Abstract
The Internet of Things (IoT) is a significant branch of the ongoing advances in the Internet and mobile communications. Yet, the use of a large number of IoT devices can severely worsen the spectrum scarcity problem. The usable spectrum resources are almost entirely occupied, and thus, the increasing demands of radio access from IoT devices cannot be met. To tackle this problem, the Cognitive Internet of Things (CIoT) has been proposed. In a CIoT network, secondary users, i.e., sensors and actuators, can access the licensed spectrum bands provided by licensed primary users (such as cellular telephones). Security is a major concern in CIoT networks. However, the traditional encryption method at upper layers (such as symmetric and asymmetric ciphers) may not be suitable for CIoT networks since these networks are composed of low-profile devices. In this paper, we address the security issues in spectrum-leasing-based CIoT networks using physical layer methods. Considering that the CIoT networks are cooperative in nature, we propose to employ cooperative jamming to achieve secure transmission. In our proposed cooperative jamming scheme, a certain secondary user is employed as the helper to harvest energy transmitted by the source and then uses the harvested energy to generate an artificial noise that jams the eavesdropper without interfering with the legitimate receivers. The goal is to minimize the Signal to Interference plus Noise Ratio (SINR) at the eavesdropper subject to the Quality of Service (QoS) constraints of the primary traffic and the secondary traffic. We formulate the minimization problem into a two-stage robust optimization problem based on the worst-case Channel State Information of the Eavesdropper (ECSI). By using Semi-Definite Programming (SDP), the optimal solutions of the transmit covariance matrices can be obtained. Moreover, in order to build an incentive mechanism for the secondary users, we propose an auction framework based on the cooperative jamming scheme. The proposed auction framework jointly formulates the helper selection and the corresponding energy allocation problems under the constraint of the eavesdropper's SINR. By adopting the Vickrey auction, truthfulness and individual rationality can be achieved. Simulation results demonstrate the effective performance of the cooperative jamming scheme and the auction framework.
1. Introduction
With the tremendous deployment of the Internet and mobile communications, the Internet of Things (IoT) emerges as a promising technology to connect billions of everyday objects and the surrounding environments using different kinds of sensors and actuators [1,2,3]. The use of a large number of IoT devices leads to a far more serious problem in terms of spectrum scarcity [4]. To solve this, a new paradigm termed the Cognitive Internet of Things (CIoT), which employs the cognitive radio technology in IoT networks, has been advocated [5,6,7]. Within a CIoT network, an unlicensed secondary user (an IoT device, such as a sensor or a actuator) is capable of operating on the licensed spectrum bands provided by a licensed primary user (such as a telephone). There are generally two types of CIoT networks: (1) spectrum-sensing-based CIoT networks [8] and (2) spectrum-leasing-based CIoT networks [9]. In the spectrum-sensing-based CIoT networks, spectrum sensing is an indispensable part. Yet, spectrum sensing may be inaccurate and leads to high power consumption [10]. Instead of employing spectrum sensing, in the spectrum-leasing-based CIoT networks, a secondary user may cooperatively assist a primary user to relay the primary signals; and in return, the primary user leases its spectrum and reserves a period of time for the secondary user to transmit its data. Moreover, if the secondary user is equipped with a multi-antenna, it can relay the primary signals while concurrently transmitting its own data.
Just like traditional wireless networks, security is one of the fundamental concerns in CIoT networks [11] (unless otherwise specified, the CIoT networks mentioned below refer to spectrum-leasing-based CIoT networks). The primary user has the requirement to prevent the eavesdropping attack (there are many different attack modes, such as denial-of-service (DoS) attacks, replay attacks and eavesdropping attacks; in this paper, we pay attention to the eavesdropping attack). In order to achieve secure transmission, physical (PHY) layer security, which exploits the characteristics of the radio spectrum to limit the amount of information extracted by eavesdroppers, has been proposed [12,13,14,15,16,17,18]. Compared to the traditional encryption methods in the upper layer, physical layer security has its advantages [19,20]. In CIoT networks with low-complexity devices, some issues are raised in upper layer security, such as key distribution for symmetric cryptosystems and the high computational complexity of asymmetric cryptosystems [21]. Different from upper layer security, physical layer security schemes enable secret communication without the aid of an encryption key. Meanwhile, the computational complexity of physical layer security schemes is low [19]. Moreover, all encryption methods are based on the assumption that it is computationally infeasible for the eavesdropper since the computing capacity of the eavesdropper is limited [22]. However, this assumption is not suitable due to the growth of computational power. For physical layer security, no limitations are assumed for the eavesdropper in terms of computational resources. For the above reasons, physical layer security is more suitable for CIoT networks. Considering that CIoT networks are cooperative networks, it is a logical idea to employ cooperation techniques in physical layer security to improve the security capability. One of the cooperation techniques is cooperative jamming, and it has been widely studied in other networks [16,17,18]. The main idea of cooperative jamming is to generate an artificial noise via multiple antennas on a cooperative helper (such as a secondary user) to confuse the eavesdropper.
However, these cooperative jamming schemes cannot be directly used in CIoT networks, since an incentive mechanism is lacking for the secondary user, which acts as the cooperative helper. As we all know, the secondary users and the primary users generally belong to different authorities [4]. For example, in the 802.22 standard [23], the secondary users that belong to the mobile phone operator can use the TV bands that are owned by the TV operator, if they cause no interference with the pay-TV subscribers (the primary users). Thus, it is unrealistic to assume that they would cooperate with each other unconditionally. To be more specific, as mentioned before, in CIoT networks, although a certain secondary user spends its own power to relay the primary signals, the secondary user gets the right to use the spectrum resource in return (the incentive mechanism of the relay node is out of the scope of this paper [27]). Additionally, for the secondary user, who acts as the helper, it uses its own power resource to jam the eavesdropper, while getting no return. On the other hand, a preferable strategy for a rational primary user is to pay less reward to the helper, while keeping a desired security capability. The problem of how to choose and negotiate with a suitable helper among multiple secondary users needs to be solved.
Bearing these challenges in mind, at first, we propose a novel cooperative jamming scheme to encourage the helper by employing energy harvesting technology [24]. In our scheme, the transmission is separated into two phases. In the first phase, a certain secondary user is arbitrarily assigned as the helper and harvests energy provided by a primary transmitter (here, we assume all of the secondary users (the IoT devices) have the energy transfer capability). In the second phase, the helper sends jamming signals to jam the eavesdropper using the energy harvested in the first phase. With the assistance of multiple antennas, the helper adjusts its transmit covariance matrix to jam the eavesdropper and simultaneously nulls out the interference at legitimate receivers. The transmit covariance matrix is an important parameter in multi-antenna-based networks. Suppose the signal vector sent by the helper is . Then, the transmit covariance matrix can be formulated as = . The goal of the proposed scheme is to deteriorate the signal to interference plus noise ratio (SINR) at the eavesdropper with quality of service (QoS) constraints on the SINR of the primary traffic and the secondary traffic. It is worth mentioning that most of the research in this area assumes that the transmitters can get the perfect Channel State Information of the Eavesdropper (referred to as ECSI) [25,26]. However, this assumption appears to be too ideal, because the eavesdropper, despite being a legitimate user, wishes to hide from the transmitter without being cooperative in the stage of channel estimation. Thus, only imperfect ECSI can be known. In this paper, we assume there exists channel mismatches for the eavesdropper links that are norm-bounded [28,29].
Based on this scheme, we propose a novel auction framework to solve the helper selection and the corresponding energy allocation problems. In the proposed auction framework, the primary user acts as the auctioneer, and the secondary users act as the bidders. The winning bidder is employed as the helper. Instead of bidding by virtual money, a nonmonetary bidding language is designed to let the users participate by a barter-like exchange. To be more specific, the primary user provides the power resource to the helper in exchange for a deteriorated SINR at the eavesdropper, and the secondary users compete for the power resource by cooperatively jamming the eavesdropper. The proposed framework guarantees an improved secure communication quality of the primary user, i.e., the degraded SINR at the eavesdropper, and stimulates the cooperative behavior of the helper. Finally, we evaluate the performance of our proposed jamming scheme and the auction framework via comprehensive simulation studies.
The rest of the paper is organized as follows. Section 2 discusses the related work. Section 3 presents the CIoT network model and describes its communication processes. The cooperative jamming scheme is detailed in Section 4. Section 5 describes the design of the auction framework. Section 6 evaluates the performance of the jamming scheme and the auction framework. Section 7 concludes the paper.
Notations: In this paper, the bold capital and lower-case letters are used to denote matrices and vectors, respectively. , , and denote the Hermitian transpose of a matrix, trace and the Euclidean norm, respectively. is the statistical expectation. denotes an identity matrix of corresponding dimension. and represent as an -dimension symmetric matrix and as an n-dimension positive semi-definite matrix, respectively.
2. Related Work
In this section, we summarize the related work under the categories of jamming schemes in physical layer security and auction frameworks in resource allocation.
2.1. Existing Work on Jamming in Physical Layer Security
Jamming is a common method to protect security in wireless networks. The authors in [12] first attempted to use artificial noise to degrade the eavesdropper’s channel, while this does not affect the channel of the intended receiver. Following this work, considerable research has investigated jamming with multiple antennas [13,14,15]. In these schemes, in addition to the information signal, part of the transmit power was allocated to send jamming signals. However, these approaches may be less effective in cooperative networks, since the cooperative characteristic in these networks is not effectively used. To enhance the security performance in cooperative networks, friendly helpers are employed to send jamming signals to confuse the eavesdropper [16,17,18]. This approach is often referred to as cooperative jamming. Cooperative jamming was initiated in [16]. The authors proposed a cooperative jamming scheme in the general Gaussian multiple access wire-tap channel and the Gaussian two-way wire-tap channel, where a non-transmitting user can help increase the secrecy capacity for a transmitting user by jamming the eavesdropper. Huang et al. [17] solved the physical layer security issue in relay networks by using cooperative jamming. To be more specific, the normally inactive node in the relay network was employed as the cooperative jamming source to confuse the eavesdropper. The closed-form jamming beamformers and the corresponding optimal power allocation of the employed node were derived in this work. Araujo et al. [18] introduced cooperative jamming in cognitive wireless sensor networks. Three scenarios were considered in this work: eavesdropper location known, eavesdropper location unknown and eavesdropper and relay co-location. The approach applied was similar to cooperative jamming [16].
Inspired by [16,17,18], we attempt to introduce cooperative jamming in CIoT networks. Note that these schemes are applied in the traditional wireless networks, and energy consumption is not considered as a design constraint. Nevertheless, for CIoT networks, energy consumption is of the utmost importance, since the CIoT devices are low-energy [30]. It is unrealistic to assume that the cooperative nodes would cooperate with each other unconditionally due to the limited energy resource. This literature cannot be directly used in CIoT networks, since an incentive mechanism is lacking to stimulate the CIoT devices. Zhang et al. [31] proposed an incentive mechanism in spectrum-leasing-based cognitive radio networks, whereby the primary user cooperates with two individual secondary users. In the scheme, these two secondary users act as a relay and a cooperative helper to improve the primary user’s secrecy. In return, the primary user allocates a fraction of access time for the secondary users’ transmission. Moreover, the case where the primary user cooperates with a cluster of secondary users to enhance the secrecy via collaborative beamforming was also considered. This inspiring work used the right of channel access as the reward. However, the helper node may not need to use the channel at the particular time slot. In addition, a simple case where each node is only equipped with one antenna was considered.
As mentioned before, in CIoT networks, the energy consumption is an important issue [30]. To solve it, energy harvesting technology has been introduced in CIoT networks [32,33,34]. Inspired by this, using energy as the reward for the helper in CIoT networks becomes a reality and may be a possible solution for the incentive mechanism. Xing et al. [35] first proposed a harvest-and-jam scheme, via which multi-antenna helpers harvest energy in the first transmission phase and jam the eavesdropper by consuming the harvested energy in the second transmission phase. In this literature, the helper candidates are deployed sufficiently close to the transmitter to reduce the power cost due to the relentless path loss. Moreover, the helper is randomly selected and uses all of the harvested energy to jam the eavesdropper. Thus, how to jointly select the cooperative helper and allocate the corresponding energy resource are still a whitespace in CIoT networks.
2.2. Existing Work on Auction
As we know, auction has been widely applied to resource allocation in wireless networks. Li et al. [36] proposed a spectrum-management framework based on auction theory to achieve a win-win situation for primary users and secondary users. Zou et al. [37] studied a power allocation scheme based on auction theory, in which the transmitting power is considered as the trading good. Wang et al. [38] considered the resource allocation problem for operational grids and networks under the constraint of a commercially-offered resource. With the purpose of avoiding misuse potentials, a trust-incentive-based combinatorial double auction algorithm was developed. The core idea of this paper is to adopt each peer’s trust values to adjust their bids. To challenge the monopoly of mobile termination charges, Tsiaras et al. [39] proposed an auction-based charging and user-centric system. The Vickrey auction was applied to guarantee honest bids that participants are forced to make. However, these research works assumes the use of monetary gains, i.e., virtual currency or credit to stimulate the participators in an auction. Thus, the method leads to problems in terms of money transaction and more complicated implementation. To solve this, the barter-like resource exchange-based auction framework has been put forward [40]. Of particular relevance to our work is [40], which addressed the physical layer security issue in spectrum-leasing-based cognitive radio networks by employing auction theory. The authors proposed a nonmonetary trading model, where the primary user creates the transmission opportunity for the secondary user, and the secondary user can choose to act as a relay or a helper to improve the secrecy rate of the primary user. Different from this inspiring work, our paper employs energy harvesting technology and uses energy as the payment to stimulate the helper.
3. System and Communication Models
As shown in Figure 1, our CIoT network is made up of two subnetworks. The primary network (a cellular network) consists of a primary transmitter-receiver pair (, ), while the secondary network (an IoT network) consists of a secondary transmitter-receiver pair (, ) and a secondary user that acts as a helper () (note that there exits a large number of CIoT devices in the secondary network; here, we only introduce three of them for clarity). intends to communicate with in the the presence of an eavesdropper (). Without loss of generality, we assume to employ to relay the primary traffic. , and are equipped with multiple antennas, while , and are legacy devices with a single antenna. The number of antennas of , and are denoted by , , and , respectively. Since we assume each node is half-duplex, the transmission in our model is separated into two phases. In the first phase, sends its information signals to while simultaneously transferring energy to . In the second phase, simultaneously forwards the information signals to and transmits its own signals to , respectively. Meanwhile, performs cooperative jamming using the respective harvested energy from the first transmission phase. Due to the distance constraint, similar to [42,43], we focus on the scenario that a direct transmission link cannot be set up between and , between and and between and . Note that in our network model, in a certain time slot, the channel provided by the primary user can only be occupied by one secondary transmitter-receiver pair. Thus, the interference caused by the helper cannot impact other devices. Similar to [44], in the following subsections, we expound the detailed procedure of these two phases.
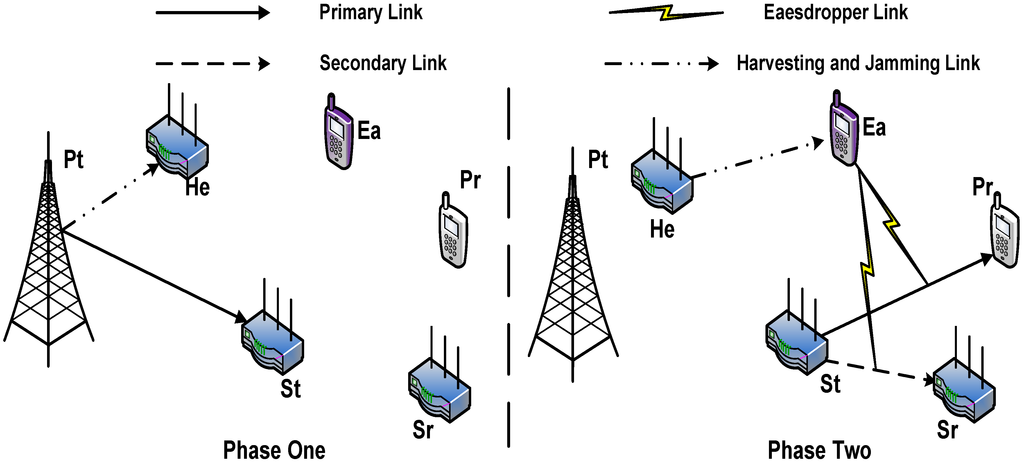
Figure 1.
System model.
3.1. Communication Process in Phase 1
In the first transmission phase, sends its information signals to while simultaneously transferring energy to . The signals received at and can be expressed as:
where denotes the information signals sent by . We express the power allocation of as , where is the transmit power constraint on . and are modeled as zero mean additive white Gaussian noise (AWGN) with variances of ; and represent the channel coefficient vectors from to and from to , respectively.
On the other hand, for the wireless power transfer, the harvested energy of is given by:
where denotes the energy harvesting efficiency of .
3.2. Communication Process in Phase 2
We assume employs the decode-and-forward (DF) protocol due to its simplicity of presentation. In the second transmission phase, simultaneously forwards the information signals to and transmits its own signals to . In the same time, transmits jamming signals to jam . The signals received at , and can be written as:
Without ambiguity, the primary signals are still denoted by . and represent the secondary signals sent by and the jamming signals sent by , respectively. The transmit covariance matrices of and are written as =, = and =, respectively. The power constraints are denoted by , and , respectively. , and represent the noises at , and , respectively; and () refers to the channel coefficient matrix/vector from node i to node j, where and . As previously mentioned, in this paper, we consider the case when only imperfect ECSI can be known. We propose to use a norm-bounded model to characterize the uncertainties of ECSI, such that:
where and are the estimates of the corresponding channels; and are their respective channel errors. Here, we assume that the channel errors consist of the norm-bounded sets and , where and are known constants.
To remove the interference caused by jamming signals, as well as primary signals, since is equipped with multiple antennas, we can deliberately design a decoding vector to decode the secondary signals at , by letting:
Therefore, the secondary signals received at can be formulated as:
As for the signals received at , since has only one antenna, it does not have the capability to apply the decoding vector. To remove the undesirable interference at , we propose to use zero-forcing (ZF) (which has been widely used in multi-antenna-based networks [45]) at and , since these two transmitters are equipped with multiple antennas. We can deliberately design the transmit covariance matrices by setting and . Then, the received primary signals at can be written as:
A detailed derivation of , and will be given in the next section. In summary, we meticulously describe the two communication processes in our CIoT network model in this section. One can see that the undesirable interference caused by is successfully removed. Furthermore, both the primary signals and the secondary signals can be perfectly received at and , respectively.
4. Proposed Cooperative Jamming Scheme
In this section, we aim to deteriorate the SINR at with QoS constraints of the primary traffic and the secondary traffic by designing the transmit covariance matrices, i.e., , and (note that, in the scheme, we assume uses all of the harvested energy to jam ; helper selection and the corresponding energy allocation problems will be solved in the next section). We formulate this problem into a two-stage robust optimization problem and use semi-definite programming (SDP) methods to solve it.
4.1. Problem Formulation
The SINR at can be written as:
The constraints on the SINR of and can be simply presented as:
where and represent the SINR of and , respectively.
Now, we focus on obtaining robust transmit covariance matrices based on the worst-case ECSI. Additionally, the problem of minimizing the SINR at can be formulated as:
where Equations (19) and (20) imply the ZF constraints to null out the secondary signals and the jamming signals at , respectively, and Equation (21) indicates that consumes all of the energy harvested in the first phase to jam in the second phase. We will study how to solve this problem in the next subsection.
4.2. Proposed Solutions
This optimization problem consists of a linear fractional objective function and a set of affine inequalities and equalities. Thus, it is a quasi-convex problem, which is hard to solve. In this paper, we relax some constraints and reformulate this problem into a two-stage optimization problem.
4.2.1. The First Stage
In the first stage, first, we make a relaxation of Equation (18) by setting:
Then, we aim to minimize the part that is related to in Equation (13). Additionally, we have:
Proposition 1.
Problem Equations (23)–(25) are equivalent to the following problem, which is given by:
Proof.
We first transform problem Equations (23)–(25) into:
This problem is still intractable to solve since Equation (35) consists of infinite constraints. To tackle this problem, we introduce the S-procedure method to turn these constraints into linear matrix inequalities (LMIs) [46].
Lemma 1:
(S-procedure) Suppose and are n-dimensional symmetric matrices, denoted by and . Additionally, there exists a vector satisfying . Then, the implication holds if and only if there exists a , such that:
The constraint Equation (32) can also be expressed as:
By letting , , we reformulate Equation (37) as:
A similar method can be used to rewrite Equation (35), and it can be given by:
According to Lemma 1, let and ; Equations (38) and (39) hold if and only if there exists a , such that:
Letting , where , problem Equations (23)–(25) can be rewritten as:
which completes the proof.
Problem Equations (41)–(45) are an SDP problem, which consists of a linear objective function together with some LMI constraints. Thus, one can employ software packages, such as SeDuMi [47], to get the optimal solution of .
As for the part related to , we also make a relaxation of Equation (17) by setting:
Additionally, we have:
Proposition 2.
Problem Equations (47) and (48) are equivalent to the following problem, which is given by:
Proof.
The proof is similar to the proof for Proposition 1, and the details are omitted here.
4.2.2. The Second Stage
In the second stage, we aim to maximize the denominator of Equation (13) to get the optimal solution of . We can formulate this problem as:
Proposition 3.
Problem Equations (53)–(55) are equivalent to:
where .
Proof.
The proof follows a similar procedure as that for Proposition 1 and is omitted.
In summary, the optimal solutions of , and can be obtained by the aforementioned two stages. Note that and do not directly appear in these optimization problems. The `hidden’ worst-case of and can be obtained by using Lagrange duality, and the derivation process is omitted here. A similar approach can be found in [28].
Furthermore, note that we relax the SINR constraints of the primary traffic and the secondary traffic, as shown in Equations (22) and (46). We have the following proposition.
Proposition 4.
The optimum of problem Equations (16)–(21) are achieved when Equations (22) and (46) hold.
Proof.
First, for given optimal solutions of , and , let , and , where , and are normalized as , and , respectively. Therefore, problem Equations (16)–(21) with respect to , and can be written as:
It can be easily found that if we enhance the SINR of the primary traffic, should be raised, which leads to an undesired increment of ’s SINR. Additionally, so is the SINR of the secondary traffic.
4.3. An Illustrative Example
To promote better understanding of the proposed jamming scheme, as shown in Figure 2, we take a simple case with a relay and a helper . With the purpose of deteriorating the SINR at , should choose optimal solutions of and . The optimal solution of can be obtained by Equations (23)–(25). Similarly, the optimal solution of can be obtained by Equations (47) and (48). As for , it should choose the optimal solution of , and this optimal solution can be obtained by Equations (53)–(55). Using the optimal solutions of , and , the minimum SINR at can be obtained by Equation (13).
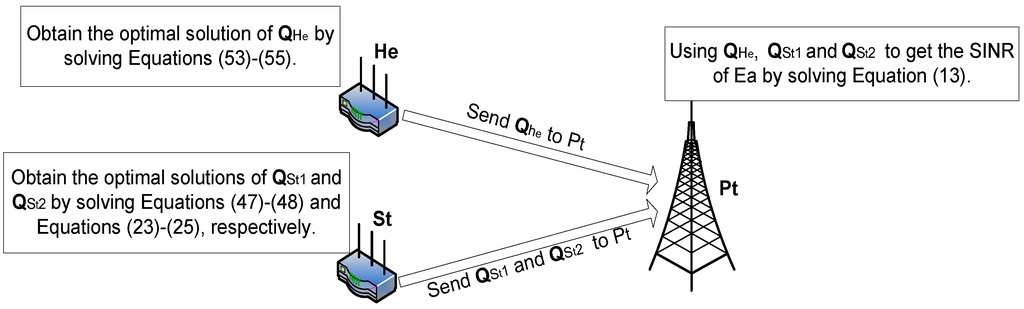
Figure 2.
Illustrative example.
5. Proposed Auction Framework
In CIoT networks, the primary user and the secondary users will cooperate with each other if their own interests can be met. The primary user wants to choose an optimal helper among multiple secondary users and provides the least amount of energy under a desired degraded SINR at . On the other hand, the helper candidates (secondary users) want to get the most amount of energy by cooperatively jamming . In this paper, we adopt the Vickrey auction [48] to solve the helper selection and corresponding energy allocation problems based on the proposed jamming scheme. In the Vickrey auction, the bidder that submits the lowest bid wins the auction, but pays a price equal to the second-lowest amount bid. Note that if there are more than one lowest bidders, one of them is randomly selected as the winner and pays its own bid (not the second-lowest bid). Unlike some research [36,37,38,39] in this area that assumes to use monetary gains (fictitious currency) to stimulate the participators in an auction, we design a nonmonetary bidding language by a barter-like exchange with the purpose of avoiding the problems associated with money transactions and facilitating the implementation. We choose to adopt the Vickrey auction due to the following two reasons [49]:
- The Vickrey auction guarantees truthfulness. As we know, truthfulness means that for each bidder, reporting true optimal demand is the best strategy regardless of how the other bidders bid. Additionally, it is the critical property for an auction.
- The Vickrey auction is individual rational. Individual rationality means that the utilities of the auctioneer and the winner bidder are always positive. Achieving individual rationality ensures that both the primary user and the secondary users have incentives to participate in the auction.
5.1. Mathematical Definitions
In this subsection, the mathematical definitions of the proposed auction framework are presented as follows.
- Auctioneer: primary user .
- Bidder: , where is the set of secondary users with size N.
- Characteristic of bidders: , where denotes the characteristic of bidder .
- Valuation of bidder : ’s valuation can be formulated as:where denotes the SINR at and denotes the expected SINR at . is the energy that has to provide to to achieve the expected SINR at .
- Bidding of bidders: , where denotes the bidding of bidder . is related to its individual valuation .
- Strategy of bidders: Φ, where describes a strategy of bidder .
- Utility of bidder : , where and denote the vectors of strategies and characteristics of the bidders, except , respectively.
5.2. Strategy of Bidders
In this subsection, we attempt to investigate the optimal strategies of bidders. For the Vickrey auction, a dominant strategy equilibrium should be achieved to guarantee the system outcome. The definition of the dominant strategy equilibrium is given as follows [49].
Definition 1.
The strategy achieves the dominant strategy equilibrium, if for every , there exists:
As mentioned before, the Vickrey auction guarantees truthfulness, which means that the dominant strategy equilibrium of every bidder is to bid truthfully. Then, we have the following proposition.
Proposition 5.
In a Vickrey auction, is the only dominant strategy equilibrium.
Proof.
Consider bids its true value as . Here, we assume is the winning bid and is the second-lowest bid offered by . According to the Vickrey auction, pays the second-lowest bid for the winning bidder. Therefore, the utility function of is:
here denotes the reserve price of . The reserve price means the upper limit of energy that can pay.
- (1)
- , and wins the auction; one can find that the utility of would be unaffected with an unchanged . Thus, the strategy of making a false bidding cannot improve the bidder’s utility.
- (2)
- , and loses the auction; under this circumstance, the utility of equals zero.
To sum up, is the only dominant strategy for bidder i, which completes the proof.
For bidder i, in order to get its true valuation, it has to calculate the energy . The required energy of for jamming to achieve can be obtained by solving the following problem:
Note that in Equation (66), and are constants, since and have been solved in Section 4.2.1. Problem Equations (64)–(66) can be solved using the same approach as problem Equations (53)–(55). Then, the energy that provides to , i.e., can be formulated as:
Besides, one can find that the value of the utility function of the winning bidder is always non-negative. Thus, the individual rationality is always achieved for the secondary users. As for the primary user, the utility function can be written as:
where denotes the SINR at without cooperative jamming. This utility function is always non-negative, which implies the individual rationality of the primary user.
5.3. Implementation Details
In this subsection, the implementation of the proposed auction is detailed. Similar to [17,40,41], we assume there exists a common control channel (CCCH) for users to exchange the control information. To be more specific, the transmitter broadcasts common information (some low-rate control or channel state information) via the CCCH. The eavesdropper can also get the control information. However, the message the eavesdropper is interested in is the confidential message sent to the destination. At the beginning of the auction, decides an expected SINR at and calculates and according to Equations (47) and (48) and Equations (23)–(25), respectively. Then, broadcasts an eager-to-help (ETH) frame, which is used to notify the secondary users that the primary user initiates an auction to employ a helper for cooperative jamming. In the ETH frame, , and are attached.
Once the ETH frame is received, the secondary users try to participate in the auction by bidding based on their true valuations. Each secondary user calculates its bid by using Equations (64)–(67). Then, the secondary user sends an able-to-help (ATH) frame to containing the bidding value (to avoid collision, the frame should be sent after a random backoff value t).
waits for a T time duration for secondary users’ responses. If no ATH frame is received, considers that no secondary user is available to fulfill its demand. Otherwise, selects the secondary user with the lowest bid as the winning bidder and pays the winning bidder with the second-lowest bid. The lowest bid proposed by the winning bidder indicates that the channel condition between the winner and is good enough. As expected, this will lead to a smaller energy cost at . Note that if only one ATH frame is received, chooses the corresponding bidder as the winning bidder and pays the winning bidder with . After choosing the winning bidder, broads a ready-to-send (RTS) frame to the secondary users. In the RTS frame, the identity of the winning bidder and the payment results are attached.
6. Simulation Study
In this section, we provide some simulation results on the performance of the proposed jamming scheme and the proposed auction framework.
As described in Section 3, , and are all equipped with a single antenna, while the numbers of antennas of , and are assumed to be four. We assume that all of the entries in channel coefficient vectors/matrices are independent complex Gaussian random variables with zero mean and unit variance. The power of background noise at all receivers, i.e., , , and , is assumed to be the same and normalized as , and the transmit power of is defined in dB with respect to the noise power. Unless otherwise specified, the channel uncertainties are assumed to be and ; the SINR of the primary traffic and the secondary traffic are set to be 10 dB and 10 dB; and the energy harvesting efficiency is given by .
6.1. Simulation Study of the Proposed Jamming Scheme
We will examine the performance of the proposed jamming scheme under two scenarios: (i) an eavesdropper can only wiretap the primary signal; (ii) a more powerful eavesdropper can wiretap both the primary and the secondary signals. These two scenarios are referred to as Scenario One and Scenario Two, respectively. For the purpose of demonstrating that the proposed jamming scheme can dramatically deteriorate the SINR at , we also examine the scheme without jamming in these two scenarios. We will give particular simulations of the performance of the proposed cooperative jamming scheme under the power constraint of , the channel error bounds and the coefficient of energy harvesting efficiency, respectively.
Figure 3 shows the SINR at as a function of ’s transmit power. One can notice that the proposed jamming scheme can definitely deteriorate the SINR at compared to the case with no jamming in Scenario One and Scenario Two. This is due to the fact that the performance of the no jamming scheme is degraded not only by the channel error between and , but also by that between and . What is more, it can be observed that when the transmit power of increases, the SINR at tends to be worse. This can be explained as with the increase of ’s transmit power, more transmit power can be harvested by , which can in turn be used to enhance the jamming effect. It is obvious that there is a trade-off between the transmit power and the security capability. With careful planning and execution, a desired SINR at can be obtained using as little transmit power as possible. In addition, the SINR at in Scenario One is worse than Scenario Two. This is reasonable since in Scenario Two, also has the interest to steal transmitted information of the secondary traffic.
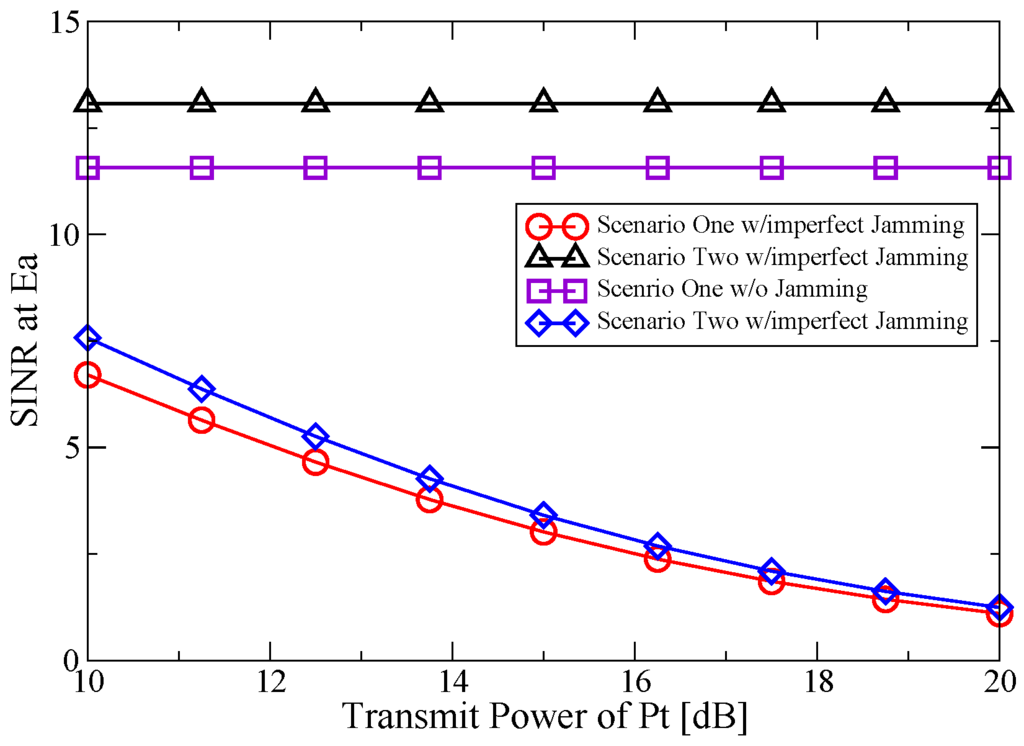
Figure 3.
SINR at Ea vs. transmit power of Pt.
In Figure 4, the SINR at versus the channel uncertainty is plotted by assuming dB and . It can be seen that when the channel uncertainties are zero, the SINR at is very low in the two scenarios. In this case, the proposed robust jamming scheme is not necessary. However, the SINR at will increase with rising and . This can be understood by the fact that the increase of the channel uncertainties implies worse channel conditions between and , and , which leads to a reduction of the jamming performance. The robustness of the proposed jamming scheme is more obvious, and it can enhance the security capability compared to the no jamming case.
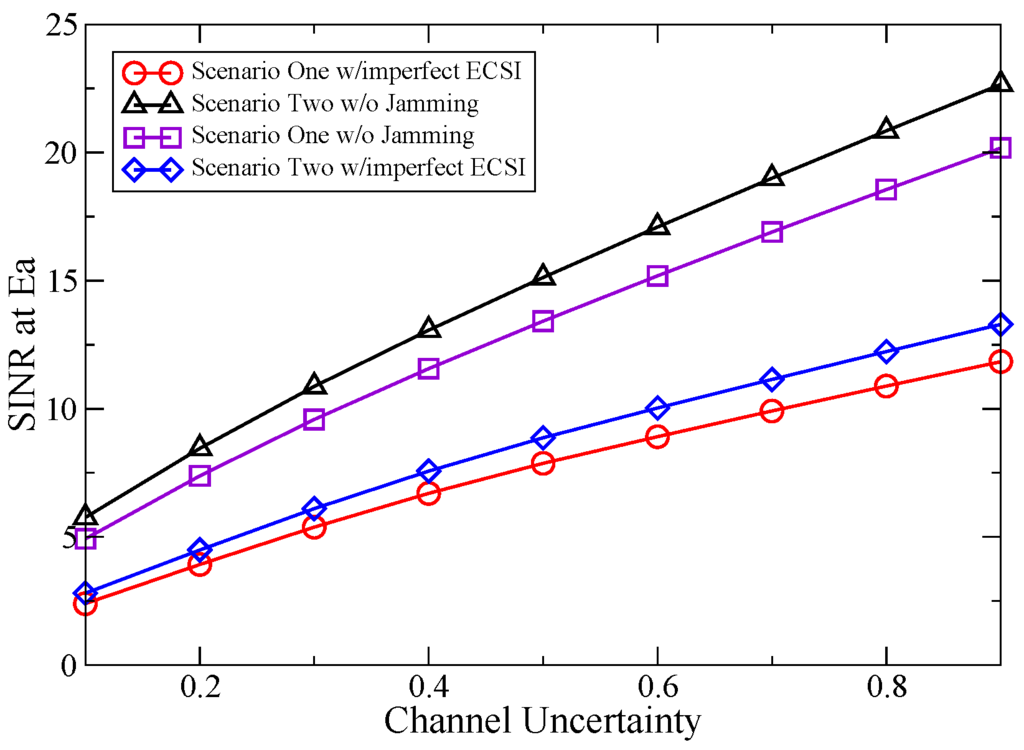
Figure 4.
SINR at Ea vs. channel uncertainty.
The impact of the energy harvesting efficiency on the SINR at Ea is presented in Figure 5. As shown in Figure 5, the security capability is greatly influenced by the energy harvesting efficiency. With the increase of the energy harvesting efficiency, more transmit power can be seized by , which leads to a more effective performance. Note that the conversion efficiency is not enough in the experimental measurement [50], resulting in a high power cost at . However, with the improvement of hardware, the conversion efficiency is expected to be increased in the near future. One can also find that the increase of the energy harvesting efficiency leads to a smaller gap between Scenario One and Scenario Two in the proposed jamming scheme. The reason is that a stronger jamming signal reduces the impact of the secondary traffic that is eavesdropped by .
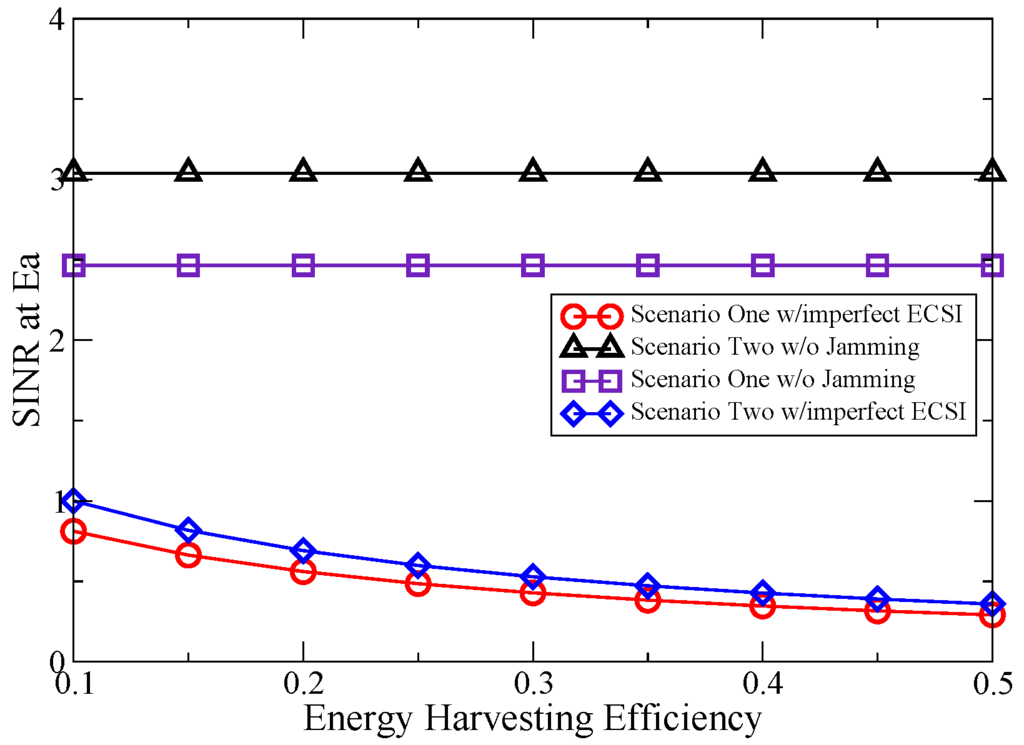
Figure 5.
SINR at Ea vs. energy harvesting efficiency.
6.2. Simulation Study of the Proposed Auction Framework
Figure 6 shows the utility value of the winning bidder as a function of the expected SINR at . It is obvious that the utility value of the winning bidder is positive. This result is expected and confirms the theoretical analysis in Section 5.2. Additionally, a large number of secondary users leads to a smaller utility of the winning bidder. This can be explained as with the increased number of secondary users, the second-lowest bid is more likely to be close to the lowest bid. Furthermore, one can find that a smaller expected SINR at leads to an increase of the utility of the winning bidder. This is because the primary user needs to spend more energy to fulfill its stringent requirement of ’s SINR. On the other hand, as can be seen in Figure 6, a higher expected SINR at may cause a no-winner result, regardless of the number of secondary users. In other words, the utility value of the winning bidder tends to be zero. This is because the second-lowest bid is more likely to be close to the lowest bid (winning bid) under a low standard requirement.
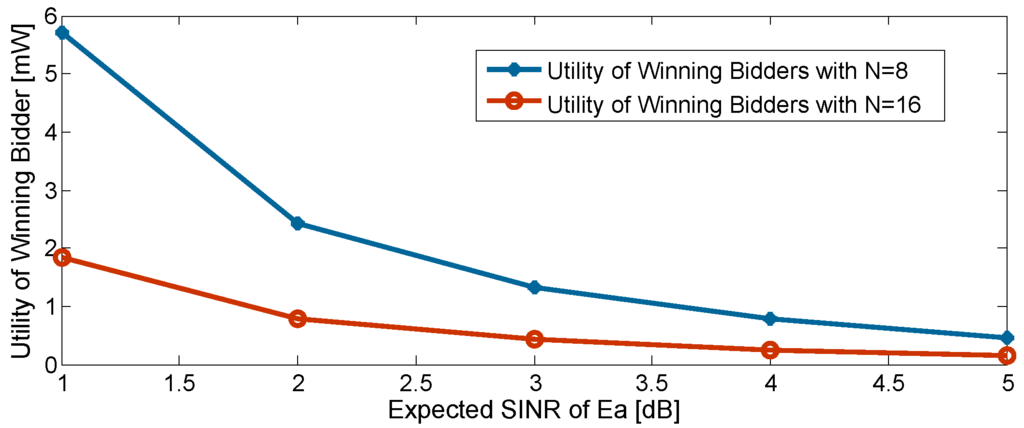
Figure 6.
Utility of winning bidder vs. expected SINR at Ea.
Figure 7 reports the impacts of the channel uncertainty and the energy harvest efficiency on the utility of winning bidder. The expected SINR at is set to be 0 dB. The utility is observed to be increased under a lower energy harvest efficiency and a bigger channel uncertainty. In the case of low energy harvest efficiency, the secondary users require more energy provided by . With different channel conditions, the lowest bid is more likely to be far from the second-lowest bid. Additionally, so is the large channel uncertainty. Note that the utility of the winning bidder also reduces as the number of the secondary users increases. This can be understood by the fact that as the number of bidders rises, the gap narrows between the second lowest bid and the lowest bid (winning bid).
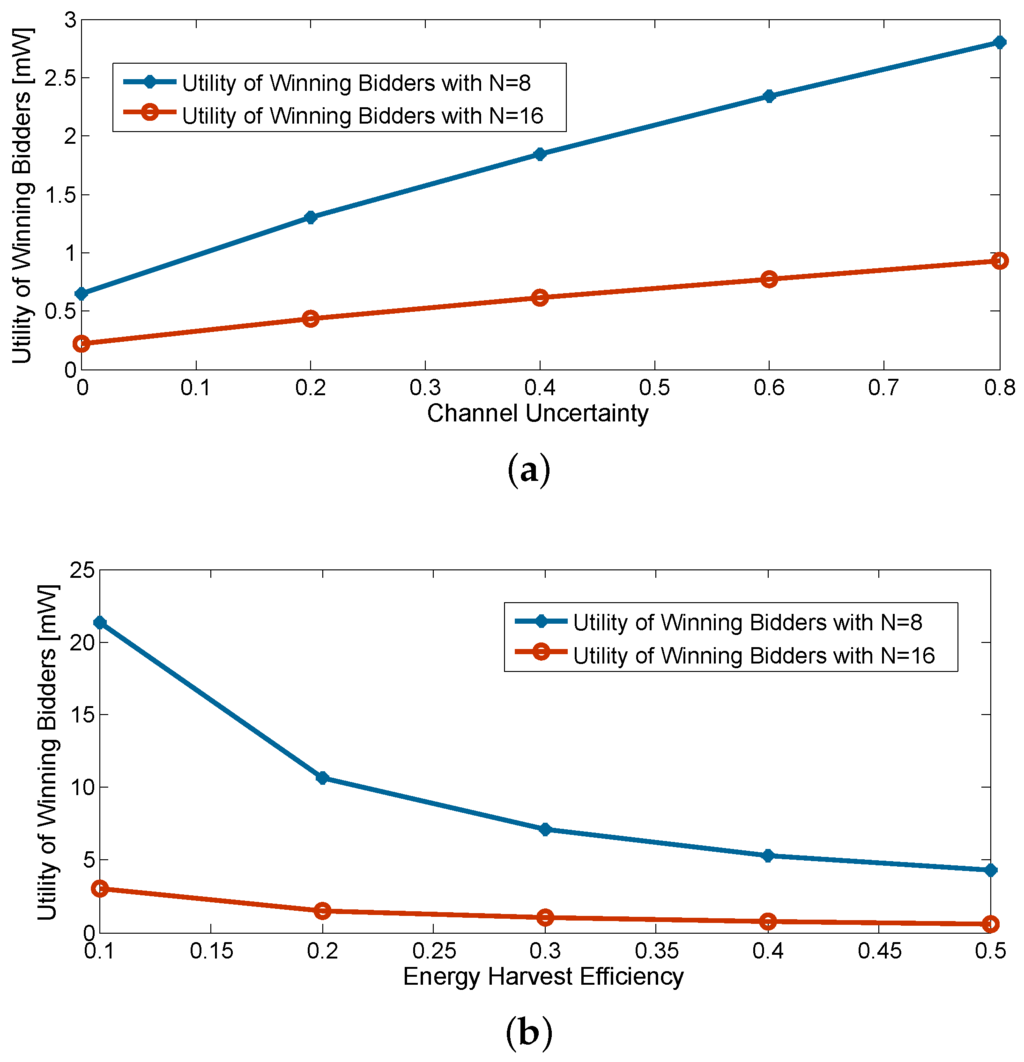
Figure 7.
Impacts of channel uncertainty and energy harvest efficiency. (a) Utility of winning bidder vs. channel uncertainty; (b) utility of winning bidder vs. energy harvest efficiency.
7. Summary and Future Work
This paper addresses the physical layer security issue in CIoT networks by employing cooperative jamming. Firstly, we propose a novel cooperative jamming scheme, in which a secondary user is arbitrarily assigned as the helper to confound the eavesdropper by sending jamming signals. The required energy is harvested from the primary transmitter. The covariance matrix of the helper, as well as the covariance matrices of the relay are optimized to minimize the SINR at the eavesdropper subject to the QoS constraints of the primary traffic and the secondary traffic. Those problems are formulated as a two-stage robust optimization problem and solved by semi-definite programming. Next, we propose to use the Vickrey auction to solve the helper selection and the corresponding energy allocation problems based on the proposed jamming scheme. The goal of the auction framework is to encourage the secondary users to jam the eavesdropper. By investigating the strategy of the secondary user, we prove the truthfulness and individual rationality of the proposed auction framework. We evaluate the performance of the proposed jamming scheme and the auction framework. The evaluation results demonstrate that the SINR at the eavesdropper is remarkably deteriorated. Meanwhile, the helper can be effectively stimulated.
As we know, the IoT device has the characteristics of limited hardware, low-complexity and severe energy constraints. In this paper, the deteriorated SINR at the eavesdropper is achieved at the expense of employing multiple antennas. In future work, we plan to study the trade-off between the security performance and the number of antennas in order to use the smallest number of antennas under a desired security performance. Furthermore, in this paper, the helper node is capable of receiving the confidential information. If the helper is a malicious node, the system security will be severely threatened. The problem of the untrusted helper node should be seriously considered. Finally, it should also be noted that the good performance of the proposed auction framework is achieved at the expense of large time complexity. To reduce the delay time, in future work, we plan to use the optimal stopping theory to design a new helper selection scheme.
Acknowledgments
The authors would like to thank the support from the Science Foundation of Beijing Jiaotong University 2015YJS019.
Author Contributions
Zhen Li conceived of and designed the cooperative jamming scheme and the auction framework. Yan Huo and Jin Qian designed the simulations and analyzed the data. Liran Ma supported the theory background and revised the paper. Tao Jing supported and supervised the research. All of the authors participated in the project, and they read and approved the final manuscript.
Conflicts of Interest
The authors declare no conflict of interest.
References
- Perera, C.; Zaslavsky, A.; Christen, P.; Georgakopoulos, D. Context Aware Computing for The Internet of Things: A Survey. IEEE Commun. Surv. Tutor. 2014, 16, 414–454. [Google Scholar] [CrossRef]
- Atzori, L.; Iera, A.; Morabito, G. The Internet of Things: A survey. Comput. Netw. 2010, 54, 2787–2805. [Google Scholar] [CrossRef]
- Jara, A.J.; Belchi, F.J.; Alcolea, A.F.; Santa, J.; Zamora-Izquierdo, M.A.; Gomez-Skarmeta, A.F. A Pharmaceutical Intelligent Information System to detect allergies and Adverse Drugs Reactions based on Internet of Things. In Proceedings of the IEEE Pervasive Computing and Communications Workshops, Mannheim, Germany, 29 March–2 April 2010; pp. 809–812.
- Afzal, A.; Zaidi, S.A.R.; Shakir, M.Z.; Imran, M.A.; Ghogho, M.; Vasilakos, A.V.; McLernon, D.C.; Qaraqe, K. The Cognitive Internet of Things: A Unified Perspective. Mob. Netw. Appl. 2015, 20, 72–85. [Google Scholar] [CrossRef]
- Massouri, A.; Cardoso, L.; Guillon, B.; Hutu, F.; Villemaud, G.; Risset, T.; Gorce, J.-M. CorteXlab: An open FPGA-based facility for testing SDR And cognitive radio networks in a reproducible environment. In Proceedings of the IEEE Conference on Computer Communications Workshops (INFOCOM WKSHPS), Toronto, ON, Canada, 27 April–2 May 2014; pp. 103–104.
- Wu, Q.H.; Ding, G.R.; Xu, Y.H.; Feng, S.; Du, Z.Y.; Wang, J.L.; Long, K.P. Cognitive Internet of Things: A New Paradigm Beyond Connection. IEEE Internet Things J. 2014, 1, 129–143. [Google Scholar] [CrossRef]
- Shah, M.A.; Zhang, S.J.; Maple, C. Cognitive radio networks for Internet of Things: Applications, challenges and future. In Proceedings of the 19th International Conference on Automation and Computing, London, UK, 13–14 September 2013; pp. 1–6.
- Aijaz, A.; Aghvami, A.H. Cognitive Machine-to-Machine Communications for Internet-of-Things: A Protocol Stack Perspective. IEEE Internet Things J. 2015, 2, 103–112. [Google Scholar] [CrossRef]
- Zhang, B.; Chen, K. Selective spectrum leasing in Internet of Things via Nash Bargaining Solutions. In Proceedings of the IEEE 2nd International Conference on Cloud Computing and Intelligent Systems, Hangzhou, China, 30 October–1 November 2012; pp. 841–845.
- Zhang, N.; Lu, N.; Cheng, N.; Mark, J.W.; Shen, X.M. Cooperative networking towards secure communications for CRNs. In Proceedings of the IEEE Wireless Communications and Networking Conference (WCNC), Shanghai, China, 7–10 April 2013; pp. 1691–1696.
- Kim, S. Cognitive Radio Anti-Jamming Scheme for Security Provisioning IoT Communications. KSII Trans. Internet Inf. Syst. 2015, 9, 4177–4190. [Google Scholar]
- Negi, R.; Goel, S. Secret communication using artificial noise. In Proceedings of the 2005 IEEE 62nd Vehicular Technology Conference, Dallas, TX, USA, 25–28 September 2005; pp. 1906–1910.
- Khisti, A.; Wornell, G.; Wiesel, A.; Eldar, Y. On the Gaussian MIMO Wiretap Channel. In Proceedings of the IEEE International Symposium on Information Theory, Nice, France, 24–29 June 2007; Volume 3, pp. 1906–1910.
- Swindlehurst, A.L. Fixed SINR solutions for the MIMO wiretap channel. In Proceedings of the IEEE International Conference on Acoustics, Speech and Signal Processing, Taipei, Taiwan, 19–24 April 2009; pp. 2437–2440.
- Mukherjee, A.; Swindlehurst, A.L. Robust Beamforming for Security in MIMO Wiretap Channels with Imperfect CSI. IEEE Trans. Signal Process. 2011, 59, 1906–1910. [Google Scholar] [CrossRef]
- Tekin, E.; Yener, A. The general Gaussian multiple Access and two-way Wire-tap channels. IEEE Trans. Inf. Theory 2010, 56, 4762–4763. [Google Scholar] [CrossRef]
- Huang, J.; Swindlehurst, A.L. Cooperative Jamming for Secure Communications in MIMO Relay Networks. IEEE Trans. Signal Process 2011, 59, 4871–4884. [Google Scholar] [CrossRef]
- Araujo, A.; Blesa, J.; Romero, E.; Nieto-Taladriz, O. Co-operative jam technique to increase physical-layer security in CWSN. In Proceedings of the 2nd International Conference on Advances in Cognitive Radio COCORA 2012, Chamonix / Mont Blanc, France, 29 April–4 May 2012.
- Mukherjee, A. Physical-Layer Security in the Internet of Things: Sensing and Communication Confidentiality Under Resource Constraints. Proc. IEEE 2015, 103, 1747–1761. [Google Scholar] [CrossRef]
- Trappe, W. The challenges facing physical layer security. IEEE Commun. Mag. 2015, 53, 16–20. [Google Scholar] [CrossRef]
- Mukherjee, A.; Fakoorian, S.A.A.; Jing, H.; Swindlehurst, A.L. Principles of Physical Layer Security in Multiuser Wireless Networks: A Survey. IEEE Commun. Commun. Surv. Tutor. 2014, 16, 1550–1573. [Google Scholar] [CrossRef]
- Massey, J.L. An introduction to contemporary cryptology. Proc. IEEE 1988, 76, 533–549. [Google Scholar] [CrossRef]
- Cordeiro, C.; Challapali, K.; Birru, D.; Sai Shankar, N. IEEE 802.22: The first worldwide wireless standard based on cognitive radios. In Proceedings of the International Symposium on New Frontiers in Dynamic Spectrum Access Networks, Baltimore, MD, USA, 8–11 November 2005; pp. 328–337.
- Liu, L.; Zhang, R.; Chuan, K.C. Secrecy Wireless Information and Power Transfer With MISO Beamforming. IEEE Trans. Signal Process. 2014, 62, 1850–1863. [Google Scholar] [CrossRef]
- Pei, Y.Y.; Liang, Y.C.; Zhang, L.; Teh, K.C.; Li, K.H. Secure communication over MISO cognitive radio channels. IEEE Trans. Wirel. Commun. 2010, 9, 1494–1502. [Google Scholar] [CrossRef]
- Li, J.Y.; Petropulu, A.P.; Weber, S. On Cooperative Relaying Schemes for Wireless Physical Layer Security. IEEE Trans. Signal Process. 2011, 59, 4985–4997. [Google Scholar] [CrossRef]
- Hu, B.; Zhao, H.V.; Jiang, H. Wireless Multicast Using Relays: Incentive Mechanism and Analysis. IEEE Trans. Veh. Technol. 2013, 62, 2204–2219. [Google Scholar] [CrossRef]
- Huang, J.; Swindlehurst, A.L. Robust Secure Transmission in MISO Channels Based on Worst-Case Optimization. IEEE Trans. Signal Process. 2012, 60, 1696–1707. [Google Scholar] [CrossRef]
- Pei, Y.Y.; Liang, Y.C.; Zhang, L.; Teh, K.C.; Li, K.H. Secure Communication in Multiantenna Cognitive Radio Networks With Imperfect Channel State Information. IEEE Trans. Signal Process. 2011, 59, 1683–1693. [Google Scholar] [CrossRef]
- Kaur, N.; Sood, S.K. An Energy-Efficient Architecture for the Internet of Things (IoT). IEEE Syst. J. 2015, PP, 1–10. [Google Scholar] [CrossRef]
- Zhang, N.; Lu, N.; Cheng, N.; Mark, J.W.; Shen, X.S. Cooperative Spectrum Access Towards Secure Information Transfer for CRNs. IEEE J. Sel. Areas Commun. 2013, 31, 2453–2464. [Google Scholar] [CrossRef]
- Kamalinejad, P.; Mahapatra, C.; Sheng, Z.G.; Mirabbasi, S.; Leung, V.C.M.; Guan, Y.L. Wireless energy harvesting for the Internet of Things. IEEE Commun. Mag. 2015, 53, 102–108. [Google Scholar] [CrossRef]
- Khandaker, M.R.A.; Wong, K.K. SWIPT in MISO Multicasting Systems. IEEE Wirel. Commun. Lett. 2014, 3, 277–280. [Google Scholar] [CrossRef]
- Martinez, G.; Li, S.F.; Zhou, C. Wastage-Aware Routing in Energy-Harvesting Wireless Sensor Networks. IEEE Sens. J. 2014, 14, 2967–2974. [Google Scholar] [CrossRef]
- Xing, H.; Chu, Z.; Ding, Z.G.; Nallanathan, A. Harvest-and-jam: Improving security for wireless energy harvesting cooperative networks. In Proceedings of the IEEE Global Communications Conference (GLOBECOM), Austin, TX, USA, 8–12 December 2014; pp. 3145–3150.
- Li, W.; Wang, S.L.; Cheng, X.Z. Truthful Multi-attribute Auction with Discriminatory Pricing in Cognitive Radio Networks. In Proceedings of the 1st ACM Workshop on Cognitive Radio Architectures for Broadband, Miami, FL, USA, 30 September–4 October 2013; pp. 21–30.
- Zou, J.N.; Xu, H.W. Auction-Based Power Allocation for Multiuser Two-Way Relaying Networks. IEEE Trans. Wirel. Commun. 2013, 12, 31–39. [Google Scholar] [CrossRef]
- Wang, K.; Li, L.; Hausheer, D.; Liu, Z.Y.; Li, W.; Shi, D.N.; He, G.L.; Stiller, B. A trust-incentive-based combinatorial double auction algorithm. In Proceedings of the 2010 IEEE Network Operations and Management Symposium (NOMS), Osaka, Japan, 19–23 April 2010; pp. 209–215.
- Tsiaras, C.; Stiller, B. Challenging the Monopoly of Mobile Termination Charges with an Auction-Based Charging and User-Centric System (AbaCUS). In Proceedings of the 2013 Conference on Networked Systems (NetSys), Stuttgart, Germany, 11–15 March 2013; pp. 110–117.
- Wang, X.; Ji, Y.; Zhou, H.; Li, J. A Non-monetary QoS-aware Auction Framework towards Secure Communications for Cognitive Radio Networks. IEEE Trans. Veh. Technol. 2015, PP. [Google Scholar] [CrossRef]
- Ly, H.D.; Liu, T.; Liang, Y.B. Multiple-Input Multiple-Output Gaussian Broadcast Channels With Common and Confidential Messages. IEEE Trans. Inf. Theory 2010, 56, 5477–5487. [Google Scholar] [CrossRef]
- Li, Q.; Yang, Y.; Ma, W.K.; Lin, M.L.; Ge, J.H.; Lin, J.R. Robust Cooperative Beamforming and Artificial Noise Design for Physical-Layer Secrecy in AF Multi-Antenna Multi-Relay Networks. IEEE Trans. Signal Process. 2015, 63, 206–220. [Google Scholar] [CrossRef]
- Yang, Y.; Li, Q.; Ma, W.K.; Ge, J.H.; Ching, P.C. Cooperative Secure Beamforming for AF Relay Networks With Multiple Eavesdroppers. IEEE Signal Process. Lett. 2013, 20, 35–38. [Google Scholar] [CrossRef]
- Li, Z.; Jing, T.; Cheng, X.Z.; Huo, Y.; Zhou, W.; Chen, D.C. Cooperative jamming for secure communications in MIMO Cooperative Cognitive Radio Networks. In Proceedings of the 2015 IEEE International Conference on Communications (ICC), London, UK, 8–12 June 2015; pp. 7609–7614.
- Chui, L.U.; Murch, R.D. A transmit preprocessing technique for multiuser MIMO systems using a decomposition approach. IEEE Trans. Wirel. Commun. 2004, 3, 20–24. [Google Scholar] [CrossRef]
- Boyd, S.; Vandenberghe, L. Convex Optimization; Cambridge University Press: Cambridge, UK, 2004. [Google Scholar]
- Sturm, J.F. Using SeDuMi 1.02, a MATLAB toolbox for optimization over symmetric cones. Optim. Methods Softw. 1999, 11, 625–653. [Google Scholar] [CrossRef]
- Stanojev, I.; Simeone, O.; Spagnolini, U.; Bar-Ness, Y.; Pickholtz, R.L. Cooperative ARQ via auction-based spectrum leasing. IEEE Trans. Commun. 2010, 58, 1843–1856. [Google Scholar] [CrossRef]
- Krishna, V. Auction Theory; Academic Press: New York, NY, USA, 2002. [Google Scholar]
- Lu, X.; Wang, P.; Niyato, D.; Hossain, E. Dynamic spectrum access in cognitive radio networks with RF energy harvesting. IEEE Wirel. Commun. 2014, 21, 102–110. [Google Scholar] [CrossRef]
© 2016 by the authors; licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons by Attribution (CC-BY) license (http://creativecommons.org/licenses/by/4.0/).