Abstract
In the last years, several attempts to combine the Internet of Things (IoT) and social networking have been made. In the meantime, things involved in IoT are becoming increasingly sophisticated and intelligent, showing a behavior that tends to look like the one of users in social networks. Therefore, it is not out of place to talk about profiles of things and about information and topics exchanged among them. In such a context, constructing topic-driven virtual communities starting from the real ones operating in a Multi-IoT scenario is an extremely challenging issue. This paper aims at providing some contributions in this setting. First of all, it presents the concept of profile of a thing. Then, it introduces the concept of topic-guided virtual IoT. Finally, it illustrates two approaches (one supervised and one unsupervised) to constructing topic-guided virtual IoTs in a Multi-IoT scenario.
1. Introduction
The Internet of Things (hereafter, IoT) is currently considered the new frontier of the Internet. As a matter of fact, a lot of research results, along with the continuous emergence of increasingly challenging issues to address, can be found in the literature [1,2,3,4,5,6,7].
One of the most effective ways to represent and handle the IoT scenario leverages social networking paradigm [8]. In this direction, several social network-based approaches to modeling and managing IoTs have been presented in the literature. Three of the most advanced ones are the SIoT (Social Internet of Things) [9,10,11,12], the MIE (Multiple IoT Environment) [13] and the MIoT (Multiple IoTs) [14] paradigms. The MIoT paradigm is the last of these proposals; it aims at extending both SIoT and MIE in such a way as to preserve their strengths and avoid their weaknesses [14]. Roughly speaking, a MIoT can be seen as a set of related IoTs, i.e., as a set of related networks of things. Actually, a more precise definition of MIoT requires the introduction of the concept of instance of a thing in an IoT. Specifically, the instance of a thing in an IoT represents a virtual view of that thing in the IoT. The nodes associated with a thing in a MIoT represent the instances of the same thing in the different IoTs of the MIoT. Indeed, a thing can have several instances, one for each IoT which it participates to. The existence of more instances for one thing plays a key role in the MIoT paradigm because it allows the definition of cross relationships among the different IoTs.
We adopted the MIoT paradigm as the reference one in this paper. There are several reasons which justify this choice. Indeed:
- The MIoT paradigm, like the SIoT and the MIE ones, introduces the idea that objects can show a social behavior in the environment where they operate. This feature allows several advantages, like the possibility of resource sharing (see [10,11,12] for a comprehensive idea of these advantages).
- Differently from SIoT, which introduces a social behavior of objects but still models IoT as one huge network of objects extended worldwide, MIE, and much more MIoT, allow the “breakdown” of the whole huge IoT into multiple networks of smart objects interconnected with each other. This way to proceed is analogous to the evolution of social networking into social internetworking [15]. In particular, MIoT allows the management of situations in which the same object shows different behaviors in different networks it joined. Furthermore, MIoT makes an object to act as a bridge between two objects allowing them to communicate even if they belong to different networks and, therefore, are not directly connected with each other.
Another important trend characterizing the current IoT scenario regards the existence of increasingly sophisticated and intelligent things. These are becoming increasingly smart and social, as well as more and more capable of performing computations and storage on their own. Furthermore, they are increasingly connected to each other through more and more complex and sophisticated frameworks, often based on cloud and edge computing [10,11,12]. The new smart and social capabilities of things and of the environments handling their interoperability paves the way to a sort of “humanization” of things, i.e., to apply to things concepts and ideas typically considered prerogative of humans. One of them is certainly the presence of a profile of a thing. Indeed, if a thing interacts with other things and exchange data with them, it is possible to determine what are the most common concepts handled by it and, based on them, to construct a corresponding profile. Analogously to the profile of a human, the one of a thing depends on its past behavior and on the profile of the other things with which it interacts. As a consequence, it could be possible to think about both a content-based and a collaborative-filtering approach to handling thing profiles.
Furthermore, starting from the real IoTs of a MIoT, it is possible to construct virtual communities of things, based on common interests. Once again, this is an attempt to transfer behaviors typical of humans to things. As a matter of fact, in Social Network Analysis, it is well recognized that, accordingly to the homophily concept [16,17], humans tend to group together in communities sharing the same interests.
In the literature, a lot of efforts have been made to investigate human profiles and virtual communities of people, especially (but not only) in Social Network Analysis [18,19]. Instead, these topics have been little investigated in the Internet of Things.
In this paper, we aim at providing a contribution in this direction. First of all, we introduce the concept of profile of a thing. As the profile of a human, the one of a thing has two components. The former denotes its past behavior and can be used, for instance, to support content-based recommendations. The latter reflects its neighbors, i.e., the other things with which it most frequently comes into contact; it can be exploited, for instance, to support collaborative filtering recommendations.
After this, we introduce the concept of topic-guided virtual IoTs in a MIoT and we propose two approaches (one supervised and one unsupervised) to the construction of them in a MIoT. Differently from the real IoTs of a MIoT, which may encompass things with very heterogeneous profiles, topic-guided virtual IoTs should include all and only those things whose profile refers to specific topics. The supervised approach requires a user to provide a set of keywords of her interest. It aims at constructing a thematic IoT comprising all the keywords specified by the user. If such an IoT does not exists, it returns more thematic IoTs that, in the whole, comprise all the keywords specified by the user. She can choose whether to accept this set of virtual IoTs or to modify her query. The unsupervised approach tries to partition a MIoT into a set of virtual IoTs characterized by the maximum internal cohesion (in terms of topics present in the profiles of the corresponding things) and the minimum external coupling. Virtual IoTs in a MIoT provide a logic representation of the objects of a MIoT, which is not based on real links but on the content exchanged by them. As will be clear in the following, this can favor the effectiveness of information exchange, the construction of communities of objects (and, possibly, of the corresponding users) sharing the same interests and the suggestions of the objects most adequate to a given exigency.
This paper is organized as follows: in Section 2, we examine related literature. In Section 3, we provide an overview of the MIoT paradigm, because its comprehension is necessary to understand the rest of this paper. In Section 4, we introduce our definition of a thing’s profile. In Section 5, we propose our approaches to construct topic-guided virtual IoTs in a MIoT. In Section 6, we present our tests devoted to verify the performance of our approach. Finally, in Section 7, we draw our conclusions and have a look at future developments of our research efforts.
2. Related Literature
Since its introduction some years ago, the term “Internet of Things—IoT” has been associated with a huge variety of concepts, technologies and solutions [5,20,21,22]. In the latest years, with the advent of new technologies, such as big data and social networking, the very definition of this term is continuously changing. What IoT will become in the future depends on the evolution of these technologies [23] and their interaction with several other ones, such as Information Centric Networks [24,25,26,27,28,29,30] and Cloud [3,31,32]. As a matter of fact, the strengths of these last ones are exactly the features necessary to overcome the weaknesses of the current IoT concept [33]. Some examples of this combination can be already found in the literature [6,10,34,35].
The first attempts to apply social networking to the IoT domain can be found in [36,37,38,39]. In these papers, the authors propose to use human social network relationships to share services provided by a set of things. An important step forward is performed in [9], where the SIoT paradigm is introduced. Here, the authors propose an approach to creating relationships among things, without requiring the owner intervention. Thanks to this idea, things can autonomously crawl the network to find services and resources of their interest provided by other things. In [40], the same authors clearly highlight what are the main strengths of SIoT. Specifically: (i) the SIoT structure can be dynamically modified to ensure network navigability and to find new things; (ii) scalability is guaranteed, like in human social networks; (iii) a level of trustworthiness among things can be established; (iv) the past social network approaches can be redefined to solve problems typical of the IoT context [41].
One of the major drawbacks of the current IoT scenario is the presence of different technologies and solutions proposed by independent vendors to enable networking among objects. This poses the basis to a subsequent set of issues ranging from concept matching to technical compatibility, if heterogeneous smart-object-network solutions should be involved in the creation of a unique interoperable IoT [42,43]. In this research context, different works partially addressing and solving these problems have been proposed. Specifically, [44] presents a study on how ontologies and semantic data processing can be used to improve interoperability across heterogeneous IoT platforms. The authors consider two use cases, namely Health Care and Trasportation and Logistics, and, for each of them, provide a survey on the main ontologies available to describe and generalize concepts and relations.
In [45], instead, the authors focus their attention on the definition of a new framework for a fully functional mobile ad-hoc social network. In this paper, the term “mobile ad-hoc social network” refers to an IoT made of mobile devices. Of course, communication between this type of objects may happen in such a wide range of modes so that the referring scenario can be considered as a constellation of mobile networks interacting with each other. Concepts from real social networks are borrowed to define user profiles, which are built starting from the objects they own and the social network they belong to. One of the main contributions of this proposal is the definition of a profile-matching strategy based on semantics.
Another contribution in the context of interoperability is the one proposed in [46]. Here, the authors illustrate a novel architecture in which objects interact with each other by leveraging an open source cloud platform. The interaction among smart devices is information-and-service-driven and can be performed in both a centralized and a peer-to-peer mode. In [47], the authors propose Acrost, a system capable of retrieving data spread among heterogeneous IoT platforms by leveraging topics and semantics awareness. To build the metadata, Acrost uses two methodologies: the former exploits regular expression-based approaches, whereas the latter makes use of random fields-based strategies.
In order to address the issues arising when the interoperability among heterogeneous IoTs must be guaranteed, another research line proposes the extension of the results concerning Social Internetworking [15,48] (instead of social networking) to the Internet of Things. By following this strategy, the MIE (Multiple IoT Environment) [13] and the MIoT (Multiple IoTs) [14] paradigms have been proposed. As specified in the Introduction, this last paradigm is the reference one for this paper.
In [49], the authors present an approach to constructing a virtual data mart on which several knowledge discovery tasks can be performed. Clearly the kinds of virtual source constructed in the approach of [49] and in our own are very different. However, the general ideas underlying the two approaches are similar.
In the past, a lot of efforts have been made to investigate human profiles and virtual communities of people, especially (but not only) in Social Network Analysis ([18,19] provide two surveys about these topics). Instead, these issues have been little investigated in the Internet of Things. Specifically, to the best of our knowledge, a comprehensive, high-level abstraction approach to building and managing a profile of a thing, which also takes into account the content it exchanges during its interactions with other things, has not yet been proposed. Instead, some approaches focusing on community detection in IoT have been presented in the very recent literature. Even if they are very different (both in their purposes and in their ways proceed) from the ones of our approach, in the following we present an overview of some of them.
The approach of [50] uses structural information derived from the complex graph of an IoT to extract communities. It exploits a neighbor-based strategy to detect also overlapping communities. The approach of [51] uses data produced by sensors to define a multi-dimensional clustering. The obtained clusters are then mapped to communities of nodes in the original IoT network. To cope with the size of the data graph, the authors leverage state-of-the-art community detection approaches. Finally, they present a new community detection approach that enhances the Girvan-Newman algorithm by using hyperbolic network embedding.
Other works, instead, use knowledge from social networks to refine their results. A similar method is proposed in [52], even though here the strategy works in the opposite way. In fact, first communities are derived from structural information of owners’ social networks and, then, objects are seen as resources available inside each community.
Finally, the authors of [53] propose a new community detection algorithm working in a Social Internet of Things (SIoT) scenario. To achieve their objective, they make use of three metrics, namely social similarity, preference similarity and movement similarity. Social similarity is defined according to the concept of cooperativeness and community interest proposed in [54]. Preference similarity takes into account resource and service preferences of the involved things in the network. Finally, movement similarity specifies how much and how long two or more nodes are spatially close.
In [55], the authors propose a community detection approach working on an architecture capable of integrating the Internet of Things and social networking. This approach assumes that two nodes belong to the same community only if they are at most one hop apart and have at least two mutual friends. In order to construct communities, it exploits graph mining techniques.
As a consequence, it does not consider semantics and contents, but leverages only on network structure.
3. The MIoT Paradigm
In this section, we provide an overview of the MIoT paradigm, described in detail in [14], because it is the reference one for our definitions of virtual IoTs in a MIoT.
A MIoT consists of a set of m Internets of Things. Formally speaking:
where is an IoT.
Let be an object of . We assume that, if belongs to , it has an instance , representing it in . The instance consists of a virtual view (or, better, a virtual agent) representing in . For example, it provides all the other instances of , and the users who interact with , with all the necessary information about . Information stored in is represented according to the format and the conventions adopted in .
A MIoT can be represented by means of a graph-based notation. In particular, each IoT can be modeled by means of a graph . In this case:
- is the set of the nodes of ; there is a node for each instance , and vice versa.
- is the set of the arcs of ; there is an arc if there exists a physical link from to .
Finally:
Here:
where
and
is the set of the inner arcs (hereafter, i-arcs) of ; they relate instances (of different objects) belonging to the same IoT. is the set of the cross arcs (hereafter, c-arcs) of ; they relate instances of the same object belonging to different IoTs.
The description of the MIoT paradigm presented above highlights that it is possible to model a MIoT at two abstraction levels. The former represents a MIoT as a network and exploits concepts typical of this environment (such as nodes, arcs and so on). The latter models a MIoT as a set of IoTs and makes use of concepts closer to this scenario (such as instances, objects and so forth). Clearly, these two representations are simply two viewpoints of the same environment, and the concepts adopted by them can be used interchangeably. For example, there is a biunivocal correspondence between a node and an instance. However, in the reality, there are some cases in which it is better to use the concept of a node (for example, when we discuss about paths in a network—see below), whereas there are other situations in which it is better the use of the concept of instance (for example, when we discuss about the transactions carried out by two smart objects).
Furthermore, in a MIoT context, a set of metadata can be associated with an object . Our metadata model refers to the one of the IPSO (Internet Protocol for Smart Objects) Alliance [56]. Specifically consists of three subsets, namely: (i), i.e., the set of descriptive metadata; (ii), i.e., the set of technical metadata; (iii), i.e., the set of behavioral metadata. All details about these metadata can be found in [14].
4. Definition of a Thing’s Profile
In this section, we present our definition of a thing’s profile, which represents a first important contribution of this paper. As pointed out in the Introduction, analogously to what happens for human profiles, the profile of a thing can have two components. The former registers its past behavior and is extremely useful for content-based recommendations; for this reason, we call it “content-based component” in the following. The latter registers the main features of those things with which it mostly interacted in the past and can be used for collaborative filtering recommendations; for this reason, we call it “collaborative filtering component” in the following.
Before illustrating in detail the profile of a thing, we must introduce some preliminary concepts. First of all, given two instances of and of in , we can define the set of the transactions from to as follows:
A transaction is represented as:
Here:
- denotes the reason why occurred, chosen among a set of predefined values.
- indicates the starting node of the path followed by .
- represents the final node of the path followed by .
- denotes the starting timestamp of .
- indicates the ending timestamp of .
- denotes whether was successful or not; it is set to true in the affirmative case, to false in the negative one, and to NULL if is still in progress.
- indicates the content “exchanged” from to during . In its turn, presents the following structure:
Here:
- indicates the format of the content exchanged during ; the possible values are: “audio”, “video”, “image” and “text”.
- denotes the name of the transmitted file.
- indicates the size in bytes of the content.
- indicates the set of the content topics; it consists of a set of keywords representing the subjects exchanged during . It can be formalized as: . In other words, the set of the topics of the transaction from to consists of w pairs; each pair consists of a keyword and the corresponding number of occurrences.
Now, we can define the set of the transactions performed by in . Specifically, let be the set of the instances of . Then:
In other words, the set of the transactions performed by an instance is given by the union of the sets of the transactions from to all the other instances of .
After having defined , we must introduce the following operators:
- ⊎: it receives a set of entity sets and performs their union not eliminating the duplicates but reporting the number of their occurrences. Therefore, this operator returns a set of pairs in which the pair indicates the entity and the number of its occurrences. In counting it, ⊎ takes the presence of synonymies and homonymies into account. These properties can be computed (for terms, images, etc.) by applying the classical approaches proposed in the past literature [57,58].
- : it receives a set of files and computes their average size.
We are now able to define the profile of the relationship existing between two instances and , which performed a set of transactions. As we will see in the following, this profile plays a crucial role in the definition of the content-based component of a thing’s profile and is indirectly used also in the definition of the collaborative filtering component of it. Specifically:
where:
- ;
- ;
- ;
- ;
- ;
- ;
- ;
- ;
- .
If we introduce the operator ⨆, which compactly represents the set of operations for obtaining a profile of a pair of instances starting from the corresponding transactions, we can formalize the previous tasks by means of only one operation as follows:
Now, let be the instance of the object in the IoT . Let be the set of the instances of with which performed at least one transaction in the past. In this case, we can define the content-based component of the profile of as:
Finally, let be an object and let be the set of the IoTs which it participates to. Let be the instances of in the IoTs of the MIoT. We can define the content-based component of the profile of as:
After having defined the content-based component of an instance and an object, in order to present the corresponding collaborative filtering components, we must introduce the concept of neighborhoods of an instance in an IoT . Specifically, the structural neighborhood of is defined as:
where:
Furthermore, we can also define the behavioral neighborhood of as:
where:
In other words, consists of those instances directly connected to from the structural viewpoint that shared at least one transaction with .
We are now able to present the collaborative filtering component of the profile of an instance in . It can be defined as follows:
Clearly, this definition is recursive and an accurate computation would require the resolution of a system with a number of equations and variables equal to the number of instances. In real situations, as there could be thousands or millions of instances in a MIoT, the time necessary to solve this system may easily become unacceptable. As a consequence, it appears reasonable to consider an approximate definition of that is much simpler to handle. It is formalized as:
After having introduced the two components of the profile of an instance of , we can combine them for defining the overall profile of . It is defined as the union of the profiles and performed by means of the operator ⊔:
Finally, we can define the overall profile of an object as follows:
5. Topic-Guided Virtual IoTs in a MIoT and Approaches to Constructing Them
In this section, we present a supervised and an unsupervised approach to constructing topic-guided virtual IoTs in a MIoT.
5.1. Supervised Approach
The supervised approach for the construction of topic-guided virtual IoTs in a MIoT requires the user to specify a query Q consisting of some keywords of her interest. It tries to construct a thematic virtual IoT in such a way that each of its instances contains at least one keyword of Q in the content-based component of its profile. If such a virtual IoT does not exist, our approach returns a minimal set of thematic IoTs that, on the whole, contain, in the content-based component of the profile of their instances, all the keywords specified by the user. In this last case, she can choose whether to accept this set of IoTs or modify her query.
Before describing in detail this approach, we must introduce a new operator that represents a modified Jaccard coefficient, as we will see below.
receives two sets of topics (We recall that, in our context, a topic is a pair , where is a keyword and is the corresponding number of occurrences.) and and computes the Jaccard coefficient between them. In carrying out this task, it considers the number of occurrences of each keyword and its possible synonyms.
More formally, first it computes the set:
Then, it computes the final result as:
After having introduced , we can describe our approach. Specifically:
- It starts when a user specifies a query Q consisting of r keywords:It searches for all the instances of the MIoT having at least one topic whose keyword is identical to, or synonymous of, at least one keyword specified in Q. These instances, as a whole, represent the set of candidate instances to be included in the new thematic view. We call this set (Candidate Instances).
- However, the fact that an instance has a keyword in common with Q is necessary but not sufficient for it to be chosen. In fact, it is advisable that has more keywords in common with Q and, possibly, that the common keywords are among the ones of with the highest number of occurrences. This condition can be guaranteed by the usage of the operator .In particular, our approach first constructs in such a way as to make the application of on the keywords specified by the user possible. Then, it constructs the set (Real Instances) of those instances of whose topics have a significant similarity with the keywords of Q:Here, is a suitable tuning threshold.
- Now, our approach can start to construct the thematic view corresponding to Q.
- -
- It first creates a node in for each instance of . Let and be the nodes corresponding to two instances and belonging to .
- *
- If an i-arc exists between the nodes corresponding to and in the MIoT , then an i-arc is also created between the nodes and in .
- *
- Instead, if a c-arc exists between the nodes corresponding to and in , then and are merged in a unique node in . This task is motivated by the fact that and represent different instances of the same object in different real IoTs, but they represent the same instance in the same virtual IoT; as a consequence, they must be merged and no cross arc can exist between them. The profile of is obtained by applying the operator ⨆ on the profiles of and of .
- Finally, our approach adds a disconnected node in for each keyword in Q such that there is no MIoT instance having at least one topic whose keyword is identical to, or synonymous of, it (The rationale underlying this step will be clearer in the following.).
- At this point, two cases may occur. In particular:
- -
- It could happen that is connected. In this case, it is returned as the answer to the query Q submitted by the user.
- -
- If is not connected and if the number of its connected components is less than a certain threshold, our approach adds the minimum number of “fictitious” i-arcs necessary to make connected.
- -
- Otherwise, if the number of connected components of is higher than a certain threshold, our approach concludes that a unique thematic virtual IoT corresponding to the keywords specified by the user does not exist and returns the thematic views related to the connected components of . At this point, the user can decide whether to accept these thematic views or to modify the query in such a way as to construct a unique thematic view by re-applying all the above mentioned steps starting from the new query.
5.2. Unsupervised Approach
The unsupervised approach begins with the construction of a support network starting from the MIoT . In particular:
- For each node of , a node is added in .
- For each i-arc in , an (unoriented) arc is added in . The arcs of are weighted. The weight of the arc is obtained by applying the operator on the topic sets and of and , respectively. Therefore, the weight of an arc in belongs to the real interval ; the higher this weight the higher the semantic similarity between the topics of the profiles and of and , respectively.
- For each c-arc in , which relates two instances and of the same object in two different IoTs and , the two nodes and in , corresponding to the nodes and in , are merged into a unique node . This node inherits all the arcs of and .
At the end of these steps, it could happen that two or more arcs relate the same nodes and in . In this case, all these arcs must be merged into a single arc. Clearly, it is necessary to determine the weight of this arc. Here, it appears reasonable that it must be higher than or equal to the maximum weight of the merged arcs. To reach this objective, our approach operates as follows. Let be the arcs to merge, ordered by decreasing weight. The new arc will have a weight equal to:
In other words, in the computation of , the arcs with the maximum weight will contribute with all their weight. All the other arcs will contribute to a lesser extent, with a fraction of their weight. This last is determined by means of the coefficient .
Once the construction of has been completed, the thematic views are derived by applying on a graph clustering algorithm among the ones already existing in the literature (see [59] for a survey on them).
5.3. Discussion
An important issue about the supervised and the unsupervised approaches to address regards their scalability or, better, the possibility to use them in MIoTs comprising thousands or even millions of nodes.
With regard to this issue, first of all we observe that both approaches aim at deriving virtual IoTs which are, then, exploited by users to perform their desired tasks (such as querying). As a consequence, we can distinguish two moments in the life of a MIoT, namely: (i) the construction of virtual IoTs, which can be performed offline, and (ii) their usage, which is generally carried out online.
The first moment is computationally expensive because it involves several network operations in the supervised approach and a clustering activity in the unsupervised one. Clustering’s computational cost is intrinsically exponential even if all the corresponding methods adopted in the reality are heuristic and most of them have a linear or a quadratic computational complexity. In any case, as pointed above, this task is performed offline and rarely because it is necessary only when many changes have been made in the MIoT.
The second moment is certainly less expensive; its cost depends on the size of the involved clusters; in fact, each user activity generally involves one or a few clusters. Concerning this aspect, it is important to verify: (i) if clustering is possible in presence of huge MIoTs, and (ii) how the size of clusters increases against the growth of the MIoT. As for the first point, we observe that, in the past, several algorithms have been specifically conceived to cluster a huge amount of elements [60]. Concerning the second point, instead, first we observe that the size of clusters can be determined by suitably tuning the parameters of the selected clustering algorithm. However, it could be interesting to verify how much the size of clusters increases if we maintain constant all the clustering algorithm parameters and the MIoT size increases. We decided to perform this experiment. It is described in detail in Section 6.6. Here, we evidence the obtained results, i.e., that when the MIoT size highly increases, the cluster size slightly grows, whereas the number of clusters increases very much. This is a positive result for our purposes because the parameter to monitor for investigating the performance obtained during the second moment is just cluster size.
Another important issue to investigate regards the possible existence of a unique framework handling all the objects of the MIoT and, therefore, in principle, thousands or millions of objects. With regard to this aspect, we evidence that, in the past, several attempts have been successfully performed in this direction (think, for instance, of the SIoT framework proposed in [9,40]). Clearly, we understand that, in the future, the number of objects possibly belonging to a MIoT is enormously higher than the number of objects available in the past IoT frameworks. However, we point out that: (i) our approach needs to store only the metadata of the involved objects, and these are small; (ii) the real objects can operate in a distributed environment thanks to the new available technologies, such as cloud, edge and fog computing, which can ease the organization and the management of distributed contexts.
6. Experiments
In this section, we present the experimental campaign that we carried out to evaluate the performance of our approach from several viewpoints. Specifically, we describe our dataset in a subsection, whereas, in the next ones, we illustrate our tests, along with the underlying motivations and the obtained results.
6.1. Adopted Dataset
To perform our experiments, we had the necessity to create several MIoTs with different sizes, ranging from hundreds to thousands of nodes. Since, currently, real MIoTs with the size and the variety handled by our model do not exist yet, we had to realize a MIoT simulator, i.e., a tool that, starting from real data, is capable of simulating MIoTs with certain characteristics specified by the user.
The MIoTs created by our simulator follow the model described in Section 3. In order to perform its task, our simulator carries out the following steps: (i) creation of objects; (ii) creation of object instances; (iii) creation of instance connections; (iv) creation of instance profiles.
Our MIoT simulator is also provided with a suitable interface allowing a user to “personalize” the MIoT to construct by specifying the desired values for several parameters, such as the number of nodes, the maximum number of instances of an object, and so forth.
To make “concrete” and “plausible” the created MIoT, our simulator leverages a real dataset. It regards the taxi routes in the city of Porto from 1 July 2013 to 30 June 2014. It can be found at the address http://www.geolink.pt/ecmlpkdd2015-challenge/dataset.html. Each route contains several Points of Interests corresponding to the GPS coordinates of the vehicle.
We partitioned the city of Porto in six areas and associated a real IoT with each of them. Our simulator associates an object with a given route recorded in the dataset and an object instance for each partition of a route belonging to an area. It creates a MIoT node for each instance and a c-arc for each pair of instances belonging to the same route. Furthermore, it creates an i-arc between two nodes of the same IoT if the length of the time interval between the corresponding routes is less than a certain threshold . The weight of the i-arc indicates the length of this time interval. The value of can be specified through the constructor interface. Clearly, the higher the more connected the constructed MIoT.
As far as instance profiles are concerned, since there are no thing profiles available (indeed, the concept of thing profile is one of the main novelties introduced in this paper), we had to simulate them. However, we aimed to make them as real as possible. In order to increase the likelihood of constructed MIoTs, we performed a sentiment analysis task for each of the six areas in which we partitioned the city of Porto and for each day which the dataset refers to. For this purpose, we leveraged IBM Watson on the social media and blogs it uses as default. Having this data at disposal, our simulator assigns to each instance the most common topics (along with the corresponding occurrences) discussed in that area in the day on which the corresponding route took place. The constructed MIoTs are returned in a format that can be directly processed by the cypher-shell of Neo4J (see below).
Some features of the constructed MIoTs are reported in Table 1. The interested reader can find the MIoTs adopted in the experiments described in this section at the address http://daisy.dii.univpm.it/miot/datasets/virtualIoTs.

Table 1.
Main features of the constructed MIoTs.
We carried out all the tests presented in this section on a server equipped with an Intel I7 Quad Core 7700 HQ processor and 16 GB of RAM with Ubuntu 16.04 operating system.
To implement our approaches we adopted:
- Python, powered with the NetworkX library, as programming language;
- Neo4J (Version 3.4.5) as underlying DBMS; we also exploited some plugins of Neo4J to perform community detection and to compute clustering coefficients.
6.2. Cohesion of the Obtained Topic-Guided Virtual IoTs
Our first test started from the idea that if our approach aims at extracting virtual thematic IoTs, they should present both a structural and a semantic cohesion higher than the corresponding ones characterizing the original IoTs of the MIoT. This experiment was devoted to evaluate if this assumption is verified. We considered two well known structural cohesion parameters used in network analysis literature, namely clustering coefficient and density [61]. Both of them range in the real interval ; the higher their value the higher the corresponding network cohesion. In the following, first we test the supervised approach and, then, we consider the unsupervised one.
6.2.1. Supervised Approach
In this test, we run our supervised approach on ten MIoTs, , ⋯, , consisting of 176, 301, 485, 778, 946, 1256, 1725, 2028, 3544 and 5024 nodes. Clearly, the number of IoTs for each MIoT was equal to six, one for each area of the city of Porto that we have defined. For each MIoT, we submitted a set of 10 queries consisting of 1 (resp., 2, 4, 6, 8 and 10) word(s).
Each query returned a virtual thematic IoT for which we computed the corresponding clustering coefficient and density. Finally, we averaged the obtained results for each MIoT and for each set of queries, and we compared them with the average clustering coefficient and the average density of the corresponding real IoTs. The obtained results are reported in Table 2 and Table 3.

Table 2.
Values of the clustering coefficient for real and virtual IoTs against the size of MIoTs and queries used to generate the virtual IoTs (supervised approach).

Table 3.
Values of the density for real and virtual IoTs against the size of MIoTs and queries used to generate the virtual IoTs (supervised approach).
From the analysis of these tables, we can observe that, in almost all circumstances, the values of both clustering coefficient and density are higher or much higher for the virtual thematic IoTs than for the real ones. This is clearly a confirmation of the goodness of our supervised approach, which returns topic-guided IoTs more cohesive than the original ones. We also observe that when increases, the values of both clustering coefficient and density increases. This can be explained by observing that, in processing Q, our approach takes the portions of networks containing at least one keyword of Q. When increases, the portion of networks selected by our approach increases too, and the probability of selecting a very high number of edges (i.e., a number so high to lead to an increase of clustering coefficient and density) increases as well.
6.2.2. Unsupervised Approach
In this test, we run our unsupervised approach, powered with the Louvain graph clustering algorithm [62] as underlying engine, on the same MIoTs described in Section 6.2.1. For each MIoT, we computed the average clustering coefficient and the average density of real and virtual IoTs. The obtained results are reported in Table 4.

Table 4.
Values of both clustering coefficient and density of real and virtual IoTs against the size of MIoTs (unsupervised approach).
From the analysis of this table we can observe that, in this case, analogously to what happened for the supervised approach, the cohesion level of the virtual IoTs is higher or much higher than the corresponding ones of the real original IoTs. Interestingly, both clustering coefficient and density values obtained by the unsupervised approach are generally higher than those returned by the supervised one, at least when the MIoT size is small. Instead, when the MIoT size is large, they become lower than the ones of the supervised approach. Actually, the increase of both clustering coefficient and density when the MIoT size increases is significant for the supervised approach, whereas it is more limited for the unsupervised one.
6.3. Average Fraction of Merged C-Nodes and Analysis of Node Distribution in Virtual IoTs
Another quality parameter for virtual IoTs returned by our approach regards the average number of merged c-nodes present in each of them. Indeed, the presence of merged c-nodes in an IoT is an indicator of the fact that this IoT is capable of connecting concepts coming from different real IoTs, and, therefore, from concepts whose relationships would have been uncaptured otherwise, or, in other words, that the knowledge it is presenting is new and did not exist previously. Clearly, the higher the fraction of merged c-nodes and the higher the fraction of different original IoTs they belong to, the higher the connecting capability of virtual IoTs.
Also for this experiment, we considered the ten MIoTs described in Section 6.2 and performed the same tasks illustrated therein for both the supervised and the unsupervised approaches. The obtained results are reported in Table 5, Table 6 and Table 7.

Table 5.
Average fraction of merged c-nodes against the size of MIoTs and queries used to generate the virtual IoTs (supervised approach).

Table 6.
Average fraction of real IoTs involved in a virtual IoT against the size of MIoTs and queries used to generate the virtual IoTs (supervised approach).

Table 7.
Average fraction of merged c-nodes and average fraction of real IoTs involved in a virtual IoT against the size of MIoTs (unsupervised approach).
From the analysis of these tables, we observe that both the supervised and the unsupervised approaches return satisfying results. As for the supervised approach, we can observe that the fraction of merged c-nodes increases when the size of MIoT increases. Furthermore, we can also observe a slight increase of this fraction when increases. The same trends can be observed for the average fraction of involved real IoTs, even if, for this parameter, its increase against the increase of is more pronounced. As for the unsupervised approach, we can observe that the average fraction of merged nodes is always very high, independently of the MIoT size. By contrast, in this case, the fraction of involved real IoTs is quite high even if lower than the ones generally observed for the supervised approach. Furthermore, its value does not significantly change when the MIoT size increases.
In order to deepen this investigation, for each virtual IoT, we compared the distribution of its nodes against the real IoTs they belong to. Indeed, if almost all the nodes of a virtual IoT derive from only one real IoT, the information contribution provided by the virtual IoT would be very small because it would be analogous to the one provided by the corresponding real IoT. By contrast, if the nodes of a virtual IoT homogeneously derive from several real IoTs, then the knowledge it provides is really new, and this knowledge would be uncaptured and lost if the new IoT had not been extracted. On the basis of this reasoning, we evaluated the heterogeneity of the provenance of the various nodes of each virtual IoT (see below). For this purpose, we adapted the Herfindahl Index [63] to our context. This index is very used in several research fields of Economics from several decades; for instance, it is exploited to evaluate the concentration degree in an industry.
In order to adapt the Herfindahl Index to our scenario, consider a MIoT consisting of s real IoTs ). Consider, also, a virtual IoT derived by either the supervised or the unsupervised approach. Let be the number of nodes of and let , , be the fraction of the nodes of belonging to (i.e., the real IoT of the MIoT). The Herfindahl Index of is defined as . ranges in the real interval ; the higher its value, the higher the concentration degree of the nodes of in . Clearly, as previously pointed out, one property desired for our approach is the ability to construct virtual IoTs connecting nodes that belong to different real IoTs in such a way as to extract knowledge that would be lost otherwise. If we report this property to the Herfindahl Index, this implies to obtain a value of this index as lower as possible (Consider that, since we have six real IoTs in our MIoTs, the minimum value of the Herfindahl Index is .).
We computed the average Herfindahl Index of the thematic IoTs returned by both the supervised and the unsupervised approaches by considering the ten MIoTs described in Section 6.2 and performing the same tasks illustrated therein. The obtained results are reported in Table 8 and Table 9.

Table 8.
Average Herfindahl Index of virtual IoTs against the size of MIoTs and queries used to generate the virtual IoTs (supervised approach).

Table 9.
Average Herfindahl Index of virtual IoTs against the size of MIoTs (unsupervised approach).
These tables evidence that also the analysis based on object distribution and Herfindahl Index returns very satisfying results that confirm and strengthen those obtained by examining the average fraction of merged nodes involved in a virtual IoT. Interestingly, as for this parameter, we observe that the supervised approach returns excellent results, very close to the best ones. By contrast, the unsupervised approach returns good results, even if those returned by the supervised approach are better.
6.4. Computation Time
In this experiment, we aimed at evaluating the variation of the computation time of both the supervised and the unsupervised approaches against the variation of the size of the involved MIoT. Furthermore, as for the supervised approach, we also evaluated the variation of the computation time against the variation of the size of queries.
To perform this task, we considered the ten MIoTs described in Section 6.2 and carried out the same tasks illustrated therein. Finally, we measured the corresponding average computation times. The obtained results are reported in Figure 1, Figure 2 and Figure 3.
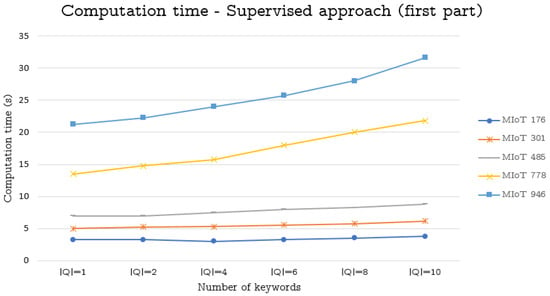
Figure 1.
Computation time (in seconds) against the size of MIoTs and queries used to generate the virtual IoTs (supervised approach)—first part.
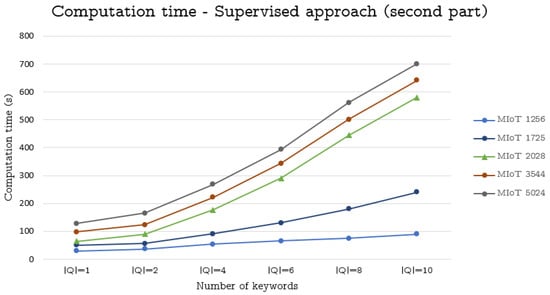
Figure 2.
Computation time (in seconds) against the size of MIoTs and queries used to generate the virtual IoTs (supervised approach)—second part
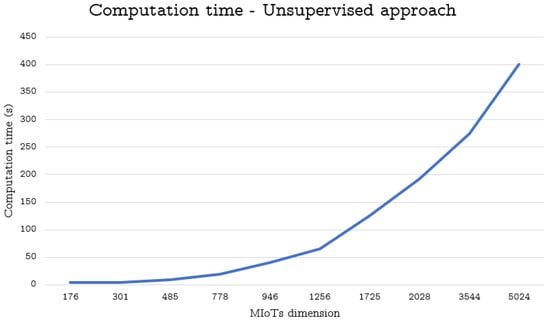
Figure 3.
Computation time (in seconds) against the size of MIoTs (unsupervised approach)
From the analysis of these figures, we can observe that our approaches obtain satisfying results. Specifically, as for the supervised approach, the computation time is always very low for MIoTs having at most 1256 nodes. Instead, for MIoTs with more than 2028 nodes, the computation time is low for or . Then, it increases, even if it remains acceptable for and , whereas it becomes excessive for and . However, with regard to this fact, we must point out that queries consisting of 8 or 10 keywords are very uncommon (It is worth pointing out that the topics considered by our approach for constructing a thing’s profile are extremely generic and heterogeneous. As a consequence, in our scenario, a query with 8 or 10 keywords would encompass a great number of different topics and, as such, it would not be generally able to capture a clear and specific desire of a user.).
As for the unsupervised approach, its computation time is still acceptable also for 2028 nodes. It starts to become excessive with MIoTs consisting of at least 10,000 nodes.
6.5. Our Approaches’ Capability of Improving the Efficiency of Information Dissemination
This experiment was devoted to measure the efficiency of both supervised and unsupervised approaches. The rationale underlying this experiment is that if some information must be transferred from a source object to a target one , the number of objects to be contacted for this task should be minimized. At the same time, if an object is involved in an information dissemination task, it would be desiderable that the information it is transmitting is also useful for it (which, in our case, means that it is in line with the interests of its profile).
In order to perform this experiment, we randomly selected some pairs of (source, target) nodes from our MIoT. Let be one of these pairs. We verified if there existed at least one virtual IoT comprising both and (This is always true for the unsupervised approach, whereas it could not happen for the supervised one.). In the negative case, we discarded that pair. Let be a virtual IoT comprising both and .
After this, we computed the number (resp., ) of MIoT nodes involved in the dissemination of information in presence (resp., absence) of the virtual IoT . Specifically, we computed by performing the information dissemination task only through its nodes; instead, we obtained by performing the same task on the whole MIoT. Finally, we computed: . Clearly, the lower , the higher the contribution of the virtual IoTs in reducing the number of nodes necessary for the information dissemination task and, consequently, the higher the contribution that our virtual IoT detection approach can provide to information dissemination.
We computed the average values of by operating on the ten MIoTs introduced in Section 6.2 and by performing the same tasks described therein for both the supervised and the unsupervised approaches. The obtained results are reported in Table 10 and Table 11.

Table 10.
Average values of against the size of MIoTs and queries used to generate the virtual IoTs (supervised approach).

Table 11.
Average values of against the size of MIoTs (unsupervised approach).
From the analysis of these tables we can observe that both the supervised and the unsupervised approaches really contribute to decrease the number of the nodes of a MIoT involved in the information dissemination, and, therefore, to increase the efficiency of this task. As for the supervised approach, we observe that the decrease of the number of involved nodes is always high. It becomes very high as the MIoT size and the number of keywords composing the query increase. As for the unsupervised approach, we observe that it leads to a decrease of the number of the MIoT nodes involved in the dissemination task. However, this decrease is minimum for small MIoTs, whereas it becomes significant for large ones (i.e., for MIoTs with a number of nodes higher than 1256).
We performed a second experiment in this direction. Specifically, given a pair of a MIoT such that information must be disseminated from to and there exists at least one virtual IoT comprising both and , we computed the fraction (resp., ) of the nodes of the MIoT involved in the diffusion of information from to and having at least one content of the disseminated information registered in their profile (which implies that, in principle, they could benefit from the information they are required to disseminate). As in the previous experiment, we computed by assuming the existence of and, hence, by performing the information dissemination task through it; by contrast, we computed by carrying out the information dissemination task through the whole MIoT. Finally, we computed . Roughly speaking, it denotes how much the presence of the virtual IoT can contribute to require information dissemination tasks only to nodes possibly benefiting of it. A value of this coefficient higher than 1 denotes a positive contribution of ; the higher this value the higher the contribution. As in the previous experiment, we computed the average values of by operating on the ten MIoTs introduced in Section 6.2 and by performing the same tasks described therein for both the supervised and the unsupervised approaches. The obtained results are reported in Table 12 and Table 13.

Table 12.
Average values of against the size of MIoTs and queries used to generate the virtual IoTs (supervised approach).

Table 13.
Average values of against the size of MIoTs (unsupervised approach).
The analysis of these tables is a further confirmation of the efficiency of our approach. Indeed, thanks to the presence of virtual IoTs, the fraction of nodes participating to the spreading of information that can also benefit from this task increases remarkably.
The results of Table 10 and Table 11, along with the ones of Table 12 and Table 13, agree to evidence that the discovery of virtual IoTs is highly beneficial in terms of efficiency for the information dissemination task in a MIoT. In this case, the contribution of in increasing the efficiency of the spreading task, by limiting it mainly to nodes that could benefit from the information they are disseminating, is very high for the supervised approach when or . When increases, this contribution decreases, even if it remains still significant. As for the unsupervised approach, the contribution of can be always observed even if it is less evident than the one characterizing the supervised approach.
6.6. Number and Size of Returned Virtual IoTs
This last experiment makes sense only for the unsupervised approach. Through it we aimed at investigating how the number and the size of returned virtual IoTs (and, therefore, the number and the size of returned clusters) vary when the MIoT size increases. To make this experiment significant, we maintained constant all the parameters of the adopted clustering algorithm. We considered the MIoTs used in the previous experiments because, in this way, we had the possibility to investigate MIoT sizes ranging from 176 to 5024 nodes. We report the obtained results in Table 14.

Table 14.
Average size and number of virtual IoTs against the increase of the MIoT size (unsupervised approach).
From the analysis of this table we can observe that the average size of virtual IoTs:
- increases when the MIoT size ranges from 176 to 946;
- slightly increases when the MIoT size ranges from 946 to 2028;
- remains essentially constant when the MIoT size is higher than 2028.
In the meantime, the number of clusters:
- slightly increases when the MIoT size ranges from 176 to 946;
- increases when the MIoT size ranges from 946 to 2028;
- highly increases when the MIoT size is higher than 2028.
The obtained results are extremely interesting because they confirm the soundness of the reasoning made in Section 5.3. In particular, this experiment confirms the scalability of our approach. As a matter of fact, after the virtual IoTs have been constructed offline, their usage for querying and for the other tasks of interest for the user can be performed online. Now, we observed that the number of available virtual IoTs highly increases when the MIoT size increases. However, because the size of each virtual IoT is only slightly impacted by the growth of the corresponding MIoT, and because user tasks generally involve one or at most a few of available virtual IoTs, we can conclude that our approach is scalable with respect to the size variation of the MIoT.
7. Conclusions
In this paper, we have discussed about the attempt of “humanizing” things. We have seen that this trend will become increasingly challenging in the future because things are becoming more and more smart and social. As a consequence, it appears natural to apply concepts typical of social networking to the Internet of Things. Actually, as things are becoming increasingly heterogeneous in their formats, semantics and behaviors, it appears even better to apply social internetworking ideas and concepts to this scenario.
For this reason, we have decided to adopt the MIoT paradigm as the reference one for our proposal. With the support of this paradigm, we have proposed a rich and high-level abstraction profile of a thing, taking into account the content that it exchanged with the other things in the past. Then, we have introduced the concept of topic-guided virtual IoT and we have proposed a supervised and an unsupervised approach to constructing topic-guided virtual IoTs in a Multi-IoT scenario.
This paper must not be considered as an ending point; on the contrary, it is a starting point for future research efforts. Indeed, the definition of a thing’s profile and the usage of paradigms, like MIoT, allowing multiple IoTs to be modeled in a way analogous to how multiple social networks interacting with each other are modeled, allow us to investigate the possible extension to the IoT context of many research themes already analyzed for social networks. For instance, it could be possible: (i) to model the concepts of trust and reputation of a thing in the IoTs it belongs to; (ii) to develop “team building” approaches aiming at constructing teams of things to perform a certain activity; (iii) to investigate new forms of centrality of a thing in a MIoT based on both its position and its profile. Actually, these are just three of the many possible future developments of our research in such a rapidly evolving and very promising scenario.
Author Contributions
Conceptualization, D.U. and A.N.; methodology, D.U. and L.V.; software, L.V. and P.L.G.; validation, L.V. and P.L.G.; formal analysis, D.U. and A.N.; investigation, A.N. and L.V.; resources, A.N.; data curation, D.U. and L.V.; writing–original draft preparation, D.U., A.N., P.L.G. and L.V.; writing–review and editing, D.U. and A.N.; visualization, L.V.; supervision, D.U.; project administration, Domenico Ursino.; funding acquisition, D.U.
Funding
This work was partially funded by the Department of Information Engineering at the Polytechnic University of Marche under the project “A network-based approach to uniformly extract knowledge and support decision making in heterogeneous application contexts” (RSAB 2018).
Conflicts of Interest
The authors declare no conflict of interest.
References
- Guinard, D.; Trifa, V.; Mattern, F.; Wilde, E. From the internet of things to the web of things: Resource-oriented architecture and best practices. In Architecting the Internet of Things; Springer: Berlin, Germany, 2011; pp. 97–129. [Google Scholar]
- Santos, J.; Wauters, T.; Volckaert, B.; Turck, F.D. Resource Provisioning in Fog Computing: From Theory to Practice. Sensors 2019, 19, 2238. [Google Scholar] [CrossRef] [PubMed]
- Distefano, S.; Merlino, G.; Puliafito, A. Enabling the cloud of things. In Proceedings of the International Conference on Innovative Mobile and Internet Services in Ubiquitous Computing (IMIS’2012), Palermo, Italy, 4–6 July 2012; pp. 858–863. [Google Scholar]
- Park, M.; Oh, H.; Lee, K. Security Risk Measurement for Information Leakage in IoT-Based Smart Homes from a Situational Awareness Perspective. Sensors 2019, 19, 2148. [Google Scholar] [CrossRef] [PubMed]
- Atzori, L.; Iera, A.; Morabito, G. The Internet of Things: A survey. In Computer Networks; Elsevier: Amsterdam, The Netherlands, 2010; Volume 54, pp. 2787–2805. [Google Scholar]
- Gubbi, J.; Buyya, R.; Marusic, S.; Palaniswami, M. Internet of Things (IoT): A vision, architectural elements, and future directions. In Future Generation Computer Systems; Elsevier: Amsterdam, The Netherlands, 2013; Volume 29, pp. 1645–1660. [Google Scholar]
- Lee, J.; Yu, S.; Park, K.; Park, Y.; Park, Y. Secure Three-Factor Authentication Protocol for Multi-Gateway IoT Environments. Sensors 2019, 19, 2358. [Google Scholar] [CrossRef] [PubMed]
- Araniti, G.; Orsino, A.; Militano, L.; Wang, L.; Iera, A. Context-aware information diffusion for alerting messages in 5G mobile social networks. IEEE Int. Things J. 2017, 4, 427–436. [Google Scholar] [CrossRef]
- Atzori, L.; Iera, A.; Morabito, G. SIoT: Giving a social structure to the Internet of Things. IEEE Commun. Lett. 2011, 15, 1193–1195. [Google Scholar] [CrossRef]
- Farris, I.; Girau, R.; Militano, L.; Nitti, M.; Atzori, L.; Iera, A.; Morabito, G. Social virtual objects in the edge cloud. IEEE Cloud Comput. 2015, 2, 20–28. [Google Scholar] [CrossRef]
- Atzori, L.; Iera, A.; Morabito, G. From “smart objects” to “social objects”: The next evolutionary step of the Internet of Things. IEEE Commun. Mag. 2014, 52, 97–105. [Google Scholar] [CrossRef]
- Saleem, Y.; Crespi, N.; Rehmani, M.; Copeland, R.; Hussein, D.; Bertin, E. Exploitation of social IoT for recommendation services. In Proceedings of the World Forum on Internet of Things (WF-IoT’16), Reston, VA, USA, 12–14 December 2016; pp. 359–364. [Google Scholar]
- Baldassarre, G.; Lo Giudice, P.; Musarella, L.; Ursino, D. A paradigm for the cooperation of objects belonging to different IoTs. In Proceedings of the International Database Engineering & Applications Symposium (IDEAS 2018), Villa San Giovanni, Italy, 18–20 June 2018; pp. 157–164. [Google Scholar]
- Baldassarre, G.; Lo Giudice, P.; Musarella, L.; Ursino, D. The MIoT paradigm: main features and an “ad-hoc” crawler. Future Gener. Comput. Syst. 2019, 92, 29–42. [Google Scholar] [CrossRef]
- Buccafurri, F.; Foti, V.; Lax, G.; Nocera, A.; Ursino, D. Bridge Analysis in a Social Internetworking Scenario. Inf. Sci. 2013, 224, 1–18. [Google Scholar] [CrossRef]
- McPherson, M.; Smith-Lovin, L.; Cook, J. Birds of a feather: Homophily in social networks. Annu. Rev. Soc. 2001, 27, 415–444. [Google Scholar] [CrossRef]
- Şimşek, Ö.; Jensen, D. Navigating networks by using homophily and degree. Proc. Natl. Acad. Sci. USA 2008, 105, 12758–12762. [Google Scholar] [CrossRef] [PubMed]
- Schiaffino, S.; Amandi, A. Intelligent user profiling. In Artificial Intelligence An International Perspective; Springer: Berlin, Germany, 2009; pp. 193–216. [Google Scholar]
- Plantié, M.; Crampes, M. Survey on social community detection. In Social Media Retrieval; Springer: Berlin, Germany, 2013; pp. 65–85. [Google Scholar]
- Atzori, L.; Iera, A.; Morabito, G. Understanding the Internet of Things: definition, potentials, and societal role of a fast evolving paradigm. Ad Hoc Netw. 2017, 56, 122–140. [Google Scholar] [CrossRef]
- Miorandi, D.; Sicari, S.; Pellegrini, F.D.; Chlamtac, I. Internet of things: Vision, applications and research challenges. Ad Hoc Netw. 2012, 10, 1497–1516. [Google Scholar] [CrossRef]
- Perera, C.; Zaslavsky, A.; Christen, P.; Georgakopoulos, D. Context aware computing for the Internet of Things: A survey. IEEE Commun. Surv. Tutor. 2014, 16, 414–454. [Google Scholar] [CrossRef]
- Tsai, C.; Lai, C.; Vasilakos, A. Future Internet of Things: open issues and challenges. Wirel. Netw. 2014, 20, 2201–2217. [Google Scholar] [CrossRef]
- Stojmenovic, I.; Olariu, S. Data-centric protocols for wireless sensor networks. In Handbook of Sensor Networks: Algorithms and Architectures; Wiley: Hoboken, NJ, USA, 2005; pp. 417–456. [Google Scholar]
- Zhang, Y.; Raychadhuri, D.; Grieco, L.; Baccelli, E.; Burke, J.; Ravindran, R.; Wang, G.; Lindgren, A.; Ahlgren, B.; Schelen, O. Requirements and Challenges for IoT over ICN. 2015. Available online: https://tools.ietf.org/html/draft-zhang-icnrg-icniot-requirements-00 (accessed on 30 March 2019).
- Zhang, Y.; Raychadhuri, D.; Ravindran, R.; Wang, G. ICN Based Architecture for IoT. 2013. Available online: https://tools.ietf.org/html/draft-zhang-iot-icn-challenges-02 (accessed on 30 March 2019).
- Amadeo, M.; Campolo, C.; Iera, A.; Molinaro, A. Named data networking for IoT: An architectural perspective. In Proceedings of the European Conference on Networks and Communications (EuCNC’2014), Bologna, Italy, 23–26 June 2014; pp. 1–5. [Google Scholar]
- Qin, Y.; Sheng, Q.; Falkner, N.; Dustdar, S.; Wang, H.; Vasilakos, A. When things matter: A survey on data-centric internet of things. J. Netw. Comput. Appl. 2016, 64, 137–153. [Google Scholar] [CrossRef]
- Amadeo, M.; Campolo, C.; Quevedo, J.; Corujo, D.; Molinaro, A.; Iera, A.; Aguiar, R.; Vasilakos, A. Information-centric networking for the internet of things: challenges and opportunities. IEEE Netw. 2016, 30, 92–100. [Google Scholar] [CrossRef]
- Perera, C.; Qin, Y.; Estrella, J.; Reiff-Marganiec, S.; Vasilakos, A. Fog computing for sustainable smart cities: A survey. ACM Comput. Surv. (CSUR) 2017, 50, 32. [Google Scholar] [CrossRef]
- Tei, K.; Gurgen, L. ClouT: Cloud of things for empowering the citizen clout in smart cities. In Proceedings of the World Forum on Internet of Things (WF-IoT’2014), Seoul, Korea, 6–8 March 2014; pp. 369–370. [Google Scholar]
- Karnouskos, S. Smart houses in the smart grid and the search for value-added services in the cloud of things era. In Proceedings of the International Conference on Industrial Technology (ICIT’2013), Cape Town, South Africa, 25–28 February 2013; pp. 2016–2021. [Google Scholar]
- Xu, K.; Qu, Y.; Yang, K. A tutorial on the internet of things: From a heterogeneous network integration perspective. IEEE Netw. 2016, 30, 102–108. [Google Scholar] [CrossRef]
- Wan, J.; Tang, S.; Shu, Z.; Li, D.; Wang, S.; Imran, M.; Vasilakos, A. Software-defined industrial internet of things in the context of industry 4.0. IEEE Sens. J. 2016, 16, 7373–7380. [Google Scholar] [CrossRef]
- Wan, J.; Liu, J.; Shao, Z.; Vasilakos, A.; Imran, M.; Zhou, K. Mobile crowd sensing for traffic prediction in internet of vehicles. Sensors 2016, 16, 88. [Google Scholar] [CrossRef] [PubMed]
- Guinard, D.; Fischer, M.; Trifa, V. Sharing using social networks in a composable web of things. In Proceedings of the International Conference on Pervasive Computing and Communications (PERCOM 2010), Mannheim, Germany, 29 March–2 April 2010; pp. 702–707. [Google Scholar]
- Ning, H.; Wang, Z. Future internet of things architecture: like mankind neural system or social organization framework? IEEE Commun. Lett. 2011, 15, 461–463. [Google Scholar] [CrossRef]
- Kranz, M.; Roalter, L.; Michahelles, F. Things that Twitter: social networks and the Internet of Things. In Proceedings of the International Workshop on Pervasive Computing (Pervasive 2010), Helsinki, Finland, 17–20 May 2010; pp. 1–10. [Google Scholar]
- Holmquist, L.; Mattern, F.; Schiele, B.; Alahuhta, P.; Beigl, M.; Gellersen, H. Smart-its friends: A technique for users to easily establish connections between smart artefacts. In Proceedings of the International Conference on Ubiquitous Computing (Ubicomp’2001), Atlanta, GA, USA, 30 September–2 October 2001; pp. 116–122. [Google Scholar]
- Atzori, L.; Iera, A.; Morabito, G.; Nitti, M. The Social Internet of Things (SIoT)– when social networks meet the Internet of Things: Concept, architecture and network characterization. Comput. Netw. 2012, 56, 3594–3608. [Google Scholar] [CrossRef]
- Ortiz, A.; Hussein, D.; Park, S.; Han, S.; Crespi, N. The cluster between internet of things and social networks: Review and research challenges. IEEE Int. Things J. 2014, 1, 206–215. [Google Scholar] [CrossRef]
- Oh, S.; Kim, Y.; Cho, S. An Interoperable Access Control Framework for Diverse IoT Platforms Based on OAuth and Role. Sensors 2019, 19, 1884. [Google Scholar] [CrossRef] [PubMed]
- Sobral, J.; Rodrigues, J.; Rabêlo, R.; Al-Muhtadi, J.; Korotaev, V. Routing Protocols for Low Power and Lossy Networks in Internet of Things Applications. Sensors 2019, 19, 2144. [Google Scholar] [CrossRef] [PubMed]
- Ganzha, M.; Paprzycki, M.; Pawłowski, W.; Szmeja, P.; Wasielewska, K. Semantic interoperability in the Internet of Things: An overview from the INTER-IoT perspective. J. Netw. Comput. Appl. 2017, 81, 111–124. [Google Scholar] [CrossRef]
- Li, J.; Wang, H.; Khan, S. A semantics-based approach to large-scale mobile social networking. Mob. Netw. Appl. 2012, 17, 192–205. [Google Scholar] [CrossRef]
- Suciu, G.; Halunga, S.; Vulpe, A.; Suciu, V. Generic platform for IoT and cloud computing interoperability study. In Proceedings of the International Symposium on Signals, Circuits and Systems (ISSCS’13), Iasi, Romania, 11–12 July 2013; pp. 1–4. [Google Scholar]
- Zhao, F.; Sun, Z.; Jin, H. Topic-centric and semantic-aware retrieval system for internet of things. Inf. Fusion 2015, 23, 33–42. [Google Scholar] [CrossRef]
- Nocera, A.; Ursino, D. PHIS: a system for scouting potential hubs and for favoring their “growth” in a Social Internetworking Scenario. Knowl. Based Syst. 2012, 36, 288–299. [Google Scholar] [CrossRef]
- Diamantini, D.; Potena, D.; Storti, E. A virtual mart for knowledge discovery in databases. Inf. Syst. Front. 2013, 15, 447–463. [Google Scholar] [CrossRef]
- Wang, L. Using the relationship of shared neighbors to find hierarchical overlapping communities for effective connectivity in IoT. In Proceedings of the International Conference on Pervasive Computing and Applications (ICPCA’11), Port Elizabeth, South Africa, 26–28 October 2011; pp. 400–406. [Google Scholar]
- Karyotis, V.; Tsitseklis, K.; Sotiropoulos, K.; Papavassiliou, S. Big Data Clustering via Community Detection and Hyperbolic Network Embedding in IoT Applications. Sensors 2018, 18, 1205. [Google Scholar] [CrossRef] [PubMed]
- Barthwal, R.; Misra, S.; Obaidat, M. Finding overlapping communities in a complex network of social linkages and Internet of things. J. Supercomput. 2013, 66, 1749–1772. [Google Scholar] [CrossRef]
- Kowshalya, A.; Valarmathi, M. Community Detection in the Social Internet of Things Based on Movement, Preference and Social Similarity. Stud. Inf. Control 2016, 25, 499–506. [Google Scholar] [CrossRef]
- Nitti, M.; Girau, R.; Atzori, L. Trustworthiness management in the social internet of things. IEEE Trans. Knowl. Data Eng. 2014, 26, 1253–1266. [Google Scholar] [CrossRef]
- Misra, S.; Barthwal, R.; Obaidat, M.S. Community detection in an integrated Internet of Things and social network architecture. In Proceedings of the IEEE Global Communications Conference (GLOBECOM 2012), Anaheim, CA, USA, 3–7 December 2012; pp. 1647–1652. [Google Scholar]
- IPSO Alliance. 2019. Available online: https://www.ipso-alliance.org/ (accessed on 30 March 2019).
- Bernstein, P.; Madhavan, J.; Rahm, E. Generic Schema Matching, Ten Years Later. Proc. VLDB Endow. 2011, 4, 695–701. [Google Scholar]
- De Meo, P.; Quattrone, G.; Terracina, G.; Ursino, D. Integration of XML Schemas at various “severity” levels. Inf. Syst. 2006, 31, 397–434. [Google Scholar] [CrossRef]
- Schaeffer, S. Graph clustering. Comput. Sci. Rev. 2007, 1, 27–64. [Google Scholar] [CrossRef]
- Fahad, A.; Alshatri, N.; Tari, Z.; Alamri, A.; Khalil, I.; Zomaya, A.; Foufou, S.; Bouras, A. A survey of clustering algorithms for big data: Taxonomy and empirical analysis. IEEE Trans. Emerg. Top. Comput. 2014, 2, 267–279. [Google Scholar] [CrossRef]
- Tsvetovat, M.; Kouznetsov, A. Social Network Analysis for Startups: Finding Connections on the Social Web; O’Reilly Media, Inc.: Sebastopol, CA, USA, 2011. [Google Scholar]
- Blondel, V.; Guillaume, J.; Lambiotte, R.; Lefebvre, E. Fast unfolding of communities in large networks. J. Stat. Mech. Theory Exp. 2008, 2008, P10008. [Google Scholar] [CrossRef]
- Hirschman, A. The paternity of an index. Am. Econ. Rev. 1964, 54, 761–762. [Google Scholar]
© 2019 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).