Reduced Overhead Routing in Short-Range Low-Power and Lossy Wireless Networks †
Abstract
1. Introduction
- (1)
- Identification of inefficiencies in RPL’s route construction and data forwarding algorithms.
- (2)
- Improvements to P2P route construction and data forwarding algorithms for RPL’s storing and non-storing MoPs.
- (3)
- A Bloom Filter based approach for P2MP data forwarding to minimize source routing overhead in RPL’s non-storing MoP.
- (4)
- Analyzing the impact of RPL’s destination-oriented directed a-cyclic graph (DODAG) depth on MP2P, P2MP, and P2P communications.
- (5)
- An analysis of the protocol using emulation, simulation, and test-bed based experiments. Our results show that ERPL demonstrates overall lower packet loss, delay, requires fewer transmissions to deliver P2P packets, lower control overhead, and is more energy-efficient compared to RPL.
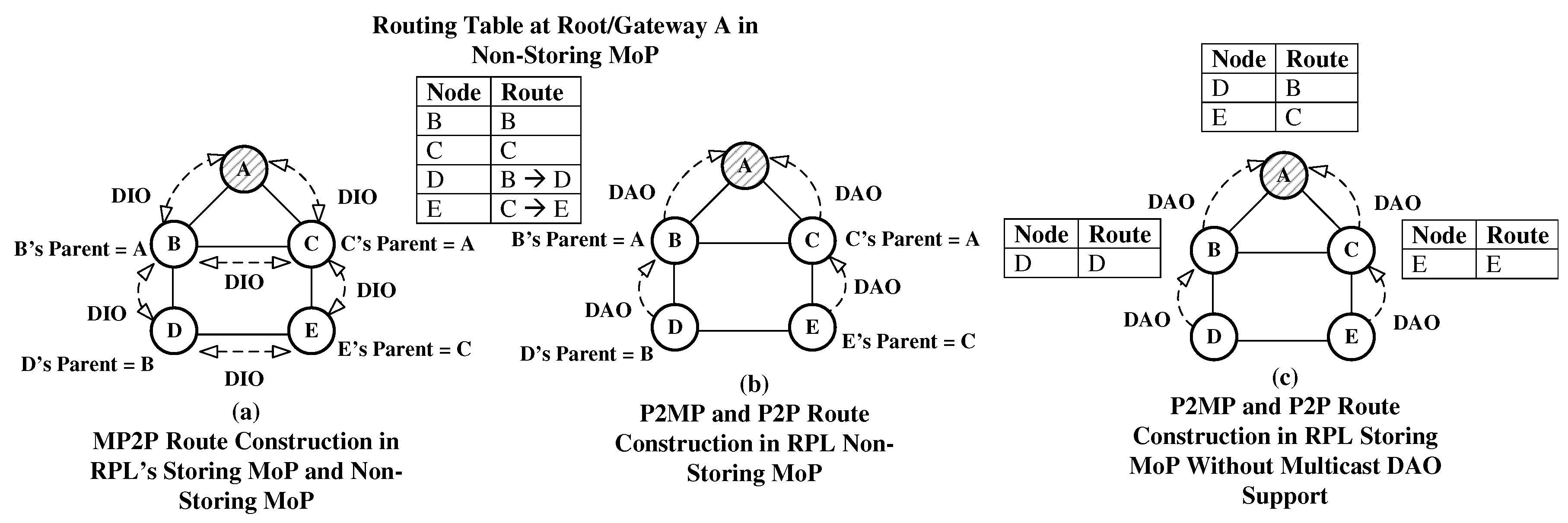
2. RPL: Routing Protocol for Low-Power and Lossy Networks
- (1)
- DIO: DODAG Information Object (used to discover forwarding paths for MP2P communication)
- (2)
- DIS: Destination Information Solicitation (a node multicasts this message to discover the route to the gateway)
- (3)
- DAO: Destination Advertisement Object (used to discover forwarding paths for M2MP and P2P communications)
2.1. DODAG Construction
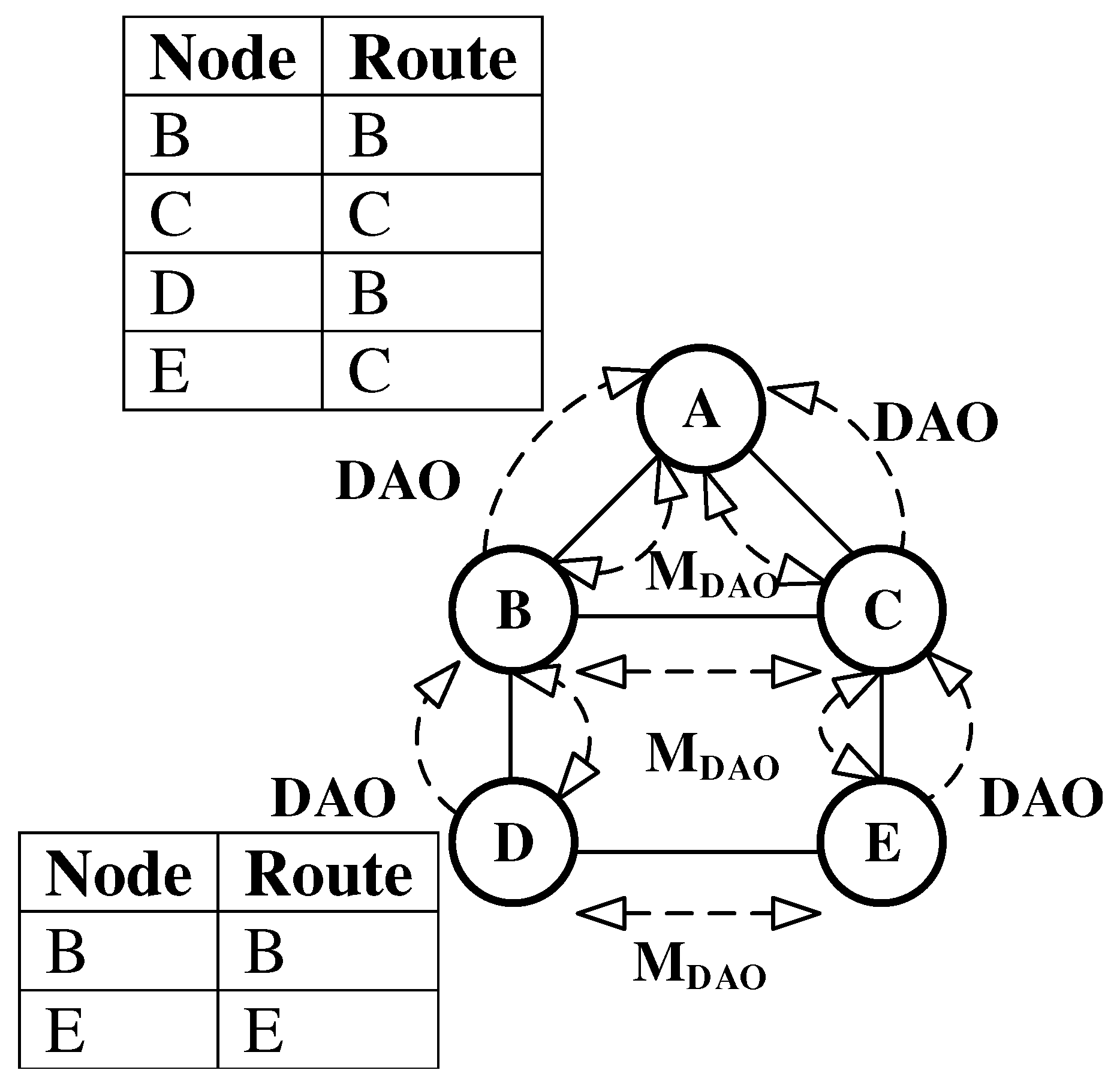
2.2. P2MP and P2P Route Construction and Data Packet Forwarding
3. Related Work
4. Reduced Overhead Routing Protocol
- (1)
- Enhanced P2P routing and forwarding
- (2)
- Reduced overhead P2MP routing
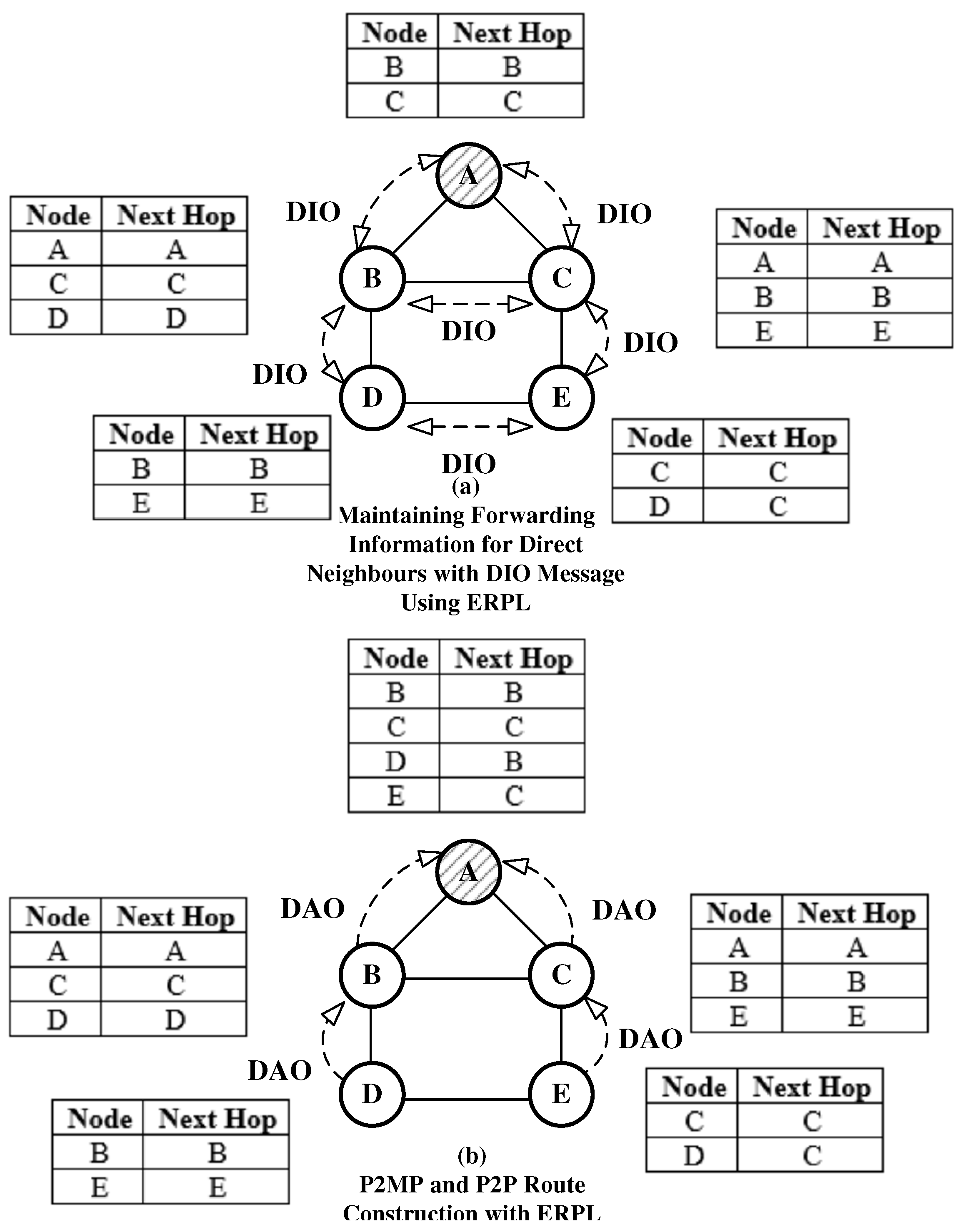
4.1. Enhanced P2P Routing and Forwarding
4.1.1. P2P Routing Problem in RPL
4.1.2. Proposed Enhancement
- (1)
- If a DIO message is received at a node, the node extracts the multicasting node’s address from the DIO message, and stores it in its forwarding table. This step is carried out without considering whether the node is interested in joining the DODAG or not. If an entry for the multicasting node is already present in the table then the entry is refreshed and the next hop field is set equal to the multicasting node’s address. If a node has a packet to transmit, it searches the destination address in its forwarding table. If the corresponding entry is available in the forwarding table, the packet is transmitted to the destination node or to the next hop. Otherwise, RPL forwarding rules are followed.
- (2)
- The above algorithm works in storing MoP, but nodes do not maintain forwarding tables in the non-storing MoP. In non-storing MoP, whenever a node receives a DIO message, it searches the IPv6 neighbor table. If the DIO message’s multicasting node is not present in the table, a new record for the multicasting node is created and stored in the neighbour table. In this case, a NULL value is stored in the neighbor table’s field for the link-local address. This forces the MAC layer to obtain a link-local address for the neighbor node before transmitting a frame. In non-storing MoP, another approach can be used that can store the multicasting node’s address at the networking layer. In the non-storing MoP, this is feasible as nodes only need to store their direct neigbours’ network layer address. In a realistic scenario nodes typically have resources to store addresses of their direct neighbors. If a node requires to transmit a packet, the node searches the destination node’s address in its neighbor table or the data structure holding addresses of the node’s direct neighbors. If a match exists, the packet is forwarded to the destination node, otherwise the RPL’s forwarding algorithm for non-storing MoP is followed. When the root forwards the packet, it uses source routing, hence the presented forwarding algorithm only works if source routing is not used, i.e., when a P2P communication packet has not reached the root.
4.2. Point to Multi-Point Reduced Overhead Routing
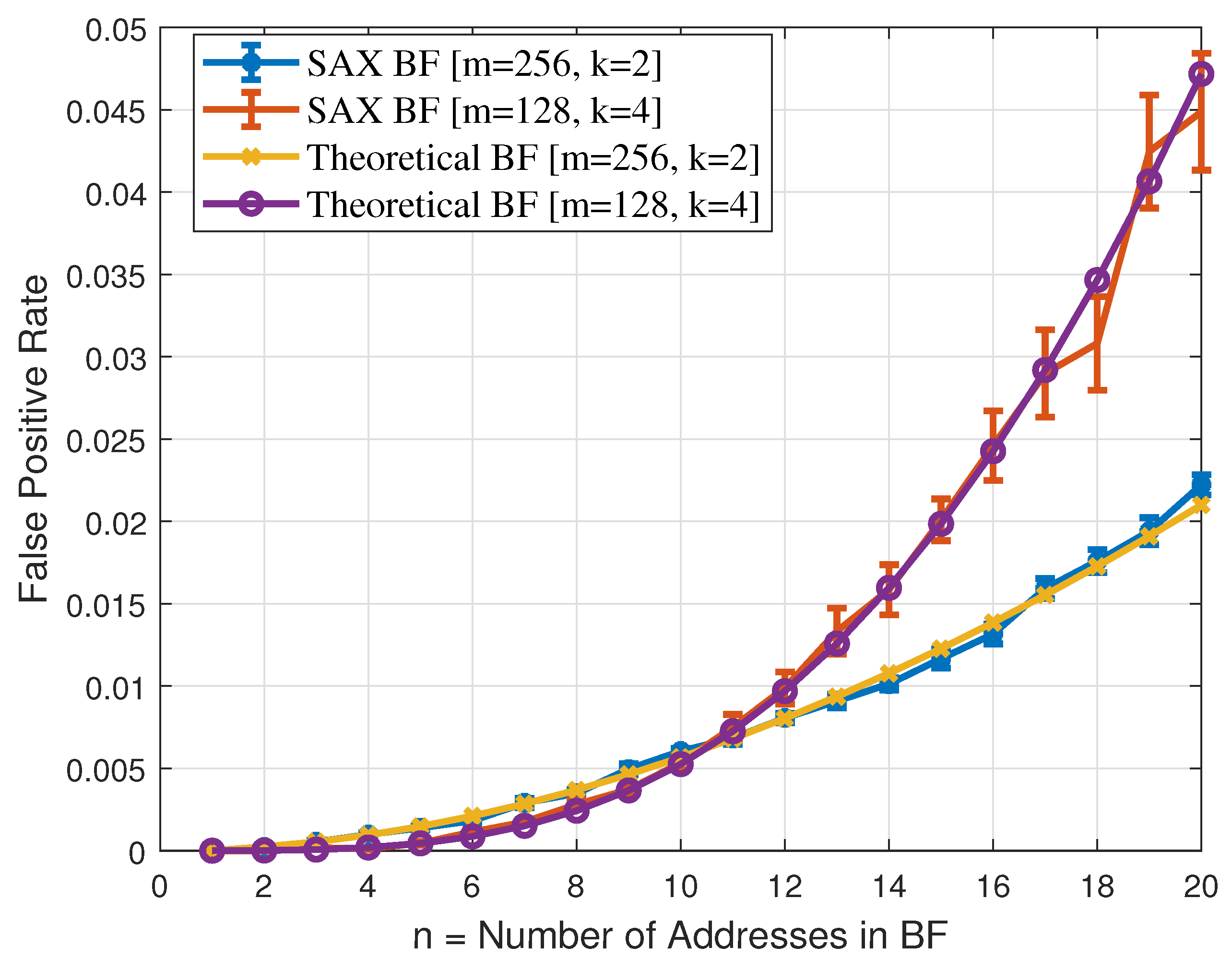
4.2.1. Choice of the Hash Functions
4.2.2. Data Packet Forwarding
4.2.3. Techniques to Reduce the Impact of False Positive on Routing
5. Performance Evaluation
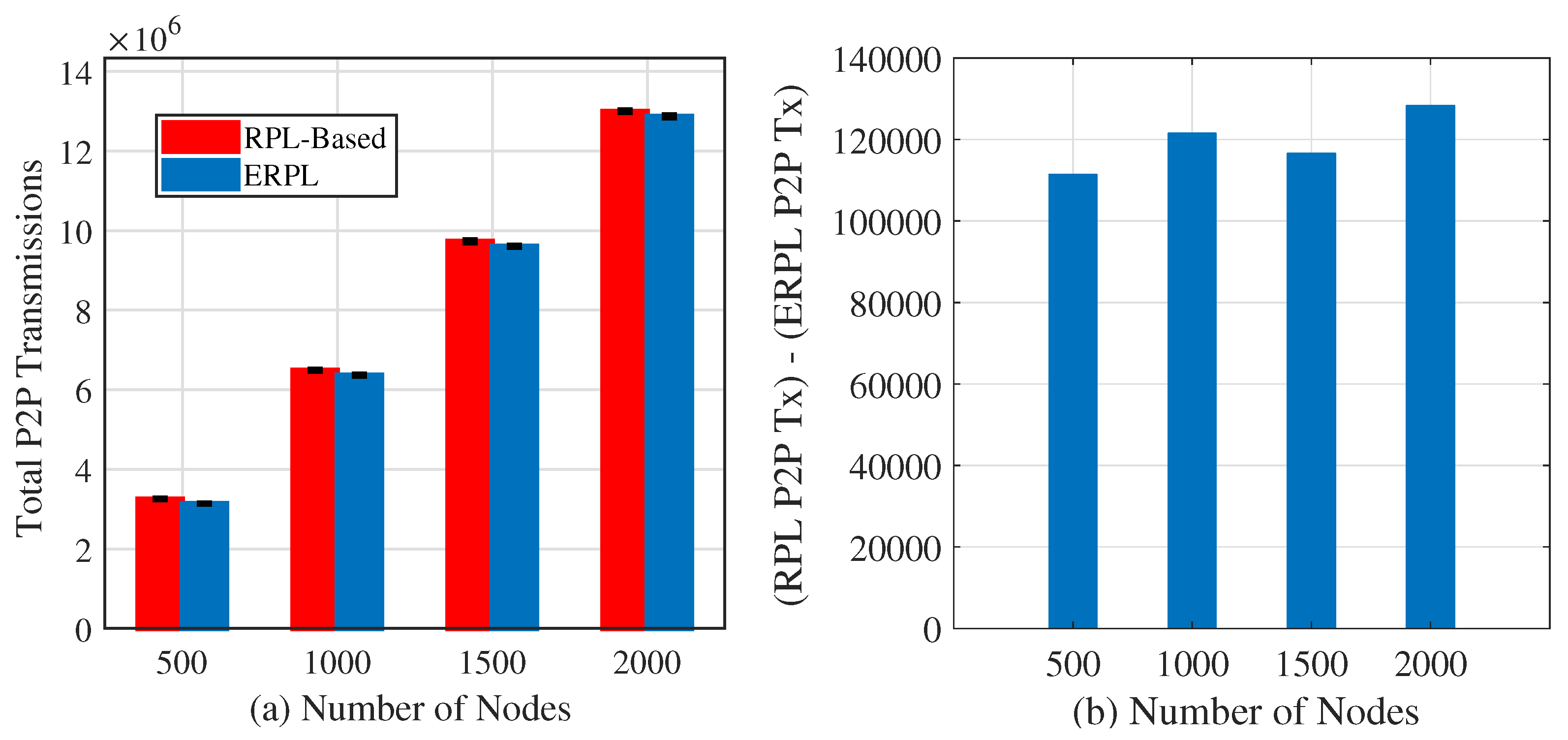
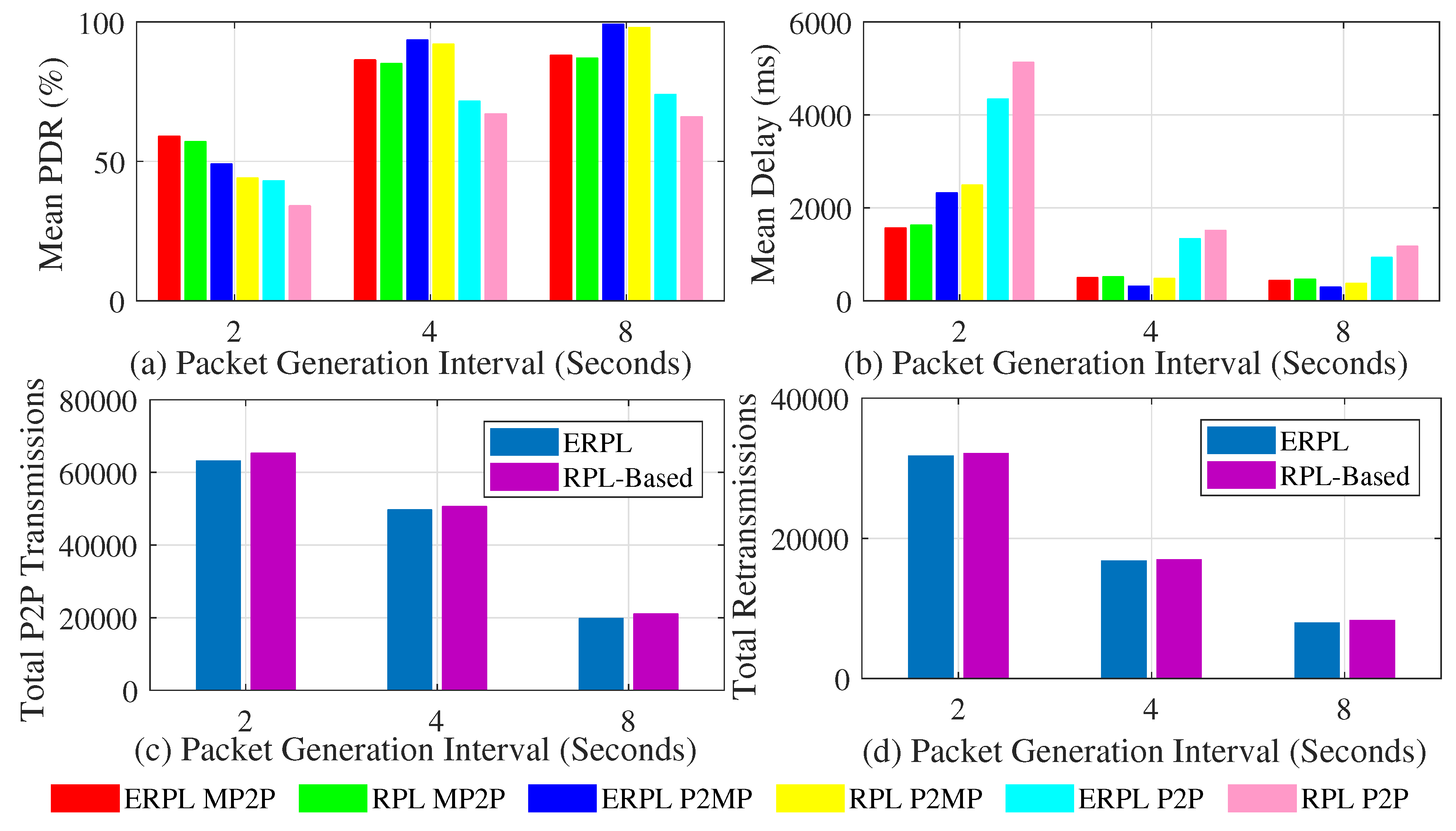
5.1. ERPL’s P2P Routing and Data Forwarding Performance Evaluation
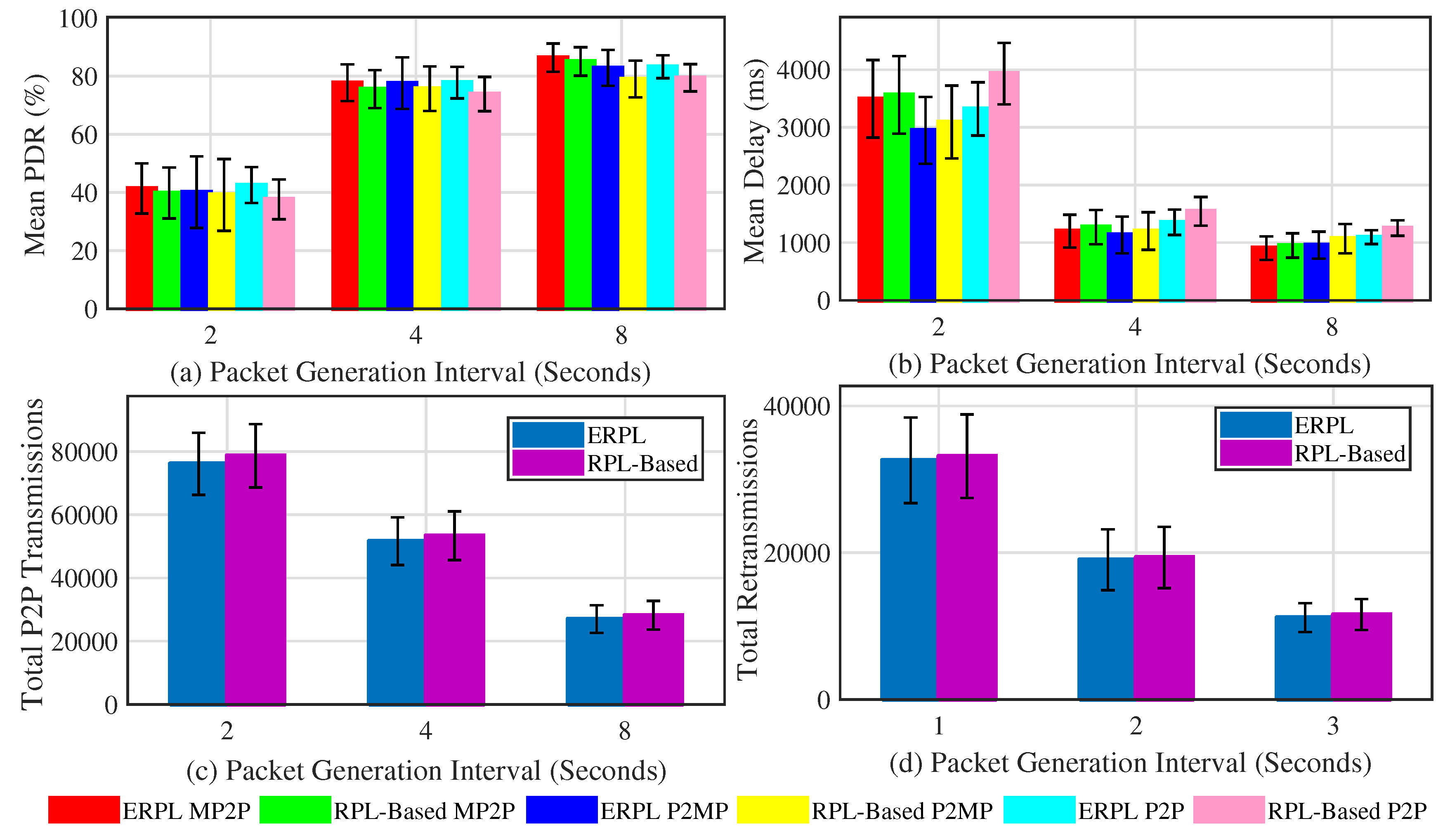
5.1.1. Random Topology Results
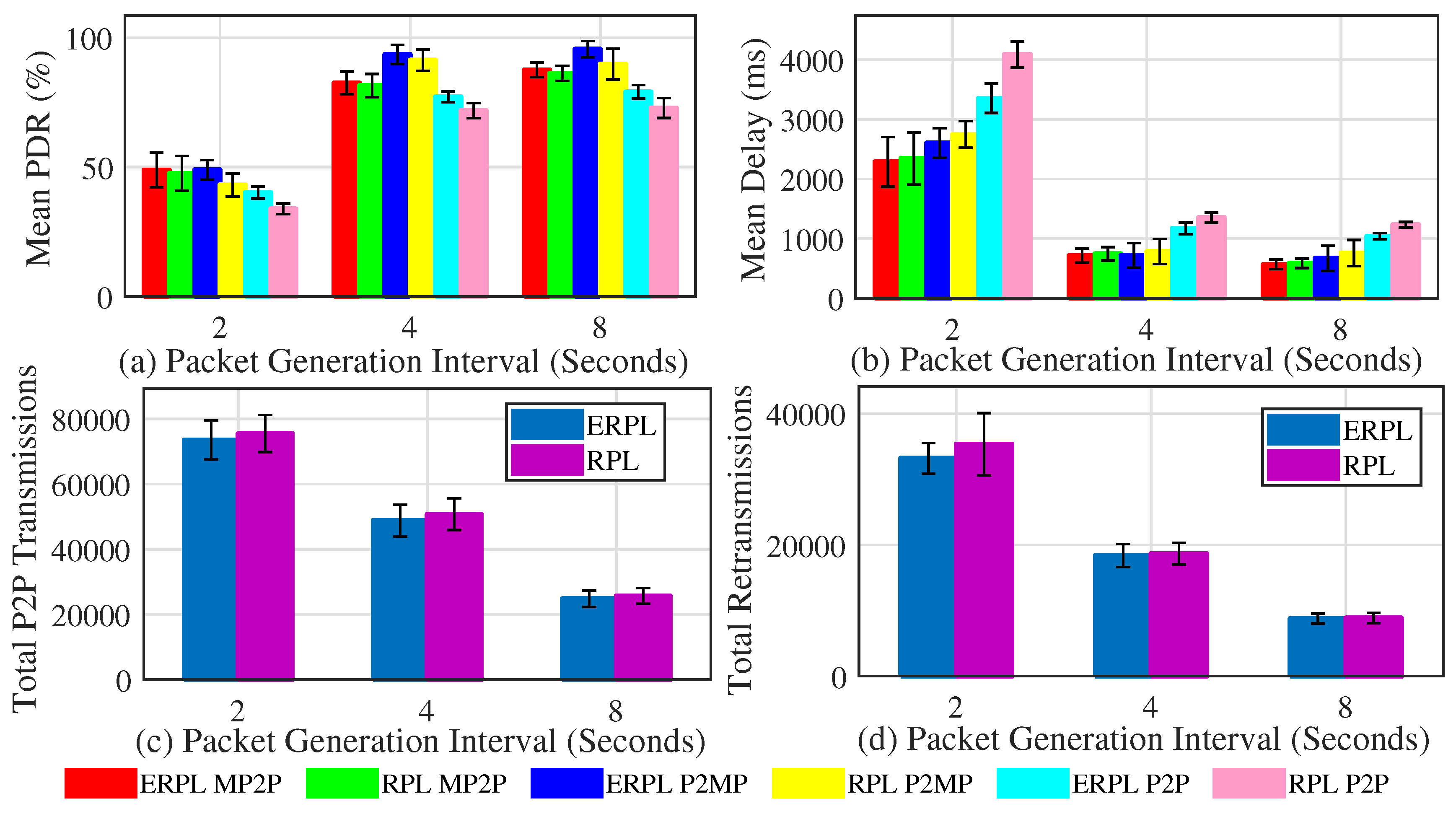
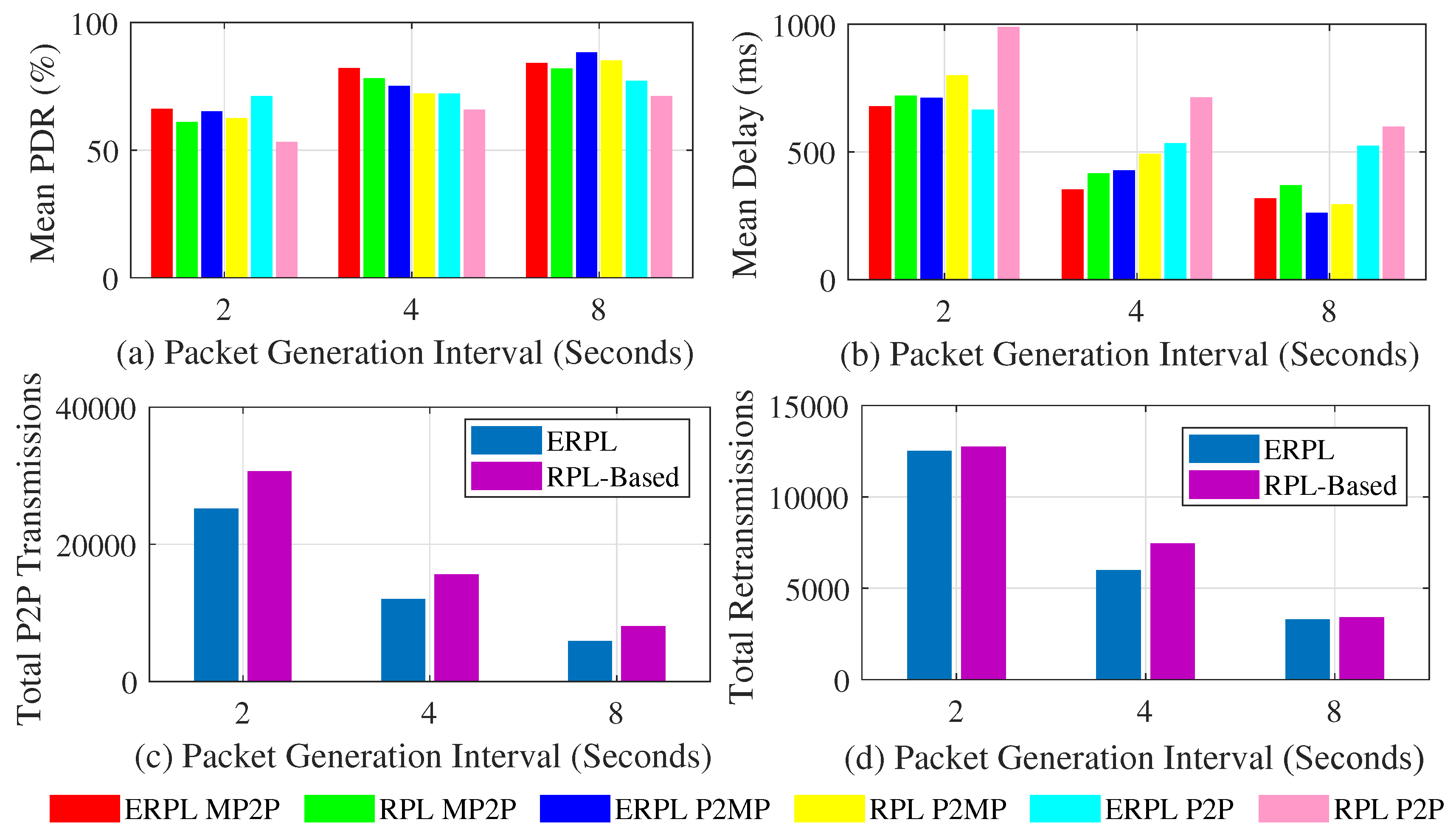
5.1.2. Results Using Grid Network Topology
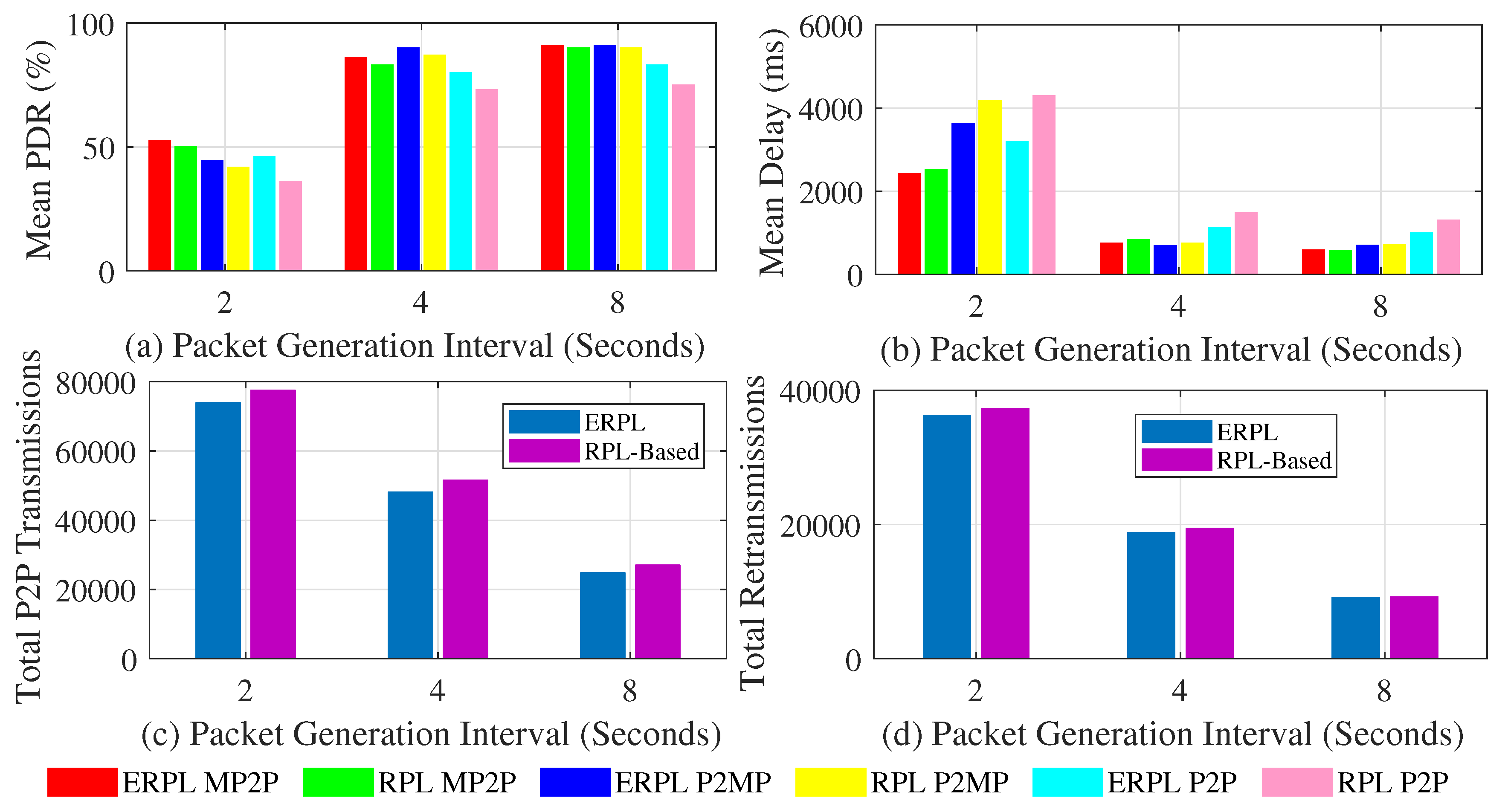
5.1.3. Testbed Results
5.1.4. Discussion
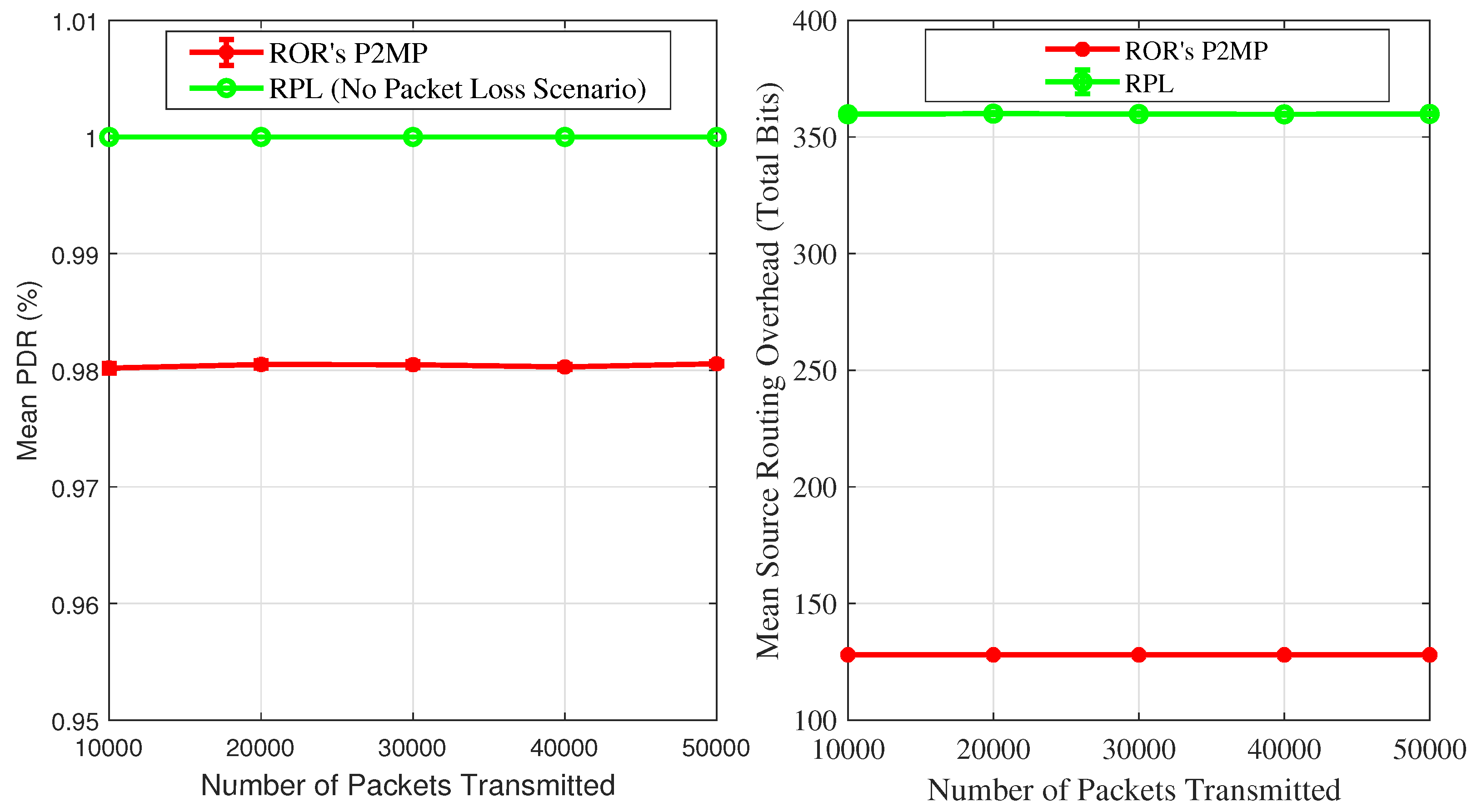
5.2. ERPL’s P2MP Routing and Data Forwarding Performance Evaluation
6. Conclusions
Author Contributions
Funding
Acknowledgments
Conflicts of Interest
References
- Brandt, A.; Hui, J.; Kelsey, R.; Levis, P.; Pister, K.; Struik, R.; Vasseur, J.; Alexander, R. RPL: IPv6 Rotuing Protocol for Low-Power and Lossy Networks. Available online: https://tools.ietf.org/html/rfc6550 (accessed on 11 March 2019).
- Sartori, B.; Thielemans, S.; Bezunartea, M.; Braeken, A.; Steenhaut, K. Enabling RPL Multihop Communications based on LoRa. In Proceedings of the IEEE 13th International Conference on Wireless and Mobile Computing, Networking and Communications (WiMob), Rome, Italy, 9–11 October 2017; pp. 1–8. [Google Scholar]
- Ko, J.; Jeong, J.; Park, J.; Jun, J.A.; Gnawali, O.; Paek, J. DualMOP-RPL: Supporting Multiple Modes of Downward Routing in a Single RPL Network. ACM Trans. Sens. Netw. 2015, 11, 39:1–39:20. [Google Scholar] [CrossRef]
- Gan, W.; Shi, Z.; Zhang, C.; Sun, L.; Ionescu, D. MERPL: A More Memory-Efficient Storing Mode in RPL. In Proceedings of the 19th IEEE International Conference on Networks, Singapore, 11–13 December 2013; pp. 1–5. [Google Scholar]
- Kiraly, C.; Istomin, T.; Iova, O.; Picco, G.P. D-RPL: Overcoming Memory Limitations in RPL Point-to-Multipoint Routing. In Proceedings of the IEEE 40th Conference on Local Computer Networks, Clearwater Beach, FL, USA, 26–29 October 2015; pp. 157–160. [Google Scholar]
- Iova, O.; Picco, P.; Istomin, T.; Kiraly, C. RPL: The Routing Standard for the Internet of Things... Or Is It? IEEE Commun. Mag. 2016, 54, 16–22. [Google Scholar] [CrossRef]
- Heurtefeux, K.; Menouar, H. Experimental Evaluation of a Routing Protocol for Wireless Sensor Networks: RPL Under Study. In Proceedings of the 6th Joint IFIP Wireless and Mobile Networking Conference, Dubai, UAE, 23–25 April 2013; pp. 1–4. [Google Scholar]
- Tripathi, J.; de Oliveira, J.C.; Vasseur, J. A Performance Evaluation Study of RPL: Routing Protocol for Low power and Lossy Networks. In Proceedings of the 44th Annual Conference on Information Sciences and Systems, Princeton, NJ, USA, 17–19 March 2010; pp. 1–6. [Google Scholar]
- Gaddour, O.; Koubaa, A.; Chaudhry, S.; Tezeghdanti, M.; Chaari, R.; Abid, M. Simulation and Performance Evaluation of DAG Construction with RPL. In Proceedings of the 3rd International Conference on Communications and Networking, Hammamet, Tunisia, 29 March–1 April 2012; pp. 1–8. [Google Scholar]
- Farooq, M.O.; Sreenan, C.J.; Brown, K.; Kunz, T. RPL-Based Routing Protocols For Multi-Sink Wireless Sensor Networks. In Proceedings of the 11th IEEE International Conference on Wireless and Mobile Computing, Networking and Communications, Abu-Dhabi, UAE, 19–21 October 2015; pp. 452–459. [Google Scholar]
- Baccelli, E.; Philipp, M.; Goyal, M. The P2P-RPL Routing Protocol for IPv6 Sensor Networks: Testbed experiments. In Proceedings of the 19th International Conference on Software, Telecommunication, and Computer Networks, Split, Croatia, 15–17 September 2011; pp. 200–209. [Google Scholar]
- Goyal, M.; Baccelli, E.; Philipp, M.; Brandt, A.; Martocci, J. Reactive Discovery of Point-to-Point Routes in Low-Power and Lossy Networks. Available online: https://tools.ietf.org/html/rfc6997 (accessed on 11 March 2019).
- Corbalan, P.; Marfievici, R.; Cionca, V.; O’Shea, D.; Pesch, D. Into the SMOG: The Stepping Stone to Centralized WSN Control. In Proceedings of the 2016 IEEE 13th International Conference on Mobile Ad Hoc and Sensor Systems (MASS), Brasília, Brazil, 10–13 October 2016; pp. 118–126. [Google Scholar]
- Duquennoy, S.; Landsiedel, O.; Voigt, T. Let the Tree Bloom: Scalable Opportunistic Routing with ORPL. In Proceedings of the 11th ACM Conference on Embedded Networked Sensor Systems, Roma, Italy, 11–15 November 2013; pp. 2:1–2:14. [Google Scholar]
- Paszkowska, A.; Iwanicki, K. The IPv6 Routing Protocol for Low-power and Lossy Networks (RPL) Under Network Partitions. In Proceedings of the International Conference on Embedded Wireless Systems and Networks (EWSN), Madrid, Spain, 14–16 February 2018; pp. 90–101. [Google Scholar]
- Eriksson, J.; Finne, N.; Tsiftes, N.; Duquennoy, S.; Voigt, T. Scaling RPL to Dense and Large Networks with Constrained Memory. In Proceedings of the International Conference on Embedded Wireless Systems and Networks (EWSN), Madrid, Spain, 14–16 February 2018; pp. 126–134. [Google Scholar]
- Pu, C.; Hajjar, S. Mitigating Forwarding Misbehaviors in RPL-based Low Power and Lossy Networks. In Proceedings of the 15th IEEE Annual Consumer Communications Networking Conference (CCNC), Las Vegas, NV, USA, 12–15 January 2018; pp. 1–6. [Google Scholar]
- Conti, M.; Kaliyar, P.; Rabbani, M.M.; Ranise, S. SPLIT: A Secure and Scalable RPL routing protocol for Internet of Things. In Proceedings of the 14th International Conference on Wireless and Mobile Computing, Networking and Communications (WiMob), Limassol, Cyprus, 15–17 October 2018. [Google Scholar]
- Farooq, M.O.; Pesch, D. ERPL: An Enhanced Peer-to-Peer Routing Mechanism for Low-Power and Lossy Networks. In Proceedings of the IFIP Wireless and Mobile Networking Conference, Prague, Czech Republic, 3–5 September 2018. [Google Scholar]
- Thubert, P. Objective Function Zero for the Routing Protocol for Low-Power and Lossy Networks (RPL). Available online: https://tools.ietf.org/html/rfc6552 (accessed on 11 March 2019).
- Sun, H.; Wang, C.; Ahmad, B.I. From Internet of Things to Smart Cities Enabling Technologies; CRC Press: New York, NY, USA, 2017. [Google Scholar]
- Ramakrishna, M.V.; Zobel, J. Performance in Practice of String Hashing Functions. In Proceedings of the Conference on Database Systems for Advanced Applications, Melbourne, Australia, 1–4 April 1997. [Google Scholar]
- Osterlind, F.; Dunkels, A.; Eriksson, J.; Finne, N.; Voigt, T. Cross-Level Sensor Network Simulation with Cooja. In Proceedings of the 31th IEEE Conference on Local Computer Networks, Tampa, FL, USA, 14–16 November 2006; pp. 641–648. [Google Scholar]
- Lim, R.; Ferrari, F.; Zimmerling, M.; Walser, C.; Sommer, P.; Beutel, J. FlockLab: A Testbed for Distributed, Synchronized Tracing and Profiling of Wireless Embedded Systems. In Proceedings of the 12th ACM/IEEE Conference on Information Procecssing in Wireless Sensor Networks (IPSN), Philadelphia, PA, USA, 8–11 April 2013; pp. 153–165. [Google Scholar]
| Parameter | Value |
|---|---|
| MAC layer | IEEE 802.15.4 CSMA-CA |
| MAC layer ACKs | Enabled |
| Radio model | Unit disk with distance loss |
| Channel rate | 250 kbps |
| MAC layer queue size | 10 frames |
| Node transmission range | 50 m |
| Node carrier sensing range | 100 m |
© 2019 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Farooq, M.O.; Pesch, D. Reduced Overhead Routing in Short-Range Low-Power and Lossy Wireless Networks. Sensors 2019, 19, 1240. https://doi.org/10.3390/s19051240
Farooq MO, Pesch D. Reduced Overhead Routing in Short-Range Low-Power and Lossy Wireless Networks. Sensors. 2019; 19(5):1240. https://doi.org/10.3390/s19051240
Chicago/Turabian StyleFarooq, Muhammad Omer, and Dirk Pesch. 2019. "Reduced Overhead Routing in Short-Range Low-Power and Lossy Wireless Networks" Sensors 19, no. 5: 1240. https://doi.org/10.3390/s19051240
APA StyleFarooq, M. O., & Pesch, D. (2019). Reduced Overhead Routing in Short-Range Low-Power and Lossy Wireless Networks. Sensors, 19(5), 1240. https://doi.org/10.3390/s19051240






