CoR-MAC: Contention over Reservation MAC Protocol for Time-Critical Services in Wireless Body Area Sensor Networks
Abstract
:1. Introduction
2. Related Work
3. Contention over Reservation MAC
3.1. System Model and Basic Assumptions
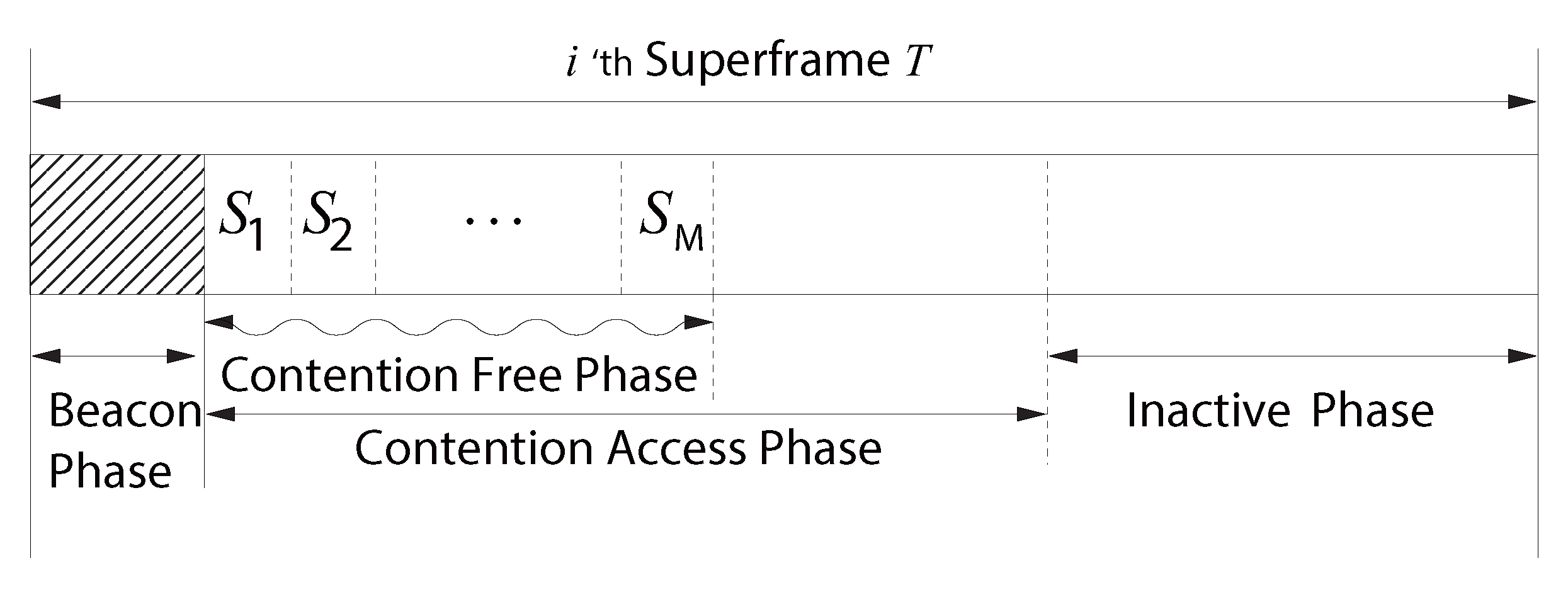
3.2. Superframe Structure
- No non-emergency traffic can be transmitted during an inactive phase that is designed for energy reduction. Although transmission is not allowed, this phase can be utilized for emergency data transmission, as in [4]. Transmission of emergency data during an inactive phase is beyond the scope of this paper.
- The beacon phase is the time in which only the coordinator is allowed to transmit a beacon frame, and it is used for network synchronization and advertising information, such as time slot allocation. The beacon frame includes superframe length, subsequent superframe start time, beacon length, CFP length, CAP length, length of the CFP time slot, network ID, the number of time slots in the CFP and the CFP allocation map, including slot number and node ID. The size of the beacon is varied according to the size of the CFP allocation map. If the number of nodes is 10∼15, the size of the beacon will be around 228∼278 bits when the size of the CFP allocation information per node is 10 bits (five bits for the number of slots and five bits for the node’s ID).
- Urgent data can be transmitted during either the CFP or CAP. A detailed description of urgent data transmission is described below.
- The time-critical data can be transmitted during CAP or the reserved time slot in CFP, as long as urgent data are not being transmitted.
- Non-time-critical data can be transmitted during either CFP or CAP, as long as urgent, time-critical or other non-time-critical data are not being transmitted.
3.3. Protocol Description
| Algorithm 1 The CoR-MAC algorithm for the coordinator. |
|
| Algorithm 2 The CoR-MAC algorithm for the node. |
|
4. Theoretical Approach
4.1. System Model
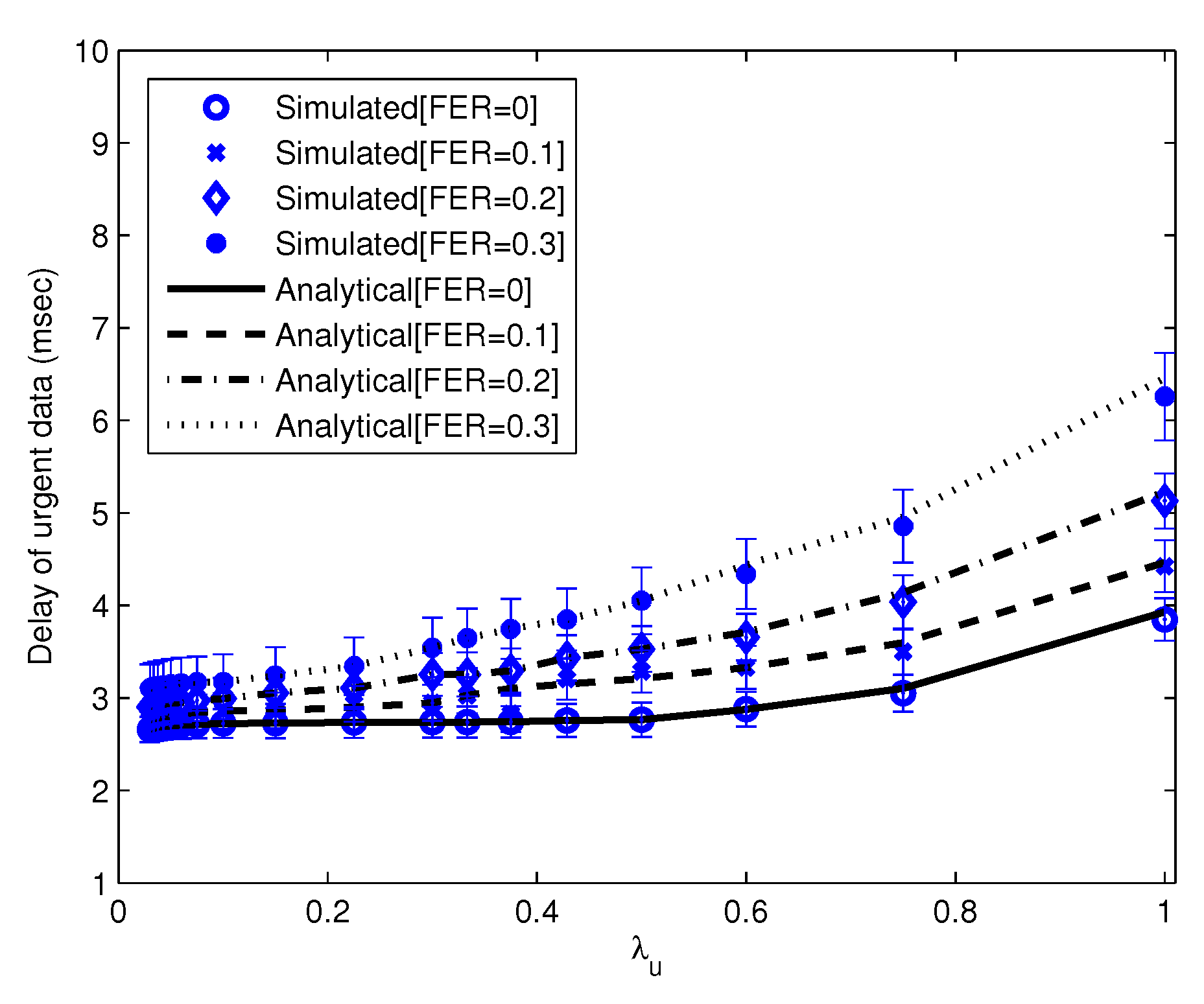
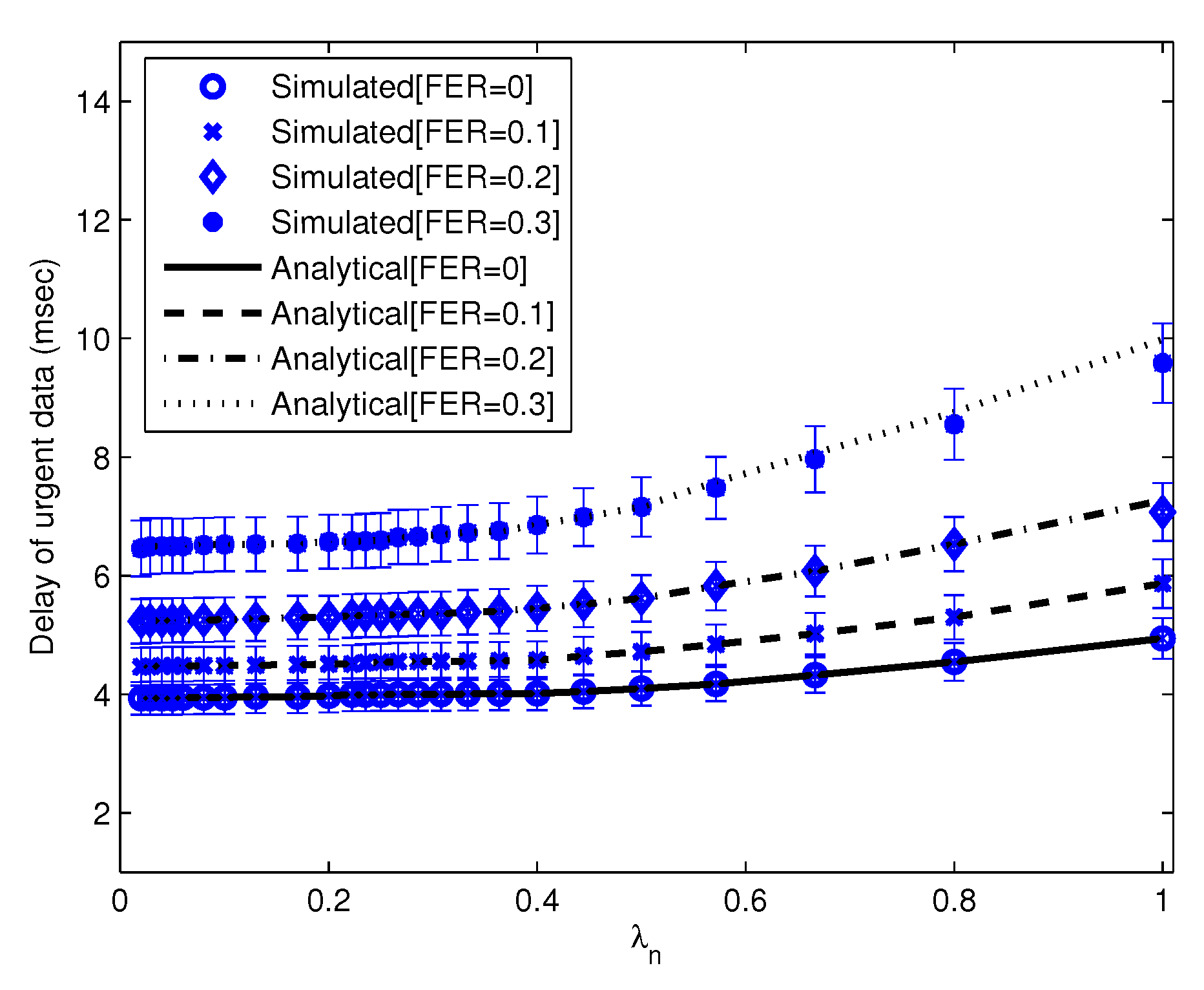
4.2. Expected Delay of Urgent Data
5. Performance Evaluation
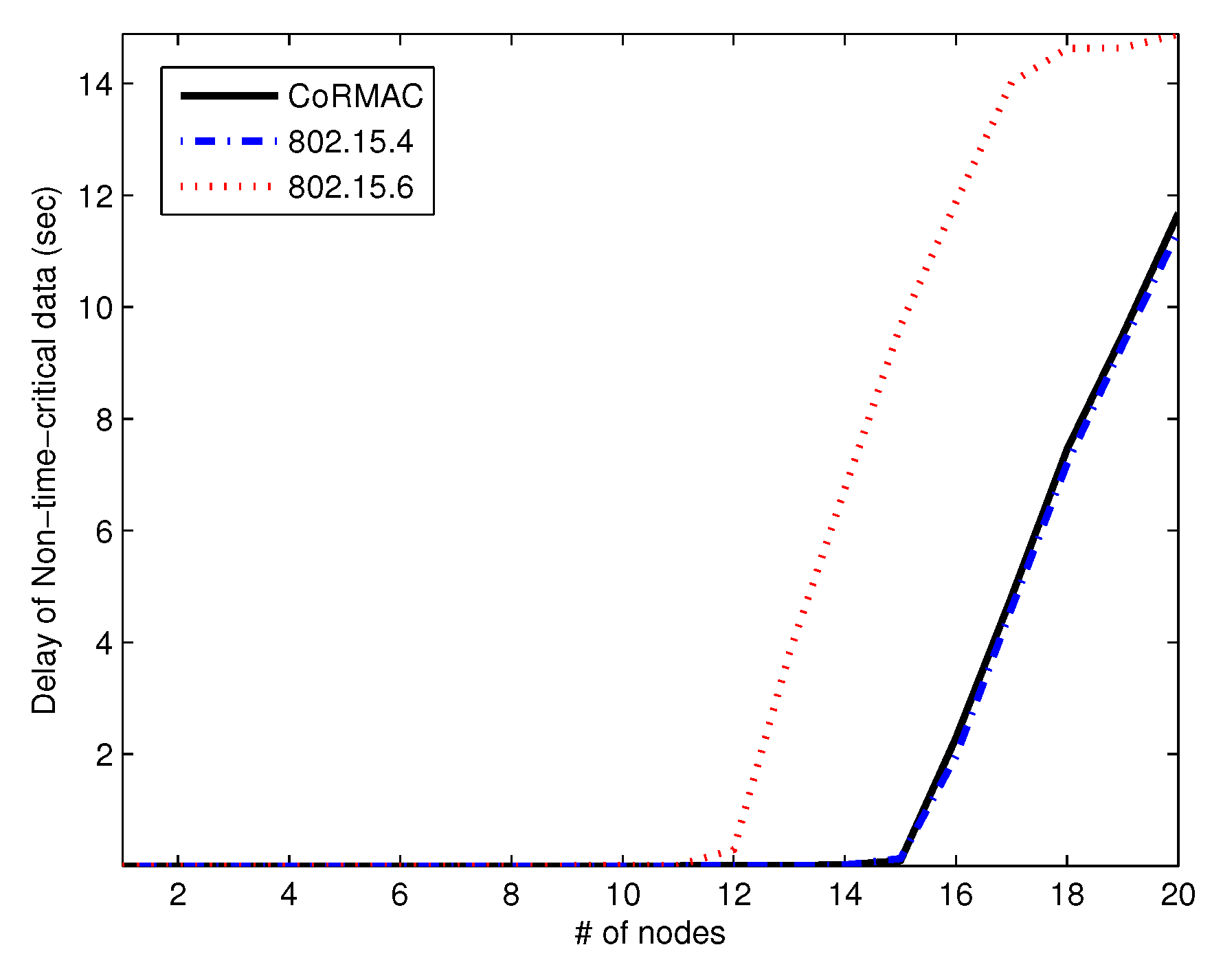
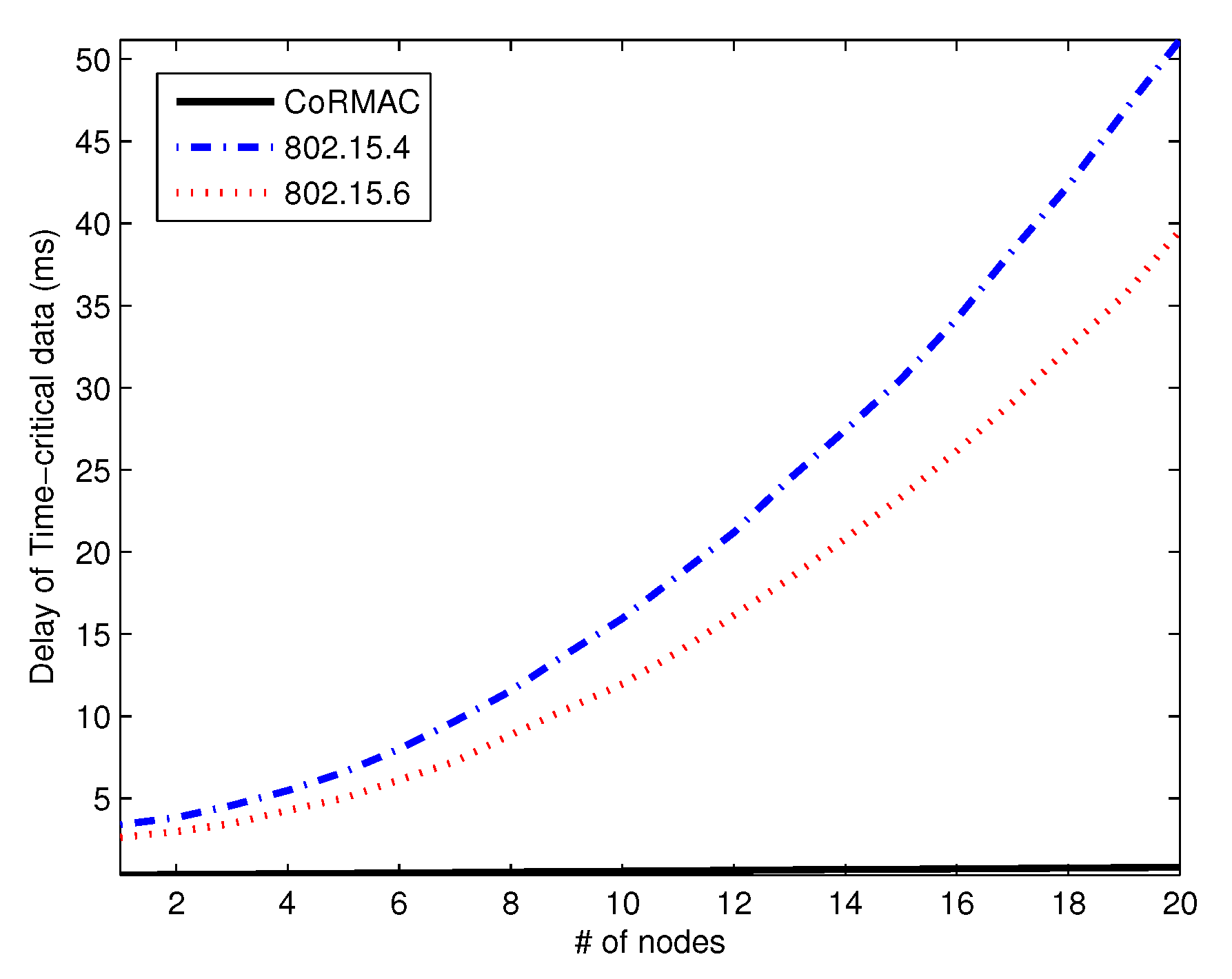
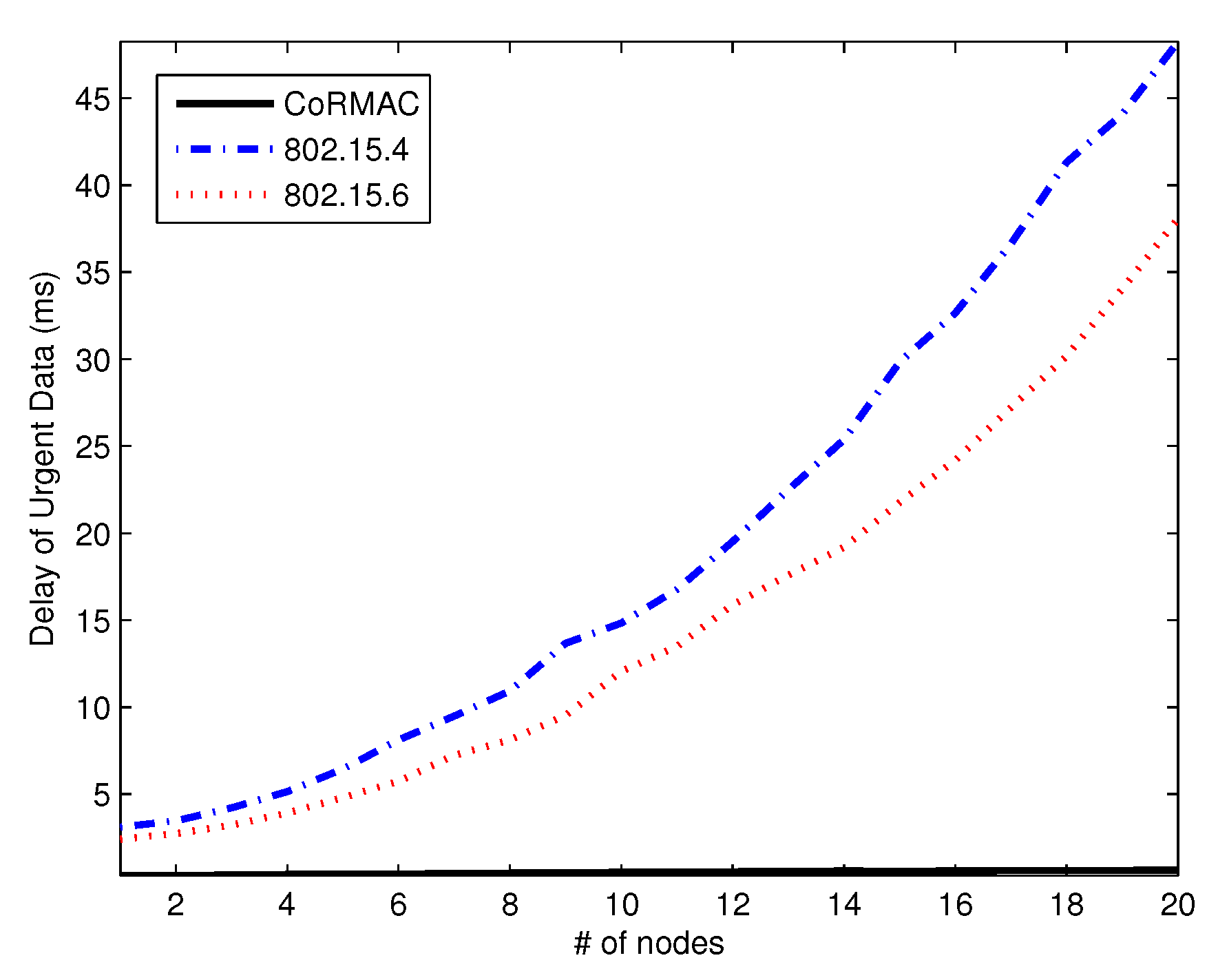
5.1. Delay
5.2. Throughput
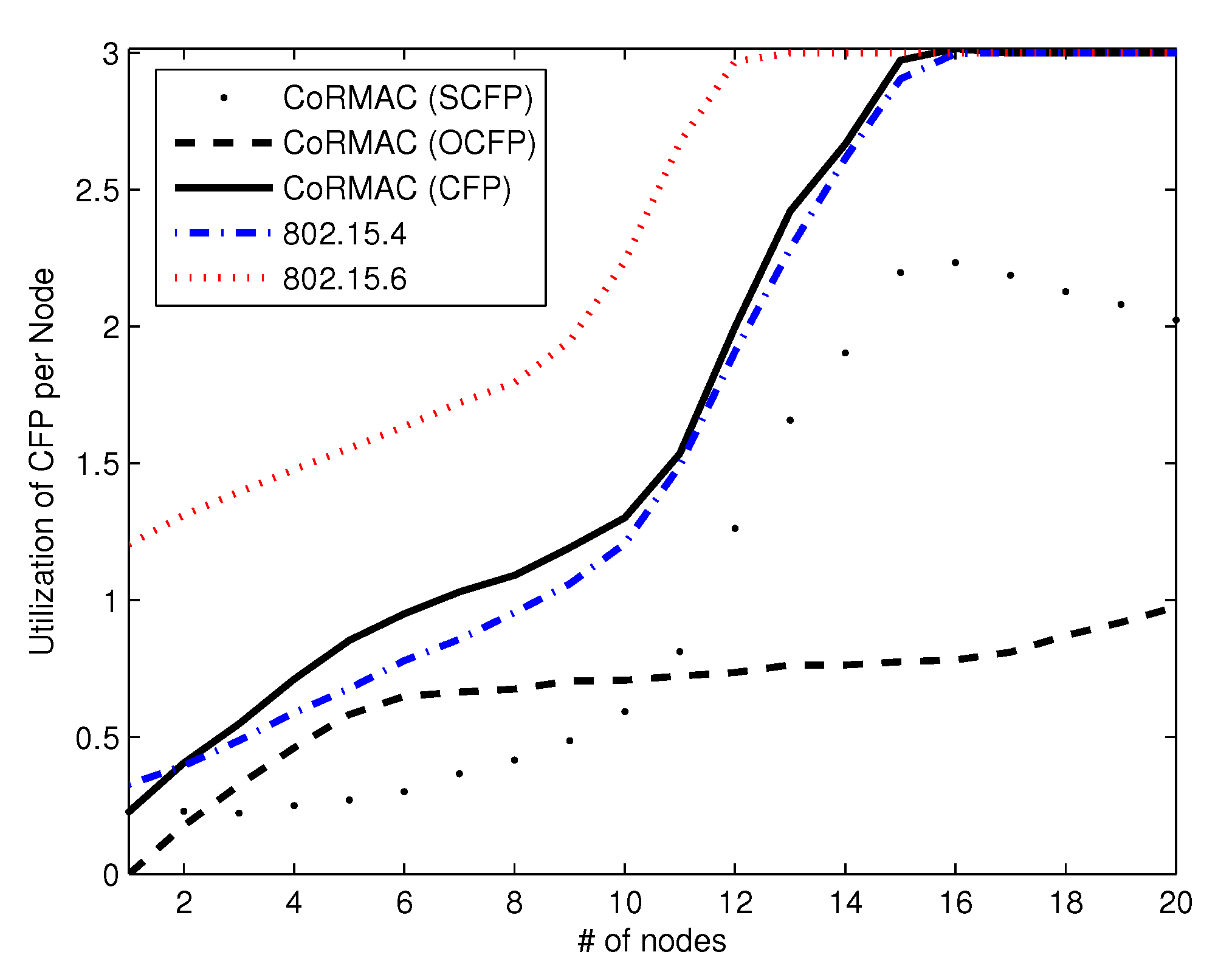
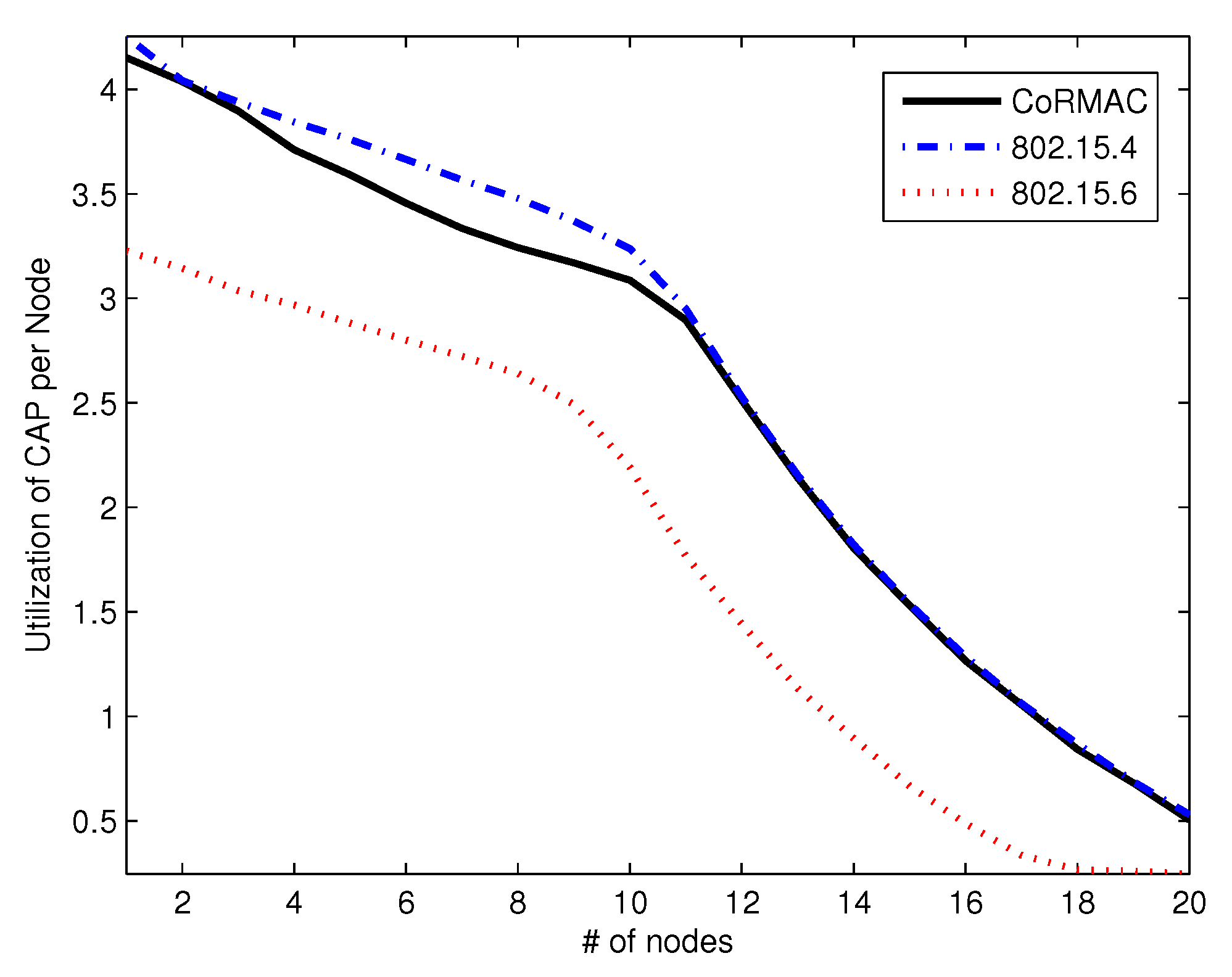
5.3. Utilization
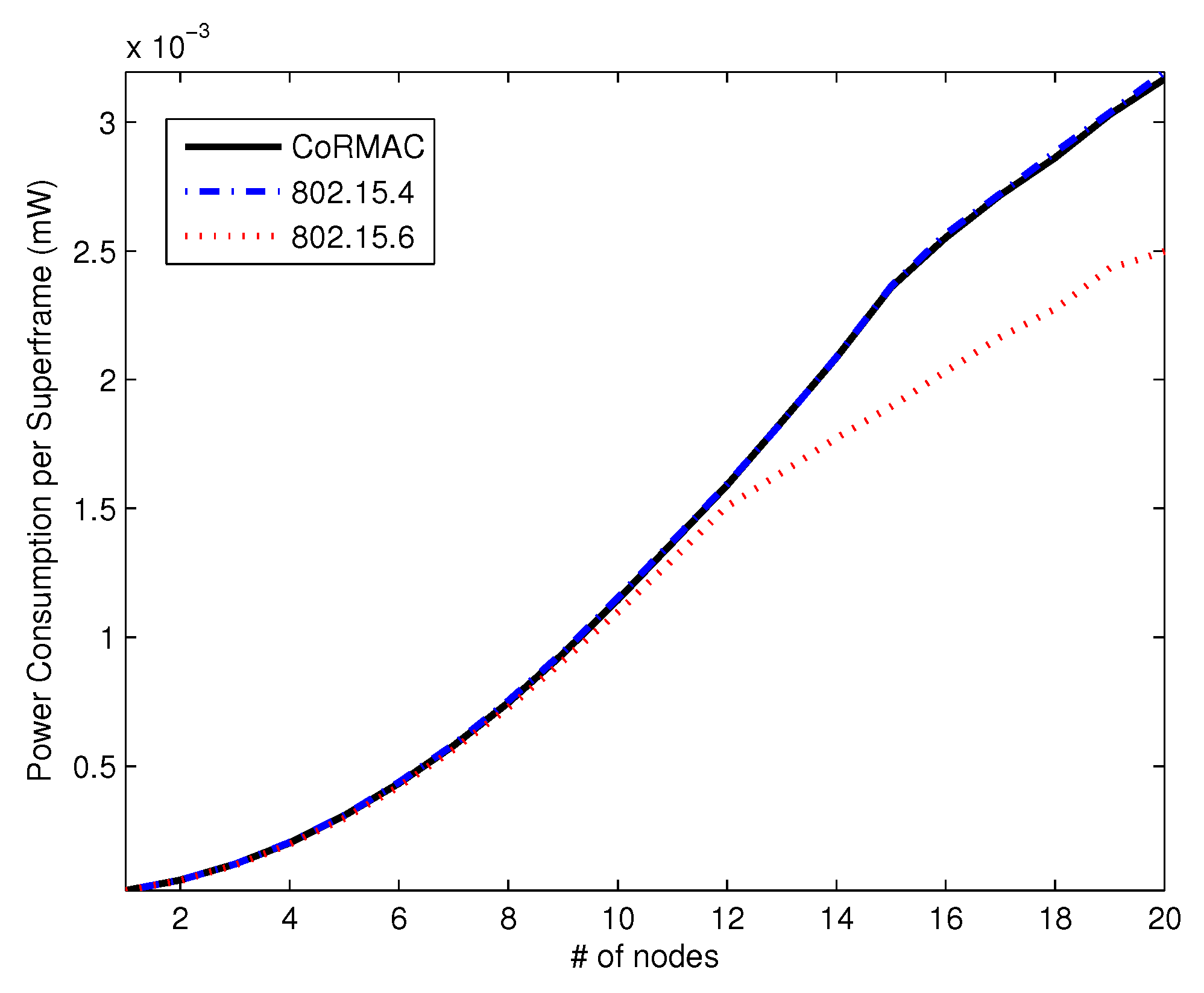
5.4. Power Consumption
6. Conclusions
Acknowledgments
Author Contributions
Conflicts of Interest
References
- Fang, X.; Hu, X.; Zhang, J.; Jiang, F.; Zhang, P. A Priority Mac Protocol for Ad hoc Networks with Multiple Channels. In Proceedings of the 2007 IEEE 18th International Symposium on Personal, Indoor and Mobile Radio Communications, Athens, Greece, 3–7 September 2007.
- He, R.; Fang, X. A Fair MAC Algorithm with Dynamic Priority for 802.11e WLANs. In Proceedings of the 2009 International Conference on Communication Software and Networks, Macau, China, 27–28 February 2009.
- Hoffmann, O.; Schaefer, F.-M.; Kays, R. Prioritized Medium Access in Ad-hoc Networks with a SystemClick Model of the IEEE 802.11n MAC. In Proceedings of the 21st Annual IEEE International Symposium on Personal, Indoor and Mobile Radio Communications, Instanbul, Turkey, 26–30 September 2010.
- Kim, H.; Min, S.G. Priority-based QoS MAC Protocol forWireless Sensor Networks. In Proceedings of the IPDPS IEEE International Symposium on Parallel and Distributed Processing, Rome, Italy, 23–29 May 2009.
- Li, M.; Prabhakaran, B. MAC Layer admission control and priority re-allocation for handling QoS guarantees in non-cooperative wireless LANs. J. ACM Mob. Netw. Appl. 2005, 10, 947–959. [Google Scholar] [CrossRef]
- Liu, G.; Chen, C.; Li, Y.; Guo, J. Priority-based Variable Multi-channel MAC Protocols in Cognitive Radio Wireless Networks: A Fair Channel Access Strategy. In Proceeding of the 2009 IEEE International Conference on Communications Technology and Applications, Beijing, China, 16–18 October 2009.
- Lee, C.; Lee, H.S.; Choi, S. An Enhanced MAC Protocol of IEEE 802.15.4 forWireless Body Area Networks. In Proceedings of the 2010 5th International Conference on Computer Science and Convergence Information Technology (ICCIT), Seoul, Korea, 30 November–2 December 2011.
- Luis, M.B.; Femando, J.V.; Antonio, S.L. Performance Evaluation of the Schedule Channel Polling MAC Protocol applied to Health Monitoring in the Context of IEEE 802.15.4. In Proceedings of the 2011 11th EuropeanWireless Conference—Sustainable Wireless Technologies (European Wireless), Vienna, Austria, 27–29 April 2011.
- Li, C.; Li, H.B.; Kohno, R. Performance Evaluation of IEEE 802.15.4 for Wireless Body Area Network (WBAN). In Proceedings of the 2009 IEEE International Conference on Communications Workshops, Dresden, Germany, 14–18 June 2009.
- Li, C.; Wang, L.; Li, J.; Zhen, B.; Li, H.B.; Kohno, R. Scalable and Robust Medium Access Control Protocol in Wireless Body Area Networks. In Proceedings of the 2009 IEEE 20th International Symposium on Personal, Indoor and Mobile Radio Communications, Tokyo, Japan, 13–16 September 2009.
- Sukor, M.; Ariffin, S.; Fisal, N.; Yusof, S.K.S.; Abdallah, A. Performance Study of Wireless Body Area Network in Medical Environment. In Proceedings of the 2008 Second Asia International Conference on Modelling and Simulation (AMS), Kuala Lumpur, Malaysia, 13–15 May 2008.
- Yang, J.; Yoon, Y. QoS of the BAN. Doc.: 15-07-0649-00-0ban. March 2007. Available online: https://mentor.ieee.org/802.15/dcn/07/15-07-0649-00-0ban-qos-ban.ppt (accessed on 14 May 2014).
- Cao, H.; Gonzalez-Valenzudla, S.; Leung, V.C.M. Employing IEEE 802.15.4 for Quality of Service Provisioning inWireless Body Area Sensor Networks. In Proceedings of the 2010 24th IEEE International Conference on Advanced Information Networking and Applications, Perth, WA, USA, 20–23 April 2010.
- Zhang, Y.; Dolmans, G.; Huang, L.; Huang, X. IMEC Narrowband MAC Proposal. Doc.: 15-09-0341-01-0006. May 2009. Available online: https://mentor.ieee.org/802.15/dcn/09/15-09-0341-01-0006-imec-narrowband-mac-proposal-presentation.pdf (accessed on 20 May 2014).
- Ali, K.A.; Sarker, J.H.; Mouftah, H.T. Urgency-based MAC Protocol for Wireless Sensor Body Area Networks. In Proceedings of the 2010 IEEE International Conference on Communications Workshops (ICC), Capetown, South Africa, 23–27 May 2010.
- Zhang, Y.; Dolmans, G. A New Priority-Guaranteed MAC Protocol for Emerging Body Area Networks. In Proceedings of the Fifth International Conference on Wireless and Mobile Communications (ICWMC), La Bocca, Cannes, France, 23–29 August 2009.
- Otal, B.; Alonso, L.; Verikoukis, C. Highly Reliable Energy-Saving MAC for Wireless Body Sensor Networks in Healthcare Systems. IEEE J. Sel. Areas Commun. 2009, 27, 553–565. [Google Scholar] [CrossRef]
- Li, C.; Li, J.; Zhen, B.; Li, H.B.; Kohno, R. Hybrid Unified-Slot Access Protocol for Wireless Body Area Networks. Int. J. Wirel. Inf. Netw. 2010, 17, 150–161. [Google Scholar] [CrossRef]
- Zhen, B.; Sung, G.; Li, H.B.; Kohno, R. NICT’s MAC proposal. Doc.: 15-09-0346-01-0006. November 2009. Available online: https://mentor.ieee.org/802.15/dcn/09/15-09-0346-01-0006-nict-s-mac-proposal.pdf (accessed on 11 February 2014).
- Yoon, J.S.; Ahn, S.G.; Seong, S.J.; Lee, M.J. PNP-MAC: Preemptive Slot Allocation and Non-Preemptive Transmission for Providing QoS in Body Area Networks. In Proceedings of the 2010 7th IEEE Consumer Communications and Networking Conference, Las Vegas, NV, USA, 9–12 January 2010.
- Zhou, G.; Lu, J.; Wan, C.Y.; Yarvis, M.D.; Stankovic, J.A. BodyQoS: Adaptive and Radio-Agnostic QoS for Body Sensor Networks. In Proceedings of the 27th Conference on Computer Communications, Phoenix, AZ, USA, 13–18 April 2008.
- IEEE Standard for Information Technology —Telecommunications and Information Exchange Between Systems - Local and Metropolitan Area Networks - Specific Requirements Part 11: Wireless LAN Medium Access Control (MAC) and Physical Layer (PHY) Specifications Amendment 8: Medium Access Control (MAC) Quality of Service Enhancements; IEEE Std 802.11e-2005 (Amendment to IEEE Std 802.11, 1999 Edition (Reaff 2003); IEEE: New York, NY, USA, 2005.
- IEEE Standard for Local and Metropolitan Area Networks—Part 15.6: Wireless Body Area Networks; IEEE Std 802.15.6-2012; IEEE: New York, NY, USA, 2012.
- IEEE Standard for Local and Metropolitan Area Networks—Part 15.4: Low-Rate Wireless Personal Area Networks (LR-WPANs); IEEE Std 802.15.4-2011 (Revision of IEEE Std 802.15.4-2006); IEEE: New York, NY, USA, 2011.
- OPNET, Application and Network Performance. Available online: http://www.opnet.com (accessed on 7 August 2011).



| Parameter | Value |
|---|---|
| N | Number of nodes |
| L | Number of slots in CAP |
| Probability of error or collision when the packet is transmitted | |
| Probability of winning a contention | |
| Arrival rate of urgent data | |
| Arrival rate of non-time critical data | |
| Length of the superframe period | |
| Length of the beacon period | |
| Length of the inactive period | |
| Transmission time in CAP | |
| Length of a CFP slot | |
| Length of a system time slot |
| Parameter | Value |
|---|---|
| Topology Size | 2 m × 0.5 m |
| Number of Sensor Node | 1–20 |
| Number of Coordinator | 1 |
| Arrival Rate of | 2 frames / |
| Urgent Data | s per node |
| Arrival Rate of | 20 frames / |
| Time-Critical Data | s per node |
| Arrival Rate of | 200 frames / |
| Non-Time-Critical Data | s per node |
| Superframe Period () | 20 ms |
| Beacon Period () | 450 μs |
| CFP Time Slot Length | 843.9 μs |
| Link Data Rate | 971.4 kbps |
| Beacon Frame Size | 128–400 bits |
| RTS Frame Size | 24 bits |
| CTS Frame Size | 24 bits |
| Data Frame Size | 192 bits |
| ACK Frame Size | 24 bits |
| System time slot | 5 μs |
| SIFS | 20 μs |
| MIFS | 75 μs |
| LIFS | 150 μs |
| Power Supply | 1.8 V |
| Power Consumption in Tx Mode | 8.5 mA |
| Power Consumption in Rx Mode | 7 mA |
| Power Consumption in | 1 μA |
| Inactive Mode |
| CoR-MAC | IEEE 802.15.4 | IEEE 802.15.6 | |
|---|---|---|---|
| Average Delay | 0.885 ms | 28.449 ms | 21.133 ms |
| Minimum Delay | 0.272 ms | 3.416 ms | 3.168 ms |
| Maximum Delay | 1.573 ms | 37.453 ms | 29.857 ms |
| Percentage over Deadline | 0% | 32.168% | 13.167% |
© 2016 by the authors; licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC-BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Yu, J.; Park, L.; Park, J.; Cho, S.; Keum, C. CoR-MAC: Contention over Reservation MAC Protocol for Time-Critical Services in Wireless Body Area Sensor Networks. Sensors 2016, 16, 656. https://doi.org/10.3390/s16050656
Yu J, Park L, Park J, Cho S, Keum C. CoR-MAC: Contention over Reservation MAC Protocol for Time-Critical Services in Wireless Body Area Sensor Networks. Sensors. 2016; 16(5):656. https://doi.org/10.3390/s16050656
Chicago/Turabian StyleYu, Jeongseok, Laihyuk Park, Junho Park, Sungrae Cho, and Changsup Keum. 2016. "CoR-MAC: Contention over Reservation MAC Protocol for Time-Critical Services in Wireless Body Area Sensor Networks" Sensors 16, no. 5: 656. https://doi.org/10.3390/s16050656
APA StyleYu, J., Park, L., Park, J., Cho, S., & Keum, C. (2016). CoR-MAC: Contention over Reservation MAC Protocol for Time-Critical Services in Wireless Body Area Sensor Networks. Sensors, 16(5), 656. https://doi.org/10.3390/s16050656







