CATSWoTS: Context Aware Trustworthy Social Web of Things System
Abstract
:1. Introduction
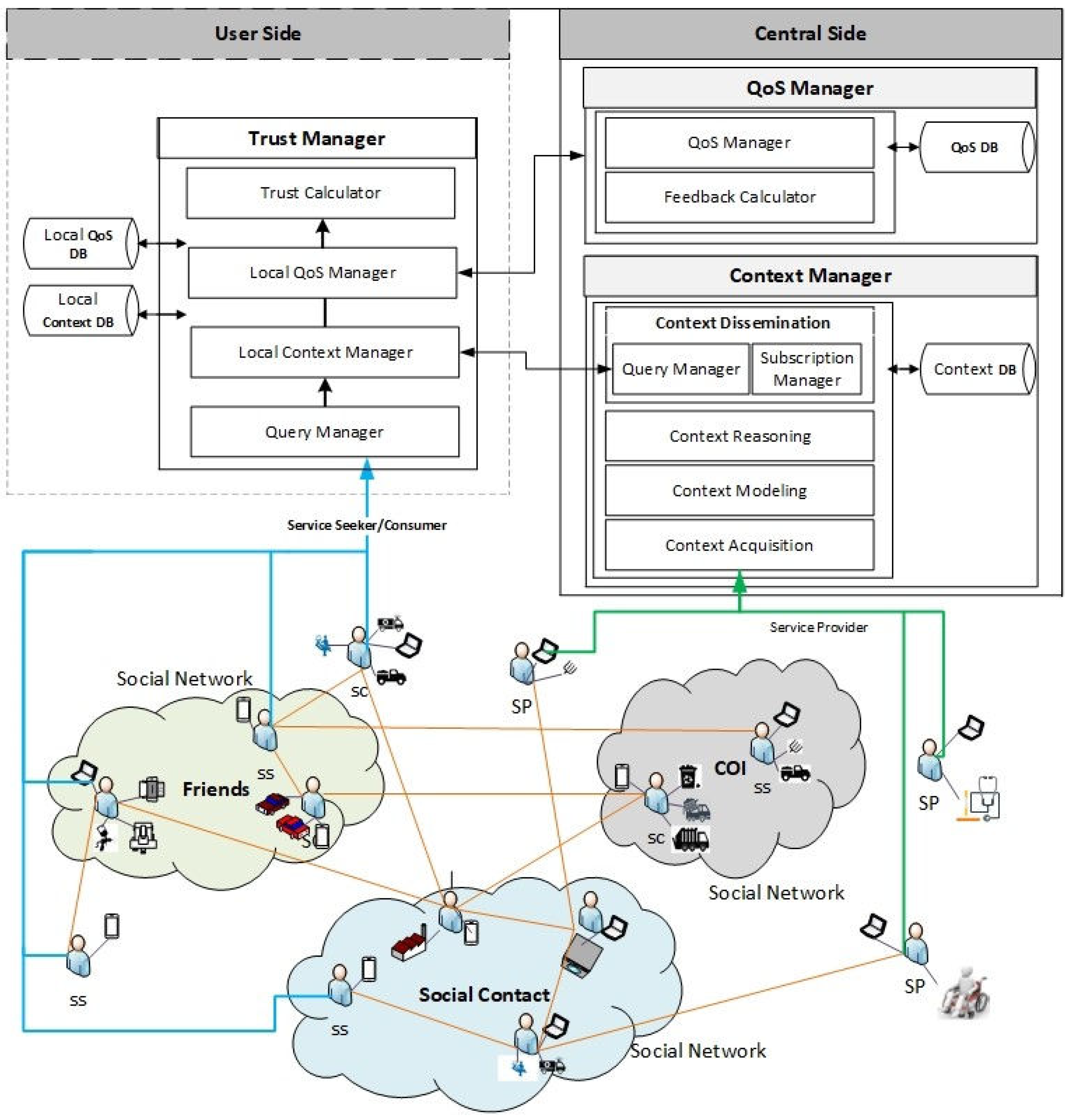
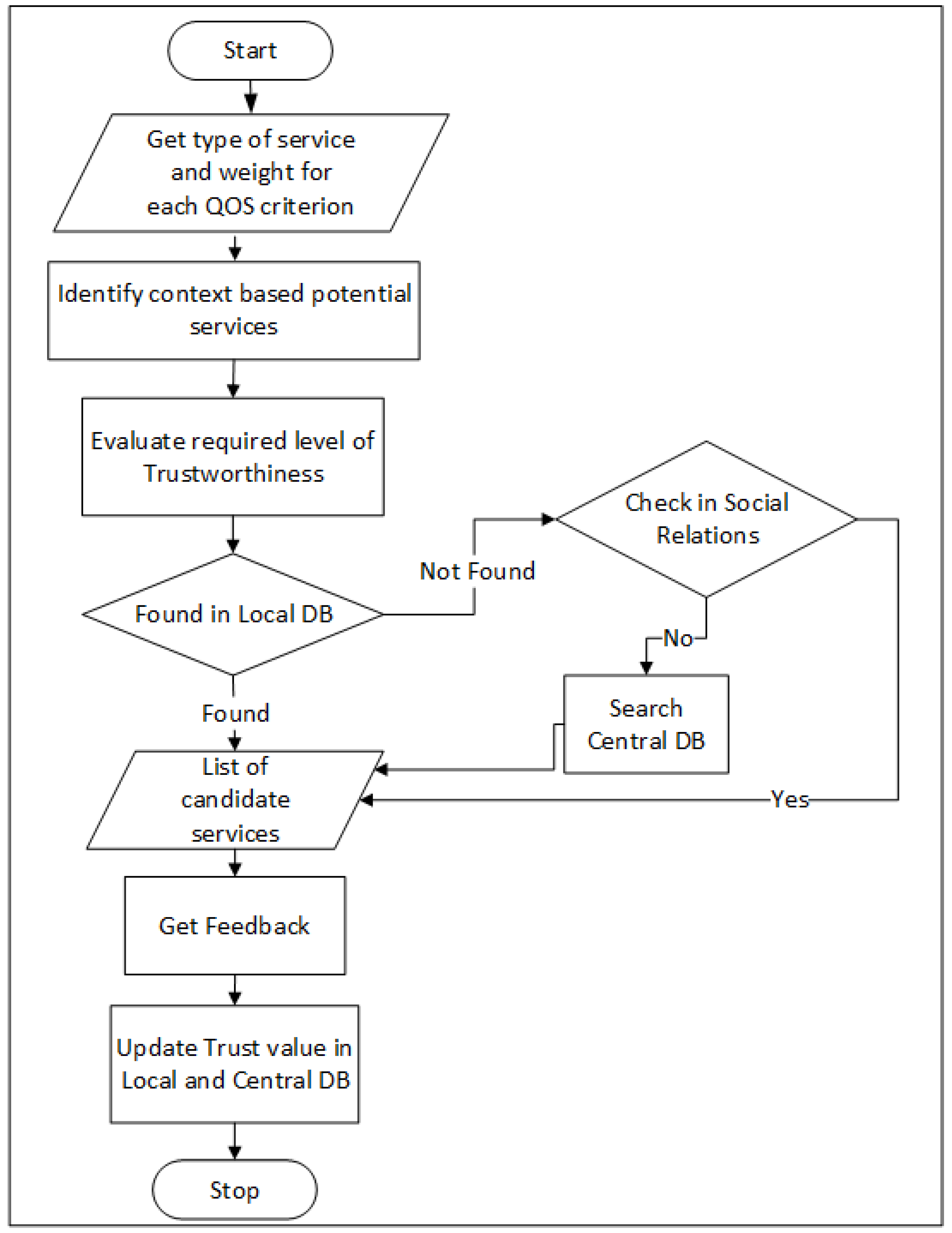
- The CATSWoTS is an encouraging step towards the settlement of trustworthy recommendations of IoT services provided either by a social circle or by a third party. The system also considers the self-experience and the recommendation of a centralized level.The authentication and authorization mechanism makes the system security as it limits the access to trusted contacts only.
- To evaluate and measure the trustworthiness of service, a rule-based collaborative filtering technique is proposed by identifying and integrating the various criteria of context and QoS in Social Web of Things. After recommending a service, feedback is also collected from a service consumer to update the trustworthy level of the consumed service which is then stored to help other service seekers.
- The experiments are conducted on a real dataset of 2507 services to evaluate the performance of the CATSWoTS. The results show that the proposed technique recommends trustworthy services by fulfilling the criteria of QoS and context awareness of a service seeker with great accuracy.
2. Background Study
2.1. Preliminary Concepts
2.2. Trust Management Systems
3. Context Aware QoS Trust Management
3.1. Users and Relations
3.1.1. Types of Users
3.1.2. Types of Social Relations
3.2. Trust Management
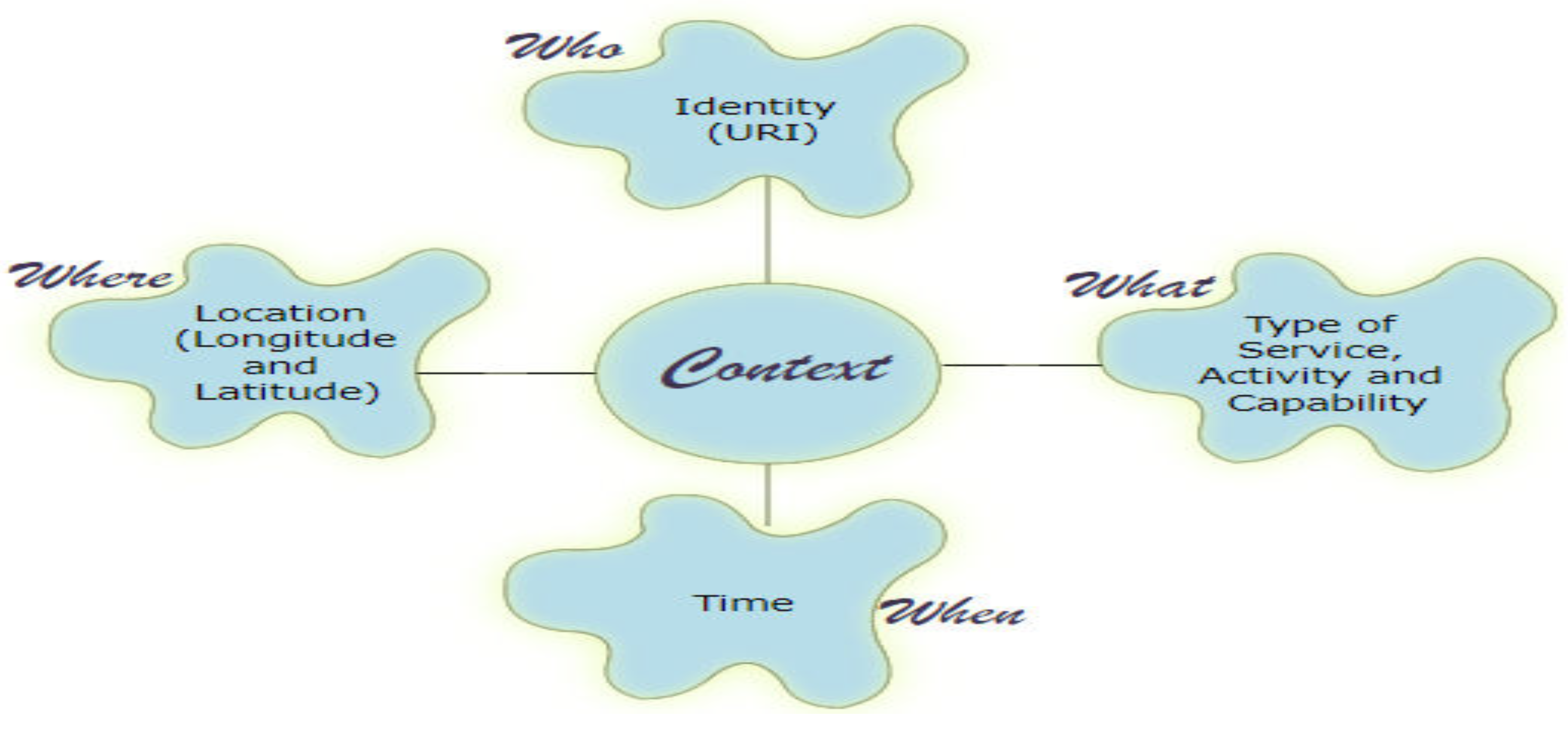
3.2.1. Context Manager
| Algorithm 1 Services identification based on context |
|
3.2.2. Social Relations
3.2.3. QoS Manager
| Algorithm 2 Services identification based on QoS |
|
- Evaluation of services based on QoS criteria,
- Feedback calculation and updating the record.
4. Experimental Validation and Results Discussion
- A central server where a context manager and a QoS manager resides. An SP may register the services there.
- The nodes that may play the role of service providers and service consumers as well. These nodes are also connected through a peer to peer network. Each node has two local managers for context, QoS and trust management. It has its own local database on which the profiles of consumed services are maintained.
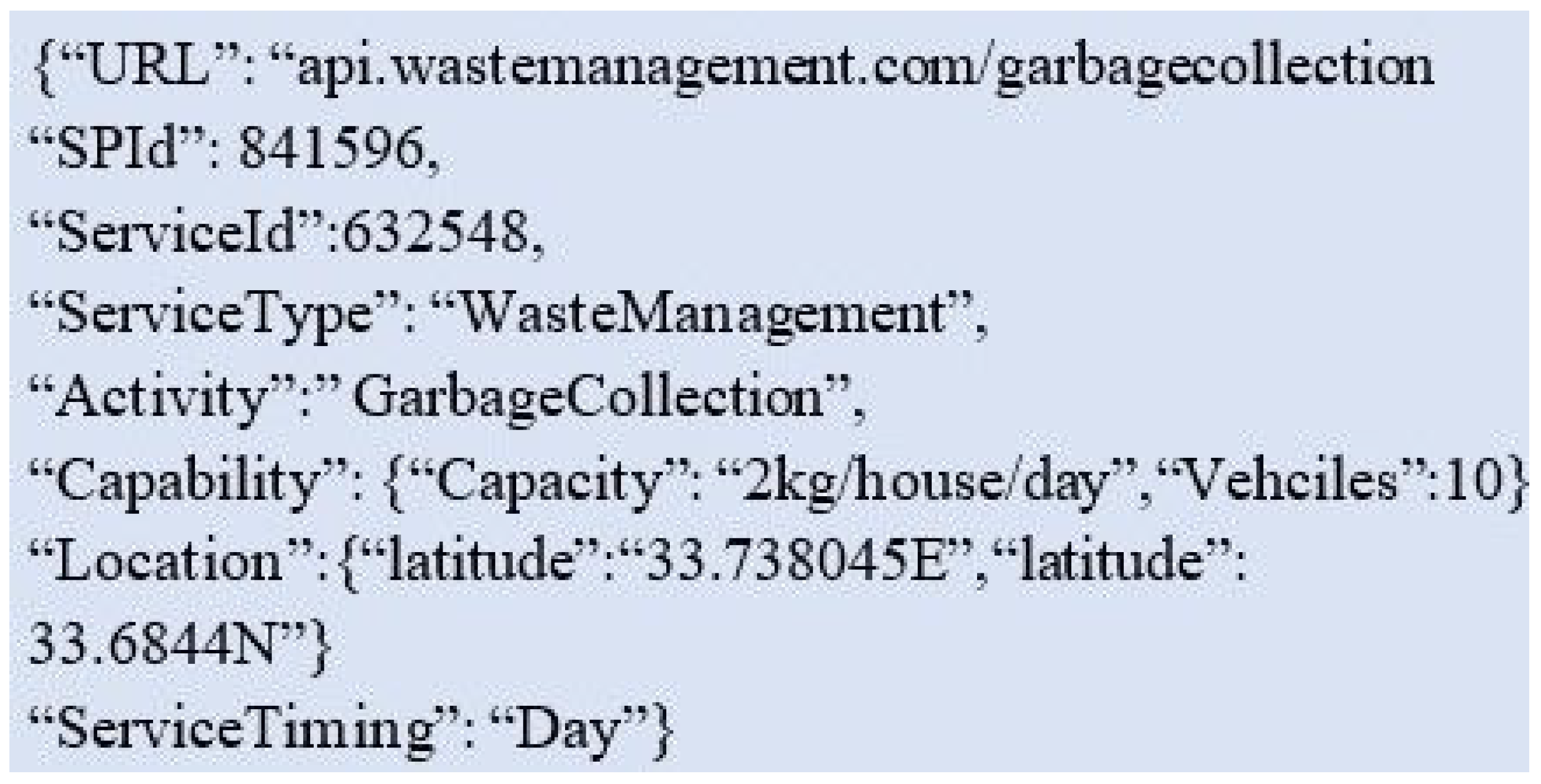
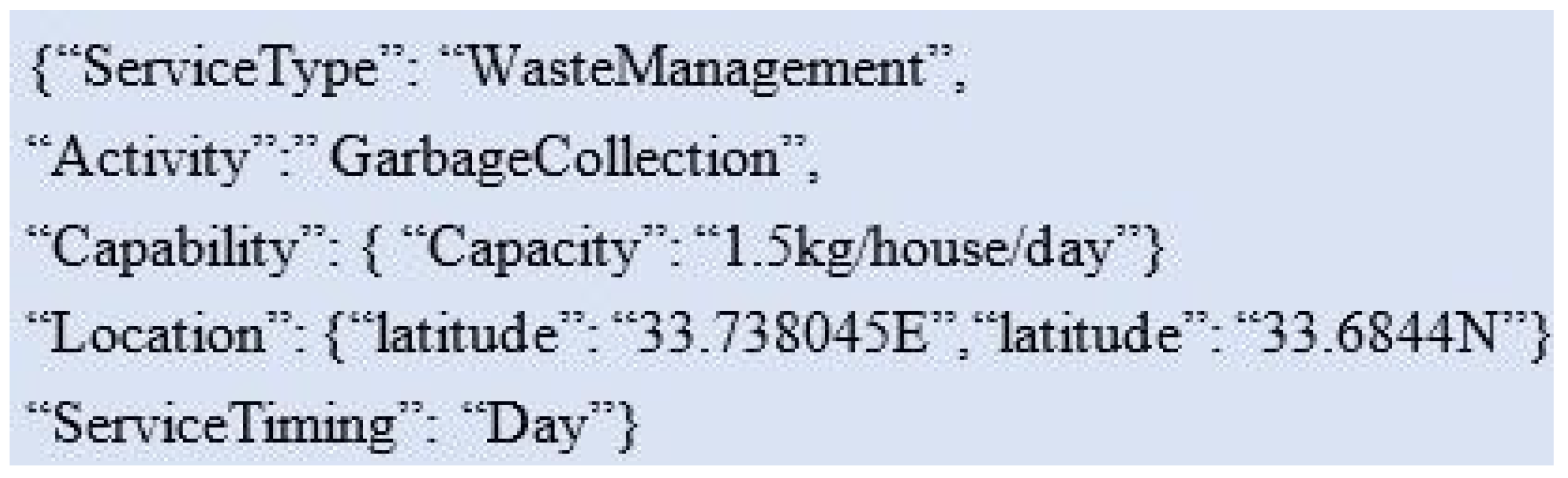
- Capacity: A set of attributes defining the capacity of any service may include battery power, processing speed, memory, and another service-related capability. For example, Alice wants the garbage collection services of IoT based waste management company. In this case, the attributes may include smart bin’s capacity to contain garbage in kilograms, battery, processing power and memory of sensors and actuators that constantly monitor the level of garbage in the bin and then intimate the SP when it needs to empty the bin. However, to keep the attribute simple and generic for testing purposes, three levels of capacity are defined which are (i) low, (ii) medium (iii) and high.
- Location: Location, where the services are provided, is described in terms of longitude and latitude.
- Time: the timings of services are described as (i) morning, (ii) noon (iii) evening and (iv) 24 h like the waste management company may provide the services in the morning but Alice wants the services in the noon then Alice is in the search of an SP which offers the services in noon.
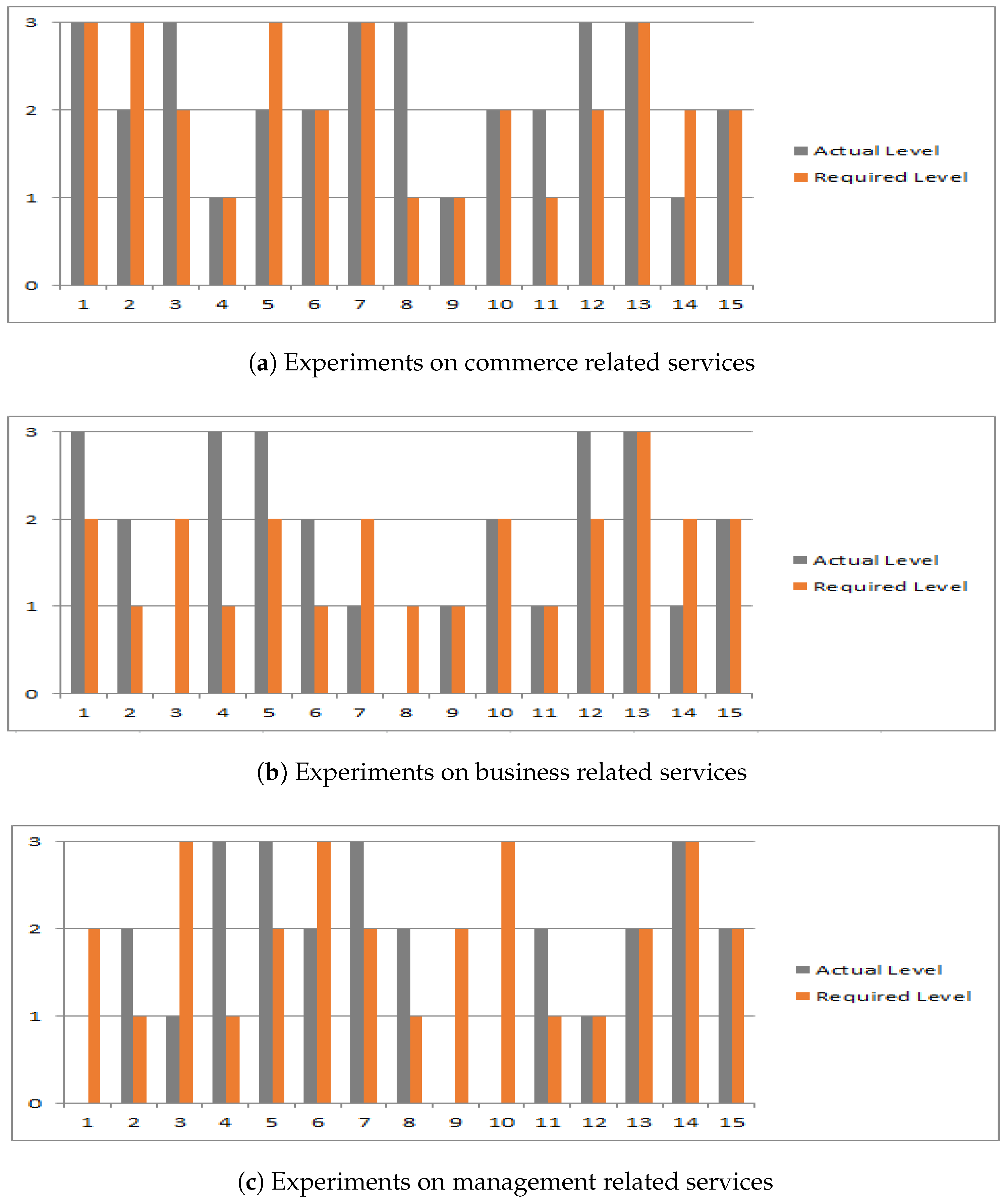
4.1. Effect of Context Aware Attributes
4.2. Effect of QoS Constraints
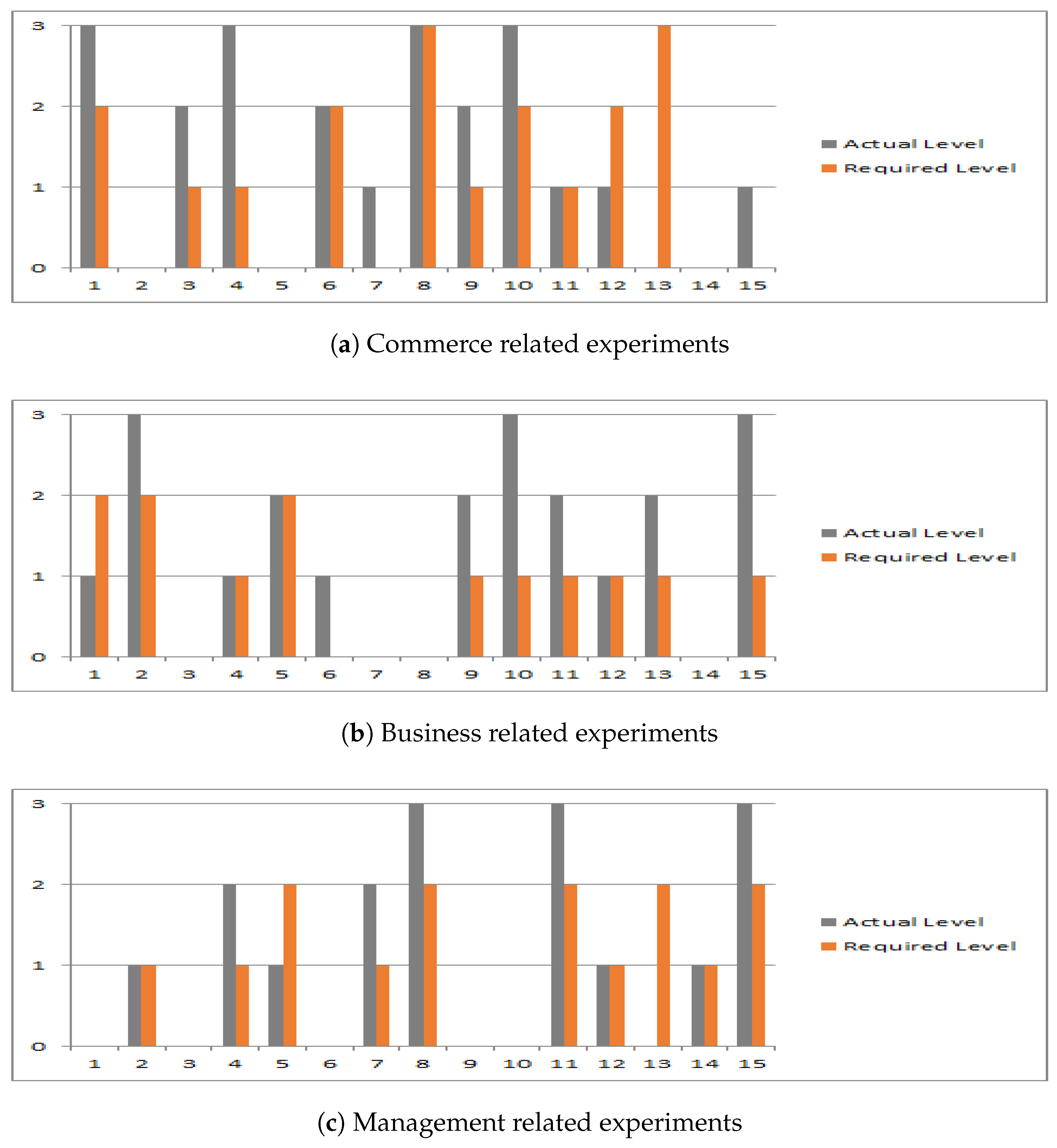
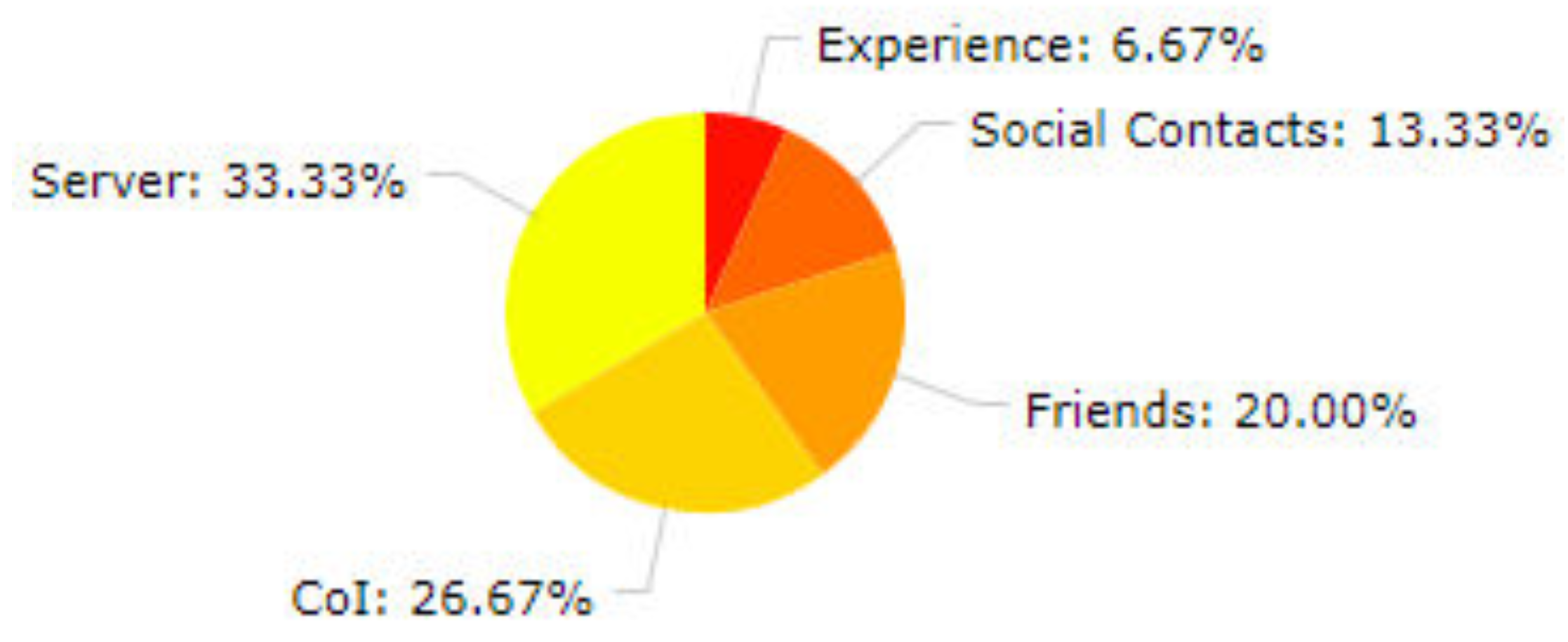
4.3. Effect of Social Relations
| Algorithm 3 Interaction between the nodes |
|
4.4. Comparison with State of the Art
5. Conclusions and Future Work
Author Contributions
Funding
Conflicts of Interest
References
- Chen, R.; Bao, F.; Guo, J. Trust-based service management for social internet of things systems. IEEE Trans. Dependable Secur. Comput. 2016, 13, 684–696. [Google Scholar] [CrossRef]
- Kamilaris, A. Enabling Smart Homes Using Web Technologies. Ph.D. Thesis, University of Cyprus, Nicosia, Cyprus, 2013. [Google Scholar]
- Chen, R.; Guo, J.; Bao, F. Trust management for soa-based iot and its application to service composition. IEEE Trans. Serv. Comput. 2016, 9, 482–495. [Google Scholar] [CrossRef]
- Varga, P.; Blomstedt, F.; Ferreira, L.; Eliasson, J.; Johansson, M.; Delsing, J.; de Soria, I. Making system of systems interoperable—The core components of the arrowhead framework. J. Netw. Comput. Appl. 2017, 81, 85–95. [Google Scholar] [CrossRef]
- Perera, C.; Zaslavsky, A.; Christen, P.; Georgakopoulos, D. Context aware computing for the internet of things: A survey. IEEE Commun. Surv. Tutor. 2014, 16, 414–454. [Google Scholar] [CrossRef]
- Atzori, L.; Iera, A.; Morabito, G. The internet of things: A survey. Comput. Netw. 2010, 54, 2787–2805. [Google Scholar] [CrossRef]
- Atzori, L.; Iera, A.; Morabito, G.; Nitti, M. The social internet of things (siot)–when social networks meet the internet of things: Concept, architecture and network characterization. Comput. Netw. 2012, 56, 3594–3608. [Google Scholar] [CrossRef]
- Usman, M.; Zhang, X.; Chiroma, H.; Abubakar, A.; Gital, A. A framework for realizing universal standardization for internet of things. J. Ind. Intell. Inf. 2014, 2, 147–153. [Google Scholar] [CrossRef]
- Guinard, D.; Trifa, V.; Mattern, F.; Wilde, E. From the internet of things to the web of things: Resource-oriented architecture and best practices. In Architecting the Internet of Things; Springer: Berlin, Germany, 2011; pp. 97–129. [Google Scholar]
- Atzori, L.; Iera, A.; Morabito, G. “From” smart objects to social objects: The next evolutionary step of the internet of things. IEEE Commun. Mag. 2014, 52, 97–105. [Google Scholar] [CrossRef]
- Andročec, D.; Novak, M.; Oreški, D. Using semantic web for internet of things interoperability: A systematic review. Int. J. Semant. Web Inf. Syst. (IJSWIS) 2018, 14, 147–171. [Google Scholar] [CrossRef]
- Aftab, S.; Afzal, H.; Khalid, A. An approach for secure semantic data integration at data as a service (daas) layer. Int. J. Inf. Educ. Technol. 2015, 5, 124. [Google Scholar] [CrossRef]
- Javaid, S.; Majeed, A.; Afzal, H. A reputation management system for efficient selection of disaster management team. In Proceedings of the 2013 15th International Conference on Advanced Communications Technology (ICACT), PyeongChang, Korea, 27–30 January 2013; pp. 829–834. [Google Scholar]
- Guo, J.; Chen, R.; Tsai, J. A survey of trust computation models for service management in internet of things systems. Comput. Commun. 2017, 97, 1–14. [Google Scholar] [CrossRef]
- Li, C.; Palanisamy, B. Privacy in internet of things: from principles to technologies. IEEE Internet Things J. 2019, 6, 488–505. [Google Scholar] [CrossRef]
- Sato, H.; Kanai, A.; Tanimoto, S.; Kobayashi, T. Establishing trust in the emerging era of iot. In Proceedings of the 2016 IEEE Symposium on Service-Oriented System Engineering (SOSE), Oxford, UK, 29 March–2 April 2016; pp. 398–406. [Google Scholar]
- Bao, F.; Chen, I.-R. Dynamic trust management for internet of things applications. In Proceedings of the 2012 International Workshop on Self-Aware Internet of Things, San Jose, CA, USA, 17 September 2012; pp. 1–6. [Google Scholar]
- Ning, H.; Liu, H. Cyber-physical-social based security architecture for future internet of things. Adv. Internet Things 2012, 2, 1. [Google Scholar] [CrossRef]
- Roman, R.; Zhou, J.; Lopez, J. On the features and challenges of security and privacy in distributed internet of things. Comput. Netw. 2013, 57, 2266–2279. [Google Scholar] [CrossRef]
- Kothmayr, T.; Schmitt, C.; Hu, W.; Brünig, M.; Carle, G. Dtls based security and two-way authentication for the internet of things. Ad Hoc Netw. 2013, 11, 2710–2723. [Google Scholar] [CrossRef]
- Kumar, S.; Anouncia, S. Qos-based concurrent user-service grouping for web service recommendation. Autom. Control Comput. Sci. 2018, 52, 220–230. [Google Scholar] [CrossRef]
- Saied, Y.; Olivereau, A.; Zeghlache, D.; Laurent, M. Trust management system design for the internet of things: A context-aware and multi-service approach. Comput. Secur. 2013, 39, 351–365. [Google Scholar] [CrossRef]
- Perera, C.; Zaslavsky, A.; Christen, P.; Georgakopoulos, D. Ca4iot: Context awareness for internet of things. In Proceedings of the 2012 IEEE International Conference on Green Computing and Communications (GreenCom), Besancon, France, 20–23 November 2012; pp. 775–782. [Google Scholar]
- Urbieta, A.; González-Beltrán, A.; Mokhtar, S.; Hossain, M.; Capra, L. Adaptive and context-aware service composition for iot-based smart cities. Future Gener. Comput. Syst. 2017, 76, 262–274. [Google Scholar] [CrossRef]
- D’Angelo, G.; Rampone, S.; Palmieri, F. Developing a trust model for pervasive computing based on apriori association rules learning and bayesian classification. Soft Comput. 2017, 21, 6297–6315. [Google Scholar] [CrossRef]
- Wang, Y.; Li, L.; Liu, G. Social context-aware trust inference for trust enhancement in social network based recommendations on service providers. World Wide Web 2015, 18, 159–184. [Google Scholar] [CrossRef]
- Rostamzadeh, K.; Nicanfar, H.; Torabi, N.; Gopalakrishnan, S.; Leung, V. A context-aware trust-based information dissemination framework for vehicular networks. IEEE Internet Things J. 2015, 2, 121–132. [Google Scholar] [CrossRef]
- Lin, J.-W.; Fournier-Viger, P.; Wu, L.; Gan, W.; Djenouri, Y.; Zhang, J. Ppsf: An open-source privacy-preserving and security mining framework. In Proceedings of the 2018 IEEE International Conference on Data Mining Workshops (ICDMW), Singapore, 17–20 November 2018; pp. 1459–1463. [Google Scholar]
- De Meo, P.; Messina, F.; Postorino, M.; Rosaci, D.; Sarné, G. A reputation framework to share resources into iot-based environments. In Proceedings of the 2017 IEEE 14th International Conference on Networking, Sensing and Control (ICNSC), Calabria, Italy, 16–18 May 2017; pp. 513–518. [Google Scholar]
- Rafey, S.; Abdel-Hamid, A.; El-Nasr, M. Cbstm-iot: Context-based social trust model for the internet of things. In Proceedings of the 2016 International Conference on Selected Topics in Mobile & Wireless Networking (MoWNeT), Cairo, Egypt, 11–13 April 2016; pp. 1–8. [Google Scholar]
- Bernabe, J.; Ramos, J.; Gomez, A. Taciot: Multidimensional trust-aware access control system for the internet of things. Soft Comput. 2016, 20, 1763–1779. [Google Scholar] [CrossRef]
- Zhou, W.; Jia, Y.; Peng, A.; Zhang, Y.; Liu, P. The effect of iot new features on security and privacy: New threats, existing solutions, and challenges yet to be solved. IEEE Internet Things J. 2018, 6, 1606–1616. [Google Scholar] [CrossRef]
- Lin, J.-W.; Wu, J.-T.; Fournier-Viger, P.; Djenouri, Y.; Chen, C.-H.; Zhang, Y. A sanitization approach to secure shared data in an iot environment. IEEE Access 2019, 7, 25359–25368. [Google Scholar] [CrossRef]
- Lin, J.-W.; Zhang, Y.; Zhang, B.; Fournier-Viger, P.; Djenouri, Y. Hiding sensitive itemsets with multiple objective optimization. In Soft Computing; Springer: Berlin/Heidelberg, Germany, 2019; pp. 1–19. [Google Scholar]
- Frustaci, M.; Pace, P.; Aloi, G.; Fortino, G. Evaluating critical security issues of the iot world: Present and future challenges. IEEE Internet Things J. 2017, 5, 2483–2495. [Google Scholar] [CrossRef]
- Rangarajan, S. Qos-Based Web Service Discovery and Selection Using Machine Learning. arXiv 2018, arXiv:1807.01439. [Google Scholar] [CrossRef]
- Modi, K.; Garg, S. Dynamic web services composition using optimization approach. Int. J. Comput. Sci. Commun. 2015, 6, 285–293. [Google Scholar]
- Al-Masri, E.; Mahmoud, Q.H. The Qws Dataset. Available online: http://www.uoguelph.ca/~qmahmoud/qws/dataset/ (accessed on 12 November 2018).
- Javaid, S.; Afzal, H.; Babar, M.; Arif, F.; Tan, Z.; Jan, M. ARCA-IoT: An Attack-Resilient Cloud-Assisted IoT System. IEEE Access. 2019, 7, 19616–19630. [Google Scholar] [CrossRef]
| QoS Constraints | Definition |
|---|---|
| Reliability | Reliability degree for service |
| Availability | Existence and availability of the service. |
| Latency | The interval between stimulation and response |
| Reputation | Feedback score is given by service consumers to a web service |
| Prev Work | Authenticity, Privacy or Security | Availability and Reliability | Social Recommendations | Context Aware |
|---|---|---|---|---|
| [16] | Yes | No | No | No |
| [17] | No | No | To some extent | No |
| [18] | Yes | To some extent | No | No |
| [20] | Yes | No | No | No |
| [22] | No | Yes | No | only capability, type |
| [23] | No | No | No | Yes |
| [24] | No | No | No | Yes |
| [26] | No | No | Yes | Yes |
| [27] | Yes | No | No | Yes |
| [31] | Yes | Yes | Yes | No |
| CATSWoTS | Yes | Yes | Yes | Yes |
© 2019 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Javaid, S.; Afzal, H.; Arif, F.; Iltaf, N.; Abbas, H.; Iqbal, W. CATSWoTS: Context Aware Trustworthy Social Web of Things System. Sensors 2019, 19, 3076. https://doi.org/10.3390/s19143076
Javaid S, Afzal H, Arif F, Iltaf N, Abbas H, Iqbal W. CATSWoTS: Context Aware Trustworthy Social Web of Things System. Sensors. 2019; 19(14):3076. https://doi.org/10.3390/s19143076
Chicago/Turabian StyleJavaid, Sabeen, Hammad Afzal, Fahim Arif, Naima Iltaf, Haider Abbas, and Waseem Iqbal. 2019. "CATSWoTS: Context Aware Trustworthy Social Web of Things System" Sensors 19, no. 14: 3076. https://doi.org/10.3390/s19143076
APA StyleJavaid, S., Afzal, H., Arif, F., Iltaf, N., Abbas, H., & Iqbal, W. (2019). CATSWoTS: Context Aware Trustworthy Social Web of Things System. Sensors, 19(14), 3076. https://doi.org/10.3390/s19143076





