Hierarchical Name-Based Mechanism for Push-Data Broadcast Control in Information-Centric Multihop Wireless Networks
Abstract
:1. Introduction
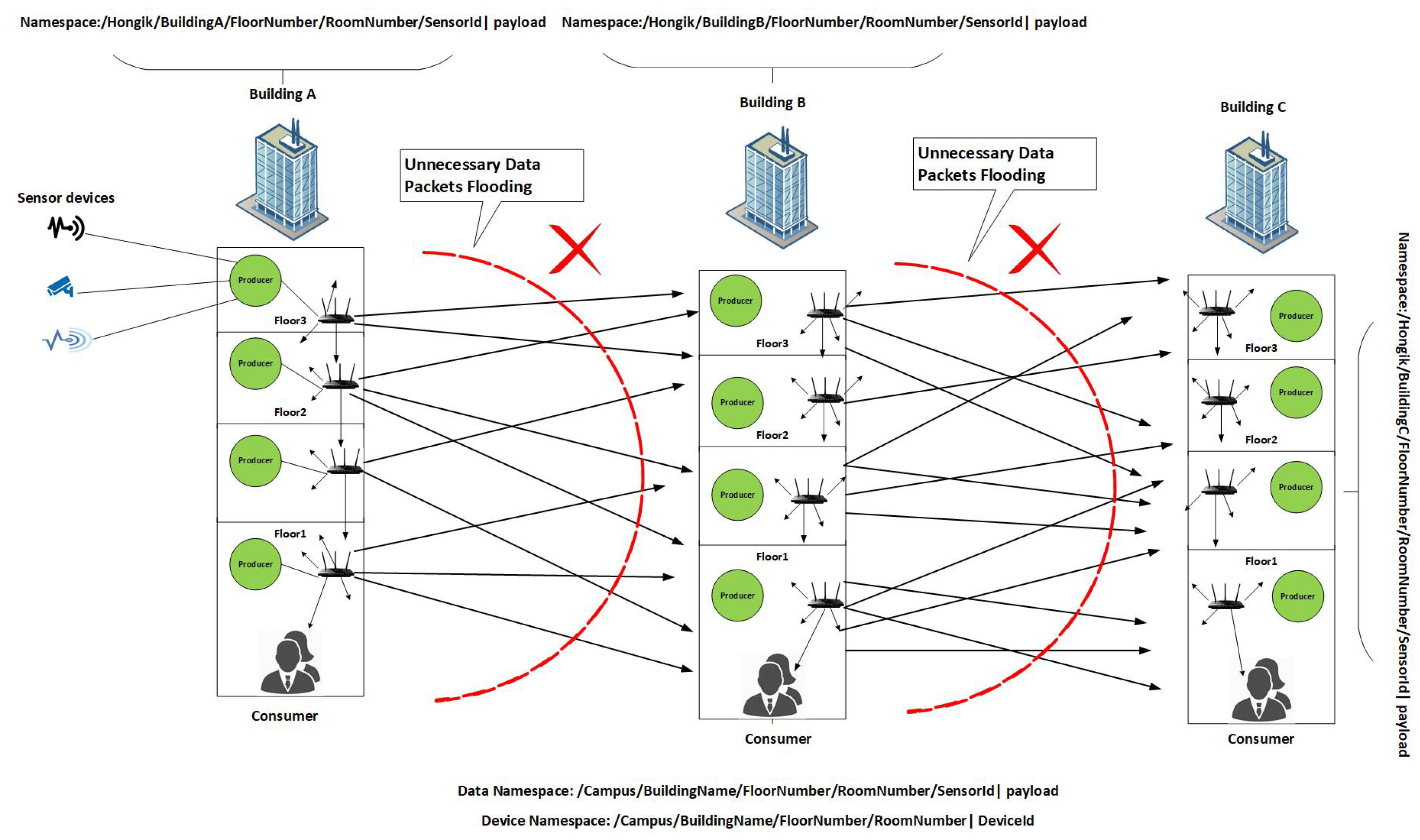
- A robust content namespace design and device namespace design for smart building to control the data packets flooding , thereby reducing the congestion in the network.
- A robust content namespace design and vehicle namespace design for Vehicular NDN to control the data packets flooding.
- Enable efficient data packet transfer to the appropriate consumer thereby reducing load on the network, minimizing energy consumption, and increasing throughput in the network.
- Enhanced the conventional data packet format for marking the alert types in case of various emergency situations.
- For evaluation of our scheme we consider two use cases (a) smart building case with static Mobile wireless nodes (b) VNDNs
- Simulations in ndnSIM to check the performance of the proposed scheme with relevant schemes in terms of total number of data packets processed/forwarded in the network, total energy consumption by all nodes in the network and average delay.
2. Background and Overview
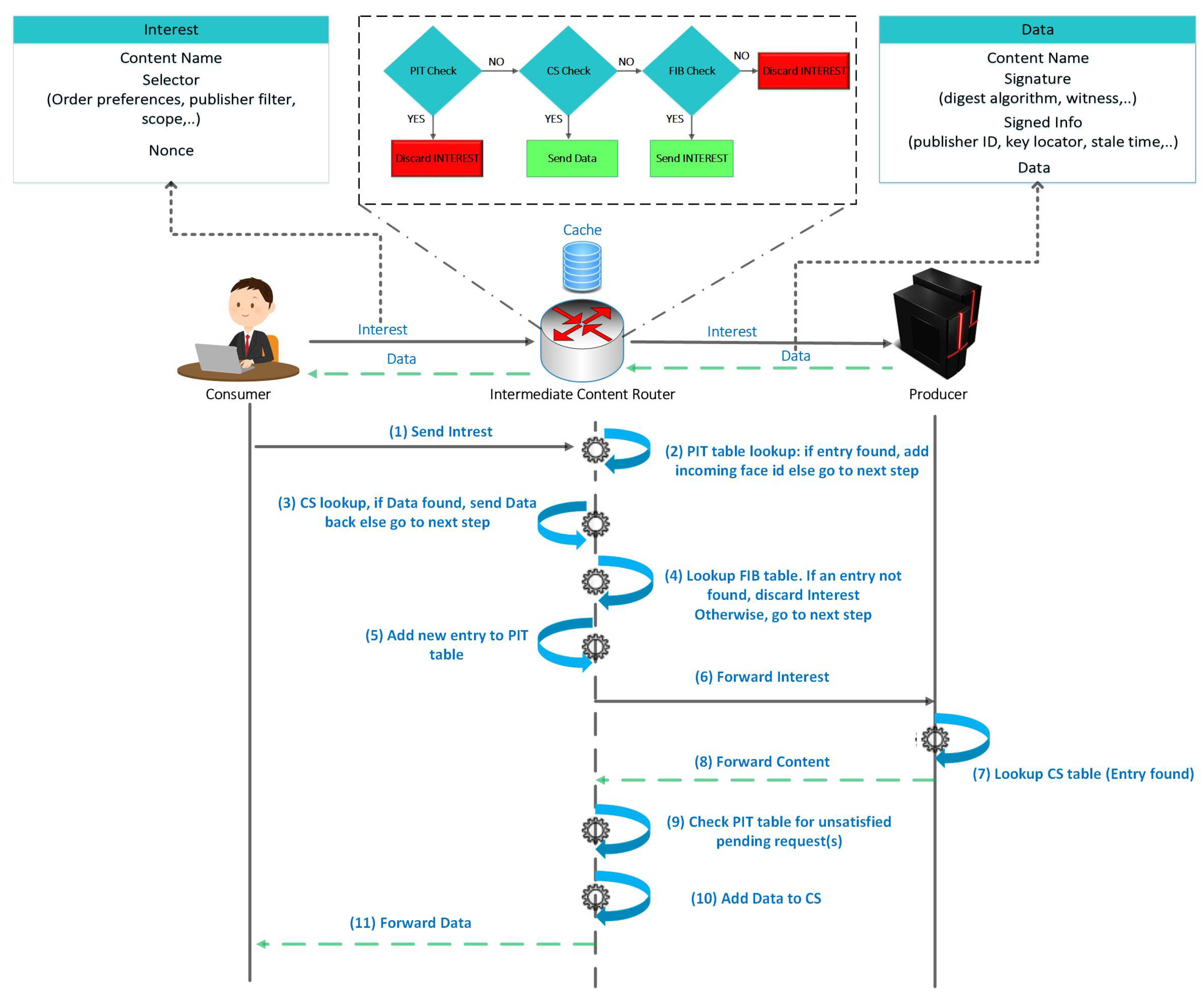
2.1. NDN in a Nutshell
2.2. The NDN forwarding Plane
3. Challenges of IoT Network Architecture and Importance of ICN for IoT
3.1. Scalability
3.2. Caching
3.3. Receiver Driven Communication
3.4. Mobility
3.5. Security
3.6. Reliability
4. Related Work and Limitations
5. Proposed Scheme
5.1. Motivation
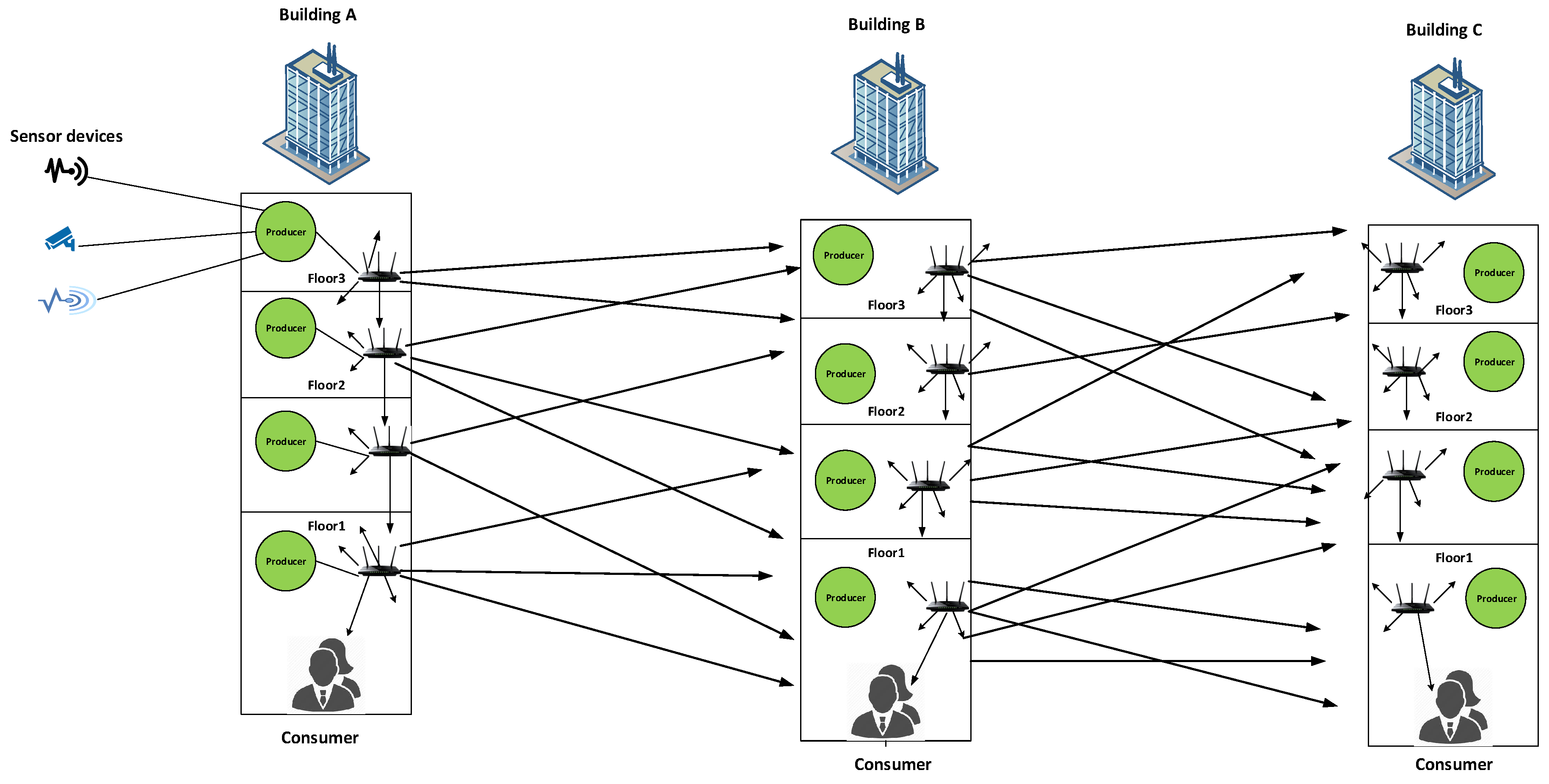
5.2. Proposed Scheme Description
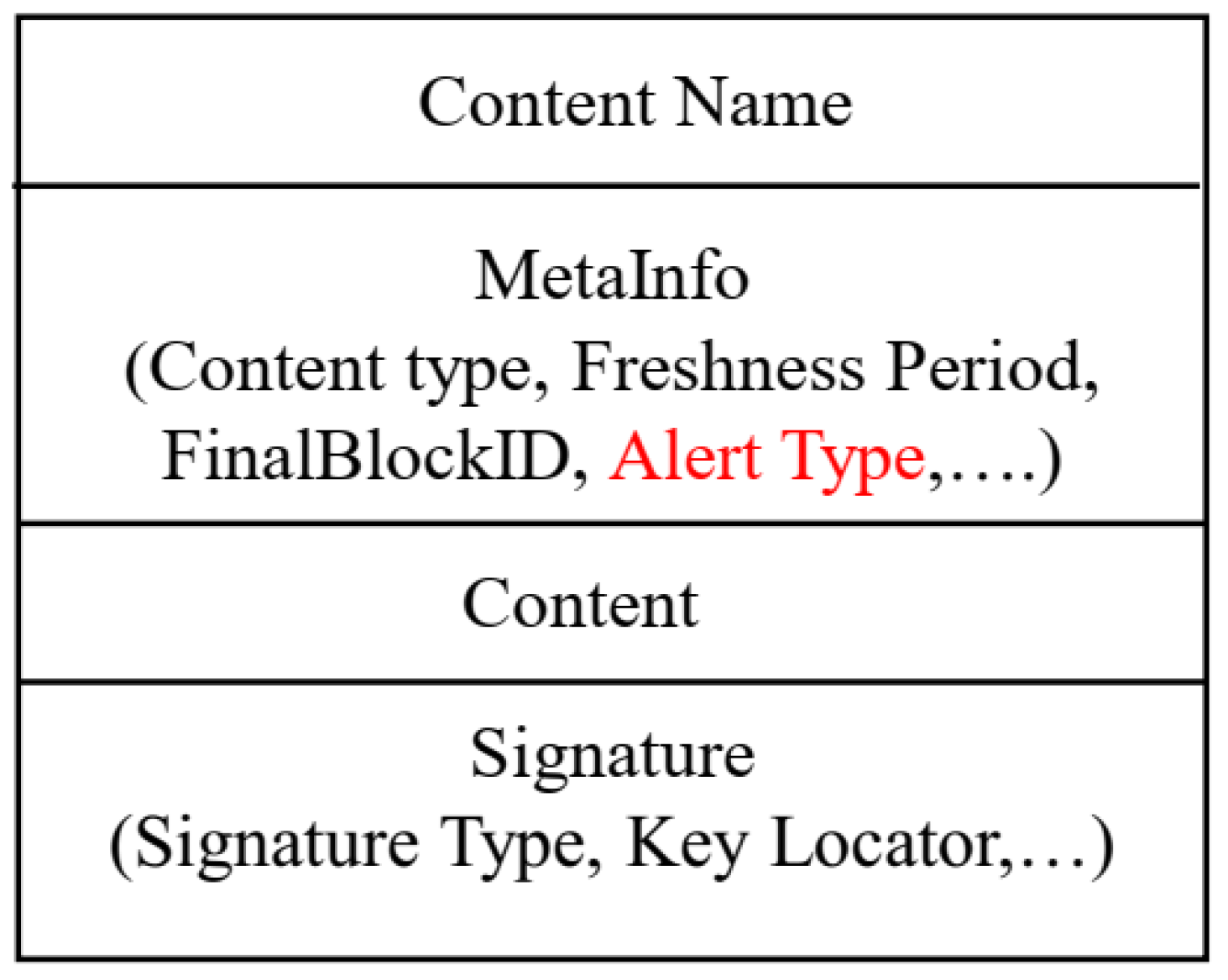
5.2.1. Enhanced Data Packet Format
5.2.2. Data/Content Namespace Design
5.2.3. Device Namespace Design
| Algorithm 1 Received data packet in the Proposed Push-based Scheme for Building Scenario |
| procedure Received [Name, MetaInfo, Data, Signature] Check PIT for Unsolicited Data if (Data is Unsolicited()) then First two components of Data; First two components of Device; if (Data.Name equals Device.Name ) then else end if else if (If face is application) then else end if end if end procedure |
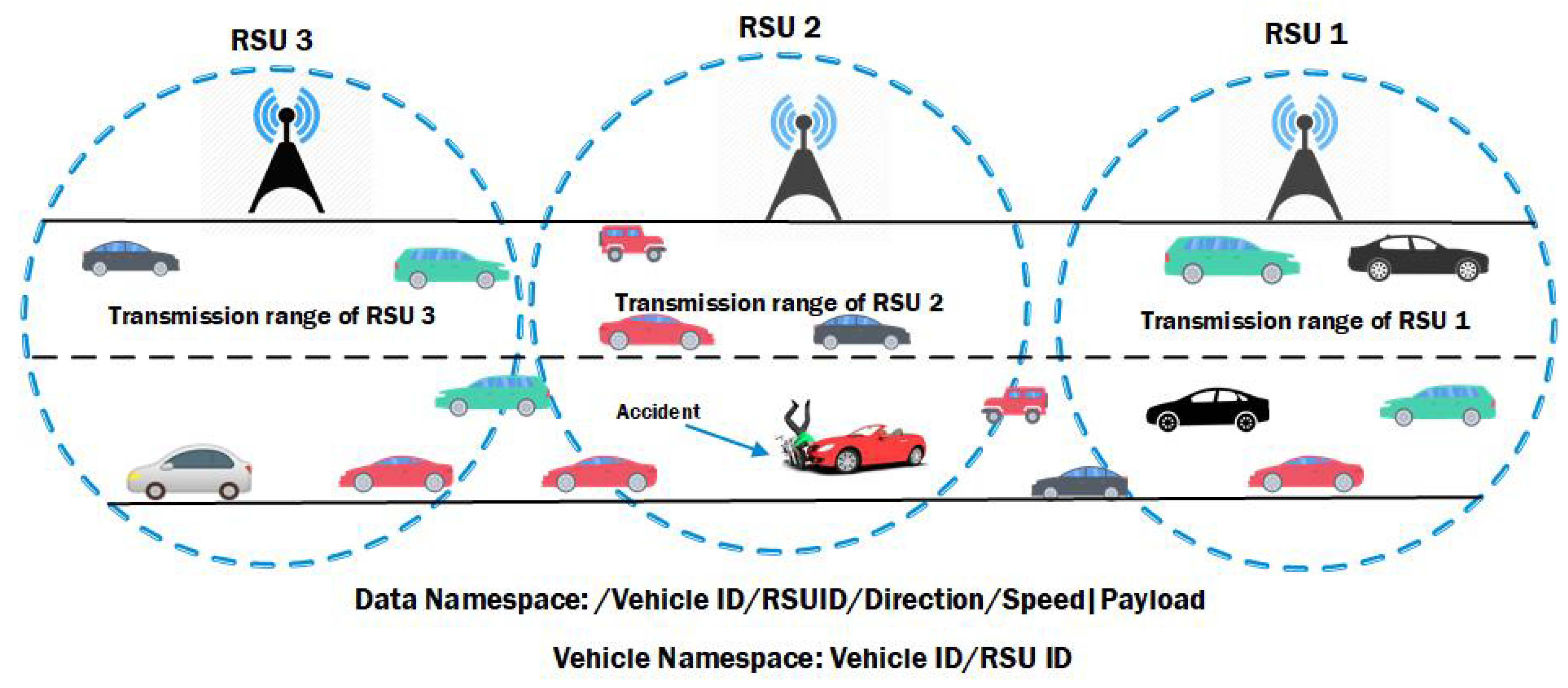
5.3. Proposed Scheme for Vehicular Scenario
- -
- In the realistic scenario, when an accident happens, then the producer node (accidental vehicle) start sending emergency messages to the nearby RSU. Therefore, the producer node in case of an accident must be immovable due to an accident. However, authors in [37] claimed that the producer node is mobile and sending emergency notifications to the nearest RSU, which is not a realistic case. In our scheme the producer node is immovable and sends emergency information to all the intermediate vehicles.
- -
- As the vehicles in VANETs are mobile and move with a certain speed. Therefore, the intermittent connectivity happens between nodes. During mobility, the vehicles quickly move out of the range easily. The authors in [37] did not define how to cope with this issue. In their scheme, the beacons are sent for making synthetic PIT entries on nodes for subsequent data arrival; however, they did not define a certain time of how long the vehicle may stay in a specific region. That means if a beacon reaches to a vehicle in order to make PIT entry, the vehicle may move out of the range after some time. In that case, the subsequent data packet will be considered to be unsolicited and will be dropped. If there is not a certain time defined for beacons and vehicles, then the purpose of sending beacons for making PIT entries are useless and it works only for static cases. This issue is addressed by [38] where authors defined a certain link layer threshold. If that threshold meets then the packet will be processed. Otherwise vehicles will not forward packets, since the vehicle may not connect or may not in the range. In our scheme, we use the scheme defined in [38] to deal with intermittent connectivity due to fast mobility of vehicles.
- -
- Moreover, in [37] the beacons are sent in a broadcast manner which increases the broadcast storm in the network. According to the NDN rituals the beacons will also be considered to be interest or data packets. In our case, our scheme requires neither any synthetic PIT entries nor any additional beacon messages.
5.3.1. Proposed Scheme Description
5.3.2. Data and Vehicle Namespace Design for VNDNs
| Algorithm 2 Received data packet in the Proposed Push-based Scheme for VNDNs |
| procedure Received [Name, MetaInfo, Data, Signature] Check PIT for Unsolicited Data if (Data is Unsolicited()) then Second component of Data; Second component of Vehicle; if (Data.Name equals Vehicle.Name ) then else end if else if (If face is application) then else end if end if end procedure |
6. Performance Evaluations
6.1. Performance Evaluation Metrics
6.1.1. Number of Data Packets Processed (DPP)
6.1.2. Total Energy Consumption
6.1.3. Average Delay
6.2. Simulation Environment: Smart Building Scenario
6.3. Performance Analysis
6.3.1. Total Number of Data Packets Processed in Static Environment
6.3.2. Total Number of Data Packets Processed in Mobile Environment
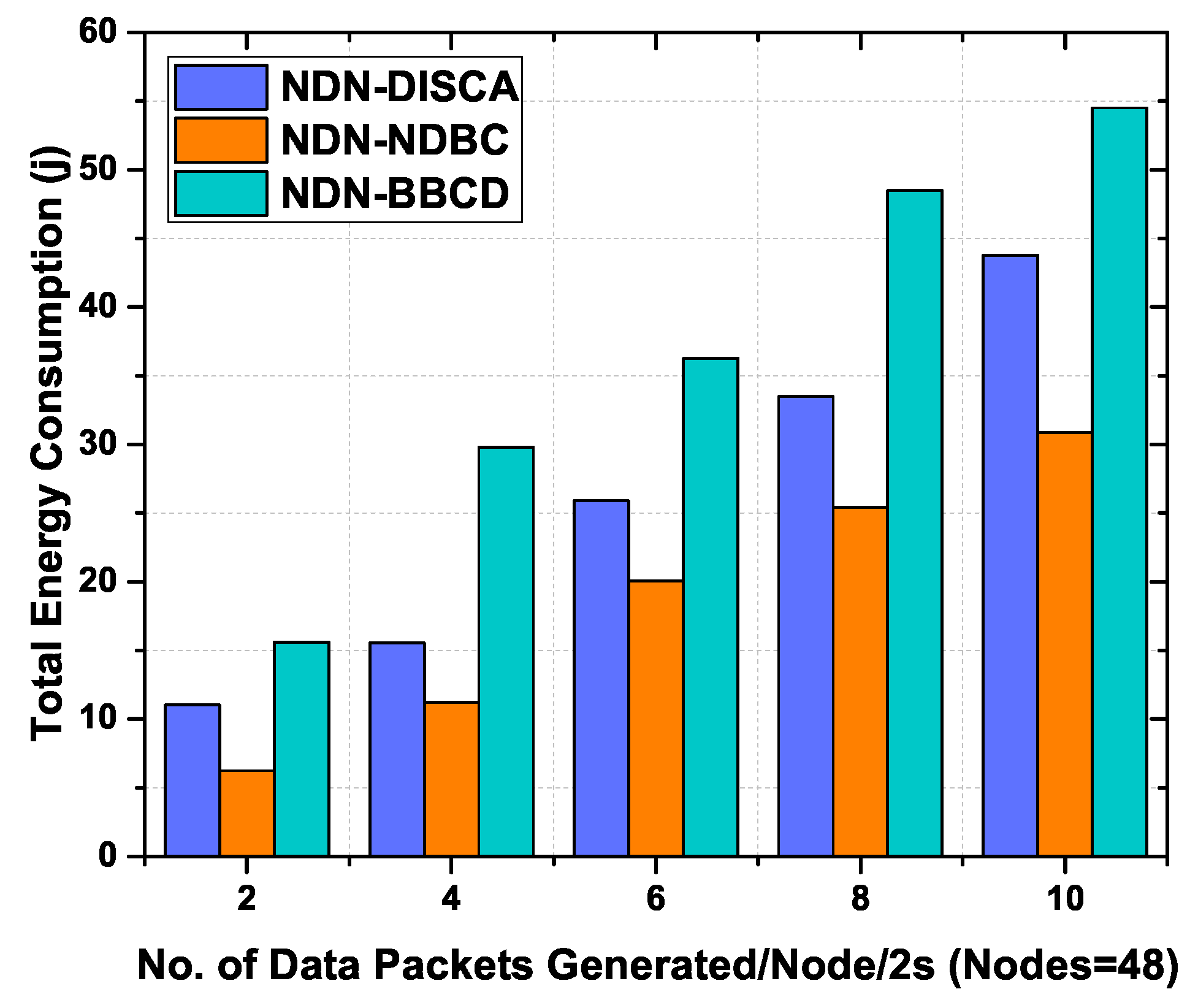
6.3.3. Total Energy Consumption in Static Environment
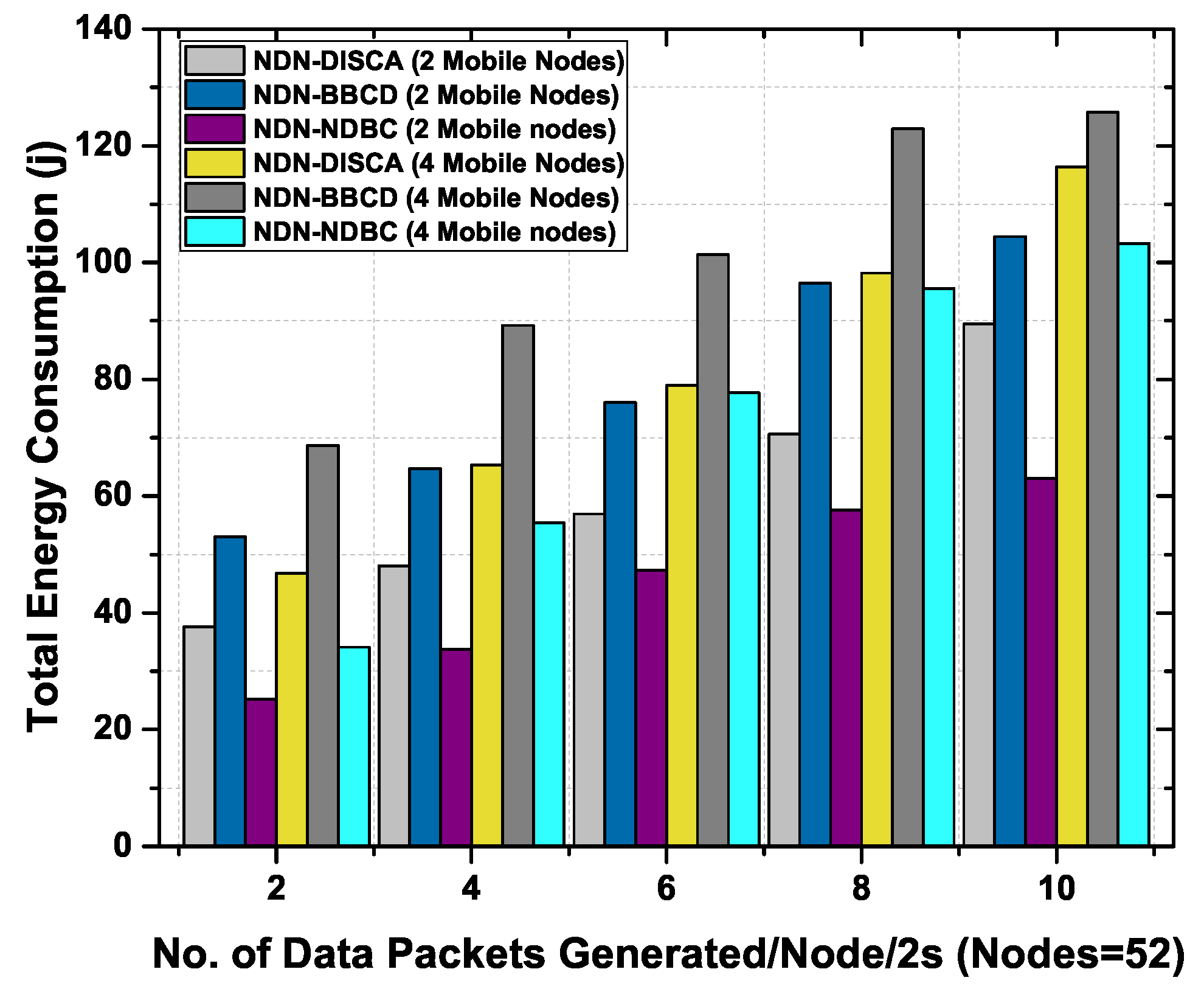
6.3.4. Total Energy Consumption in Mobile Environment
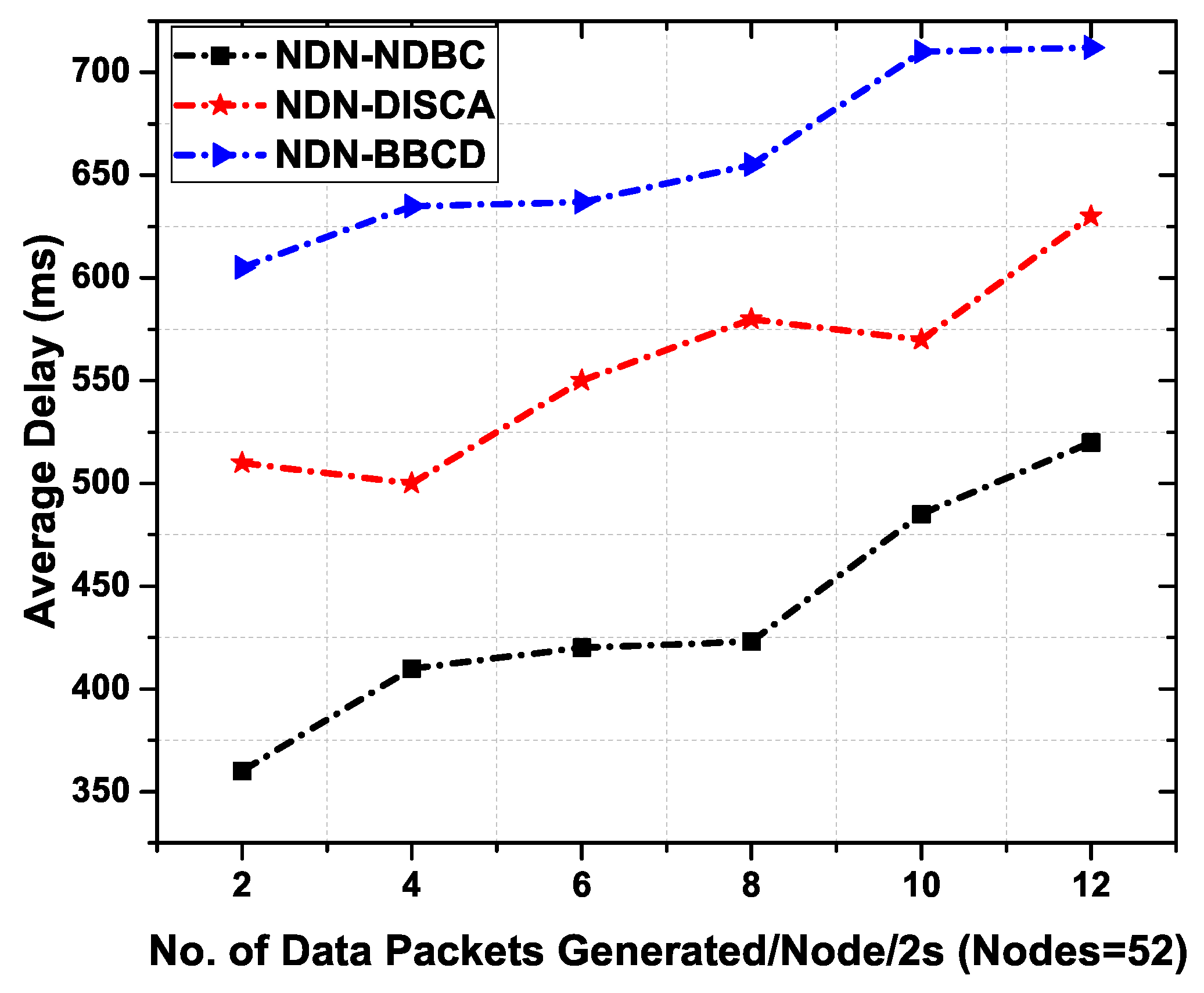
6.3.5. Average Delay
6.4. Vehicular NDN Scenario and Experimental Setup
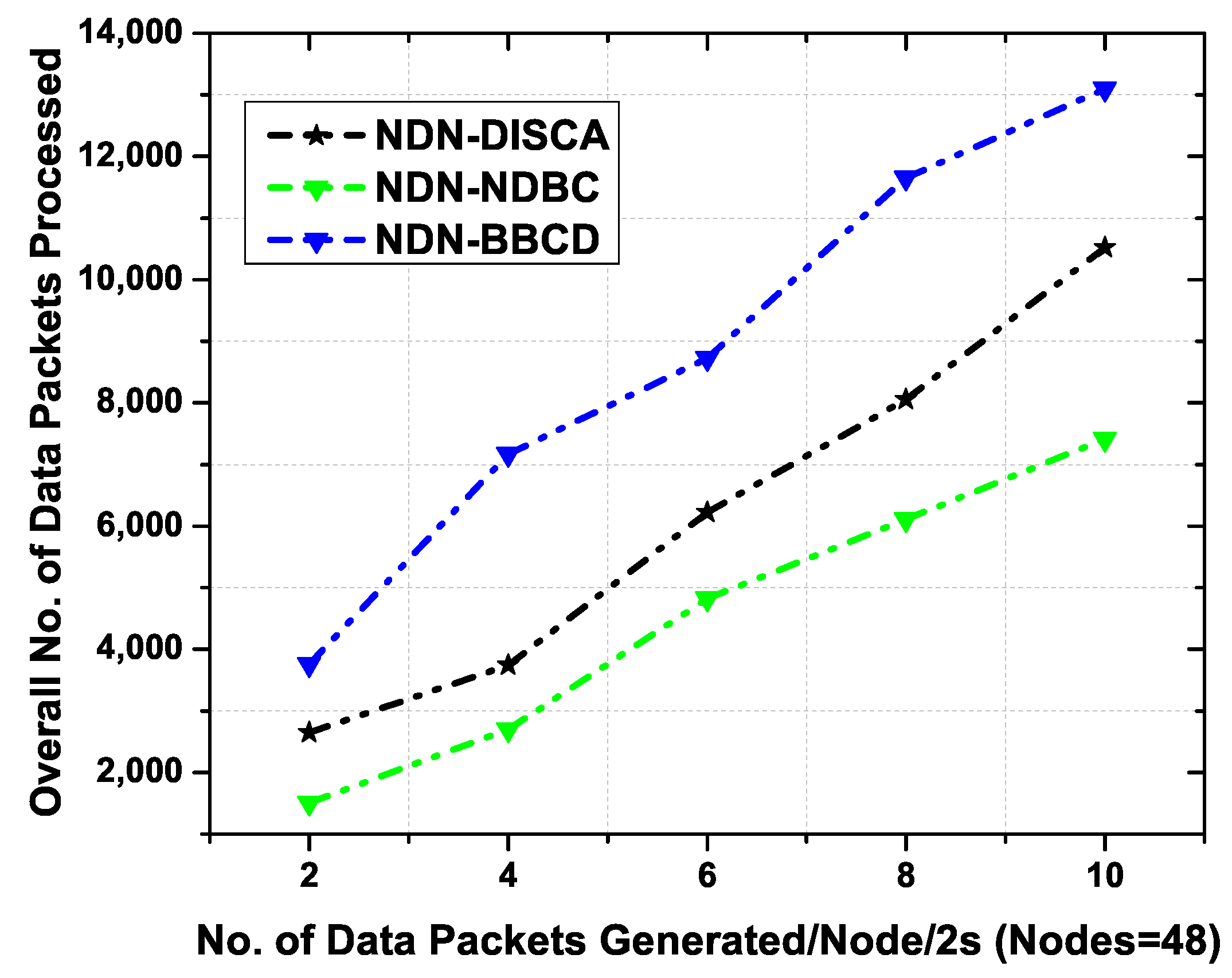
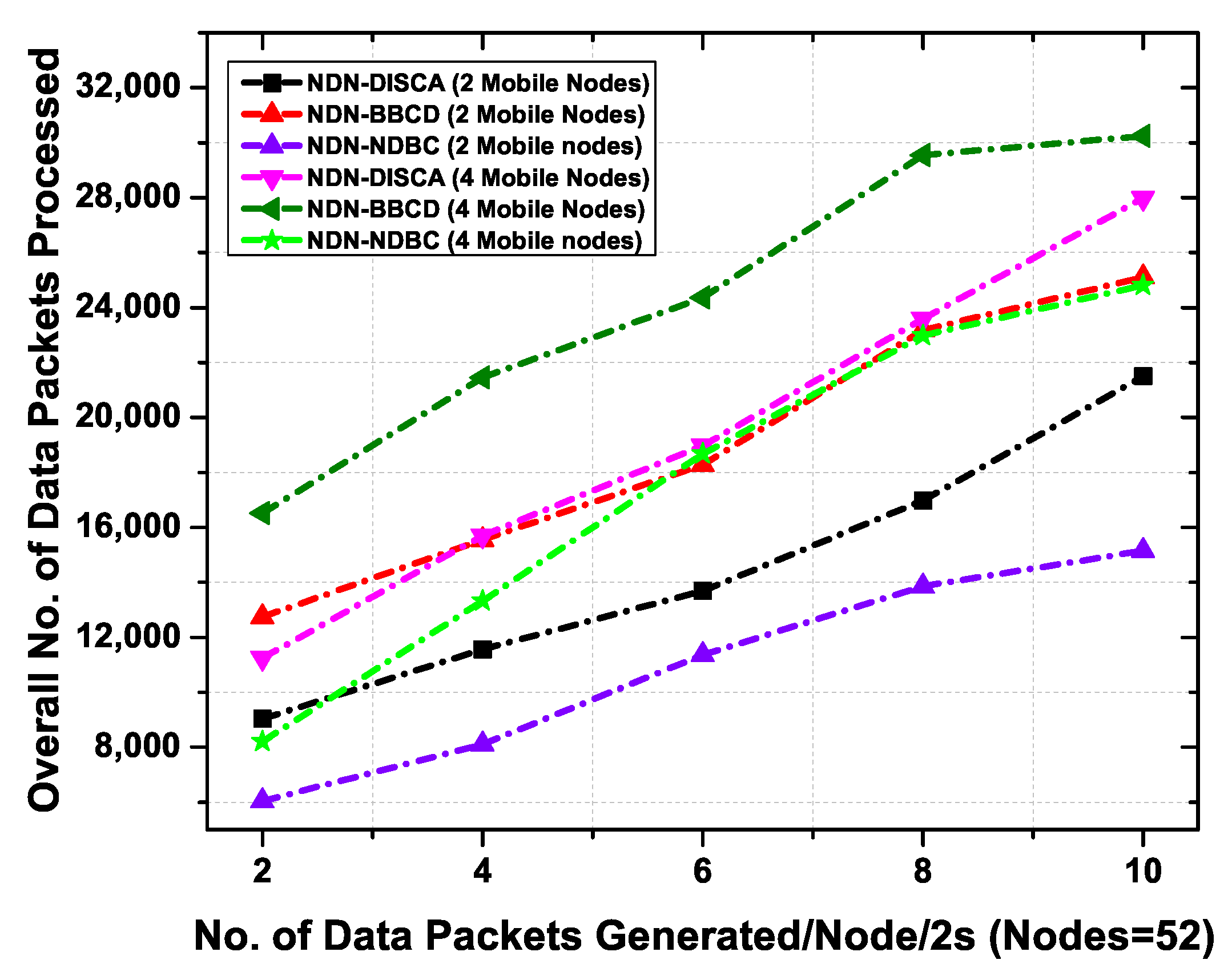
6.4.1. Performance Analysis
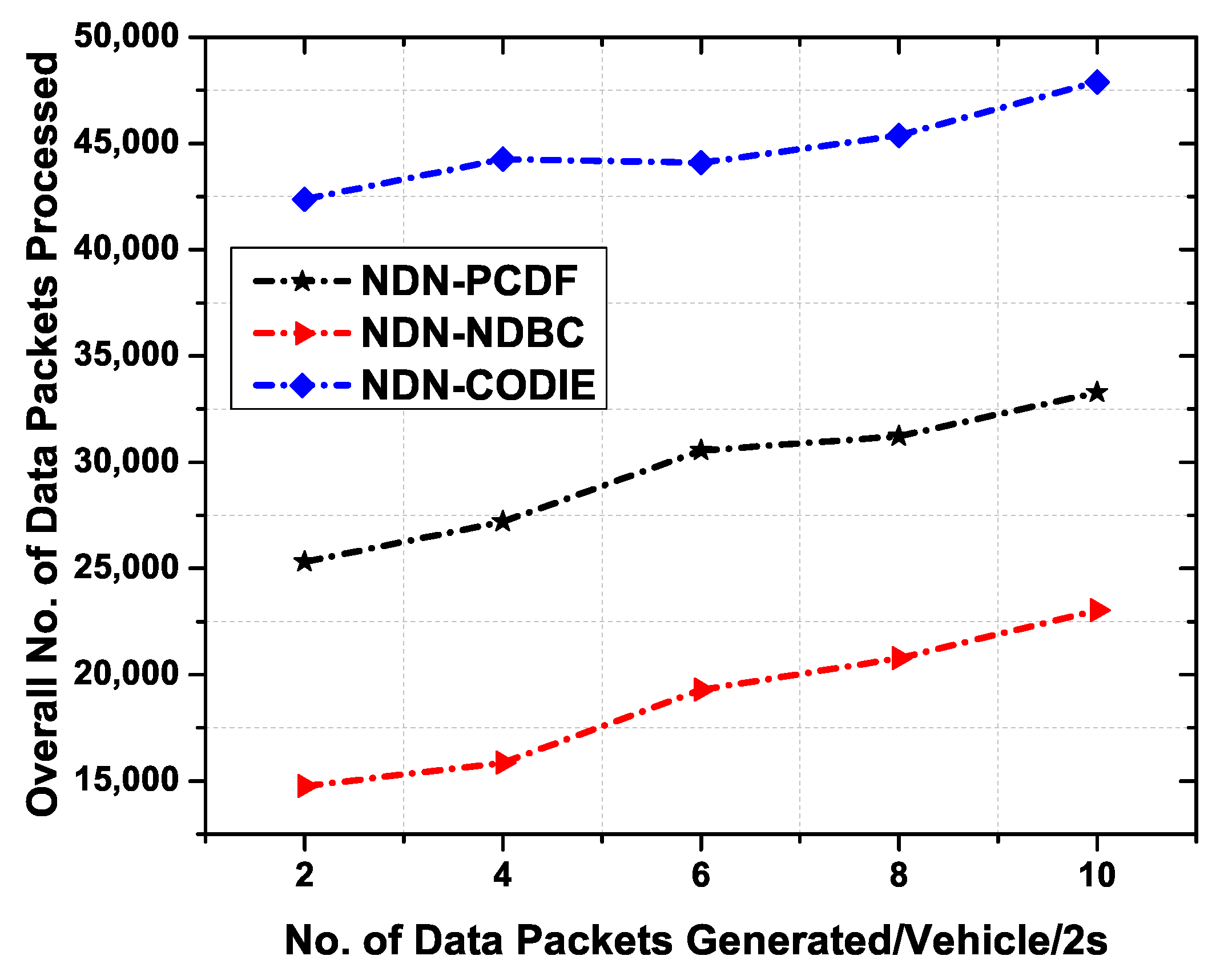
6.4.2. Total Number of Data Packets Processed with Data Generation Rate
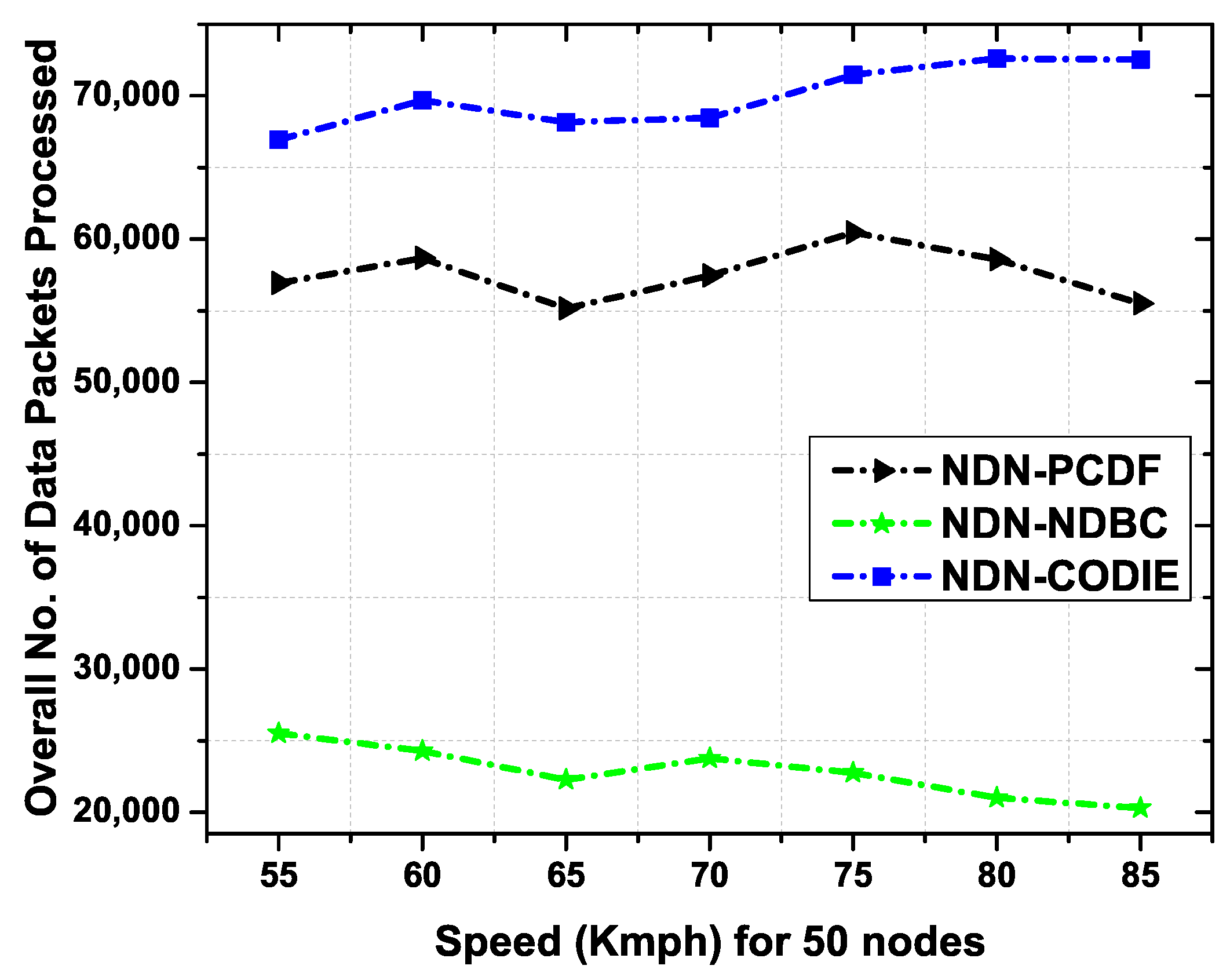
6.4.3. Total Number of Data Packets Processed with Relative Speed
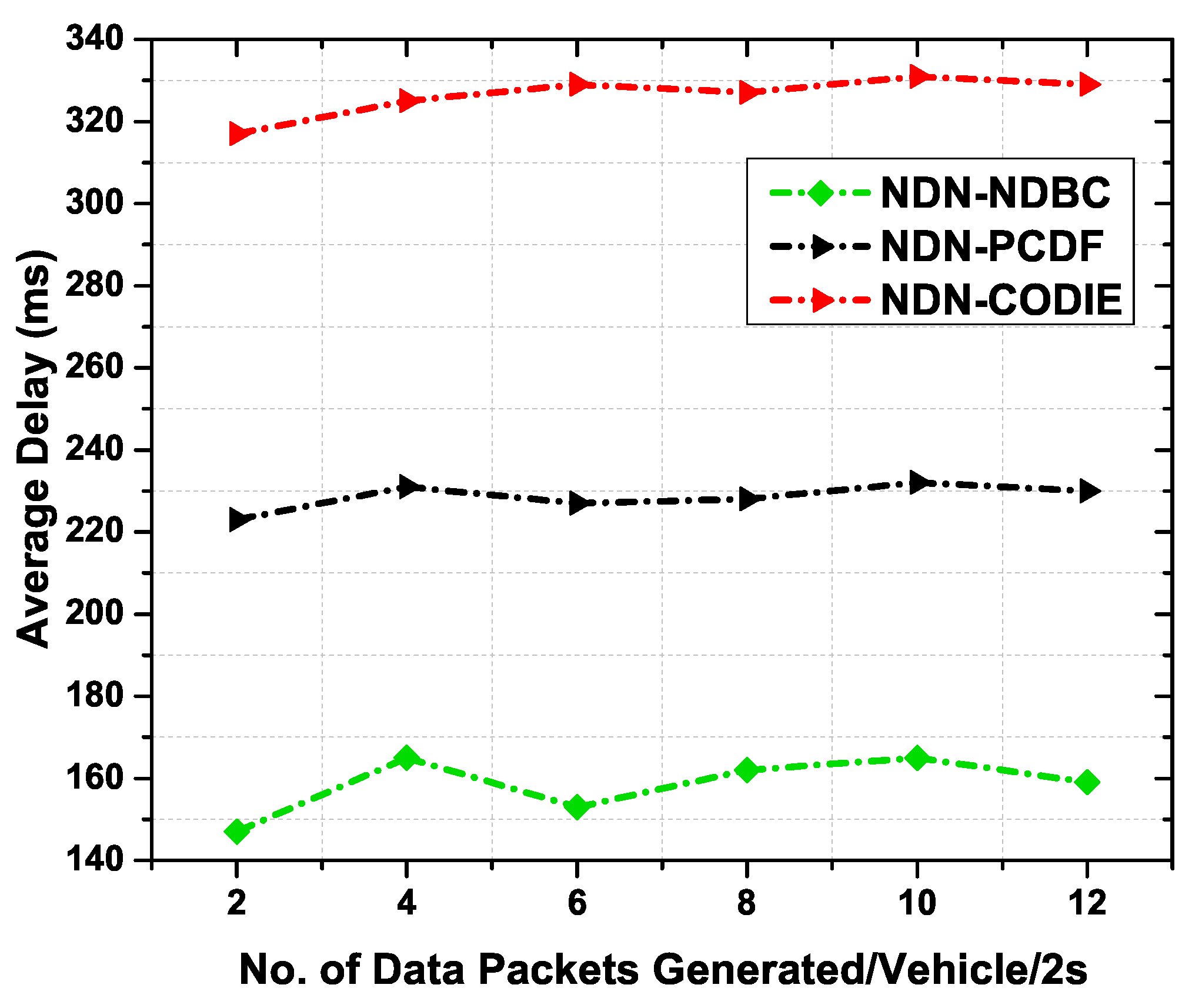
6.4.4. Average Delay
7. Conclusions
Author Contributions
Funding
Conflicts of Interest
References
- Piao, Z.; Peng, M.; Liu, Y.; Daneshmand, M. Recent Advances of Edge Cache in Radio Access Networks for Internet of Things: Techniques, Performances, and Challenges. IEEE Int. Things J. 2019, 6, 1010–1028. [Google Scholar] [CrossRef]
- Meddeb, M. Information-Centric Networking, A Natural Design for IoT Applications? Ph.D. Thesis, INSA Toulose, Toulouse, France, 2017. [Google Scholar]
- Jacobson, V.; Smetters, D.K.; Thornton, J.D.; Plass, M.F.; Briggs, N.H.; Braynard, R.L. Networking named content. In Proceedings of the 5th International Conference on Emerging Networking Experiments and Technologies, Rome, Italy, 1–4 December 2009; pp. 1–12. [Google Scholar] [CrossRef]
- Ahlgren, B.; Dannewitz, C.; Imbrenda, C.; Kutscher, D.; Ohlman, B. A survey of information-centric networking. IEEE Commun. Mag. 2012, 50, 26–36. [Google Scholar] [CrossRef]
- CCNx—Content Centric Networking. Available online: https://www.ccnx.org/ (accessed on 15 February 2019).
- Ahmed, S.H.; Bouk, S.H.; Yaqub, M.A.; Kim, D.; Song, H.; Lloret, J. CODIE: Controlled Data and Interest Evaluation in Vehicular Named Data Networks. IEEE Transa. Veh. Technol. 2016, 65, 3954–3963. [Google Scholar] [CrossRef]
- Ulah, R.; Afzal, M.K.; Kim, B.-S. A novel parallel processing mechanism for data transmission in wireless content-centric networking. J. Int. Fuzzy Syst. 2018, 35, 5815–5825. [Google Scholar] [CrossRef]
- Rehman, R.A.; Kim, B. LOMCF: Forwarding and Caching in Named Data Networking Based MANETs. IEEE Trans. Veh. Technol. 2017, 66, 9350–9364. [Google Scholar] [CrossRef]
- Ullah, R.; Ahmed, S.H.; Kim, B. Information-Centric Networking With Edge Computing for IoT: Research Challenges and Future Directions. IEEE Access 2018, 6, 73465–73488. [Google Scholar] [CrossRef]
- Fotiou, N.; Polyzos, G.C. Realizing the internet of things using information-centric networking. In Proceedings of the 10th International Conference on Heterogeneous Networking for Quality, Reliability, Security and Robustness, Rhodes, Greece, 18–20 August 2014; pp. 193–194. [Google Scholar]
- Ion, M.; Zhang, J.; Schooler, E.M. Toward content-centric privacy in icn: Attribute-based encryption and routing. In Proceedings of the 3rd ACM SIGCOMM Workshop on Information-Centric Networking, Hong Kong, China, 12 August 2013; pp. 39–40. [Google Scholar]
- Borgia, E. The internet of things vision: Key features, applications and open issues. Comput. Commun. 2014, 54, 1–31. [Google Scholar] [CrossRef]
- Al-Fuqaha, A.; Guizani, M.; Mohammadi, M.; Aledhari, M.; Ayyash, M. Internet of things: A survey on enabling technologies, protocols, and applications. IEEE Commun. Surv. Tutor. 2015, 17, 2347–2376. [Google Scholar] [CrossRef]
- Sifalakis, M.; Kohler, B.; Scherb, C.; Tschudin, C. An information centric network for computing the distribution of computations. In Proceedings of the 1st ACM Conference on Information-Centric Networking (ACM-ICN’14), Paris, France, 24–26 September 2014; pp. 137–146. [Google Scholar] [CrossRef]
- Arshad, S.; Azam, M.A.; Rehmani, M.H.; Loo, J. Recent Advances in Information-Centric Networking based Internet of Things (ICN-IoT). IEEE Int. Things J. 2018, 6, 2128–2158. [Google Scholar] [CrossRef]
- Shang, W.; Yu, Y.; Droms, R.; Zhang, L. Challenges in IoT Networking via TCP/IP Architecture; NDN, Technical Report NDN-0038; NDN Project; University of California: Los Angeles, CA, USA, 2016. [Google Scholar]
- Shang, W.; Bannis, A.; Liang, T.; Wang, Z.; Yu, Y.; Afanasyev, A.; Thompson, J.; Burke, J.; Zhang, B.; Zhang, B. Named Data Networking of Things (Invited Paper). In Proceedings of the 2016 IEEE First International Conference on Internet-of-Things Design and Implementation (IoTDI), Berlin, Germany, 4–8 April 2016; pp. 117–128. [Google Scholar] [CrossRef]
- Garcia-Luna-Aceves, J.J. ADN: An Information-Centric Networking Architecture for the Internet of Things. In Proceedings of the Second International Conference on Internet-of-Things Design and Implementation, Pittsburgh, PA, USA, 18–21 April 2017; pp. 27–36. [Google Scholar]
- Saadallah, B.; Lahmadi, A.; Festor, O. CCNx for Contiki: Implementation Details; Technical Report RT-0432; INRIA: Rocquencourt, France, 2012; p. 52. [Google Scholar]
- Ren, Z.; Hail, M.A.; Hellbrück, H. CCN-WSN-A lightweight, flexible Content-Centric Networking protocol for wireless sensor networks. In Proceedings of the 2013 IEEE Eighth International Conference on Intelligent Sensors, Sensor Networks and Information Processing, Melbourne, Australia, 2–5 April 2013; pp. 123–128. [Google Scholar] [CrossRef]
- Amadeo, M.; Campolo, C.; Molinaro, A.; Mitton, N. Named Data Networking: A natural design for data collection in Wireless Sensor Networks. In Proceedings of the 2013 IFIP Wireless Days (WD), Valencia, Spain, 13–15 November 2013; pp. 1–6. [Google Scholar]
- Quevedo, J.; Corujo, D.; Aguiar, R. A case for ICN usage in IoT environments. In Proceedings of the 2014 IEEE Global Communications Conference, Austin, TX, USA, 8–12 December 2014; pp. 2770–2775. [Google Scholar]
- Baccelli, E.; Mehlis, C.; Hahm, O.; Schmidt, T.C.; Wählisch, M. Information centric networking in the IoT: Experiments with NDN in the wild. In Proceedings of the 1st International Conference on Information-Centric Networking (ICN’14), Paris, France, 24–26 September 2014; pp. 77–86. [Google Scholar]
- CCN Lite: Lightweight Implementation of the Content Centric Networking Protocol. 2014. Available online: http://ccn-lite.net (accessed on 20 April 2019).
- RIOT: The Friendly Operating System for the Internet of Things. Available online: http://www.riot-os.org/ (accessed on 28 December 2018).
- Amadeo, M.; Campolo, C.; Molinaro, A. Multi-source data retrieval in IoT via named data networking. In Proceedings of the 1st ACM Conference on Information-Centric Networking, Paris, France, 24–26 September 2014; pp. 67–76. [Google Scholar]
- Amadeo, M.; Campolo, C.; Iera, A.; Molinaro, A. Information centric networking in IoT scenarios: The case of a smart home. In Proceedings of the 2015 IEEE International Conference on Communications (ICC), London, UK, 8–12 June 2015; pp. 648–653. [Google Scholar]
- Bouk, S.H.; Ahmed, S.H.; Kim, D. Hierarchical and hash-based naming with compact trie name management scheme for vehicular content centric networks. Comput. Commun. 2015, 71, 73–83. [Google Scholar] [CrossRef]
- Shang, W.; Ding, Q.; Marianantoni, A.; Burke, J.; Zhang, L. Securing building management systems using named data networking. IEEE Netw. 2014, 28, 50–56. [Google Scholar]
- Bouk, S.H.; Ahmed, S.H.; Kim, D. NDN goes deep: Foreseeing the underwater named data networks. In Proceedings of the Symposium on Applied Computing, Marrakech, Morocco, 3–7 April 2017; pp. 642–646. [Google Scholar]
- Arshad, S.; Shahzaad, B.; Azam, M.A.; Loo, J.; Ahmed, S.H.; Aslam, S. Hierarchical and Flat-Based Hybrid Naming Scheme in Content-Centric Networks of Things. IEEE Int. Things J. 2018, 5, 1070–1080. [Google Scholar] [CrossRef]
- Waltari, O.K. Content-Centric Networking in the Internet of Things. Master’s Thesis, Department of Computer Science, University of Helsinki, Helsinki, Finland, 25 November 2013. Available online: http://hdl.handle.net/10138/42303 (accessed on 11 January 2019).
- Francois, J.; Cholez, T.; Engel, T. CCN traffic optimization for IoT. In Proceedings of the 2013 Fourth International Conference on the Network of the Future (NoF), Pohang, Korea, 23–25 October 2013; pp. 1–5. [Google Scholar]
- Majeed, M.F.; Ahmed, S.H.; Muhammad, S.; Song, H.; Rawat, D.B. Multimedia streaming in information- centric networking: A survey and future perspectives. J. Netw. Comput. Appl. 2017, 125, 103–121. [Google Scholar] [CrossRef]
- Marica, A.; Campolo, C.; Antonella, M. Internet of Things via Named Data Networking: The Support of Push Traffic. In Proceedings of the 2014 International Conference and Workshop on the Network of the Future (NOF), Paris, France, 3–5 December 2014. [Google Scholar]
- Hannan, A.; Arshad, S.; Azam, M.A.; Loo, J.; Ahmed, S.H.; Majeed, M.F.; Shah, S.C. Disaster Management System Aided by Named Data Network of Things: Architecture, Design, and Analysis. Sensors 2018, 18, 2431. [Google Scholar] [CrossRef] [PubMed]
- Majeed, M.F.; Ahmed, S.H.; Dailey, M.N. Enabling Push-Based Critical Data Forwarding in Vehicular Named Data Networks. IEEE Commun. Lett. 2016, 21, 873–876. [Google Scholar] [CrossRef]
- De Sousa, A.M.; Araújo, F.R.C.; Sampaio, L.N. A Link-Stability-Based Interest-Forwarding Strategy for Vehicular Named Data Networks. IEEE Int. Comput. 2018, 22, 16–26. [Google Scholar] [CrossRef]
- Gao, S.; Zhang, H.; Das, S.K. Efficient data collection in wireless sensor networks with path-constrained mobile sinks. IEEE Trans. Mob. Comput. 2011, 10, 592–608. [Google Scholar] [CrossRef]
- Kuang, J.; Yu, S. Broadcast-Based Content Delivery in Information-Centric Hybrid Multihop Wireless Networks. IEEE Commun. Lett. 2017, 21, 889–892. [Google Scholar] [CrossRef]
- Mastorakis, S.; Afanasyev, A.; Zhang, L. On the Evolution of ndnSIM: An Open-Source Simulator for NDN Experimentation. ACM SIGCOMM Comput. Commun. Rev. 2017, 47, 19–33. [Google Scholar] [CrossRef]
- Afanasyev, A.; Shi, J.; Zhang, B.; Zhang, L.; Moiseenko, I.; Yu, Y.; Shang, W.; Li, Y.; Mastorakis, S.; Huang, Y.; et al. NFD Developer’s Guide; Technical Report, NDN-0021, NDN; University of California: Los Angeles, CA, USA, 2018. [Google Scholar]
- IEEE Std 802. 11-2012. Part 11: Wireless LAN Medium Access Control (MAC) and Physical Layer (PHY) Specifications; IEEE: New York, NY, USA, 2000. [Google Scholar]

| Parameter | Value |
|---|---|
| Simulator | NS-3 (ndnSIM) |
| Propagation Delay Model | Constant-Speed Propagation |
| Propagation Loss Model | Log Distance |
| Mobility Model for static nodes | Random_Disc_Position_Allocator Model |
| Mobility Model for mobile nodes | Random_Direction 2D Mobility Model |
| Mobile Node speed | 0.3 s |
| Technology | Wi-Fi_STANDARD_IEEE 802.11a |
| Area (m × m) | 40 × 40 |
| Number of Nodes | 52 (48 Static Nodes and 4 Mobile Nodes) |
| Frequency of Data packets/2s | 2, 4, 6, 8, 10 |
| Packet Size | 1040 bytes |
| TxPowerStart | 5 (dbm) |
| TxPowerEnd | 5 (dbm) |
| Energy Consumption | 0.5 J/bit |
| Initial Energy | 10 Joules |
| Caching Policy | LCE |
| Replacement Policy | LRU |
| Simulation Time (s) | 1200 s |
© 2019 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Ullah, R.; Rehman, M.A.U.; Kim, B.S. Hierarchical Name-Based Mechanism for Push-Data Broadcast Control in Information-Centric Multihop Wireless Networks. Sensors 2019, 19, 3034. https://doi.org/10.3390/s19143034
Ullah R, Rehman MAU, Kim BS. Hierarchical Name-Based Mechanism for Push-Data Broadcast Control in Information-Centric Multihop Wireless Networks. Sensors. 2019; 19(14):3034. https://doi.org/10.3390/s19143034
Chicago/Turabian StyleUllah, Rehmat, Muhammad Atif Ur Rehman, and Byung Seo Kim. 2019. "Hierarchical Name-Based Mechanism for Push-Data Broadcast Control in Information-Centric Multihop Wireless Networks" Sensors 19, no. 14: 3034. https://doi.org/10.3390/s19143034
APA StyleUllah, R., Rehman, M. A. U., & Kim, B. S. (2019). Hierarchical Name-Based Mechanism for Push-Data Broadcast Control in Information-Centric Multihop Wireless Networks. Sensors, 19(14), 3034. https://doi.org/10.3390/s19143034







