A Survey on Intermediation Architectures for Underwater Robotics
Abstract
:1. Introduction
1.1. The Need for Middleware Architectures in Underwater Heterogeneous Environments
1.2. Cooperation and Communication in Underwater Heterogeneous Environments
1.3. Related Works
- CLARAty [11] is defined as a framework both generic and object-oriented used for new algorithms integration in a variety of fields, such as vision, control, locomotion, navigation, localization, manipulation, planning and execution. It is mentioned to have been adapted to heterogeneous robots with different hardware control architectures and mechanisms.
- Player 2.0 [12], based on a previous work named Player/Stage that uses robotics under a client-server paradigm, is claimed to improve the latter in two aspects: simplicity (withholding some of the features of the driver API from the user) and flexibility (library division to allow its usage with different transport layers).
- ORCA [13] is an open-source software project making use of component-based software engineering to robotics. The framework is described to be the most prominent feature of the proposal, as it is able to adopt a commercial middleware package, an approach towards framework design that intends to be as minimalist as possible, and a stress on multi-language and multi-platform support.
- MIRO [14] is another object-oriented robot middleware focused on obtaining portability and maintainability for the developed robot software. It provides generic abstract services like localization or behavior engines.
- OpenRTM-aist [15] implements some of the extended features that are used according to the Robotics Technology (RT) middleware standard. It has actually been developed by the same institution that created the RT standard (National Institute of Advanced Industrial Science and Technology, Tokyo, Japan). It includes a manager component to aid the manipulation of other RT Components, too.
- ASEBA [16] is described as a modular architecture for event-based control of complex robots. It is used by running script inside virtual machines with self-contained actuators and sensors.
- MARIE [17] can be regarded as a middleware framework used to integrate both new and legacy software in robotic systems. The authors list as a success the development of a “socially interactive autonomous mobile robot platform” able to perform several different functionalities, such as localization, navigation, map building, sound source localization, tasks scheduling, tracking and separation, visual tracking, etc.
- RSCA [18], an acronym for Robot Software Communications Architecture, is composed of a real-time operating system, deployment and communication middleware in a hierarchical way. The functionalities that can be used with the middleware modules are creation, installation, start, stop, tear-down and uninstallation.
- OPRoS [19] makes use of a component-based development paradigm to provide a robot software platform to support the development of new software. It offers specifications for several components: model, composer, an authoring tool and an execution engine.
- ROS [20] is a flexible framework used for robotics software development. It provides a set of several facilities (libraries, tools, conventions) aimed to aid the creation of software that will be used across a variety of platforms and coded with several different coding languages. A significant number of the proposals related to underwater robotics that have been studied rely on ROS to an extent for their performance.
- MRDS or Microsoft Robotics Developer Studio [21] is an environment used for robot control and simulation. Since it has been developed by Microsoft, it should come as no surprise that it is aimed to development under Windows-based operating systems. It offers a suite of tools (visual programming, windows and web-based interfaces, etc.) to make development possible.
1.4. Contributions Offerred
- Extraction of the advisable requirements that a middleware architecture should have when it is deployed in an underwater environment, especially when it is done so in underwater robotics.
- A survey of the most prominent proposals has been included, highlighting their most important characteristics and how they are used.
- Open issues that have been found as a result of the study done.
- Future works that can be carried out so that the quality of future middleware architectures in underwater robotics will be improved.
2. Technical Features for an Underwater Middleware Architecture
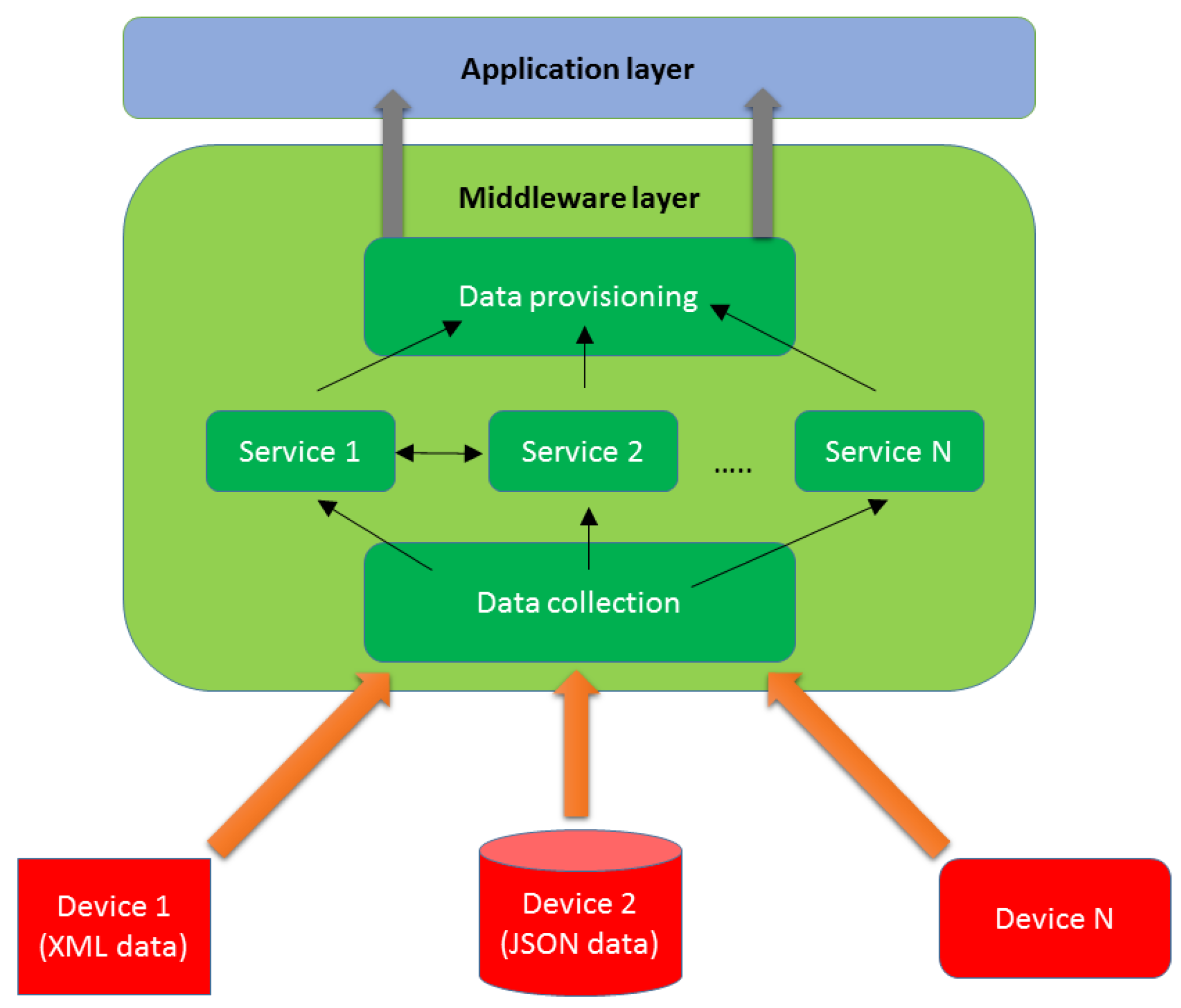
- Middleware must be capable of handling different data formats that might be used by equipment manufactured by different vendors as the ones that based their businesses in robotics or software intermediation architectures. Thus, data heterogeneity management must be considered.
- Since middleware is used to interconnect pieces of equipment scattered in a relatively wide area (underwater and/or surface vehicles that are deployed during a mission) it has to take into account system distribution.
- Optimization of the information that is transferred throughout the distributed collection of deployed robots is usually required by the parties involved in the deployment. One of the most efficient methods to get is inferring the knowledge that is contained in the sent and received data. Therefore, semantic capabilities become a desirable way to improve middleware and the deployment where it is located.
- Middleware is not only used as a messenger between the deployed pieces of equipment, it can also offer some other services, such as device registration, quality of service, security features, etc. Consequently, middleware services must also be taken into account.
- Any intermediation architecture must be capable of carrying on working despite of faults in the hardware appliances where it has been installed (for example, one of the robot sensors takes damage or its control signal is lost for a while). Thus, fault tolerance becomes a feature more than welcome to offer in an architecture like this.
- As it happens with many other software developments, scalability is also needed, as the middleware that is installed in the underwater robots should be capable of coping with new hardware additions and other appliances involved in missions, due to the cooperative nature of them (several AUVs and/or ASVs may have to be deployed during a mission).
- Deployed robots must be aware of the different parameters of their surroundings so that their actions can be done in an effective manner, as missions usually involve a degree of knowledge and interaction with the context they have been sent into. Due to this reason, context awareness must be regarded as another major feature in a middleware expected to work with underwater robots.
- Features as data integrity, confidentiality and user authenticity are important as well so that the transferred information will not be misused by a hostile third party. In a distributed environment, as underwater robotic deployments are, this is a major concern because there are more potential zones where information can be leaked or tarnished. Therefore, security will also be taken into account as a significant feature.
- Some of the objectives of the missions that are carried out by underwater robots require real time capabilities (conceiving this as the capacity of the system to react to changes that take place at one specific moment almost at that very moment), especially when fast decisions have to be made. Real time as a feature is also addressed in this study.
- Last but not least, the easiness to provide information to the community of developers and the usage of open source resources must also be commented, as there is an ever-increasing amount of middleware solutions that rely on open source-based tools and developments. All in all, the availability of information can also be a very useful tool for underwater robotics middleware. Therefore, information availability is also included in this study.
2.1. Data Heterogeneity Management
| Architecture Features | Grade Description |
|---|---|
| Grade: 5 | The proposal manages data by means of a differentiated layer that uses a set of very specific and well-defined set of functionalities. The procedure used to perform that data management is described with profuse details. Standards have been used to homogenize data transferred (XML, JSON, common information models, etc.). Extensive implementation and testing details are provided with actual deployments rather than simulations whenever it is possible to do so. |
| Grade: 4 | A separated middleware architecture or layer is used for data management. The procedures used to describe data heterogeneity are shown in a very detailed manner. Standards have not been used to homogenize data that is being transferred, so it might be harder to port the middleware architecture to another system. Implementation and testing information is provided in order to know about the performance of the proposal. Some details might be vague or testing might be limited to simulations. |
| Grade: 3 | A layer used for data heterogeneity management is provided in the proposal, although it lacks details or there is not abundant information abut its inner components, messages interchanges or performance results. Heterogeneous data is managed correctly but explanations are not detailed enough. |
| Grade: 2 | Poor information is provided about the proposal and the intermediation architecture that is provided or its inner procedures. Diagrams and illustrations are available, but they provide only hints and vague information. |
| Grade: 1 | There is not a differentiated intermediation architecture layer (such as middleware) to manage data. Information regarding how heterogeneous data are managed is either non-existent or irrelevant. |
2.2. System Distribution
| Architecture Features | Grade Description |
|---|---|
| Grade: 5 | The system works with a large distribution degree, not having any centralized point that can be overloaded to the point that, if collapsing, would jeopardize the performance of the system. Extensive information is provided about how implementation and testing have been carried out, among other stages of the development of the solution, and those stages of development are done using actual pieces of equipment in a real deployment. |
| Grade: 4 | The system is distributed but there is some kind of prominent element within the deployment regarding the distribution of the system, so distribution is not complete and if that prominent element fails, the whole system could be in trouble as it cannot be easily replaced by another node. Testing activities have been done but they are using a simulated environment rather than a real one. |
| Grade: 3 | Information about the distributed nature of the proposal is provided (significant and descriptive illustrations and descriptions are available, message formats are offered, UML diagrams explain the inner performance of the system etc.) and it becomes justified how the architecture is a distributed one, but just at a high level without getting into a deep description level. Scarce information is available with regards to the system performance. |
| Grade: 2 | Little information is provided about the distributed nature of the proposal. Hints are put forward on how the system is not centralized. |
| Grade: 1 | There is no data about system distribution (the most prominent functionalities are conceived as centralized), or it is presented with little to no importance or stress. |
2.3. Semantic Capabilities
| Architecture Features | Grade Description |
|---|---|
| Grade: 5 | An extensive description of the semantic capabilities of the system is provided: new ontologies have been created for the deployment capable of storing content specific of underwater robots environment (chemical data, temperatures, underwater currents force, etc.), or already existing ones become seamlessly adapted for the use cases described in the proposal. Descriptive information regarding implementation and testing of the proposal is provided, especially regarding real or large environments. |
| Grade: 4 | The proposal uses semantic capabilities to a significant extent and information relevant to the mission where the robots have been deployed is inferred from the data collected from the environment. Development or adaptation of new ontologies is provided as available information. Testing of the capabilities of the semantics-related modules is provided at a simulation or laboratory level. |
| Grade: 3 | Semantics are present in the proposal and the functionalities of the ontologies or alike additions are explained, although it is not clear how they are implemented. Adaptation of already existing ontologies has been done but no new ones have been created. |
| Grade: 2 | Scarce details are provided regarding semantics; it is only mentioned that they are present, but without information about to what extent and how they are specifically implemented. |
| Grade: 1 | There is no information about data semantics in the proposal that is being assessed. |
2.4. System Services
| Architecture Features | Grade Description |
|---|---|
| Grade: 5 | A complete plethora of services is provided by the proposal (data registration, decision making modules, security, context awareness, events, upper layer interaction, etc.). The implementation of those services is thoroughly described in terms of performance. Furthermore, testing of these services has been done in actual hardware and performance results have been obtained. |
| Grade: 4 | The proposal has a remarkable number of services, taking into account the inputs and the outputs that must be obtained from them. Requirements that resulted in the implementation of those services are described and diagrams are offered. Testing has been done in a simulated environment. |
| Grade: 3 | The set of services that are put forward by the proposal are not fully implemented, although they are fully described, either as part of specifications of the proposal or as a future work that can be done in the future. Some implementation works are shown and an implementation of the available services is offered, but inly to a limitied extent without extensive performance results. |
| Grade: 2 | Poor information is offered regarding the services that can be provided by the proposal. Illustrations and diagrams are available regarding the services to be obtained. Scarce information about services implementation is offered. |
| Grade: 1 | No information about the services that are provided by the proposal is offered or details are too scarce to have a good idea of the services that can be expected from it. |
2.5. Fault Tolerance
| Architecture Features | Grade Description |
|---|---|
| Grade: 5 | A detailed description of how fault tolerance is present in the system is provided in the proposal. By this statement, it is meant that the procedures used to react against an unpleasant and unforeseeable event (e.g., system or hardware failures) are fully described. Implementation details, inner actions and performance results are also shown. |
| Grade: 4 | A description on how fault tolerance is provided, although it is done from a more theoretical perspective and the data that have been obtained regarding its performance have been done so by using simulations rather than having a plethora of robots deployed and deliberately creating a disruption in the system to test it. |
| Grade: 3 | Resilience mechanisms are described from a theoretical point of view rather than as something that has been implemented with a practical purpose. Data are shown about the procedures implemented by these mechanisms, but no information regarding tests is provided. |
| Grade: 2 | Scarce data are offered regarding the resilience mechanisms of the proposal. There are just acknowledged in illustrations or in the available text of the proposals. |
| Grade: 1 | Either no information is provided regarding resilience mechanisms or they are nonexistent in the proposal. |
2.6. Scalability
| Architecture Features | Grade Description |
|---|---|
| Grade: 5 | A specific mechanism is provided so that scalability is guaranteed in the system. The procedures that describe how a new hardware entity is included and how the system will behave to share information with it, as well as data being sent and received, are shown. Either there is a separated module to deal with this issue within the intermediation architecture or it is done by other parts of the system. Scalability has been tested in a real deployment. |
| Grade: 4 | A mechanism to guarantee scalability is described thoroughly, often consisting of an autonomous, separated module. Implementation details, such as the programming language and the interaction with other parts of the system are shown. Information about its performance is present. However, it has only been tested in a simulation level, rather than with actual devices. |
| Grade: 3 | Scalability is offered or even guaranteed to an extent, and diagrams or a description is offered to support this claim. A general overview of the procedures to guarantee scalability has been provided. Despite this, it is not clear how it is done, as there is no information about how scalability fares as a tested feature. |
| Grade: 2 | Scarce information is provided with regard to the way to cope with scalability challenges in a very generic level. A mechanism or a procedure is described to an extent. |
| Grade: 1 | No contingency plans are expected to be carried out in case scalability is required. |
2.7. Context Awareness
| Architecture Features | Grade Description |
|---|---|
| Grade: 5 | Context awareness is fully implemented as a mechanism to become aware of the conditions that surround the deployed piece of hardware. Its location in the middleware architecture is shown and the procedures to collect information from the context and use them are described. Implementation sketches and abundant details are provided. The module, facility or procedure that has been created to do so has been fully tested in a real deployment. |
| Grade: 4 | Context awareness is provided as a service with a description profuse in details, and information on how it works is available as well. Procedures to collect information from the environment in order to take action based on it are formulated. However, its testing activities have been done with simulations in a controlled environment, so it is not clear how context awareness would be used in an actual deployment. |
| Grade: 3 | Context awareness is provided as a black box where inputs and outputs are offered in a theoretical-only manner. A rough description on how it works is also provided without further details. Little information is offered regarding its performance. |
| Grade: 2 | Scarce data is provided to take into account the context awareness feature. Diagrams and illustrations are available. |
| Grade: 1 | No context awareness is provided, or it is done in a way that no effective information is provided. |
2.8. Security
| Architecture Features | Grade Description |
|---|---|
| Grade: 5 | Security is a fully fledged component in the intermediation architecture capable of covering a significant number of security functionalities (Authentication and Authorization, DDS based service, public key infrastructures), thus preventing any major security attacks to take place (Distributed Denial of Service, Man in the middle, etc.). The list of attacks that could be prevented is provided along with corresponding methodologies. Implementation and test details are provided in a profuse manner. |
| Grade: 4 | Security is provided as a component or a module capable of preventing major security attacks to happen. Information about their inner performance is provided. Testing has been done with simulated environments rather than with actual underwarter vehicles. |
| Grade: 3 | Security appears in the proposal, but it is either a scarcely described module or there are security functionalities in the proposal that are not explained in detail. Few data about its testing and performance are provided. |
| Grade: 2 | Little information is provided about the security feature. Illustrations and/or diagrams have been provided to describe the security components of the proposal. |
| Grade: 1 | No security is provided in the proposal, or there is not enough information to figure out its minimal performance. |
2.9. Real Time
| Architecture Features | Grade Description |
|---|---|
| Grade: 5 | Real time functionalities are provided either as a set of methods or a module capable of sending and receiving information immediately to the upper levels of the middleware architecture without a significant delay. Information, such as code or diagrams, is provided. Implementations or tests in actual vehicles have been carried out with success. |
| Grade: 4 | Real time functionalities are provided and a description on how they are tackled has been provided. Although there is plenty of information available, no code has been placed. Real time capabilities have been implemented and tested in a simulated environment. |
| Grade: 3 | Real time features have been enabled in the proposal but there is little information about how data are transmitted from the lower levels of the architecture to the upper ones without significant delays. |
| Grade: 2 | Very little data is provided about how real time capabilities are provided in the proposal, such as diagrams or a black box. |
| Grade: 1 | No real-time capabilities have been conceived for the proposal or no information about them can be inferred. |
2.10. Information Availability
| Architecture Features | Grade Description |
|---|---|
| Grade: 5 | A complete set of deliverables describing the steps and the overall proposal is available online and they can be downloaded. Among some other features, open source tools have been used and the resulting code can be downloaded from an online repository. The description of the proposal is an accurate depiction of what has been included in the available resources. |
| Grade: 4 | Deliverables and code are available online in an open source manner, but the information provided by the deliverables is either too generic, or too cryptic. Code is of good quality and has been provided with comments that make it easy to understand and use. |
| Grade: 3 | Deliverables are available to understand the scope and the aim of the proposal, but no code is available to download or share. |
| Grade: 2 | No code is available in an online repository, or the proposal has been done using proprietary solutions that cannot be easily shared or ported. |
| Grade: 1 | No resources that help have a better grasp of the proposal are available. |
3. Description of the Proposals
3.1. Robot Operating System (ROS)
| Characteristic | Mark | Explanation |
|---|---|---|
| Data heterogeneity management | 4 | Information/messages are standardized and described by a language-neutral interface definition language. An appropriate data management should be chosen and tested in real environments. |
| System distribution | 5 | ROS is conceived as a distributed middleware composed of different nodes (interchangeable with software module) at a fine-grained scale. The distribution has been proven in many real projects. |
| Semantic capabilities | 1 | No semantic capabilities are included or even mentioned in the design. But it could be possible to add this feature in the next version of ROS as it can evolve to meet more requirements. |
| System services | 5 | A variety of system services are provided with detailed descriptions and implementations, such as service registry, debugging and configuration etc. |
| Fault tolerance | 4 | A component called Diagnostics provides a standard way to produce, collect, and aggregate information regarding analysis, troubleshooting and logging of the inner operation in robots. With the diagnostic information, it is easy to know the state of robot and address the fault detected in it. |
| Scalability | 3 | It provisions sharable resources like cores, cache etc. for guaranteed use by a process. It could be scalable to deal with increasing components or entities connected, but it lacks practical proof. |
| Context awareness | 1 | Context awareness is not considered in ROS, thus, no methodology is provided to endow ROS with this feature. |
| Security | 1 | No security mechanisms are considered. |
| Real time | 4 | ROS real time tools are available. However, the current capability is limited to provide the realtime publisher. Resource code is open released with relevant specifications. This feature is tested in simulations. |
| Information availability | 5 | Open sources are enabled regarding source code and documentations. Lots of publications regarding applications using ROS are available. Besides, the ROS community behind can be very useful for providing supports regarding ROS developments. |
3.2. Distributed Robot Monitoring System (Drums)
- Generating and monitoring the computation graph which models the state of different resources in the middleware.
- De-abstracting and de-multiplexing abstract services, interactions, and communication channels into atomic and simple processes.
- Dynamically monitoring and diagnosing failures.
- Aggregating collected data into a central time series database in a cost-efficient way.
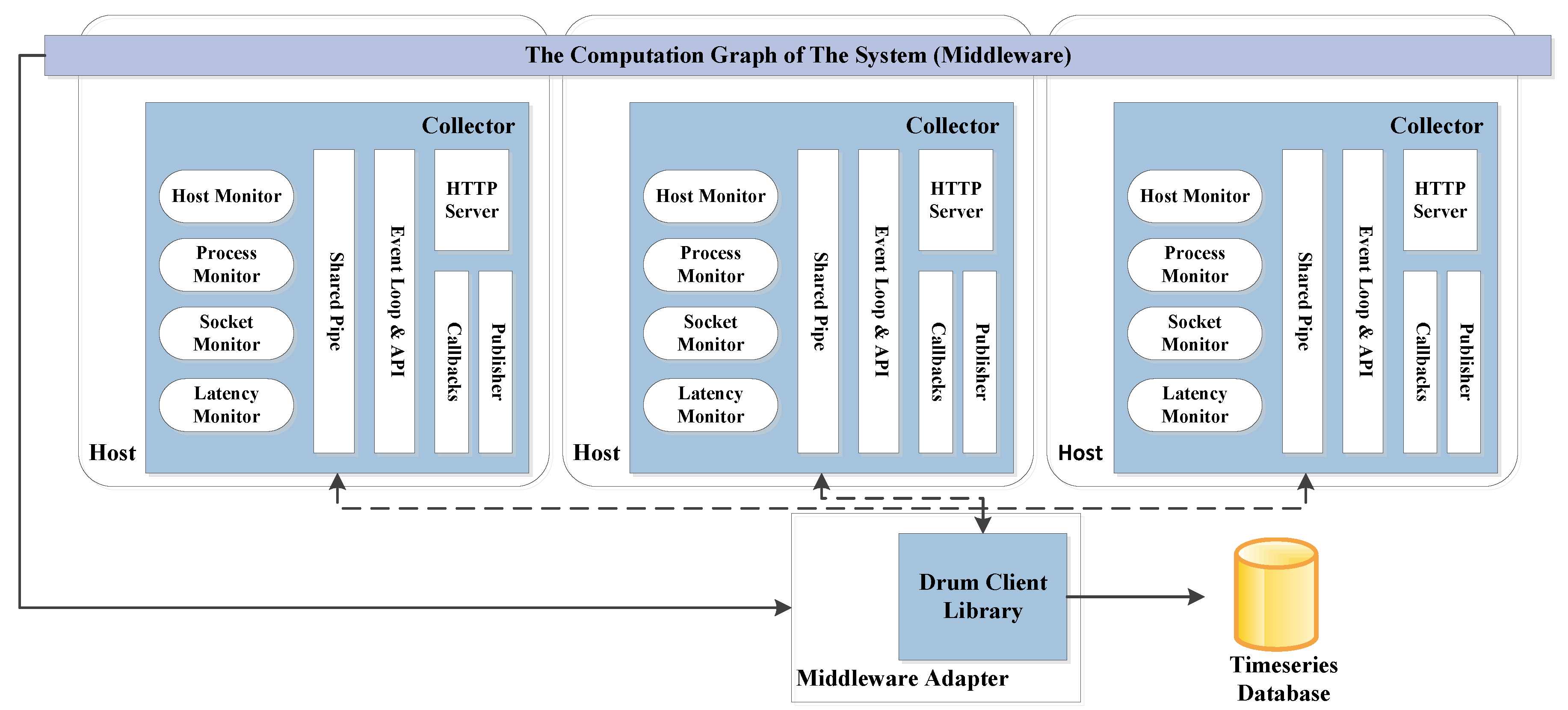
| Characteristic | Mark | Explanation |
|---|---|---|
| Data heterogeneity management | 4 | Data is aggregated and organized into a central time series database. |
| System distribution | 5 | Different collectors can be mounted in different hardware using different adapters in a distributed manner. |
| Semantic capabilities | 1 | No semantic capabilities are included or even mentioned in the design. |
| System services | 1 | The middleware does not claim it could provide necessary system services, thus, insufficient information is described further. |
| Fault tolerance | 5 | Specific monitors are defined to dynamically monitor and diagnose failures. Information generated from the monitoring process is tested in two scenarios. |
| Scalability | 1 | No scalability mechanism is included. |
| Context awareness | 2 | Although this concept is not mentioned in the design, Drums can be regarded as using some kind of context aware because it can closely monitor changes of computation graph and provide diagnosis accordingly. However, the context awareness level is very limited. |
| Security | 1 | No information about security is included. |
| Real time | 2 | Very little information regarding this feature is provided. However, the proposal of latency monitor can be a useful hint. |
| Information availability | 5 | Open access to code is available with detailed tutorials. A few publications are also available for understanding this proposal. |
3.3. CoHoN
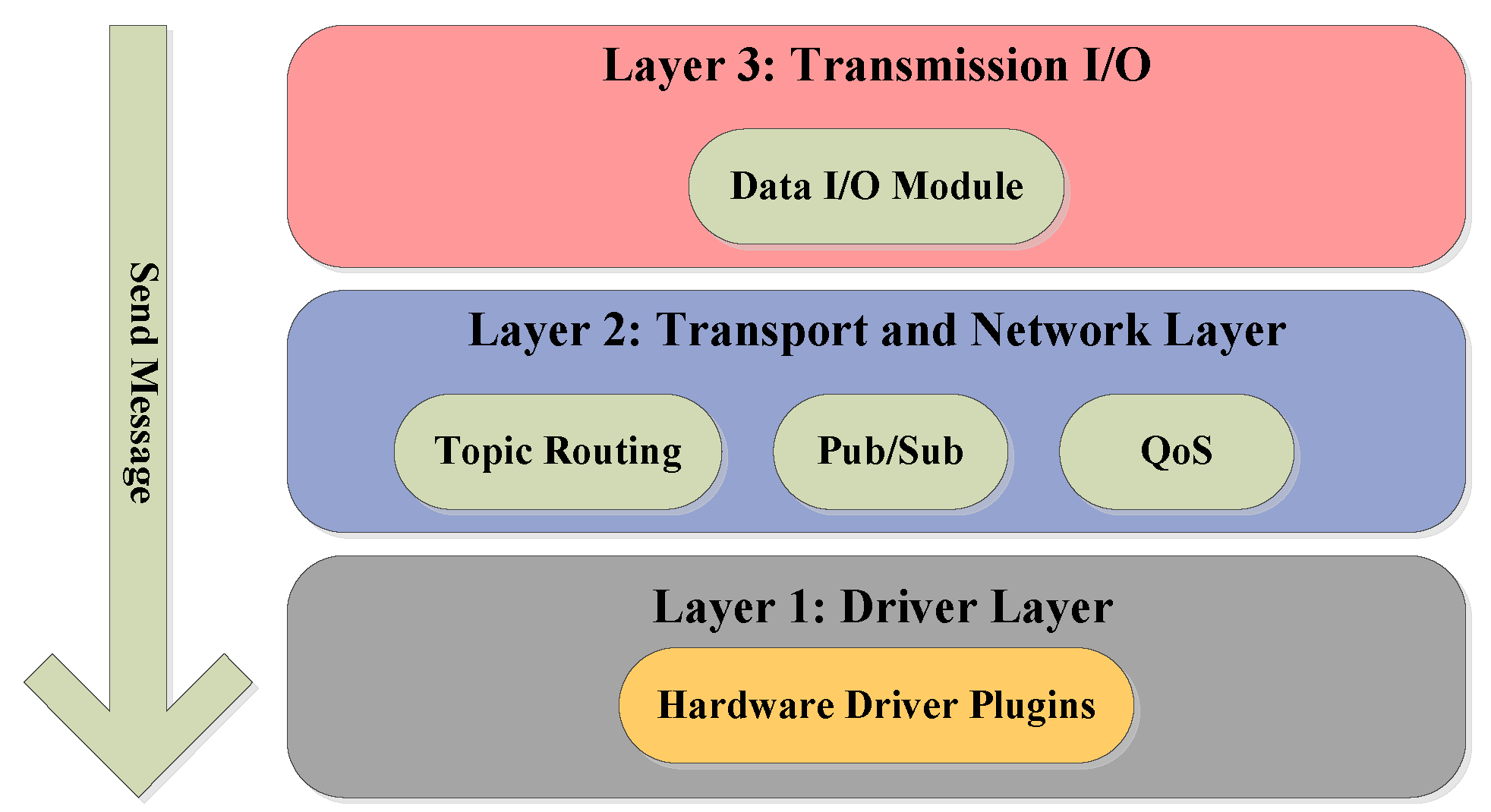
| Characteristic | Mark | Explanation |
|---|---|---|
| Data heterogeneity management | 1 | Information regarding the specific method to manage data is non-existent. |
| System distribution | 3 | It is claimed the middleware is distributed and decentralized without descriptive explanations about the specific strategy applied. |
| Semantic capabilities | 1 | No semantic capabilities are included or even mentioned in the design. |
| System services | 3 | System services are fully described without complete implementation. They are pointed out as future work. |
| Fault tolerance | 3 | A resilience mechanism which can provide alternative routing in case of failures or disconnections is theoretically introduced. No practical tests are available. |
| Scalability | 1 | No scalability mechanism is included. |
| Context awareness | 1 | This concept is not taken into account. |
| Security | 3 | Security regarding encription is mentioned as an extra I/O functionality. However, it is not explained in detail. |
| Real time | 3 | Real time is mentioned to be guaranteed to some extent by a topic-based routing mechanism. It lacks detailed descriptions and further justifications. |
| Information availability | 3 | Publications and webpages are available to describle the purpose and funcationalities of this middleware. Code is not released as open source. |
3.4. RAUVI Architecture
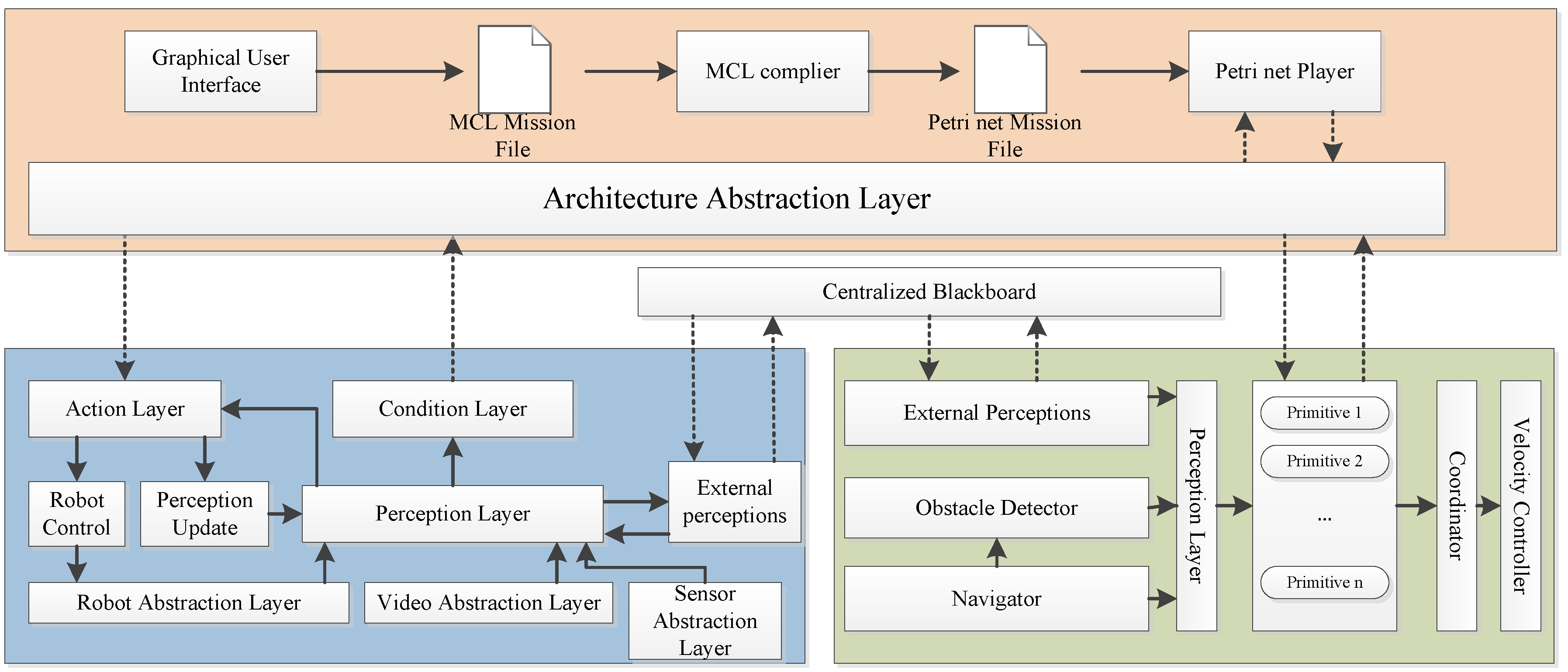
| Characteristic | Mark | Explanation |
|---|---|---|
| Data heterogeneity management | 1 | This feature is entirely missing in this proposal. No information is provided to introduce any data management mechanism. |
| System distribution | 1 | It is not conceived as a distributed solution. |
| Semantic capabilities | 1 | No semantic capabilities are included or even mentioned in the design. |
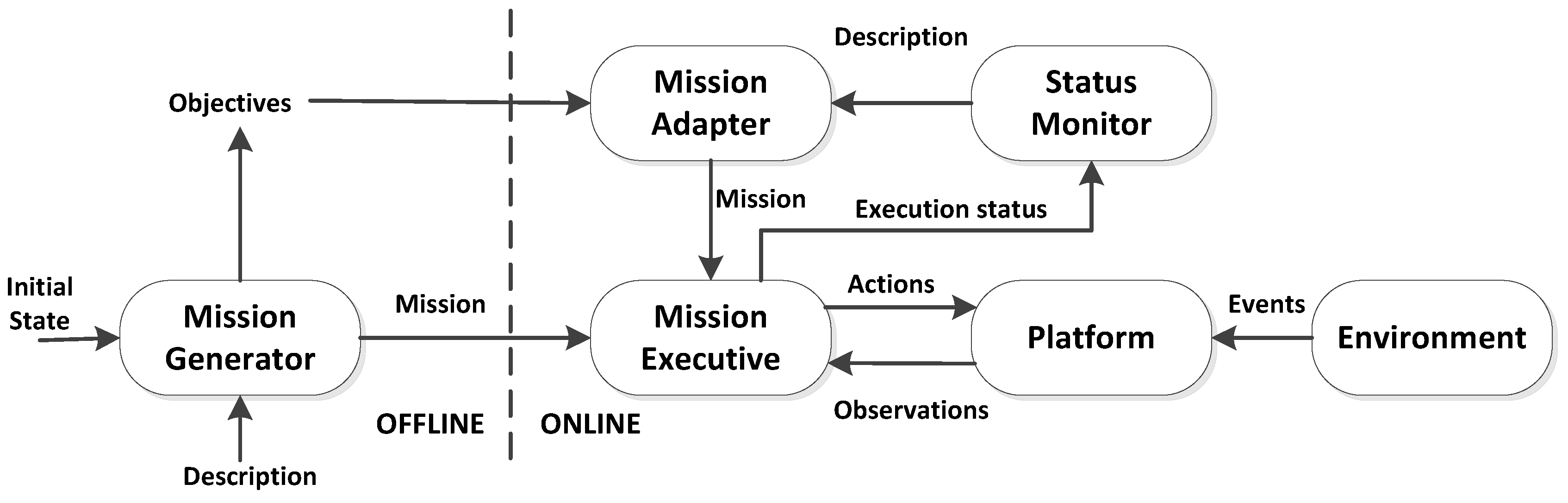
| System services | 3 | Capabilities, such as user interface, mission plan etc., are provided with detailed descriptions, however, implementation lacks. |
| Fault tolerance | 1 | This feature is not taken into account in this proposal. |
| Scalability | 1 | No scalability mechanism is included. |
| Context awareness | 1 | It is a missing feature in this proposal. |
| Security | 1 | It is not taken into account in RAUVI. |
| Real time | 2 | Little information is provided to describe the specific strategy of supporting real time feature. It is only stated that tasks can execute in real time after a single Petri net generated. |
| Information availability | 3 | Publications and demos are available to introduce the idea of this middleware. Code is not released. |
3.5. Pandora Architecture

| Characteristic | Mark | Explanation |
|---|---|---|
| Data heterogeneity management | 5 | The ontology-based approach to manage heterogeneity is described and tested in a controlled environment. Data storage is also enabled. |
| System distribution | 4 | Different agents consisting of necessary capabilities can be distributed in different vehicles or computation device. A simulated environment, rather than real test is described. |
| Semantic capabilities | 4 | Data semantics are included to infer more useful information which could be used for decision making purposes. A hierarchical ontology is created to describe the knowledge domain. The ontology is tested based on KnowRob at a simulation level. |
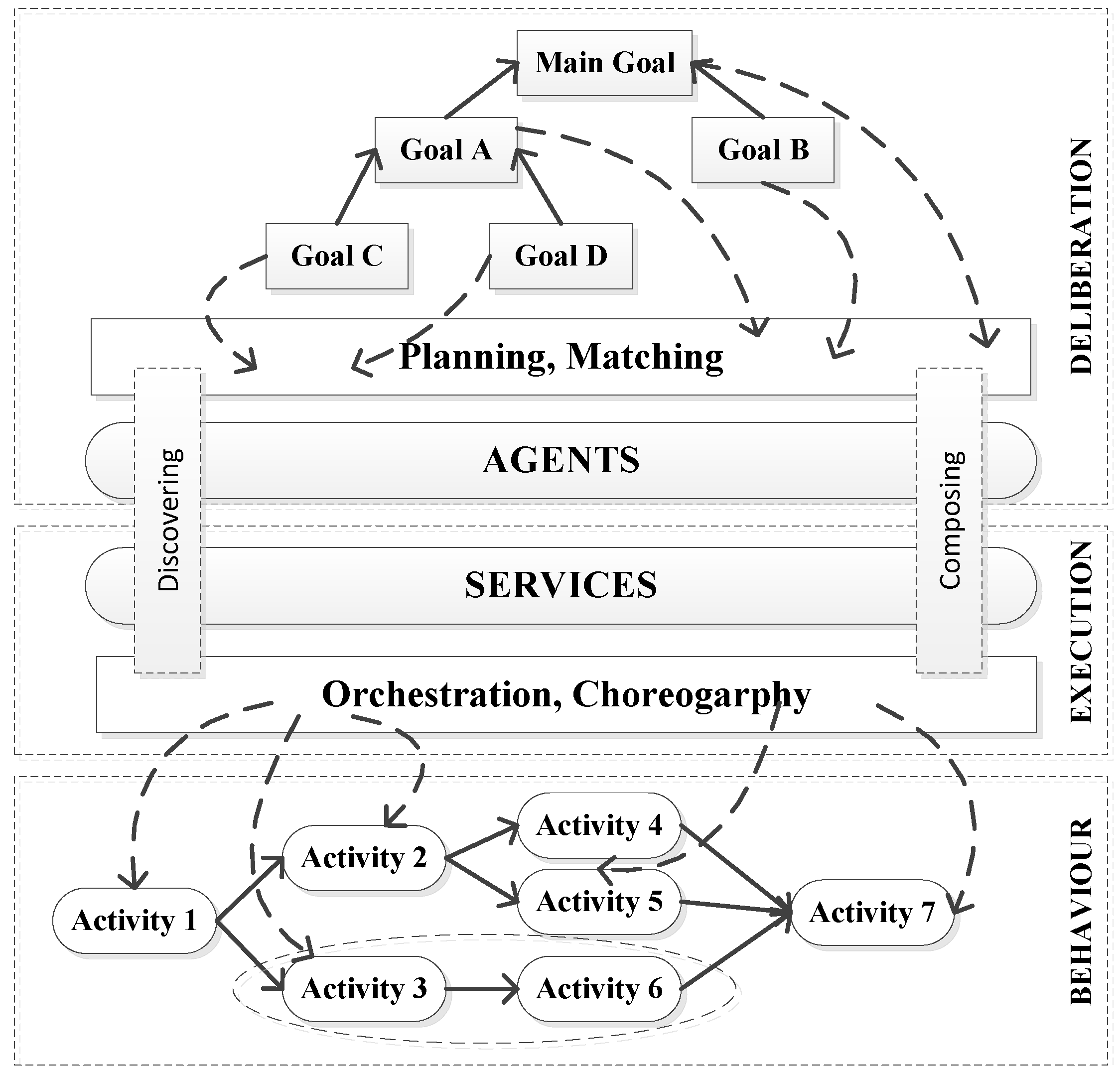
| System services | 4 | System services like service discovery, service composition, service choreography etc. are fully described and tested in a simulated environment. |
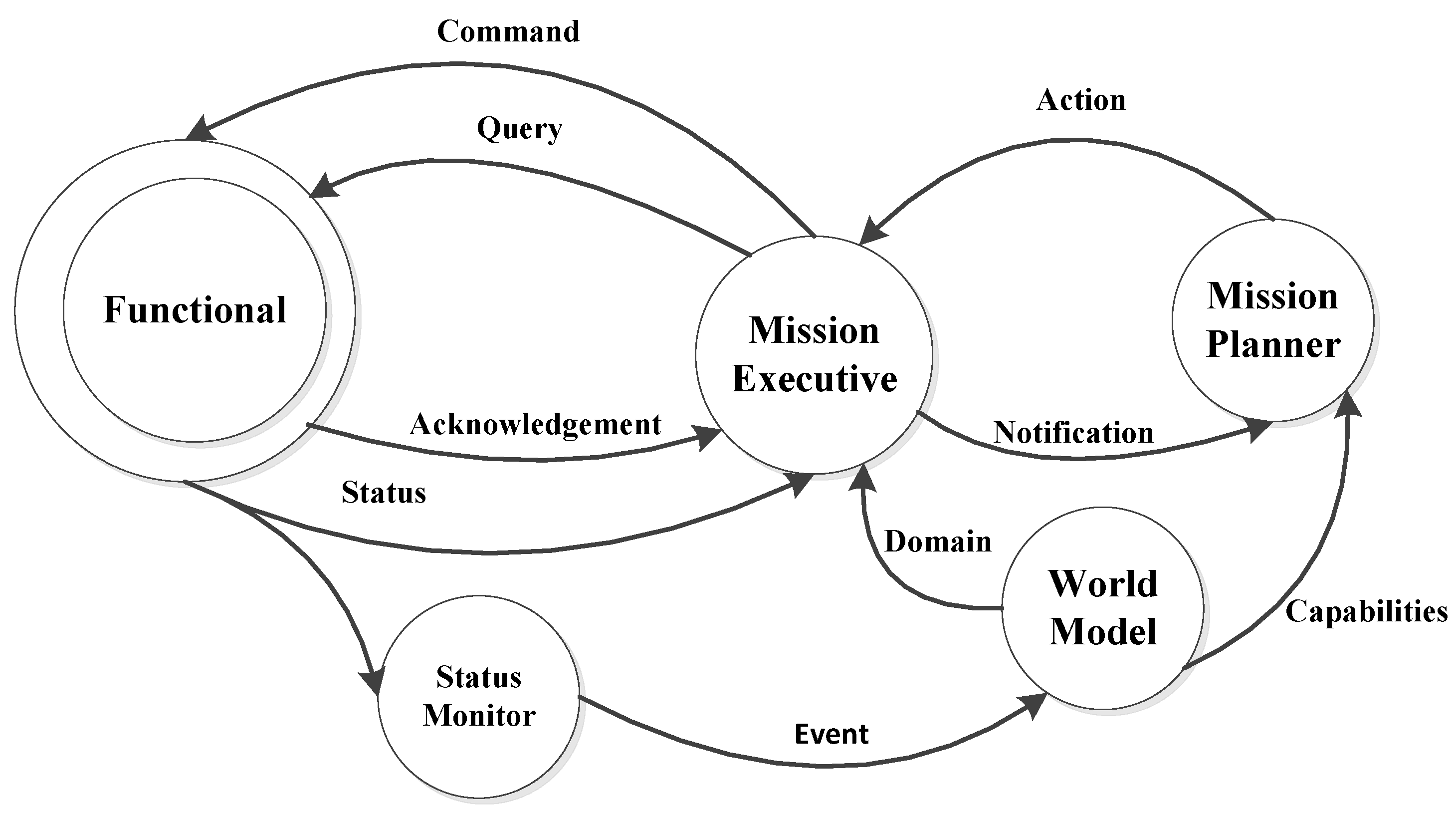
| Fault tolerance | 4 | Plan execution status is monitored by a diagnosis engine and passed to the planner to generate alternative plan. Actual deployment is missing. |
| Scalability | 4 | The adoption of KnowRob can handle an increasing amount of data. Besides, the concept “agent” can enable Pandora to accommodate more entities. |
| Context awareness | 3 | Although this concept is not specifically mentioned in this proposal it can be claimed as a service that it can hold. A mechanism on how context data is processed and deduced to produce more useful knowledge for enabling robots to adjust behaviors accordingly to the environment is introduced, which in fact exposes this potential capability. |
| Security | 1 | It is entirely missing in this middleware. |
| Real time | 1 | This feature is not addressed in this middleware. |
| Information availability | 3 | Publications, deliverables, and project webpages are available while code has not been released to the public. |
3.6. TRIDENT Proposal

| Characteristic | Mark | Explanation |
|---|---|---|
| Data heterogeneity management | 5 | Data heterogeneity is abstracted within a hierarchical ontology and tested in real harbor environments. |
| System distribution | 4 | It is conceived in a distributed fashion and prototyped in real scenarios. Details about maintenance tasks are not present. |
| Semantic capabilities | 5 | Data semantics are exposed to support the reasoning procedure. This feature has been proven in real scenarios. |
| System services | 4 | Various system services are offered and tested like registry and reasoning etc. |
| Fault tolerance | 5 | The status monitor keeps a close eye on how mission is executing and provides failure information for planner to deal with unexpected failures or disconnections. It is claimed that it has been shown in the harbor experiment. |
| Scalability | 2 | Scarce information is provided to justify the scalability issue. From the data management point of view, it is scalable to manage increasing data. |
| Context awareness | 5 | Context awareness is achieved following an OODA loop. Context data is obtained and processed to a great extent with the idea of generating useful information for robots to understand the underwater environment. A descriptive logic reasoning mechanism is applied. It is tested in real environments. |
| Security | 1 | Security is not considered in this middleware. |
| Real time | 1 | No information regarding real time is provided |
| Information availability | 3 | Publications and project webpages are availble to show this middleware design details. However, source code is not available. |
3.7. Sunrise Proposal

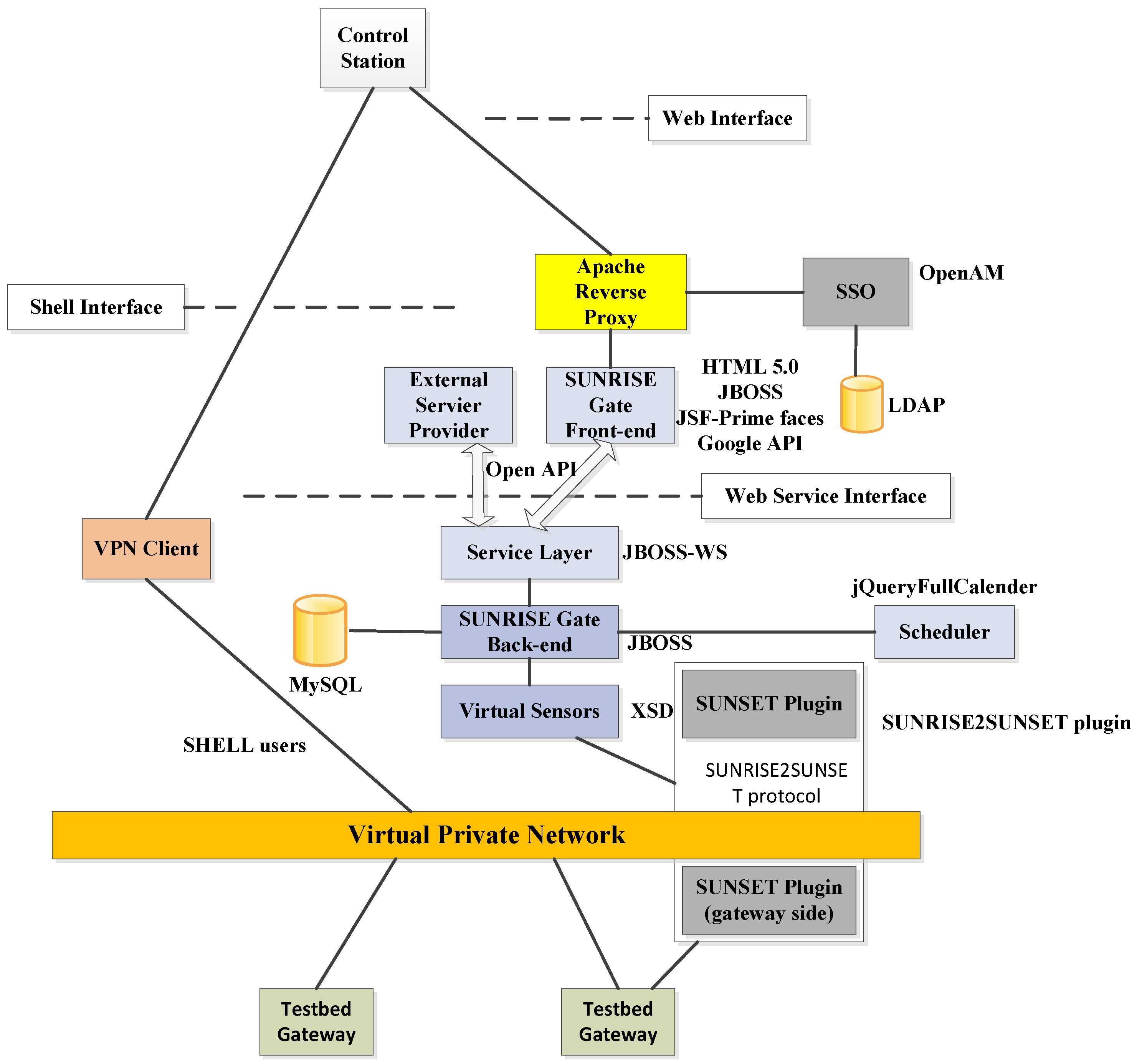
| Characteristic | Mark | Explanation |
|---|---|---|
| Data heterogeneity management | 4 | Various data are formatted and stored in a relational database, namely, MySQL. |
| System distribution | 5 | It is theoretically conceived in a distributed fashion and prototyped in real testbeds. |
| Semantic capabilities | 1 | This feature is missing in this proposal. |
| System services | 5 | A set of system services like application connection are provided. Particularly, registry is done by parsing xml-based messages. Security is ensured by SSO and LDAP. All these services are implemented and tested in real testbeds. |
| Fault tolerance | 3 | The status monitor keeps a close eye on how mission is executing and provides failure information for planner to deal with unexpected failures or disconnections. Proof of concept is missing. |
| Scalability | 2 | No detailed information is provided to justify the scalability issue. However, the concept “Internet of Underwater Things” in this proposal reveals possibilities to be scalable to connect more entities, though further details should be provided. |
| Context awareness | 1 | This feature is not mentioned in this proposal as well as relevant descriptions. |
| Security | 5 | Two modules are provided to guarantee authentication, authorization and accounting. This security mechanism is validated in real underwater environments. |
| Real time | 4 | Real time is included by the adoption of Sunset gateway. Details about the gateway are available.However, code is not available. |
| Information availability | 3 | Publications and project webpages are available. Source code keeps unreleased. |
3.8. CoCoRo

| Characteristic | Mark | Explanation |
|---|---|---|
| Data heterogeneity management | 3 | UML is chosen as the modelling method to formalize data needing more explanations about the specific procedure. |
| System distribution | 3 | System decentralization is claimed at a conceptual level without further proof. |
| Semantic capabilities | 1 | Semantic capabilities are unavailable. |
| System services | 2 | Limited services like individual cognition, swarms planning are introduced. No more details are provided. |
| Fault tolerance | 3 | Fault detection is not available. However, it could be possible to employ different bio-inspired algorithms to generate alternative plans in the presence of failures. |
| Scalability | 3 | It is not clearly mentioned or tested in this proposal. However, judging from the theoretical analysis in this proposal, it could be possible for this middleware to accommodate to a bigger group of vehicles. |
| Context awareness | 4 | Awareness of the surrounding is achieved in a hierarchical manner, varying from an individual level to a swarm level. It is tested in a simulated environment. |
| Security | 1 | Security is not considered in CoCoRo. |
| Real time | 1 | Real time is a missing feature in CoCoRo. |
| Information availability | 3 | Publications and project webpages are available. Source code is not provided. |
3.9. T-REX

| Characteristic | Mark | Explanation |
|---|---|---|
| Data heterogeneity management | 3 | Sample collection of different elements found in the sea and underwater mapping have been proven to be done in different missions. It is not clear if there is a software module devoted to sending and receiving data throughout all the deployed underwater robots, or how the proposal transfers information outside the vehicle. |
| System distribution | 2 | The proposal portrays the deployed robots as autonomous and capable of taking decisions by themselves. A description of a procedure to coordinate activities among several of them is not provided, nor are details regarding distribution given. |
| Semantic capabilities | 1 | No semantic capabilities are mentioned in the proposal. |
| System services | 5 | The proposal is capable of providing a wide range of services in missions, such as sampling, mapping and finding suspended particles in the sea. The most prominent of these features is the analysis of Intermediate Nepheloid Layers (INLs). Machine learning techniques are claimed to be used as well. |
| Fault tolerance | 4 | The system establishes a hierarchy, relying on a chain of reactors until a solution is found for the problem. Replanning a mission when unforeseen events take place can also be done. The usage of other underwater vehicles that might support a failing one is not explained. |
| Scalability | 2 | The autonomy of the underwater robots enables their extended usage, but it is not explained how they coordinate one with the other, or to what extent the chain of reactors can be extended. |
| Context awareness | 2 | It is mentioned that there is a reaction from the environment and actions can be taken regarding this reaction, but there is not a detailed explanation on how to do so, nor any diagram is provided. |
| Security | 1 | No security measures are mentioned in this proposal. |
| Real time | 2 | The real time used by the operating system installed in the robots is real-time based, so T-REX could be able to handle request of that nature. Yet it remains unconfirmed as far as the middleware architecture is concerned. |
| Information availability | 2 | Scientific publications are available online, as well as the initiative where it was tested [54]. Open source resources are claimed to be used. No code or deliverables have been found. |
3.10. Huxley

| Characteristic | Mark | Explanation |
|---|---|---|
| Data heterogeneity management | 4 | The proposal is used by several different underwater vehicles of different features, so data of different characteristics can be managed. There is no information regading interconnectivity among the different vehicles once they are deployed. |
| System distribution | 1 | No information about system distribution is provided in the proposal. |
| Semantic capabilities | 1 | No semantic capabilities are mentioned in the proposal. |
| System services | 5 | The proposal has been used for different tasks with a considerable degree of success; applications mentioned are mine-countermeasures or battlespace preparation. Interest is shown in expanding those activities to persistent surveillance and anti-submarine warfare (ASW). |
| Fault tolerance | 2 | Fault detection and recovery are mentioned as a feature tackled by the executive layer, but it is not described how it is provided. |
| Scalability | 2 | Scalability is mentioned as extensibility in the proposal, but little information is provided about it, and it seems not to imply scalability in the number of vehicles than can be used. |
| Context awareness | 2 | Context awareness is only hinted in the proposal, mentioned as a will to make observations of the world around the hardware entity and take actions within that framework. |
| Security | 1 | No security measures are mentioned in this proposal. |
| Real time | 1 | No real time features are mentioned in the proposal. |
| Information availability | 2 | Huxley runs in an open source Linux environment [56]. No code or extensive documentation (tutorials, deliverables, etc.) has been found online. |
3.11. LCM

| Characteristic | Mark | Explanation |
|---|---|---|
| Data heterogeneity management | 4 | Heterogeneous data are encoded and decoded (referring to as marshalling and unmarshalling) for exchange among different modules according to the LCM data type specification language. This mechanism has been tested as useful in real scenarios. |
| System distribution | 5 | It is a modular system which can be distributed in different physically separate computation devices. The distribution feature of LCM has been shown in a number of real robotics applications, such as land and underwater vehicles, autonomous indoor flight etc. Extensive information regarding implementation guide are presented in the LCM’s website. |
| Semantic capabilities | 1 | Semantic capabilities are not available in the LCM middleware. |
| System services | 2 | Communication related services, like marshalling, unmarshalling, debugging, and analysis are fully described, implemented, and tested. No other kinds of services (like service registry, decision making etc.) beyond this are provided. |
| Fault tolerance | 1 | This feature is not taken into account in this proposal. Thus, no fault tolerance scheme is mentioned. |
| Scalability | 3 | It is claimed that communications can be ensured in an increasing number of modules as UDP multicast is used to guarantee high bandwidth and scalability. Nevertheless, no specific module is designed to deal with this issue. |
| Context awareness | 1 | No information regarding the context awareness feature is provided in this proposal. |
| Security | 1 | No security mechanisms are mentioned in this middleware. |
| Real time | 5 | A module, called real time analysis, is devoted to enabling this feature. Details about the specific mechanism are provided. Besides, this feature has been tested in actual vehicles. |
| Information availability | 5 | Scientific papers and webpages are available to understand the internal composition of this middleware. Besides, source code regarding different platforms (Linux, OS X, Windows and any POSIX-1.2001 system) and different languages (including C, C++, C#, Java, Lua, Matlab and Python) is released. |
3.12. MORPH
- A Surface Support Vehicle (SSV).
- A Global Communication Vehicle (GCV), used to improve the navigation accuracy and relay communications.
- A Local Sonar Vehicle (LSV), equiped with one multibeam echosounder.
- A couple of camera carrying vehicles (C1V and C2V).
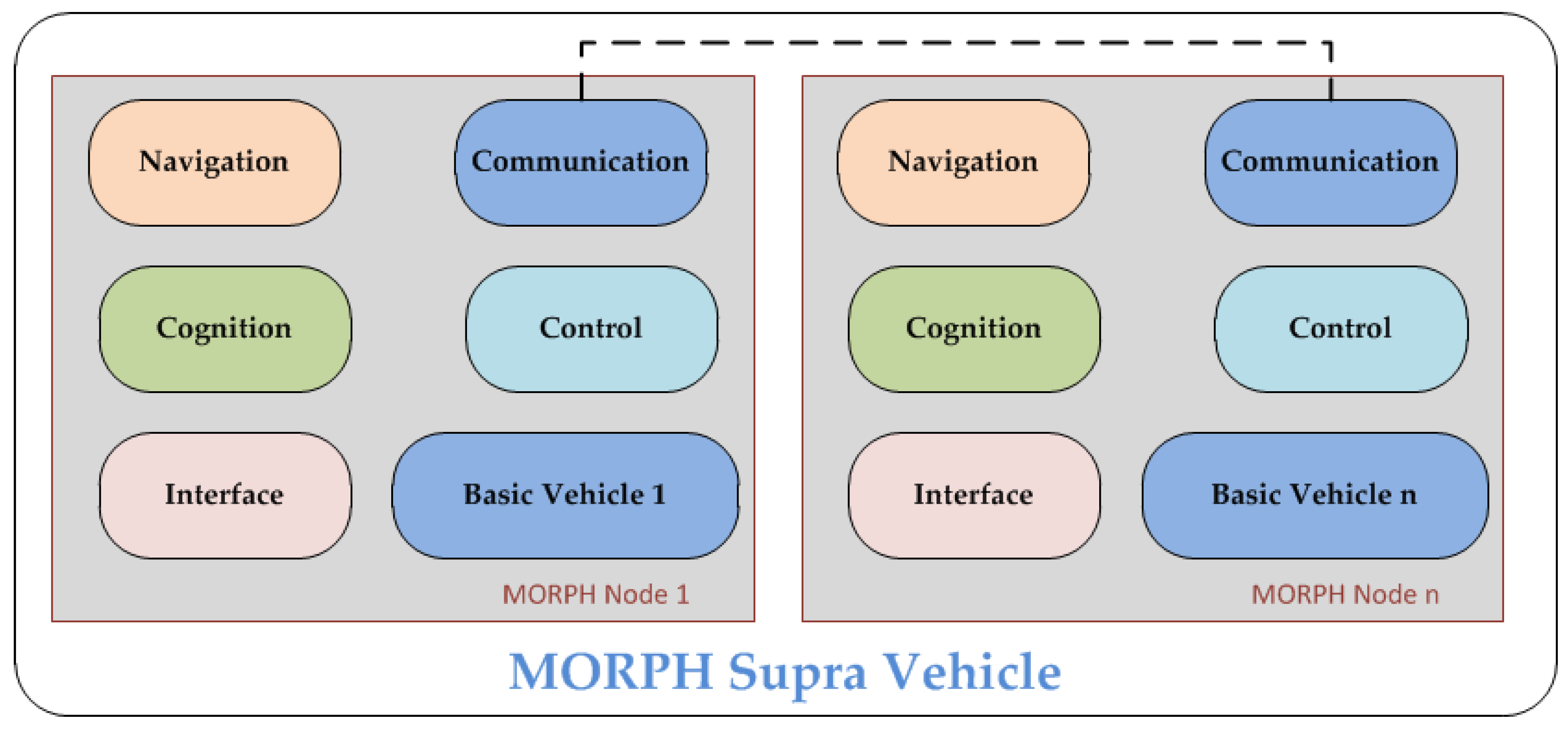
| Characteristic | Mark | Explanation |
|---|---|---|
| Data heterogeneity management | 2 | From the diagrams and publications it seems clear that there must be some kind of data heterogeneity management, as the system provides coordination between heterogeneous vehicles. But there is no clear or relevant information regarding this topic. |
| System distribution | 4 | The system is distributed using a common set of modules to provide a composed view of all the vehicles as one. |
| Semantic capabilities | 1 | There is no information about data semantics. |
| System services | 3 | Services have been defined and tested in real environments. However, they are tightly coupled to the specific goals of the project. |
| Fault tolerance | 2 | No specific information has been provided regarding fault tolerance. The description of the project and the architecture acknowledge that some resilience mechanisms should be implemented. |
| Scalability | 3 | The definition of the interface module provides the capacity of adding new hardware entities or vehicles to the system. The description of the interface module is lacking information. |
| Context awareness | 3 | Context awareness, as defined in this proposal, is provided by the cognition module. No details have been provided on the implementation and performance of this module. |
| Security | 1 | No information about security mechanisms is available. |
| Real time | 3 | There is no information related to real time data transfers. |
| Information availability | 2 | Source code and architecture details are not open. A collection of publications regarding algorithms developed to achieve the goals are available. |
4. Main Issues and Challenges
4.1. Comparisons of the Proposals
| Middleware Proposals | Data Heterogeneity Management | System Distribution | Semantic Capabilities | System Services | Fault Tolerance | Scalability | Context Awareness | Security | Real Time | Information Availability | Total Score |
|---|---|---|---|---|---|---|---|---|---|---|---|
| ROS | 4/5 | 5/5 | 1/5 | 5/5 | 4/5 | 3/5 | 1/5 | 1/5 | 4/5 | 5/5 | 33 |
| Drums | 4/5 | 5/5 | 1/5 | 1/5 | 5/5 | 1/5 | 2/5 | 1/5 | 2/5 | 5/5 | 27 |
| CoHoN | 1/5 | 3/5 | 1/5 | 3/5 | 3/5 | 1/5 | 1/5 | 3/5 | 3/5 | 3/5 | 22 |
| RAUVI | 1/5 | 1/5 | 1/5 | 3/5 | 1/5 | 1/5 | 1/5 | 1/5 | 2/5 | 3/5 | 15 |
| Pandora | 5/5 | 4/5 | 4/5 | 4/5 | 4/5 | 4/5 | 3/5 | 1/5 | 1/5 | 3/5 | 33 |
| Trident | 5/5 | 4/5 | 5/5 | 4/5 | 5/5 | 2/5 | 5/5 | 1/5 | 1/5 | 3/5 | 35 |
| Sunrise | 4/5 | 5/5 | 1/5 | 5/5 | 3/5 | 2/5 | 1/5 | 5/5 | 4/5 | 3/5 | 33 |
| CoCoRo | 3/5 | 3/5 | 1/5 | 2/5 | 3/5 | 3/5 | 4/5 | 1/5 | 1/5 | 3/5 | 24 |
| T-REX | 3/5 | 2/5 | 1/5 | 5/5 | 4/5 | 2/5 | 2/5 | 1/5 | 2/5 | 2/5 | 24 |
| Huxley | 4/5 | 1/5 | 1/5 | 5/5 | 2/5 | 2/5 | 2/5 | 1/5 | 1/5 | 2/5 | 21 |
| LCM | 4/5 | 5/5 | 1/5 | 2/5 | 1/5 | 3/5 | 1/5 | 1/5 | 5/5 | 5/5 | 28 |
| MORPH | 2/5 | 4/5 | 1/5 | 3/5 | 2/5 | 3/5 | 3/5 | 1/5 | 3/5 | 2/5 | 24 |
4.2. Open Issues
4.2.1. Lack of Implementation Works
4.2.2. Unsatisfactory Performance
4.2.3. Security
4.2.4. Consideration for Low Capable Vehicles
4.2.5. Low Context Awareness Level
4.2.6. Consideration of Data Imperfection
5. Conclusions and Future Works
- The underwater robotic middleware should fully resolve the heterogeneity inherent to different hardware manufacturers, information exchange and software components so that seamless interconnection and interaction can be achieved to a great extent. A series of ICT technologies, such as the semantic web, cloud computing, and ontologies, can be exploited and reused in underwater robotic middleware.
- The particular constraints coming from tough underwater environments should be considered during the design of underwater robotics middleware. Scarce communication width, an uncertain and noisy environment, heterogeneous data sources and low-capable underwater vehicles will impose a considerable amount of constrains to be tackled by a well-designed underwater robotic middleware.
- The underwater robotic middleware should become innovative by supporting the distributed coordination and integration of information and functionalities coming from different AUVs/ROVs. Improving robustness and reliability of the underwater vehicles could be addressed too. Cost-effectiveness should be guaranteed by leveraging and orchestrating already available functionalities offered by AUVs/ROVs instead of new developments of services from scratch.
- Middleware architectures are expected to have a holistic awareness of the underwater environment so as to adapt its decision/command for vehicles accordingly to the unreliable environment. Context awareness is highly needed and can be realized by an effective and efficient exploitation on data. Semantic capabilities can be added to embed semantics into gathered information, infer more useful knowledge, as well as support the collection and transmission of information to the cooperating AUVs/ROVs involved in specific underwater mission execution process.
- Added value capabilities (i.e., service discovery & registry, fault tolerance, security schemes, friendly user interface) should be encased in the underwater robotic middleware of the future. In this way, the middleware could possibly become suitable for “all settings” in real usages.
- Potential cooperation between different underwater vehicles adopting different underwater robotic middleware architectures should be considered. A major problem hindering the potential cooperation exists in the use of different information models (i.e., ontologies) in different middleware architectures. Ontology alignment or mapping should be addressed to achieve a homogeneous understanding between various middleware architectures.
- The underwater robotic middleware should be tested, validated and demonstrated in relevant and environmentally controlled scenarios under extreme conditions. Furthermore, a step forward trial experiments (i.e., open source licenses or commercial promotion) should be conceived to expand the utilization of underwater robotic middleware intermediation architectures.
- One module will be used as an interface with the electronic equipment collecting data from the environment. This module will be responsible for handling heterogeneity regarding robot manufacturers in a deployment.
- Another module will be used to interconnect the middleware architecture to the high level application that make use of the retrieved data.
- There will be other modules that deal with functionalities related to information management: device registration, publish/subscribe paradigm etc.
- Finally, more advanced features addressed in this survey, such as security and context awareness will be developed within their own modules. In this way, most of the challenges that have been mentioned here can be solved to a significant extent.
Acknowledgments
Conflicts of Interest
References
- Acosta, G.G.; Calvo Ibanez, O.A.; Curti, H.J.; Rozenfeld, A.F. Low-cost autonomous underwater vehicle for pipeline and cable inspections. In Proceedings of the Symposium on Underwater Technology and Workshop on Scientific Use of Submarine Cables and Related Technologies, Tokyo, Japan, 17–20 April 2007; pp. 331–336.
- Diercks, A.R.; Asper, V.L.; Highsmith, R.; Woolsey, M. MIUST—Deepwater horizon oil spill response cruise. In Proceedings of the OCEANS, Seattle, WA, USA, 20–23 September 2010; pp. 1–7.
- Kaninski, C.; Crees, T.; Ferguson, J.; Forrest, A. 12 days under ice-an historic AUV deployment in the Canadian high arctic. In Proceedings of the 2010 IEEE/OES Autonomous Underwater Vehicles (AUV), Monterey, CA, USA, 1–3 September 2010; pp. 1–11.
- Naur, P.; Randell, B. Software Engineering. NATO Software Engineering Conference 1968. Garmisch, Germany, 7–11 October 1968; Available online: http://homepages.cs.ncl.ac.uk/brian.randell/NATO/nato1968.PDF (accessed on 1 December 2015).
- Smart, W.D. Is a common middleware for robotics possible? In Proceedings of the IEEE/RSJ International Conference on Intelligent Robots and Systems Workshop on Measures and Procedures for the Evaluation of Robot Architectures and Middleware, San Diego, CA, USA, 29 October 2007.
- Mohamed, N.; AI-jaroodi, J.; Jawhar, I. Middleware for robotics: A survey. In Proceedings of the IEEE International Conference on Robotics, Automation, and Mechatronics, Chengdu, China, 21–24 September 2008; pp. 736–742.
- Mohamed, N.; AI-jaroodi, J.; Jawhar, I. A Review of Middleware for Networked Robots. IJCSNS 2009, 9, 139–148. [Google Scholar]
- Ceriani, S.; Miglianvacca, M. Middleware in Robotics. Internal Report for “Advanced Methods of Information Technology for Autonomous Robotics”. Available online: http://home.deib.polimi.it/gini/AdvancedRobotics/docs/CerianiMigliavacca.pdf (accessed on 2 February 2016).
- Namoshe, M.; Tlale, N.S.; Kumile, C.M.; Bright, G. Open middleware for robotics. In Proceedings of the 15th International Conference on Mechatronics and Machine Vision in Practice (M2VIP08), Auckland, New Zealand, 2–4 December 2008; pp. 189–194.
- Elkady, A.; Sobh, T. Robotics middleware: A comprehensive literature survey and attribute-based bibliography. J. Robot. 2012, 2012. [Google Scholar] [CrossRef]
- Nesnas, I.A.; Simmons, R.; Gaines, D. CLARAty: Challenges and steps toward reusable robotic software. Int. J. Adv. Robot. Syst. 2006, 3, 23–30. [Google Scholar]
- Collett, T.H.J.; MacDonald, B.A.; Gerkey, B. Player 2.0: Toward a practical robot programming framework. In Proceedings of the Australasian Conference on Robotics and Automation (ACRA), Sydney, Australia, 5–7 December 2005.
- Makarenko, A.; Brooks, A. Orca: Components for robotics. In Proceedings of IEEE/RSJ International Conference on Intelligent Robots and Systems, Beijing, China, 9–15 October 2006.
- Utz, H.; Sablatnog, S.; Enderle, S.; Kraetzschmar, G. Miro-middleware for mobile robot applications. IEEE Trans. Robot. Autom. 2002, 18, 493–497. [Google Scholar]
- Ohara, K.; Suzuki, T.; Ando, N. Distributed control of robotic functions using RT middleware. In Proceedings of the SICE-ICASE International Joint Conference, Busan, Korea, 18–21 October 2006; pp. 2629–2632.
- Magnenat, S.; Retornaz, P.; Bonani, M. ASEBA: A modular architecture for even-based control of complex robots. IEEE/ASME Trans. Mechatron. 2010, 16, 321–329. [Google Scholar]
- Cote, C.; Brosseau, Y.; Letourneau, D. Robotic software integration using MARIE. Int. J. Adv. Robot. Syst. 2006, 3, 55–60. [Google Scholar]
- Yoo, J.; Kim, S.; Hong, S. The Robot Software Communications Architecture (RSCA): QoS-aware middleware for networked service robots. In Proceedings of the International Joint Conference, Busan, Korea, 18–21 October 2006; pp. 330–335.
- Jang, C.; Lee, S.; Jung, S.W. OPRoS: A new component-based robot software platform. ETRI J. 2010, 32, 646–656. [Google Scholar] [CrossRef]
- Robot Operating System (ROS). Available online: http://www.ros.org/ (accessed on 20 November 2015).
- Jackson, J. Microsoft robotics studio: A technical introduction. IEEE Robot. Autom. Mag. 2007, 14, 82–87. [Google Scholar]
- Mallet, A.; Pasteur, C.; Herrb, M.; Lemaignan, S. GenoM3: building middleware-independent robotic components. In Proceedings of the IEEE International Conference on Robotics and Automation, Anchorage, AK, USA, 3–7 May 2010.
- Martinez Cruz, J.; Romero-Garces, A.; Bandera Rubio, J.P.; Bandera Rubio, A. Nerve: A lightweight middleware for quality-of-service networked robotics. In Proceedings of the 2011 8th International Conference on Information Technology: New Generations, Las Vegas, NV, USA, 11–13 April 2011.
- Einhorn, E.; Langner, T.; Stricker, R.; Martin, C. MIRA-middleware for robotic applications. In Proceedings of the 2012 IEEE/RSJ International Conference on Intelligent Robots and Systems, Vilamoura, Portugal, 7–12 October 2012.
- Pangercic, D.; Pitzer, B.; Tenorth, M.; Beetz, M. Semantic object maps for robotic housework-represenation, acquisition and use. In Proceedings of the 2015 34th Chinese Control Conference, Hangzhou, China, 28–30 July 2015; pp. 5119–5124.
- Casan, G.A.; Cervera, E.; Moughlbay, A.A. ROS-based online robot programming remote education and training. In Proceedings of the 2015 IEEE International Conference on Robotics and Automation, Seattle, WA, USA, 26–30 May 2015; pp. 6101–6106.
- Zhang, S.; Sun, L.; Chen, Z.L. A ros-based smooth motion planning scheme for a home service robot. In Proceedings of the 2015 34th Chinese Control Conference, Hangzhou, China, 28–30 July 2015; pp. 5119–5124.
- Monajjemi, V.; Wawerla, J.; Vaughan, R. “Drums”: A middleware-aware distributed robot monitoring system. In Proceedings of the 2014 Canadian Conference on Computer and Robot Vision, Montreal, QC, Canada, 6–9 May 2014; pp. 211–218.
- Planthaber, S.; Vogengesang, J.; Nieben, E. CoHoN: A middleware for robots in heterogeneous communication environments with changing topology. In Proceedings of the 2011 IEEE International Conference on Robotics and Biomimetics, Phuket, Thailand, 7–11 December 2011.
- RAUVI: Reconfigurable AUV for Intervention Missions Project. Available online: http://www.robot.uji.es/lab/plone/projects/rauvi/ (accessed on 2 February 2016).
- Palomeras, N.; Garcia, J.M.; Prats, M.; Fernández, J.J.; Sanz, P.J.; Ridao, P. A Distributed Architecture for Enabling Autonomous Underwater Intervention Missions. In Proceedings of the 2010 4th Annual IEEE Systems Conference, San Diego, CA, USA, 5–8 April 2010; pp. 159–164.
- Murata, T. Petri Nets: Properties, Analysis and Applications. Proc. IEEE 2002, 77, 541–580. [Google Scholar]
- The Pandora Persistently Autonomous Robots Project. Available online: http://persistentautonomy.com/ (accessed on 20 November 2015).
- Insaurralde, C.C.; Cartwright, J.J.; Petillot, Y.R. Cognitive Control Architecture for Autonomous Marine Vehicles. In Proceedings of the 2012 IEEE International Systems Conference (SysCon), Vancouver, BC, Canada, 19–22 March 2012; pp. 1–8.
- KnowRob. Available online: http://www.knowrob.org/ (accessed on 2 February 2016).
- Tenorth, M.; Beetz, M. KnowRob: A knowledge processing infrastructure for cognition-enabled robots. Int. J. Robot. Res. 2013, 32, 566–590. [Google Scholar]
- Tenorth, M.; Beetz, M. Representations for robot knowledge in the KnowRob. Artif. Intell. 2015. [Google Scholar] [CrossRef]
- Mullane, J.; Vo, B.; Adams, M.D. Rao-Blackwellised PHD SLAM. In Proceedings of the IEEE International Conference on Robotics and Automation, Anchorage, AK, USA, 3–8 May 2010.
- PHD/SLAM. Available online: http://persistentautonomy.com/wp-content/uploads/2015/07/D1.2.pdf (accessed on 14 January 2016).
- The TRIDENT (Marine Robots and Dexterous Manipulation for Enabling Autonomous Underwater Multipurpose Intervention Missions) Project. Available online: http://www.irs.uji.es/trident/aboutproject.html (accessed on 2 February 2016).
- Miguelañez, E.; Patron, P.; Brown, K.E.; Petillot, Y.R.; Lane, D.M. Semantic Knowledge-Based Framework to Improve the Situation Awareness of Autonomous Underwater Vehicles. Knowl. Data Eng. IEEE Trans. 2015, 23, 759–773. [Google Scholar] [CrossRef]
- The SUNRISE: Building the Internet of Underwater Things Project. Available online: http://fp7-sunrise.eu/ (accessed on 2 February 2016).
- The SUNRISE GATE: Accessing the SUNRISE Federation of Facilities to Test Solutions for the Internet of Underwater Things. Available online: http://fp7-sunrise.eu/Files/OpenCalls/SUNRISE_GATE_description.pdf (accessed on 2 February 2016).
- The CoCoRo (Collective Cognitive Robots) Project. Available online: http://cocoro.uni-graz.at/drupal/home (accessed on 2 February 2016).
- Hereford, J.M. Analysis of a new swarm search algorithm based on trophallaxis. In Proceedings of the IEEE Congress on Evolutionary Computation, Barcelona, Spain, 18–23 July 2010; pp. 1–8.
- Bonabeau, E. Inspiration for optimization from social insect behavior. Nature 2000, 406, 39–42. [Google Scholar] [PubMed]
- Monismith, D.R.; Mayfield, B.E. Slime mold as a model for numerical optimization. In Proceedings of the IEEE Swarm Intelligence Symposium, St. Louis, MO, USA, 21–23 September 2008; pp. 1–8.
- Baptista, F.D.; Rodrigues, S.; Morgado-Dias, F. Performance comparison of ANN training algorithms for classification. In Proceedings of the IEEE 8th International Symposium on Intelligent Signal Processing, Funchal, Portugal, 16–18 September 2013; pp. 115–120.
- Bai, Q.H. Analysis of particle swarm optimization algorithm. Comput. Inf. Sci. 2010, 3. [Google Scholar] [CrossRef]
- Bastos Filho, C.J.A.; de Lima Neto, F.B.; Lins, A.J.C.C. A novel search algorithm based on fish school behavior. In Proceedings of the IEEE International Conference on System, Man and Cybernetics, Singapore, 12–15 October 2008; pp. 2646–2651.
- Schmickl, T.; Moslinger, C.; Thenius, R. CoCoRo-A self-aware swarm of underwater vehicles. Aware. Self Aware. Autonomous Syst. 2011. [Google Scholar] [CrossRef]
- The subCULTron Project. Available online: http://www.subcultron.eu/ (accessed on 13 December 2015).
- Rajan, K.; Py, F.; McGann, C. Adaptive Control of AUVs Using Onboard Planning and Execution. Available online: http://sea-technology.com/features/2010/0410/adaptive_control_auvs.html (accessed on 2 February 2016).
- T-REX Exercise. Available online: http://rep13.lsts.pt/en/about/exercise (accessed on 21 January 2016).
- Goldberg, D. Huxley: A flexible robot control architecture for autonomous underwater vehicles. In Proceedings of the IEEE OCEANS, Santander, Spain, 6–9 June 2011; pp. 1–10.
- Huxley Running Environment. Available online: http://www.bluefinrobotics.com/media/press/moos-ivp-the-open-source-backseat-driver-software-successfully-demonstrated-on-bluefin-9/ (accessed on 21 January 2016).
- Huang, A.S.; Olson, E.; Moore, D.C. LCM: Lightweight communications and marshalling. In Proceedings of the IEEE/RSJ International Conference on Intelligent Robots and Systems (IROS), Taipei, Taiwan, 18–22 October 2010; pp. 4057–4062.
- Computer Science and Artificial Intelligence Laboratory Technical Report: Lightweight Communications and Marshalling for Low-Latency Interprocess Communications. Available online: http://dspace.mit.edu/bitstream/handle/1721.1/46708/MIT-CSAIL-TR-2009–041.pdf?sequence=1 (accessed on 2 February 2016).
- Srinivasan, R. XDR: External Data Representation Standard. Internet Engineering Task Force, RFC 1832. Available online: http://dl.acm.org/citation.cfm?id=RFC1832 (accessed on 14 December 2015).
- Kalwa, J.; Carreiro-Silva, M.; Tempera, F.; Fontes, J.; Santos, R.S.; Fabri, M.C.; Brignone, L.; Ridao, P.; Birk, A.; Glotzbach, T.; et al. The MORPH concept and its application in marine research. In Proceedings of 2013 MTS/IEEE OCEANS Conference, Bergen, Norway, 10–14 June 2013; pp. 1–8.
- Newman, P.M. MOOS—Mission Orientated Operating Suite; Massachusetts Institute of Technology: Cambridge, MA, USA, Technical Report; 2008; Volume 2299. [Google Scholar]
- Maurelli, F.; Saigol, Z.A.; Papadimitriou, G. Probabilistic approaches in ontologies: Joining semantics and uncertainty for AUV persistent autonomy. In Proceedings of the Oceans, San Diego, CA, USA, 23–27 September 2013; pp. 1–6.
- Bobillo, F.; Straccia, U. Fuzzy ontology representation using OWL 2. Int. J. Approx. Reason. 2011, 52, 1073–1094. [Google Scholar]
© 2016 by the authors; licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons by Attribution (CC-BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Li, X.; Martínez, J.-F.; Rodríguez-Molina, J.; Martínez, N.L. A Survey on Intermediation Architectures for Underwater Robotics. Sensors 2016, 16, 190. https://doi.org/10.3390/s16020190
Li X, Martínez J-F, Rodríguez-Molina J, Martínez NL. A Survey on Intermediation Architectures for Underwater Robotics. Sensors. 2016; 16(2):190. https://doi.org/10.3390/s16020190
Chicago/Turabian StyleLi, Xin, José-Fernán Martínez, Jesús Rodríguez-Molina, and Néstor Lucas Martínez. 2016. "A Survey on Intermediation Architectures for Underwater Robotics" Sensors 16, no. 2: 190. https://doi.org/10.3390/s16020190
APA StyleLi, X., Martínez, J.-F., Rodríguez-Molina, J., & Martínez, N. L. (2016). A Survey on Intermediation Architectures for Underwater Robotics. Sensors, 16(2), 190. https://doi.org/10.3390/s16020190








