Trust Model of Wireless Sensor Networks and Its Application in Data Fusion
Abstract
:1. Introduction
2. Related Work
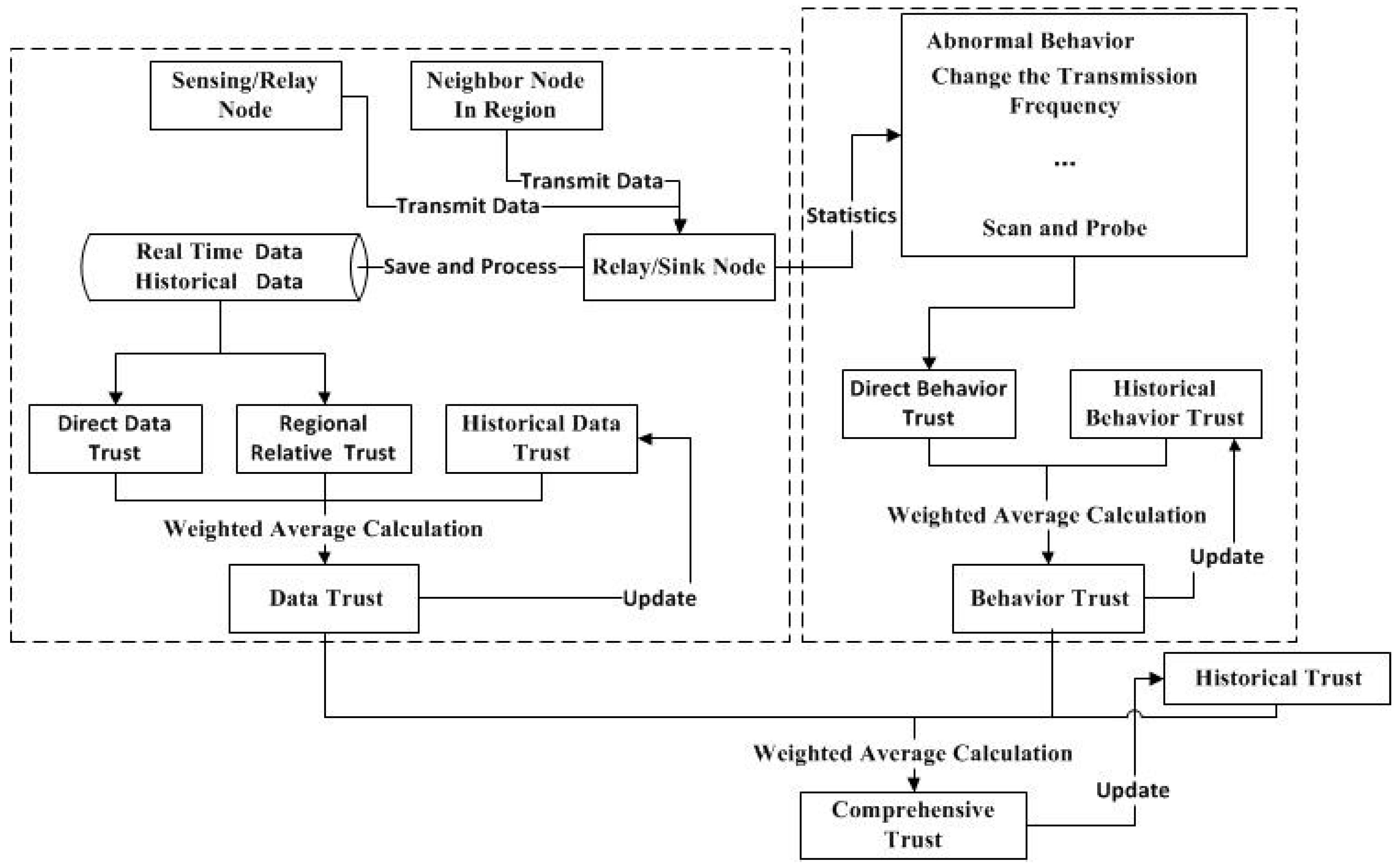
3. Trust Evaluation Model
3.1. Trust Evaluation of Sensor Node
3.1.1. Data Trust of Sensor Node
3.1.2. Behavior Trust of Sensor Node
3.1.3. Comprehensive Trust of Sensor Node
3.1.4. Historical Trust of Sensor Node
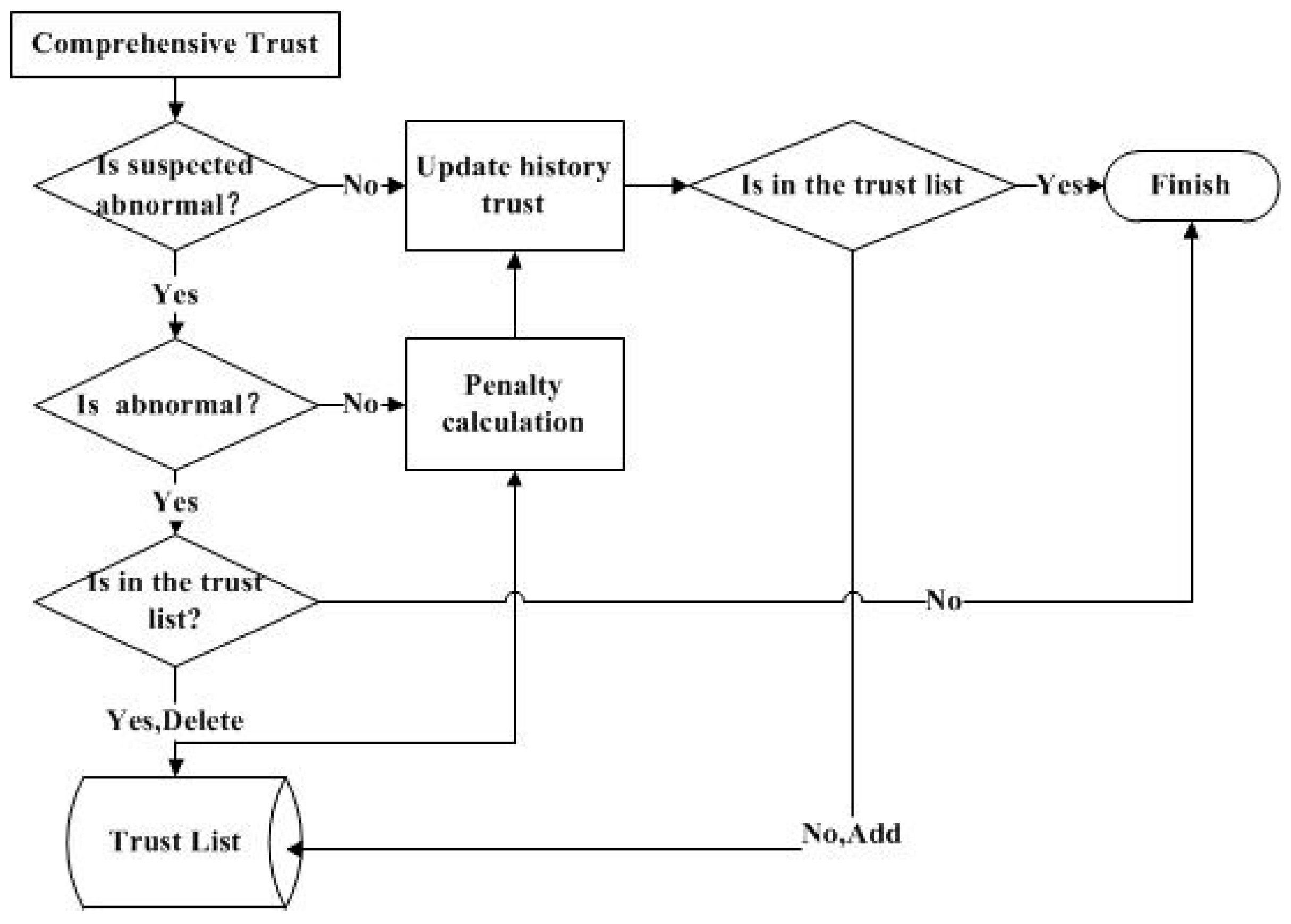
3.2. Trust Evaluation of Relay Node
3.2.1. Data Trust
3.2.2. Trust List
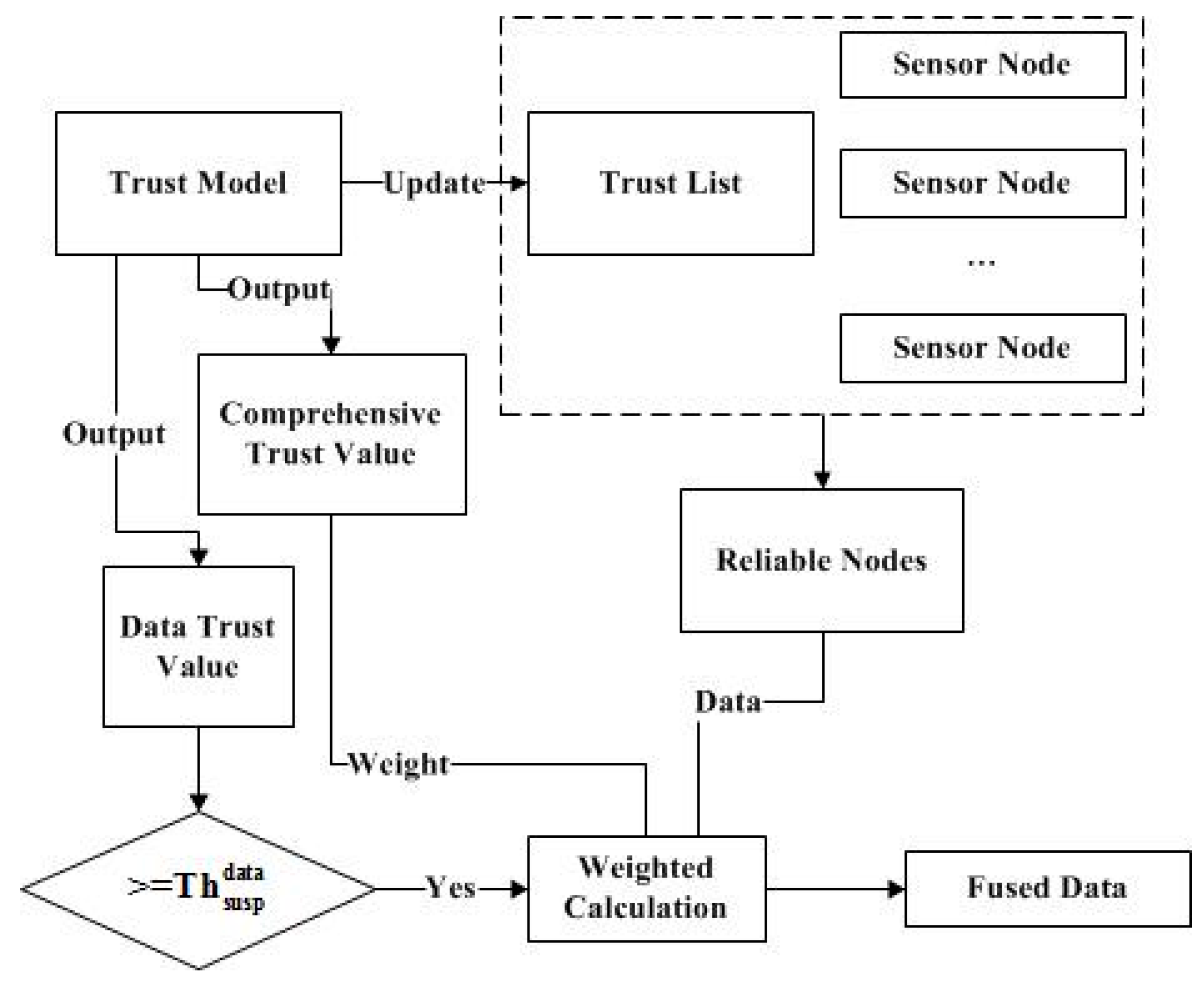
4. Trust Evaluation Model Used in Data Fusion
5. Results and Discussion
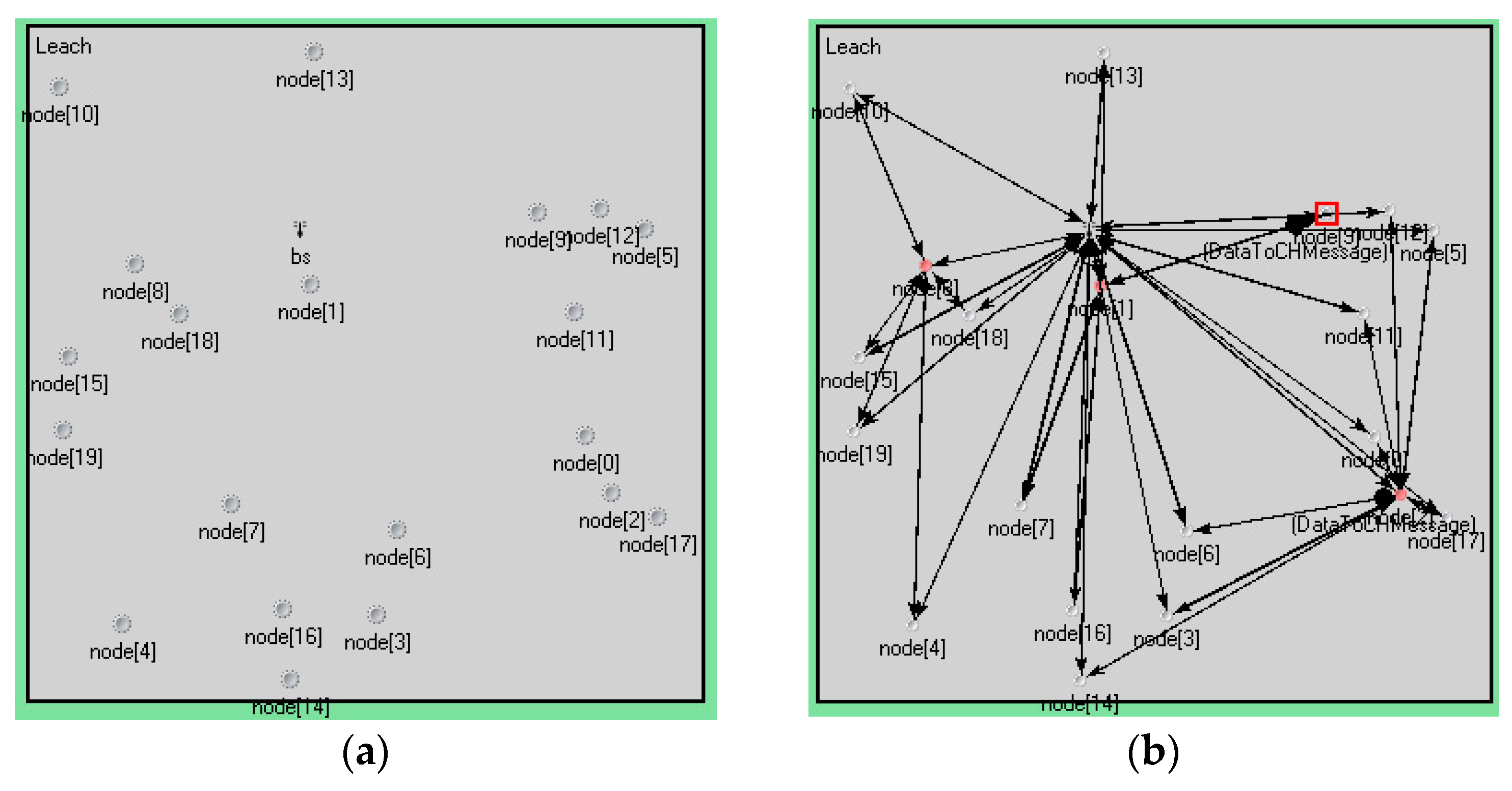
5.1. Simulation Environment and Parameter Setting
5.2. Simulation and Analysis
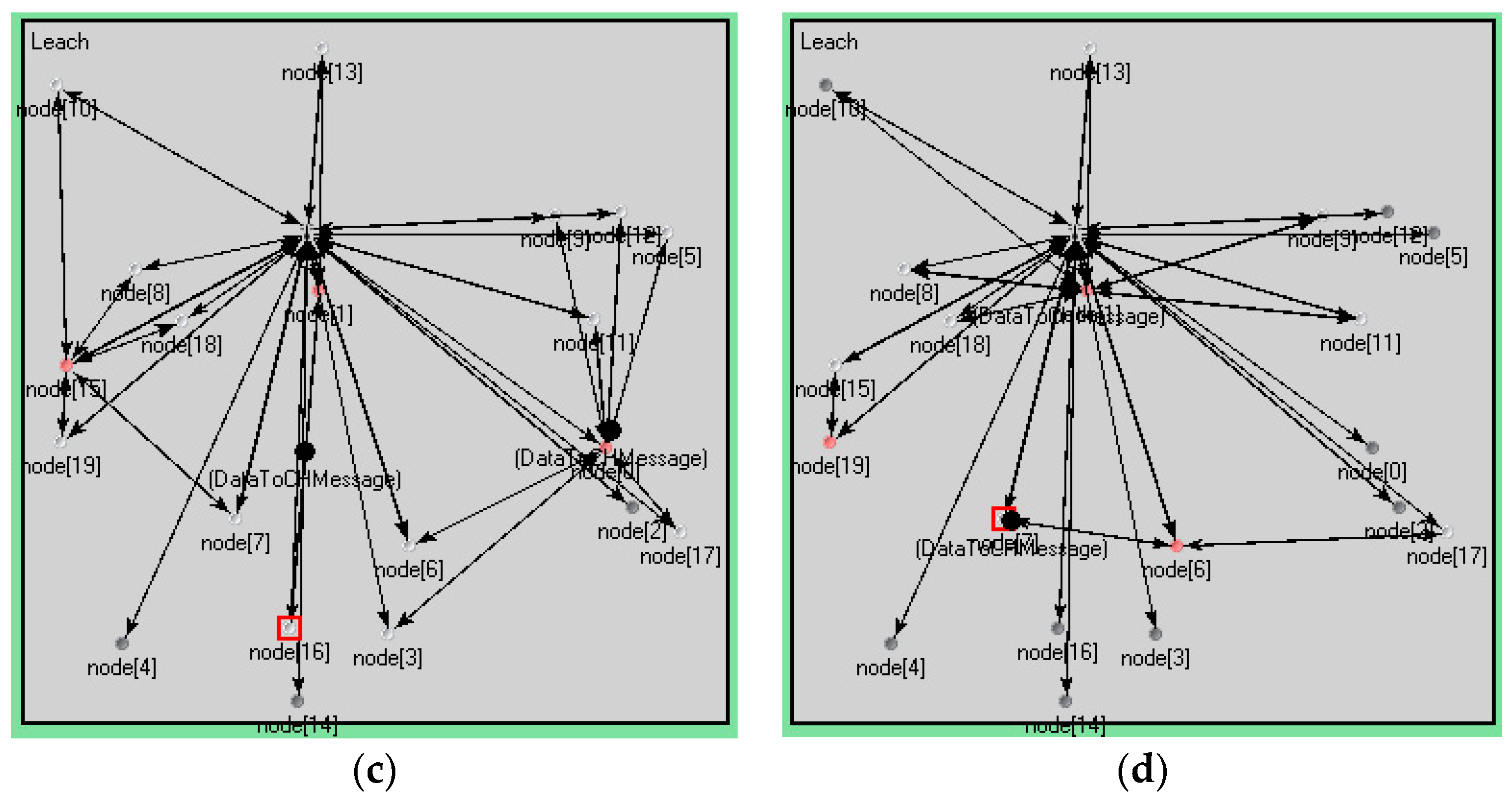
5.2.1. Node Distribution and Topology
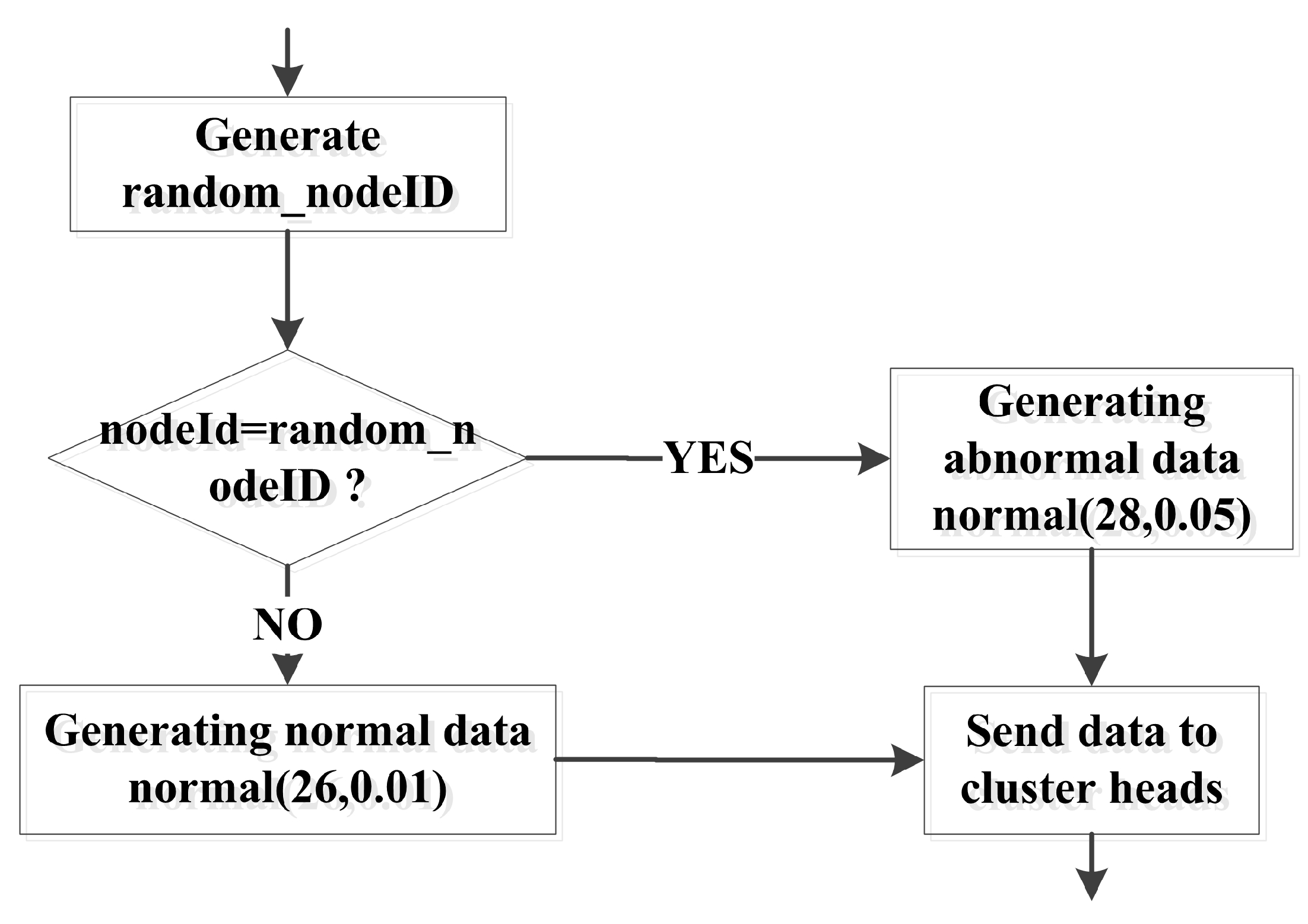
5.2.2. Simulation Data
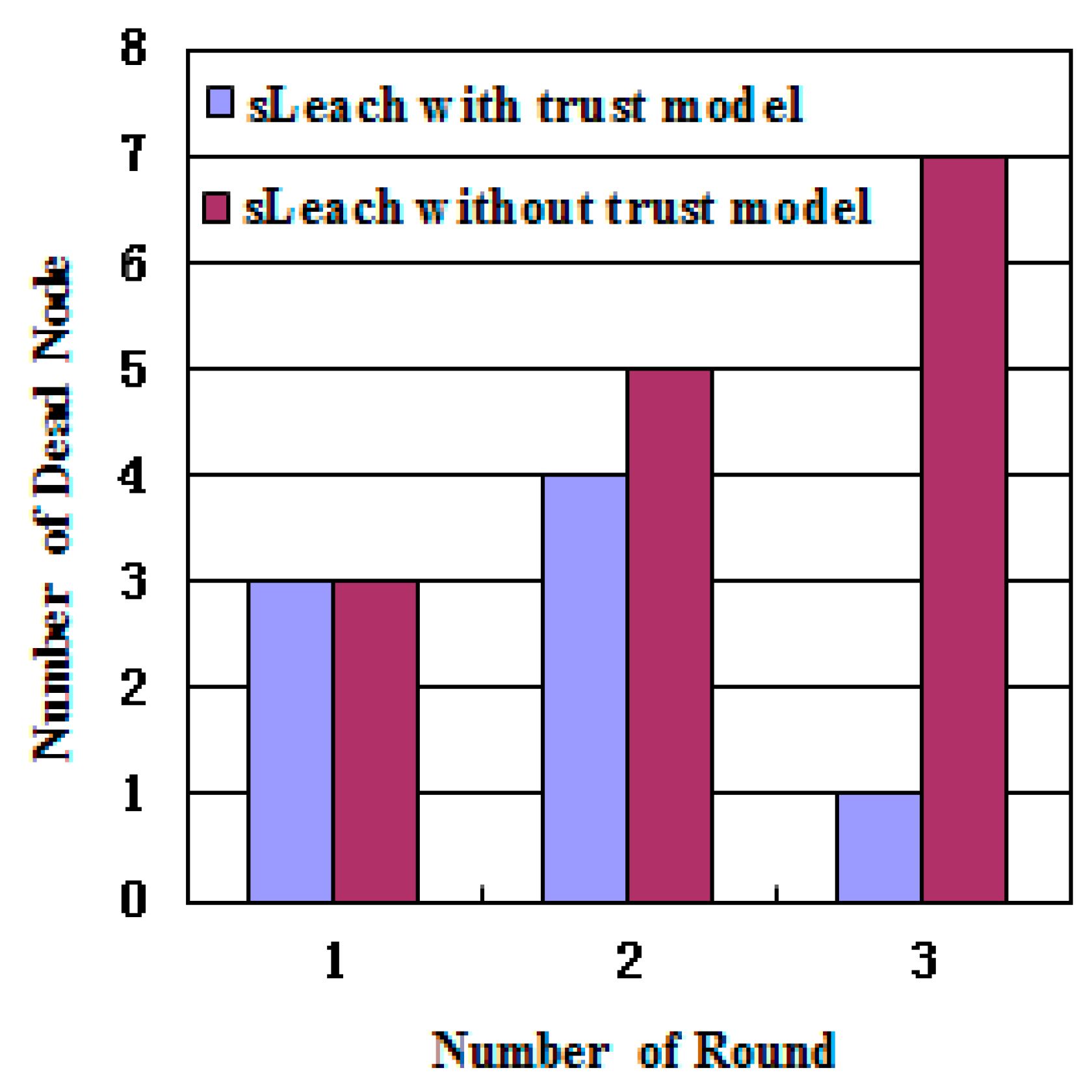
5.2.3. Improvements in Energy and Node Survival
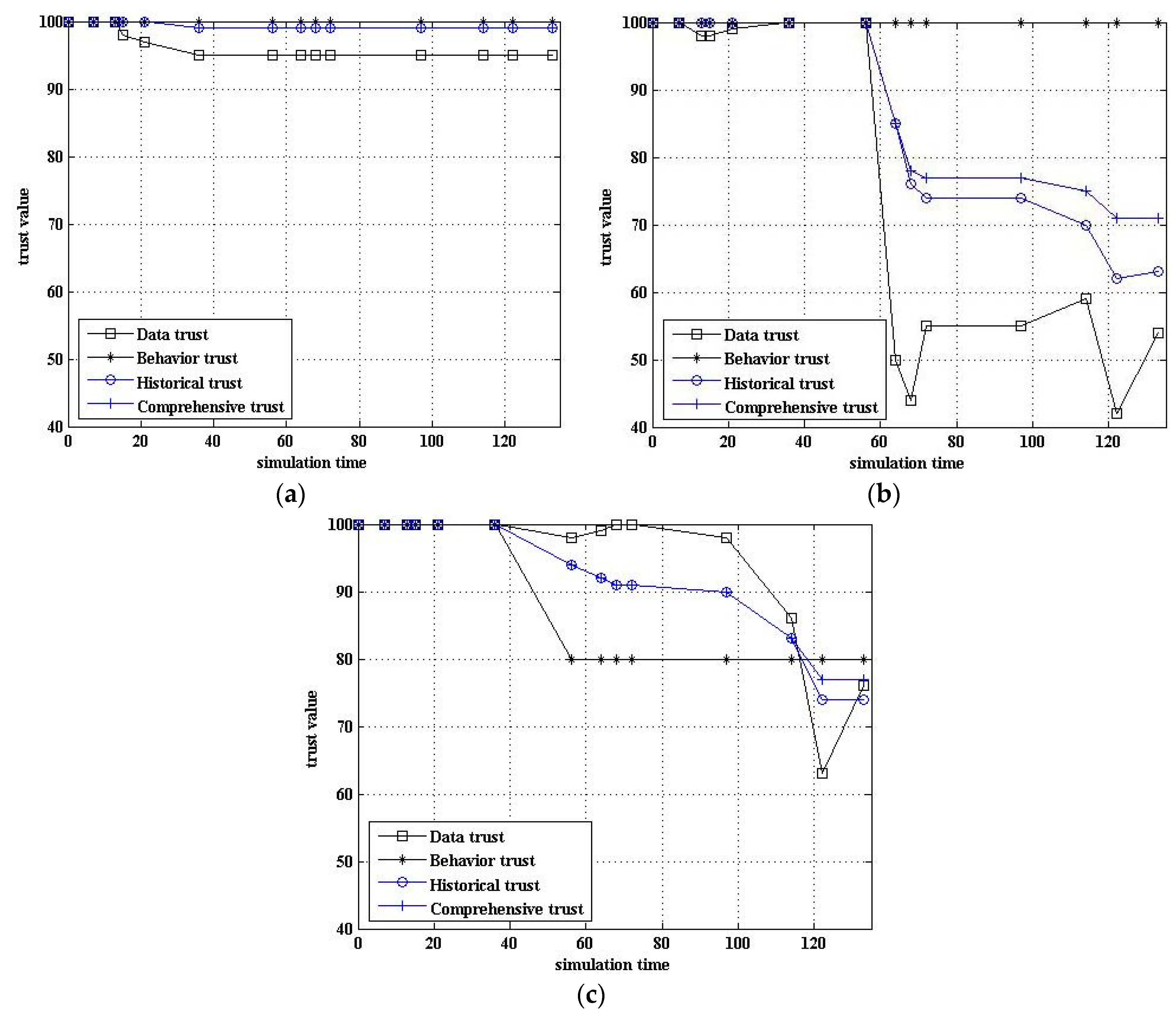
5.2.4. Comparison of Trust Value
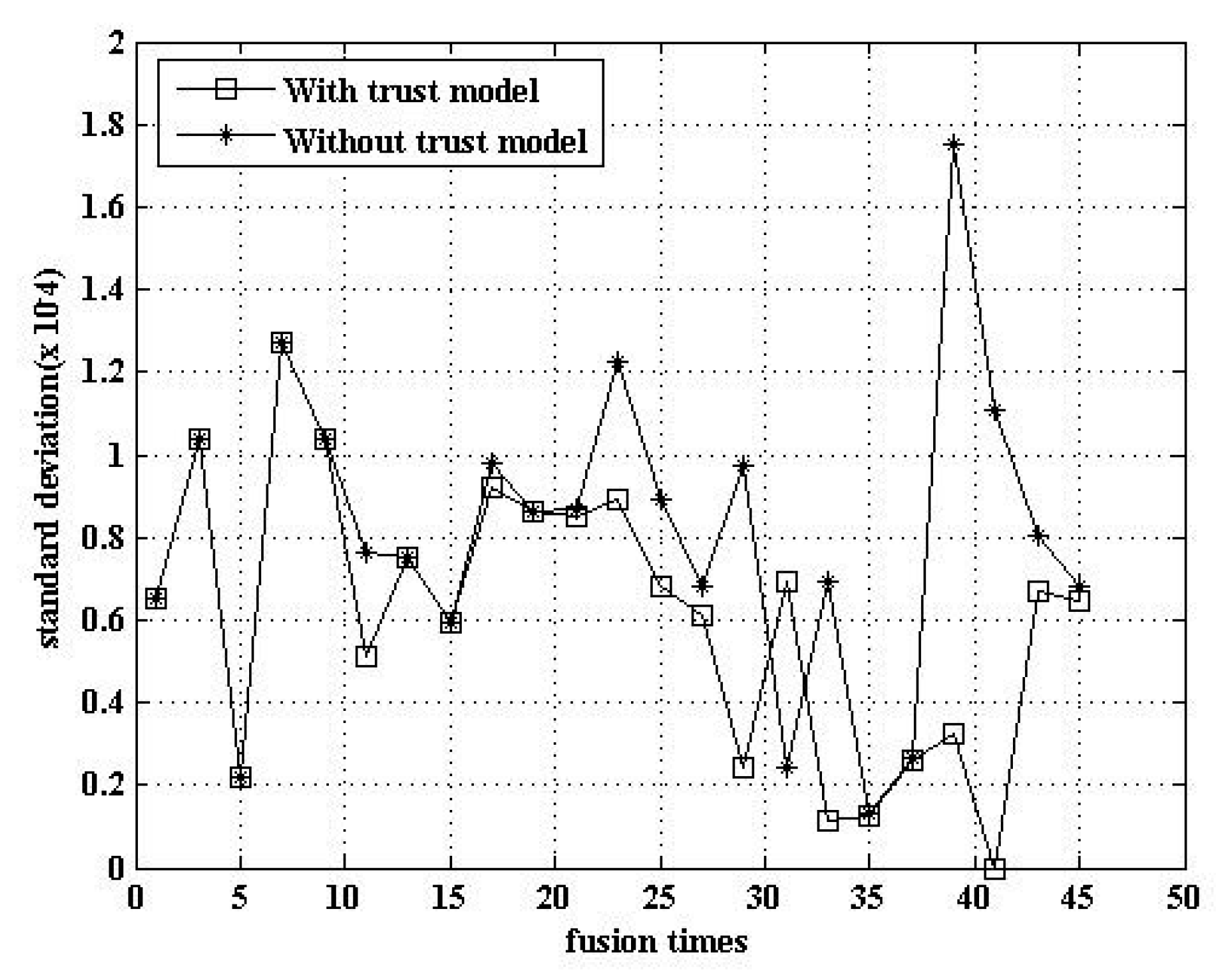
5.2.5. Comparison of Fusion Data
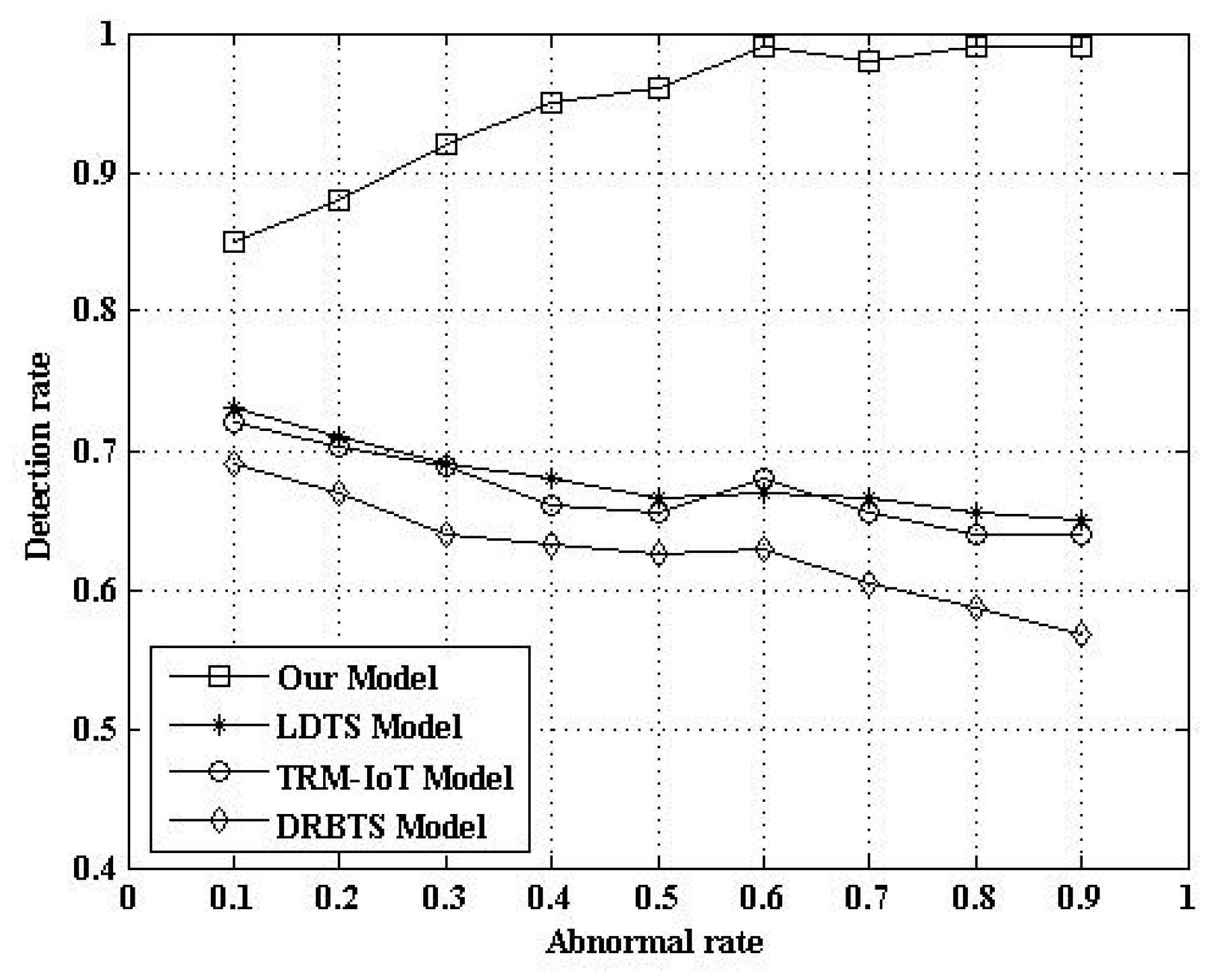
5.2.6. Comparison of Abnormal Detection Rate
6. Conclusions
Acknowledgments
Author Contributions
Conflicts of Interest
References
- Atzori, L.; Iera, A.; Morabito, G. The Internet of Things: A Survey. Comput. Netw. 2010, 54, 2787–2805. [Google Scholar] [CrossRef]
- Wan, J.; Yan, H.; Suo, H.; Li, F. Advances in Cyberphysical Systems Research. KSII Trans. Internet Inf. Syst. 2011, 5, 1891–1908. [Google Scholar]
- International Telecommunication Union. Internet Reports 2005: The Internet of Things; ITU: Geneva, Switzerland, 2005. [Google Scholar]
- Hachem, S.; Teixeira, T.; Issarny, V. Ontologies for the Internet of Thing. In Proceedings of the MDS ‘11 Proceedings of the 8th Middleware Doctoral Symposium, Lisbon, Portugal, 12–21 December 2011; pp. 1127–1131. [Google Scholar]
- Bandyopadhyay, D.; Sen, J. Internet of things: Applications and Challenges in Technology and Standardization. Wirel. Pers. Commun. 2011, 58, 49–69. [Google Scholar] [CrossRef]
- Khalid, O.; Khan, S.U.; Madani, S.A.; Hayat, K.; Khan, M.I.; Allah, N.M.; Kołodziej, J.; Wang, L.; Zeadally, S.; Chen, D. Comparative Study of Trust and Reputation Systems for Wireless Sensor Networks. Secur. Commun. Netw. 2013, 6, 669–688. [Google Scholar] [CrossRef]
- Ganeriwal, S.; Balzano, L.K.; Srivastava, M.B. Reputation-based framework for high integrity sensor networks. ACM Trans. Sens. Netw. 2008, 4, 1–37. [Google Scholar] [CrossRef]
- Srinivasan, A.; Teitelbaum, J.; Wu, J. DRBTS: Distributed Reputation-based Beacon Trust System. In Proceedings of the IEEE International Symposium on Dependable, Autonomic and Secure Computing, Indianapolis, IN, USA, 29 September–1 October 2006; pp. 277–283. [Google Scholar]
- Chen, D.; Chang, G.; Sun, D.; Li, J.; Jia, J.; Wang, X. TRM-IoT: A Trust Management Model Based on Fuzzy Reputation for Internet of Things. Comput. Sci. Inf. Syst. 2011, 8, 1207–1228. [Google Scholar]
- Dhulipala, V.R.S.; Karthik, N.; Chandrasekaran, R. A Novel Heuristic Approach Based Trust Worthy Architecture for Wireless Sensor Networks. Wirel. Pers. Commun. Int. J. 2013, 70, 189–205. [Google Scholar] [CrossRef]
- Jing, Q.; Tang, L.Y.; Chen, Z. Trust Management in Wireless Sensor Networks. J. Softw. 2008, 19, 1716–1730. [Google Scholar] [CrossRef]
- Xiao, D.Q.; Feng, J.Z.; Zhou, Q.; Yang, B. Gauss Reputation Framework for Sensor Networks. J. Commun. 2008, 29, 47–53. [Google Scholar]
- Fan, C.Q.; Wang, S.G.; Sun, Q.B.; Wang, H.M.; Zhang, G.W.; Yang, F.C.A. Trust Evaluation Method of Sensors Based on Energy Monitoring. Acta Electron. Sin. 2013, 41, 646–651. [Google Scholar]
- Li, X.Y.; Zhou, F.; Du, J. LDTS: A Lightweight and Dependable Trust System for Clustered Wireless Sensor Networks. IEEE Trans. Inf. Forensics Secur. 2013, 8, 924–935. [Google Scholar] [CrossRef]
- Zhang, B.; Huang, Z.H.; Xiang, Y.A. Novel Multiple-Level Trust Management Framework for Wireless Sensor Networks. Comput. Netw. 2014, 72, 45–61. [Google Scholar] [CrossRef]
- Yan, Z.; Zhang, P.; Vasilakos, A.V. Survey on Trust Management for Internet of Things. J. Netw. Comput. Appl. 2014. [Google Scholar] [CrossRef]
- Duan, J.Q.; Gao, D.Y.; Yang, D.; Foh, C.H.; Chen, H.H. An Energy-Aware Trust Derivation Scheme With Game Theoretic Approach in Wireless Sensor Networks for IoT Applications. IEEE Internet Things J. 2014, 1, 58–69. [Google Scholar] [CrossRef]
- Sahoo, S.S.; Sardar, A.R.; Singh, M.; Ray, S.; Sarkar, S.K. A Bio-Inspired and Trust Based Approach for Clustering in WSN. Nat. Comput. 2015, 15, 423–434. [Google Scholar] [CrossRef]
- Zhou, A.; Li, J.L.; Fan, C.Q.; Lei, T.; Yang, F.C. A Security Authentication Method Based on Trust Evaluation in VANETs. EURASIP J. Wirel. Commun. Netw. 2015. [Google Scholar] [CrossRef]
- Labraoui, N.; Gueroui, M.; Sekhri, L.A. Risk-Aware Reputation-Based Trust Management in Wireless Sensor Networks. Wirel. Pers. Commun. 2015, 87, 1037–1055. [Google Scholar] [CrossRef]
- Ramos, A.; Filho, R.H. Sensor Data Security Level Estimation Scheme for Wireless Sensor Networks. Sensors 2015, 15, 2104–2136. [Google Scholar] [CrossRef] [PubMed]
- Sicaria, S.; Rizzardia, A.; Griecob, L.A.; Coen-Porisinia, A. Security, Privacy and Trust in Internet of Things: The Road Ahead. Comput. Netw. 2015, 76, 146–164. [Google Scholar] [CrossRef]
- Nguyen, K.T.; Laurent, M.; Oualha, N. Survey on Secure Communication Protocols for the Internet of Things. Ad Hoc Netw. 2015, 32, 17–31. [Google Scholar] [CrossRef]
- Neisse, R.; Steri, G.; Fovino, I.N.; Baldini, G. SecKit: A Model-based Security Toolkit for the Internet of Things. Comput. Secur. 2015, 54, 60–76. [Google Scholar] [CrossRef]
- Li, P.; Wang, J.X.; Cao, J.N. Abnormal Event Detection Scheme Based on Compressive Sensing and GM (1, 1) in Wireless Sensor Networks. J. Electron. Inf. Technol. 2015, 37, 1586–1590. [Google Scholar]
- Wang, J.; Tang, S.J.; Yin, B.C.; Li, X.Y. Distributed Compressive Sampling for Lifetime Optimization in Dense Wireless Sensor Networks through Intelligent Compressive Sensing. In Proceedings of the IEEE International Conference on Computer Communications, Orlando, FL, USA, 25–30 March 2012; pp. 603–611. [Google Scholar]
- Xia, Y.; Zhao, Z.; Zhang, H. Distributed Anomaly Event Detection in Wireless Networks Using Compressed Sensing. In Proceedings of the 2011 11th International Symposium on Communications and Information Technologies (ISCIT), Hangzhou, China, 12–14 October 2011; pp. 250–255. [Google Scholar]
- Chen, Z.G.; Tian, L.Q. Application of the Trust Model in the Evaluation of Haze Perception Source. J. Comput. Appl. 2016, 36, 472–477. [Google Scholar]
- Wagner, D. Resilient Aggregation in Sensor Networks. In Proceedings of the ACM Workshop on Security of Ad Hoc and Sensor Networks, Washington, DC, USA, 25 October 2004; pp. 78–87. [Google Scholar]
- Bohli, J.M.; Papadimitratos, P.; Verardi, D.; Westhoff, D. Resilient Data Aggregation for Unattended WSNs. In Proceedings of the 2011 IEEE 36th Conference on Local Computer Networks, Bonn, Germany, 4–7 October 2011; pp. 994–1002. [Google Scholar]
- Liu, X.; Yu, J.; Wang, M. Network Security Situation Generation and Evaluation Based on Heterogeneous Sensor Fusion. In Proceedings of the International Conference on Wireless Communications, Networking and Mobile Computing, Beijing, China, 24–26 September 2009; pp. 1–4. [Google Scholar]
- Voigt, T.; Dunkels, A.; Alonso, J.; Schiller, J. Solar-aware Clustering in Wireless Sensor Networks. In Proceedings of the International Symposium on Computers and Communications, Alexandria, Egypt, 28 June–1 July 2004; pp. 238–243. [Google Scholar]

| Parameter | Value | Parameter | Value |
|---|---|---|---|
| Number of Nodes | 20 | Number of Rounds | 3 |
| Nodes Distribution | 200 m × 200 m | Time per Round | 90 time units |
| Number of Cluster Head | 3 | Number of Frames per Round | 5 |
| Initial Energy of Node | 0.2 J | Sim-Time-Limit | 200 s |
| Parameter | Value | Parameter | Value |
|---|---|---|---|
| 100 | 5 | ||
| (0.2, 0.5) | (0.4, 0.6) | ||
| (0.2, 0.3, 0.5) | (70, 80) | ||
| (70, 80) | 1.1 | ||
| 1.1 | (0.3, 0.3, 0.4) | ||
| (0.5, 0.5) | (70, 80) | ||
| 0, 1, 2 | - | - |
| Round | Cluster Heads (Index) | Node in the Cluster (Index) |
|---|---|---|
| 1 | 1 | 7, 9, 13, 16 |
| 2 | 0, 3, 5, 6, 11, 12, 14, 17 | |
| 8 | 4, 10, 15, 18, 19 | |
| 2 | 0 | 3, 5, 6, 9, 11, 12, 17 |
| 1 | 13, 16 | |
| 15 | 7, 8, 10, 18, 19 | |
| 3 | 1 | 8, 9, 10, 11, 13, 16, 18 |
| 6 | 7, 17 | |
| 19 | 15 |
© 2017 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Chen, Z.; Tian, L.; Lin, C. Trust Model of Wireless Sensor Networks and Its Application in Data Fusion. Sensors 2017, 17, 703. https://doi.org/10.3390/s17040703
Chen Z, Tian L, Lin C. Trust Model of Wireless Sensor Networks and Its Application in Data Fusion. Sensors. 2017; 17(4):703. https://doi.org/10.3390/s17040703
Chicago/Turabian StyleChen, Zhenguo, Liqin Tian, and Chuang Lin. 2017. "Trust Model of Wireless Sensor Networks and Its Application in Data Fusion" Sensors 17, no. 4: 703. https://doi.org/10.3390/s17040703
APA StyleChen, Z., Tian, L., & Lin, C. (2017). Trust Model of Wireless Sensor Networks and Its Application in Data Fusion. Sensors, 17(4), 703. https://doi.org/10.3390/s17040703




