1. Introduction
With the arrival of the era of Internet of Things (IoT), the widespread use of internet-enabled devices has led to a drastic increase in mobile data traffic. In recent years, there has been research on communication algorithms considering various data traffic characteristics for IoT networks [
1,
2,
3,
4,
5,
6]. Qinghe et al. applied the ultra-narrow band (UNB) technique to wireless clinical networks and proposed the corresponding massive access scheme, which is called hybrid periodic-random massive access (HPRMA), for co-existing periodic and random services [
1]. In HPRMA, the number of UNB channels allocated to periodic and random services can be dynamically tuned according to traffic load information and diverse services can be simultaneously aligned with their periodic requirements. Hongliang et al. proposed a traffic-aware access class barring (TAACB) scheme to improve the scalability of machine-to-machine networks [
2]. In TAACB, it is possible to accommodate more devices ensuring low access delay by regulating the parameter of access probability based on network traffic load. Qinghe et al. proposed the peer-to-peer share enabled routing schemes over multi-hop interference-constrained device-to-device networks, where multiple subscribers attempt to download the common data load from multiple distributed servers [
3]. Maria et al. proposed a novel traffic aware scheduling algorithm (TASA) by extending the theoretically well-established graph theory methods based on network topology and traffic load [
4]. Navrati et al. identified the complexity of the optimal traffic awareness in cloud radio access networks and designed a framework for traffic-aware energy optimization [
5]. Nicola et al. presented a new decentralized traffic-aware scheduling algorithm, which is able to construct optimal multi-hop schedules in a distributed fashion, and proved its effectiveness by means of simulation results in IoT-compliant multi-hop networks [
6]. In particular, to prevent base stations from being overloaded owing to the rapid increase in data traffic, there has been research on traffic load balancing methods using direct communication between mobile devices [
7]. In this context, it is believed that Wi-Fi Direct is suitable for IoT networks, in which a connection between any two devices is created without going through a wireless router or a repeater [
8].
For short-distance direct communications, Wi-Fi Direct is comparable with other technologies such as ZigBee and particularly Bluetooth that is widely used for communication between mobile devices. When a Wi-Fi chip that supports IEEE 802.11n is utilized [
9], it transmits data at transfer rates as high as 250 Mbps that is 10 times higher than 24 Mbps, the maximum transfer rate of the currently used Bluetooth 4.0. The transfer distance is 100 m, which is ten times longer than that of Bluetooth [
10].
Devices connected to the Wi-Fi Direct are classified into the group of owner (GO) and the client. The GO functions as an access point (AP) in an existing Wi-Fi network, while the clients are connected through the GO. Clients can communicate only via the GO, either one-to-one or one to
N [
11]. The GO consumes more energy than the clients, as it has to perform certain functions such as beaconing and forwarding [
12]. While research on the method to save the energy in terminals connected to an AP in an existing infrastructure Wi-Fi network has been conducted, there has been little research on the AP power-saving because a constant power supply is assumed for the APs. As the GO plays the role of an AP in the Wi-Fi Direct, it should be portable and is therefore limited by the battery capacity. Thus, the usage of the opportunistic method and the NoA method for power-saving in the GO has been suggested [
13].
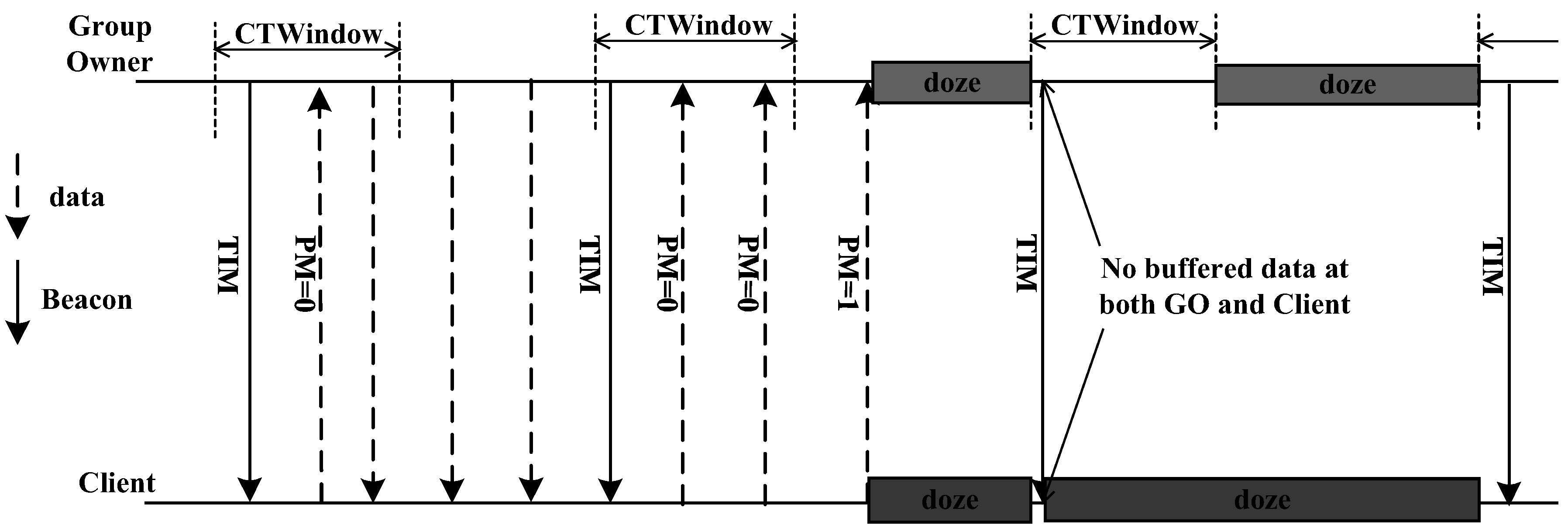
Figure 1 shows the opportunistic power-saving method. As the GO sends beacon TIMs (Traffic Indication Messages) regularly to the clients, they are awakened in the section of CT Window (Client Traffic Window) for data transfer. If data transmission is completed before the section of the CT Window ends, the GO and the clients go into the sleep mode upon the end of CT Window. If the GO continues to have more data to send after the end of CT Window, it continues transferring and the clients do not enter the sleep mode until the data transmission is completed. When a client has data to transfer to the GO, the power management bit in the data is set to 0 (PM = 0). At the last data transmission, the power management bit in the data is set to 1 (PM = 1) for notifying that data transmission is completed. If the GO receives a data with PM = 1 during the section of the CT Window, it enters the sleep mode after the Window. If it does not receive a data with PM = 1 even after the CT Window ends, the GO remains awake until it receives the data with PM = 1. Thereafter, it stays in the sleep mode until the next beacon interval [
14].
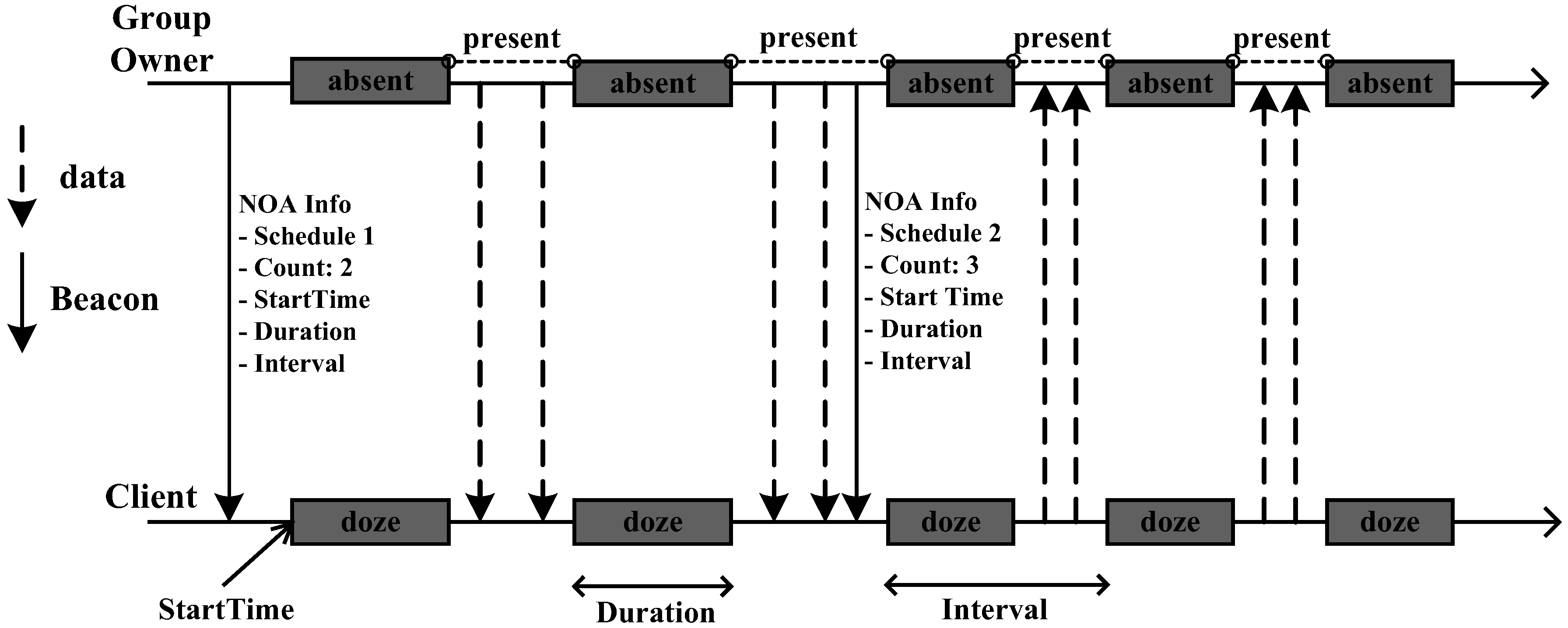
Figure 2 shows the NoA method. While the opportunistic method transmits and receives data mainly in the CT Window after the GO sends a beacon, the NoA method
dynamically determines the number of active/absence periods and its duration in a beacon interval. In the NoA method, the GO sends to the clients the scheduling information of a beacon interval such as the start time of the first absence period, the duration of each absence period, time interval between the absence periods, the number of absence periods in a beacon interval, etc. as part of the beacon message. Clients connect to the GO, then avoid sending data in these absence periods, and the GO enters the sleep mode during the absence periods to save energy [
13] .
Various research related to the Wi-Fi Direct power-saving methods has been conducted. In [
14], the authors have proposed a new power management system that changes the power management methods depending on the traffic characteristic and have verified through experiments that it is efficient to apply the NoA method for the traffics with periodic characteristic, and to apply the opportunistic method for the traffic with bursty characteristics. In [
15], the TAPS (Traffic Awake Parameter tuning Scheme) method that adjusts the parameters dynamically depending upon the traffic load has been proposed and the algorithm to express the GO parameters (CT Window, awake interval, etc.) in traffic flow functions has been developed. Experiment results show that the TAPS method equilibrated the trade-off relationship between the energy and throughput. The author of [
12] has suggested two traffic-based dynamic management methods: the adaptive single present period (ASPP) method and the adaptive multiple present period (AMPP) method. These two methods adopt an algorithm that schedules the awake intervals of the GO at each beacon interval based on the traffic activity (utilization) for the purpose of energy saving. Reference [
16] proposes an algorithm that takes into account both the energy and the delay for an application with periodic streaming traffics. This algorithm supports two functions for utilization of the existing opportunistic method. The first function is for recognizing the patterns of data sets that are transferred in Wi-Fi Direct frame and the second function is for awakening a device instantly during a sleep interval and receiving periodic data by adjusting the duty cycle dynamically. This function defines the temporary CT window (TCTW) and is applied to the opportunistic method.
In this paper, we propose a method to enhance the energy efficiency of the Wi-Fi Direct power-saving considering the characteristics of variable bit rate (VBR) video traffic. The suggested method determines the number of and the length of awake intervals in a beacon interval reflecting the probability density function (pdf) of the size of video frames so as to reduce unnecessary energy consumption and transmission delay. In addition, the proposed method prioritizes the frame transmission per frame class by considering the inter-dependence between the video frames with the purpose of increasing the success probability of a high priority video frame transmission and thus enhancing the transmission efficiency.
2. Video Traffic Model
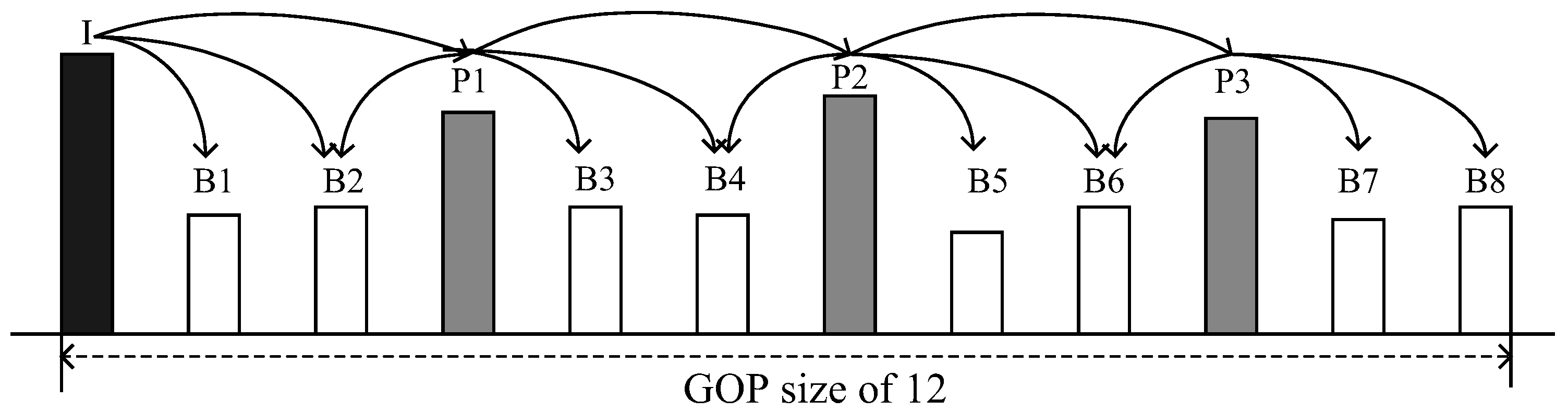
The VBR video traffic consists of three types of video frames: Intra (I), Predictive (P), and Bi-directional (B). As shown in
Figure 3, the frames are arranged in pre-determined patterns from an
I-frame to the next, called a group of picture (GoP) structure. The GoP structure is expressed mainly as MmNn, where n indicates the total number of frames in the GoP and m indicates the
I-P or
P-
P-frame interval [
17]. All the frames with the exception of the
I-frame are encoded based on the dependency among the adjacent frames, while the
I-frames are encoded as they are without referring to other images.
P-frames are encoded with reference to the previous
I-frame or
P-frame, while
B-frames refer to the previous and following
I-frame and (or)
P-frame. Thus, when an
I-frame is lost, all frames in the GoP are lost. When a
P-frame is lost, all of the following
P- and
B-frames are lost. In contrast, when a
B-frame is lost, it does not affect the other frames [
18]. To sum up, the listing of the frames in descending order according to their significance is as follows:
I-frame,
P-frame, and
B-frame.
The I-frame gamma autoregressive (I-GAR) model proposed for the asynchronous transfer mode (ATM) network moving picture experts group (MPEG) streams shows some characteristics on the distribution of the video frame size [
19]. Since a GoP has only one
I-frame and
I-frame is encoded independently regardless of the other frames,
I-frame does not include a motion compensation functionality that is used to reduce the frame size, so
I-frame is usually larger than the
B-frame and
P-frame in size. Thus, in the
I-GAR model, the distribution of
I-frame size is selected as the basis, and it is shown that the pdf of
I-frame size follows the gamma distribution and the pdfs of the
B-frame and
P-frame sizes are expressed also as gamma distributions with the scalar products to the rate parameter of the gamma distribution of
I-frame size [
19].
Let the random variables denoting the size of
I-frame,
P-frame and
B-frame be
,
, and
, respectively. From [
19], the pdfs of the each frame size are given by
where
and
. Here, the expectations of
,
, and
are calculated by
The variances of
,
, and
are calculated by
3. Proposed Power-Saving Method for Video Traffic
This chapter explains the proposed power-saving method in the Wi-Fi Direct for the VBR video traffic model. The key idea of the power-saving method proposed in this study is that the scheduling of a beacon interval (the number of and the length of the awake intervals in a beacon interval) is determined dynamically, considering the distribution of the video frame size and the priority of the video frame.
3.1. Beacon Interval Scheduling in the Proposed Method
In this subsection, we describe the detailed method to determine the number of awake intervals in a beacon interval and the length of each awake interval. The number of awake intervals in a beacon interval are set so as to satisfy the one-to-one mapping relation between each awake interval and each video frame; i.e., a single awake interval is allotted to one video frame. The length of an awake interval is decided per frame class. Thus, there exists awake intervals for I-frames, P-frames, and B-frames, respectively. Hereafter, we call the awake intervals assigned to I-frames, P-frames, and B-frames as the I-frame interval, P-frame interval, and B-frame interval, respectively. The detailed algorithm to determine the length of the x-frame (Here, x-frame may be I-, P-, or B-frame) interval is presented as follows.
At first, the GO sets the target probability, , for x-frame. The target probability of the x-frame indicates the probability that the x-frame can be transmitted wholly in the x-frame interval, so there is no segmentation or frame drop due to the short awake interval compared to the frame size. For instance, if the target probability of the I-frame, , is set to , then it means that the probability of a whole I-frame being transferred without any segmentation or frame drop in the I-frame interval is 95%, and some I-frames cannot be wholly sent in the I-frame interval owing to its large size, with a probability of .
From the above definition, once
is determined, we can get the following expression for a certain positive real number per
x-frame,
, by
Here,
indicates the largest size of the
x-frame being able to be wholly transferred in the
x-frame interval.
is a variable decided by the network operator, and, in this study, it is determined with reference to the average and variance of the frame size distribution of each frame class, which is given by
where
c is the scale factor that controls the value of
. The schematic illustration of
and
is given in
Figure 4.
Finally, the length of the awake interval for
x-frame as a function of the scale factor
c is calculated by
where
v is the data rate of the given channel.
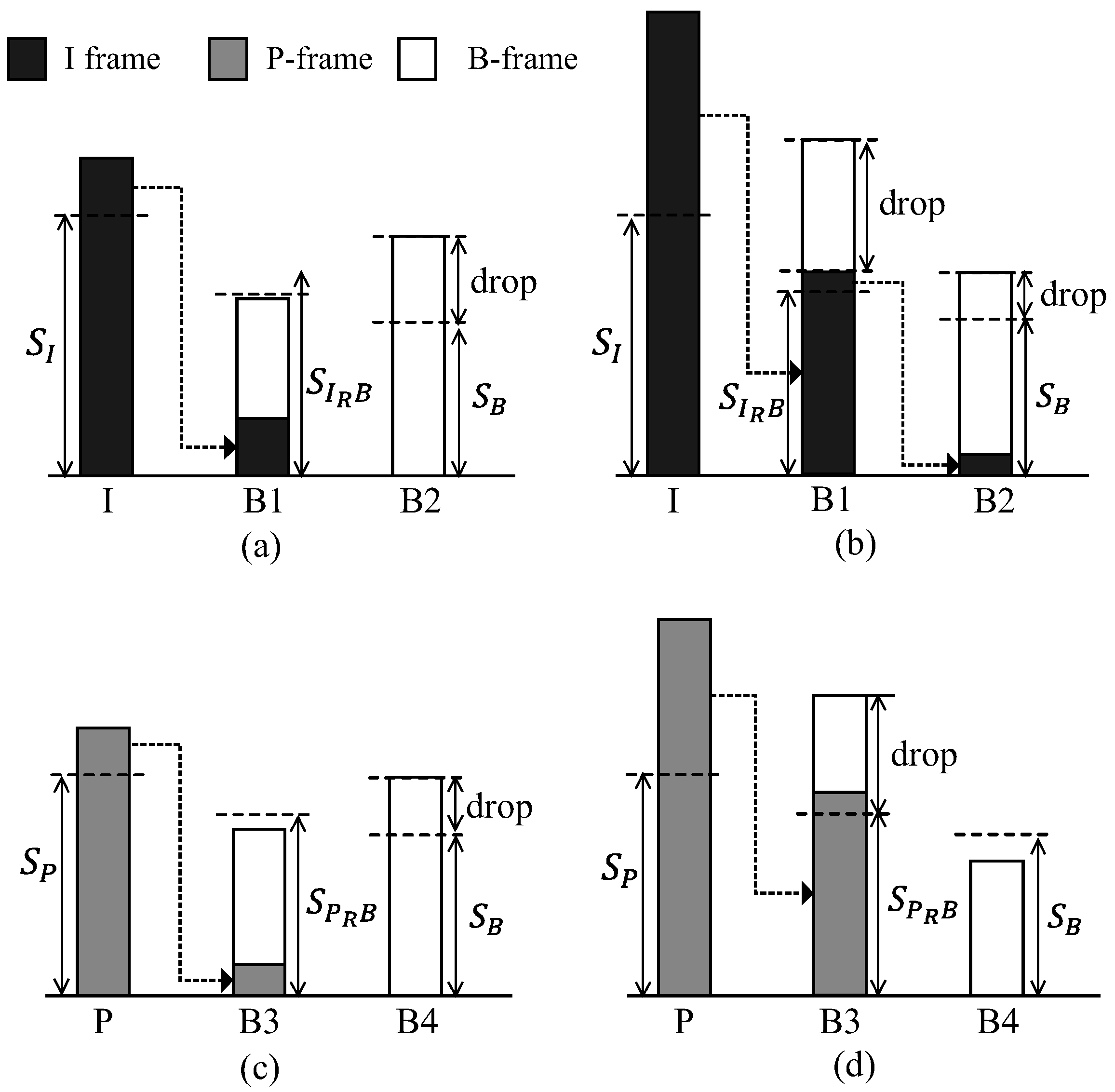
3.2. Frame Transmission Strategy Based on the Frame Priority
From the definition of
,
x-frames with a size larger than
cannot be wholly transmitted during the
x-frame interval with the probability of
. In this case, there exists a remaining fraction of the frame and the method of dealing with the remaining fraction of the frame is different depending upon the priority of each frame. First,
I-frame has the highest priority, and thus the remaining fraction of the
I-frame is concatenated with the immediately following
-frame and transmitted along with the
-frame in the
-frame interval, in order to enhance the transmission success probability of the
I-frame, as seen in
Figure 5a. If
-frame interval is unable to accommodate the remaining fraction of the
I-frames, the remaining fraction of the
I-frame in
-frame interval is again concatenated with the
-frame and is transmitted in the
-frame interval, while the whole
-frame is dropped, as seen in
Figure 5b.
As shown in
Figure 3,
P-frame has the second highest priority. Thus, similar to the case of the
I-frame, the remaining fraction of the
P-frame not being transferred in its
P-frame interval is transmitted in the following
B-frame interval (
-frame interval in
Figure 5c). However, unlike to the case shown in
Figure 5b, the proposed method does not transfer the remaining fraction of the
P-frame not being accommodated in the
-frame interval to the next
B-frame interval (
-frame interval in
Figure 5d), but insists on it being dropped.
Finally, the oversized B-frames is dropped because of its low priority.
5. Results
To evaluate the performance of the proposed method, we execute the Monte Carlo simulation runs with
GoP frames. The implementation of a testbed by using real devices reveals additional constraints issues in relation to power consumption due to the limitations of devices [
20] and additional power consumption such as standby power of devices [
21]. In this paper, the validity of the proposed method is verified via numerical method and simulation in order to exclude the impact of the additional constraints in relation to power consumption and focus on the performance evaluation of the proposed method. The simulation setup is as follows: as VBR traffic, a video codec with 25 fps and the GoP pattern of
is assumed. Therefore, we have
,
, and
= 8. The frame interval in a GoP structure,
f, is set to 40 ms, and the beacon interval is set to 120 ms so that each beacon interval could transfer consecutive three video frames. From [
19],
and
are used for the gamma distribution of
I-frame size. The scale factors for the distribution of the
B- and
P-frame sizes are set as
and
, respectively. The channel speed is set to 6 Mbps from [
22]. The values of
and
are obtained from [
12], and
is obtained from [
20]. Simulation parameters used in our study is summarized in
Table 1.
For the performance evaluation, we measure the average delay per frame and the average energy consumption per frame using both the proposed method and the NoA method. Here, we compare the performance of the proposed method with that of the NoA method other than the opportunistic method because the video traffic considered in this study is predictable in the sense that the traffic is generated periodically, and is therefore more suitable for the NoA method than the opportunistic method.
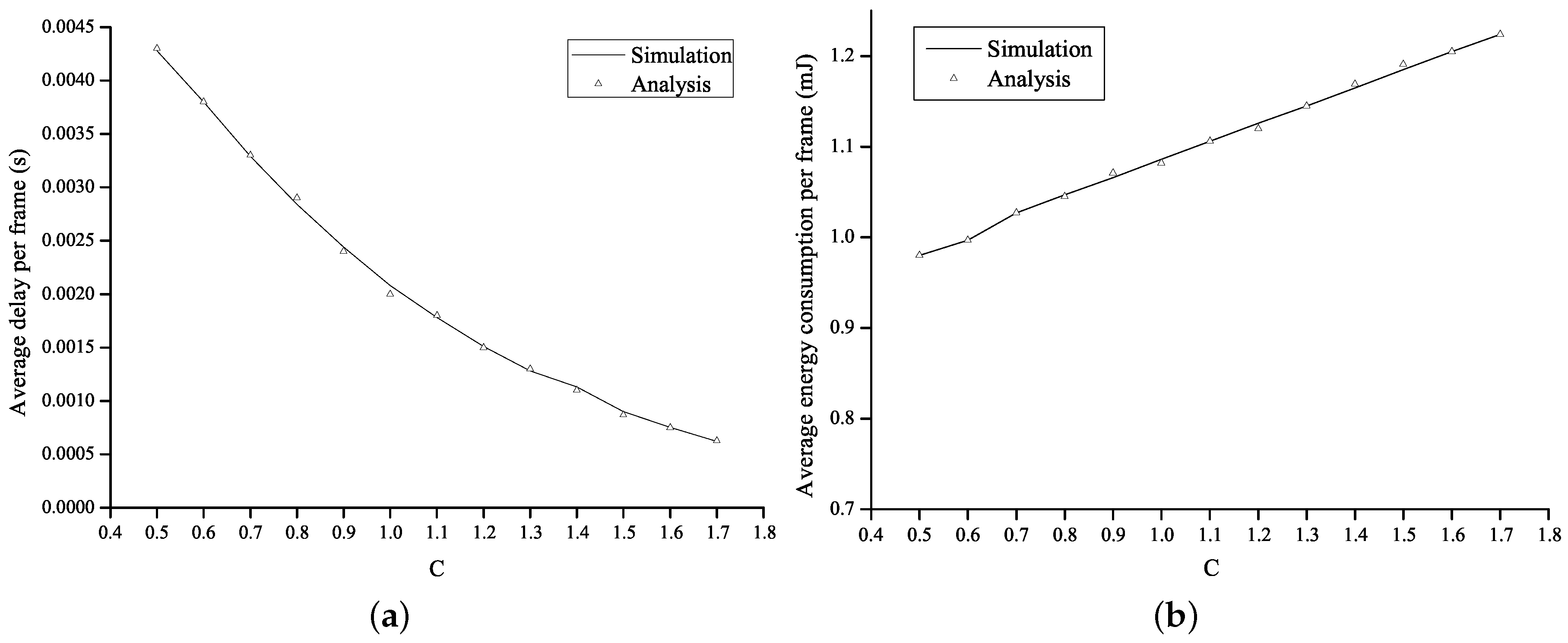
Figure 6 shows the average energy consumption per frame and the average delay per frame as a function of the value of
c in the proposed method. The operational parameter
c is set to range from
to
.
Figure 6a shows that, as
c increases, the awake interval is extended so that the number of the frame transmission failure decreases. As a result, the average delay is shortened. However, as the awake interval is extended in proportion to the value of
c, more energy was consumed, as shown in
Figure 6b.
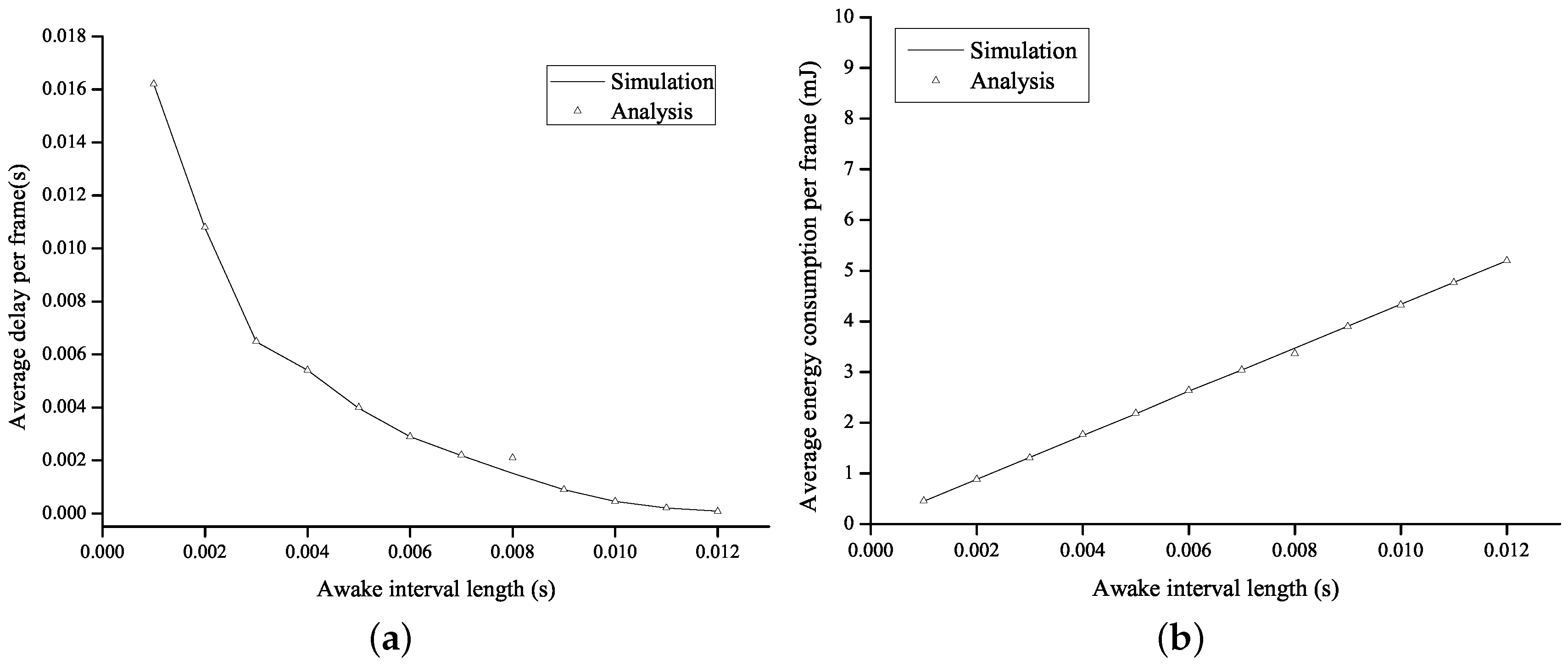
Figure 7 shows the average energy consumption per frame and the average delay per frame as a function of the length of the awake interval in the NoA method. In the proposed method, the shortest and the longest awake intervals correspond to the
B-frame interval with
and the
I-frame interval with
, respectively. To compare the performance of the NoA method with that of the proposed method under the same environment, the length of the awake interval in the NoA method is set to a range of 1–12 ms, which includes the shortest and the longest awake intervals in the proposed method. We can verify the trade-off relation between the energy consumption of a node and the transmission delay from
Figure 7, so that the average energy consumption increases as the length of the awake interval increases and the average delay decreases accordingly.
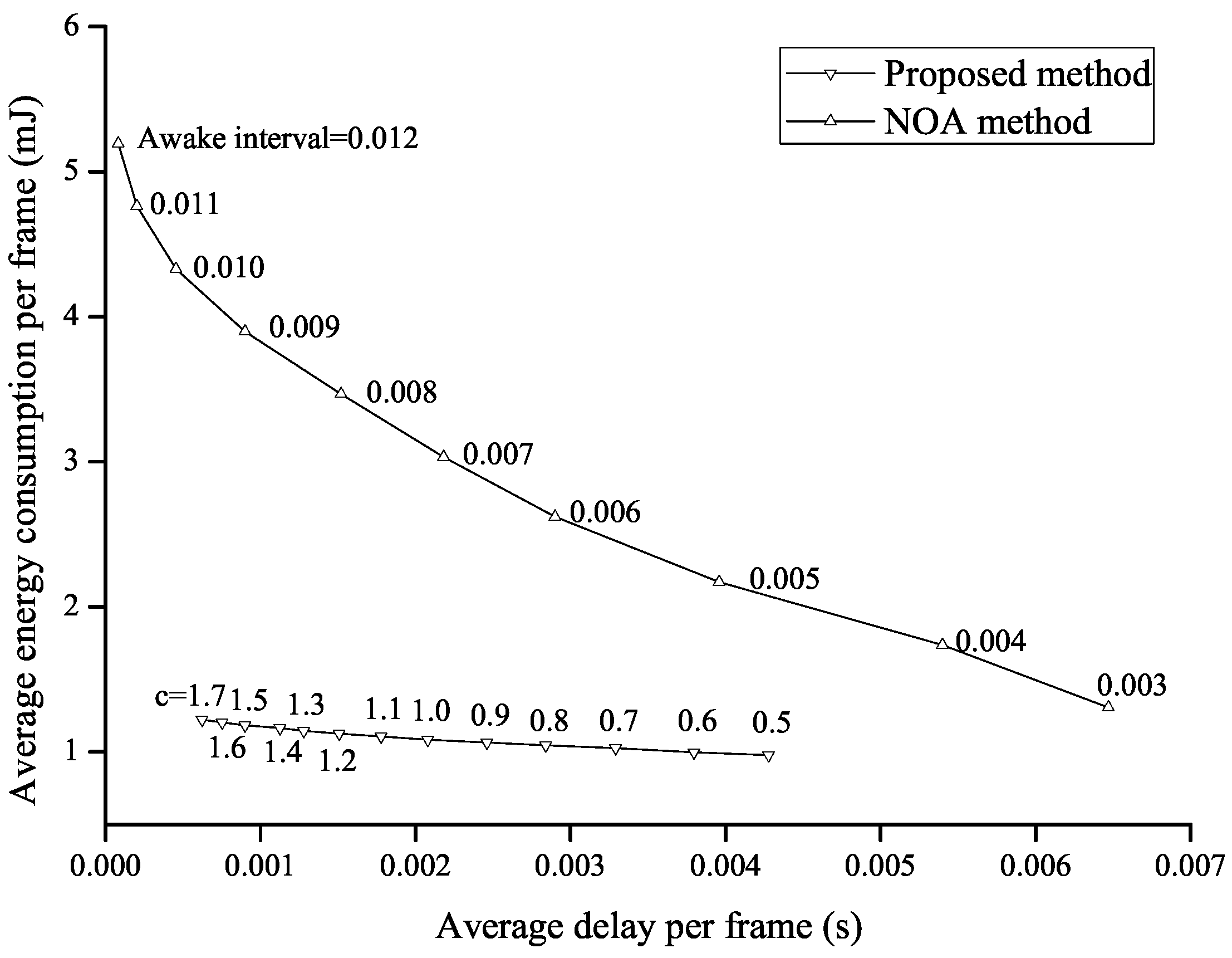
In
Figure 8, the performance of the proposed method is directly compared to that of the NoA method in terms of the average delay per frame and the average energy consumption per frame. Every point on each curve can be obtained by varying the value of
c in the proposed method or by varying the length of the awake interval in the NoA method. The energy-delay trade-off relation is shown in both of the methods, and the energy consumption decreases as the average delay increases. It is noticed that the inner curve shows better tradeoff performances, i.e., both the energy consumption and the delay are smaller than those of the outer curve. The outer curve is given by the NoA method, and the inner curve is given by the proposed method. This implies that the proposed method enhances the overall performance and shows better performance than the NoA method.
6. Conclusions
In this paper, we propose an algorithm for scheduling a beacon interval based on the video frame size distribution in order to enhance energy efficiency. The proposed method schedules a beacon interval so that one awake interval is mapped to one video frame, and determines the length of the awake interval per frame class considering the distribution functions of the sizes of I-frame, P-frame, and B-frame. In addition, considering the fact that video frames are prioritized due to mutual dependency, it is set that a frame having high priority is transmitted with higher probability than a frame having lower priority by making the remaining fraction of the high priority frame be concatenated and transmitted with the following next frame. Simulation runs are conducted to compare the performance of the proposed method with that of the NoA method, and it is shown that the proposed method shows a better performance than the NoA method in terms of the average energy consumption and the average delay. On the other hand, the proposed algorithm in this work assumed that there is a single client associated with the GO. However, there may be multipl clients that share the same traffic characteristics, and thus it would be our important future work to extend the proposed algorithm for multiple clients. Furthermore, we have a plan to develop the appropriate power-saving algorithm for various traffic other than video traffic, which will be another important future work. In addition, we will evaluate the performance of proposed method in a real testbed in order to verify the validity of the proposed method and possible constraints in relation to power consumption.
multiple