Poaching Detection Technologies—A Survey
Abstract
:1. Introduction
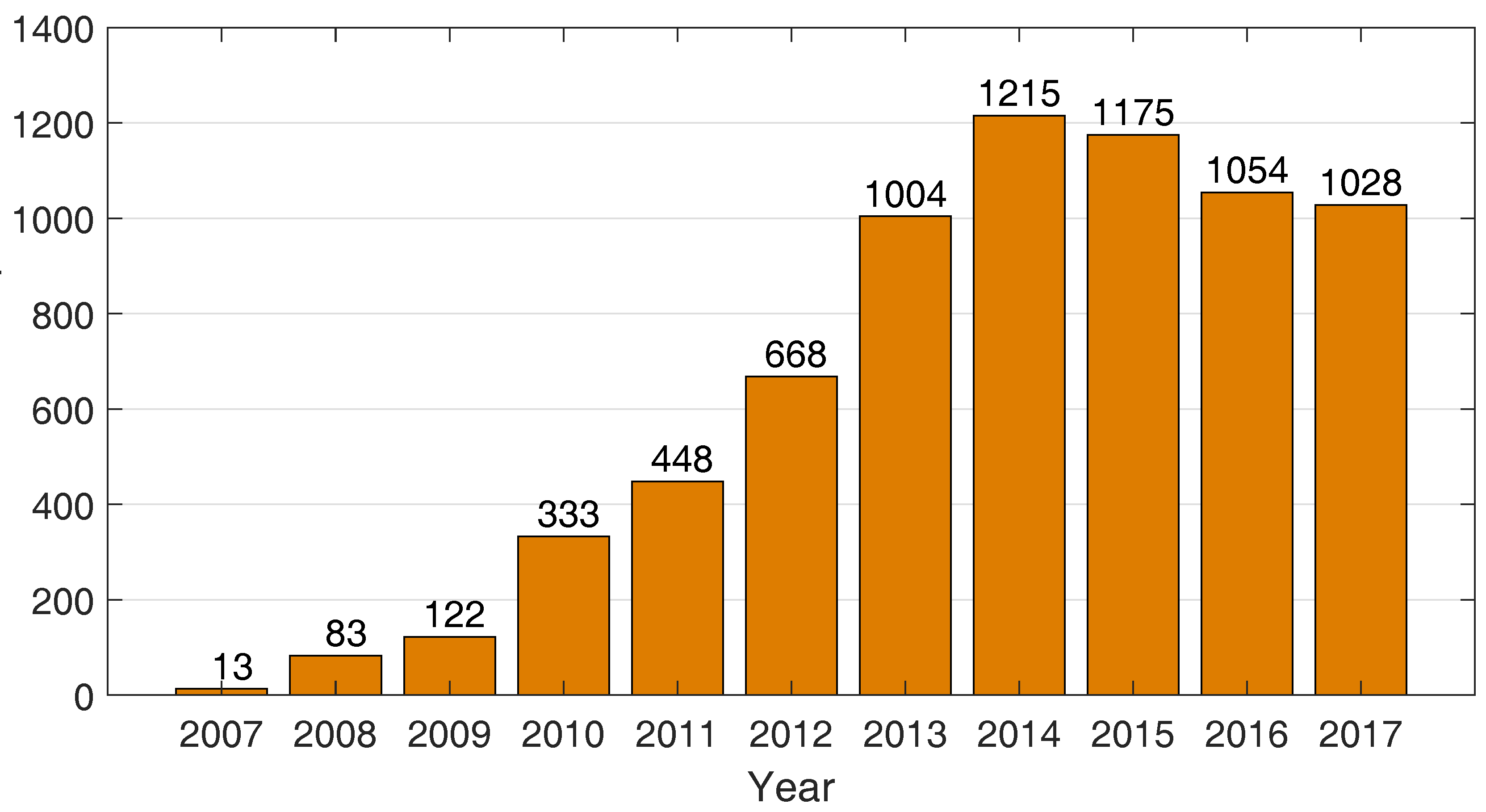
1.1. Poaching
1.2. Drivers of Demand
1.3. Drivers of Supply
1.4. Methods
2. Requirement of Poaching Detection Systems
- Energy Efficiency: Many locations in wildlife areas are very remote and do not have available infrastructure such as road, power lines, and network. Therefore, an APS can be isolated from power lines and rely solely on battery power and energy harvesting technologies. Any solution that is deployed in areas without infrastructure should be to operate for long periods of time to minimize costs and effort. The goal of an APS could be to have devices placed on animals or in the field, unattended, for months or years to come. Each device should be able to efficiently manage its local power supply in order to maximize the total system life-time in the long run, by deploying it on the field with a solar panel or energy harvesting mechanism to increase the energy efficiency by considering a hardware solution.
- Deployment issues: Game park managers are often uncomfortable with obtrusive technologies such as sensor poles or solar panels. These type of technologies are perceived to be unnatural. An APS usually covers a large area in which environmental factors such as weather conditions and wildlife interaction will eventually disable components of the APS. Hence, an APS should be easily maintainable so that a continuous protection of wildlife can be guaranteed. In addition, deployment of an APS should be camouflaged from poachers. Otherwise poachers might damage components and attempt to disable the APS. The system should avoid attracting visual attention, for instance, blinking LEDs, colorful mounting devices and other obviously visible pillars.
- Robustness: An APS should endure various technical and environmental deployment factors. Problems in a detection system can occur at any point between the poaching event, detection and surveillance process. For instance, the destruction of individual components should not lead to a complete failure of the overall system. Key challenges in wildlife parks include, but are not limited to, severe tropical storms, lightning strikes, flooding (near rivers) and field fires. Wildlife in parks can dig holes in the ground and play with any infrastructure that is placed in the park. Elephants and baboons, for example, can be very destructive. Hence, an APS should be robust to at least common technical faults among the distributed system components, and demonstrate strong resilience so that information remain uncorrupted.
- Scalability: The areas that are vulnerable to poaching activities are often very large. The APS should therefore be scalable. Technologically, the APS should be able to accommodate a growing number of additional devices joining the system. Scalability can be achieved by means of hardware and software techniques. When the APS is scaled up by introducing new hardware components, the system should seamlessly accept new components with no or little manual modification. Scalability also means the possibility of extending an APS in order to cover large areas, whilst staying within the bounds of other requirements denoted in this section.
- Coverage: Providing full coverage of the protected field is a very important aspect for a successful surveillance technique. In order to reduce coverage overlap, optimization methods should be used to select the best placement of the system devices. The system deployment should be positioned efficiently within a specified region to cover security blind spots and prevent intruders from exploiting these spots.
- Ethical and Legal Issues: When designing an APS that utilizes sensors located on or near animals, ethical and legal implications should be considered. When for example wildlife is collared, a general rule of thumb for the weight of an animal collar is usually 5% of their body weight [13]. Brooks et al. [14] found a significant effect of collar weight and its fit on the travel rate of zebra females. The authors compared two types of Global Positioning System (GPS) collars. Although types of GPS collars were well within accepted norms of collar weight, the slightly heavier collars (0.6% of the total body mass) reduced the rate of travel by more than 5% when foraging compared with the collar that was 0.4% of total body mass. When utilizing animals for an APS or related research, all aspects of animal handling and research should comply with methods such as those proposed by the American Society of Mammalogists for research on wild mammals [15].
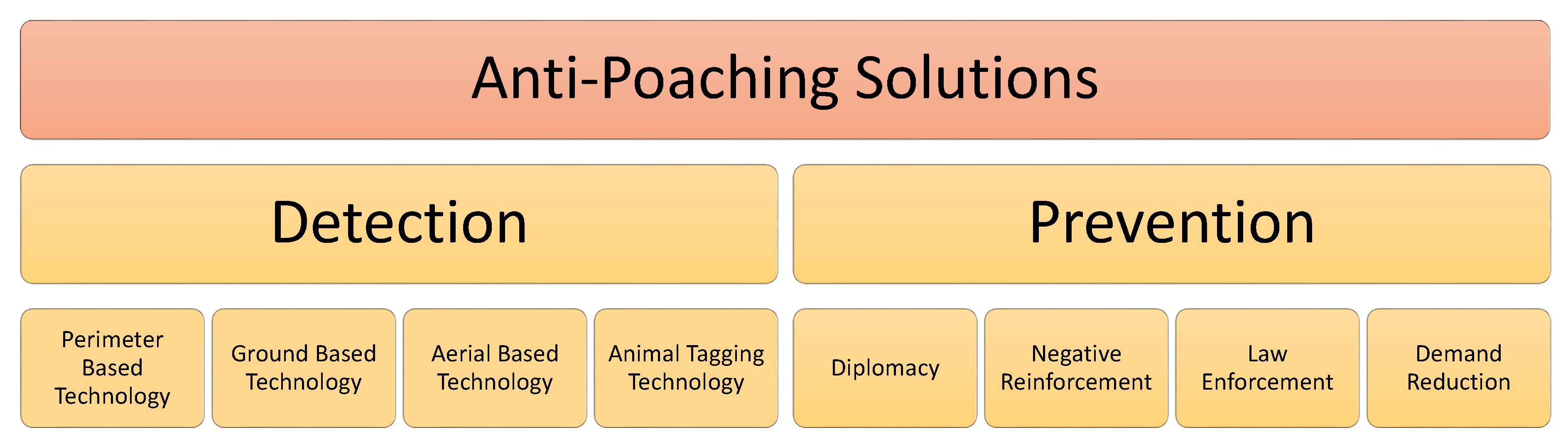
3. Existing Poaching Detection Technologies
3.1. Types of Sensor Technologies
3.1.1. Radar
3.1.2. Magnetic
3.1.3. Acoustic
3.1.4. Ultrasonic
3.1.5. Optical
3.1.6. Infrared and Thermal
3.1.7. Radio Frequency
3.1.8. Motion
3.1.9. Seismic
3.1.10. Chemical
3.1.11. Animal Sentinels
3.2. Perimeter Based Technologies
3.3. Ground Based Technologies
3.4. Aerial Based Technologies
3.5. Animal Tagging Technologies
3.6. Research Challenges and Future Directions
3.6.1. Sensitivity and Reliability
3.6.2. Sensor Development
3.6.3. Logistics
3.6.4. Legal and Politics
4. Prevention of Poaching
4.1. Diplomacy
4.2. Law Enforcement
4.3. Negative Reinforcement
4.4. Substitution
4.5. Demand Reduction
5. Conclusions
Author Contributions
Acknowledgments
Conflicts of Interest
References
- Emslie, R.H. African Rhinoceroses—Latest trends in rhino numbers and poaching. Afr. Indaba e-Newsl. 2013, 51, 11–12. [Google Scholar]
- Rhino, S.T. Poaching: The Statistics. 2015. Available online: https://www.savetherhino.org/rhino_info/poaching_statistics (accessed on 14 June 2017).
- Rhino, A.; Groups, S.; Milliken, T.; Emslie, R.H.; Talukdar, B. African and Asian Rhinoceroses—Status, conservation and trade. Africa 2009, 230, 1–18. [Google Scholar]
- Chase, M.J.; Schlossberg, S.; Griffin, C.R.; Bouché, P.J.; Djene, S.W.; Elkan, P.W.; Ferreira, S.; Grossman, F.; Kohi, E.M.; Landen, K.; et al. Continent-wide survey reveals massive decline in African savannah elephants. PeerJ 2016, 4, e2354. [Google Scholar] [CrossRef] [PubMed]
- World Wildlife Fund. Fighting Illicit Wildlife Trafficking; WWF Report; World Wildlife Fund: Gland, Switzerland, 2012; p. 32. [Google Scholar]
- WildAid. 2017. Available online: http://wildaid.org/ (accessed on 14 June 2017).
- Milliken, B.T.; Shaw, J.; Emslie, R.H.; Taylor, R.D.; Turton, C. The South Africa—Vietnam rhino horn trade nexus. Traffic 2012, 134–136. [Google Scholar]
- Lunstrum, E. Green militarization: Anti-poaching efforts and the spatial contours of Kruger national park. Ann. Assoc. Am. Geogr. 2014, 104, 816–832. [Google Scholar] [CrossRef]
- Wildlife Campus. The Who, What & Why of Poaching. 2016. Available online: http://www.wildlifecampus.com/Courses/Anti-Poaching/IntroductiontoAnti-Poaching/WhatWhoandWhy/1923.pdf (accessed on 14 June 2017).
- Rhino, S.T. Poaching for Rhino Horn. 2015. Available online: https://www.savetherhino.org/rhino_info/threats_to_rhino/poaching_for_rhino_horn (accessed on 14 June 2017).
- Modise, A. Rules Tightened on Rhino Trophy Hunting, 2012. Available online: http://www.politicsweb.co.za/documents/rules-tightened-on-rhino-trophy-hunting--doea (accessed on 26 June 2017).
- Montesh, M. Rhino Poaching: A New Form of Organised Crime; Technical Report; School of Criminal Justice: Pretoria, South Africa, 2012. [Google Scholar]
- Andrusiak, L.; Walters, E.L.; Terry, E.; Simpson, K. Wildlife Radio-Telemetry Standards for Components of British Columbia’s Biodiversity No. 5; Resources Inventory Committe: Victoria, BC, Canada, 1998.
- Brooks, C.; Bonyongo, C.; Harris, S. Effects of global positioning system collar weight on zebra behavior and location error. J. Wildl. Manag. 2008, 72, 527–534. [Google Scholar] [CrossRef]
- Sikes, R.S.; Gannon, W.L. Guidelines of the American society of mammalogists for the use of wild mammals in research. J. Mammal. 2011, 92, 235–253. [Google Scholar] [CrossRef]
- Inomata, K.; Hirai, T. Microwave Back-Projection Radar for Wide-area Surveillance System. In Proceedings of the First European Radar Conference (EURAD), Amsterdam, The Netherlands, 11–15 October 2004; pp. 89–92. [Google Scholar]
- Neumann, C.; Weiss, G.; Wahlen, A.; Brehm, T. Ground surveillance with mmw radar for border control and camp protection applications. In Proceedings of the 37th European Microwave Conference (EUMC), Munich, Germany, 8–12 October 2007; pp. 700–703. [Google Scholar]
- Caris, M.; Johannes, W.; Stanko, S.; Pohl, N. Millimeter wave radar for perimeter surveillance and detection of MAVs (Micro Aerial Vehicles). In Proceedings of the 16th International Radar Symposium (IRS), Dresden, Germany, 24–26 June 2015; pp. 284–287. [Google Scholar]
- Essen, H.; Johannes, W.; Stanko, S. Perimeter surveillance using a miniaturized millimetre-wave radar. SPIE Secur. Def. 2012, 8544, 85440K. [Google Scholar]
- Harman, K.; Hodgins, B. Next generation of guidar technology. In Proceedings of the 38th Annual 2004 International Carnahan Conference on Security Technology, Albuquerque, NM, USA, 11–14 October 2004; pp. 169–176. [Google Scholar]
- Arora, A.; Dutta, P.; Bapat, S.; Kulathumani, V.; Zhang, H.; Naik, V.; Mittal, V.; Cao, H.; Demirbas, M.; Gouda, M.; et al. A line in the sand: A wireless sensor network for target detection, classification, and tracking. Comput. Netw. 2004, 46, 605–634. [Google Scholar] [CrossRef]
- The Samraksh Company. 2015. Available online: https://samraksh.com (accessed on 7 December 2015).
- He, J.; Roy, D.; Mcgrath, M.; Arora, A. Demo abstract: Mote-scale human-animal classification via micropower radar. In Proceedings of the 12th ACM Conference on Embedded Network Sensor Systems (SenSys), Memphis, TN, USA, 3–6 November 2014; pp. 328–329. [Google Scholar]
- Butler, W.; Poitevin, P.; Bjomholt, J. Benefits of wide area intrusion detection systems using FMCW radar. In Proceedings of the 41st Annual IEEE International Carnahan Conference on Security Technology, Ottawa, ON, Canada, 8–11 October 2007; Volume 6943, pp. 176–182. [Google Scholar]
- Tuinstra, J.D. Perimeter Security and Intruder Detection Using Gravity Gradiometry: A Feasability Study; Accession Number ADA540035; Defense Technical Information Center: Fort Belvoir, VA, USA, 2011.
- Kim, Y.; Kang, J.; Kim, D.; Kim, E.; Chong, P.K.; Seo, S. Design of a fence surveillance system based on wireless sensor networks. In Proceedings of the 2nd International Conference on Autonomic Computing and Communication Systems, Turin, Italy, 23–25 September 2008; pp. 1–7. [Google Scholar]
- He, T.; Krishnamurthy, S.; Stankovic, J.A.; Abdelzaher, T.; Luo, L.; Stoleru, R.; Yan, T.; Gu, L.; Hui, J.; Krogh, B. Energy-efficient surveillance system using wireless sensor networks. In Proceedings of the 2nd International Conference on Mobile Systems, Applications, and Services (MobiSys), Boston, MA, USA, 7–9 June 2004; pp. 270–283. [Google Scholar]
- He, T.; Krishnamurthy, S.; Luo, L.; Yan, T.; Gu, L.; Stoleru, R.; Zhou, G.; Cao, Q.; Vicaire, P.; Stankovic, J.A.; et al. VigilNet: An integrated sensor network system for energy-efficient surveillance. ACM Trans. Sen. Netw. 2006, 2, 1–38. [Google Scholar] [CrossRef]
- Preetam, S.; Subhdeep, K.; Vrijendra, S.; Maringanti, R. Algorithm for gunshot detection using mel-frequency cepstrum coefficients (MFCC). In Proceedings of Ninth International Conference on Wireless Communication and Sensor Networks; Springer: New Delhi, India, 2014; pp. 155–166. [Google Scholar]
- Zeppelzauer, M.; Stoeger, A.S. Establishing the fundamentals for an elephant early warning and monitoring system. BMC Res. Notes 2015, 8, 409. [Google Scholar] [CrossRef] [PubMed]
- Langbauer, W.R.; Payne, K.B.; Charif, R.A.; Rapaport, L.; Osborn, F. African elephants respond to distant playbacks of low-frequency conspecific calls. J. Exp. Biol. 1991, 157, 35–46. [Google Scholar]
- Petersen, J.K. Understanding Technologies Surveillance Spy Devices, Their Origins & Applications; CRC Press: Boca Raton, FL, USA, 2002; ISBN 978-0849322983. [Google Scholar]
- Aseeri, M.; Ahmed, M.R.; Ghamdind, A.A.; Almorqi, S. Peer trust based trust and reputation model for wireless sensor networks to protect border. Int. J. Comput. Sci. Netw. Secur. 2014, 14, 14–21. [Google Scholar]
- Piper, S. New Invention Could Drive Poaching Towards Extinction. 2015. Available online: http://www.hsi.org/world/united_kingdom/news/releases/2015/07/protect-rapid-072015.html (accessed on 15 October 2015).
- Mishra, A.; Sudan, K.; Soliman, H. Detecting border intrusion using wireless sensor network and artificial neural network. In Proceedings of the 6th IEEE International Conference on Distributed Computing in Sensor Systems Workshops (DCOSSW), Santa Barbara, CA, USA, 21–23 June 2010; pp. 1–6. [Google Scholar]
- Mulero-Pázmány, M.; Stolper, R.; van Essen, L.D.; Negro, J.J.; Sassen, T. Remotely piloted aircraft systems as a rhinoceros anti-poaching tool in Africa. PLoS ONE 2014, 9, e83873. [Google Scholar] [CrossRef] [PubMed]
- Zhang, J.; Chen, C. A wildlife monitoring system based on wireless image sensor networks. Sens. Transducers 2014, 180, 104–109. [Google Scholar]
- Shepherd, A. Air Shepherd Initiative. 2015. Available online: http://airshepherd.org/ (accessed on 26 November 2015).
- Sun, Z.; Wang, P.; Vuran, M.C.; Al-Rodhaan, M.A.; Al-Dhelaan, A.M.; Akyildiz, I.F. BorderSense: Border patrol through advanced wireless sensor networks. Ad Hoc Netw. 2011, 9, 468–477. [Google Scholar] [CrossRef]
- Rothenpieler, P.; Pfisterer, D.; Fischer, S.; Dudek, D.; Haas, C.; Kuntz, A.; Zitterbart, M.; Kruger, D. FleGSens—Secure area monitoring using wireless sensor networks. In Proceedings of the 4th Safety and Security Systems in Europe, Micro Materials Center Berlin at Fraunhofer Institute IZM and Fraunhofer ENAS, Potsdam, Germany, 4–5 June 2009; pp. 1629–1640. [Google Scholar]
- Cambron, M.E.; Brode, C.; Butler, P.; Olszewkski, G.; Green, B. Poacher detection at fence crossing. In Proceedings of the SoutheastCon 2015, Fort Lauderdale, FL, USA, 9–12 April 2015; pp. 1–2. [Google Scholar]
- Harman, R.K.; Mackay, N. GUIDAR: An intrusion detection system for perimeter protection. In Proceedings of the 1976 Carnahan Conference on Crime Countermeasures, Lexington, KY, USA, 5–7 May 1976. [Google Scholar]
- Poirier, J.L. Leaky coaxial cable resource protection sensor performance Analysis. IEEE Trans. Aerosp. Electron. Syst. 1982, AES-18, 275–285. [Google Scholar] [CrossRef]
- Inomata, K.; Tsujita, W.; Hirai, T. Pattern analysis for human intrusion detection with leaky coaxial cables. In Proceedings of the 2014 IEEE MTT-S International Microwave Symposium (IMS2014), Tampa, FL, USA, 1–6 June 2014; pp. 1–4. [Google Scholar]
- Inomata, K.; Hirai, T.; Sumi, K.; Tanaka, K. Wide-area surveillance sensor with leaky coaxial cables. In Proceedings of the SICE-ICASE International Joint Conference, Busan, South Korea, 18–21 October 2006; pp. 959–963. [Google Scholar]
- Senstar. Specification for OmniTrax Ranging Buried Ported Coaxial Cable Outdoor Intrusion Detection System; Technical Report; Stellar; Senstar: Ottawa, ON, Canada, 2011. [Google Scholar]
- Wittenburg, G.; Terfloth, K.; Villafuerte, F.L.; Naumowicz, T.; Ritter, H.; Schiller, J. Fence monitoring-experimental evaluation of a use case for wireless sensor networks. In Proceedings of the 4th European Conference on Wireless Sensor Networks (EWSN’07), Delft, The Netherlands, 29-31 January 2007; pp. 163–178. [Google Scholar]
- Yousefi, A.; Member, S.; Dibazar, A.; Berger, T. Intelligent fence intrusion detection system: Detection of intentional fence breaching and recognition of fence climbing. In Proceedings of the 2008 IEEE Conference on Technologies for Homeland Security, Waltham, MA, USA, 12–13 May 2008; pp. 620–625. [Google Scholar]
- Stellar. Intelli-FLEX Microphonic Cable Fence Disturbance Sensor; Technical Report; Senstar: Ottawa, ON, Canada, 2015. [Google Scholar]
- Maki, M. Fiber Optic Fence Sensor Developments. In Proceedings of the International Carnahan Conference on Security Technology, Ottawa, ON, Canada, 8–11 October 2007; pp. 163–168. [Google Scholar]
- Maki, M.; Newcomb, I.; Robotham, J. Cost effective security system integration. In Proceedings of the IEEE 32nd Annual 1998 International Carnahan Conference on Security Technology, Alexandria, VA, USA, 12–14 October 1998; pp. 140–146. [Google Scholar]
- Southwest Microwave. MicroPoint Cable a New Fence Sensor Technology; Technical Report; Southwest Microwave: Tempe, AZ, USA, 2015. [Google Scholar]
- Backx, A.; Harman, R. Intrepid MicroPoint system—European fence experience. In Proceedings of the 36th Annual International Carnahan Conference onSecurity Technology, Atlantic City, NJ, USA, 20–24 October 2002; pp. 80–86. [Google Scholar]
- Zhou, X.; Slone, J.D.; Rokas, A.; Berger, S.L.; Liebig, J.; Ray, A.; Reinberg, D.; Zwiebel, L.J. Phylogenetic and transcriptomic analysis of chemosensory receptors in a pair of divergent ant species reveals sex-specific signatures of odor coding. PLoS Genet. 2012, 8, e1002930. [Google Scholar] [CrossRef] [PubMed]
- Smith, D. South African Game Reserve Poisons Rhino’s Horns to Prevent Poaching. 2015. Available online: http://www.theguardian.com/environment/2013/apr/04/rhino-horns-poisoned-poachers-protect (accessed on 15 October 2015).
- Anderson, B.; Jooste, J. Wildlife poaching: Africa’s surging trafficking threat. Afr. Secur. Brief 2014, May, 1–8. [Google Scholar]
- Mukwazvure, A.; Magadza, T.B.H.T. A survey on anti-poaching strategies. Int. J. Sci. Res. 2014, 3, 2012–2014. [Google Scholar]
- Sahin, Y.G. Animals as mobile biological sensors for forest fire detection. Sensors 2007, 7, 3084–3099. [Google Scholar] [CrossRef] [PubMed]
- Banzi, J.F. A sensor based anti-poaching system in Tanzania. Int. J. Sci. Res. Publ. 2014, 4, 1–7. [Google Scholar]
- Recio, M.R.; Mathieu, R.; Denys, P.; Sirguey, P.; Seddon, P.J. Lightweight GPS-tags, one giant leap for wildlife tracking? An assessment approach. PLoS ONE 2011, 6, e28225. [Google Scholar] [CrossRef] [PubMed]
- Succi, G.P. Problems in seismic detection and tracking. Proc. SPIE 2000, 4040, 165–173. [Google Scholar]
- Mishra, R.G. Distributed fibre optic virtual fencing system. Ed. Wired Wirel. Netw. Adv. Appl. 2013, 3, 1–15. [Google Scholar]
- Snider, W.; Madsen, C.; Atkins, R.; Simcik, J.S., III. Border Security Utilizing a Distributed Fiber Optic Intrusion Sensor; CiteSeerX: Princeton, NJ, USA, 2008. [Google Scholar]
- Dziengel, N.; Seiffert, M.; Ziegert, M.; Adler, S.; Pfeiffer, S.; Schiller, J. Deployment and evaluation of a fully applicable distributed event detection system in wireless sensor networks. Ad Hoc Netw. 2015, 1–23. [Google Scholar] [CrossRef]
- Kim, D.; López, T.S.; Yoo, S.; Sung, J.; Kim, J.; Kim, Y.; Doh, Y. ANTS: An evolvable network of tiny sensors. In Proceedings of the Embedded and Ubiquitous Computing (EUC 2005); Springer: Berlin, Germany, 2005; pp. 142–151. [Google Scholar]
- Souza, É.L.; Pazzi, R.W.; Nakamura, E.F. A prediction-based clustering algorithm for tracking targets in quantized areas for wireless sensor networks. Wirel. Netw. 2015, 21, 2263–2278. [Google Scholar] [CrossRef]
- Zhang, W.; Jiang, T. Intrusion detection and classification in forest area using inter-sensor communication signals and SVM. In Proceedings of the International Conference on Communication Problem-Solving (ICCP), Beijing, China, 5–7 December 2014; pp. 401–404. [Google Scholar]
- Jiang, T.; You, M. New method for target identification in a foliage environment using selected bispectra and chaos particle swarm optimisation-based support vector machine. IET Signal Process. 2014, 8, 76–84. [Google Scholar]
- Wildlife Conservation UAV Challenge. 2015. Available online: http://www.wcuavc.com/ (accessed on 10 December 2015).
- Park, N.; Serra, E.; Subrahmanian, V. Saving rhinos with predictive analytics. IEEE Intell. Syst. 2015, 30, 86–88. [Google Scholar]
- Park, N.; Serra, E.; Snitch, T.; Subrahmanian, V.S. APE: A data-driven, behavioral model-based anti-poaching engine. IEEE Trans. Comput. Soc. Syst. 2016, 2, 15–37. [Google Scholar]
- O‘donoghue, P.; Rutz, C. Real-time anti-poaching tags could help prevent imminent species extinctions. J. Appl. Ecol. 2016, 53, 5–10. [Google Scholar] [CrossRef] [PubMed] [Green Version]
- Intel. Anti-Poaching Technology: Wearables Are Helping Save Rhinos, 2015. Available online: http://blogs.intel.com/csr/2014/08/rhino/ (accessed on 14 December 2015).
- Jones, B.; Hounsham, T.; Brown, C.; Tarr, S. The development of a methodology for the evaluation of wide area detection systems (WADS). In Proceedings of the IEEE International Carnahan Conference on Security Technology (ICCST), Barcelona, Spain, 18–21 October 2011; pp. 1–5. [Google Scholar]
- Schiller, J.; Liers, A.; Ritter, H. ScatterWeb: A wireless sensornet platform for research and teaching. Comput. Commun. 2005, 28, 1545–1551. [Google Scholar] [CrossRef]
- Fowler, E.P.; Eng, C. Microphony of coaxial cables. Proc. Inst. Electr. Eng. 1976, 123, 1043–1046. [Google Scholar] [CrossRef]
- Leach, G.; Horner, M. Sensitivity variations in linear microphonic cables. In Proceedings of the IEEE 31st Annual 1997 International Carnahan Conference on Security Technology, Canberra, ACT, Australia, 15–17 October 1997; pp. 25–30. [Google Scholar]
- Mahmoud, S.S.; Katsifolis, J. Performance investigation of real-time fiber optic perimeter intrusion detection systems using event classification. In Proceedings of the 44th Annual 2010 IEEE International Carnahan Conference on Security Technology, San Jose, CA, USA, 5–8 October 2010; pp. 387–393. [Google Scholar]
- Feraday, S.; Tarr, S. Standardised procedures for evaluating PIDS. In Proceedings of the 2008 42nd Annual IEEE International Carnahan Conference on Security Technology, Prague, Czech, 13–16 October 2008; pp. 98–101. [Google Scholar]
- Vries, J.D. A low cost fence impact classification system with Neural Networks. In Proceedings of the 7th Africon Conference in Africa, Gaborone, Botswana, 15–17 September 2004. [Google Scholar]
- Logan, B. Mel frequency cepstral coefficients for music modeling. ISMIR 2000, 270, 1–11. [Google Scholar]
- Jolliffe, I. Principal Component Analysis; Springer: New York, NY, USA, 2002; pp. 115–128. [Google Scholar]
- Cortes, C.; Vapnik, V. Support-vector networks. Mach. Learn. 1995, 20, 273–297. [Google Scholar] [CrossRef]
- Africa Wildlife Tracking. GPS Collar. 2015. Available online: http://www.awt.co.za/ (accessed on 15 October 2015).
- Rawat, P.; Singh, K.D.; Chaouchi, H.; Bonnin, J.M. Wireless sensor networks: A survey on recent developments and potential synergies. J. Supercomput. 2014, 68, 1–48. [Google Scholar] [CrossRef]
- Xiao, L.; Boyd, S. A scheme for robust distributed sensor fusion based on average consensus. In Proceedings of the Fourth International Symposium on Information Processing in Sensor Networks, Boise, ID, USA, 15 April 2005; pp. 63–70. [Google Scholar]
- Le, D.; Nguyen, T.; Scholten, H.; Havinga, P. Symbiotic sensing for energy-intensive tasks in large-scale mobile sensing applications. Sensors 2017, 17, 2763. [Google Scholar] [CrossRef] [PubMed]
- Saving The Wild. South Africa Rejects Rhino Horn Legalization. 2016. Available online: http://www.savingthewild.com/2016/04/south-africa-rejects-rhino-horn-legalization/ (accessed on 20 May 2016).
- CITES. 2015. Available online: https://www.cites.org/ (accessed on 20 November 2015).
- TRAFFIC. 2015. Available online: https://www.traffic.org/ (accessed on 20 November 2015).
- Wildlife Crime Initiative. 2015. Available online: http://goo.gl/5EMlQU (accessed on 3 December 2015).
- Haas, T.C.; Ferreira, S.M. Optimal patrol routes: Interdicting and pursuing rhino poachers. Police Pract. Res. 2018, 19, 61–82. [Google Scholar] [CrossRef]
- Fang, F.; Nguyen, T.H.; Pickles, R.; Lam, W.Y.; Clements, G.R.; An, B.; Singh, A.; Schwedock, B.C.; Tambe, M.; Lemieux, A. PAWS—A deployed game-theoretic application to combat poaching. AI Mag. 2017, 38, 23. [Google Scholar] [CrossRef]
- Fang, F.; Nguyen, T.H.; Sinha, A.; Gholami, S.; Plumptre, A.; Joppa, L.; Tambe, M.; Driciru, M.; Wanyama, F.; Rwetsiba, A.; et al. Predicting poaching for wildlife protection. IBM J. Res. Dev. 2017, 61, 3:1–3:12. [Google Scholar] [CrossRef]
- Kar, D.; Ford, B.; Gholami, S.; Fang, F.; Plumptre, A.; Tambe, M.; Driciru, M.; Wanyama, F.; Rwetsiba, A.; California, S.; et al. Cloudy with a chance of poaching: Adversary behavior modeling and forecasting with real-world poaching data. In Proceedings of the 16th Conference on Autonomous Agents and MultiAgent Systems, Sao Paulo, Brazil, 8–12 May 2017; pp. 159–167. [Google Scholar]
- Sintov, N.; Seyranian, V.; Lyet, A. Fostering adoption of conservation technologies: A case study with wildlife law enforcement rangers. Oryx 2018, 1–5. [Google Scholar] [CrossRef]
- Ferreira, S.; Hofmeyr, M.; Pienaar, D.; Cooper, D. Chemical horn infusions: A poaching deterrent or an unnecessary deception? Pachyderm 2014, 55, 54–61. [Google Scholar]
- Rhino Rescue Project. Rhino Horn Infusion in Action. 2016. Available online: http://rhinorescueproject.org/infusion-in-action/ (accessed on 18 August 2016).
- Save The Rhino. De-horning. 2015. Available online: https://www.savetherhino.org/rhino_info/issues_ for_debate/de-horning (accessed on 26 June 2017).
- Milner-Gulland, E.J.; Beddington, J.R.; Leader-Williams, N. Dehorning African rhinos: A model of optimal frequency and profitability. Proc. R. Soc. B Biol. Sci. 1992, 249, 83–87. [Google Scholar] [CrossRef]
- WildAid. WildAid Calls for Ban on Synthetic Rhino Horn Exports, 2016. Available online: http://wildaid.org/news/wildaid-calls-ban-synthetic-rhino-horn-exports (accessed on 20 May 2016).
- IEEE Spectrum. Biotech and 3-D Printing Could Make Rhino Poaching Pointless. 2015. Available online: http://goo.gl/NDaEU0 (accessed on 7 December 2015).


| Techniques | Details |
|---|---|
| Energy Efficiency | Energy saving capability of an anti-poaching technology is still an open issue |
| Deployment issues | Running power consumption, stealthiness to the environment, maintainability and its easy of deployment are categorized into deployment issues |
| Robustness | An Anti-Poaching System (APS) should be robust to at least common technical faults |
| Scalability | The capability of an APS to seamless integrate additional number of devices with the system |
| Coverage | The ability of an APS to provide full surveillance coverage of a certain protective region |
| Ethical and legal | The ability of an APS to deal with moral principles and to be abide by the regulations and laws, especially wildlife conservation laws |
| Sensor Technology | Advantages | Disadvantages | Ref. |
|---|---|---|---|
| Radar | Longer range; does not require direct line of sight; estimate velocity of target; tracking of target | No stealth due to active nature; sensitive to interference, such as precipitation and foliage; intruders can reduce radar signature; expensive | [16,17,18,19,20,21,22,23,24,25] |
| Magnetic | Detection of metal objects such as cars or weapons | Very short range | [21,26,27,28] |
| Acoustic | Long range; economical | Different acoustic characteristics found in different environments; large vocal repertoire | [26,29,30,31] |
| Ultrasonic | Long range; economical | Ultrasonic sound is easily absorbed by clothing and foliage | [32] |
| Optical | Long range; identification of targets | Require line of sight; expensive | [26,33,34,35,36,37,38,39] |
| Infrared and Thermal | Possibility to detect target at night | Difficult to detect target in hot environments | [36,37,40,41] |
| Radio Frequency | Does not require line of sight; high level of stealth | Require (buried) cables along perimeter; limited volumetric range | [20,42,43,44,45,46] |
| Motion | Possibility to classify intrusion type on fences or structures; economical | Range limited to physical structure that sensors are attached to | [41,47,48,49,50,51,52,53] |
| Seismic | High level of stealth | Range and quality of seismic measurements is different for each environment (soil type) | [25,26,39] |
| Chemical | Can be used to mark targets for identification; tracking of poached items | Does not prevent animals from being killed; can be obtrusive to animals | [7,32,54,55,56,57] |
| Animal Sentinels | In theory very large volumetric range; high sensitivity | Many sensors needed; deployment difficulties such as power usage and collaring | [32,58,59,60] |
| Technique | Advantages | Disadvantages | Ref. |
|---|---|---|---|
| Perimeter Based Technologies | Fences are often already in place (sometimes electrified) and can be fortified with the surveyed approaches; some of the surveyed approaches are commercially available | Detect intrusion only along the perimeter of an area, not inside the area itself (linear detection zone). Poachers can enter through the main gate, e.g., disguised as tourist operators. | |
| Lasers combined with movement detection PIR sensors | Lasers can cover larger distances | No classification; triggered by plants and animals; large False Alarm Rate (FAR) | [41] |
| Sensor nodes with accelerometers attached to a fence | Classification of intrusion event, thus lower FAR | Many sensors needed; low stealth | [47,48] |
| Microphonic cables attached to fence | Classification and localization of intrusion | 200 m segments; a lot of infrastructure needed; low stealth | [49,50,51,52,53] |
| Optical fiber attached to fence | Classification and localization of intrusion; segments up to 1000 m; no power needed along segments; insensitive to electromagnetic inference; very sensitive; reliable | Expensive; low stealth. | [50] |
| Buried optical fiber to detect footsteps | High stealth; harder to destroy; segment ranges up to 10 km | Difficult to bury cables in wildlife areas; soil types vary; expensive | [62,63] |
| Networked sensors of various types (infrared, magnetic, camera) on and around a fence | Higher resilience; some works include distributed algorithms that aim to decrease FAR | Many sensors needed; large overhead | [26,27,28,33,39,40,64,65] |
| Ground Based Technologies | Can detect intruders on larger area; not limited to linear zone. | Any infrastructure placed inside a wildlife area is prone to be damaged by wildlife. | |
| Buried coaxial cable | High stealth. Field is wider than optical fiber approach. Commercially available. | Difficult to bury cables in wildlife areas; soil types vary; expensive; volumetric range is not very high. | [20,42,43,44,45] |
| Fixed sensor node placement with various sensors (RADAR, microphone, light intensity, magnetometers) | Improved animal tracking | Many sensors needed; deployment difficulties such as power usage and destruction of nodes | [21,23,35,66] |
| Recording animal sounds | Some animals can be heard 4 km away; thus larger range | More challenging approach because: necessary to understand animal sounds; different acoustic characteristics are found in different environments; difference in the vocal repertoire between different species | [30] |
| Gunshot detection | Gunshots can be heard from far away; thus larger range | High chance of animal being killed before poacher detection | [29] |
| Ultra Wide Band (UWB) WSN | Classification of intrusion event; thus lower FAR; higher stealth. Improved detection in forested areas. | Limited range; many sensors needed; deployment difficulties such as power usage and destruction of nodes | [67,68] |
| Aerial Based Technologies | Very agile and can cover large areas | Aerial based techniques are obtrusive to habitants and tourists; crashing drones can be a hazard to people and wildlife; can be vulnerable to shooting | |
| Drones with heat sensing and camera equipment | Works up to 180 m height, thus large range | Unable to detect people under foliage; high running costs | [36,37,69] |
| Using predictive analytics for automated air surveillance | Improved surveillance accuracy; less sensors needed | Unable to detect people under foliage; high running costs | [70,71] |
| Animal Tagging Technologies | Can potentially cover very large areas with high sensitivity | Many sensors needed; deployment difficulties such as power usage and collaring | |
| Attach various sensors (cameras, motion, GPS) to animals and classify anomalous behavior | Timely notification of anomalies | Difficult to classify anomalies | [58,59,60] |
| Monitor physiological status of rhino and implement camera + GPS in rhino horn | Timely notification of animal distress or death; possibility to identify poachers through photos taken from the horn | Still high chance of animal being killed; location data of rhinos is very valuable and can motivate corruption | [34,72] |
| Detect horn separation from body through RFID | Helps to notify rangers as soon as animal is poached and increases possibility of the poacher’s capture | Rhino will be killed; the RFID chips will grow out of the horn | [73] |
© 2018 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Kamminga, J.; Ayele, E.; Meratnia, N.; Havinga, P. Poaching Detection Technologies—A Survey. Sensors 2018, 18, 1474. https://doi.org/10.3390/s18051474
Kamminga J, Ayele E, Meratnia N, Havinga P. Poaching Detection Technologies—A Survey. Sensors. 2018; 18(5):1474. https://doi.org/10.3390/s18051474
Chicago/Turabian StyleKamminga, Jacob, Eyuel Ayele, Nirvana Meratnia, and Paul Havinga. 2018. "Poaching Detection Technologies—A Survey" Sensors 18, no. 5: 1474. https://doi.org/10.3390/s18051474
APA StyleKamminga, J., Ayele, E., Meratnia, N., & Havinga, P. (2018). Poaching Detection Technologies—A Survey. Sensors, 18(5), 1474. https://doi.org/10.3390/s18051474






