UAV IoT Framework Views and Challenges: Towards Protecting Drones as “Things”
Abstract
1. Introduction
- Overviews new UAV application domains enabled by IoT and 5G technologies.
- Analyzes the IoT sensor requirements for drones.
- Summarizes the privacy and security challenges of UAV applications.
- Overviews solutions for fleet management over aerial networking.
2. Overview on UAVs as Members of IoT
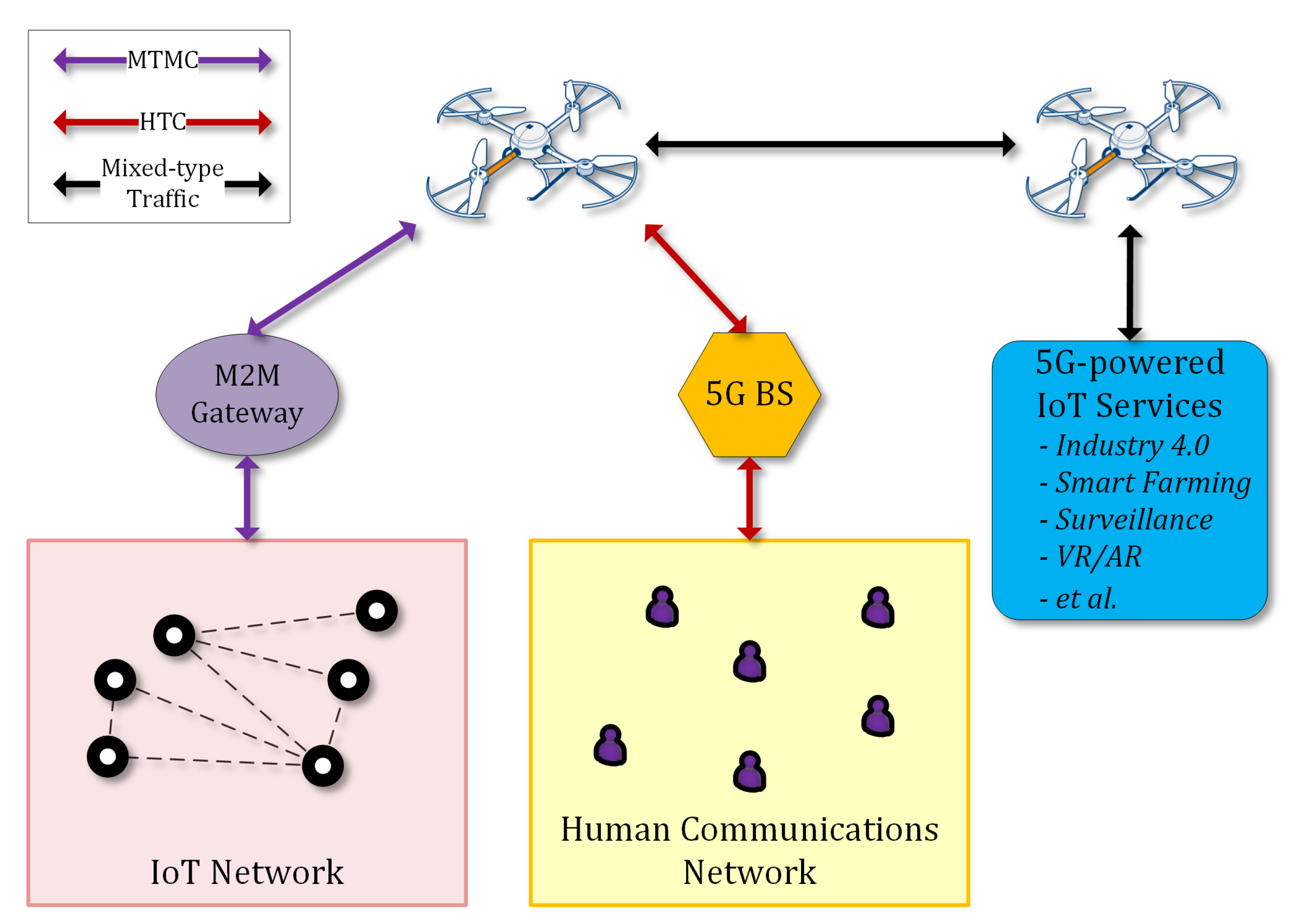
2.1. UAVs for Wireless Networks
2.1.1. Use Cases for Wireless Networking with UAVs
- UAV-carried flying base stations that complete heterogeneous 5G systems to enhance the coverage and capacity of existing wireless access technologies.
- UAV-based aerial networks that allow reliable, flexible, and fast wireless connections in public-safety scenarios.
- UAVs that support terrestrial networks for disseminating information and enhancing connectivity.
- UAVs as flying antennas that can be deployed on demand to enable mmWave communications, massive MIMO, and 3D network MIMO.
- UAVs that are used to provide energy-efficient and reliable IoT uplink connections.
- UAVs that form the backhaul of terrestrial networks to allow agile, reliable, cost-effective, and high-speed connectivity.
- UAVs able to cache popular content and efficiently serve mobile users by following their mobility patterns.
- UAVs that act as users of the wireless infrastructure for surveillance, remote-sensing, and virtual-reality cases, and package-delivery applications.
- UAVs that collect vast amounts of city data and/or enhance cellular network coverage in a smart-city scenario.
2.1.2. UAV Types and Classifications
2.1.3. Interference Management, Deployment, Path Planning, and Energy Consumption of UAVs in IoT Networks
2.2. UAV–IoT Frameworks
2.3. 5G and IoT Sensor Technologies for UAVs
2.3.1. Flight Control Sensor for Internal State Evaluation
2.3.2. Data-Acquisition Sensors
- For military use cases, UAVs may be equipped with high-end electro-optical sensors, and radars for airborne systems providing resolutions from submillimeters to a few centimetres.
- In surveillance and monitoring applications, we can have sensors at the lower end of the spectrum, such as low- or high- (e.g., 4K) resolution RGB (Red Green Blue) cameras, NDVI (Normalized Difference Vegetation Index) cameras for precision farming, LIDAR (Light Imaging, Detection, And Ranging) for simultaneous localization and mapping, and ultrasonic sensors for sense and obstacle-avoidance methods.
- We can also have hyperspectral depth and thermal sensors [32]. Applications that monitor environmental and weather conditions and are deployed in disaster relief and management require sensors to measure or detect liquefied petroleum gas (LPG), butane, methane (CH4), hydrogen, smoke, oxygen, temperature, and humidity.
2.3.3. Communication Systems
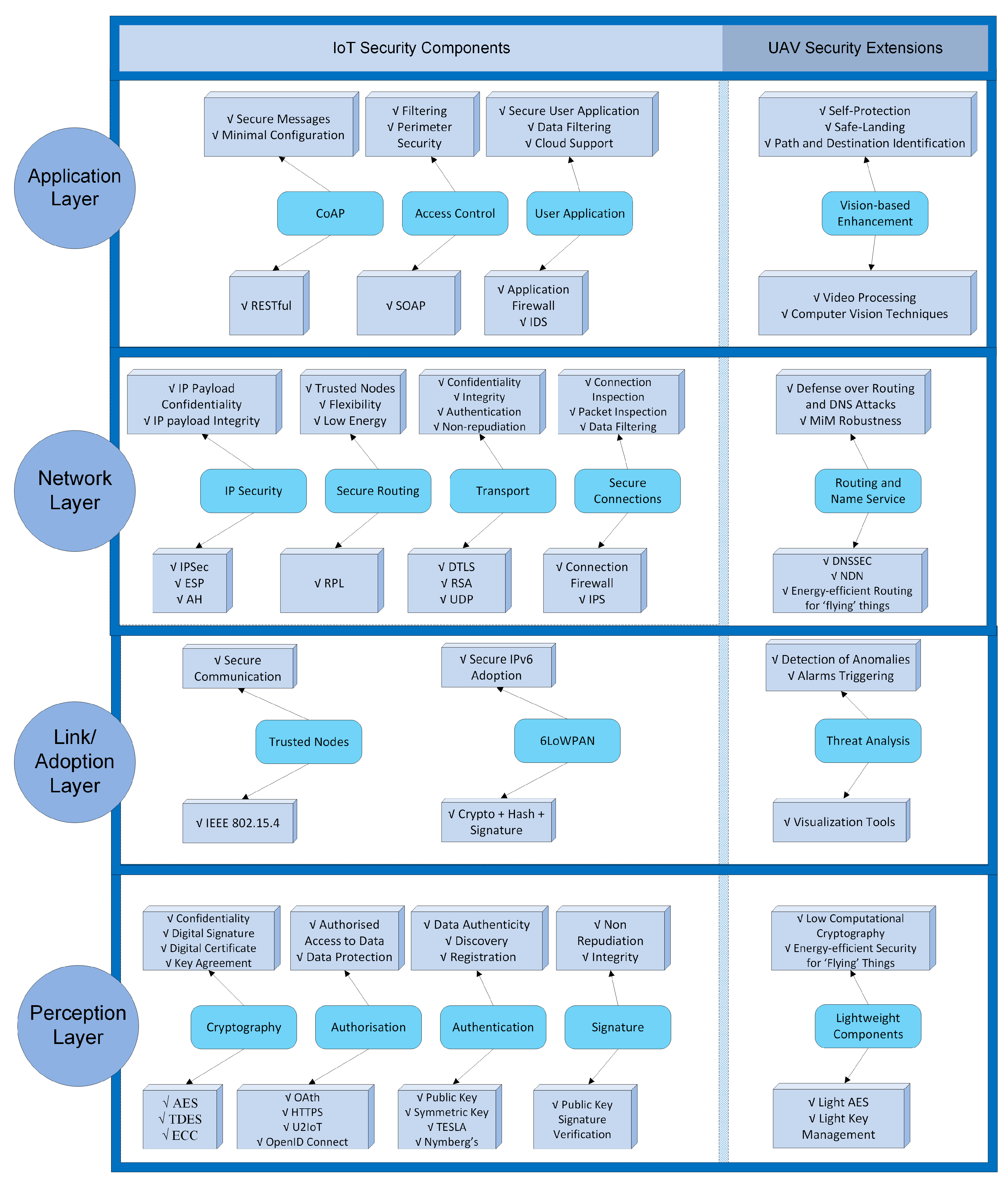
2.4. Security for UAVs over IoT
2.4.1. Security Component
2.4.2. Privacy Component
2.5. Protection for UAVs
2.5.1. Aerial Networking
- Proactive protocols [72] incorporate tables for each node that are periodically updated to store routing information for all other nodes of the topology. The main advantage of proactive protocols is that the tables of each node contain up-to-date information on routes due to continuous message exchanges; a fact, though, that causes bandwidth constraints.
- Reactive protocols [73] search and store routing paths between two nodes only when the need for communication between them arises. These types of protocols present the advantage of consuming low bandwidth, but there are many cases, specifically in large topologies, where route-path calculation is very slow, causing high latency.
- Geographic protocols [74] assume that the source node is aware of the geographic position of the receiving node and therefore sends the message directly without the need for searching for a route path. This protocol is very effective in terms of latency, bandwidth, and throughput, though localization information should be available. Such information can be very challenging to obtain in GPS-denied environments; however, this is quite unlikely to occur in the case of FANETs, while signal-based tracking methods (such as the one introduced in Reference [75]) can be additionally adopted.
2.5.2. Fleet Management
- In the centralized schema, a formation manager that can be one of the aerial vehicles of the fleet or a ground-based station [82], acts as a supervisor for all aerial vehicles and manages their topology. Centralized schemas present the advantage that important decisions are performed at a higher level, by centralized high-power computer systems, where humans can also interfere. On the other hand, the major disadvantage of this schema is that it requires frequent ground communications, which can be energy consuming and, in case of disruptions/failures, ground management can cause delays [83].
- In the decentralized schema [4], each aerial vehicle has a certain freedom in decision making, while the whole formation must be capable of reconfiguring, making decisions, and achieving mission goals. This schema is energy-efficient and presents reduced reaction times, though it may produce conflicting decisions, jeopardizing the fleet formation and, in cases of critical formation updates, it may require ground-control assistance [83].
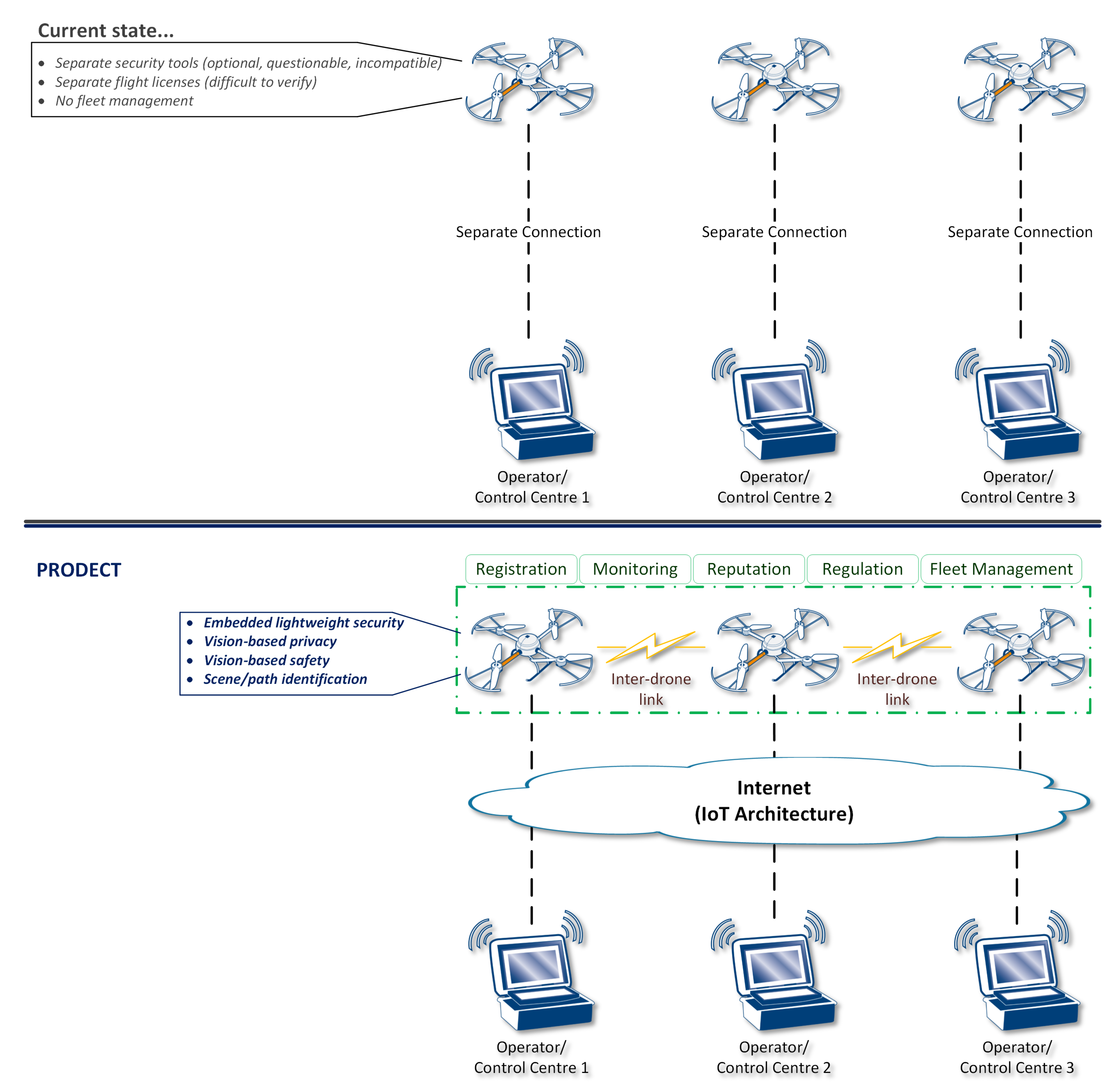
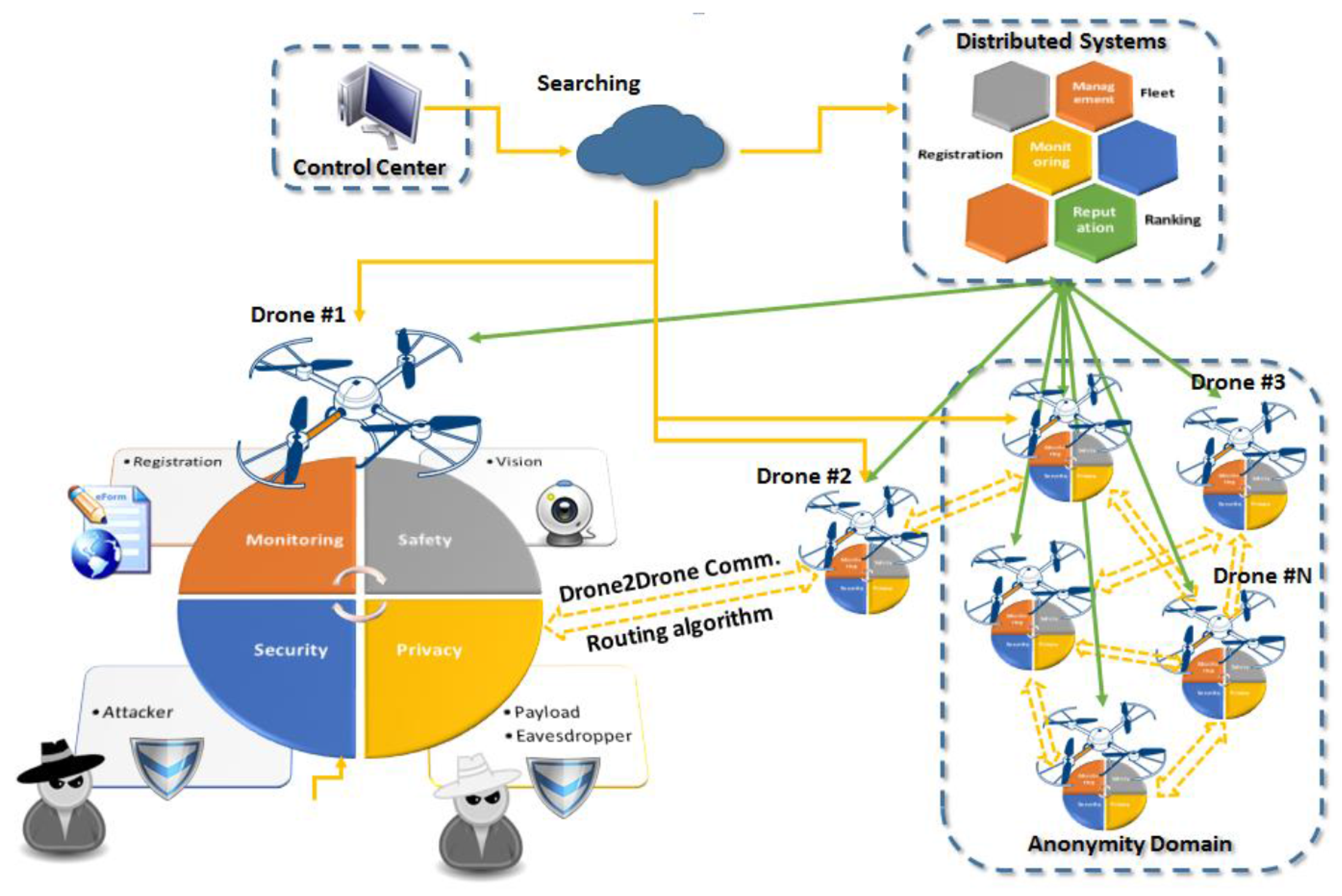
3. Proposed Framework and Methodology
3.1. Overall Concept and Methodology
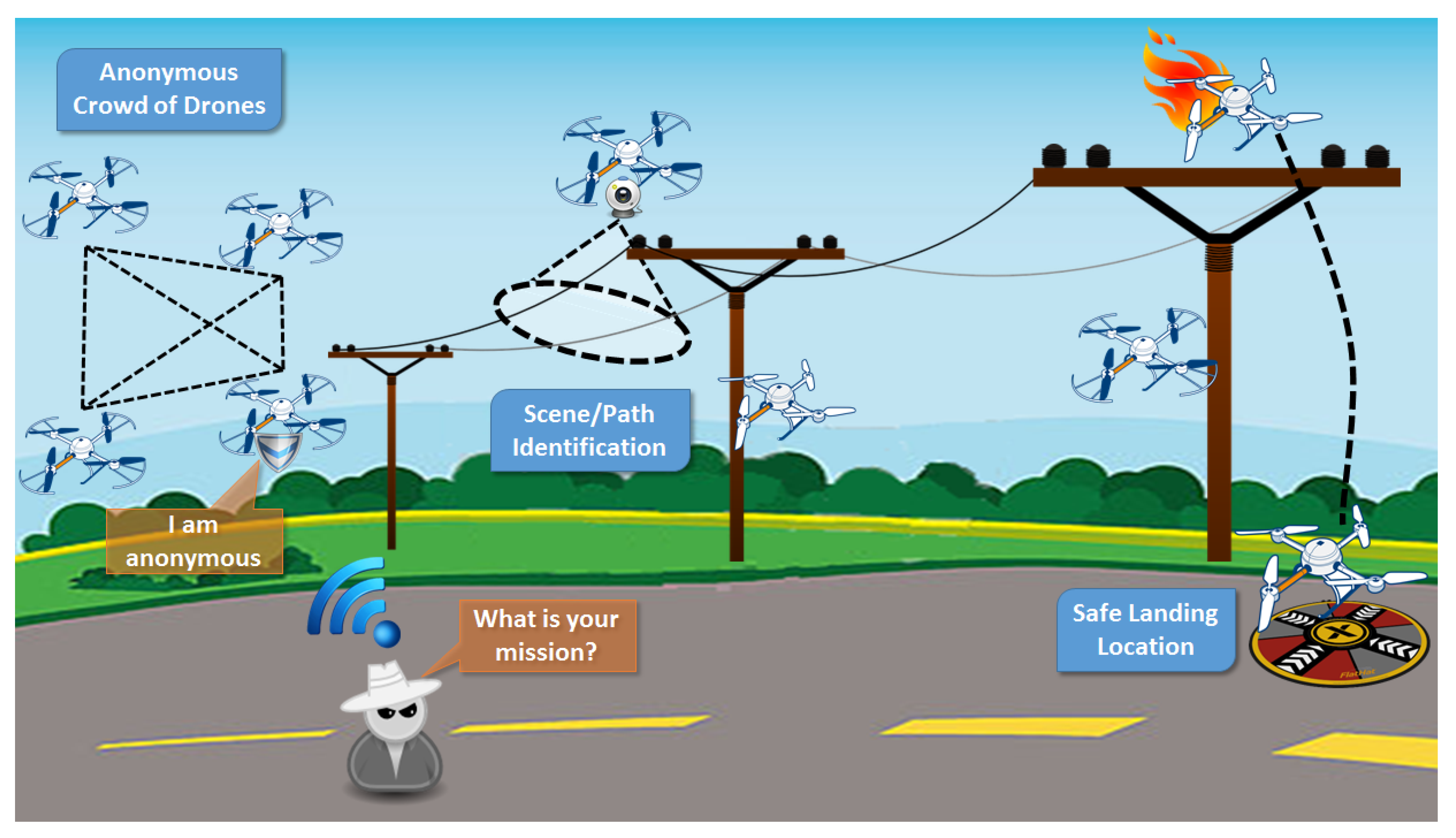
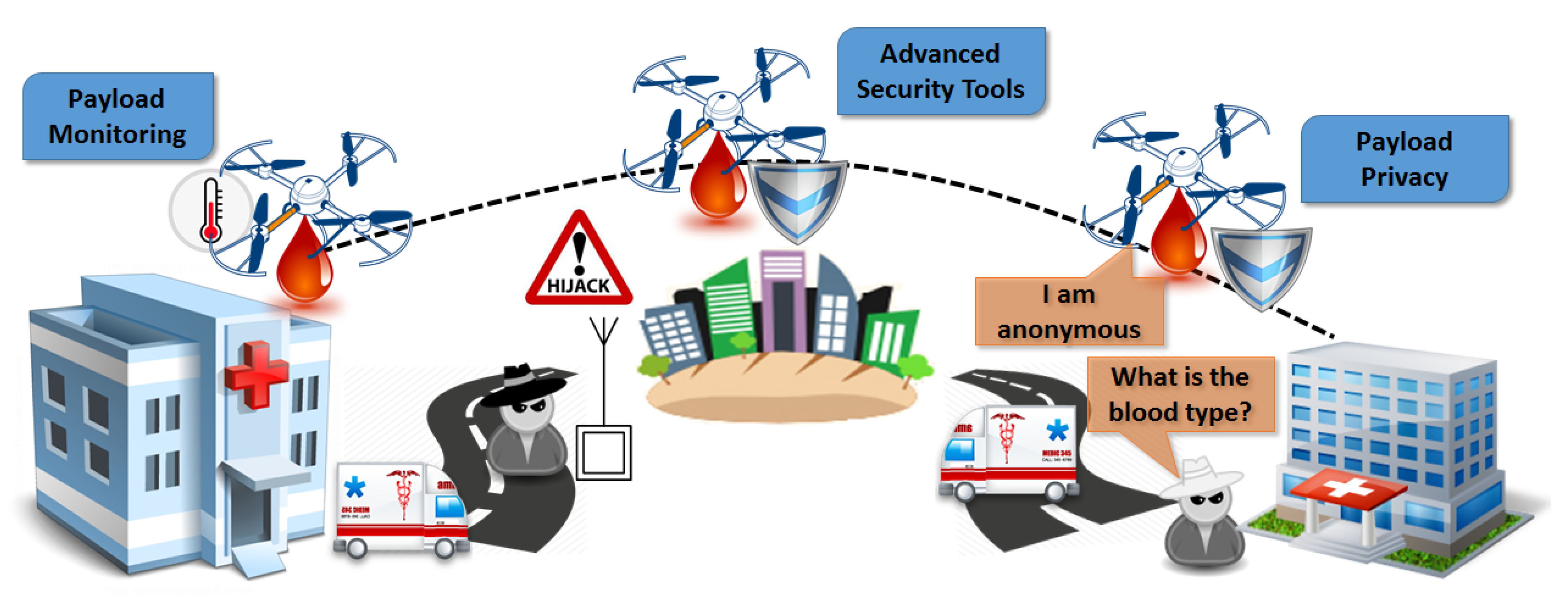
- At device level, the proposed framework enhances drones with embedded lightweight security, privacy, and safety based on cutting-edge vision-based techniques, which also enable advanced scene/path identification.
- At network level, drones become part of the IoT architecture and they are accessed/controlled through it. Furthermore, agile communications among drones are enabled, providing self-organizing capabilities that set the basis for innovative features, namely, device registration, flight dynamic monitoring, trust establishment through a distributive reputation point system, enforcement and verification of flight-plan regulations, and extensive fleet management via advanced interoperability.
3.1.1. Lightweight Security Toolbox in “Flying” Things
3.1.2. Vision-Based Novel Solutions as Security Enhancement
3.1.3. Privacy Prevention and Anonymity in “Flying” Things
3.2. Proposed UAV IoT Architecture
3.3. Potential Security-Sensitive UAV IoT Applications
3.3.1. Power-Line Monitoring
3.3.2. Human Blood Delivery
4. Requirements, Suggestions, and Evaluation
5. Conclusions
Author Contributions
Funding
Conflicts of Interest
References
- Motlagh, N.H.; Bagaa, M.; Taleb, T. UAV-based IoT platform: A crowd surveillance use case. IEEE Commun. Mag. 2017, 55, 128–134. [Google Scholar] [CrossRef]
- Kersnovski, T.; Gonzalez, F.; Morton, K. A UAV system for autonomous target detection and gas sensing. In Proceedings of the Aerospace Conference, Big Sky, MT, USA, 4–11 March 2017; pp. 1–12. [Google Scholar]
- Kumbhar, A.; Guvenc, I.; Singh, S.; Tuncer, A. Exploiting LTE-Advanced HetNets and FeICIC for UAV-assisted public safety communications. IEEE Access 2018, 6, 783–796. [Google Scholar] [CrossRef]
- Bupe, P.; Haddad, R.; Rios-Gutierrez, F. Relief and emergency communication network based on an autonomous decentralized UAV clustering network. In Proceedings of the SoutheastCon, Fort Lauderdale, FL, USA, 9–12 April 2015; pp. 1–8. [Google Scholar]
- Merwaday, A.; Guvenc, I. UAV assisted heterogeneous networks for public safety communications. In Proceedings of the Wireless Communications and Networking Conference Workshops (WCNCW), New Orleans, LA, USA, 9–12 March 2015; pp. 329–334. [Google Scholar]
- Luo, C.; Nightingale, J.; Asemota, E.; Grecos, C. A UAV-cloud system for disaster sensing applications. In Proceedings of the 2015 IEEE 81st Vehicular Technology Conference (VTC Spring), Glasgow, UK, 11–14 May 2015; pp. 1–5. [Google Scholar]
- Zanella, A.; Bui, N.; Castellani, A.; Vangelista, L.; Zorzi, M. Internet of Things for Smart Cities. IEEE Internet Things J. 2014, 1, 22–32. [Google Scholar] [CrossRef]
- Eleftherakis, G.; Pappas, D.; Lagkas, T.; Rousis, K.; Paunovski, O. Architecting the IoT paradigm: A middleware for autonomous distributed sensor networks. Int. J. Distr. Sens. Netw. 2015, 11, 139735. [Google Scholar] [CrossRef]
- Solomitckii, D.; Gapeyenko, M.; Semkin, V.; Andreev, S.; Koucheryavy, Y. Technologies for efficient amateur drone detection in 5G millimeter-wave cellular infrastructure. IEEE Commun. Mag. 2018, 56, 43–50. [Google Scholar] [CrossRef]
- Mozaffari, M.; Saad, W.; Bennis, M.; Nam, Y.H.; Debbah, M. A Tutorial on UAVs for Wireless Networks: Applications, Challenges, and Open Problems. arXiv, 2018; arXiv:1803.00680. [Google Scholar]
- Al-Hourani, A.; Kandeepan, S.; Jamalipour, A. Modeling air-to-ground path loss for low altitude platforms in urban environments. In Proceedings of the 2014 IEEE Global Communications Conference, Austin, TX, USA, 8–12 December 2014; pp. 2898–2904. [Google Scholar] [CrossRef]
- Zeng, Y.; Zhang, R.; Lim, T.J. Wireless communications with unmanned aerial vehicles: Opportunities and challenges. IEEE Commun. Mag. 2016, 54, 36–42. [Google Scholar] [CrossRef]
- Mozaffari, M.; Saad, W.; Bennis, M.; Debbah, M. Mobile Unmanned Aerial Vehicles (UAVs) for Energy-Efficient Internet of Things Communications. IEEE Trans. Wirel. Commun. 2017, 16, 7574–7589. [Google Scholar] [CrossRef]
- Soorki, M.N.; Mozaffari, M.; Saad, W.; Manshaei, M.H.; Saidi, H. Resource Allocation for Machine-to-Machine Communications with Unmanned Aerial Vehicles. In Proceedings of the 2016 IEEE Globecom Workshops (GC Wkshps), Washington, DC, USA, 4–8 December 2016; pp. 1–6. [Google Scholar] [CrossRef]
- Mozaffari, M.; Saad, W.; Bennis, M.; Debbah, M. Efficient Deployment of Multiple Unmanned Aerial Vehicles for Optimal Wireless Coverage. IEEE Commun. Lett. 2016, 20, 1647–1650. [Google Scholar] [CrossRef]
- Chen, Y.; Feng, W.; Zheng, G. Optimum Placement of UAV as Relays. IEEE Commun. Lett. 2018, 22, 248–251. [Google Scholar] [CrossRef]
- Kalantari, E.; Yanikomeroglu, H.; Yongacoglu, A. On the Number and 3D Placement of Drone Base Stations in Wireless Cellular Networks. In Proceedings of the 2016 IEEE 84th Vehicular Technology Conference (VTC-Fall), Montreal, QC, Canada, 18–21 September 2016; pp. 1–6. [Google Scholar] [CrossRef]
- Mozaffari, M.; Saad, W.; Bennis, M.; Debbah, M. Unmanned Aerial Vehicle With Underlaid Device-to-Device Communications: Performance and Tradeoffs. IEEE Trans. Wirel. Commun. 2016, 15, 3949–3963. [Google Scholar] [CrossRef]
- Zeng, Y.; Zhang, R. Energy-Efficient UAV Communication With Trajectory Optimization. IEEE Trans. Wirel. Commun. 2017, 16, 3747–3760. [Google Scholar] [CrossRef]
- Tran, T.X.; Hajisami, A.; Pompili, D. Cooperative Hierarchical Caching in 5G Cloud Radio Access Networks. IEEE Netw. 2017, 31, 35–41. [Google Scholar] [CrossRef]
- Anton, S.R.; Inman, D.J. Performance modeling of unmanned aerial vehicles with on-board energy harvesting. In Active and Passive Smart Structures and Integrated Systems; International Society for Optics and Photonics: Bellingham, WA, USA, 2011; Volume 7977. [Google Scholar]
- Ceran, E.T.; Erkilic, T.; Uysal-Biyikoglu, E.; Girici, T.; Leblebicioglu, K. Optimal energy allocation policies for a high altitude flying wireless access point. Trans. Emerg. Telecommun. Technol. 2017, 28, e3034. [Google Scholar] [CrossRef]
- Motlagh, N.H.; Taleb, T.; Arouk, O. Low-Altitude Unmanned Aerial Vehicles-Based Internet of Things Services: Comprehensive Survey and Future Perspectives. IEEE Internet Things J. 2016, 3, 899–922. [Google Scholar] [CrossRef]
- Shaikh, Z.; Baidya, S.; Levorato, M. Robust Multi-Path Communications for UAVs in the Urban IoT. In Proceedings of the 2018 IEEE International Conference on Sensing, Communication and Networking (SECON Workshops), Hong Kong, China, 11–13 June 2018; pp. 1–5. [Google Scholar] [CrossRef]
- Yan, S.; Peng, M.; Cao, X. A Game Theory Approach for Joint Access Selection and Resource Allocation in UAV Assisted IoT Communication Networks. IEEE Internet Things J. 2018. [Google Scholar] [CrossRef]
- Chakareski, J. Aerial UAV-IoT sensing for ubiquitous immersive communication and virtual human teleportation. In Proceedings of the 2017 IEEE Conference on Computer Communications Workshops (INFOCOM WKSHPS), Atlanta, GA, USA, 1–4 May 2017; pp. 718–723. [Google Scholar] [CrossRef]
- Zhou, Z.; Feng, J.; Tan, L.; He, Y.; Gong, J. An Air-Ground Integration Approach for Mobile Edge Computing in IoT. IEEE Commun. Mag. 2018, 56, 40–47. [Google Scholar] [CrossRef]
- Mozaffari, M.; Saad, W.; Bennis, M.; Debbah, M. Mobile Internet of Things: Can UAVs Provide an Energy-Efficient Mobile Architecture? In Proceedings of the 2016 IEEE Global Communications Conference (GLOBECOM), Washington, DC, USA, 4–8 December 2016; pp. 1–6. [Google Scholar] [CrossRef]
- Wang, D.; Bai, L.; Zhang, X.; Guan, W.; Chen, C. Collaborative relay beamforming strategies for multiple destinations with guaranteed QoS in wireless machine-to-machine networks. Int. J. Distr. Sens. Netw. 2012, 8, 525640. [Google Scholar] [CrossRef]
- Sarigiannidis, P.; Lagkas, T.; Bibi, S.; Ampatzoglou, A.; Bellavista, P. Hybrid 5G optical-wireless SDN-based networks, challenges and open issues. IET Netw. 2017, 6, 141–148. [Google Scholar] [CrossRef]
- Klepac, L.; Rozehnal, D. Scavenging simulation of small two-stroke engine with low-pressure fuel injection for usage in unmanned aerial vehicle (UAV). In Proceedings of the 2017 International Conference on Military Technologies (ICMT), Brno, Czech Republic, 31 May–2 June 2017; pp. 457–461. [Google Scholar]
- Honkavaara, E.; Eskelinen, M.A.; Plnen, I.; Saari, H.; Ojanen, H.; Mannila, R.; Holmlund, C.; Hakala, T.; Litkey, P.; Rosnell, T. Remote sensing of 3-D geometry and surface moisture of a peat production area using hyperspectral frame cameras in visible to short-wave infrared spectral ranges onboard a small unmanned airborne vehicle (UAV). IEEE Trans. Geosci. Remote Sens. 2016, 54, 5440–5454. [Google Scholar] [CrossRef]
- Zhang, C.; Zhang, W. Spectrum sharing for drone networks. IEEE J. Sel. Areas Commun. 2017, 35, 136–144. [Google Scholar]
- Triantafyllou, A.; Sarigiannidis, P.; Lagkas, T.D. Network Protocols, Schemes, and Mechanisms for Internet of Things (IoT): Features, Open Challenges, and Trends. Wirel. Commun. Mobile Comput. 2018, 2018. [Google Scholar] [CrossRef]
- Bellavista, P.; Giannelli, C.; Lagkas, T.; Sarigiannidis, P. Quality Management of Surveillance Multimedia Streams Via Federated SDN Controllers in Fiwi-Iot Integrated Deployment Environments. IEEE Access 2018, 6, 21324–21341. [Google Scholar] [CrossRef]
- Altawy, R.; Youssef, A.M. Security, privacy, and safety aspects of civilian drones: A survey. ACM Trans. Cyber-Phys. Syst. 2017, 1, 7. [Google Scholar] [CrossRef]
- Granjal, J.; Monteiro, E.; Silva, J.S. Security for the internet of things: a survey of existing protocols and open research issues. IEEE Commun. Surv. Tutor. 2015, 17, 1294–1312. [Google Scholar] [CrossRef]
- Wallgren, L.; Raza, S.; Voigt, T. Routing Attacks and Countermeasures in the RPL-based Internet of Things. Int. J. Distr. Sens. Netw. 2013, 9, 794326. [Google Scholar] [CrossRef]
- Bloom, V.; Makris, D.; Argyriou, V. Clustered spatio-temporal manifolds for online action recognition. In Proceedings of the 2014 22nd International Conference on Pattern Recognition (ICPR), Stockholm, Sweden, 24–28 August 2014; pp. 3963–3968. [Google Scholar]
- Bloom, V.; Argyriou, V.; Makris, D. Hierarchical transfer learning for online recognition of compound actions. Comput. Vis. Image Underst. 2016, 144, 62–72. [Google Scholar] [CrossRef]
- Winter, T.; Thubert, P.; Brandt, A.; Hui, J.; Kelsey, R.; Levis, P.; Pister, K.; Struik, R.; Vasseur, J.P.; Alexander, R. RPL: IPv6 Routing Protocol for Low-Power and Lossy Networks; Technical report; Internet Engineering Task Force (IETF): Fremont, CA, USA, 2012. [Google Scholar]
- Tsitsiroudi, N.; Sarigiannidis, P.; Karapistoli, E.; Economides, A.A. EyeSim: A mobile application for visual-assisted wormhole attack detection in IoT-enabled WSNs. In Proceedings of the 2016 9th IFIP Wireless and Mobile Networking Conference (WMNC), Colmar, France, 11–13 July 2016; pp. 103–109. [Google Scholar]
- Zhang, L.; Afanasyev, A.; Burke, J.; Jacobson, V.; Crowley, P.; Papadopoulos, C.; Wang, L.; Zhang, B. Named data networking. ACM SIGCOMM Comput. Commun. Rev. 2014, 44, 66–73. [Google Scholar] [CrossRef]
- Leloglu, E. A review of security concerns in Internet of Things. J. Comput. Commun. 2016, 5, 121. [Google Scholar] [CrossRef]
- Shepherd, C.; Akram, R.N.; Markantonakis, K. Towards Trusted Execution of Multi-modal Continuous Authentication Schemes. In Proceedings of the Symposium on Applied Computing; ACM: New York, NY, USA, 2017; pp. 1444–1451. [Google Scholar] [CrossRef]
- Akram, R.N.; Markantonakis, K.; Mayes, K.; Bonnefoi, P.F.; Sauveron, D.; Chaumette, S. An efficient, secure and trusted channel protocol for avionics wireless networks. In Proceedings of the 2016 IEEE/AIAA 35th Digital Avionics Systems Conference (DASC), Sacramento, CA, USA, 25–30 September 2016; pp. 1–10. [Google Scholar]
- Markantonakis, K.; Akram, R.N.; Holloway, R. A secure and trusted boot process for avionics wireless networks. In Proceedings of the Integrated Communications Navigation and Surveillance (ICNS), Herndon, VA, USA, 19–21 April 2016; pp. 1C3–1. [Google Scholar]
- Gurulian, I.; Akram, R.N.; Markantonakis, K.; Mayes, K. Preventing relay attacks in mobile transactions using infrared light. In Proceedings of the Symposium on Applied Computing, Marrakech, Morocco, 3–7 April 2017; pp. 1724–1731. [Google Scholar]
- Akram, R.N.; Bonnefoi, P.F.; Chaumette, S.; Markantonakis, K.; Sauveron, D. Secure Autonomous UAVs Fleets by Using New Specific Embedded Secure Elements. In Proceedings of the Trustcom/BigDataSE/ISPA, Tianjin, China, 23–26 August 2016; pp. 606–614. [Google Scholar]
- Yao, X.; Han, X.; Du, X.; Zhou, X. A lightweight multicast authentication mechanism for small scale IoT applications. IEEE Sens. J. 2013, 13, 3693–3701. [Google Scholar] [CrossRef]
- Ning, H.; Liu, H.; Yang, L. Cyber-entity security in the Internet of things. Computer 2013, 46, 46–53. [Google Scholar] [CrossRef]
- Trojak, D.; Komosny, D. System for Anonymous Data Collection Based on Group Signature Scheme. Acta Univ. Agric. Silvicult. Mendel. Brun. 2016, 64, 1785–1795. [Google Scholar] [CrossRef]
- De Cristofaro, E.; Soriente, C. Short paper: PEPSI-privacy-enhanced participatory sensing infrastructure. In Proceedings of the Fourth ACM Conference on Wireless Network Security, Hamburg, Germany, 14–17 June 2011; pp. 23–28. [Google Scholar]
- Senior, A.; Pankanti, S.; Hampapur, A.; Brown, L.; Tian, Y.L.; Ekin, A.; Connell, J.; Shu, C.F.; Lu, M. Enabling video privacy through computer vision. IEEE Secur. Privacy 2005, 3, 50–57. [Google Scholar] [CrossRef]
- Korshunov, P.; Ebrahimi, T. Using face morphing to protect privacy. In Proceedings of the 2013 10th IEEE International Conference on Advanced Video and Signal Based Surveillance (AVSS), Krakow, Poland, 27–30 August 2013; pp. 208–213. [Google Scholar]
- Korshunov, P.; Ebrahimi, T. Using warping for privacy protection in video surveillance. In Proceedings of the 2013 18th International Conference on Digital Signal Processing (DSP), Fira, Greece, 1–3 July 2013; pp. 1–6. [Google Scholar]
- Villasenor, J. Observations from above: unmanned aircraft systems and privacy. Harv. J. Law Public Policy 2013, 36, 457. [Google Scholar]
- Finn, R.L.; Wright, D. Unmanned aircraft systems: Surveillance, ethics and privacy in civil applications. Comput. Law Secur. Rev. 2012, 28, 184–194. [Google Scholar] [CrossRef]
- Clarke, R. The regulation of civilian drones’ impacts on behavioural privacy. Comput. Law Secur. Rev. 2014, 30, 286–305. [Google Scholar] [CrossRef]
- Wilson, R.L. Ethical issues with use of drone aircraft. In Proceedings of the IEEE 2014 International Symposium on Ethics in Engineering, Science, and Technology, Chicago, IL, USA, 23–24 May 2014; p. 56. [Google Scholar]
- Boult, T.E. PICO: Privacy through invertible cryptographic obscuration. In Proceedings of the Computer Vision for Interactive and Intelligent Environment, Lexington, KY, USA, 17–18 November 2005; pp. 27–38. [Google Scholar]
- Carrillo, P.; Kalva, H.; Magliveras, S. Compression independent reversible encryption for privacy in video surveillance. EURASIP J. Inf. Secur. 2009, 2009, 5. [Google Scholar] [CrossRef]
- Rahman, S.M.M.; Hossain, M.A.; Mouftah, H.; El Saddik, A.; Okamoto, E. Chaos-cryptography based privacy preservation technique for video surveillance. Multimed. Syst. 2012, 18, 145–155. [Google Scholar] [CrossRef]
- Dufaux, F.; Ebrahimi, T. Video surveillance using JPEG 2000. In Applications of Digital Image Processing XXVII; International Society for Optics and Photonics: Bellingham, WA, USA, 2004; Volume 5558, pp. 268–276. [Google Scholar]
- Martinez-Ponte, I.; Desurmont, X.; Meessen, J.; Delaigle, J.F. Robust human face hiding ensuring privacy. In Proceedings of the International Workshop on Image Analysis for Multimedia Interactive Services, Montreux, Switzerland, 13–15 April 2005; Volume 4. [Google Scholar]
- Dufaux, F.; Ebrahimi, T. Scrambling for privacy protection in video surveillance systems. IEEE Trans. Circ. Syst. Video Technol. 2008, 18, 1168–1174. [Google Scholar] [CrossRef]
- Alcaide, A.; Palomar, E.; Montero-Castillo, J.; Ribagorda, A. Anonymous authentication for privacy- preserving IoT target-driven applications. Comput. Secur. 2013, 37, 111–123. [Google Scholar] [CrossRef]
- Akram, R.N.; Ko, R.K. Unified model for data security-A position paper. In Proceedings of the IEEE 13th International Conference on Trust, Security and Privacy in Computing and Communications (TrustCom), Beijing, China, 24–26 September 2014; pp. 831–839. [Google Scholar]
- Suen, C.H.; Ko, R.K.; Tan, Y.S.; Jagadpramana, P.; Lee, B.S. S2logger: End-to-end data tracking mechanism for cloud data provenance. In Proceedings of the 2013 12th IEEE International Conference on Trust, Security and Privacy in Computing and Communications (TrustCom), Melbourne, Australia, 16–18 July 2013; pp. 594–602. [Google Scholar]
- Gupta, L.; Jain, R.; Vaszkun, G. Survey of important issues in UAV communication networks. IEEE Commun. Surv. Tutor. 2016, 18, 1123–1152. [Google Scholar] [CrossRef]
- Bekmezci, I.; Sahingoz, O.K.; Temel, A. Flying ad-hoc networks (FANETs): A survey. Ad Hoc Netw. 2013, 11, 1254–1270. [Google Scholar] [CrossRef]
- Cheng, B.N.; Moore, S. A comparison of MANET routing protocols on airborne tactical networks. In Proceedings of the MILCOM 2012—2012 IEEE Military Communications Conference, Orlando, FL, USA, 29 October–1 November 2012; pp. 1–6. [Google Scholar]
- Shirani, R.; St-Hilaire, M.; Kunz, T.; Zhou, Y.; Li, J.; Lamont, L. Combined reactive-geographic routing for unmanned aeronautical ad-hoc networks. In Proceedings of the 2012 8th International Wireless Communications and Mobile Computing Conference (IWCMC), Limassol, Cyprus, 27–31 August 2012; pp. 820–826. [Google Scholar]
- Yu, Q.; Zhang, B.; Liu, C.; Mouftah, H.T. Energy-Efficient Geographical Forwarding Algorithm for Wireless Ad Hoc and Sensor Networks. In Proceedings of the Wireless Communications and Networking Conference, Las Vegas, NV, USA, 31 March–3 April 2008; pp. 2468–2473. [Google Scholar]
- Lagias, A.E.; Lagkas, T.D.; Zhang, J. New RSSI-Based Tracking for Following Mobile Targets Using the Law of Cosines. IEEE Wirel. Commun. Lett. 2018, 7, 392–395. [Google Scholar] [CrossRef]
- Rault, T.; Bouabdallah, A.; Challal, Y. Energy efficiency in wireless sensor networks: A top-down survey. Comput. Netw. 2014, 67, 104–122. [Google Scholar] [CrossRef]
- Maza, I.; Ollero, A. Multiple UAV cooperative searching operation using polygon area decomposition and efficient coverage algorithms. In Distributed Autonomous Robotic Systems 6; Springer: Berlin/Heidelberg, Germany, 2007; pp. 221–230. [Google Scholar]
- Dixon, S.R.; Wickens, C.D.; Chang, D. Mission control of multiple unmanned aerial vehicles: A workload analysis. Hum. Fact. 2005, 47, 479–487. [Google Scholar] [CrossRef] [PubMed]
- Ruff, H.A.; Calhoun, G.L.; Draper, M.H.; Fontejon, J.V.; Guilfoos, B.J. Exploring Automation Issues in Supervisory Control of Multiple UAVs; Technical Report; Sytronics Inc.: Dayton, OH, USA, 2004. [Google Scholar]
- Cummings, M.L.; Bruni, S.; Mercier, S.; Mitchell, P.J. Automation Architecture for Single Operator, Multiple UAV Command and Control; Technical Report; Massachusetts Institute of Technology: Cambridge, MA, USA, 2007. [Google Scholar]
- Arslan, O.; Inalhan, G. Design of a decision support architecture for human operators in UAV fleet C2 applications. In Proceedings of the 14th International Command and Control Research and Technology Symposium (ICCRTS), Washington, DC, USA, 15–17 June 2009. [Google Scholar]
- Lee, J.; Kim, K.; Yoo, S.; Chung, A.Y.; Lee, J.Y.; Park, S.J.; Kim, H. Constructing a reliable and fast recoverable network for drones. In Proceedings of the 2016 IEEE International Conference on Communications (ICC), Kuala Lumpur, Malaysia, 22–27 May 2016; pp. 1–6. [Google Scholar]
- Giulietti, F.; Pollini, L.; Innocenti, M. Autonomous formation flight. IEEE Control Syst. 2000, 20, 34–44. [Google Scholar]
| Category | Technology | Data Rate | Range | Latency |
|---|---|---|---|---|
| WPAN | Bluetooth 4.0 | <1 Mbps | 60 m | 50 |
| WPAN | Zigbee | <250 kbps | <100 m | 50 |
| WLAN | 802.11a/b/g/n/ac | <600 Mbps | <250 m | 75 |
| WLAN | WAVE 802.11p | <27 Mbps | <1 km | 50 |
| LPWA | LoRA | <50 kbps | <15 km | 82 |
| LPWA | SigFox | <100 bps | <20 km | 82 |
| Cellular | NB-IoT | <250 kbps | World wide | 75 |
| Cellular | LTE-M | <1 Mbps | World wide | 75 |
| Cellular | LTE Advanced (4G) | <1 Gbps | World wide | 50 |
| Cellular | LTE D2D | - | World wide | 25 |
| Cellular | 5G | <10 Gbps | World wide | 3 |
© 2018 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Lagkas, T.; Argyriou, V.; Bibi, S.; Sarigiannidis, P. UAV IoT Framework Views and Challenges: Towards Protecting Drones as “Things”. Sensors 2018, 18, 4015. https://doi.org/10.3390/s18114015
Lagkas T, Argyriou V, Bibi S, Sarigiannidis P. UAV IoT Framework Views and Challenges: Towards Protecting Drones as “Things”. Sensors. 2018; 18(11):4015. https://doi.org/10.3390/s18114015
Chicago/Turabian StyleLagkas, Thomas, Vasileios Argyriou, Stamatia Bibi, and Panagiotis Sarigiannidis. 2018. "UAV IoT Framework Views and Challenges: Towards Protecting Drones as “Things”" Sensors 18, no. 11: 4015. https://doi.org/10.3390/s18114015
APA StyleLagkas, T., Argyriou, V., Bibi, S., & Sarigiannidis, P. (2018). UAV IoT Framework Views and Challenges: Towards Protecting Drones as “Things”. Sensors, 18(11), 4015. https://doi.org/10.3390/s18114015








