Differentiated Data Aggregation Routing Scheme for Energy Conserving and Delay Sensitive Wireless Sensor Networks
Abstract
1. Introduction
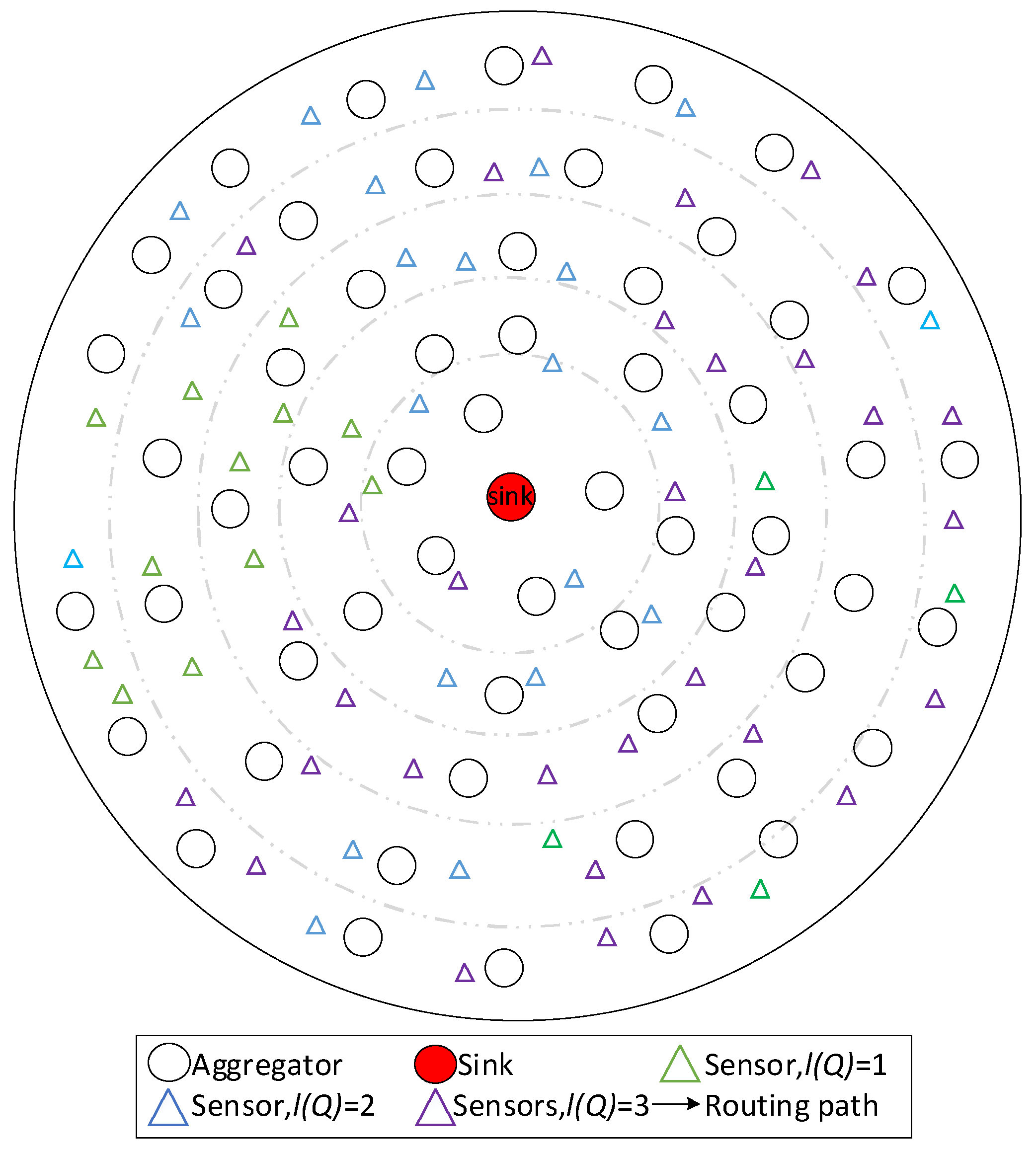
- The DDAR scheme is a novel data aggregation routing framework. In this framework, each node configures only one set of parameters to satisfy a certain QoS requirement. When a node performs aggregation, it searches an aggregator whose service most closely matches its QoS requirement for next hop. The most closely matching refers to the nodes which have the smallest difference of QoS requirement with the sender. DDAR scheme ameliorates the high energy consumption, complex storage and poor service guarantee in previous strategies. Thus, DDAR scheme realizes the differentiated data aggregation routing in the true sense, and is able to significantly reduce energy consumption while ensuring that data transmission of data packets meets service requirement.
- Based on DDAR scheme, we propose an improved DDAR scheme to reduce delay and improve energy efficiency by utilizing the residual energy in the nodes far from the sink. Whatever routing strategy is adopted, the data volume a node transmits decreases with the increase of distance to the sink. This phenomenon illustrates that the energy consumption of the nodes near the sink is larger than the nodes far from the sink, there is residual energy in the nodes when the network dies. In this paper, improved DDAR enhances the performance by increasing the frequency of aggregation.
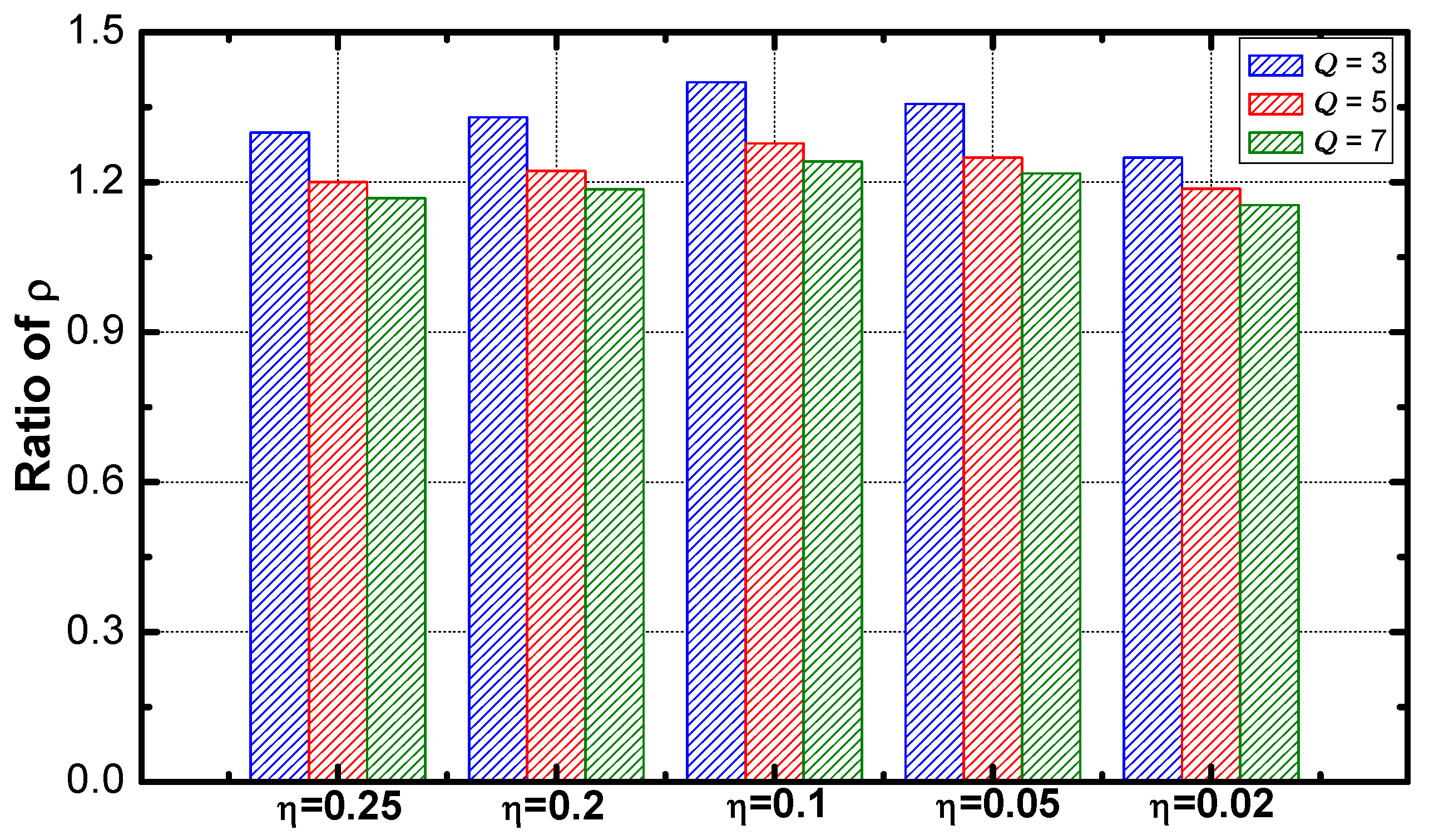
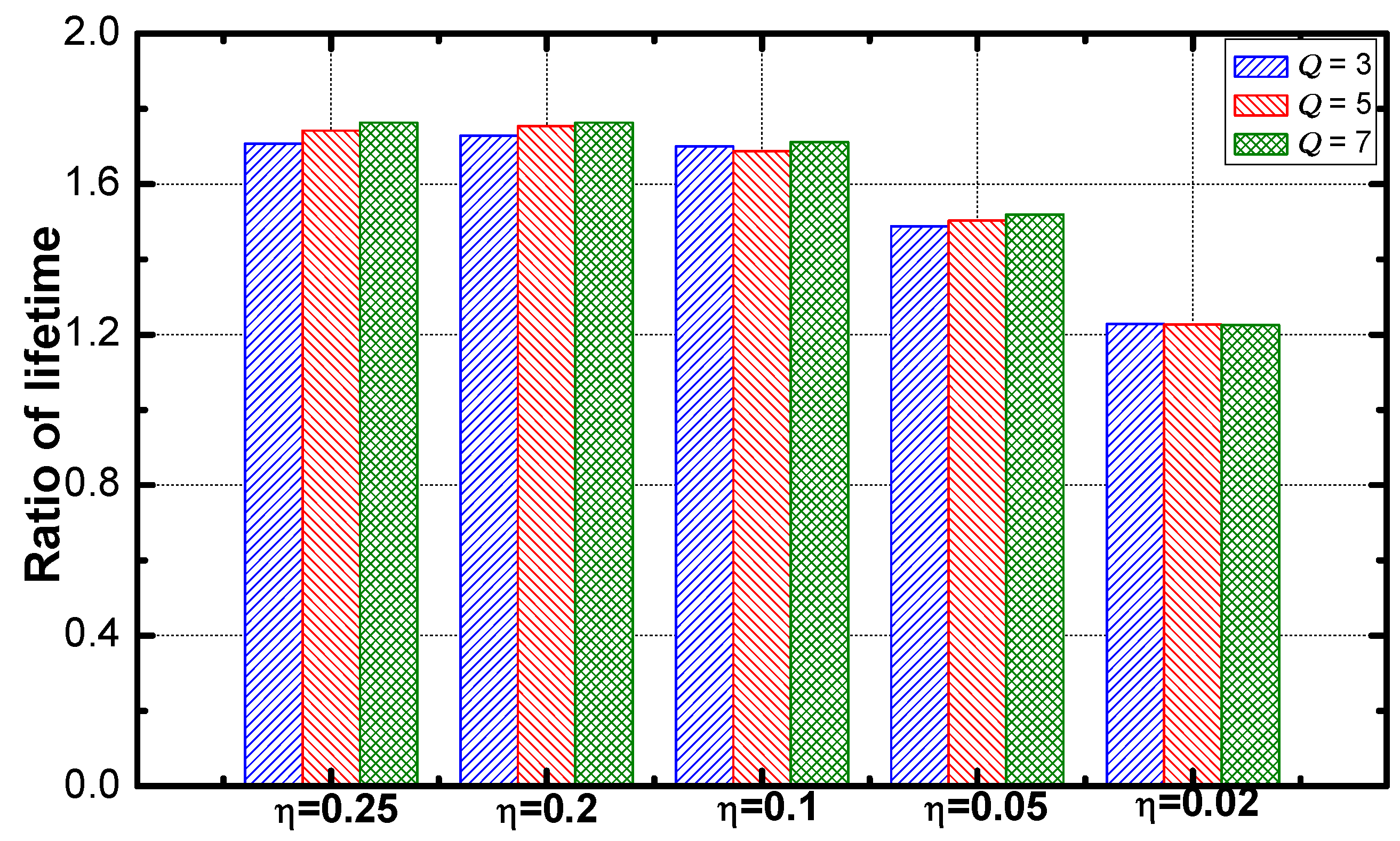
- In this paper, we propose the differentiated data aggregation routing scheme. Simulation results demonstrate that DDAR can improve the service guarantee rate by 25.1%, network lifetime by 55.45% and energy efficiency by 83.99%.
2. Related Work
2.1. Research on Data Aggregation Routing
2.2. Research on Delay Optimization
3. System Model and Problem Statement
3.1. System Model
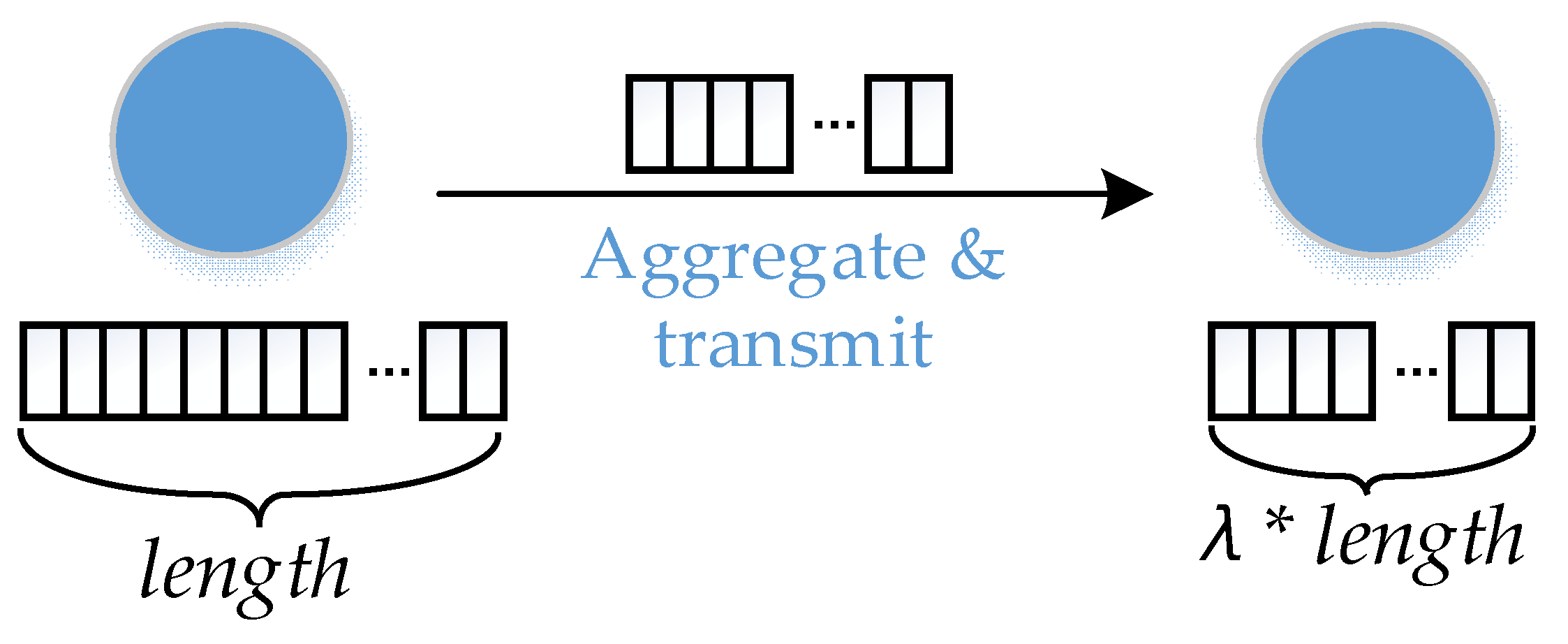
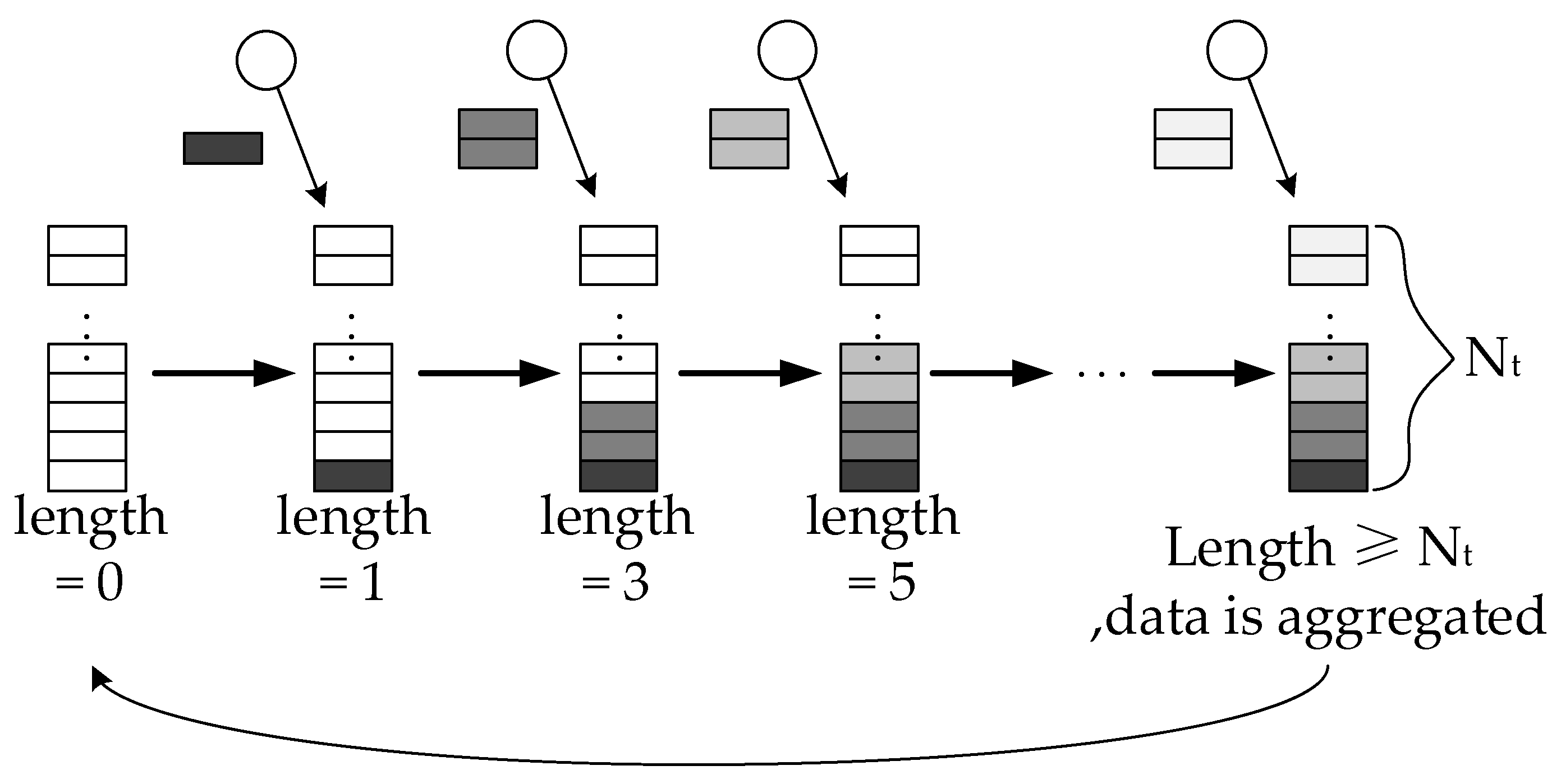
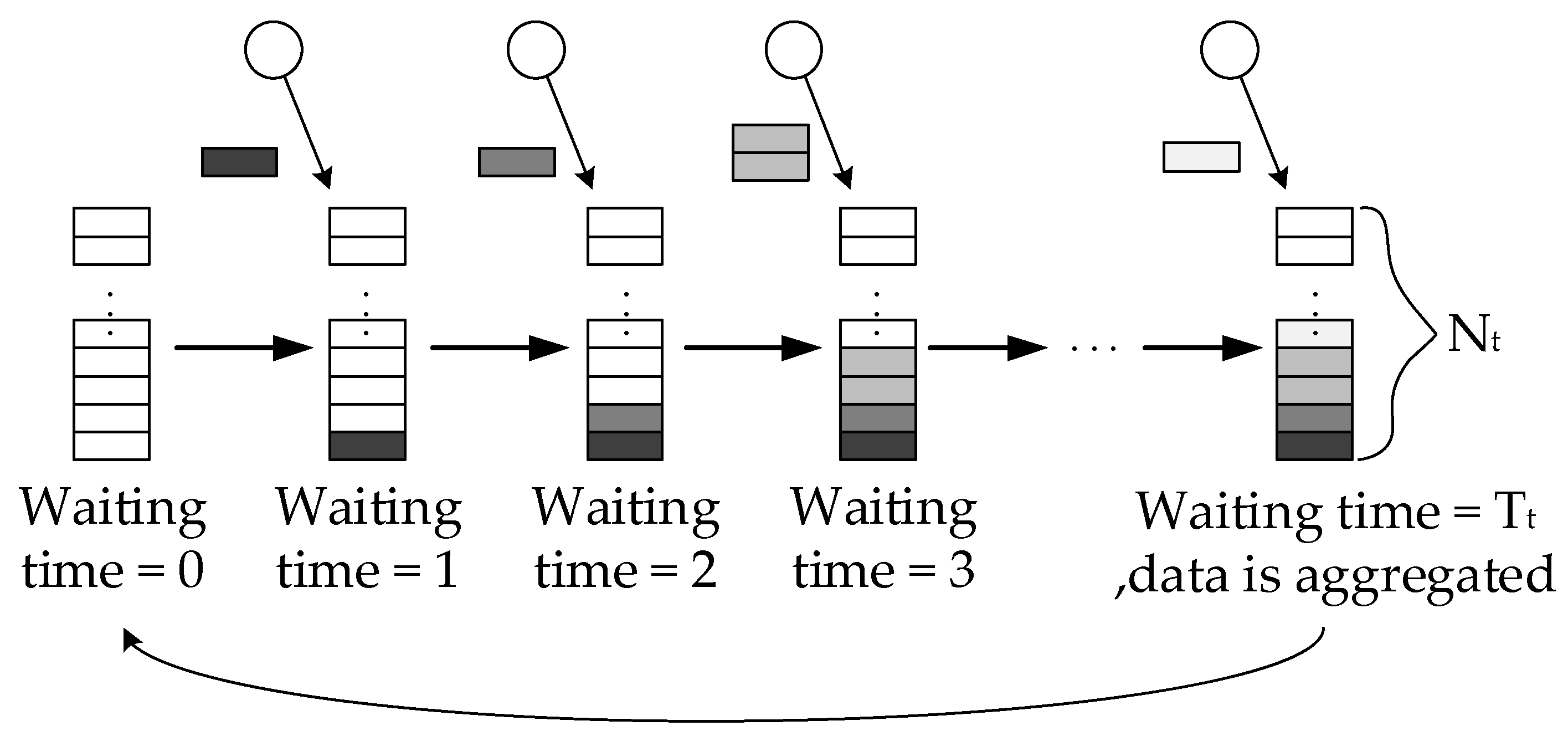
3.2. System Parameters
3.3. Problem Statements
4. Optimization Mechanism Design
4.1. Research Motivation
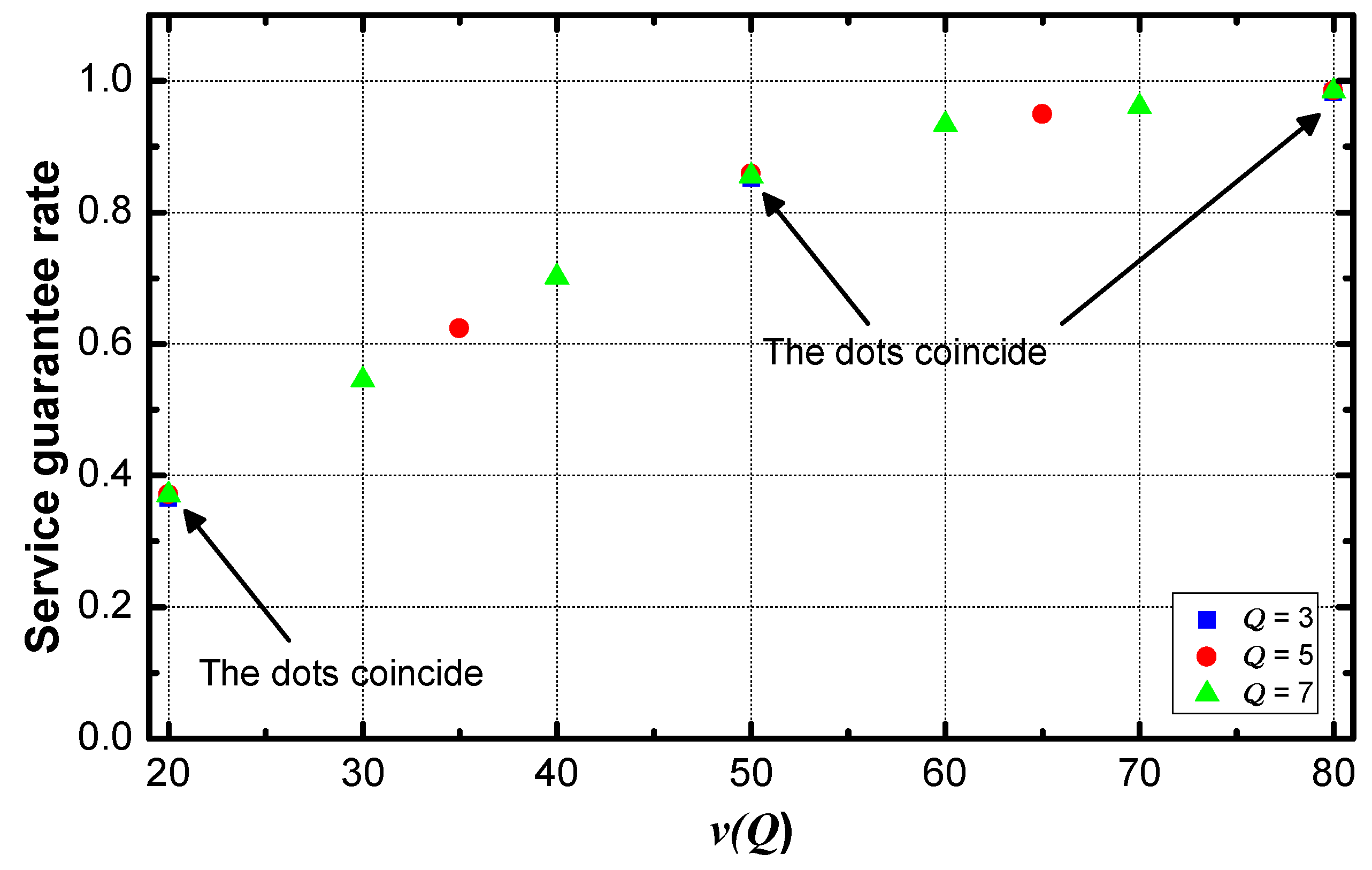
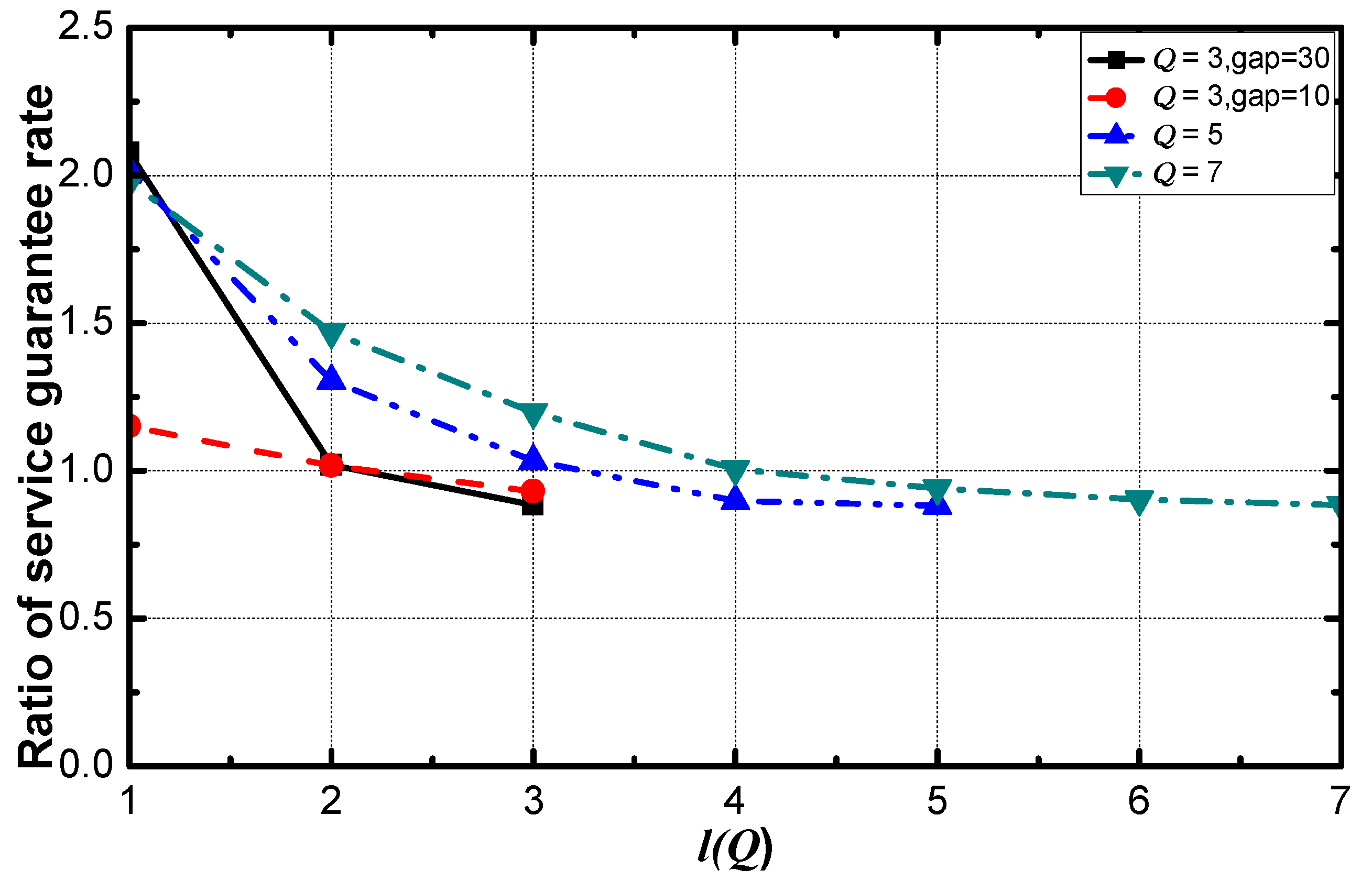
- In the DiffServ networks without a method for service guarantee, there is a gap between service guarantee rates of different service requirements (shown in Figure 5). With the increase of , the service requirement becomes loose. The service guarantee rate is high when the service requirement is loose. That is, the rate increases with the increase of the value of service requirement. Therefore, it is necessary to reduce the transmission delay of data with a small value of service requirement to improve the service guarantee rate of these kinds of data.
- Compared with the data generated near the sink, the data packets generated by sensing nodes far from the sink spend more hops to arrive at the sink. This process contributes most of the delay. The delay can be effectively reduced by reducing the delay of these packets, and service guarantee rate can be improved as well.
- The aggregators far from the sink transmit fewer data packets than aggregators near the sink. The data aggregation and transmission are the primary consumption methods of energy. In the model, all the aggregators are homogenous in energy. To enhance the transmission frequency of these distant nodes, the energy efficiency can be improved while the lifetime doesn’t extensively deteriorate.
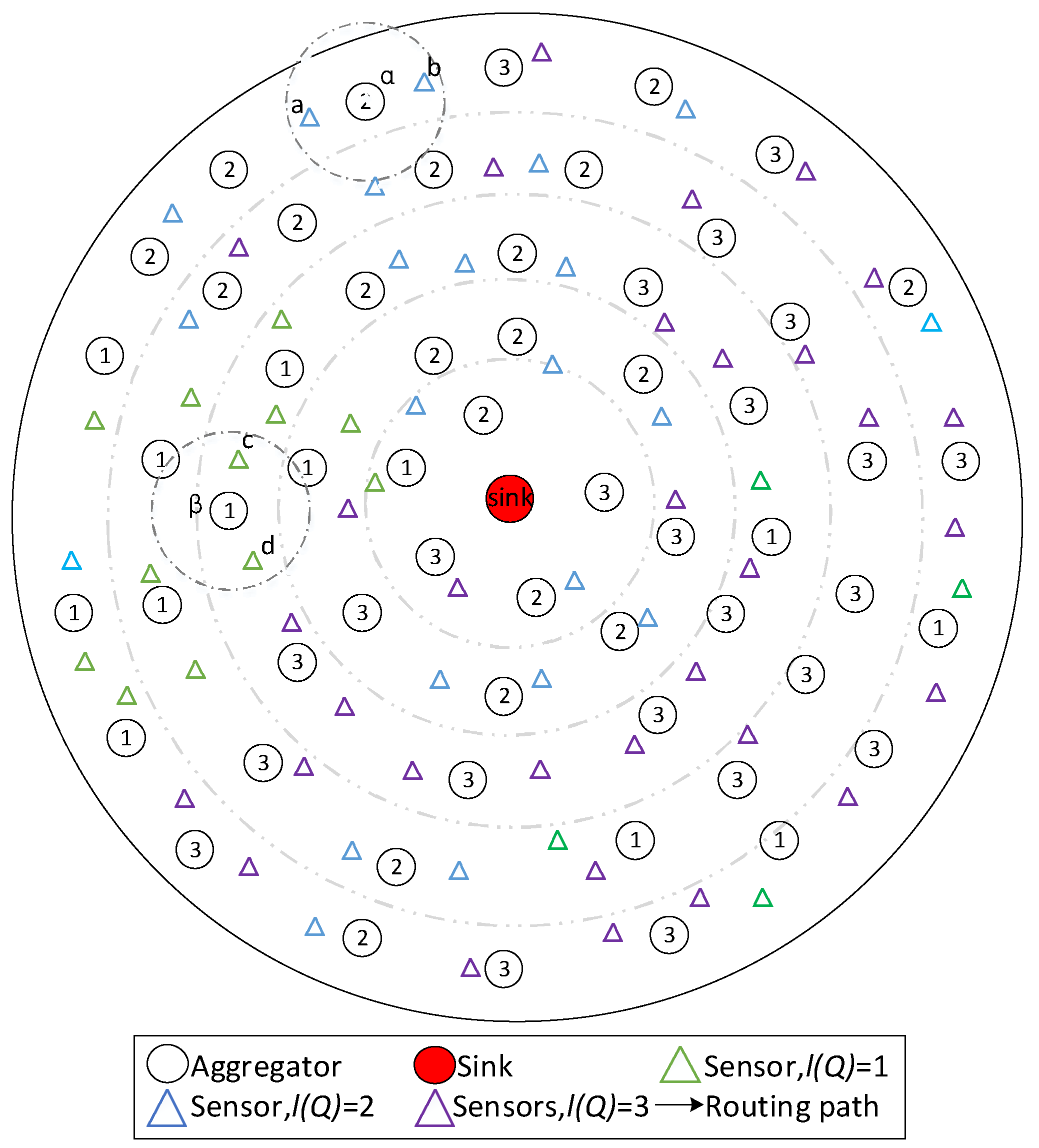
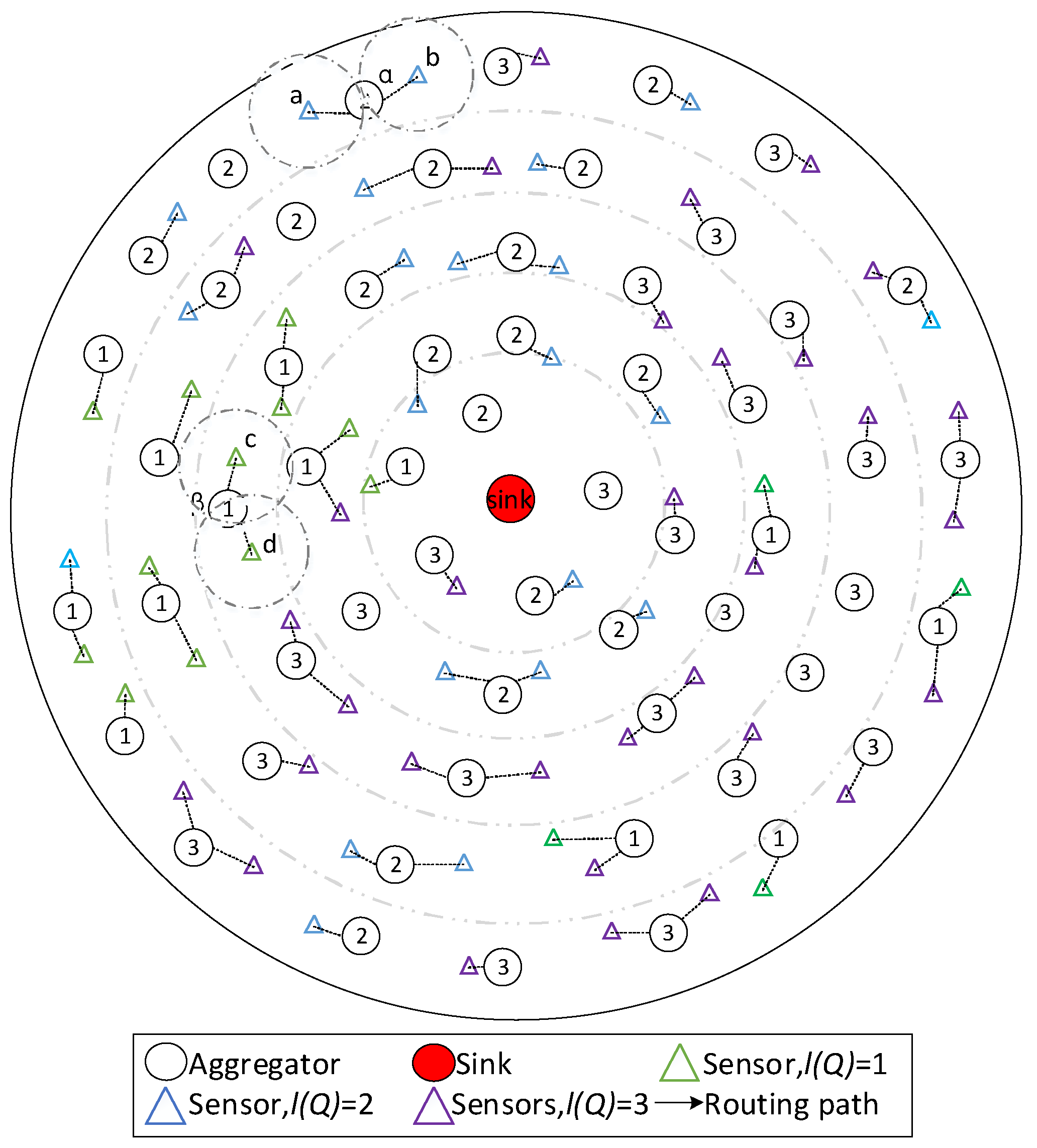
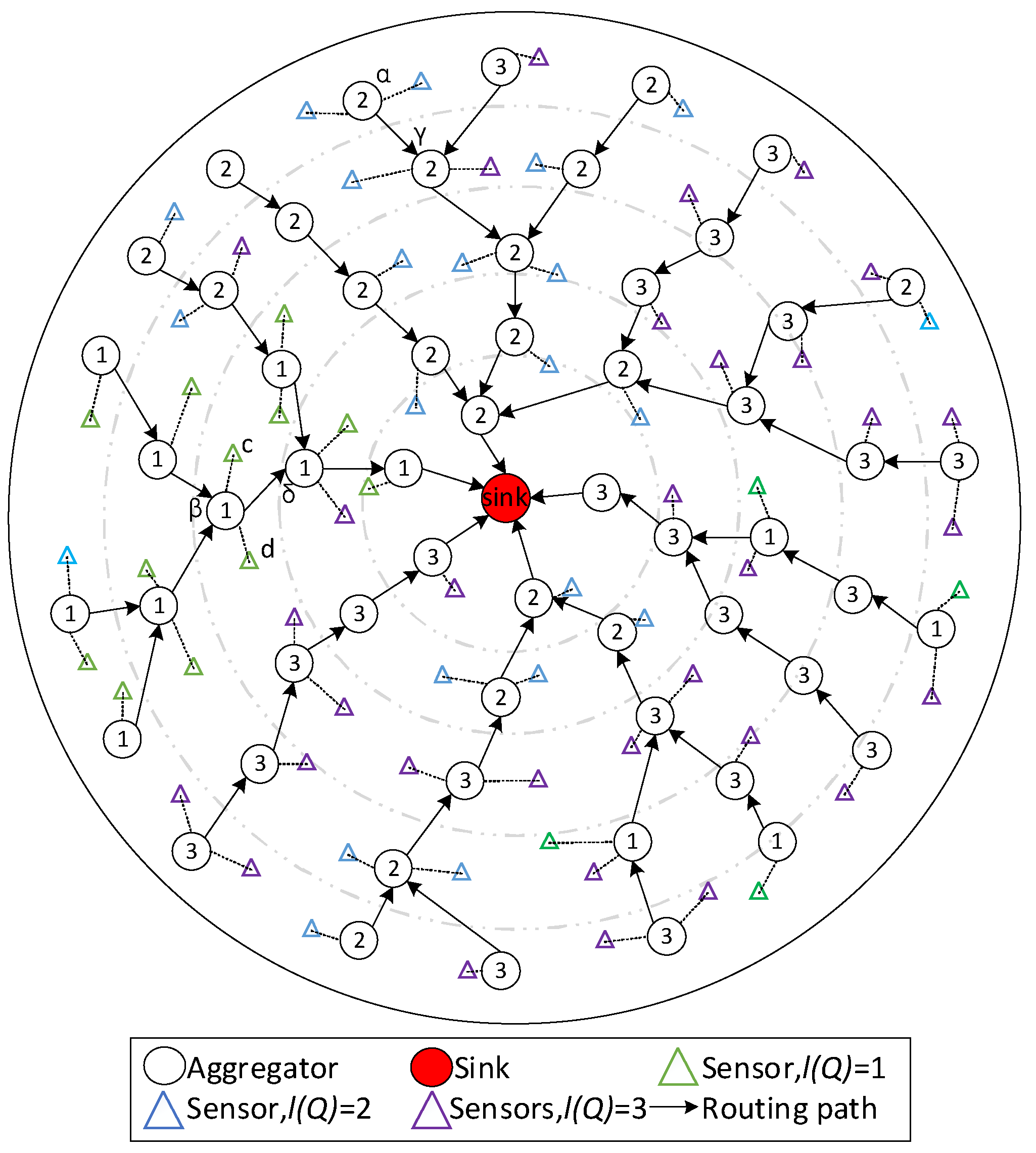
4.2. General Design of DDAR
- Aggregators identify their service tag.
- Aggregators configure and .
- Sensors determine the destination of their data.
- Aggregators choose an aggregator with the same service tag as their next hop.
- Service tags rotate.
| Algorithm 1 Configuration of Service Tag of Aggregator . |
| 1: Aggregator sends a broadcast message to sensors in its predetermined communication range to inquire the rank of service of each node. 2: Each sensor replies a message to inform the rank of service to the aggregator. 3: For each received by the aggregator do 4: ++ 5: End for 6: maxIndex = 0 7: For each do 8: If then 9: maxIndex = 10: End if 11: = maxIndex |
| Algorithm 2 Establishment of Routing for a Sensor . |
| 1: Sensor sends a broadcast message to aggregators in its predetermined communication range to inquire the tag of service of each node. 2: Each aggregator replies a message to inform the tag of service to the sensor. 3: For each received by the senisng node do 4: If == then 5: = 6: Return 7: End if 8: End for 9: If there is no aggregator whose is equal to 10: 11: While do 12: For each do 13: If then 14: 15: Return 16: End if 17: End for 18: index-- 19: End while 20: 21: While do 22: For each do 23: If then 24: 25: Return 26: End if 27: End for 28: index++ 29: End while 30: End if |
| Algorithm 3 Establishment of Routing for an Aggregator in Level . |
| 1: Aggregator sends a broadcast message to aggregators in its predetermined communication range to inquire the tag of service of each node. 2: Each aggregator replies a message to inform the tag of service to the sensor. 3: For each received by the senisng node do 4: If == then 5: = 6: Return 7: End if 8: End for 9: If there is an aggregator with no service tag 10: = 11: = 12: Return 13: End if 14: If there is no aggregator whose is equal to 15: 16: While do 17: For each do 18: If then 19: 20: Return 21: End if 22: End for 23: index-- 24: End while 25: 26: While do 27: For each do 28: If then 29: 30: Return 31: End if 32: End for 33: index++ 34: End while 35: End if |
5. Performance Analysis and Optimization
5.1. Optimization Performance on Service Guarantee Rate
5.2. Optimization Performances on Lifetime
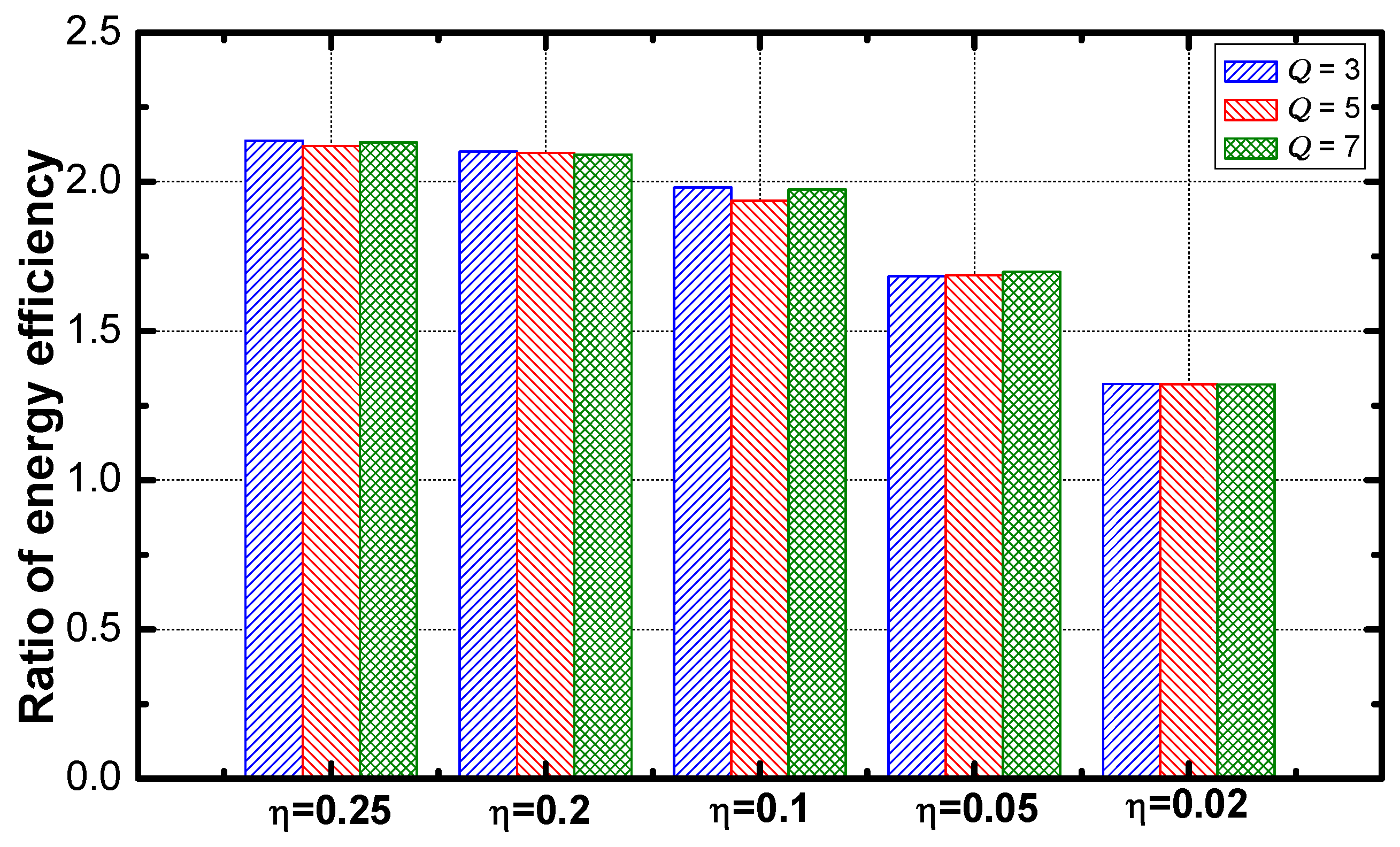
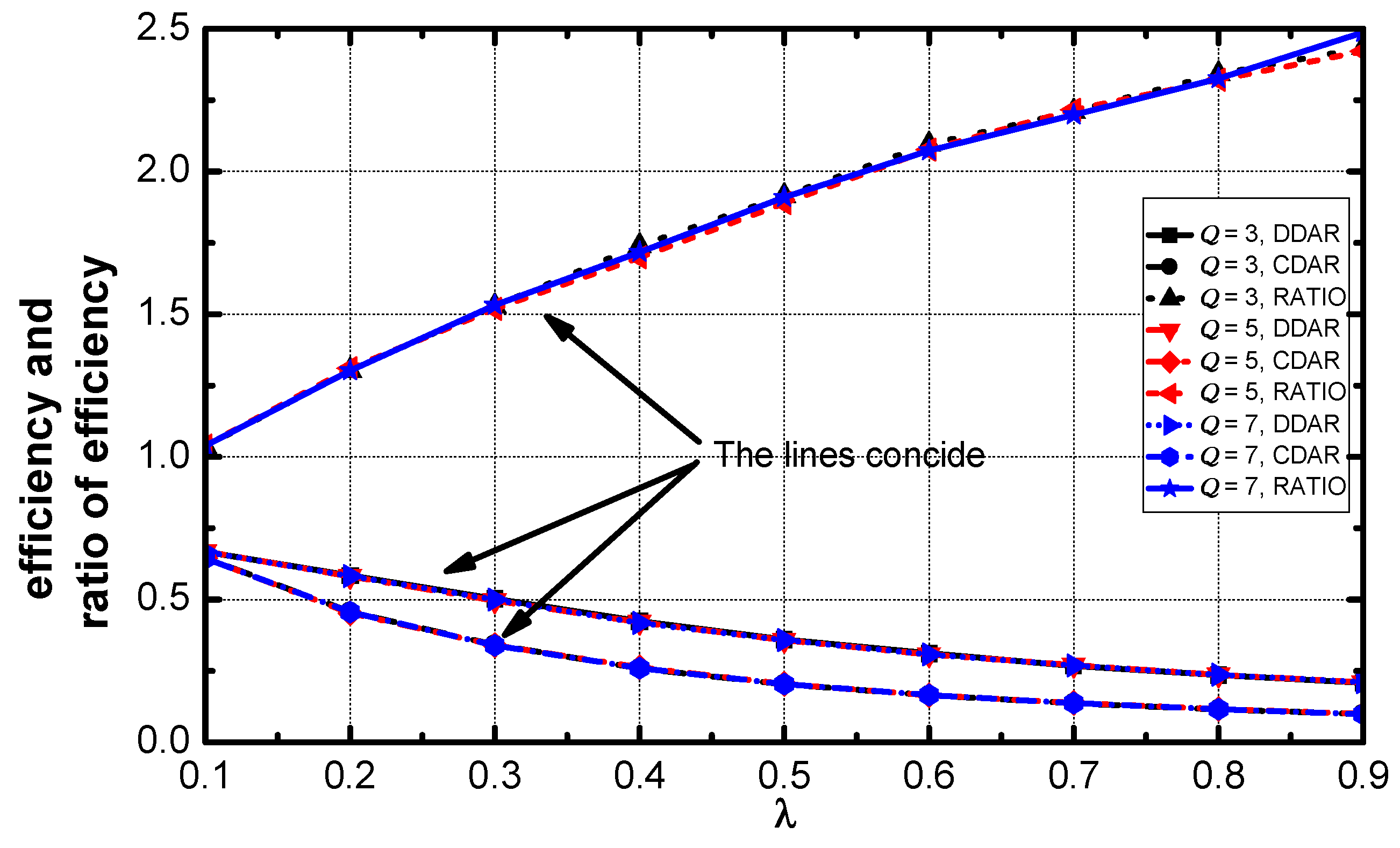
5.3. Optimization Performance on Energy Efficiency
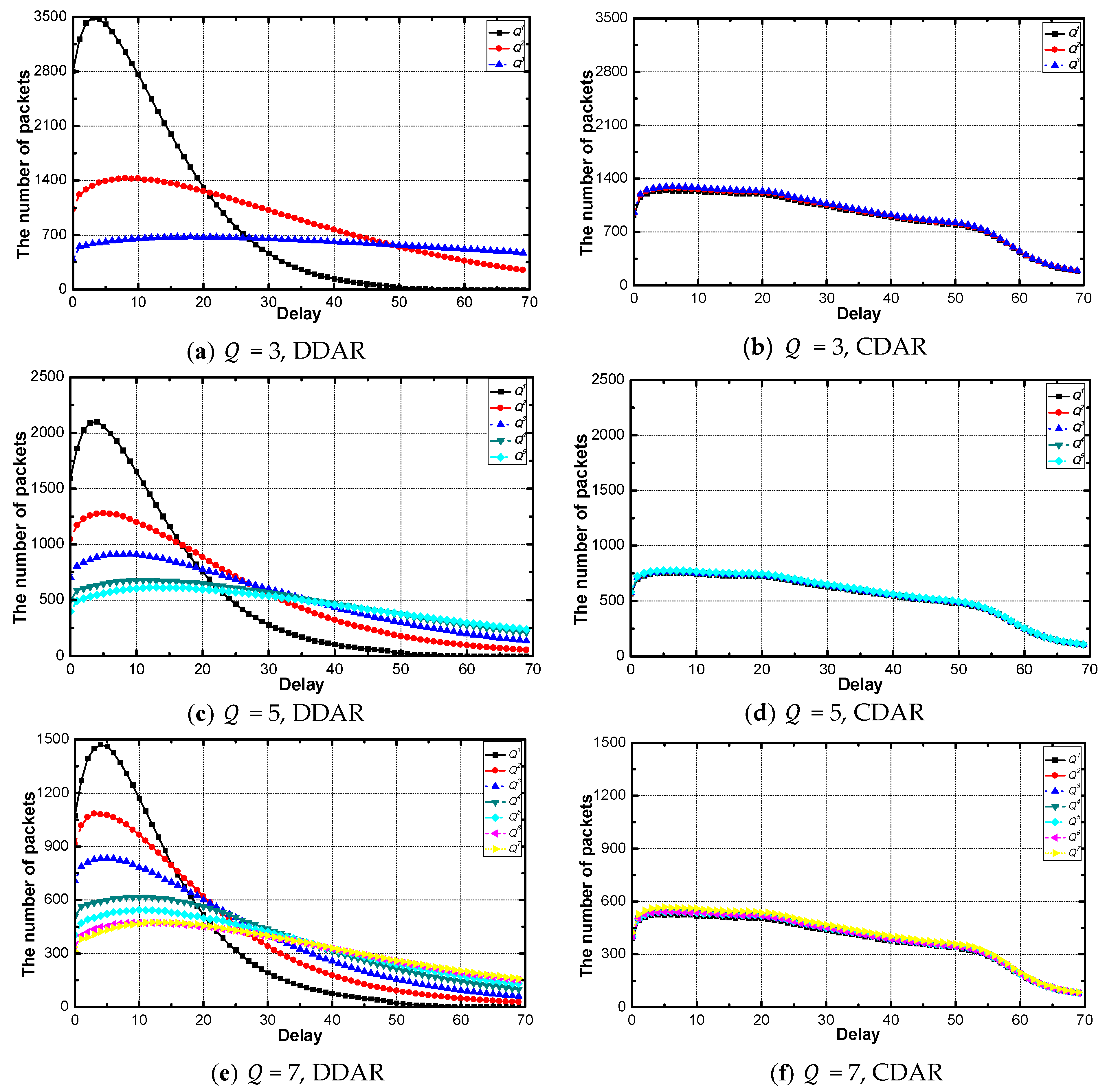
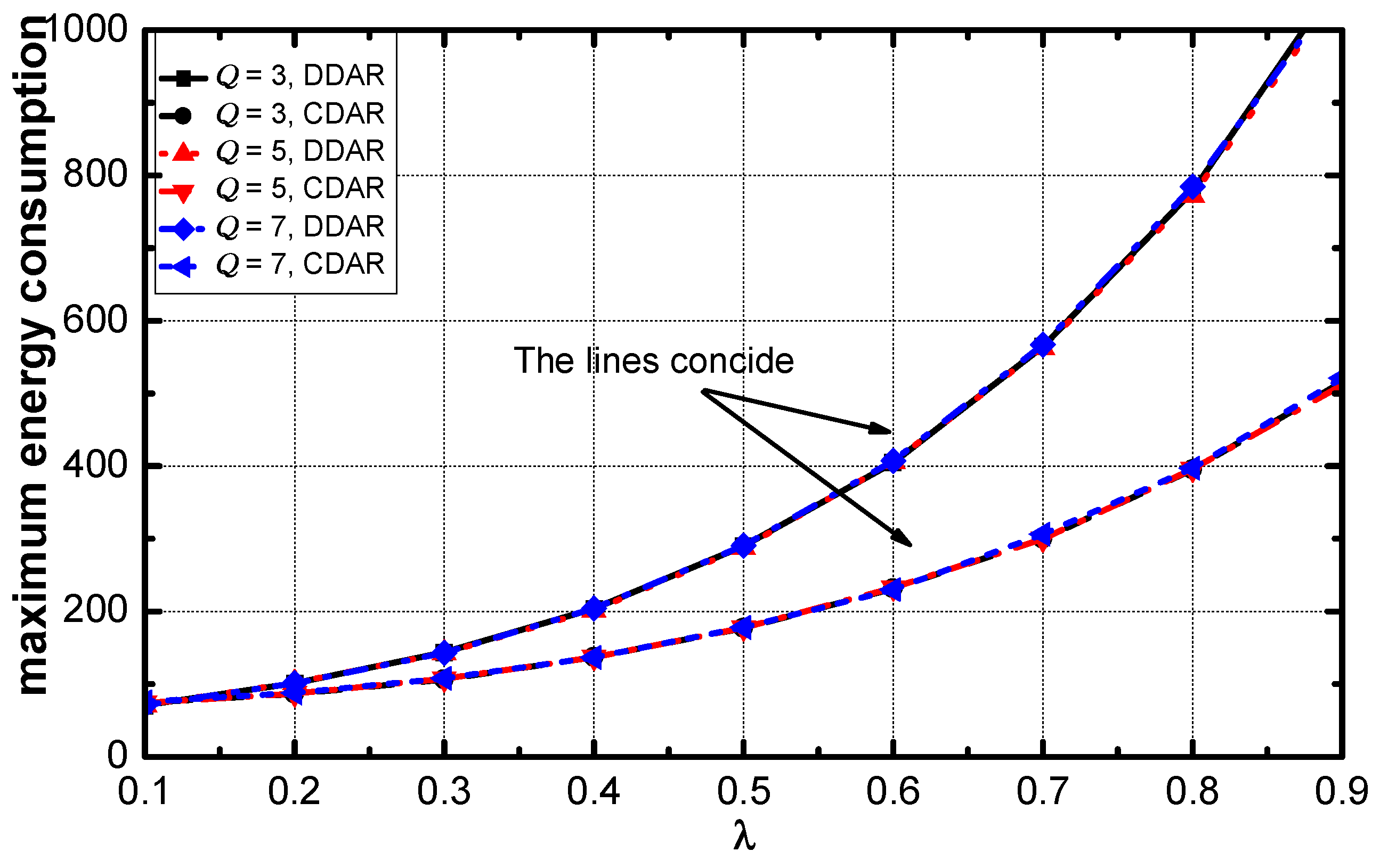
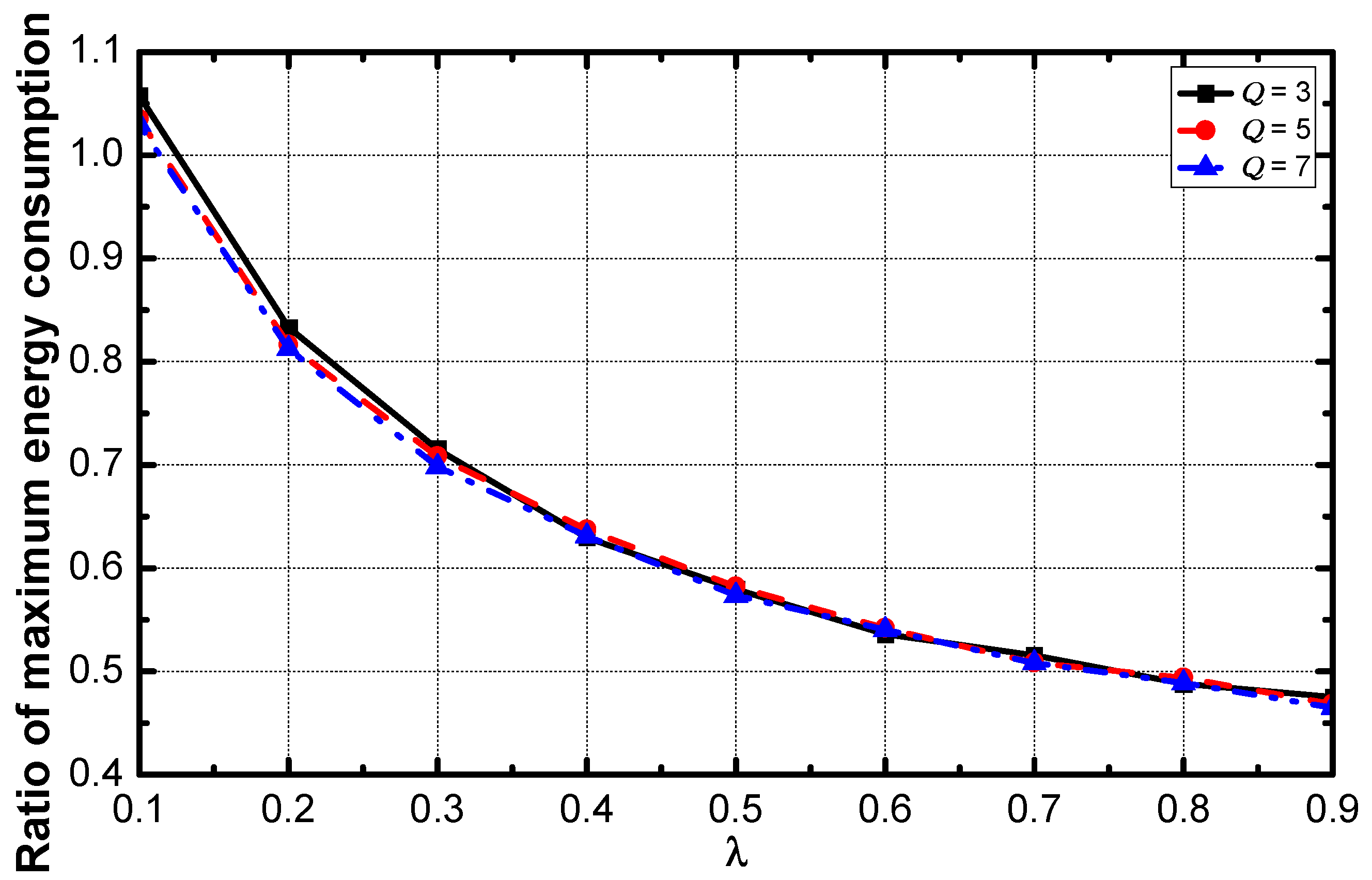
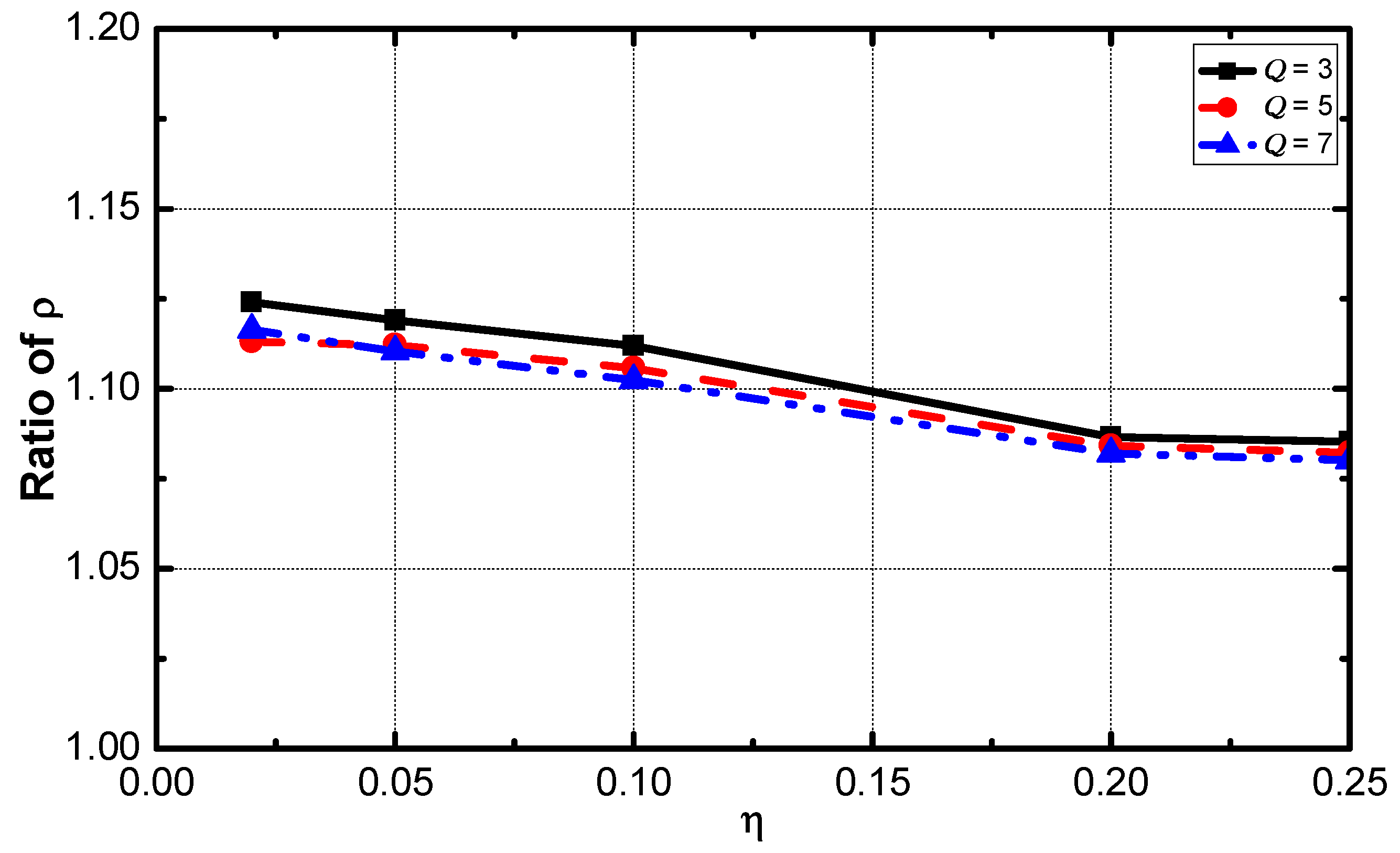
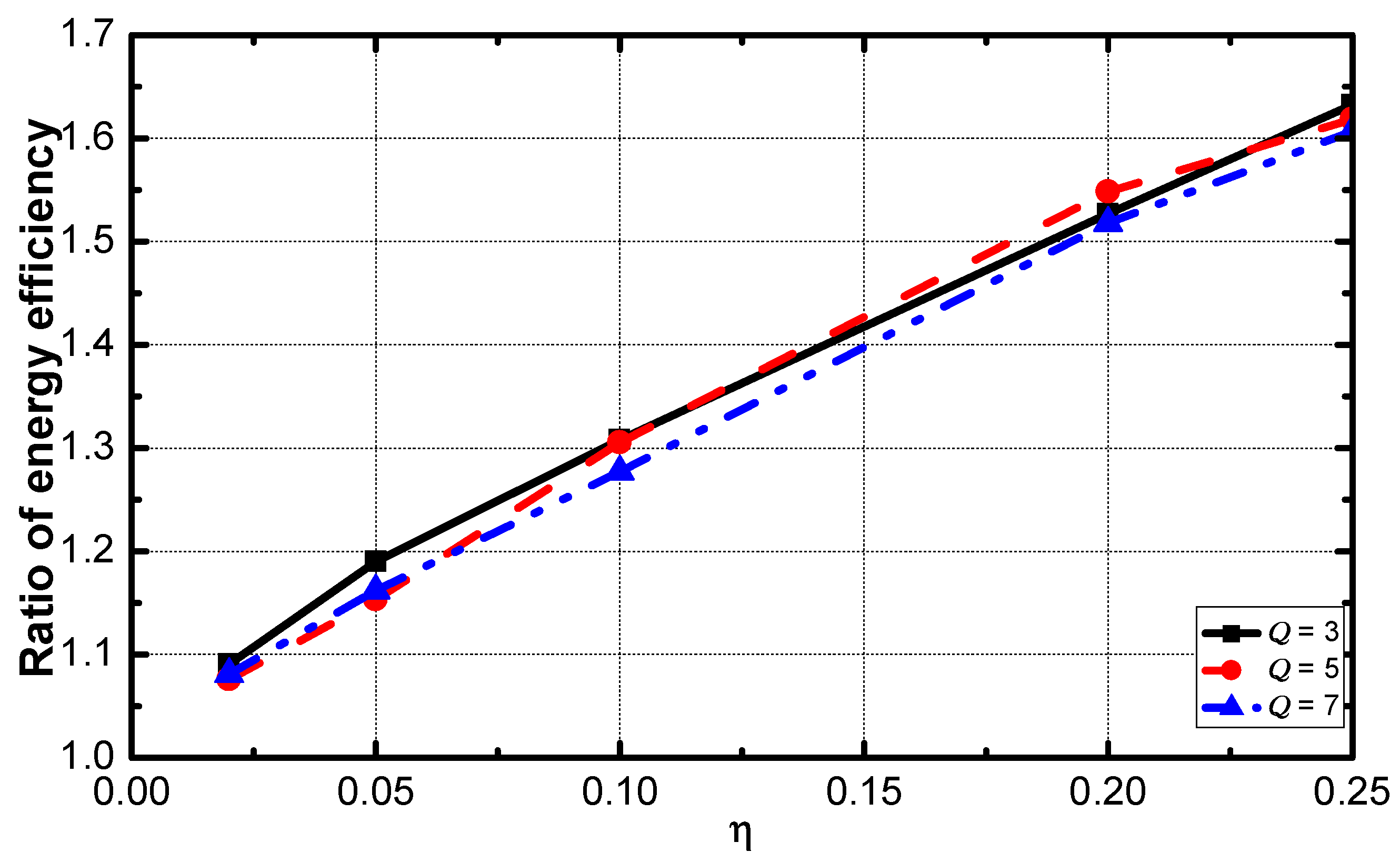
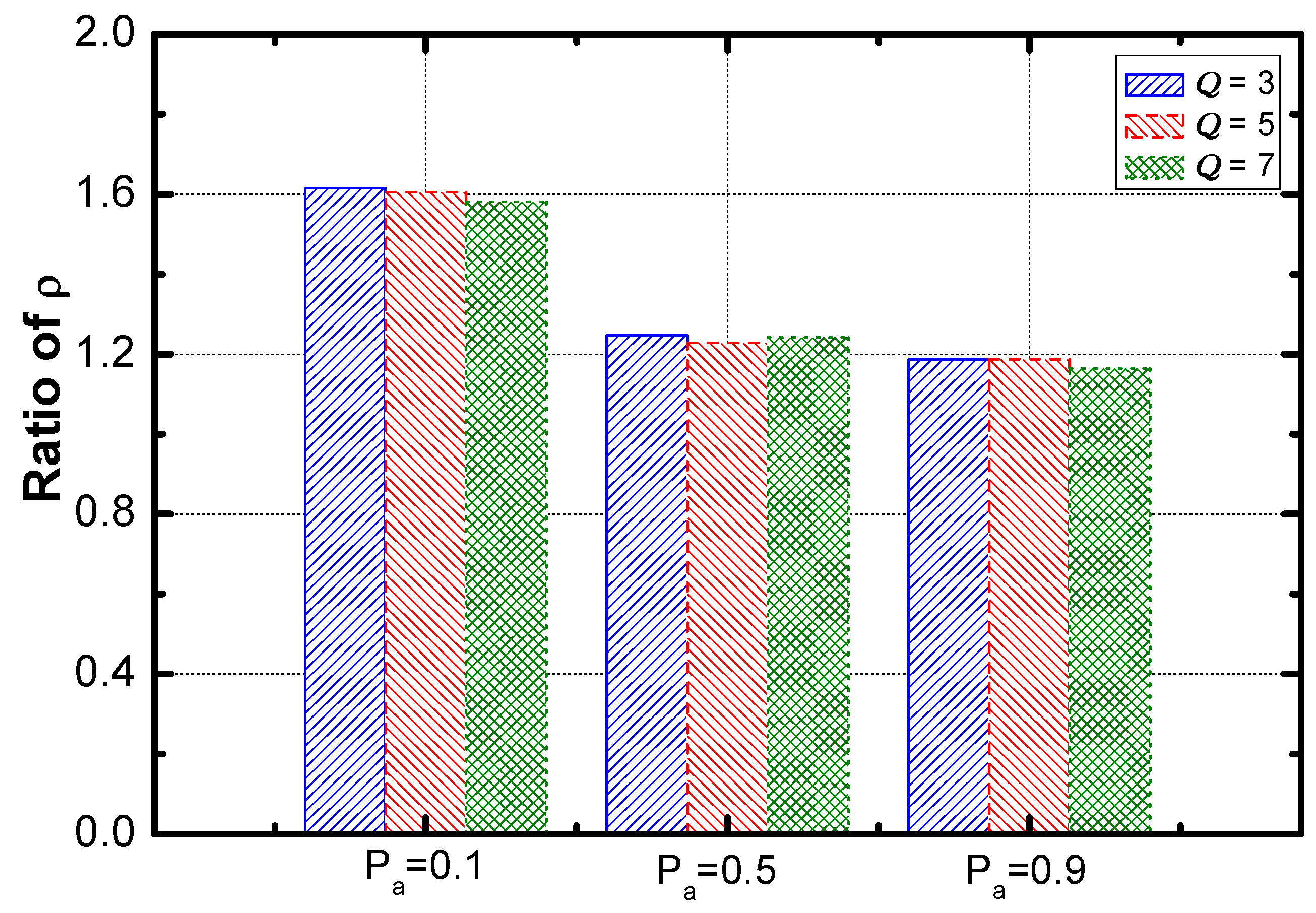
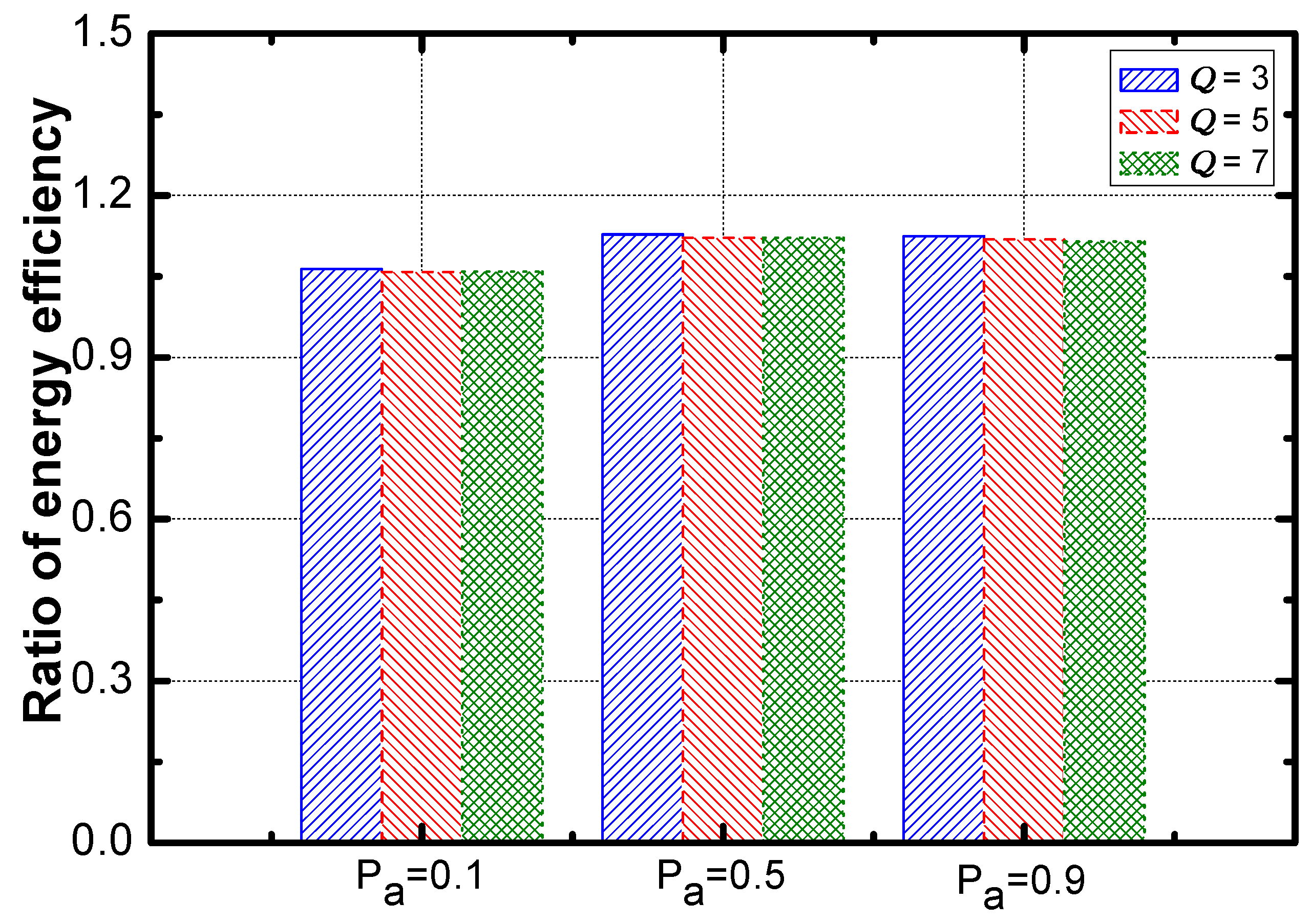
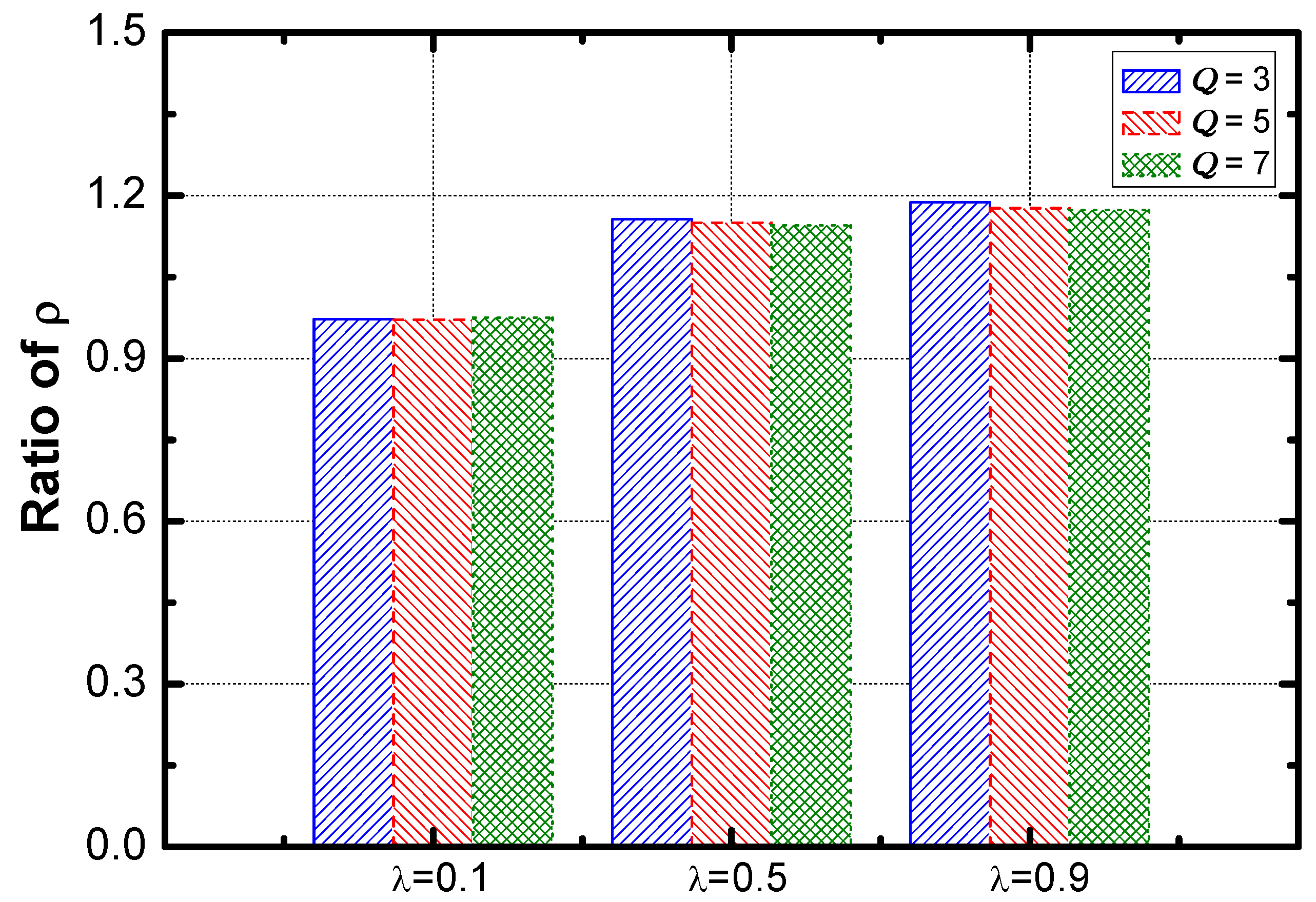
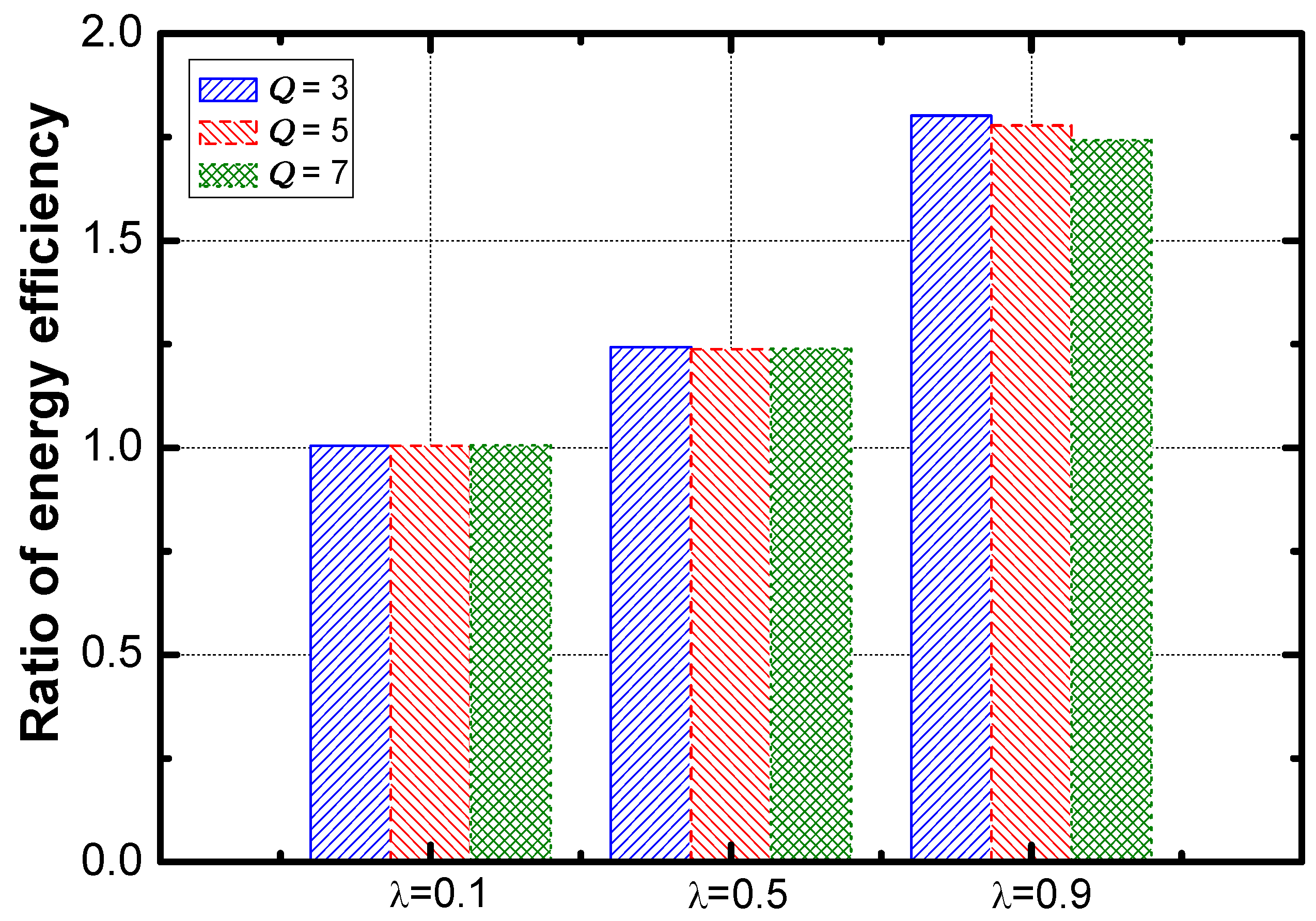
5.4. Performance of the Improved DDAR Scheme vs. the Common DDAR Scheme
6. Conclusions
Author Contributions
Funding
Conflicts of Interest
References
- Mukherjee, M.; Shu, L.; Hu, L.; Hancke, G.P.; Zhu, C. Sleep scheduling in industrial wireless sensor networks for toxic gas monitoring. IEEE Wirel. Commun. 2017, 24, 106–112. [Google Scholar] [CrossRef]
- Wu, M.; Wu, Y.; Liu, C.; Cai, Z.; Xiong, N.; Liu, A.; Ma, M. An Effective Delay Reduction Approach through Portion of Nodes with Larger Duty Cycle for Industrial WSNs. Sensors 2018, 18, 1535. [Google Scholar] [CrossRef] [PubMed]
- Wang, X.; Ning, Z.; Wang, L. Offloading in Internet of Vehicles: A Fog-enabled Real-time Traffic Management System. IEEE Trans. Ind. Inf. 2018. [Google Scholar] [CrossRef]
- Liu, X.; Liu, Y.; Liu, A.; Yang, L. Defending On-Off Attacks using Light Probing Messages in Smart Sensors for Industrial Communication Systems. IEEE Trans. Ind. Inf. 2018. [Google Scholar] [CrossRef]
- Xiao, F.; Wang, Z.; Ye, N.; Wang, R.; Li, X.Y. One More Tag Enables Fine-Grained RFID Localization and Tracking. IEEE/ACM Trans. Netw. 2018, 26, 161–174. [Google Scholar] [CrossRef]
- Zhou, H.; Xu, S.; Ren, D.; Huang, C.; Zhang, H. Analysis of event-driven warning message propagation in vehicular ad hoc networks. Ad Hoc Netw. 2017, 55, 87–96. [Google Scholar] [CrossRef]
- Xiang, J.; Zhou, Z.; Shu, L.; Rahman, T.; Wang, Q. A Mechanism Filling Sensing Holes for Detecting the Boundary of Continuous Objects in Hybrid Sparse Wireless Sensor Networks. IEEE Access 2017, 5, 7922–7935. [Google Scholar] [CrossRef]
- Huang, B.; Liu, A.; Zhang, C.; Xiong, N.; Zeng, Z.; Cai, Z. Caching Joint Shortcut Routing to Improve Quality of Experiments of Users for Information-Centric Networking. Sensors 2018, 18, 1750. [Google Scholar] [CrossRef] [PubMed]
- Zhu, H.; Xiao, F.; Sun, L.; Wang, R.; Yang, P. R-TTWD: Robust device-free through-the-wall detection of moving human with WiFi. IEEE J. Sel. Areas Commun. 2017, 35, 1090–1103. [Google Scholar] [CrossRef]
- Liu, X.; Dong, M.; Liu, Y.; Liu, A.; Xiong, N. Construction Low Complexity and Low Delay CDS for Big Data Codes Dissemination. Complexity 2018, 2018. [Google Scholar] [CrossRef]
- Ding, Z.; Ota, K.; Liu, Y.; Zhang, N.; Zhao, M.; Song, H.; Liu, A.; Cai, Z. Orchestrating Data as Services based Computing and Communication Model for Information-Centric Internet of Things. IEEE Access 2018. [Google Scholar] [CrossRef]
- Huang, M.; Liu, A.; Xiong, N.; Wang, T.; Vasilakos, A.V. A Low-latency Communication Scheme for Mobile Wireless Sensor Control Systems. IEEE Trans. Syst. Man Cybern. Syst. 2018, PP, 1–16. [Google Scholar] [CrossRef]
- Ye, X.; Li, J.; Xu, L. Distributed Separate Coding for Continuous Data Collection in Wireless Sensor Networks. ACM Trans. Sens. Netw. 2014, 11, 17. [Google Scholar] [CrossRef]
- Bhuiyan, M.Z.A.; Wang, G.; Wu, J.; Cao, J.; Liu, X.; Wang, T. Dependable structural health monitoring using wireless sensor networks. IEEE Trans. Dependable Secure Comput. 2017, 14, 363–376. [Google Scholar] [CrossRef]
- Yu, S.; Liu, X.; Liu, A.; Xiong, N.; Cai, Z.; Wang, T. Adaption Broadcast Radius based Code Dissemination Scheme for Low Energy Wireless Sensor Networks. Sensors 2018, 18, 1509. [Google Scholar] [CrossRef] [PubMed]
- Xu, X.; Zhang, N.; Song, H.; Liu, A.; Zhao, M.; Zeng, Z. Adaptive Beaconing based MAC Protocol for Sensor based Wearable System. IEEE Access 2018, 6, 29700–29714. [Google Scholar] [CrossRef]
- Liu, X.; Liu, Y.; Xiong, N.; Zhang, N.; Liu, A.; Shen, H.; Huang, C. Construction of Large-Scale Low Cost Deliver Infrastructure using Vehicular Networks. IEEE Access 2018, 6, 21482–21497. [Google Scholar] [CrossRef]
- Li, J.; Li, Y.K.; Chen, X.; Lee, P.P.C.; Lou, W. A hybrid cloud approach for secure authorized deduplication. IEEE Trans. Parallel Distrib. Syst. 2015, 26, 1206–1216. [Google Scholar] [CrossRef]
- Li, J.; Li, J.; Chen, X.; Jia, C.; Lou, W. Identity-based encryption with outsourced revocation in cloud computing. IEEE Trans. Comput. 2015, 64, 425–437. [Google Scholar] [CrossRef]
- Huang, M.; Liu, Y.; Zhang, N.; Xiong, N.; Liu, A.; Zeng, Z.; Song, H. A Services Routing based Caching Scheme for Cloud Assisted CRNs. IEEE Access 2018, 6, 15787–15805. [Google Scholar] [CrossRef]
- Liu, Y.; Liu, A.; Guo, S.; Li, Z.; Choi, Y.J. Context-aware collect data with energy efficient in Cyber-physical cloud systems. Future Gener. Comput. Syst. 2017. [CrossRef]
- Guo, Y.; Liu, F.; Cai, Z.; Xiao, N.; Zhao, Z. Edge-Based Efficient Search over Encrypted Data Mobile Cloud Storage. Sensors 2018, 18, 1189. [Google Scholar] [CrossRef] [PubMed]
- Li, Z.; Chang, B.; Wang, S.; Liu, A.; Zeng, F.; Luo, G. Dynamic Compressive Wide-band Spectrum Sensing Based on Channel Energy Reconstruction in Cognitive Internet of Things. IEEE Trans. Ind. Inf. 2018, 14, 2598–2607. [Google Scholar] [CrossRef]
- Yang, G.; He, S.; Shi, Z. Leveraging crowdsourcing for efficient malicious users detection in large-scale social networks. IEEE Int. Things J. 2017, 4, 330–339. [Google Scholar] [CrossRef]
- Zhou, H.; Wang, H.; Li, X.; Leung, V. A Survey on Mobile Data Offloading Technologies. IEEE Access 2018, 6, 5101–5111. [Google Scholar] [CrossRef]
- Teng, H.; Zhang, K.; Dong, M.; Ota, K.; Liu, A.; Zhao, M.; Wang, T. Adaptive Transmission Range based Topology Control Scheme for Fast and Reliable Data Collection. Wirel. Commun. Mob. Comput. 2018, 2018. [Google Scholar] [CrossRef]
- Xu, J.; Liu, A.; Xiong, N.; Wang, T.; Zuo, Z. Integrated Collaborative Filtering Recommendation in Social Cyber-Physical Systems. Int. J. Distrib. Sens. Netw. 2017, 13. [Google Scholar] [CrossRef]
- Zhou, H.; Ruan, M.; Zhu, C.; Leung, V.; Xu, S.; Huang, C. A Time-ordered Aggregation Model-based Centrality Metric for Mobile Social Networks. IEEE Access 2018, 6, 25588–25599. [Google Scholar] [CrossRef]
- Jiang, W.; Wang, G.; Bhuiyan, M.Z.A.; Wu, J. Understanding graph-based trust evaluation in online social networks: Methodologies and challenges. ACM Comput. Surv. (CSUR) 2016, 49, 10. [Google Scholar] [CrossRef]
- Ning, Z.; Wang, X.; Kong, X.; Hou, W. A social-aware group formation framework for information diffusion in narrowband internet of things. IEEE Int. Things J. 2017, 5, 1527–1538. [Google Scholar] [CrossRef]
- Liu, Q.; Liu, A. On the hybrid using of unicast-broadcast in wireless sensor networks. Comput. Electr. Eng. 2017. [Google Scholar] [CrossRef]
- Liu, X.; Li, G.; Zhang, S.; Liu, A. Big Program Code Dissemination Scheme for Emergency Software-Define Wireless Sensor Networks. Peer-to-Peer Netw. Appl. 2018, 11, 1038–1059. [Google Scholar] [CrossRef]
- Ren, Y.; Liu, Y.; Zhang, N.; Liu, A.; Xiong, N.; Cai, Z. Minimum-Cost Mobile Crowdsourcing with QoS Guarantee Using Matrix Completion Technique. Pervasive Mob. Comput. 2018, 49, 23–44. [Google Scholar] [CrossRef]
- Zhou, K.; Gui, J.; Xiong, N. Improving cellular downlink throughput by multi-hop relay-assisted outband D2D communications. EURASIP J. Wirel. Commun. Netw. 2017, 2017, 209. [Google Scholar] [CrossRef]
- Ota, K.; Dong, M.; Gui, J.; Liu, A. QUOIN: Incentive Mechanisms for Crowd Sensing Networks. IEEE Netw. 2018, 32, 114–119. [Google Scholar] [CrossRef]
- Tang, J.; Liu, A.; Zhang, J.; Zeng, Z.; Xiong, N.; Wang, T. A Security Routing Scheme Using Traceback Approach for Energy Harvesting Sensor Networks. Sensors 2018, 18, 751. [Google Scholar] [CrossRef] [PubMed]
- Liu, A.; Huang, M.; Zhao, M.; Wang, T. A Smart High-Speed Backbone Path Construction Approach for Energy and Delay Optimization in WSNs. IEEE Access 2018, 6, 13836–13854. [Google Scholar] [CrossRef]
- Naranjo, P.G.V.; Shojafar, M.; Mostafaei, H.; Pooranian, Z.; Baccarelli, E. P-SEP: A prolong stable election routing algorithm for energy-limited heterogeneous fog-supported wireless sensor networks. J. Supercomput. 2017, 73, 733–755. [Google Scholar] [CrossRef]
- Xu, X.; Yuan, M.; Liu, X.; Liu, A.; Xiong, N.; Cai, Z.; Wang, T. Cross-layer Optimized Opportunistic Routing Scheme for Loss-and-delay Sensitive WSNs. Sensors 2018, 18, 1422. [Google Scholar] [CrossRef] [PubMed]
- Li, X.; Liu, A.; Xie, M.; Xiong, N.; Zeng, Z.; Cai, Z. Adaptive Aggregation Routing to Reduce Delay for Multi-Layer Wireless Sensor Networks. Sensors 2018, 18, 1216. [Google Scholar] [CrossRef] [PubMed]
- Xu, X.; Li, X.Y.; Mao, X.; Tang, S.; Wang, S. A delay-efficient algorithm for data aggregation in multihop wireless sensor networks. IEEE Trans. Parallel Distrib. Syst. 2011, 22, 163–175. [Google Scholar]
- Kim, U.H.; Kong, E.; Choi, H.H.; Lee, J.R. Analysis of Aggregation Delay for Multisource Sensor Data with On-Off Traffic Pattern in Wireless Body Area Networks. Sensors 2016, 16, 1622. [Google Scholar] [CrossRef] [PubMed]
- Li, Z.; Liu, Y.; Ma, M.; Liu, A.; Zhang, X.; Luo, G. MSDG: A Novel Green Data Gathering Scheme for Wireless Sensor Networks. Comp. Netw. 2018, 142, 223–239. [Google Scholar] [CrossRef]
- Cheng, L.; Niu, J.; Luo, C.; Shu, L.; Kong, L.; Zhao, Z.; Gu, Y. Towards minimum-delay and energy-efficient flooding in low-duty-cycle wireless sensor networks. Comp. Netw. 2018, 134, 66–77. [Google Scholar] [CrossRef]
- Wang, J.; Liu, A.; Yan, T.; Zeng, Z. A Resource Allocation Model Based on Double-sided Combinational Auctions for Transparent Computing. Peer-to-Peer Netw. Appl. 2018, 11, 1038–1059. [Google Scholar] [CrossRef]
- Liu, X.; Dong, M.; Ota, K.; Yang, L.T.; Liu, A. Trace malicious source to guarantee cyber security for mass monitor critical infrastructure. J. Comput. Syst. Sci. 2016. [Google Scholar] [CrossRef]
- Bhuiyan, M.Z.A.; Wu, J.; Wang, G.; Wang, T.; Hassan, M.M. e-Sampling: Event-Sensitive Autonomous Adaptive Sensing and Low-Cost Monitoring in Networked Sensing Systems. ACM Trans. Auton. Adapt. Syst. 2017, 12, 1. [Google Scholar] [CrossRef]
- Le Nguyen, P.; Ji, Y.; Liu, Z.; Vu, H.; Nguyen, K.V. Distributed hole-bypassing protocol in WSNs with constant stretch and load balancing. Comput. Netw. 2017, 129, 232–250. [Google Scholar] [CrossRef]
- Chen, X.; Pu, L.; Gao, L.; Wu, W.; Wu, D. Exploiting massive D2D collaboration for energy-efficient mobile edge computing. IEEE Wirel. Commun. 2017, 24, 64–71. [Google Scholar] [CrossRef]
- Fang, S.; Cai, Z.; Sun, W.; Liu, A.; Liu, F.; Liang, Z.; Wang, G. Feature Selection Method Based on Class Discriminative Degree for Intelligent Medical Diagnosis. CMC Comput. Mater. Continua 2018, 55, 419–433. [Google Scholar]
- Li, J.; Chen, X.; Li, M.; Li, J.; Lee, P.; Lou, W. Secure Deduplication with Efficient and Reliable Convergent Key Management. IEEE Trans. Parallel Distrib. Syst. 2014, 25, 1615–1625. [Google Scholar] [CrossRef]
- Chen, X.; Li, J.; Weng, J.; Ma, J.; Lou, W. Verifiable computation over large database with incremental updates. IEEE Trans. Comput. 2016, 65, 3184–3195. [Google Scholar] [CrossRef]
- Li, T.; Tian, S.; Liu, A.; Liu, H.; Pei, T. DDSV: Optimizing Delay and Delivery Ratio for Multimedia Big Data Collection in Mobile Sensing Vehicles. IEEE Int. Things J. 2018. [Google Scholar] [CrossRef]
- Gui, J.S.; Hui, L.H.; Xiong, N.X. Enhancing Cellular Coverage Quality by Virtual Access Point and Wireless Power Transfer. Wirel. Commun. Mob. Comput. 2018. [Google Scholar] [CrossRef]
- Pu, L.; Chen, X.; Xu, J.; Fu, X. D2D fogging: An energy-efficient and incentive-aware task offloading framework via network-assisted D2D collaboration. IEEE J. Sel. Areas Commun. 2016, 34, 3887–3901. [Google Scholar] [CrossRef]
- Liu, A.; Zhao, S. High Performance Target Tracking Scheme with Low Prediction Precision Requirement in WSNs. Int. J. Ad Hoc Ubiquitous Comput. 2017. Available online: http://www.inderscience.com /info/ingeneral/forthcoming.php?jcode=ijahuc (accessed on 2 May 2018).
- Nazhad, S.H.H.; Shojafar, M.; Shamshirband, S.; Conti, M. An efficient routing protocol for the QoS support of large-scale MANETs. Int. J. Commun. Syst. 2018, 31, 1–18. [Google Scholar] [CrossRef]
- Huang, S.; Wan, P.; Vu, C.T.; Li, Y.; Yao, F. Nearly constant approximation for data aggregation scheduling in wireless sensor networks. In Proceedings of the 26th IEEE International Conference on Computer Communications (INFOCOM 2007), Vancouver, BC, Canada, 31 July–3 August 2007; pp. 366–372. [Google Scholar]
- Jiang, L.; Liu, A.; Hu, Y.; Chen, Z. Lifetime Maximization through Dynamic Ring-Based Routing Scheme for Correlated Data Collecting in WSNs. Comput. Electr. Eng. 2015, 41, 191–215. [Google Scholar] [CrossRef]
- Villas, L.A.; Boukerche, A.; Ramos, H.S.; de Oliveira, H.A.F.; de Araujo, R.B.; Loureiro, A.A.F. DRINA: A lightweight and reliable routing approach for in-network aggregation in wireless sensor networks. IEEE Trans. Comput. 2013, 62, 676–689. [Google Scholar] [CrossRef]
- Neamatollahi, P.; Abrishami, S.; Naghibzadeh, M.; Moghaddam, M.H.Y.; Younis, O. Hierarchical Clustering-Task Scheduling Policy in Cluster-Based Wireless Sensor Networks. IEEE Trans. Ind. Inf. 2018, 14, 1876–1886. [Google Scholar] [CrossRef]
- Liu, A.; Liu, X.; Wei, T.; Yang, L.; Rho, S.; Paul, A. Distributed Multi-Representative Re-Fusion Approach for Heterogeneous Sensing Data Collection. ACM Trans. Embed. Comput. Syst. 2017, 16, 73. [Google Scholar] [CrossRef]
- Liu, A.; Zheng, Z.; Zhang, C.; Chen, Z.; Shen, X. Secure and Energy-Efficient Disjoint Multi-Path Routing for WSNs. IEEE Trans. Veh. Technol. 2012, 61, 3255–3265. [Google Scholar] [CrossRef]
- Liu, Y.; Liu, A.; Hu, Y.; Li, Z.; Choi, Y.; Sekiya, H.; Li, J. FFSC: An Energy Efficiency Communications Approach for Delay Minimizing in Internet of Things. IEEE Access 2016, 4, 3775–3793. [Google Scholar] [CrossRef]
- Liu, Y.; Liu, A.; Chen, Z. Analysis and Improvement of Send-and-Wait Automatic Repeat-Request Protocols for Wireless Sensor Networks. Wirel. Pers. Commun. 2015, 81, 923–959. [Google Scholar] [CrossRef]
| Problem Set | Work |
|---|---|
| Convergecast | Xu et al. [41], Huang et al. [58] |
| Adaptive Aggregation Scheme | Li et al. [42] |
| Optimize Data Aggregation | Villa et al. [61] |
| Cluster-based WSNs | Nazhad et al. [62] |
| Approximate Routing | Liu et al. [63] |
| Problem Set | Work |
|---|---|
| Optimizing the transmission power | Xu et al. [16] |
| Routing Algorithms to Balance The Energy | Huang et al. [20], Tang et al. [36], Naranjo et al. [38], Xu et al. [39], Hazard et al. [57] |
| Optimizations Including Security | Tang et al. [36] |
| Data packets split | Liu et al. [63] |
| Optimizing The Delay in Duty Cycle | Liu et al. [64] |
| Sending Data to Multiple receivers | Xu et al. [39], |
| Optimization for Retransmission | Liu et al. [65] |
| Parameter | Description |
|---|---|
| The number of the nodes in the network. | |
| The number of the layers in the network. | |
| The proportion of aggregators in nodes. | |
| An aggregator. | |
| A sensor. | |
| The value of packet aggregation threshold for the service requirement . | |
| The value of the packet aggregation timer for service requirement . | |
| The probability that a sensor generates a data packet during a packet generation period. | |
| Data aggregation ratio. | |
| The number of the type of service requirements in a network. | |
| The initial energy in an aggregator . | |
| The energy consumption of aggregator in a unit time | |
| The level of service requirement of sensor . | |
| The value of service requirement . | |
| Service guarantee rate. | |
| The service tag of aggregator . | |
| The aggregator that sensor transmits the data packets to. | |
| The next hop that the aggregated queues of aggregator transmits the data packets to. |
| L = 4 | L = 5 | L = 6 | L = 7 | |
|---|---|---|---|---|
| 97.61 | 97.66 | 97.73 | 97.71 | |
| 97.53 | 97.66 | 97.81 | 97.74 | |
| 97.65 | 97.73 | 98.02 | 98.42 |
| Parameter | Value |
|---|---|
| 100 (m) | |
| 20 (m) | |
| 1000 | |
| {0.1, 0.5, 0.9} | |
| {0.1, 0.2, 0.3, 0.4, 0.5, 0.6, 0.7, 0.8, 0.9} | |
| {0.02, 0.05, 0.1, 0.2, 0.25} | |
| {3, 5, 7} | |
| {3, 50, 30},{5, 50, 15},{7, 50, 10} |
| Ratio of (%) | 132.7 | 122.65 | 119.68 |
| DDAR (J) | CDAR (J) | Ratio (%) | |
|---|---|---|---|
| 226.78 | 403.57 | 64.78 | |
| 224.82 | 400.70 | 64.35 | |
| 224.79 | 403.86 | 63.86 |
| DDAR (J) | |||
| 229.41 | 224.38 | 229.54 | |
| 229.55 | 216.62 | 228.28 | |
| 229.09 | 218.42 | 226.87 | |
| CDAR (J) | |||
| 423.44 | 396.69 | 390.58 | |
| 420.37 | 396.96 | 384.78 | |
| 422.43 | 398.75 | 390.40 | |
| Ratio (%) | |||
| 63.53 | 63.97 | 67.85 | |
| 63.30 | 62.18 | 67.63 | |
| 62.72 | 61.90 | 66.98 |
| DDAR (%) | CDAR (%) | Ratio (%) | |
|---|---|---|---|
| 39.60 | 26.94 | 184.49 | |
| 39.47 | 26.97 | 183.22 | |
| 39.45 | 26.92 | 184.26 |
| DDAR (%) | |||
| 47.65 | 37.19 | 33.96 | |
| 47.00 | 37.35 | 34.05 | |
| 46.81 | 37.32 | 34.22 | |
| CDAR (%) | |||
| 29.55 | 25.73 | 25.96 | |
| 29.58 | 25.64 | 25.62 | |
| 29.56 | 25.64 | 25.78 | |
| Ratio (%) | |||
| 199.98 | 184.03 | 169.46 | |
| 195.24 | 185.24 | 169.91 | |
| 194.94 | 185.67 | 172.17 |
| Scenario | Energy Efficiency (%) | Service Guarantee Rate (%) | Energy Consumption (%) |
|---|---|---|---|
| 134.97 | 110.54 | 102.88 | |
| 134.03 | 109.95 | 103.23 | |
| 132.90 | 109.83 | 103.44 |
© 2018 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Li, X.; Liu, W.; Xie, M.; Liu, A.; Zhao, M.; Xiong, N.N.; Zhao, M.; Dai, W. Differentiated Data Aggregation Routing Scheme for Energy Conserving and Delay Sensitive Wireless Sensor Networks. Sensors 2018, 18, 2349. https://doi.org/10.3390/s18072349
Li X, Liu W, Xie M, Liu A, Zhao M, Xiong NN, Zhao M, Dai W. Differentiated Data Aggregation Routing Scheme for Energy Conserving and Delay Sensitive Wireless Sensor Networks. Sensors. 2018; 18(7):2349. https://doi.org/10.3390/s18072349
Chicago/Turabian StyleLi, Xujing, Wei Liu, Mande Xie, Anfeng Liu, Ming Zhao, Neal N. Xiong, Miao Zhao, and Wan Dai. 2018. "Differentiated Data Aggregation Routing Scheme for Energy Conserving and Delay Sensitive Wireless Sensor Networks" Sensors 18, no. 7: 2349. https://doi.org/10.3390/s18072349
APA StyleLi, X., Liu, W., Xie, M., Liu, A., Zhao, M., Xiong, N. N., Zhao, M., & Dai, W. (2018). Differentiated Data Aggregation Routing Scheme for Energy Conserving and Delay Sensitive Wireless Sensor Networks. Sensors, 18(7), 2349. https://doi.org/10.3390/s18072349








