Butterfly Encryption Scheme for Resource-Constrained Wireless Networks †
Abstract
:1. Introduction
2. Related Work
3. Butterfly Encryption Scheme
3.1. Butterfly Seed Generation Algorithm
3.2. Encryption Scheme Employing Butterfly Seed Generation
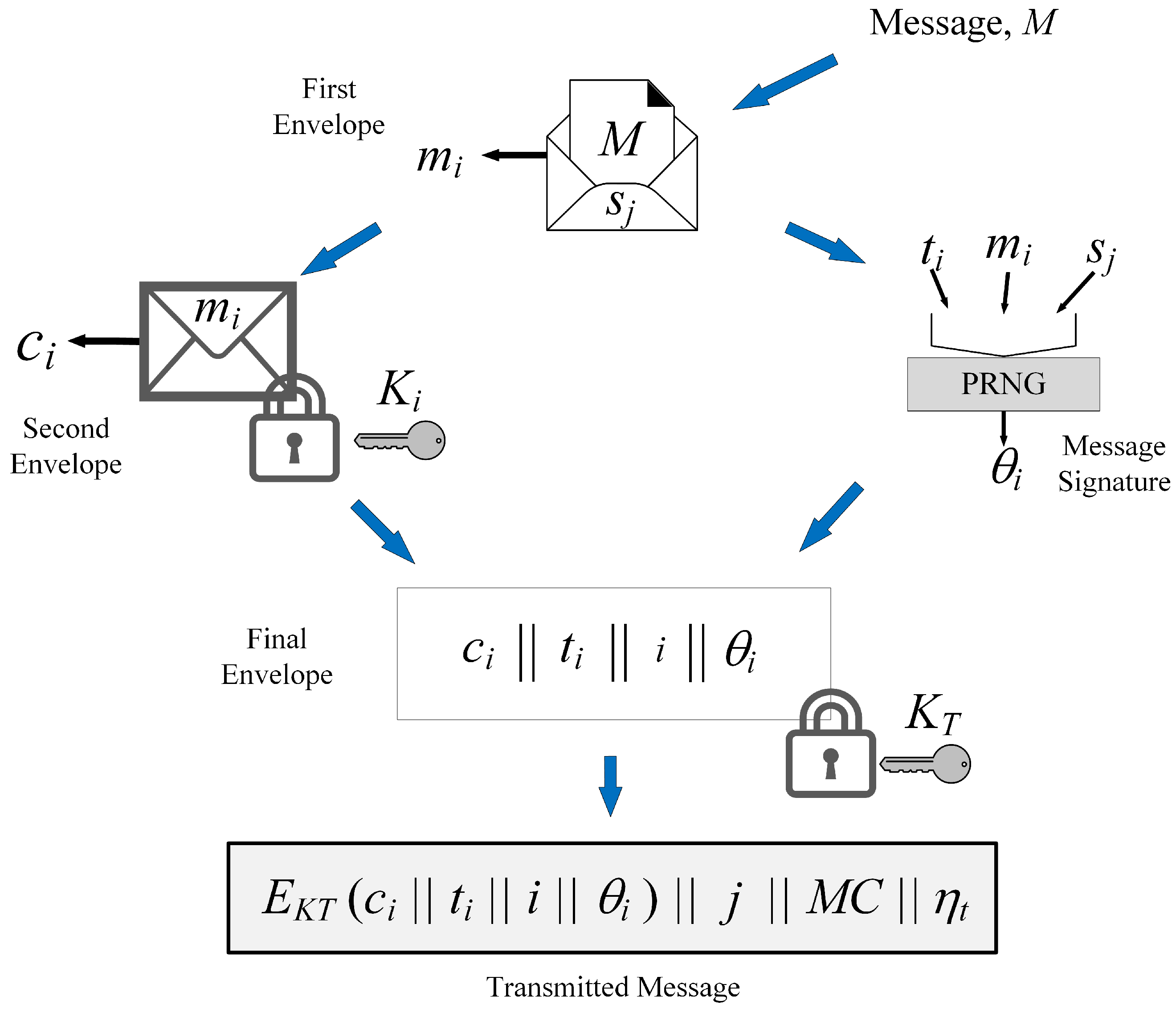
3.2.1. Preliminaries
3.2.2. Protocol of Operation
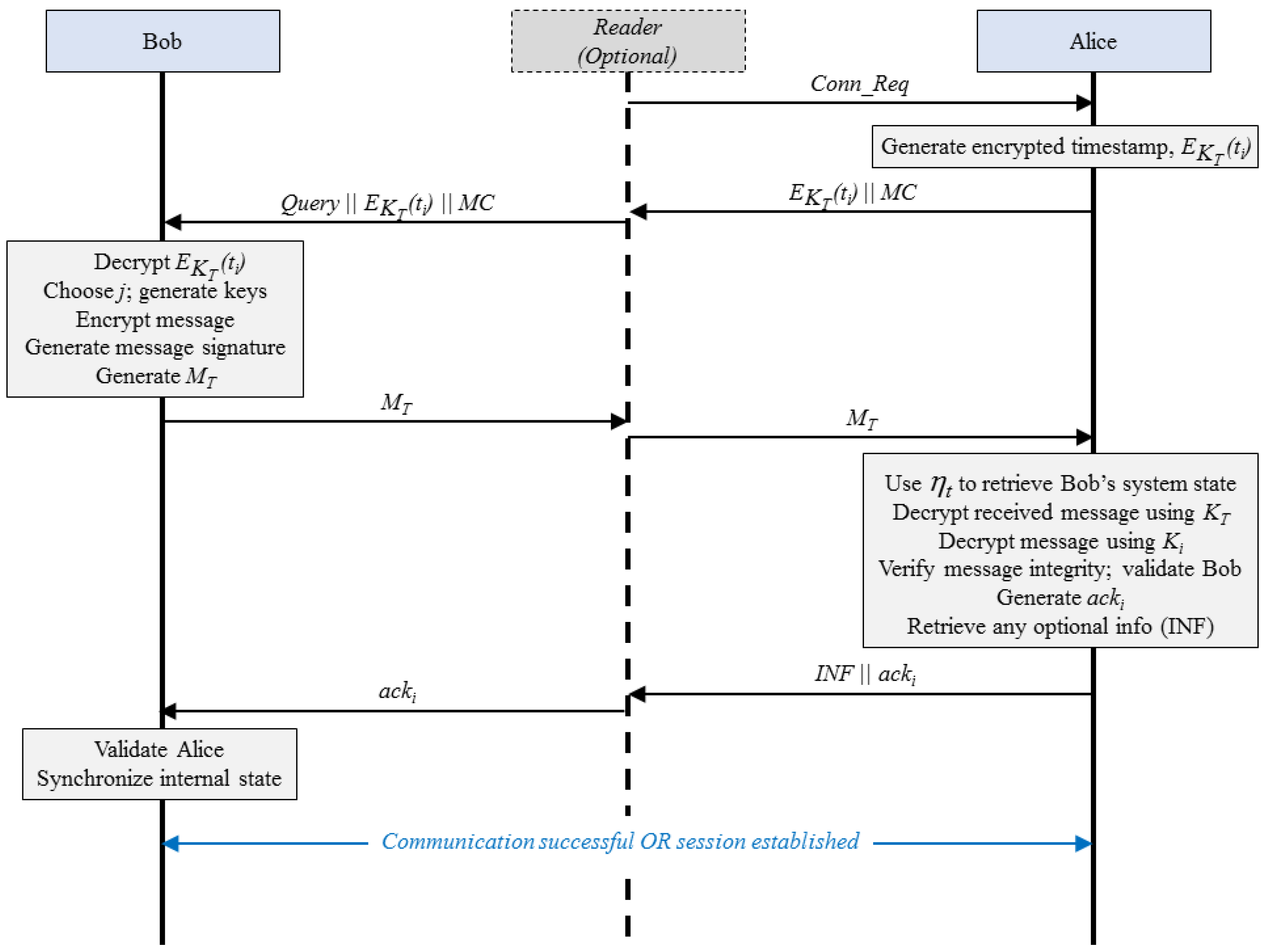
3.2.3. Decryption
3.2.4. Seed Refresh
| Algorithm 1: Key Generation and Encryption in the Butterfly Encryption Scheme |
| Input: Seed bit identifier (j), updated seed (), timestamp (). Output: Transmitted message () or Seed update response (). Choose j; ; ; ; //Choose appropriate message code (2 bits): if (First message, ) then ; else if (Response, ) then ; else if (ACK, ) then ; else if (Special message) then ; ; ; ; if or or then
|
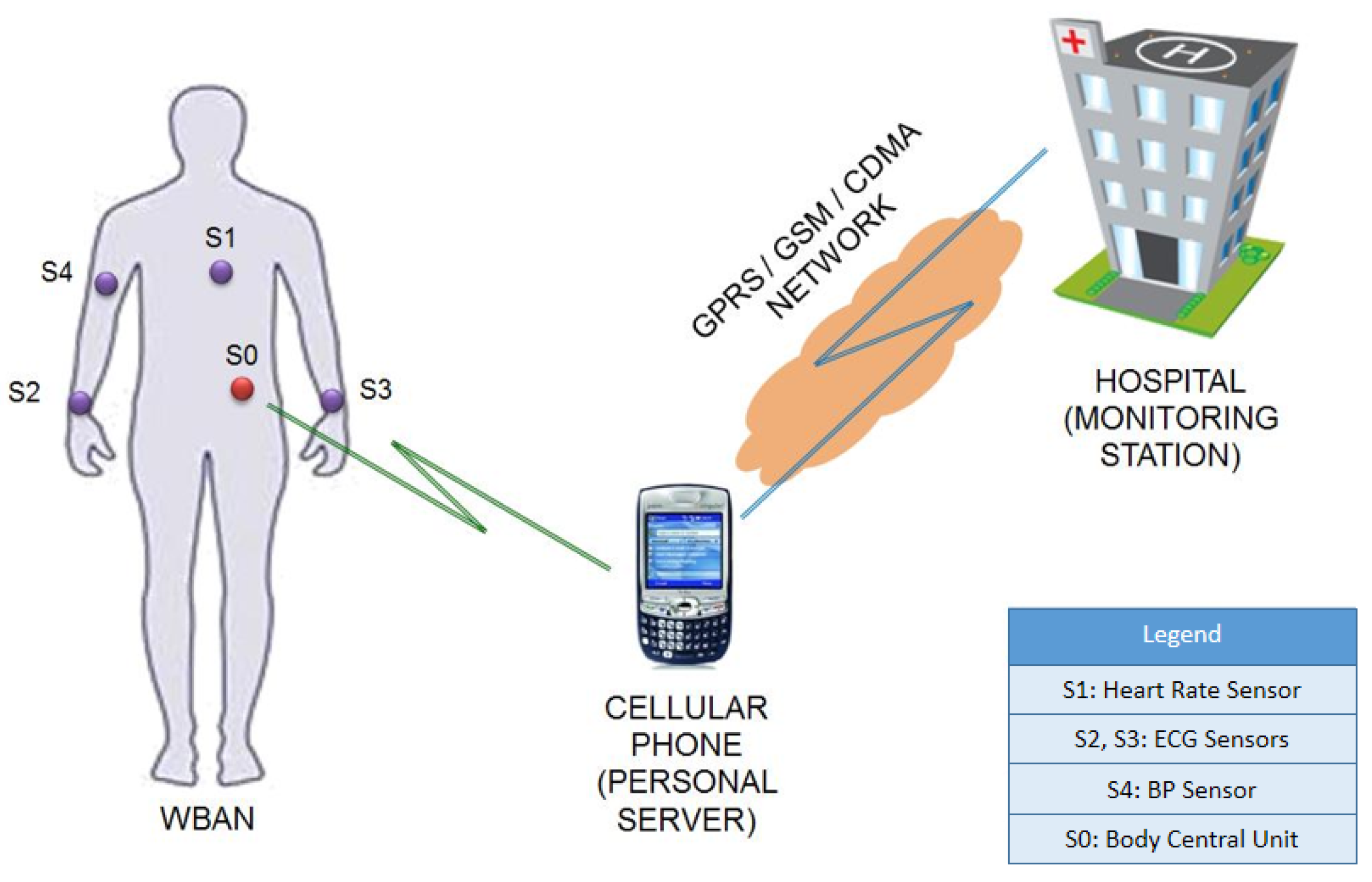
4. Extending Butterfly Encryption Scheme to WBANs
5. Evaluation and Results
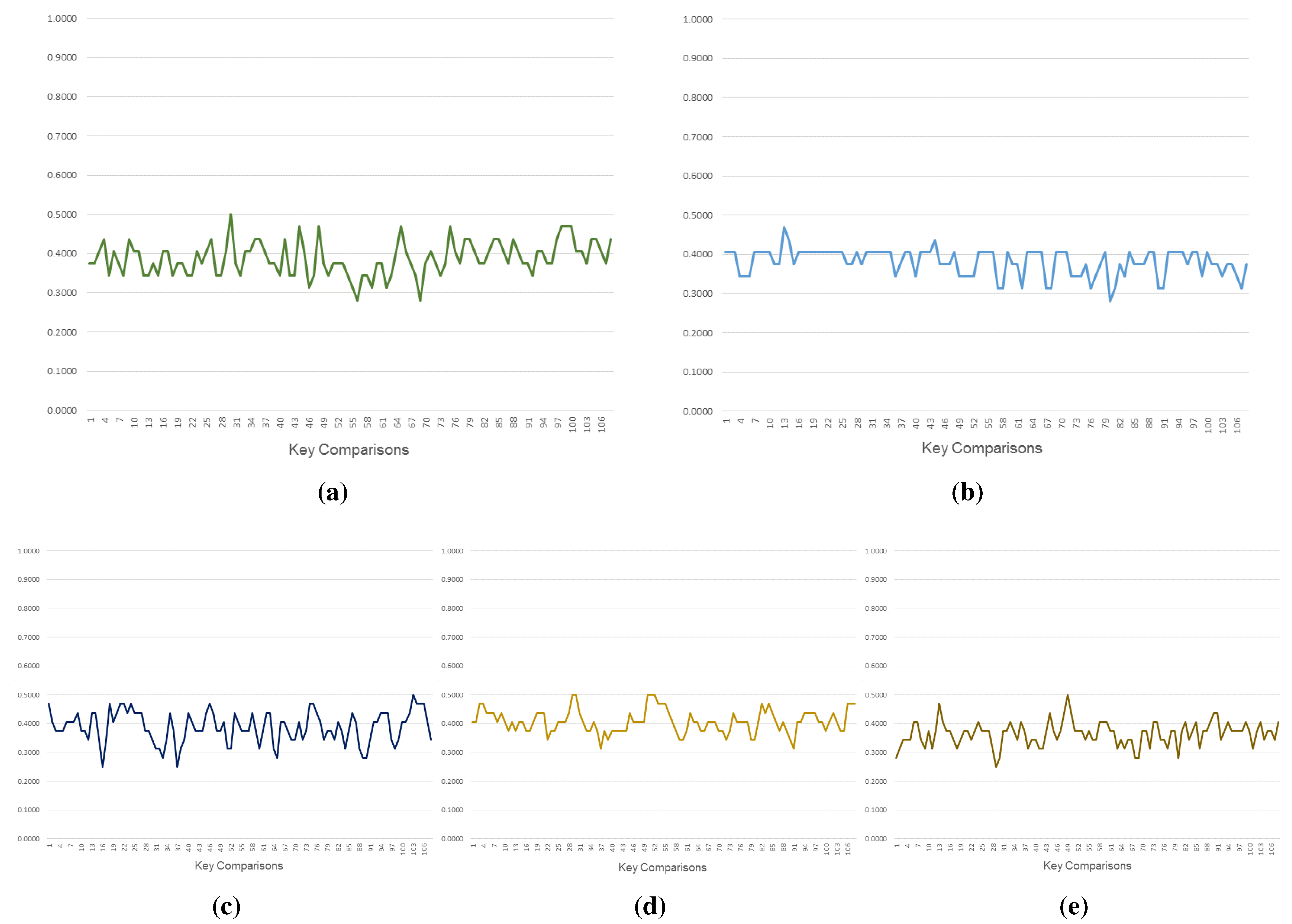
- Key Sequence Evaluation: We implemented our approach using Java programming language to verify the working of the concept and generation of key sequences for further evaluation. We used the generated key sequences to test similarity between consecutive keys using Sörensen’s Similarity Index () [31] and to verify the randomness in key sequences using the Statistical Test Suite (STS) published by NIST (National Institute of Standards and Technology) [32]. Using the results so obtained, we compared the performance of our approach with the RFID security proposals by Zhu et al. [13] and Dong et al. [12], and with an AES-based key generation approach for WBANs proposed by Liu et al. [20]. Note that we also implemented the proposals by Zhu et al., Dong et al., and Liu et al. using Java to generate key sequences for our assessment.
- Hardware Complexity Evaluation: We estimated the approximate resource requirement for implementing the Butterfly encryption scheme on hardware.
5.1. Key Sequence Evaluation
5.1.1. Methodology
5.1.2. Results
| Configuration | Average SSI () |
|---|---|
| Butterfly () | 0.3809 |
| Butterfly () | 0.3833 |
| Liu et al. [20] | 0.3826 |
| Zhu et al. [13] | 0.4110 |
| Dong et al. [12] | 0.3815 |
| Configuration (Keys Considered) | FM Test | FB Test | Runs Test | LR Test | DFT Test |
|---|---|---|---|---|---|
| Butterfly () | 9895 | 9908 | 9906 | 9896 | 9862 |
| Butterfly () | 9906 | 9906 | 10,000 | 9917 | 10,000 |
| Liu et al. [20] | 9913 | 9914 | 9888 | 9912 | 9837 |
| Zhu et al. [13] | 9891 | 9892 | 9892 | 9886 | 9832 |
| Dong et al. [12] | 9898 | 9926 | 9890 | 9894 | 9833 |
5.2. Hardware Complexity Evaluation
| Logic Circuit | Count |
|---|---|
| PRNG | n bit |
| Addition | bit |
| XOR * | n bit |
| NOT (Invert) | 1 bit |
| MUX (Multiplexer) |
5.3. Security Evaluation
| Claim | Bob | Alice | ||
|---|---|---|---|---|
| Status | Comments | Status | Comments | |
| Secret | OK | NAWB * | OK | NAWB |
| Secret | OK | NAWB | OK | NAWB |
| Secret i | OK | NAWB | OK | NAWB |
| Secret | OK | NAWB | OK | NAWB |
| Secret θ | OK | NAWB | OK | NAWB |
| Secret | OK | NAWB | OK | NAWB |
| Secret | OK | NAWB | OK | NAWB |
| Secret | OK | NAWB | OK | NAWB |
| Secret | OK | NAWB | OK | NAWB |
| Secret | OK | NAWB | OK | NAWB |
| Secret | OK | NAWB | OK | NAWB |
| OK | NA-Verified | OK | NAWB | |
| OK | NA-Verified | OK | NAWB | |
| OK | NAWB | OK | NAWB | |
| OK | NAWB | OK | NAWB | |
6. Discussion
7. Conclusions
Acknowledgments
Author Contributions
Conflicts of Interest
References
- Gubbi, J.; Buyya, R.; Marusic, S.; Palaniswami, M. Internet of Things (IoT): A vision, architectural elements, and future directions. Fut. Gen. Comput. Syst. 2013, 29, 1645–1660. [Google Scholar] [CrossRef]
- Glover, B.; Bhatt, H. RFID Essentials, 1st ed.; O’Reilly Media: Sebastopol, CA, USA, 2006. [Google Scholar]
- O’Donovan, T.; O’Donoghue, J.; Sreenan, C.; Sammon, D.; O’Reilly, P.; O’Connor, K. A context aware wireless body area network (BAN). In Proceedings of the 3rd International Conference on Pervasive Computing Technologies for Healthcare, 2009. PervasiveHealth 2009, London, UK, 1–3 April 2009; pp. 1–8.
- Association, I.S. IEEE Standard for Local and Metropolitan Area Networks-Part 15.6: Wireless Body Area Networks; IEEE: New York, NY, USA, 2012; pp. 155–172. [Google Scholar]
- Trappe, W.; Washington, L.C. Introduction to Cryptography with Coding Theory; Pearson Prentice Hall: Englewood Cliff, NJ, USA, 2006. [Google Scholar]
- Lorenz, E.N. Predictability; Does the Flap of a Butterfly’s Wings in Brazil Set Off a Tornado in Texas? J. Atmos. Sci. 1972, 20, 130–141. [Google Scholar] [CrossRef]
- Poulin, D. A Rough Guide to Quantum Chaos; Physics Department & IQC, University of Waterloo: Waterloo, ON, Canada, 2006. [Google Scholar]
- Sampangi, R.V.; Sampalli, S. RFID Encryption Scheme Featuring Pseudorandom Numbers and Butterfly Seed Generation. In Proceedings of the 2014 22nd International Conference on Software, Telecommunications and Computer Networks (SoftCOM), Split, Croatia, 17–19 September 2014; pp. 1–5.
- Blum, L.; Blum, M.; Shub, M. A simple unpredictable pseudo-random number generator. SIAM J. Comput. 1986, 15, 364–383. [Google Scholar] [CrossRef]
- Melia-Segui, J.; Garcia-Alfaro, J.; Herrera-Joancomarti, J. Multiple-polynomial LFSR based pseudorandom number generator for EPC Gen2 RFID tags. In Proceedings of the IECON 2011 37th Annual Conference on IEEE Industrial Electronics Society, Melbourne, Australia, 7–10 November 2011; pp. 3820–3825.
- Martin, H.; San Millan, E.; Entrena, L.; Lopez, P.; Castro, J. AKARI-X: A pseudorandom number generator for secure lightweight systems. In Proceedings of the 2011 IEEE 17th International On-Line Testing Symposium (IOLTS), Athens, Greece, 13–15 July 2011; pp. 228–233.
- Dong, Q.; Zhang, J.; Wei, L. A SHA-3 based RFID mutual authentication protocol and its implementation. In Proceedings of the 2013 IEEE International Conference on Signal Processing, Communication and Computing (ICSPCC), Kunming, China, 5–8 August 2013; pp. 1–5.
- Zhu, G.; Khan, G. Symmetric key based RFID authentication protocol with a secure key-updating scheme. In Proceedings of the 2013 26th Annual IEEE Canadian Conference on Electrical and Computer Engineering (CCECE), Regina, SK, Canada, 5–8 May 2013; pp. 1–5.
- Liu, J.; Zhang, Z.; Chen, X.; Kwak, K.S. Certificateless Remote Anonymous Authentication Schemes for Wireless Body Area Networks. IEEE Trans. Parallel Distrib. Syst. 2014, 25, 332–342. [Google Scholar] [CrossRef]
- Kovacevic, T.; Perkovic, T.; Cagalj, M. LIRA: A new key deployment scheme for Wireless Body Area Networks. In Proceedings of the 2013 21st International Conference on Software, Telecommunications and Computer Networks (SoftCOM), Split-Primosten, Croatia, 18–20 September 2013; pp. 1–6.
- Bertoni, G.; Daemen, J.; Peeters, M.; Assche, G.V. The Road from Panama to Keccak via RadioGatún. In Proceedings of the Dagstuhl Seminar, Dagstuhl, Germany, 19–22 November 2009; pp. 1–9.
- Choi, W.; Kim, S.; Kim, Y.; Park, Y.; Ahn, K. PUF-based Encryption Processor for the RFID Systems. In Proceedings of the 2010 IEEE 10th International Conference on Computer and Information Technology (CIT), Bradford, West Yorkshire, UK, 29 June–1 July 2010; pp. 2323–2328.
- EPCglobal. EPC Radio-Frequency Identity Protocols Generation-2 UHF RFID. In EPCglobal Specifications; EPCglobal: Littleton, CO, USA, 2013; pp. 1–52. [Google Scholar]
- ISO/IEC. ISO/IEC 29167-1:2014–Information technology–Automatic identification and data capture techniques–Part 1: Security services for RFID air interfaces. In International Standard; International Organization for Standardization (ISO): Geneva, Switzerland, 2014; pp. 1–52. [Google Scholar]
- Liu, J.; Kwak, K.S. Hybrid security mechanisms for wireless body area networks. In Proceedings of the 2010 Second International Conference on Ubiquitous and Future Networks (ICUFN), Jeju Island, Korea, 16–18 June 2010; pp. 98–103.
- Luo, Y.; Chai, Q.; Gong, G.; Lai, X. A Lightweight Stream Cipher WG-7 for RFID Encryption and Authentication. In Proceedings of the 2010 IEEE Global Telecommunications Conference (GLOBECOM 2010), Miami, FL, USA, 6–10 December 2010; pp. 1–6.
- Shen, S.S.; Liao, H.R.; Lin, S.H.; Chiu, J.H. A Novel Stream Cipher with Hash Function for the RFID Device. In Proceedings of the 2011 Fifth International Conference on Innovative Mobile and Internet Services in Ubiquitous Computing (IMIS), Seoul, Korea, 30 June–2 July 2011; pp. 532–536.
- Maurer, U. A universal statistical test for random bit generators. J. Cryptol. 1992, 5, 89–105. [Google Scholar] [CrossRef]
- Bishop, R.C. On Separating Predictability and Determinism. Erkenntnis 2003, 58, 169–188. [Google Scholar]
- Peris-Lopez, P.; San Millan, E.; van der Lubbe, J.; Entrena, L. Cryptographically secure pseudo-random bit generator for RFID tags. In Proceedings of the 2010 International Conference for Internet Technology and Secured Transactions (ICITST), London, UK, 8–10 November 2010; pp. 1–6.
- Katti, R.; Srinivasan, S. Efficient hardware implementation of a new pseudo-random bit sequence generator. In Proceedings of the IEEE International Symposium on Circuits and Systems (ISCAS 2009), Taipei, Taiwan, 24–27 May 2009; pp. 1393–1396.
- National Institute of Standards and Technology (NIST). Advanced Encryption Standard (AES). In Federal Information Processing Standards Publication 197; NIST: Springfield, IL, USA, 2001; pp. 1–47. [Google Scholar]
- EPCglobal. Tag Class Definitions; EPCglobal: Littleton, CO, USA, 2007. [Google Scholar]
- Sampangi, R.V.; Dey, S.; Urs, S.R.; Sampalli, S. A security suite for wireless body area networks. Int. J. Netw. Secur. Appl. (IJNSA) 2012, 4, 97–116. [Google Scholar] [CrossRef]
- IEEE 802.15. IEEE 802.15: WIRELESS PERSONAL AREA NETWORKS (PANs); IEEE: Piscataway, NJ, USA, 2005. [Google Scholar]
- Sorensen, T. A method of establishing groups of equal amplitude in plant sociology based on similarity of species content and its application to analyses of the vegetation on Danish commons. Biol. Skr. K. Dan. Vidensk. Selsk. 1957, 5, 1–34. [Google Scholar]
- Rukhin, A.; Soto, J.; Nechvatal, J.; Smid, M.; Barker, E.; Leigh, S.; Levenson, M.; Vangel, M.; Banks, D.; Heckert, A.; et al. A Statistical Test Suite for Random and Pseudorandom Number Generators for Cryptographic Applications; National Institute of Standards and Technology (NIST): Springfield, IL, USA, 2010. [Google Scholar]
- Cremers, C. The Scyther Tool.; Department of Computer Science, University of Oxford: Oxford, UK, 2014. [Google Scholar]
- Lowe, G. A hierarchy of authentication specifications. In Proceedings of the 10th Computer Security Foundations Workshop, Rockport, MA, USA, 10–12 June 1997; pp. 31–43.
- Hollestelle, G. Systematic Analysis of Attacks on Security Protocols. Master’s Thesis, Technische Universiteit Eindhoven, Eindhoven, Netherlands, 2005. [Google Scholar]
- Cremers, C. Scyther User Manual; Department of Computer Science, University of Oxford: Oxford, UK, 2014. [Google Scholar]
- Paar, C.; Pelzl, J. Understanding Cryptography; Springer: Berlin/Heidelberg, Germany, 2010. [Google Scholar]
- Stallings, W. Cryptography and Network Security: Principles and Practice, 5th ed.; Prentice Hall: New York, NY, USA, 2010. [Google Scholar]
© 2015 by the authors; licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Sampangi, R.V.; Sampalli, S. Butterfly Encryption Scheme for Resource-Constrained Wireless Networks. Sensors 2015, 15, 23145-23167. https://doi.org/10.3390/s150923145
Sampangi RV, Sampalli S. Butterfly Encryption Scheme for Resource-Constrained Wireless Networks. Sensors. 2015; 15(9):23145-23167. https://doi.org/10.3390/s150923145
Chicago/Turabian StyleSampangi, Raghav V., and Srinivas Sampalli. 2015. "Butterfly Encryption Scheme for Resource-Constrained Wireless Networks" Sensors 15, no. 9: 23145-23167. https://doi.org/10.3390/s150923145
APA StyleSampangi, R. V., & Sampalli, S. (2015). Butterfly Encryption Scheme for Resource-Constrained Wireless Networks. Sensors, 15(9), 23145-23167. https://doi.org/10.3390/s150923145






