Mobile Code Anti-Reversing Scheme Based on Bytecode Trapping in ART
Abstract
1. Introduction
2. Background
2.1. Differences between Dalvik VM and ART
2.1.1. Installation and Execution
2.1.2. Compilation
2.2. Runtime Environment Transition
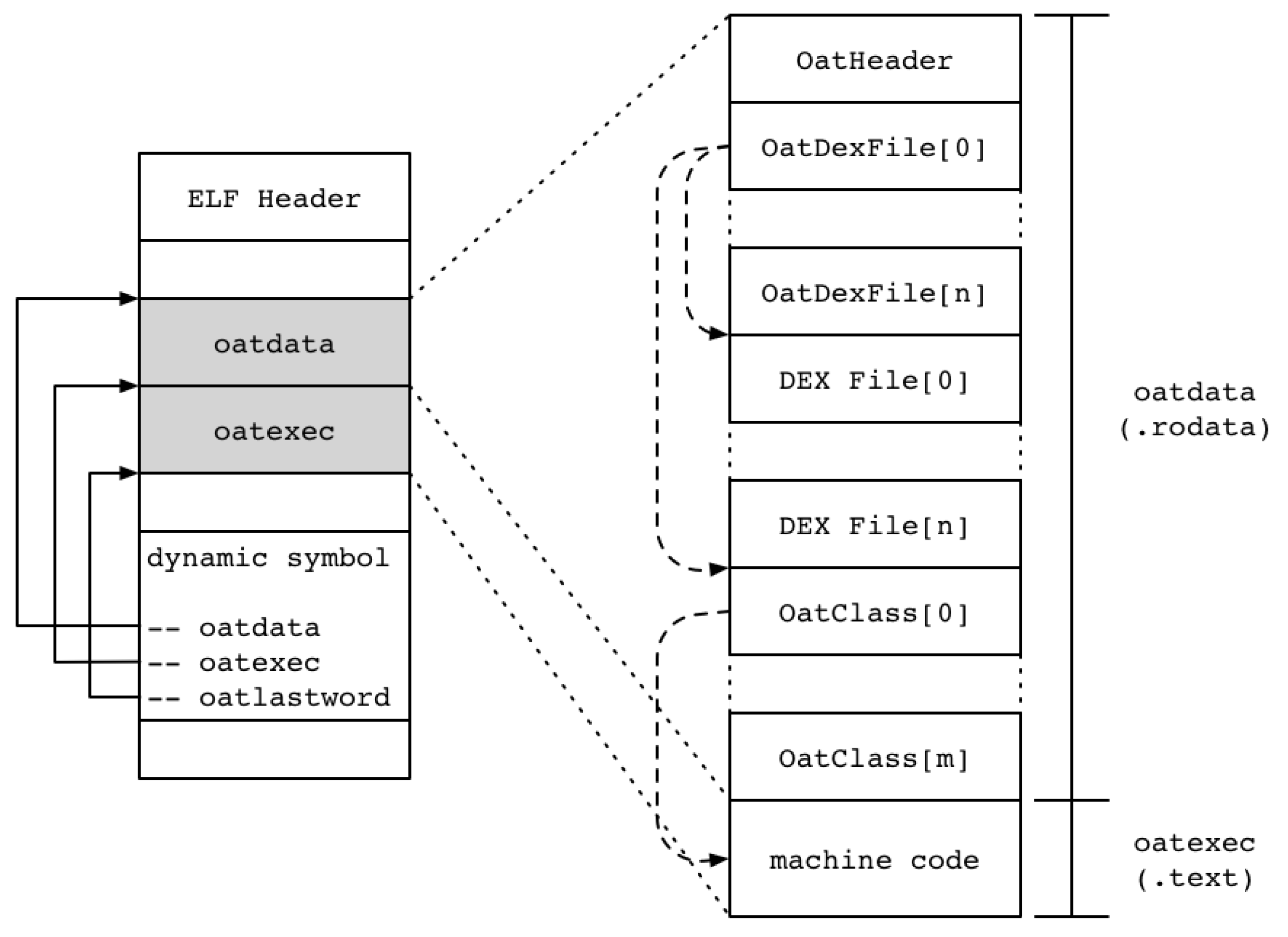
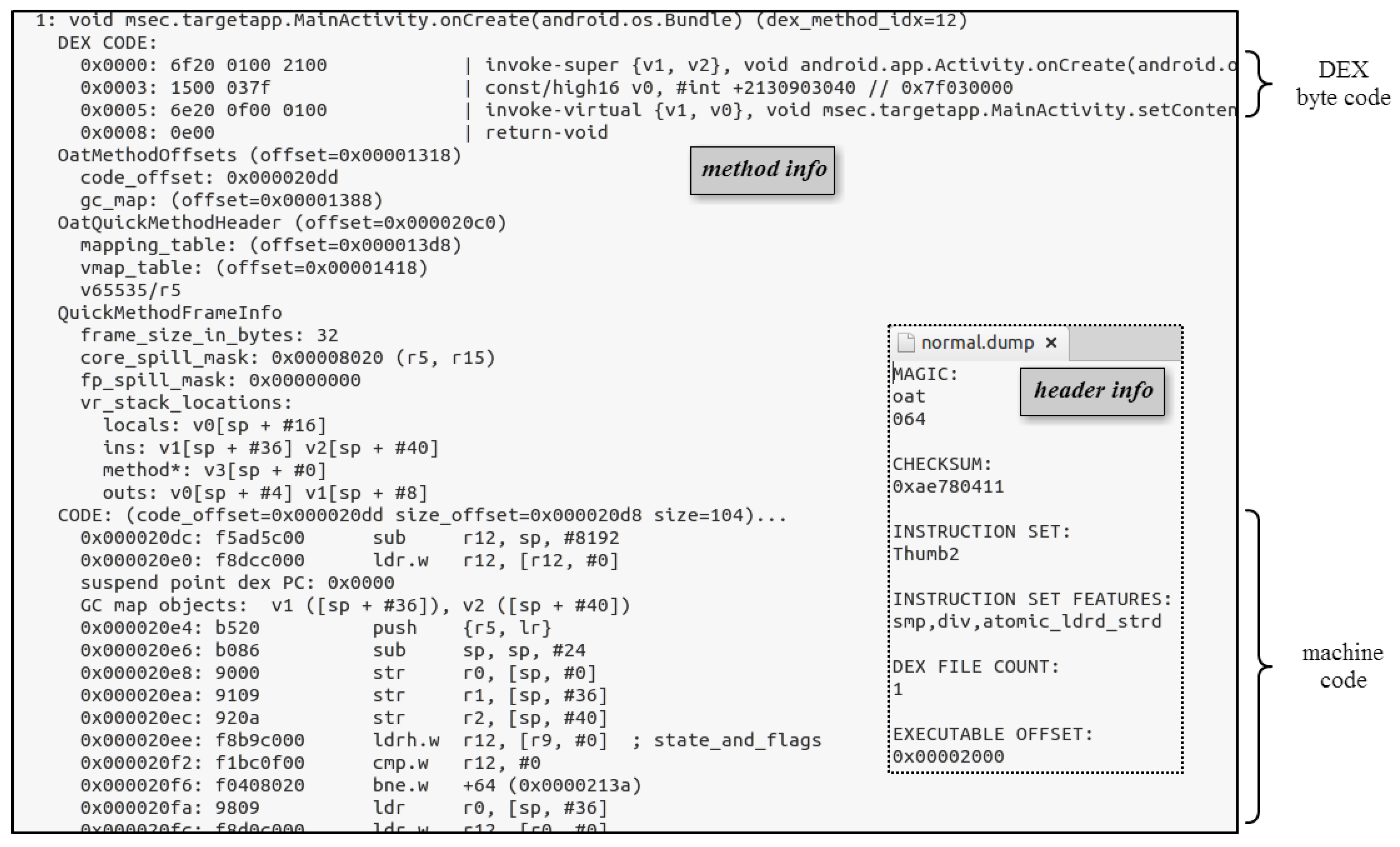
2.2.1. OAT File Structure
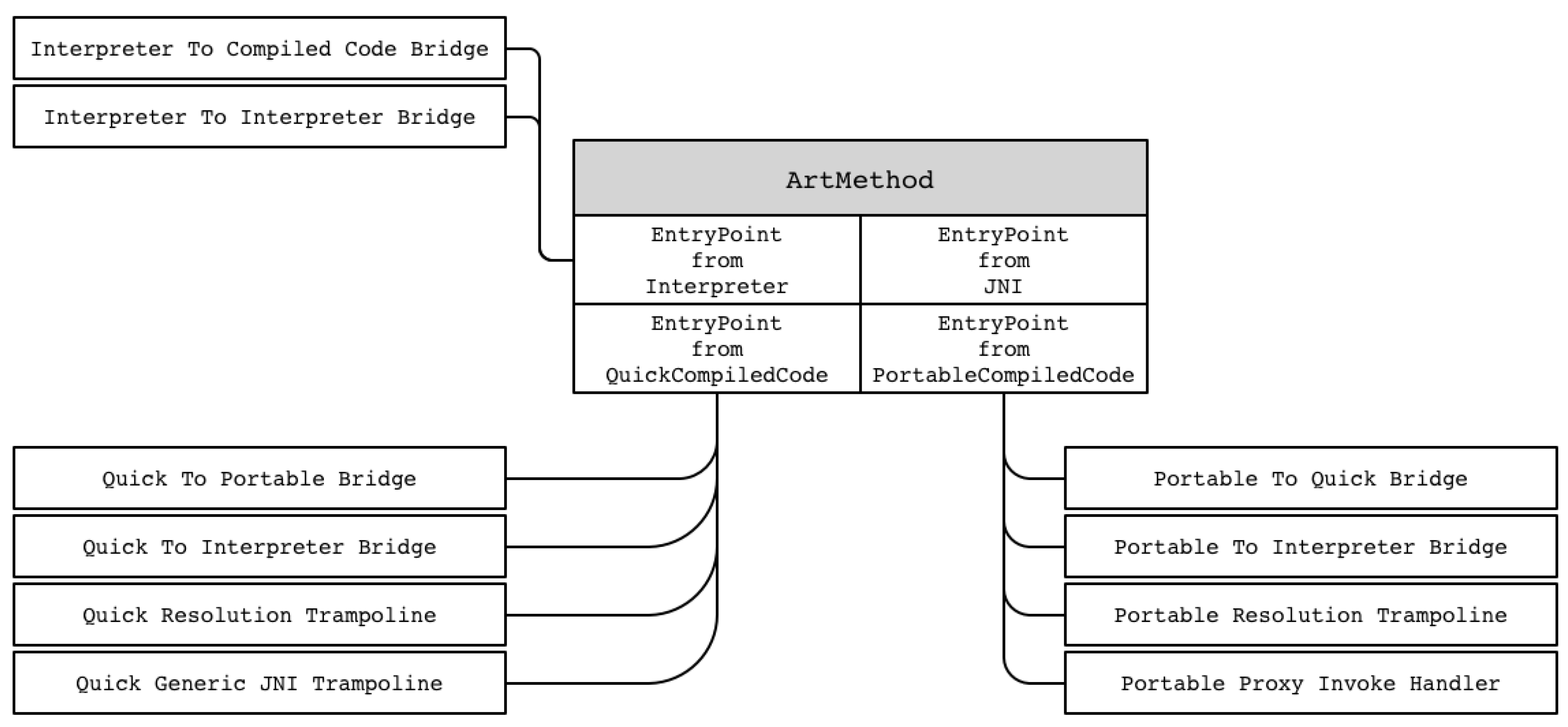
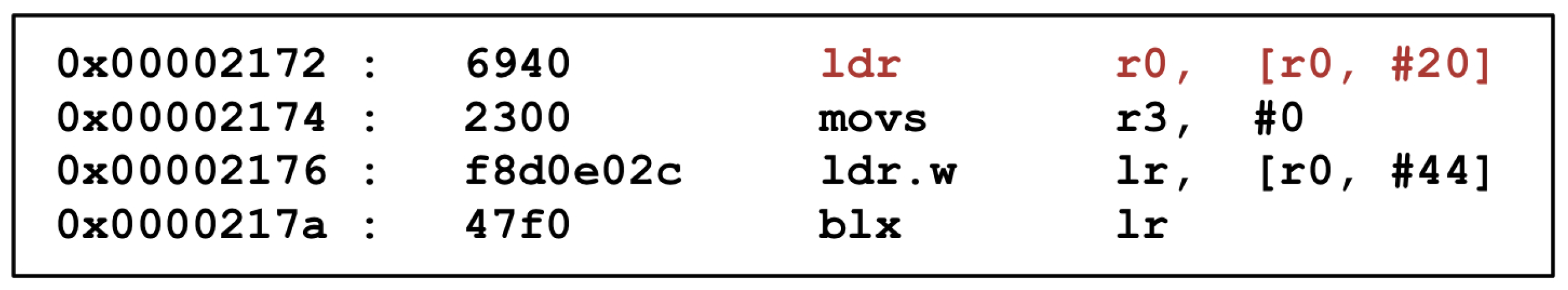
2.2.2. Method Execution and Entry Point Management
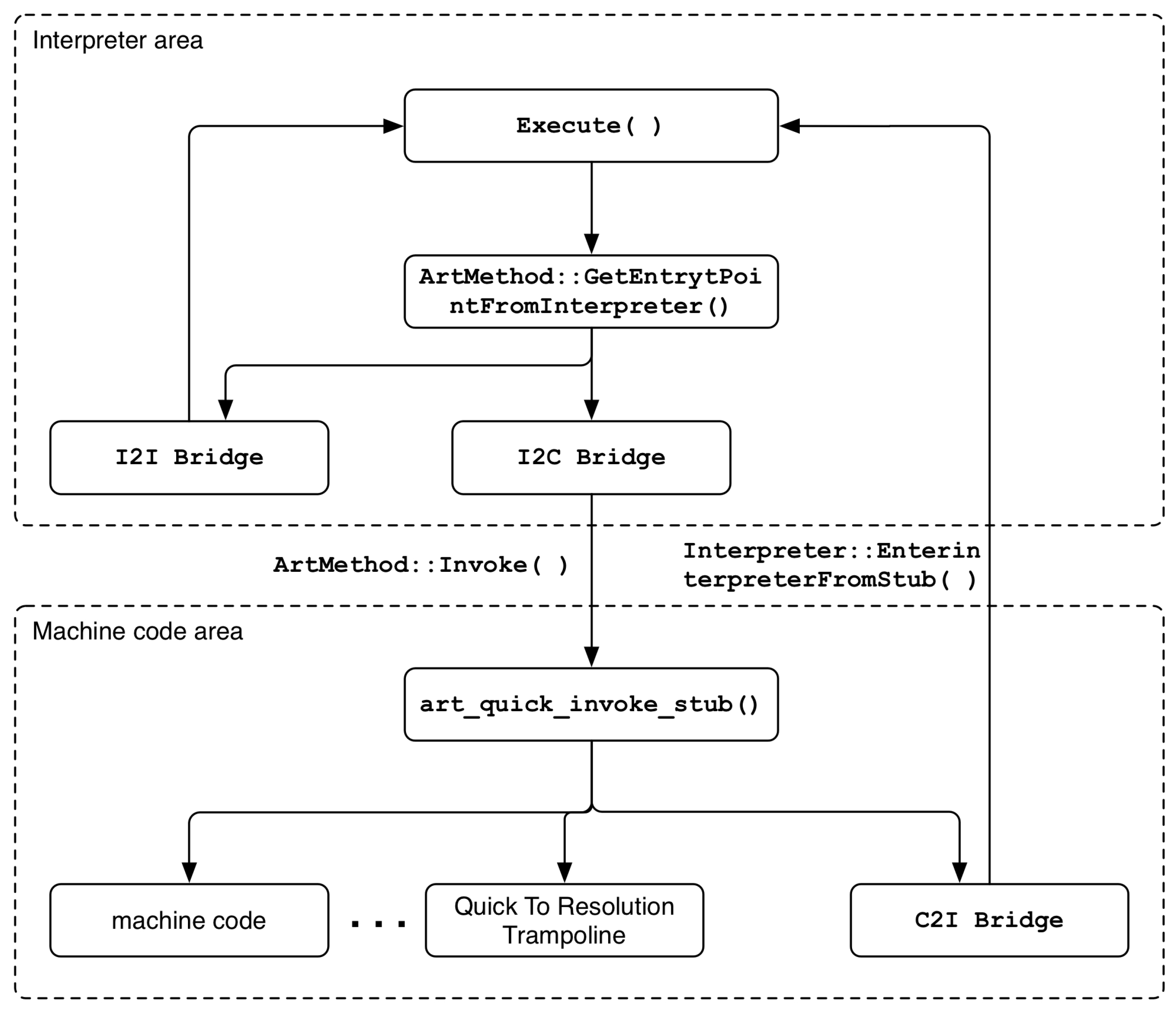
2.2.3. Bridge and Trampoline
- Interpreter_To_Interpreter_Bridge (I2I Bridge): This bridge is used to maintain the execution flow from the interpreter area to the interpreter area. After calling the callee method in the call stack frame, it checks whether the class to which the method belongs is initialized, and finally executes the method through the Execute() function in the interpreter area.
- Interpreter_To_Compiled_Code_Bridge (I2C Bridge): This bridge is called when switching the execution flow from the interpreter area to the machine code area. In the case of Interpreter_To_Interpreter_Bridge, the callee method is searched from the call stack frame to check whether the class to which the method belongs is initialized. However, the actual method is executed through the Invoke() function, which is a member method of the ArtMethod class, not the Execute() function. The Invoke() function internally calls the art_quick_invoke_stub() function, which is written in assembly language, to execute the machine code of the method. In other words, the Entry_Point_from_Quick_CompiledCode of the method is checked again, the entry set point is entered, and finally the machine code of the method is executed.
- Quick_To_Interpreter_Bridge (C2I Bridge): This bridge is used when a transition from the compiled machine code execution region to the interpreter region is required. The bridge internally calls the EnterInterpreterFromStub() function, which causes the method to be executed in the interpreter area via the Execute() function, exactly like the final execution of Interpreter_To_Interpreter_Bridge described above.
3. Challenges to Reverse Engineering
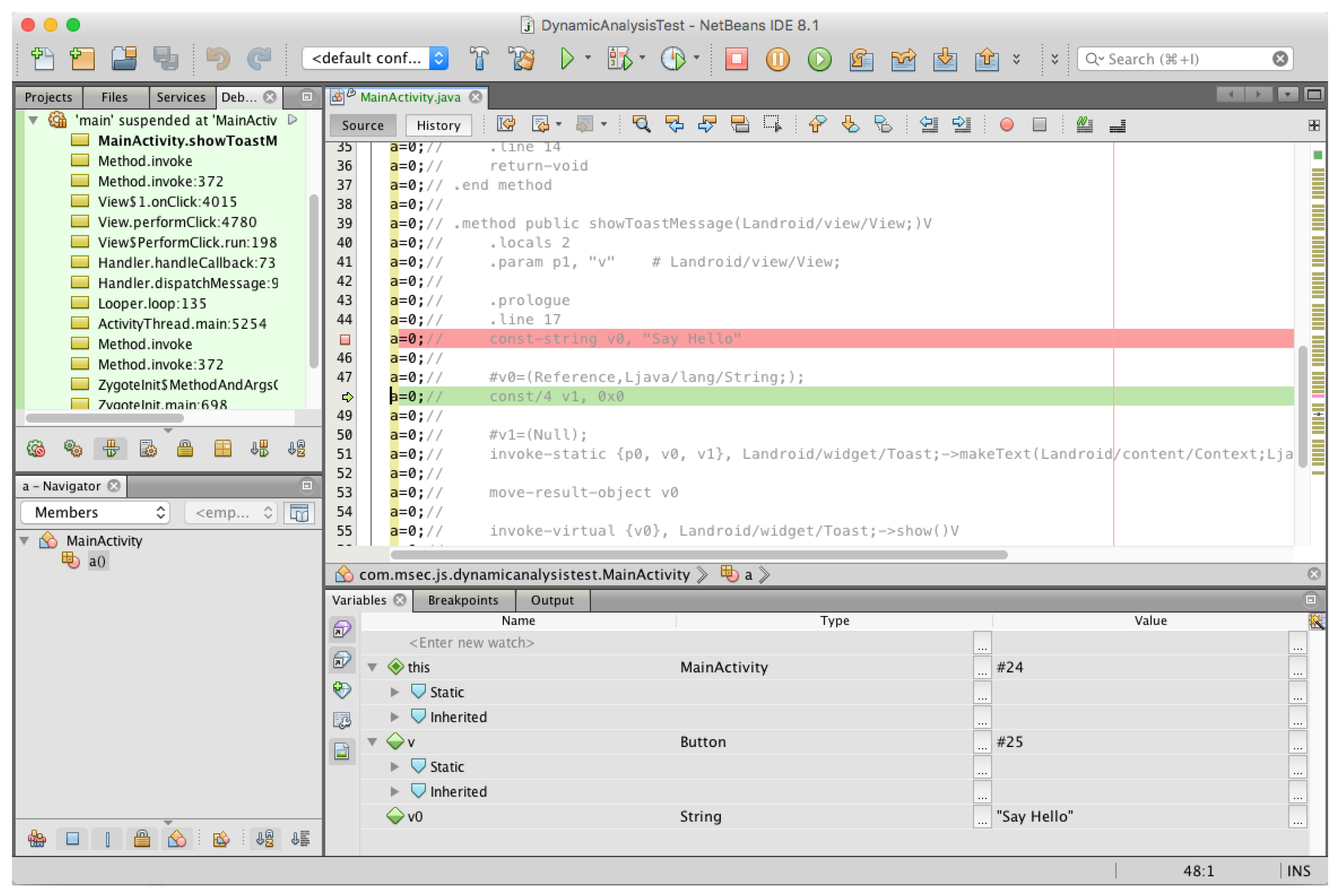
3.1. Dynamic Debugging Support
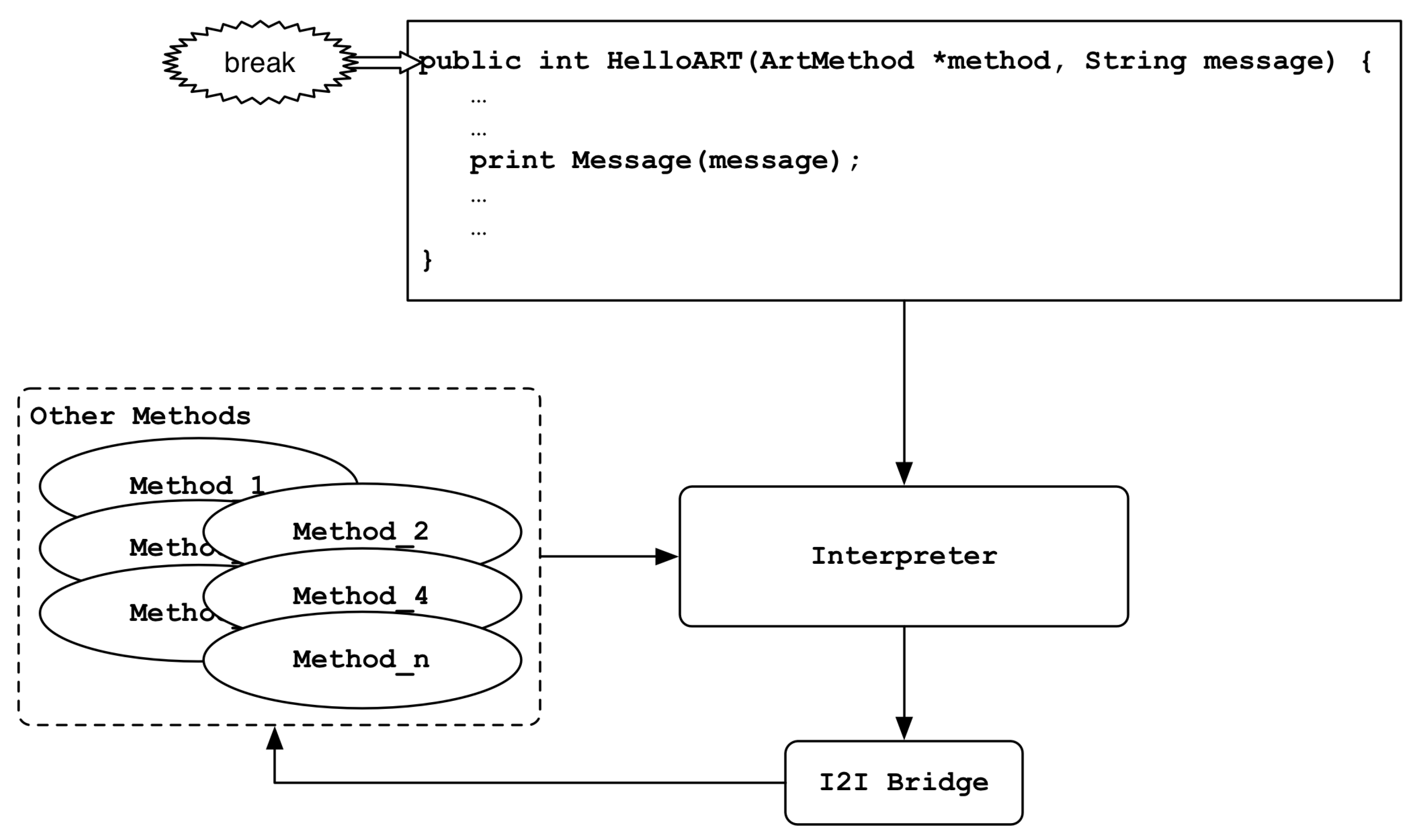
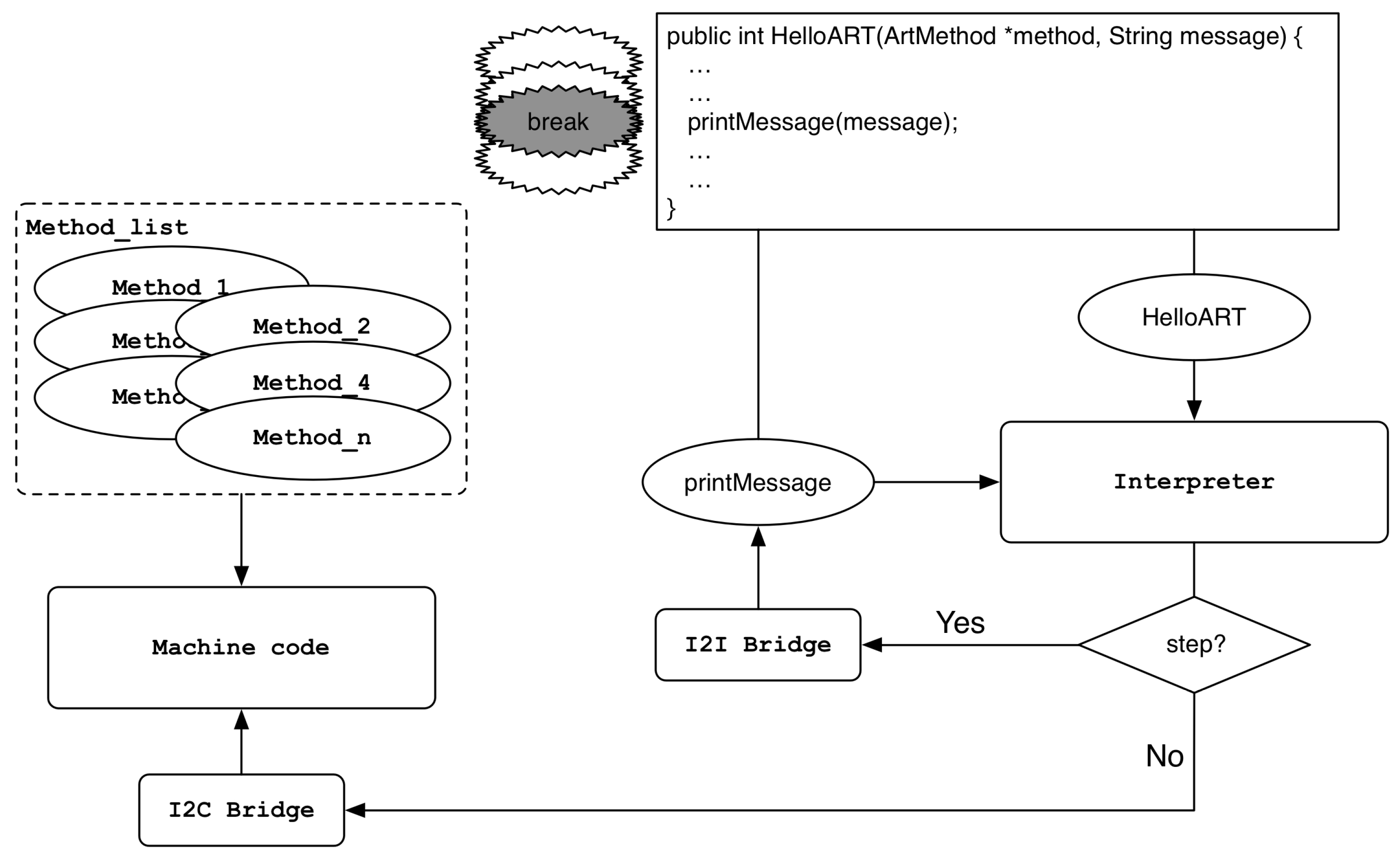
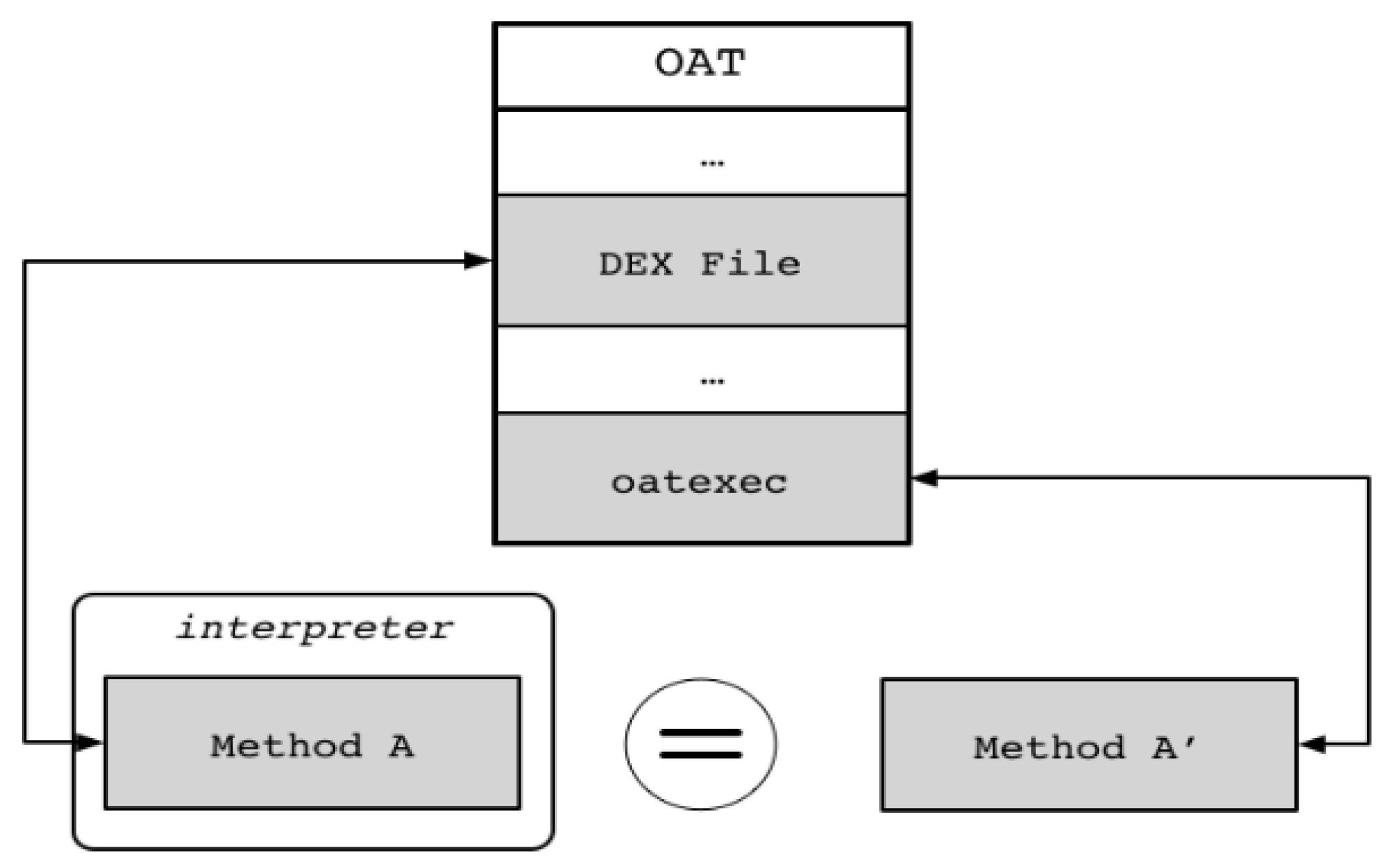
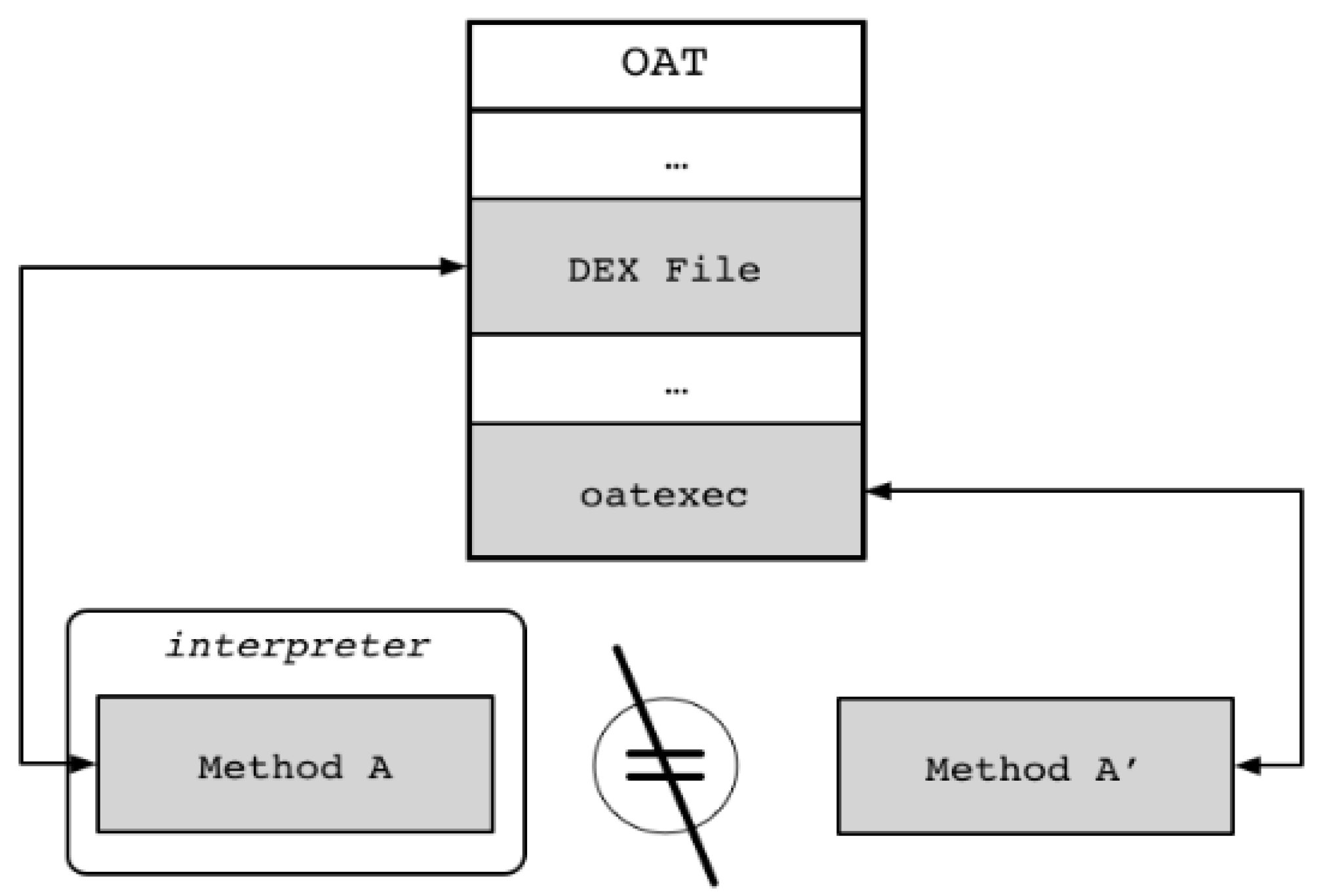
- kFullDeoptimization/kFullUndeoptimization: When the kFullDeoptimization request is passed to the ProcessDeoptimizationRequest() function, bridges and trampolines are set at entry points of the method so that all methods of the application operate in the interpreter domain. Conversely, in the case of a kFullUndeoptimization request, method execution through the interpreter is disabled, and bridges and trampolines are set at entry points of the method to act as the method’s original execution flow. As shown in Figure 4, the above request occurs when we break or release a breakpoint in a method’s header.
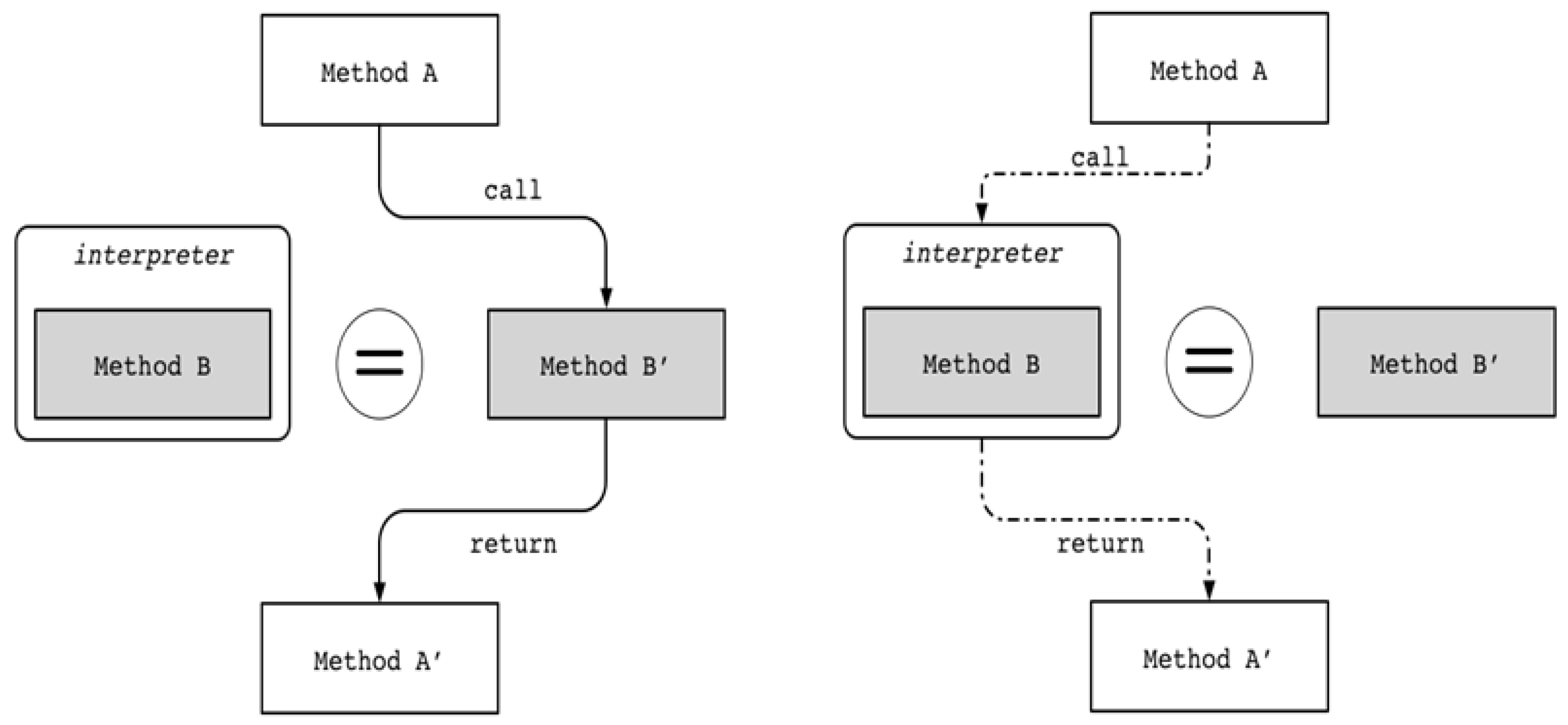
- kSelectiveDeoptimization/kSelectiveUndeoptimization: kSelectiveDeoptimization is a request to execute only certain methods in the interpreter area. As shown in Figure 5, when a breakpoint is placed on or off a method body, the request is made and the entry points of the methods are set to the appropriate bridges and trampolines via the UpdateEntryPoints() function.Assume that there is a part in the body of Method A that calls Method B. It is important to note that Method A is executed in the interpreter area, and Method B, in the same step as step over or step into the part where Method B is called, is executed in the interpreter area. On the contrary, in case of resume, another entry point update is performed, and Method B is executed as machine code through Interpreter_To_Compiled_Code_Bridge. When the call to Method B in the body of Method A is finished, the remaining part of Method A is transferred to the interpreter area through Quick_To_Interpreter_Bridge.
3.2. Dynamic Analysis on Applications
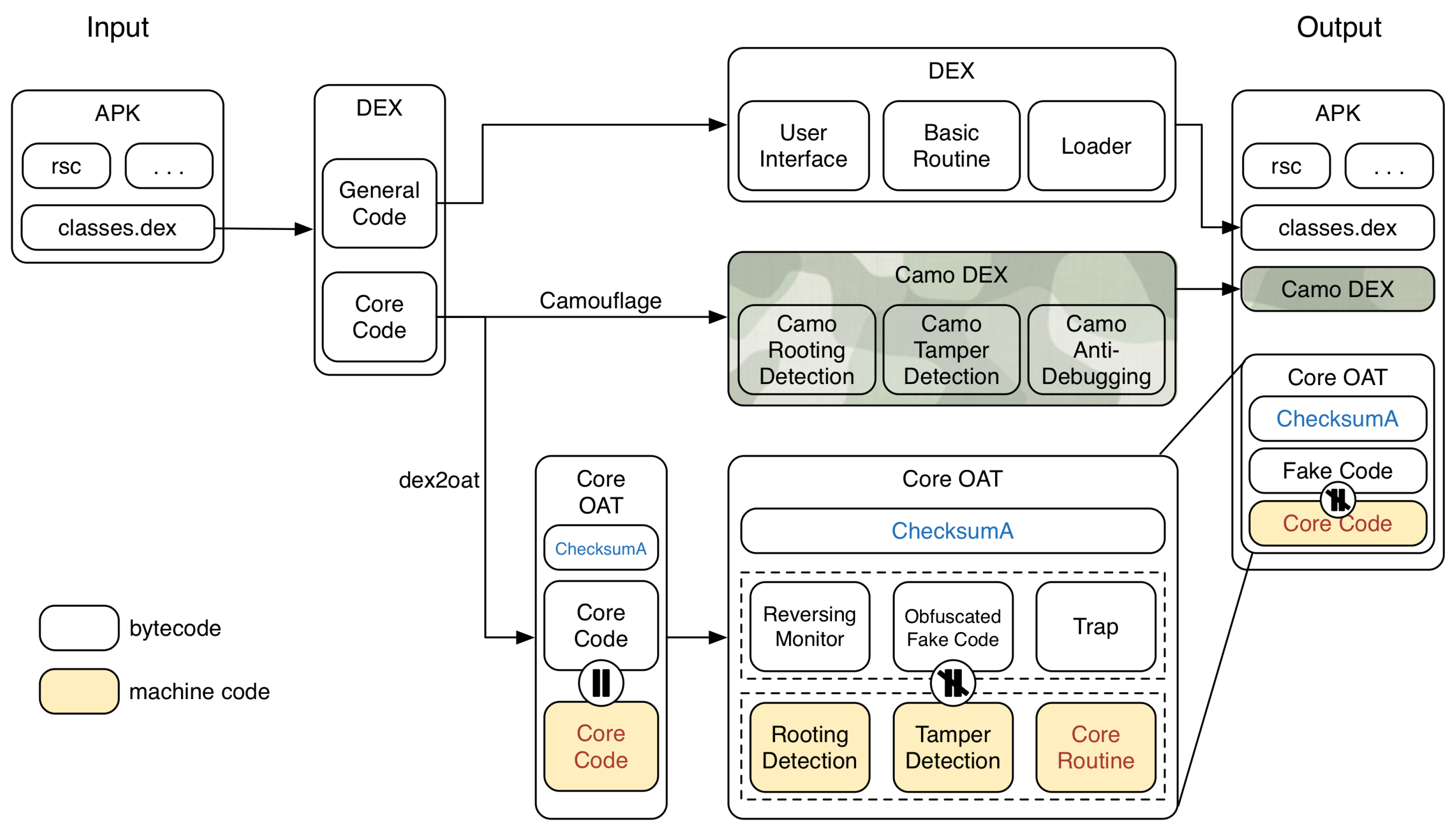
4. Proposed Scheme
4.1. Principal Idea
4.2. Design Concept
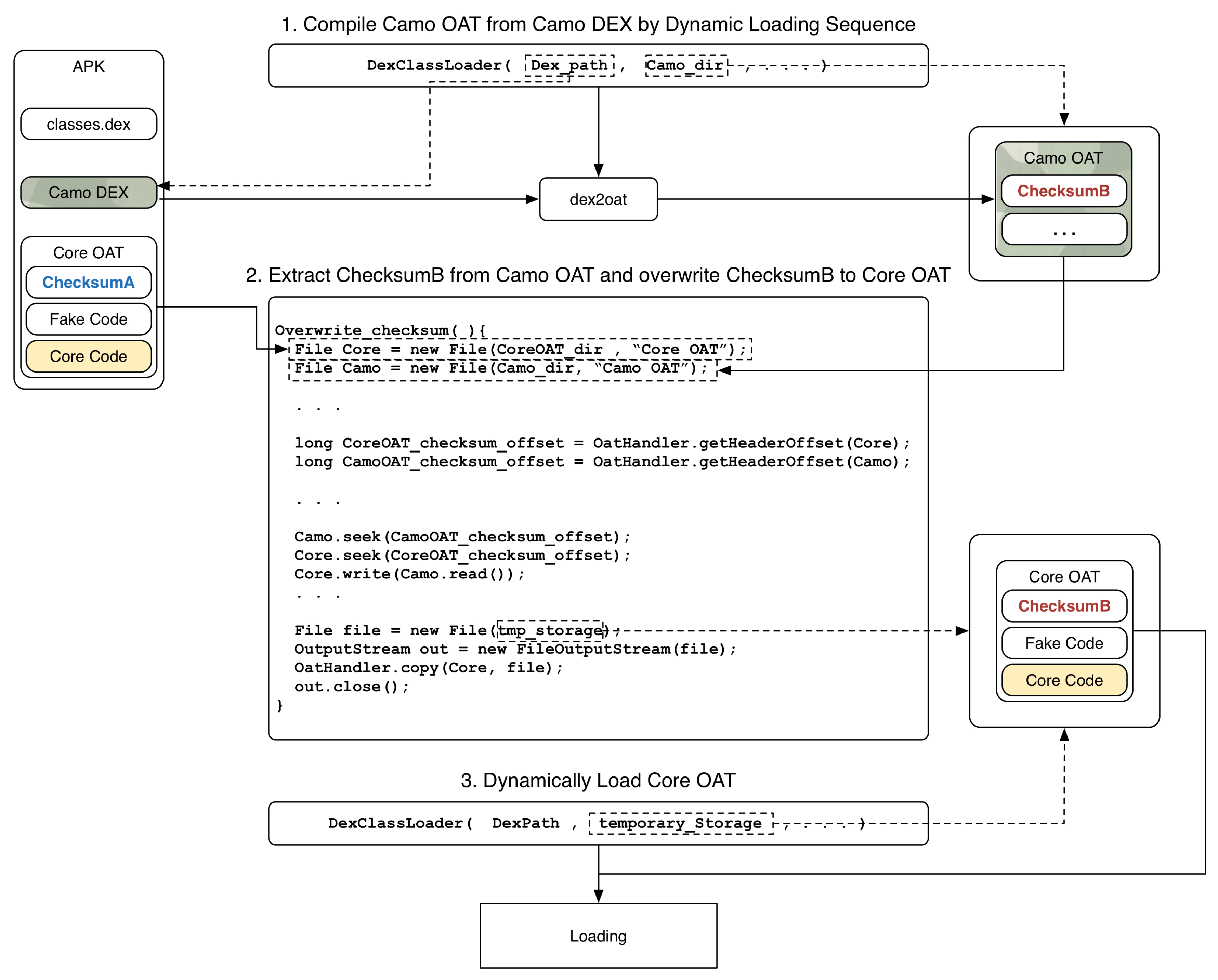
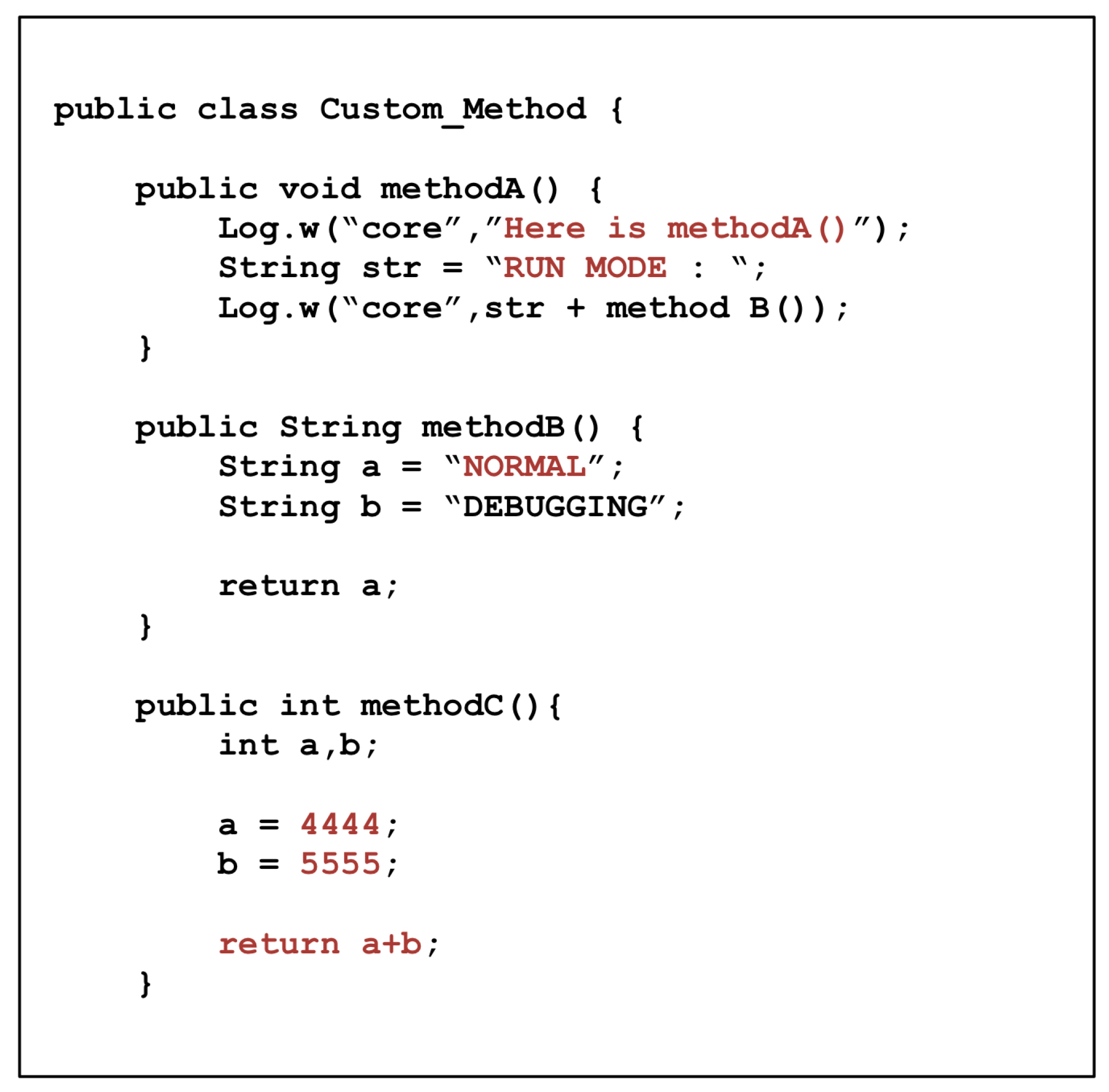
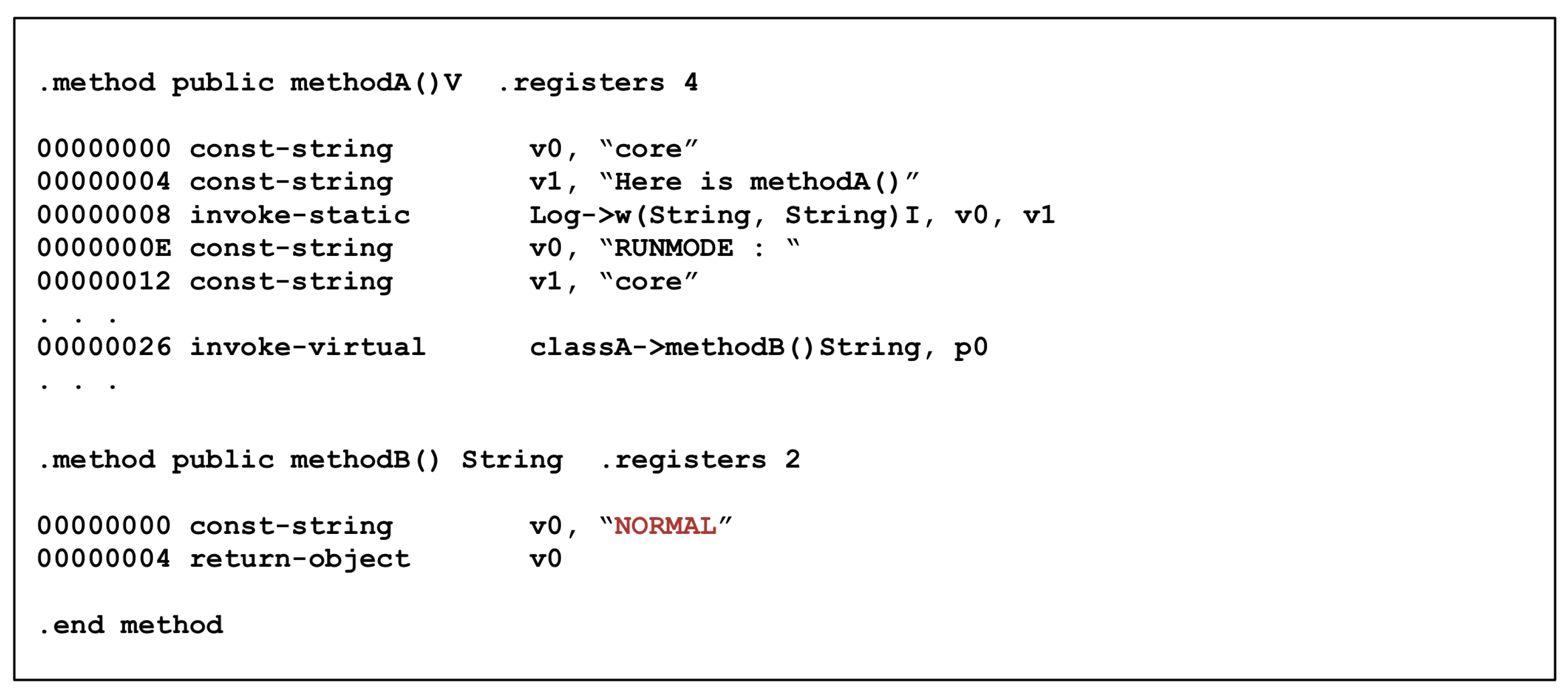
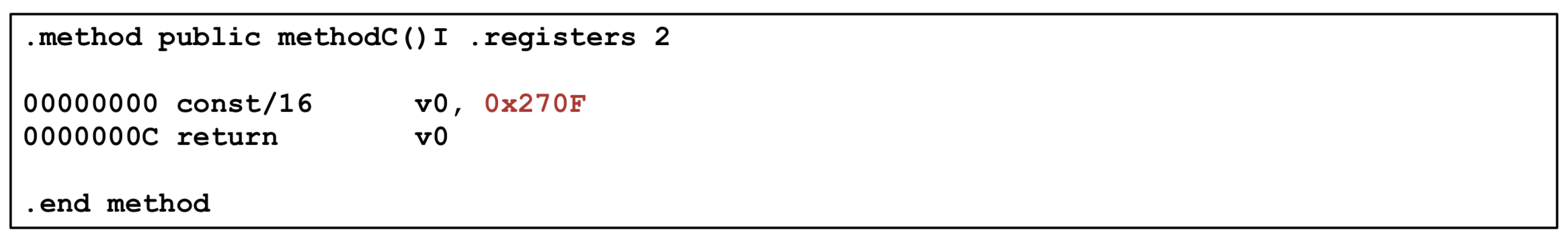
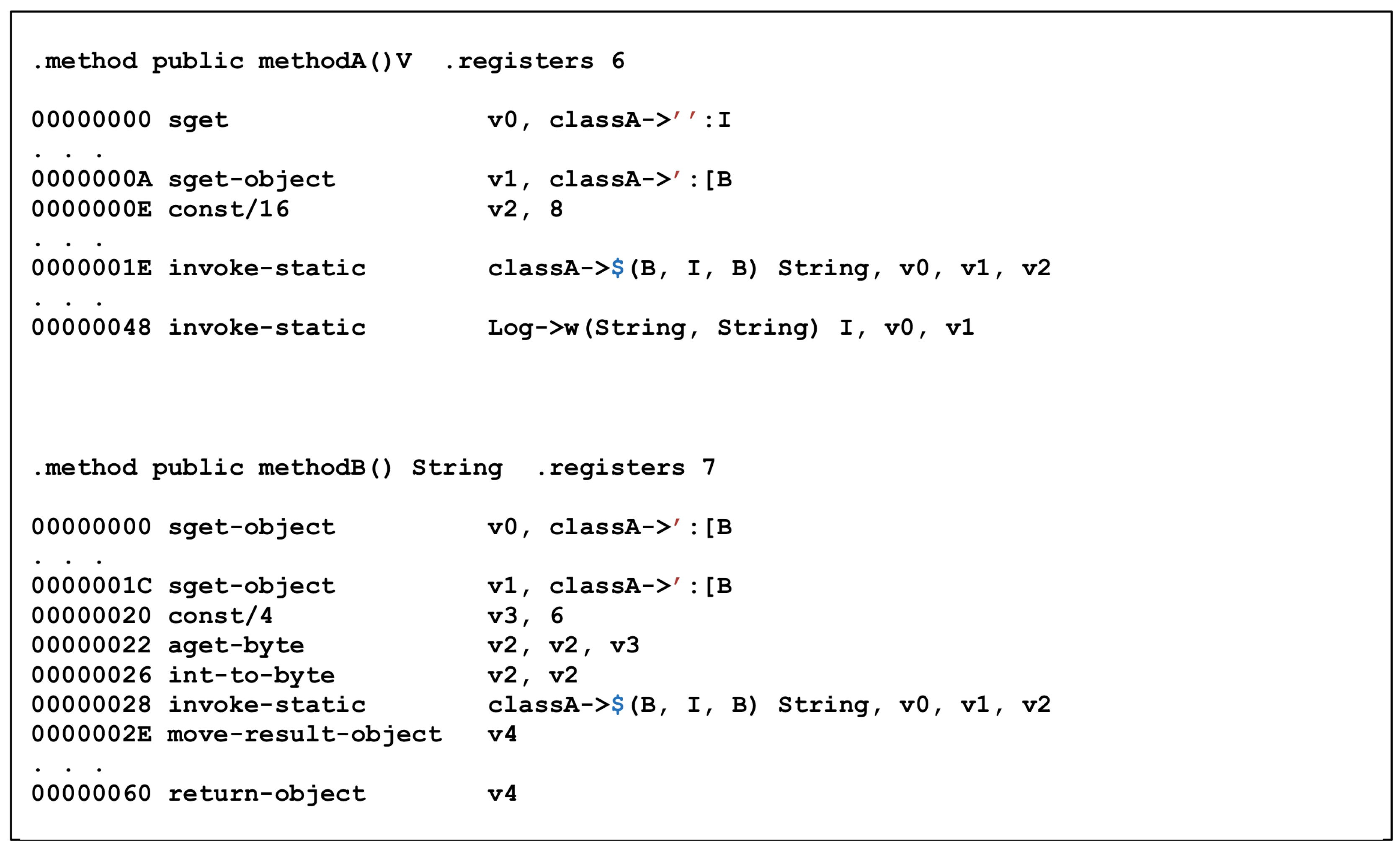
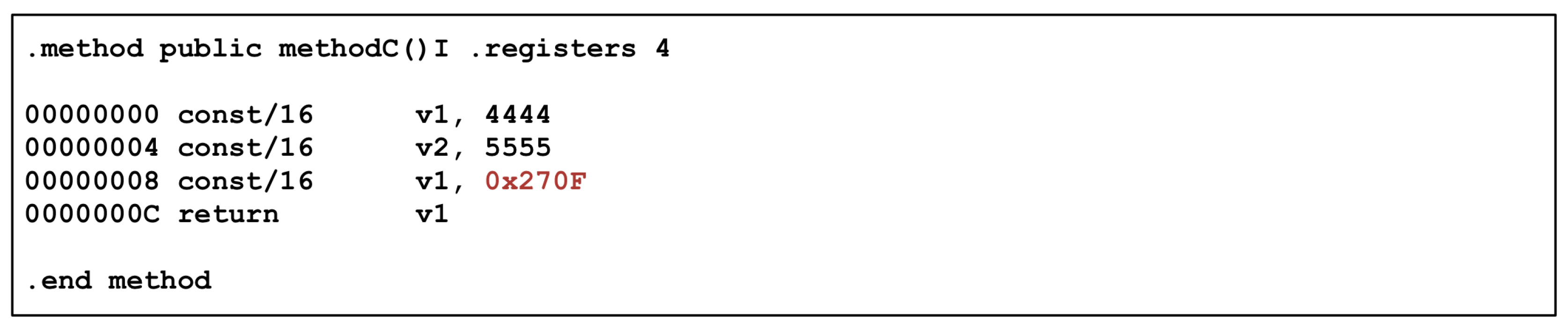
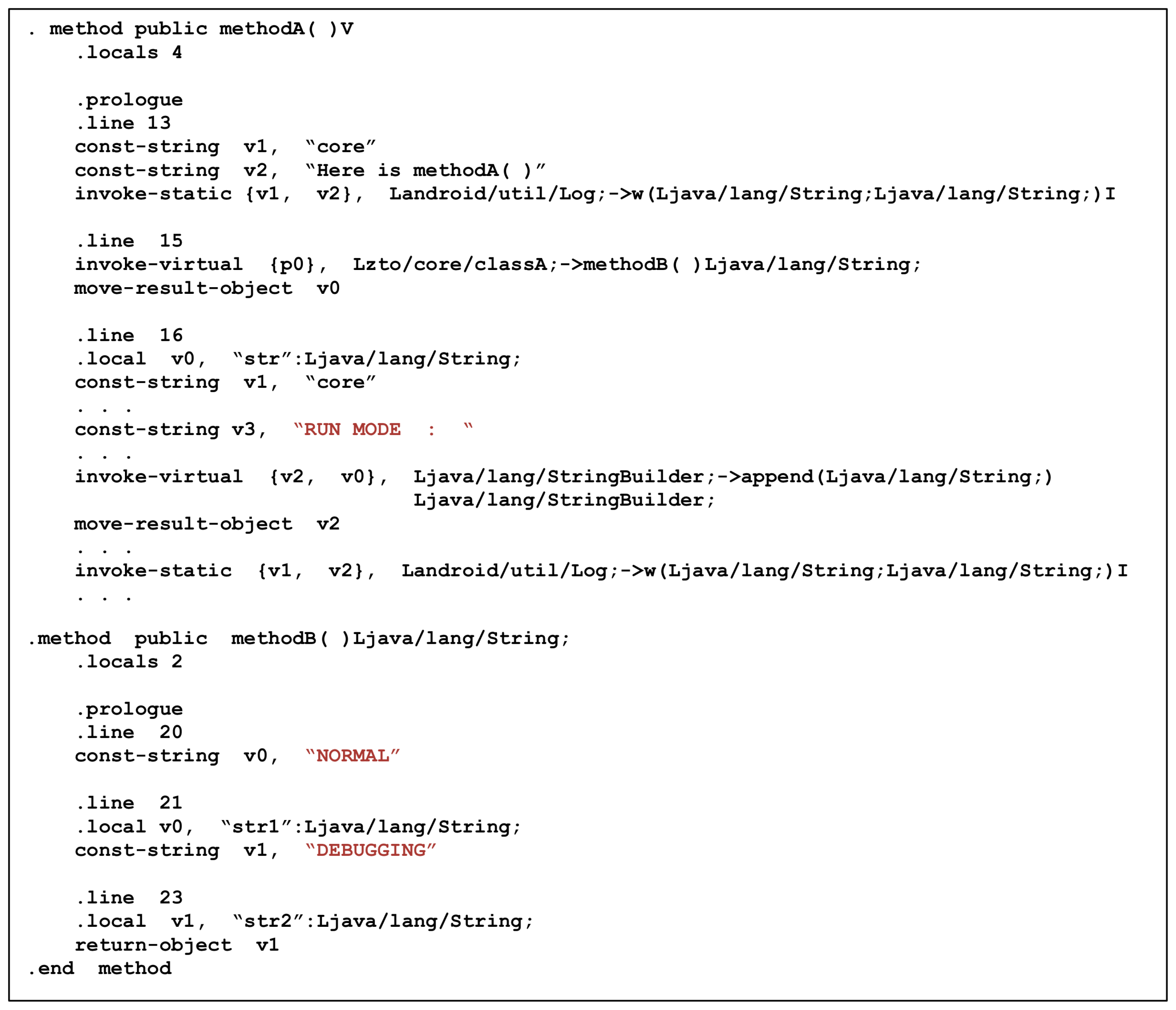
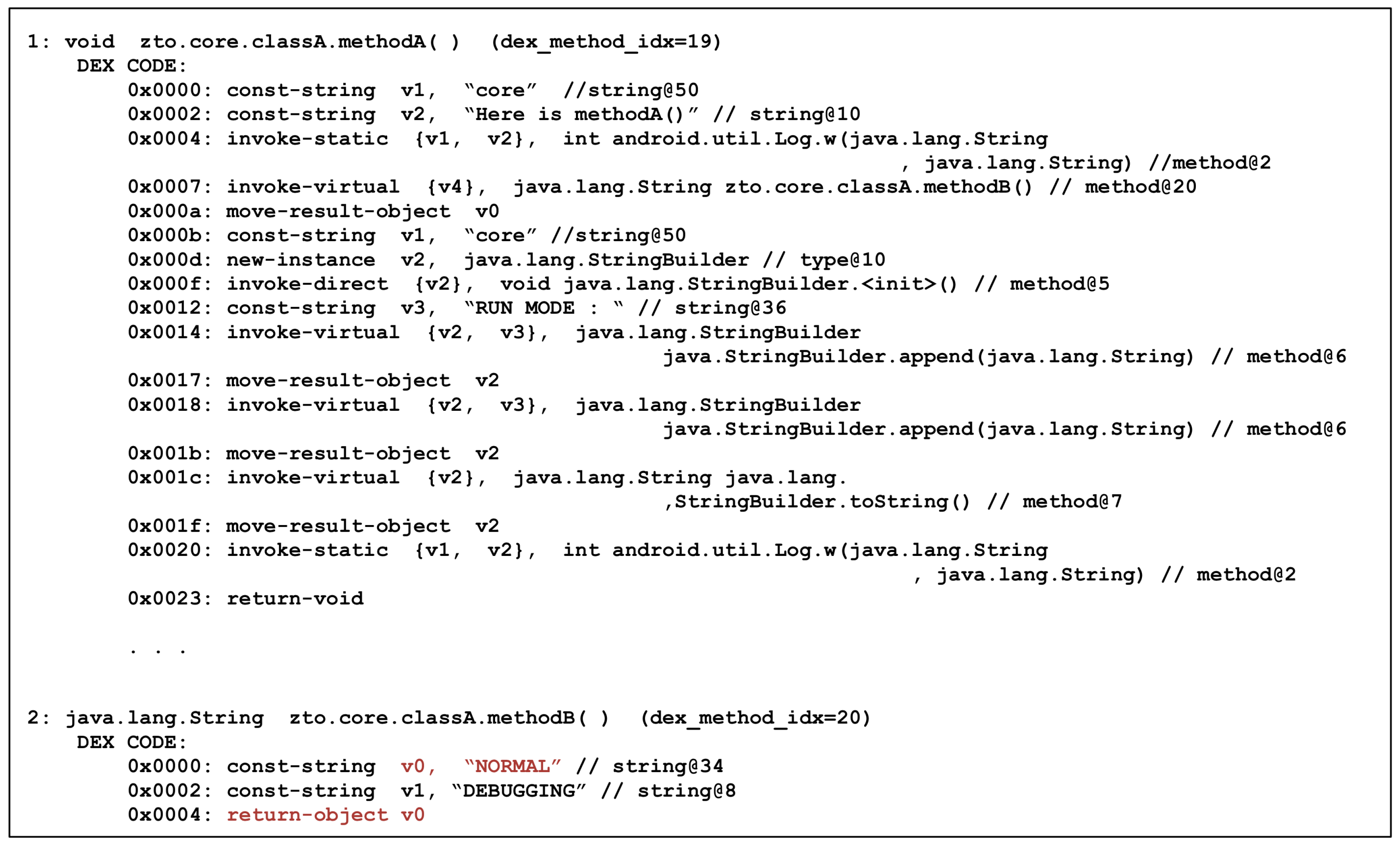
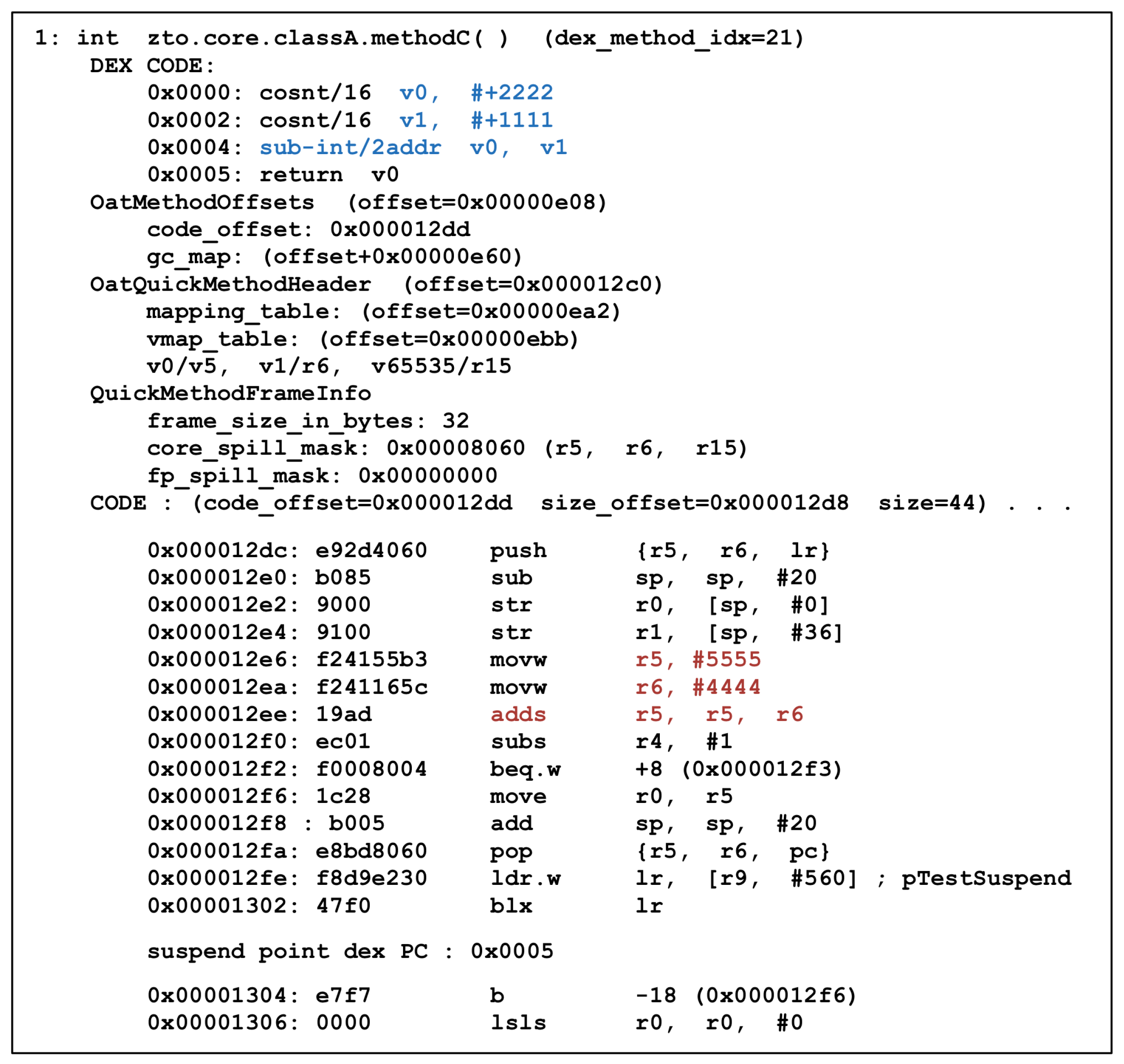
4.2.1. Core OAT Generation
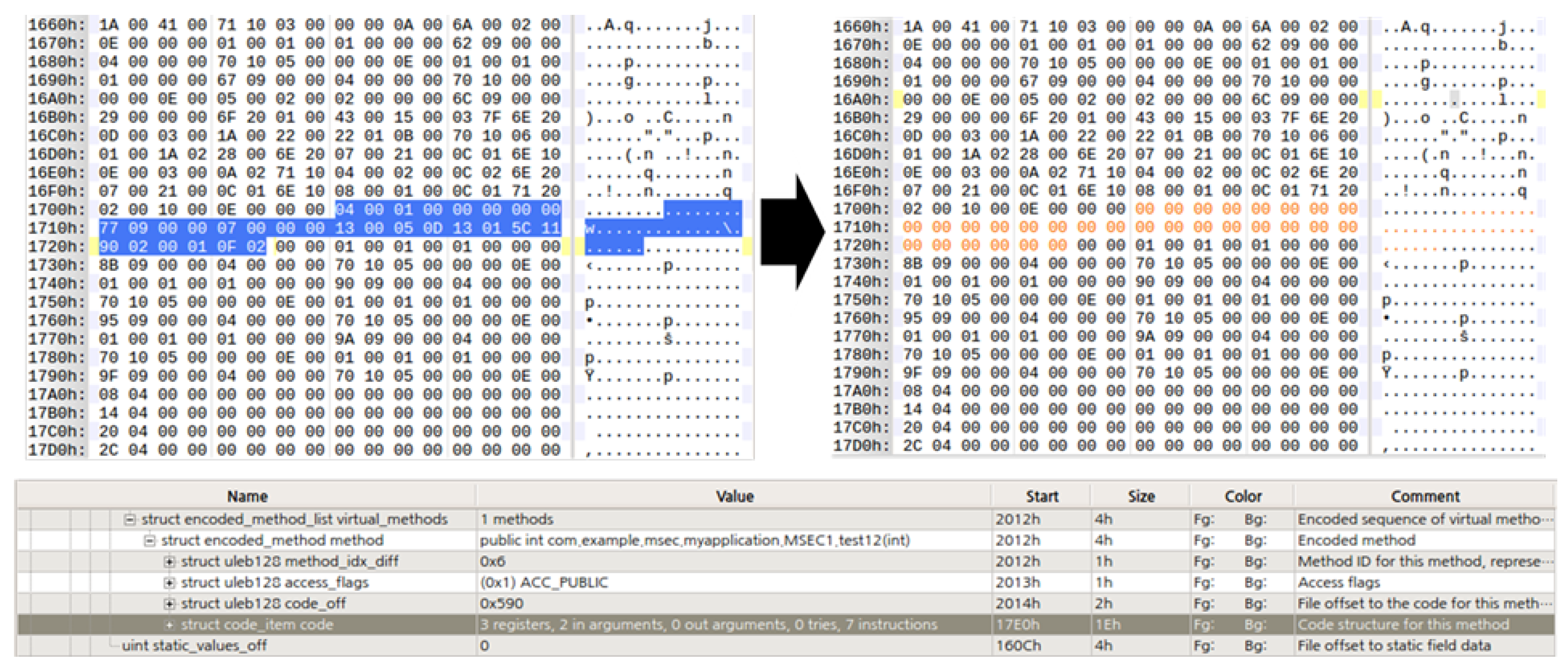
4.2.2. Camo DEX Generation
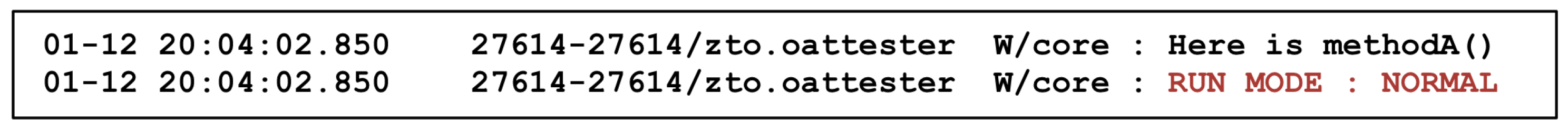
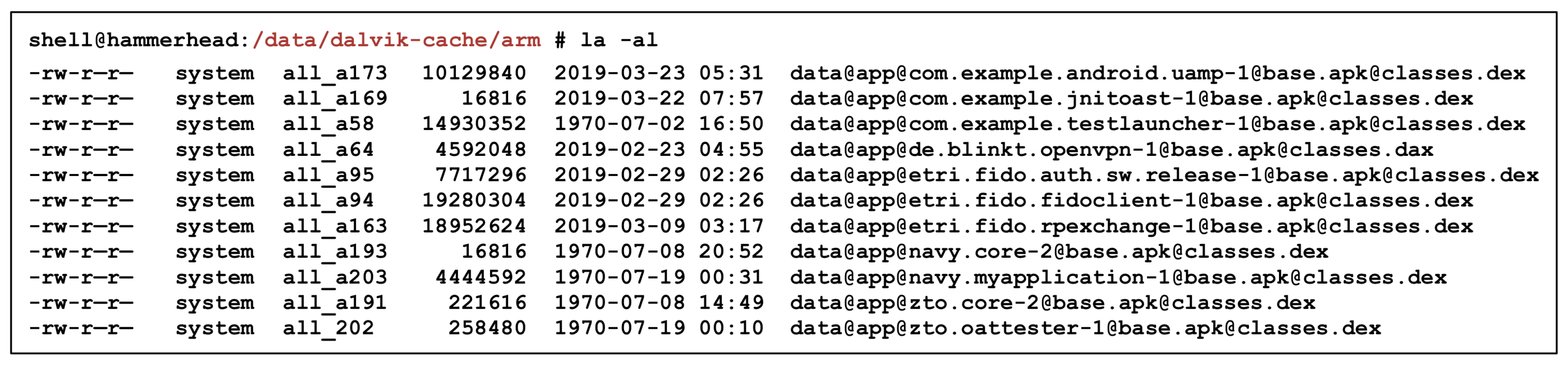
4.2.3. Core OAT Loading and Execution
5. Experimental Results
5.1. Experimental Setup
5.2. Resistance to Reverse Engineering with ProGuard
5.3. Resistance to Reverse Engineering with DexGuard
5.4. Resistance to Reverse Engineering with Proposed Scheme
5.5. Difficulty and Overhead Comparison
6. Discussion
6.1. Core OAT Dynamic Loading Requirement
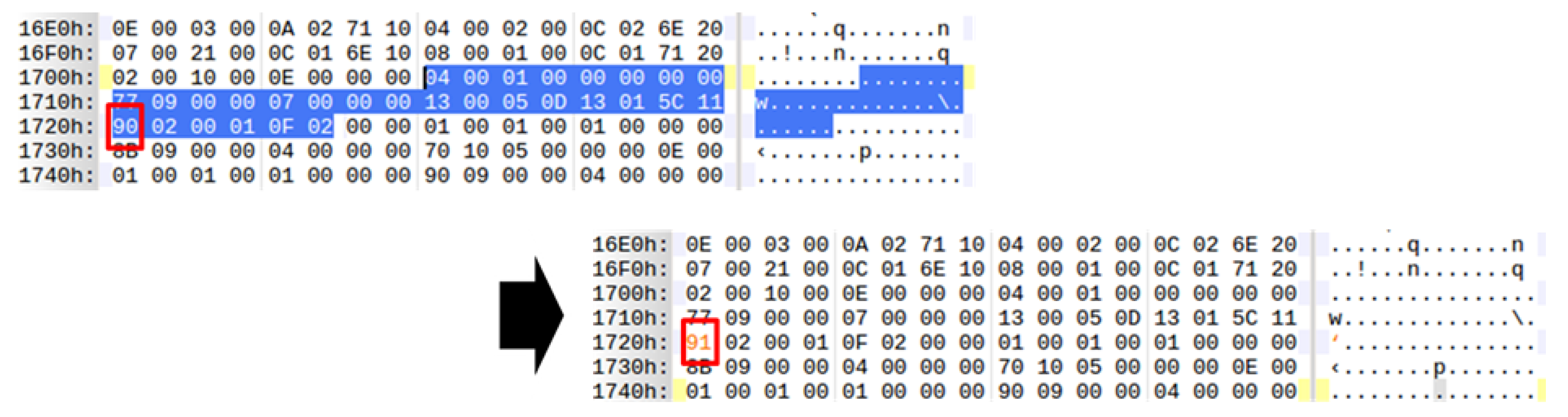
6.2. Additional Trapping through Core OAT Modulation
6.3. Core OAT Integrity Check
6.4. Limitations
7. Conclusions
Author Contributions
Funding
Conflicts of Interest
References
- Cheng, J.; Chen, W.; Tao, F.; Lin, C.L. Industrial IoT in 5G Environment Towards Smart Manufacturing. J. Ind. Inf. Integr. 2018, 10, 10–19. [Google Scholar] [CrossRef]
- Jones, N. Top Strategic IoT Trends and Technologies Through 2023. Gartner Report G00370381. 2018. Available online: https://www.gartner.com/doc/3890506/top-strategic-iot-trends-technologies (accessed on 22 March 2019).
- Brahler, S. Analysis of the Android Architecture. 2010. Available online: os.itec.kit.edu (accessed on 20 March 2019).
- Apktool. Available online: https://ibotpeaches.github.io/Apktool/ (accessed on 11 March 2019).
- Dex2jar. Available online: https://sourceforge.net/projects/dex2jar/ (accessed on 19 March 2019).
- Piao, Y.; Jung, J.H.; Yi, J.H. Server-Based Code Obfuscation Scheme for APK Tamper Detection. Secur. Commun. Netw. 2016, 9, 457–467. [Google Scholar] [CrossRef]
- Jung, J.H.; Kim, J.Y.; Lee, H.C.; Yi, J.H. Repackaging Attack on Android Banking Applications and Its Countermeasures. Wirel. Pers. Commun. 2013, 73, 1421–1437. [Google Scholar] [CrossRef]
- Banescu, S.; Collberg, C.; Ganesh, V.; Newsham, Z.; Pretschner, A. Code Obfuscation Against Symbolic Execution Attacks. In Proceedings of the 32nd Annual Conference on Computer Security Applications, Los Angeles, CA, USA, 5–8 December 2016. [Google Scholar]
- Balachandran, V.; Sufatrio; Tan, D.J.J.; Thing, V.L.L. Control Flow Obfuscation for Android Applications. Comput. Secur. 2016, 61, 72–93. [Google Scholar] [CrossRef]
- Kim, S.R.; Kim, J.N.; Kim, S.T.; Shin, S.; Yi, J.H. Anti-reversible Dynamic Tamper Detection Scheme using Distributed Image Steganography for IoT Applications. J. Supercomput. 2018, 74, 4261–4280. [Google Scholar] [CrossRef]
- Aucsmith, D. Tamper Resistant Software: An Implementation. In International Workshop on Information Hiding; Springer: Berlin/Heidelberg, Germany, 1996; pp. 317–333. [Google Scholar]
- Bangcle. Available online: https://www.bangcle.com/ (accessed on 19 February 2019).
- Ijiami. Available online: http://www.ijiami.cn/ (accessed on 7 February 2019).
- DexGuard. Available online: https://www.guardsquare.com/en/products/dexguard (accessed on 6 May 2019).
- Proguard. Available online: https://www.guardsquare.com/en/products/proguard (accessed on 6 May 2019).
- DexProtector. Available online: https://dexprotector.com/ (accessed on 9 May 2019).
- Bartel, A.; Klein, J.; Traon, Y.L.; Monperrus, M. Dexpier: Converting Android Dalvik Bytecode to Jimple for Static Analysis with Soot. In Proceedings of the Association for Computing Machinery SiGPLAN International Workshop on State of the Art in Java Program Analysis, Beijing, China, 14 June 2012; pp. 27–38. [Google Scholar]
- Payet, E.; Spoto, F. Static Analysis of Android Programs. Inf. Softw. Technol. 2012, 54, 1192–1201. [Google Scholar] [CrossRef][Green Version]
- Ning, Z.; Zhang, F. DexLego: Reassembleable Bytecode Extraction for Aiding Static Analysis. In Proceedings of the 48th Annual IEEE/IFIP International Conference on Dependable Systems and Networks, Luxembourg, 25–28 June 2018; pp. 690–701. [Google Scholar]
- Alam, S.; Qu, Z.; Riley, R.; Chen, Y.; Rastogi, V. DroidNative: Automating and Optimizing Detection of Android Native Code Malware Variants. Comput. Secur. 2017, 65, 230–246. [Google Scholar] [CrossRef]
- Cho, H.; Yi, J.H.; Ahn, G.J. DexMonitor: Dynamically Analyzing and Monitoring Obfuscated Android Applications. IEEE Access 2018, 6, 71229–71240. [Google Scholar] [CrossRef]
- Android Runtime. Available online: https://en.wikipedia.org/wiki/AndroidRuntime (accessed on 25 March 2019).
- Yadav, R.; Bhadoria, R.S. Performance Analysis for Android Runtime Environment. In Proceedings of the Fifth International Conference on Communication Systems and Network Technologies, Gwalior, India, 4–6 April 2015; pp. 1076–1079. [Google Scholar]
- Backes, M.; Schranz, O.; von Styp-Rekowsky, P. POSTER: Towards Compiler-Assisted Taint Tracking on Android Runtime. In Proceedings of the 22nd Association for Computing Machinery SIGSAC Conference on Computer and Communications Security, Denver, CO, USA, 12–16 October 2015; pp. 1629–1631. [Google Scholar]
- Sabanal, P. State of the ART Exploring the New Android KitKat Runtime. In Proceedings of the Hack In The Box Security Conference, K. Lumpur, Malaysia, 13–16 October 2014. [Google Scholar]
- Sabanal, P. Hiding Behind ART. Available online: https://www.blackhat.com/docs/asia-15/materials/asia-15-Sabanal-Hiding-Behind-ART-wp.pdf (accessed on 9 June 2019).
- Arnatovich, Y.L.; Wang, L.; Ngo, N.M.; Soh, C. A Comparison of Android Reverse Engineering Tools via Program Behaviors Validation Based on Intermediate Languages Transformation. IEEE Access 2018, 6, 12382–12394. [Google Scholar] [CrossRef]
- Ahead-Of-Time Compilation. Available online: https://en.wikipedia.org/wiki/Ahead-of-timecompilation (accessed on 21 March 2019).
- Sharma, M.; Thakur, A. Review Paper on Android Operating System. Int. J. Emerg. Trends Sci. Technol. 2015, 2, 2486–2490. [Google Scholar]
- ART and Dalvik. Available online: https://source.android.com/ (accessed on 25 March 2019).
- Just-In-Time Compilation. Available online: https://en.wikipedia.org/wiki/Just-in-timecompilation (accessed on 21 March 2019).
- Collberg, C.; Martin, S.; Myers, J.; Nagra, J. Distributed Application Tamper Detection via Continuous Software Updates. In Proceedings of the 28th Annual Computer Security Applications Conference, Orlando, FL, USA, 3–7 December 2012; pp. 319–328. [Google Scholar]
- Falcarin, P.; Di Carlo, S.; Cabutto, A.; Garazzino, N.; Barberis, D. Exploiting Code Mobility for Dynamic Binary Obfuscation. In Proceedings of the World Congress on Internet Security, London, UK, 21–23 Feburary 2011; pp. 114–120. [Google Scholar]
- Cabutto, A.; Falcarin, P.; Abrath, B.; Coppens, B.; De Sutter, B. Software Protection with Code Mobility. In Proceedings of the Second Association for Computing Machinery Workshop on Moving Target Defense, Denver, CO, USA, 12 October 2015; pp. 95–103. [Google Scholar]
- Android Version Market Share. Available online: https://developer.android.com/about/dashboards (accessed on 27 May 2019).
- Geethanjali, D.; Ying, T.L.; Melissa, C.W.J.; Balachandran, V. AEON: Android Encryption Based Obfuscation. In Proceedings of the Eighth Association for Computing Machinery Conference on Data and Application Security and Privacy, Tempe, AZ, USA, 19–21 March 2018; pp. 146–148. [Google Scholar]
- Park, Y.; Park, T.; Yi, J.H. Multi-Partitioned Bytecode Wrapping Scheme For Minimizing Code Exposure on Android. J. Int. Technol. 2018, 19, 1199–1208. [Google Scholar]
- Yoo, J.; Yi, J.H. Code-Based Authentication Scheme for Lightweight Integrity Checking of Smart Vehicles. IEEE Access 2018, 6, 46731–46741. [Google Scholar] [CrossRef]



| Sectioname | Section Component Name |
|---|---|
| OatHeader | alder32_checksum |
| OatHeader | image file location oat checksum |
| OatHeader | image file location oat data begin |
| OatDexFile | dex file location checksum |
| Dex File | dex file checksum |
| Dex File | SHA1 signature |
| Target Objects | Required Skills | ProGuard | DexGuard | Proposed Scheme |
|---|---|---|---|---|
| Decompile | ✓ | ✓ | ✓ | |
| Dalvik bytecode | ✓ | ✓ | ✓ | |
| Bytecode | API knowledge | ✓ | ✓ | ✓ |
| Repackaging | ✓ | ✓ | ✓ | |
| Dalvik VM & ART framework | ✓ | |||
| Crypto routine | Encryption algorithms | ✓ | ||
| CPU instruction | ✓ | |||
| Machine code | Disassemble | ✓ | ||
| Debugging | ✓ | |||
| OAT(ELF) file structure | ✓ |
| Original | ProGuard | DexGuard | Proposed Scheme | |
|---|---|---|---|---|
| Execution time (milliseconds) | 11.494 | 11.073 | 58.699 | 17.793 |
© 2019 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Na, G.; Lim, J.; Lee, S.; Yi, J.H. Mobile Code Anti-Reversing Scheme Based on Bytecode Trapping in ART. Sensors 2019, 19, 2625. https://doi.org/10.3390/s19112625
Na G, Lim J, Lee S, Yi JH. Mobile Code Anti-Reversing Scheme Based on Bytecode Trapping in ART. Sensors. 2019; 19(11):2625. https://doi.org/10.3390/s19112625
Chicago/Turabian StyleNa, Geonbae, Jongsu Lim, Sunjun Lee, and Jeong Hyun Yi. 2019. "Mobile Code Anti-Reversing Scheme Based on Bytecode Trapping in ART" Sensors 19, no. 11: 2625. https://doi.org/10.3390/s19112625
APA StyleNa, G., Lim, J., Lee, S., & Yi, J. H. (2019). Mobile Code Anti-Reversing Scheme Based on Bytecode Trapping in ART. Sensors, 19(11), 2625. https://doi.org/10.3390/s19112625





