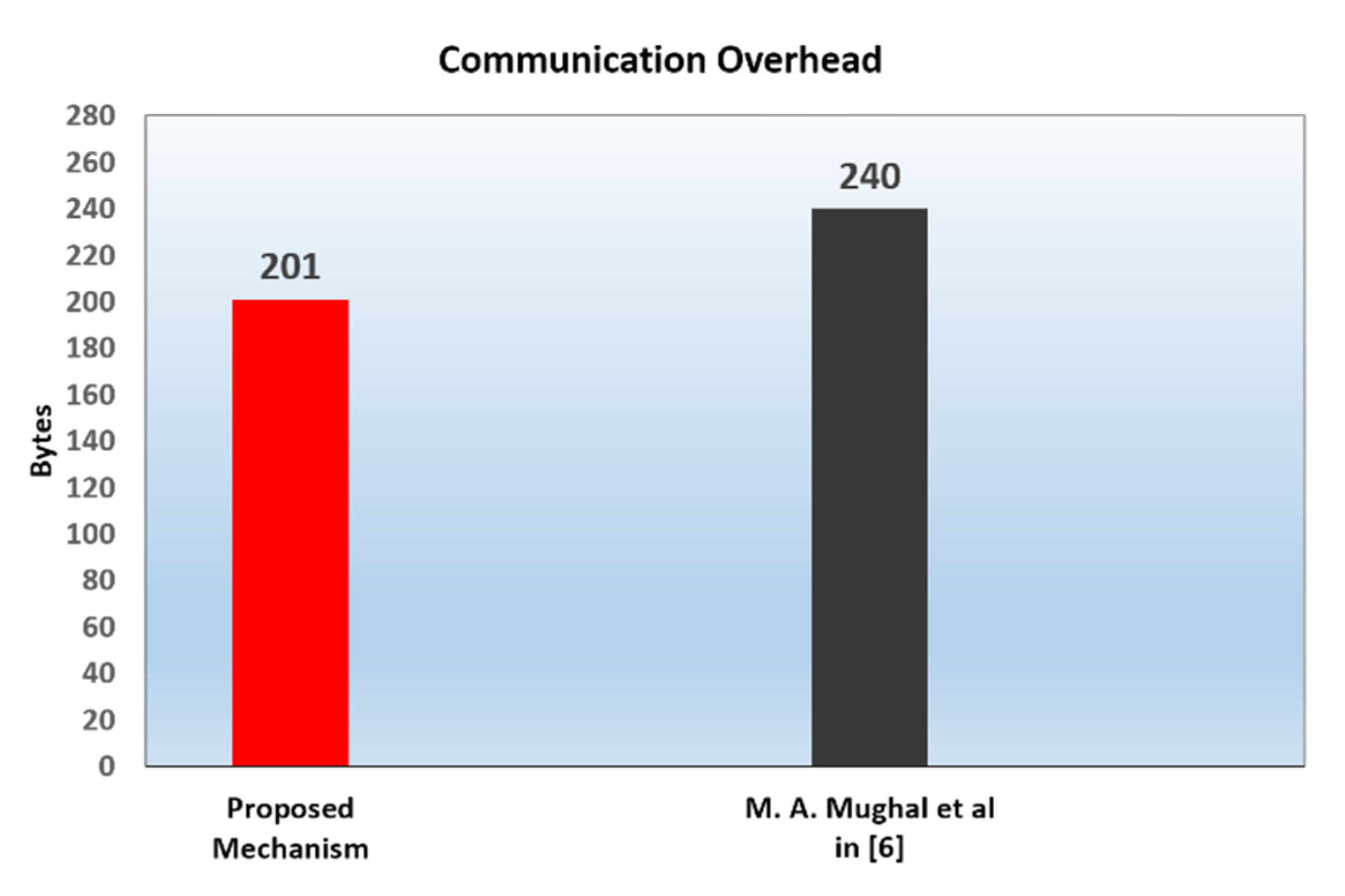
6.2. Communication Overhead
6.3. Storage Constraints
7. Conclusions
8. Future Work
Author Contributions
Funding
Conflicts of Interest
References
- Aman, M.N.; Chua, K.C.; Sikdar, B. Mutual Authentication in IoT Systems using Physical Unclonable Functions. IEEE IoT 2017, 4, 1327–1340. [Google Scholar] [CrossRef]
- Hung, C.; Hsu, W. Power Consumption and Calculation Requirement Analysis of AES for WSN IoT. Sensors 2018, 18, 1675. [Google Scholar] [CrossRef] [PubMed]
- Gope, P.; Sikdar, B. Lightweight and Privacy-Preserving Two-Factor Authentication Scheme for IoT Devices. IEEE IoT 2019, 6, 580–589. [Google Scholar] [CrossRef]
- Rabiah, A.B.; Ramakrishnan, K.K.; Liri, E.; Kar, K. Lightweight Authentication and Key Exchange Protocol for IoT. In Workshop of Decentralized IoT Security and Standards (DISS); NDSS: San Diego, CA, USA, 2018; ISBN 1-891562-51-7. [Google Scholar] [CrossRef]
- Who Needs to Worry About Firmware Attacks? Available online: https://www.opswat.com/blog/who-needs-worry-about-firmware-attacks (accessed on 30 July 2020).
- Mughal, M.A.; Luo, X.; Mahmood, Z.; Ullah, A. Physical Unclonable Function Based Authentication Scheme for Smart Devices in Internet of Things. In Proceedings of the IEEE International Conference on (SmartIoT), Xi’an, China, 17–19 August 2018; pp. 1601–1665. [Google Scholar]
- Alizai, Z.A.; Tareen, N.F.; Jadoon, I. Improved IoT Device Authentication Scheme Using Device Capability and Digital Signatures. In Proceedings of the 2018 International Conference on Applied and Engineering Mathematics (ICAEM), Taxila, Pakistan, 4–5 September 2018. [Google Scholar] [CrossRef]
- Han, J.; Kim, J. A Lightweight authentication mechanism between IoT. In Proceedings of the 2017 International Conference on (ICTC), Jeju, Korea, 18–20 October 2017. [Google Scholar] [CrossRef]
- Rajaguru, K.; Hansdah, R.C. Symmetric Key-Based Lightweight Authentication Protocols for RFID Security. In Proceedings of the 2018 32nd International Conference on (WAINA), Krakow, Poland, 16–18 May 2018. [Google Scholar]
- Braun, M.; Hess, E.; Meyer, B. Using Elliptic Curves on RFID Tags. IJCSNS 2008, 8, 1–9. [Google Scholar]
- Tewari, A.; Gupta, B.B. A Mutual Authentication Protocol for IoT Devices Using Elliptic Curve Cryptography. In Proceedings of the 2018 8th International Conference on Cloud Computing, Data Science & Engineering, Noida, India, 11–12 January 2018. [Google Scholar]
- Kumari, A.; Kumar, V.; YahyaAbbasi, M.; Alam, M. The Cryptanalysis of a Secure Authentication Scheme Based on Elliptic Curve Cryptography for IOT and Cloud Servers. In Proceedings of the 2018 International Conference on Advances in Computing, Communication Control and Networking (ICACCCN), Greater Noida, India, 12–13 October 2018. [Google Scholar]
- Costin, A.; Zaddach, J.; Francillon, A.; Balzarotti, D. A Large Scale Analysis of the Security of Embedded Firmwares. In Proceedings of the 23rd USENIX Security Symposium, San Diego, CA, USA, 20–22 August 2014; Available online: https://www.usenix.org/conference/usenixsecurity14/technical-sessions/presentation/costin/ (accessed on 30 July 2020).
- Balakrishnan, M. Freescale Trust Computing and Security in the Smart Grid, Freescale White Paper, Document Number: TRCMPSCSMRTGRDWP REV 1. 2013. Available online: http://cache.nxp.com/files/32bit/doc/white_paper/TRCMPSCSMRTGRDWP.pdf (accessed on 30 July 2020).
- Akgul, F.; Ye, Y.; Pahlavan, K.; Steger, C.; Alizadeh-shabdiz, F.; Morgan, T. Taking Positioning Indoors: Wi-Fi Localization and GNSS. 2010, pp. 40–47. Available online: https://www.academia.edu/4255217/Taking_Positioning_Indoors_Wi_Fi_Localization_and_GNSS (accessed on 2 August 2020).
- e Silva, P.F.; Kaseva, V.; Lohan, E.S. Wireless Positioning in IoT: A Look at Current and Future Trends. Sensors 2018, 8, 2470. [Google Scholar] [CrossRef] [PubMed]
- Zhang, F.; Kondoro, A.; Muftic, S. Location-Based Authentication and Authorization Using Smart Phones. In Proceedings of the 2012 IEEE 11th International Conference on Trust, Security and Privacy in Computing and Communications, Liverpool, UK, 25–27 June 2012. [Google Scholar]
- Babaei, A.; Schiele, G. Physical Unclonable Functions in the Internet of Things: State of the Art and Open Challenges. Sensors 2019, 19, 3208. [Google Scholar] [CrossRef] [PubMed]
- Herder, C.; Yu, M.; Koushanfar, F.; Devadas, S. Physical Unclonable Functions and Applications: A Tutorial. Proc. IEEE 2014, 102, 1126–1141. [Google Scholar] [CrossRef]
- Rührmair, U.; Sehnke, F.; Sölter, J.; Dror, G.; Devadas, S.; Schmidhuber, J. Modeling attacks on physical unclonable functions. In Proceedings of the 17th ACM Conference on (CCS), Chicago, Illinois, USA, 4–8 October 2010; pp. 237–249. [Google Scholar]
- Maes, R.; Tuyls, P.; Verbauwhede, I. Low-overhead implementation of a soft decision helper data algorithm for SRAM PUFs. In Proceedings of the Cryptographic Hardware and Embedded Systems—CHES 2009: 11th International Workshop, Lausanne, Switzerland, 6–9 September 2009. [Google Scholar]
- Schrijen, G.; Garlati, C. Physical Unclonable Functions to the Rescue A New Way to Establish Trust in Silicon. Available online: https://pdfs.semanticscholar.org/79b1/8f8641ae94e90a4558de822ce0d2a0bd4f6c.pdf?_ga=2.260509514.692675847.1586827044-134552544.1586827044 (accessed on 30 July 2020).
- Suh, G.E.; Devadas, S. Physical Unclonable Functions for Device Authentication and Secret Key Generation. In Proceedings of the 2007 44th ACM/IEEE Design Automation Conference 2007, San Diego, CA, USA, 4–8 June 2007; pp. 9–14. [Google Scholar]
- Gassend, B.; Clarke, D.; van Dijk, M.; Devadas, S. Silicon physical random functions. In Proceedings of the 9th ACM Conference on (CCS), Washington, DC, USA, 18–22 November 2002; pp. 148–160. [Google Scholar]
- Pappu, R.; Ravikanth, P.S.; Recht, B.; Taylor, J.; Gershenfeld, N. Physical one-way functions. Science 2002, 297, 2026–2030. [Google Scholar] [CrossRef] [PubMed]
- TOTP: Time-Based One-Time Password Algorithm. Available online: https://tools.ietf.org/html/rfc6238 (accessed on 30 July 2020).
- Computer Network|HMAC Algorithm. Available online: https://www.geeksforgeeks.org/computer-network-hmac-algorithm/ (accessed on 30 July 2020).
- What You Need to Know About SHA-3 for Embedded System Security. Available online: https://www.electronicdesign.com/technologies/embedded-revolution/article/21808025/what-you-need-to-know-about-sha3-for-embedded-system-security (accessed on 30 July 2020).
- The Constrained Application Protocol (CoAP). Available online: https://tools.ietf.org/html/rfc7252 (accessed on 30 July 2020).
- Invasive Attacks. Available online: https://www.sec.ei.tum.de/en/research/invasive-attacks/ (accessed on 30 July 2020).
- van der Leest, V.; Maes, R.; Schrijen, G.J.; Tuyls, P. Hardware intrinsic security to protect value in the mobile market. In ISSE 2014 Securing Electronic Business Processes; Springer: Wiesbaden, Germany, 2014; pp. 1881–1898. [Google Scholar]
- Xu, H.; Ding, J.; Li, P.; Zhu, F.; Wang, R. A Lightweight RFID mutual authentication protocol based on physical unclonable function. Sensors 2018, 18, 760. [Google Scholar] [CrossRef] [PubMed]
- Banerjee, S.; Odelu, V.; Das, A.K.; Chattopadhyay, S.; Rodrigues, J.J.P.C.; Park, Y. Physically Secure Lightweight Anonymous User Authentication Protocol for Internet of Things Using Physically Unclonable Functions. IEEE Access 2019, 7, 85627–85644. [Google Scholar] [CrossRef]
- Burrows, M.; Abadi, M.; Needham, R. A logic of authentication. ACM Trans. Comput. Syst. 1990, 8, 18–36. [Google Scholar] [CrossRef]
- Advanced Encryption Standard (AES) Ciphersuites for Transport layer Security (TLS). Available online: https://tools.ietf.org/html/rfc3268 (accessed on 30 July 2020).
- Guy-Cedric, T.; Suchithra, R. A Comparative Study on AES 128 BIT AND AES 256 BIT. Int. J. Sci. Res. Comput. Sci. Eng. 2018, 6, 30–33. [Google Scholar] [CrossRef]
- IoT Specific IPv6 Stateless Address Autoconfiguration with Modified EUI-64. Available online: https://tools.ietf.org/html/draft-pskim-iot-ipv6-eui64-00 (accessed on 30 July 2020).
- AES-CCM Cipher Suites for Transport Layer Security (TLS). Available online: https://tools.ietf.org/html/rfc6655 (accessed on 30 July 2020).
- Using HMAC-SHA-256, HMAC-SHA-384, and HMAC-SHA-512 with IPsec. Available online: https://tools.ietf.org/html/rfc4868 (accessed on 30 July 2020).


| Notation | Description |
|---|---|
| ‖ | Concatenation symbol |
| IDd | IoT device’s identifier |
| TS1, TS2, TS3, and TS4 | Timestamps |
| SRAMk | Secret key (identifier) extracted from SRAM |
| HMAC(SRAMk, TS1) | A keyed hash message authentication code of the timestamp TS1 |
| C | Challenge for the Arbiter PUF of the IoT device |
| R | Arbiter PUF’s response for the C challenge |
| CRP (C, R) | Challenge–Response Pair of C and R |
| Encrypting using AES algorithm and the SRAMk as the cryptography key |
| ID. | Attack Scenario: Definition |
|---|---|
| 01 | Replay attack: A type of network attack where a legitimate traffic is maliciously repeated or delayed in order to disrupt the communications. |
| 02 | Machine Learning (ML) attack: PUF’s CRPs can be exploited to predict the PUF response by using ML algorithms. |
| 03 | Man-in-the-middle attack: A type of attack where an attacker secretly intercepts the traffic between two parties and possibly alters the communicated information. |
| 04 | Invasive attack: It is a hardware attack, where an attacker physically accesses the hardware’s semiconductor, i.e., an IC, with the purpose of reading the stored secrets on it or discovering its structure [30]. |
| 05 | Firmware attack: An attacker remotely connects to the IoT device and alters or injects a malicious software to compromise the stored secret key. |
| 06 | Impersonating/spoofing attacks: A type of attack where an attacker tries to act as if they are a trusted node in an IoT system. |
| 07 | Eavesdropping attack: A form of sniffing attack where an attacker seeks out sensitive data from insecure communication networks. |
| 08 | Side channel attack: A type of attack which requires physical access to the PUF. The attack can be invasive, semi-invasive, and non-invasive. In the first two types, the attacker will have access to the internal structure of the PUF. The attack would not damage the PUF if semi-invasive, but it could damage the PUF if invasive. In non-invasive attack, the attacker would try to recover PUF secret key by analyzing data such as the PUF power consumption. Side channel attacks can be active where the attacker actively manipulates the PUF environment such as its power supply, or they can be passive, where the attacker is only collecting data about the PUF, such as the temperature, and analyzes these data [31]. |
| Security Feature | Mughal et al. [6] | Aman et al. [1] | Alizai et al. [7] | Han and Kim [8] | Xu et al. [32] | Banerjee et al. [33] | Proposed Mechanism |
|---|---|---|---|---|---|---|---|
| Utilized security algorithms | PUF and Encryption and Hash algorithms | PUF and Encryption and Hash algorithms | Functional Operation and Encryption and Hash | Encryption (Block Cipher algorithm) | PUF and Encryption | PUF and Hash algorithm and XOR operation | PUF and Hash algorithm |
| Number of security methods used | 3 | 3 | 3 | 1 | 2 | 3 | 2 |
| Two-Factor Authentication | Yes | No | Yes | No | No | Yes | Yes |
| Resilience to replay attack | No | No | Yes | No | Yes | Yes | Yes |
| Resilience to machine learning attack | No | Yes | No | N/A | N/A | N/A | N/A |
| Resilience to Man–in-the-middle attack | No | No | No | No | Yes | Yes | Yes |
| Resilience to invasive attack | Yes | Yes | N/A | N/A | Yes | Yes | Yes |
| Resilience to firmware attack | No | Yes | No | No | No | No | Yes |
| Resilience to spoofing attack | No | Yes | No | No | Yes | Yes | Yes |
| Resilience to eavesdropping attack | No | Yes | No | No | Yes | Yes | Yes |
| Authentication Mechanism | IoT Device | Server |
|---|---|---|
| Mughal et al. [6] | 6NH + 2NPUF + 3NENC | 6NH + 3NENC |
| Proposed Mechanism | 2NPUF + 3NHMAC | 3NHMAC |
© 2020 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Mostafa, A.; Lee, S.J.; Peker, Y.K. Physical Unclonable Function and Hashing Are All You Need to Mutually Authenticate IoT Devices. Sensors 2020, 20, 4361. https://doi.org/10.3390/s20164361
Mostafa A, Lee SJ, Peker YK. Physical Unclonable Function and Hashing Are All You Need to Mutually Authenticate IoT Devices. Sensors. 2020; 20(16):4361. https://doi.org/10.3390/s20164361
Chicago/Turabian StyleMostafa, Ahmed, Suk Jin Lee, and Yesem Kurt Peker. 2020. "Physical Unclonable Function and Hashing Are All You Need to Mutually Authenticate IoT Devices" Sensors 20, no. 16: 4361. https://doi.org/10.3390/s20164361
APA StyleMostafa, A., Lee, S. J., & Peker, Y. K. (2020). Physical Unclonable Function and Hashing Are All You Need to Mutually Authenticate IoT Devices. Sensors, 20(16), 4361. https://doi.org/10.3390/s20164361





