Context Aware Middleware Architectures: Survey and Challenges
Abstract
:1. Introduction
2. Principles of Context Aware Environments
2.1. Context
- “…the set of location, identities of nearby people and objects and changes to those objects.” [7]
- “…location, identities of the people around the user, the time of day, season, temperature and so forth.” [8]
- “…the combination of the user’s location, environment, identity and time.” [9]
- “…what is happening at this moment.” [10]
- “…the state of the application’s surroundings.” [11]
- “…just the aspects of a current situation.” [12]
- “…extending to model the activities and tasks that are taking place in a location.” [13]
- “…the set of circumstances surrounding it are of relevance to its completion.” [14]
- “…any information that can be used to characterize the situation of entities (i.e., whether a person, place, or object) are considered relevant to the interaction between a user and an application, including the user and the application. Context is typically the location, identity, and state of people, groups and computational and physical objects.” [15]
2.1.1. Context Categorization
| Context Categorization | Observation Aspects and Context Features | Examples |
|---|---|---|
| 5W1H (Who, When, Where, What, Why and How) | Analysis of the environment from different points of view. Intuitive to understand. | Life assistance of elderly Peter, 8 o’clock, garden, picking fruit, apples are ripe, with a ladder. |
| Physical/Virtual | Differentiation according to sources: sensing devices (physical); user, context servers, etc. (virtual). Simple but ambiguity to identify the same context as it can be physical or virtual depending on different situations. | Rehabilitation Physical: heart rate Virtual: patient’s medical history from database |
| Static/Dynamic | Observation over time: always equal (static) or adaptive to changes in the environment (dynamic). Intuitive to understand. | Plant inspection Static: the place where a tree grows Dynamic: the aspect of the tree due to the current season |
| Direct/Indirect | Differentiation through obtainment complexity, indirect context is more complex to acquire and needs computation, inference etc. Simple to identify. | Birthday Direct: actual date is the birthday Indirect: which birthday is it and does this mean something (e.g., 50th Birthday) |
| Sensed, Combined, Inferred and Learned | Refined differentiation of obtainment complexity by sub-categorizations. Ambiguity in identifying the complexity of obtainment, difficult to distinguish clear differences of sub-categorizations | Navigation Sensed: proximity to an object Combined: speed and direction of motion Inferred: check distance (rules) Learned: compare with similar situations |
| Internal/External | Differentiation of sources from the user’s point of view. Ambiguity in classifying the same context. | Life assistance Internal: desire to get up from the bed External: it is the time to get up |
| Primary/Secondary | Obtainment complexity similar to direct/indirect. Simple. Ambiguity in identifying the complexity of obtainment. | Health monitoring Primary: check blood pressure Secondary: comparison of historical blood pressure data |
2.1.2. Context Features
Context Sources
Context Scope
Context Variety
Context Temporal Validity
Context Flexibility
2.2. Context Awareness and Its Categorizations
- “...the ability of computing devices to detect and sense, interpret and respond to aspects of a user’s local environment and the computing devices themselves.” [26]
- “...provide the maximum flexibility of service based on real time context.” [29]
- “...automatically provide information or take actions according to the user’s present context and need.” [30]
- “...if an application has the ability to monitor input from sensing devices and choose the suitable context according to user’s need or interests, then it can be labelled as a context-aware application.” [31]
- Observing from the user interaction based viewpoint, the level of context awareness increases as the demand for the invention from users reduces.
- The hardware’s point of view focuses on the acquisition of context data which could be independent (the system itself obtains all necessary data) or based on an external infrastructure of devices. Hereby, intermediate levels could exist, as e.g., context awareness achieved by self-contained hardware could be augmented by using other technologies or infrastructures. The work reported in [32] states a close relation between active context awareness and infrastructure-based context awareness because of some common characteristics. It is believed that the extra infrastructure support is needful for the realization of active context awareness. The prominent commonality is that both try to reduce or even eliminate unnecessary user intervention in order to make the performance as “intelligent” as possible.
- If the measurement by hardware is the only means to realize context awareness, then the corresponding achievement is limited to be in the hard level. Soft context awareness is achieved by means of applying operations, e.g., analysis, inference, and learning on context knowledge base. However, it is difficult to apply and use to examine the level of a real context aware middleware, as most architectures simultaneously depend on both hardware and knowledge repository (context history).
- Based on the different models used to express context, context awareness can be grouped into three levels: location aware, medium and semantic. The investigation of [35] on the history of context aware systems shows that the development went over three generations which happen to represent one level, respectively. The first level is provided merely according to user's location. In the 2nd generation, more kinds of context information are employed to enable systems to know more about the environment. However, due to ambiguity, only a medium level of awareness is reached here. Later, common semantic technologies (e.g., ontology) were adopted to unambiguously represent context structures and their relationships in the 3rd generation. Here, context awareness can take advantage of semantic techniques to ensure formality, flexibility, interoperability and scalability.
| Classification Aspect | Context Awareness Levels | Description |
|---|---|---|
| User interaction | Personalized | Interaction is available for users to set preferences |
| Passive | Execution of appropriate options is subject to users’ decisions | |
| Active | Execution of appropriate options acts autonomously | |
| Acquisition hardware | Self-contained | Context awareness is achieved by independent hardware without any external support |
| Infrastructure-based | External systems or infrastructures provide additional support to realize context awareness | |
| Information acquisition tool | Hard | Context awareness is obtained solely by hardware |
| Soft | Knowledge inference based on context repository is applied to achieve context awareness | |
| Context model | Location aware | Context awareness is limited to location awareness |
| Medium-level | Various context is used but not unambiguously managed | |
| Semantic | Semantic technologies are employed to enhance context awareness |
2.3. Context Lifecycle
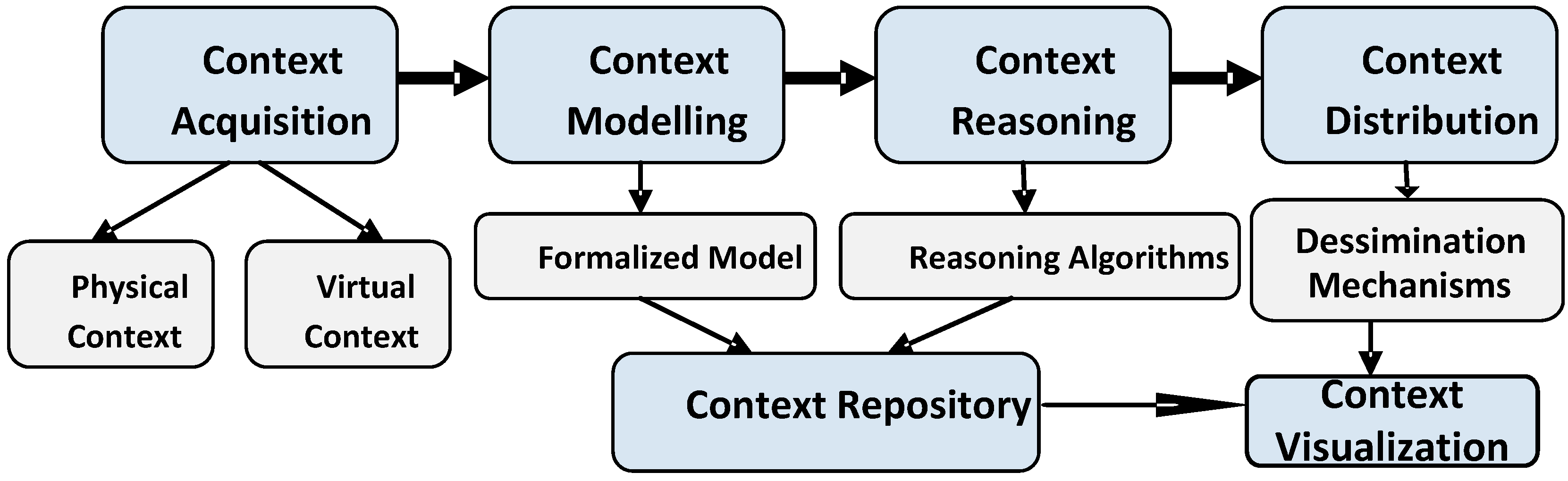
2.3.1. Context Acquisition
Physical Context
Virtual Context
2.3.2. Context Modelling
Key-Value Context Modelling
Markup Context Modelling
Graphical Context Modelling
Object-Oriented Modelling
Logic-Based Context Modelling
Multidisciplinary Context Modelling
Domain-Focused Context Modelling
User-Centric Context Modelling
Ontology-Based Context Modelling
Chemistry Inspired Context Modelling
| Context Modelling Technique | Advantages | Disadvantages | Applicability |
|---|---|---|---|
| Key-value | Simple; Ease of use; Flexible | Lack of standards; Useless when big in size; Cannot represent relationships; Difficult to retrieve information; Lack of validation tools; Lack of scalability; Only exact matching. | Adequate to model limited context in simple and self-independent applications which do not need to share data with other applications. Examples: [39,49] |
| Markup | Structured; Some validation tools are available; Flexible. | Lack of standards; Problems in capturing relationships; Timeless; Dependencies; Inconsistency checking; Reasoning and Uncertainty. | Efficient as mode of data transfer about shallow context over network; Applications in which levels of information are few. Examples: [50,51] |
| Graphical | Rich expressiveness; Relationships are allowed; Validation is possible through constraints; Different standards and implementations are available. | Interoperability is unsolved; Configuration must be required; A generic and well-developed standard is needed. | Particularly applicable to derive an ER-model which is useful as structuring instrument for a relational database. Examples: [52,53] |
| Object-oriented | Relationships are allowed; Some development tools are available; Can be fused by using programming languages. | Lack of standards; Lack of validation; Hard to retrieve information; Reasoning is not supported. | Suitable to be used in code-based (high-level programming languages) applications with high computational capability. Examples: [40,54] |
| Logic-based | Rich expressiveness; Support reasoning; Consistency check; Simplicity; Processing tools are available. | Lack of standards; Lack of validation. | Suitable for applications in which high-level information is needed and developers are willing to specify constraints. Examples: [41,55,56] |
| Multidisciplinary | Comprehensive understanding for context based on multiple disciplines; The division of context is concrete. | Too complex; Still at the first stage; Interoperability is unsolved. | Tailored to applications in which key human and social issues should be identified. Examples: [42] |
| Domain-focused | Expressive; Flexible; Structured. | Lack of standards; Lack of validation. | Suitable to single domain-focused applications. Examples: [43] |
| User-centric | Express context in an organized way; Scalability; Allow reasoning. | Lack of standards; Complex to use; Lack of validation; Lack of formality. | Suits applications focused on perspectives of users; data expression is in an intuitive manner. Examples: [44] |
| Ontology-based | Support reasoning; Rich expressiveness; Relationships are allowed; Strong validation; Processing tools available; Mature standards; Interoperability. | Representation can be complicated; It will be complex to retrieve context information; Unable to address uncertainty. | Suitable to applications which highly need to exchange information with others; Sufficient knowledge engineering skills are available. Examples: [45,57,58,59] |
| Chemistry inspired | Medium expressivity to represent many kinds of context; Support for triggering services autonomously; Cross-domain inspired. | Lack of standards; Lack of validation; Not dynamic and scalable; In a nascent stage. | It is possible to apply this model to applications which require spontaneous interaction and composition of information. Examples: [46] |
2.3.3. Context Reasoning
Bayesian Network
Probabilistic Logic-Based Reasoning
Case-Based Reasoning
Rule-Based Reasoning
Ontology-Based Reasoning
2.3.4. Context Distribution
Subscribe/Publish
Polling
2.3.5. Context Visualization
3. Survey on Context Aware Middleware Architectures
3.1. Technical Considerations for Context Aware Middleware
Architectural Style
- The stand-alone architecture is the simplest and least powerful in which only a fixed amount of context is processed in an independent module. Besides, context sharing is not allowed.
- In the layered manner, different responsibilities are allocated to multiple layers. However, the interaction and dependence among all layers raises concerns.
- As the core of the centralized middleware architecture, a central server is endowed with crucial computational capabilities and rich storage capacity. Communication exists between the central server and other devices for exchanging information. The prominent limitation is once the central server fails, the entire architecture will be influenced dramatically.
- The distributed architecture is widely applied and it enables developers to design middleware in a more flexible manner. Different components hold distributed responsibilities and they are independent of each other. However, every component involved in the distributed architecture needs to cope with the stress of computation and storage.
Fault Tolerance
Scalability
Security & Privacy
Interoperability
Service Discovery
Context Abstraction
Storage
Cloud-Based Big Data Analytics
3.2. Context Aware Middleware Architectures
3.2.1. Context Aware Middleware for Pervasive Elderly Homecare (CAMPH)
- Physical Space Layer: Each Physical Space (PS) may contain physical entities such as sensors, actuators and computing devices. At this layer, data is modelled as a pair of attribute-value. PSs with high relevance, such as having similar attributes, are sorted into the same class named context domain or context space.
- Context Data Management Layer: Main components allocated in this layer are Context data/events database, Query processing, Context space management, and Context reasoning. A hierarchical reasoning scheme, in which low-level reasoning performs on single PS data while high-level reasoning makes inference from context domain, is applied. Besides, SQL-based context query interface is available to acquire context data or subscribe to event notifications.
- Service Management Layer: Context data is fully utilized to enable context aware service organization and discovery.
- Application Layer: Different homecare applications can invoke and orchestrate context aware services or make requests for context data directly in this layer.
3.2.2. ACoMS+
3.2.3. Octopus
3.2.4. FIWARE
3.2.5. Context Awareness for Internet of Things (CA4IOT)
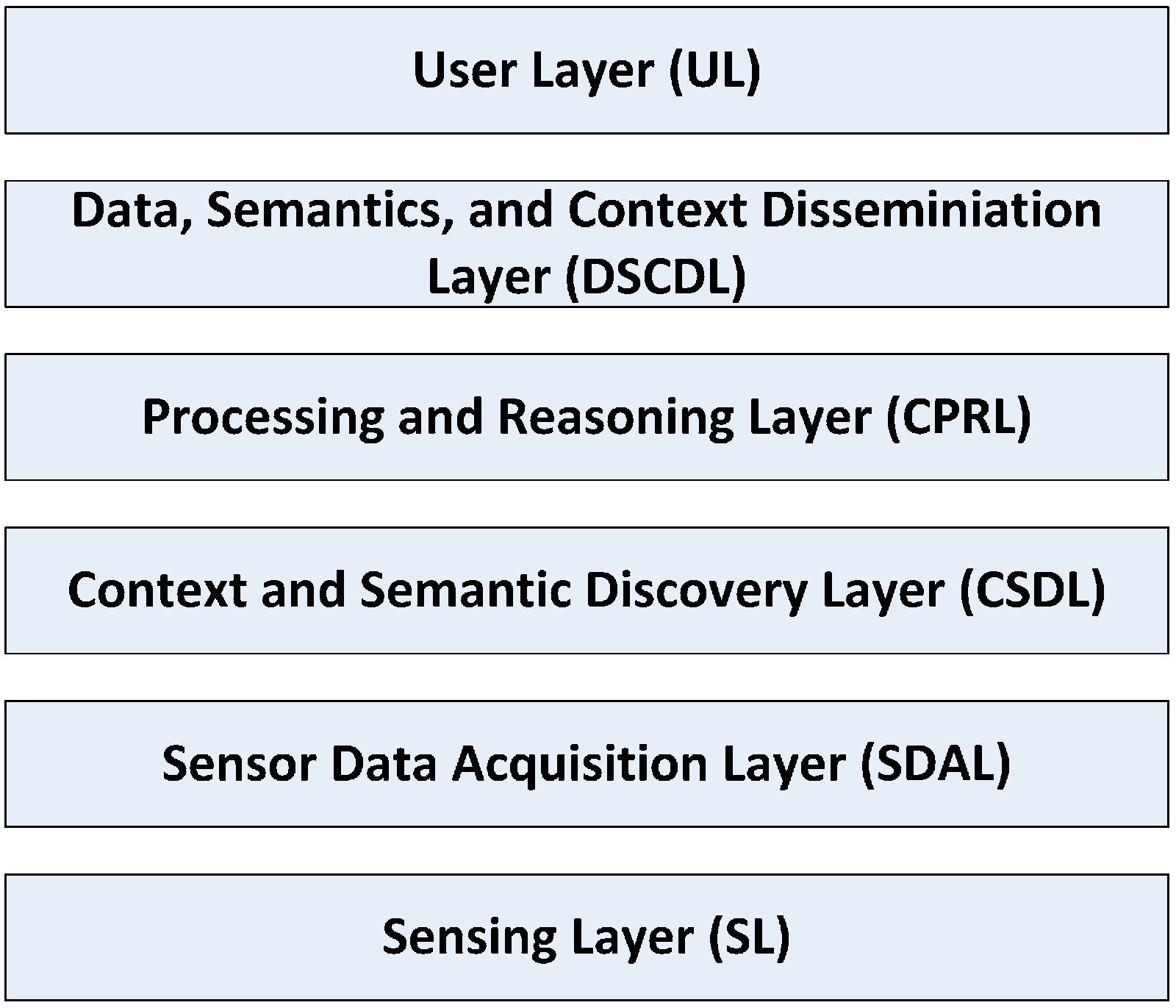
- SDAL. The main components located in this layer are sensor wrappers, wrapper repository, wrapper generator, sensor device definition (SDD) local repository and SDD cloud repository. This layer is responsible for acquiring a variety of context data.
- CSDL. This layer is in charge of discovering context and semantic. Relevant components are context and semantic discoverers, context and semantic discoverer generator, and context and semantic discoverers repository.
- CPRL. A collection of important functions are distributed in this layer like processing data, reasoning high-level context, fusing context, knowledge generating and storing.
- DSCDL. Users can make requests via multi-model interfaces. Local repository can interact with repositories which reside in the cloud or open linked data to provide better answers for those queries by means of big data analytics.
3.2.6. CAMPUS
- The programming layer. It is responsible for constructing and reconfiguring context aware applications by adopting the instructions from the decision layer.
- The knowledge layer. Three ontologies including Context Model, Tasklet Model, and Service Model are proposed to represent semantics of knowledge which is necessarily required by CAMPUS to make adaptation decisions. The knowledge could be the requirements desired by target service, the properties of the available tasklets, the context requirements imposed by tasklets, and the properties of run-time context.
- The decision layer. Decision maker uses a multi-stage normative decision model, which includes preprocessing, screening and choice, to choose the best tasklet alternatives for a given task. The automated adaptation decisions will be forwarded to the programming layer.
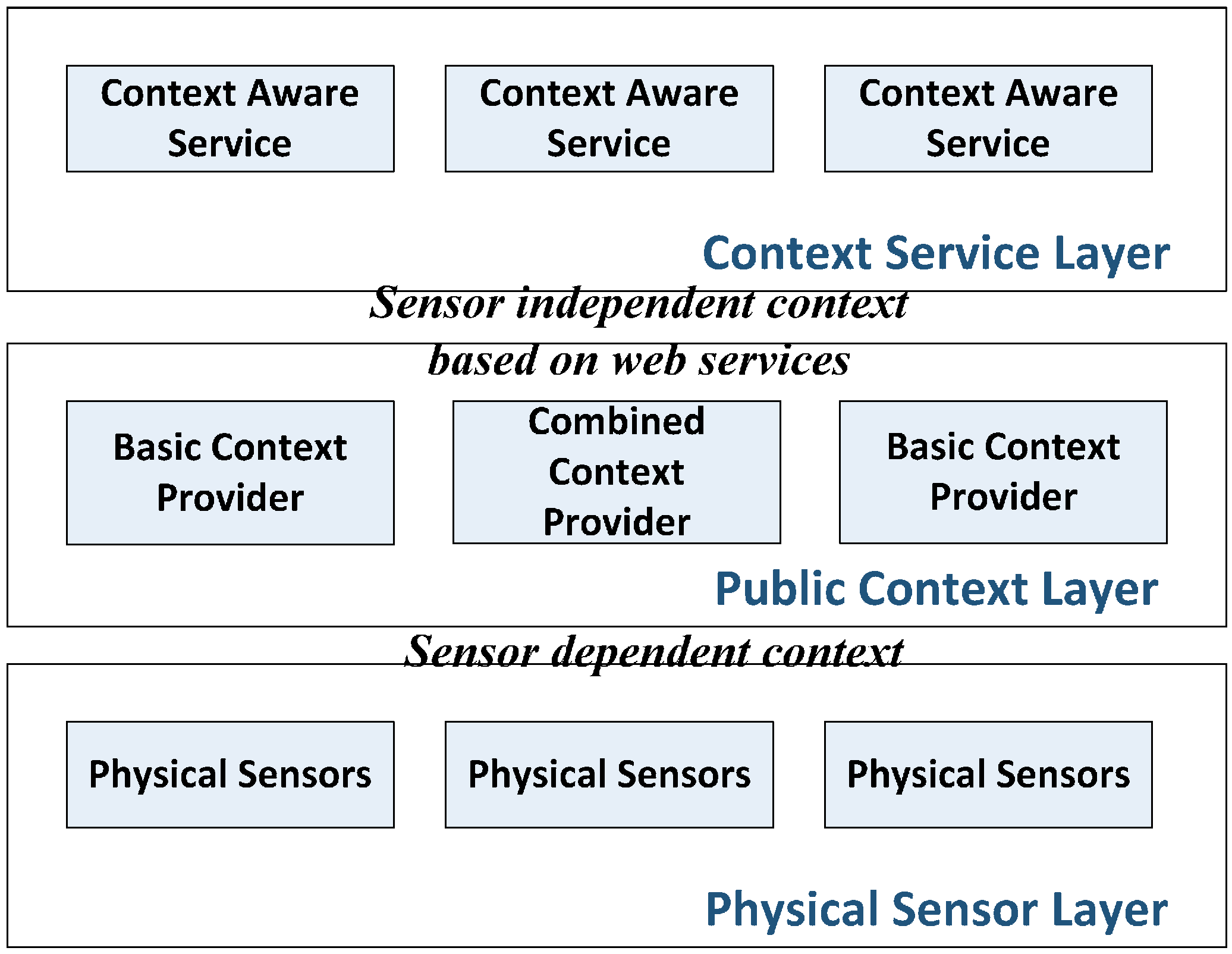
3.2.7. Context-Aware Services Framework (CASF)
- Physical sensor layer. It can only recognize sensor data. Physical sensors are the only context information source.
- Public context layer. Two types of context providers in terms of complexity of context information process are located in this layer. A basic context provider only processes sensor data from physical sensors while a combined context provider can make use of information from both sensors and other context providers. All context information generated in this layer is served based on web services so that openness and interoperability are achieved. By using a proposed context ontology and OWL-S, context providers are able to be constructed in web services.
- Context service layer. Context information is consumed in this layer so that context aware services can be generated and provided to users.
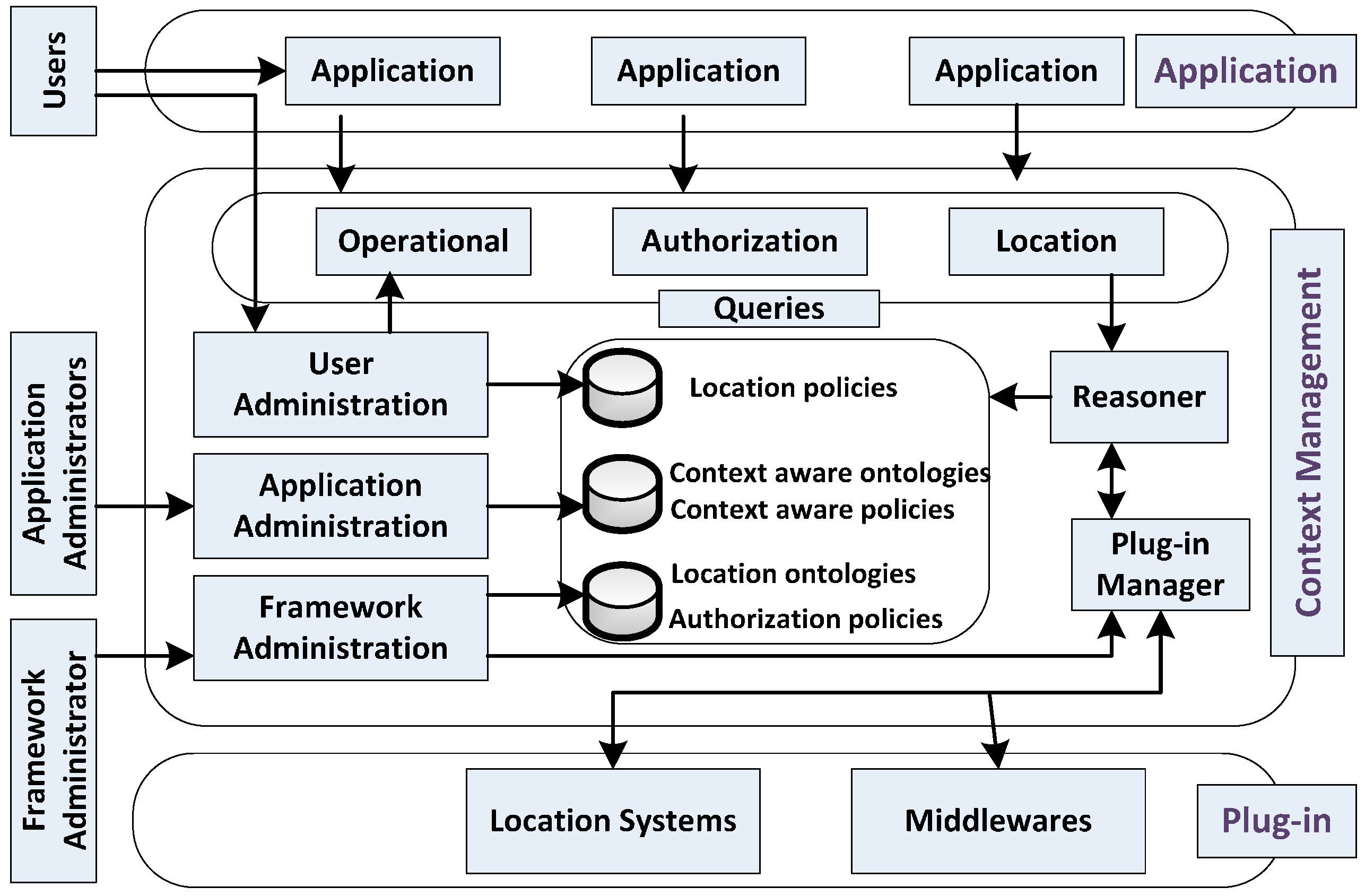
3.2.8. Semantic Web-Based Context Management (SeCoMan)
- Application. Different applications reside on top of SeCoMan in order to offer desired services for users.
- Context Management. As the core of the SeCoMan framework, it provides context aware supports for applications. Three kinds of actors with different rights to interact with SeCoMan are defined including Framework Administrator, Application Administrator, and Users. A set of predefined queries are allowed for applications to get information about indoor location of users and objects. Semantic rules are used to specify policies regarding restricted access to location information so that privacy is guaranteed.
- Plug-in. It provides SeCoMan with context information, which is especially focused on locations. In other words, the plug-in layer acts as an independent context source.
3.2.9. CoCaMAAL
- AAL systems. This component, as the hardware architecture, includes different BSN (Body Sensor Network) foundations and monitoring systems for meeting different target user requirements.
- Context aggregator and providers (CAP). Raw data from AAL systems is converted and abstracted to high-level context by CAP. More specifically, context providers categorize sensor data into context based on pre-designed ontology. Afterwards, different context is integrated by context aggregator to provide complete information. In addition, reasoning mechanisms are applied to infer more useful information.
- Service providers. They are the producers of context aware services, such as applications.
- Context aware middleware (CaM). By utilizing existing knowledge and incoming context, CoM is able to indentify assistive services for the given context and trigger associated actions. CaM is the core component of CoCaMAAL with multiple key functions, such as context management, context storing, context retrieval, context manipulation, service mapping, self-adaptation, service discovery, and security service.
- Context data visualization. Proper interfaces (e.g., GUI) are available for users to visualize context data.
3.2.10. Big Data for Context Aware Monitoring (BDCaM)
3.2.11. FlexRFID
3.3. Comparisons
| Middleware | Year | Architectural Style | Context Abstraction | Context Reasoning | Scalability | Cloud-Based Big Data Analytics |
|---|---|---|---|---|---|---|
| CAMPH | 2009 | Layered & Distributed | Key-value | Rule | × | × |
| ACoMS+ | 2010 | Distributed | Graphical | Rule | √ | √ |
| Octopus | 2011 | Layered | Not specified | Not specified | × | × |
| FIWARE | 2011 | Distributed | Ontology | Ontology | √ | √ |
| CA4IoT | 2012 | Layered & Distributed | Ontology | Ontology and statistical | √ | √ |
| CAMPUS | 2013 | Layered | Ontology | Ontology | × | × |
| CASF | 2013 | Layered | Ontology | Ontology | × | × |
| SeCoMan | 2014 | Layered | Ontology | Ontology and rule | × | × |
| CoCaMAAL | 2014 | Distributed | Ontology | Ontology | √ | √ |
| BDCaM | 2015 | Distributed | Ontology | Ontology | √ | √ |
| FlexRFID | 2015 | Layered & Distributed | Markup | Rule | × | × |
| Middleware | Fault Tolerance | Interoperability | Service Discovery | Storage | Security & Privacy | Context Awareness Level |
|---|---|---|---|---|---|---|
| CAMPH | × | × | √ | √ | × | Medium level |
| ACoMS+ | √ | × | √ | √ | × | Medium level |
| Octopus | √ | × | × | √ | × | Medium level |
| FIWARE | √ | √ | √ | √ | √ | Semantic |
| CA4IoT | √ | √ | √ | √ | × | Semantic |
| CAMPUS | × | √ | √ | √ | × | Semantic |
| CASF | × | √ | √ | √ | × | Semantic |
| SeCoMan | × | √ | × | √ | √ | Location aware |
| CoCaMAAL | √ | √ | √ | √ | × | Semantic |
| BDCaM | √ | √ | √ | √ | × | Semantic |
| FlexRFID | √ | × | √ | √ | √ | Medium level |
4. Open Issues
- Security & Privacy are a must in any middleware architecture. Amounts of sensitive context are employed to characterize the situation so as to provide relevant services. Hence, the demand for enforcing security & privacy is increasing. Besides, as it is agreed that it will be a fashion to drive middleware architectures to be cloud-oriented, leveraging cloud resources will impose many challenges on security & privacy. e.g., it could be possible for any entity with internet connection to easily collect, access, visualize, archive, share, and search data or services from the cloud. It will not be an easy task to guarantee security & privacy, political or legal restrictions of data in cloud. Potential solutions could be restricting unauthorized manipulation, protecting privacy of information storage, ensuring the information security during processing or probably creating private clouds dedicated to public sectors.
- Increase the degree/level of context awareness. There has been a plethora of so-called context aware middleware proposals in recent years. However, they differ in real capabilities, which refer to context awareness level. The desired awareness means that middleware could adequately understand any change of current environment based on all available context information. The majority of current context aware middleware proposals only reach a very limited level of cognition and awareness for their involved circumstances.
- Standardization. It seems that it will not be feasible to formulate a single standard for a generalized context aware middleware due to the variety of domains and applications involved. However, considerable efforts have been put to build a generic domain-focused middleware solution [106]. For example, [107] put forward a standardized middleware for the semantic web domain. Different middleware solutions adopt different standards compliant with needs from different domains. All these standards should be collected to form a complete standardization platform in which the selection of standard could be enabled to fit in a certain domain.
- Increase autonomy. Although context aware middleware architectures reduce the need of human intervention when they serve personalized applications, human intervention is still necessary and playing an important role in realizing context awareness. For instance, to infer more useful and higher-level context information, users have to define rules again and again when the involved surrounding changes. Real autonomy can be developed if the inference rules can evolve and change automatically according to the changing environment. Potential solutions can make use of big data related techniques like mining and learning algorithms.
- Lack of testing. It can be noted that most of middleware architectures included in this survey are still at the conceptual stage. Prototypes based on some of these middleware solutions have been built, but complete implementations (let alone actual usage) are missing. Besides, commercial or practical operation which goes beyond simple pilot projects is even a more difficult target. More attempts should be made to drive the move of these middleware solutions from theoretical research to tests and further to full-fledged deployment to actual environments.
5. Conclusions
Conflicts of Interest
References
- Vermesan, O.; Friess, P.; Guillemin, P.; Gusmeroli, S.; Sundmaeker, H.; Bassi, A. Internet of Things Strategic Research Roadmap. In Internet of Things: Converging Technologies for Smart Environments and Integrated Ecosystems, 1st ed.; Vermensan, O., Friess, P., Eds.; River Publishers: Aalborg, Denmark, 2013; pp. 7–144. [Google Scholar]
- Hu, P.Z.; Indulska, J.; Robinson, R. An Autonomic Context Management System for Pervaisve Computing. In Title of Pervasive Computing and Communications, Proceedings of the Sixth Annual IEEE International Conference, Hong Kong, China, 17–21 March 2008.
- Hyunjung, P.; Jeehyong, L. A Framework of Context-Awareness for Ubiquitous Computing Middlewares, Proceedings of the 2005 Fourth Annual ACIS International Conference on Computer and Information Science, Jeju Island, Korea, 14–16 July 2005; pp. 369–374.
- Jianping, Y.; Yu, H.; Jiannong, C.; Xianping, T. Middleware Support for Context-Awareness in Asynchronous Pervasive Computing Environments, Proceedings of the 2010 IEEE/IFIP 8th International Conference on Embedded and Ubiquitous Computing (EUC), Hong Kong, China, 11–13 December 2010; pp. 136–143.
- Sain, M.; Lee, H.; Chung, W.Y. Designing context awareness middleware architecture for personal healthcare information system. In Proceedings of the 2010 12th International Conference on Advanced Communication Technology (ICACT), Phoenix Park, Korea, 7–10 February 2010; pp. 1650–1654.
- Wang, C.D.; Mo, X.L.; Wang, H.B. An intelligent home middleware system based on context-awareness. In Proceedings of the Fifth International Conference on Natural Computation, ICNC’09, Tianjin, China, 14–16 August 2009; pp. 165–169.
- Schilit, W.N. A System Architecture for Context-Aware Mobile Computing; Columbia University: New York, NY, USA, 1995. [Google Scholar]
- Brown, P.J.; Bovey, J.D.; Xian, C. Context-aware applications: From the laboratory to the marketplace. IEEE Pers. Commun. 1997, 4, 58–64. [Google Scholar] [CrossRef]
- Pascoe, J.; Ryan, N.; Morse, D. Human Computer Giraffe Interaction: HCI in the Field. In Proceedings of the 2nd International Symposium on Wearable Computers (ISWC 98), Glasgow, UK, 19–20 October 1998.
- Flachsbart, D.F. All gadget and no representation makes jack a dull environment. In Proceedings of the AAAI 1998 Spring Symposium on Intelligent Environments, Palo Alto, CA, USA, 23–25 March 1998.
- Ward, A.; Jones, A.; Hopper, A. A new location technique for the active office. IEEE Pers. Commun. 1997, 4, 42–47. [Google Scholar] [CrossRef]
- Hull, R.; Neaves, P.; Bedford-Roberts, J. Towards situated computing. In Proceedings of the Digest of Papers First International Symposium on Wearable Computers, Cambridge, MA, USA, 13–14 October 1997; pp. 146–153.
- Chen, H.; Finin, T.; Joshi, A. An Intelligent Broker for Context-Aware Systems; University of Maryland: Baltimore County, MD, USA, 2004. [Google Scholar]
- Henricksen, K. A Framework for Context-Aware Pervasive Computing Applications; University of Queensland: Queensland, Australia, 2003. [Google Scholar]
- Dey, A.K. Providing Architectural Support for Building Context-Aware Applications; Georgia Institute of Technology: Atlanta, GA, USA, 1999. [Google Scholar]
- Kim, J.D.; Son, J.; Baik, D.K. Onto: Ontological context-aware model based on 5w1h. Int. J. Distrib. Sens. Netw. 2012, 2012, 11. [Google Scholar] [CrossRef]
- Zhang, D.; Huang, H.; Lai, C.F.; Liang, X.; Zou, Q.; Guo, M. Survey on context-awareness in ubiquitous media. Multimed. Tools Appl. 2013, 67, 179–211. [Google Scholar] [CrossRef]
- Frank, K.; Rockl, M.; Nadales, M.J.V.; Robertson, P.; Pfeifer, T. Comparison of Exact Static and Dynamic Bayesian Context Inference Methods for Activity Recognition. In Proceedings of the 8th IEEE International Conference on Pervasive Computing and Communications Workshops (PERCOM Workshops), Mannheim, Germany, 29 March–2 April 2010; pp. 189–195.
- García de Prado, A.; Ortiz, G. Context-aware services: A survey on current proposals. In Proceedings of the Third International Conferences on Advanced Service Computing, Rome, Italy, 25–30 September 2011; pp. 104–109.
- Lee, K.-C.; Kim, J.-H.; Lee, J.H.; Lee, K.-M. Implementation of ontology based context-awareness framework for ubiquitous environment. In Proceedings of the International Conference on Multimedia and Ubiquitous Engineering, (MUE ’07), Seoul, Korea, 26–28 April 2007; pp. 278–282.
- Gwizdka, J. What’s in the context? In Proceedings of Computer Human Interaction (CHI) 2000 workshop, Toronto, ON, Canada, 1–6 April 2000.
- Abowd, G.D.; Dey, A.K.; Brown, P.J.; Davies, N.; Smith, M.; Steggles, P. Towards a better understanding of context and context-awareness. In Proceedings of the 1st International Symposium on Handheld and Ubiquitous Computing, Karlsruhe, Germany, 27–29 September 1999; Springer-Verlag: Karlsruhe, Germany, 1999; pp. 304–307. [Google Scholar]
- Van Bunningen, A.H.; Feng, L.; Apers, P.M.G. Context for ubiquitous data management. In Proceedings of the International Workshop on Ubiquitous Data Management, UDM 2005, Washington, DC, USA, 4 April 2005; pp. 17–24.
- Henricksen, K.; Indulska, J.; Rakotonirainy, A. Modeling context information in pervasive computing systems. In Proceedings of the First International Conference on Pervasive Computing, Zürich, Switzerland, 26–28 August 2002; Springer-Verlag: Berlin/Heidelberg, Germany, 2002; pp. 167–180. [Google Scholar]
- Want, R.; Hopper, A.; Falc, V.; Gibbons, J. The active badge location system. ACM Trans. Inf. Syst. 1992, 10, 91–102. [Google Scholar] [CrossRef]
- Pascoe, J. Adding generic contextual capabilities to wearable computers. In Proceedings of the Second International Symposium on Wearable Computers, Pittsburgh, PA, USA, 19–20 October 1998; pp. 92–99.
- Dey, A.K. Context-aware computing: The cyberdesk project. In Proceedings of the AAAI 98 Spring Symposium on Intelligent Environments, Menlo Park, CA, USA, 23–25 March 1998.
- Dey, A.K.; Abowd, G.D.; Wood, A. Cyberdesk: A framework for providing self-integrating context-aware services. Knowl. Based Syst. 1998, 11, 47–54. [Google Scholar] [CrossRef]
- Salber, D.; Dey, A.K.; Abowd, G.D. Ubiquitous Computing: Defining an Hci Research Agenda for an Emerging Interaction Paradigm; Georgia Insititute of Technology: Atlanta, GA, USA, 1998. [Google Scholar]
- Brown, P.J. Triggering information by context. Pers. Technol. 1998, 2, 18–27. [Google Scholar] [CrossRef]
- Ryan, N. Mobile Computing in a Fieldwork Environment: Metadata Elements; University of Kent: Canterbury, Kent, UK, 1997. [Google Scholar]
- Baldauf, M.; Dustdar, S.; Rosenberg, F. A survey on context-aware systems. Int. J. Ad Hoc Ubiquit. Comput. 2007, 2, 263–277. [Google Scholar] [CrossRef]
- Perera, C.; Zaslavsky, A.; Christen, P.; Georgakopoulos, D. Context aware computing for the internet of things: A survey. IEEE Commun. Surv. Tutor. 2014, 16, 414–454. [Google Scholar] [CrossRef]
- Tuulari, E. Context Aware Hand-Held Devices; VTT Electronics: Espoo, Finland, 2000. [Google Scholar]
- Lee, S.; Chang, J.; Lee, S.G. Survey and trend analysis of context-aware systems. Inf. Int. Interdiscip. J. 2011, 14, 527–547. [Google Scholar]
- Chin, T.J.; You, Y.L.; Coutrix, C.; Lim, J.H.; Chevallet, J.-P.; Nigay, L. Snap2play: A mixed-reality game based on scene identification. In Advances in Multimedia Modeling; Satoh, S.I., Nack, F., Etoh, M., Eds.; Springer: Berlin/Heidelberg, Germany, 2008; Volume 4903, pp. 220–229. [Google Scholar]
- Boukhobza, J.; Olivier, P.; Rubini, S. Cach-ftl: A cache-aware configurable hybrid flash translation layer. In Proceedings of the 21st Euromicro International Conference on Parallel, Distributed and Network-Based Processing (PDP), Belfast, Northern Ireland, 27 February–1 March 2013; pp. 94–101.
- List of Sensors. Available online: http://en.wikipedia.org/wiki/List_of_sensors (accessed on 1 August 2015).
- Schilit, B.; Adams, N.; Want, R. Context-aware computing applications. In Proceedings of the 1994 First Workshop on Mobile Computing Systems and Applications, Santa Cruz, CA, USA, 8–9 December 1994; IEEE Computer Society: Washington, DC, USA, 1994; pp. 85–90. [Google Scholar]
- Cheverst, K.; Mitchell, K.; Davies, N. Design of an object model for a context sensitive tourist guide. Comput. Graph. 1999, 23, 883–891. [Google Scholar] [CrossRef]
- Xu, C.; Cheung, S.C. Inconsistency detection and resolution for context-aware middleware support. SIGSOFT Softw. Eng. Notes 2005, 30, 336–345. [Google Scholar] [CrossRef]
- Bradley, N.A.; Dunlop, M.D. Toward a multidisciplinary model of context to support context-aware computing. Hum. Comput. Interact. 2005, 20, 403–446. [Google Scholar] [CrossRef]
- Castelli, G.; Rosi, A.; Mamei, M.; Zambonelli, F. A simple model and infrastructure for context-aware browsing of the world. In Proceedings of the Fifth Annual IEEE International Conference on Pervasive Computing and Communications, 2007, PerCom ’07, White Plains, NY, USA, 19–23 March 2007; pp. 229–238.
- Hong, D.; Schmidtke, H.R.; Woo, W. Linking context modelling and contextual reasoning. In Proceedings of the 4th International Workshop on Modelling and Reasoning in Context, Roskilde, Denmark, 20–21 August 2007.
- Studer, R.; Benjamins, V.R.; Fensel, D. Knowledge engineering: Principles and methods. Data Knowl. Eng. 1998, 25, 161–197. [Google Scholar] [CrossRef]
- Ikram, A.; Baker, N.; Knappmeyer, M.; Reetz, E.S.; Tonjes, R. An artificial chemistry based framework for personal and social context aware smart spaces. In Proceedings of the 7th International Wireless Communications and Mobile Computing Conference (IWCMC), Istanbul, Turkey, 4–8 July 2011; pp. 2009–2014.
- Sathish, S.; Flora, C.D. Supporting smart space infrastructures: A dynamic context-model composition framework. In Proceedings of the 3rd International Conference on Mobile Multimedia Communications, Nafpaktos, Greece, 27–29 August 2007; ICST (Institute for Computer Sciences, Social-Informatics and Telecommunications Engineering): Nafpaktos, Greece, 2007; pp. 1–6. [Google Scholar]
- Yue, S.; Yuanchun, S. Towards initiative smart space model. In Proceedings of the Third International Conference on Pervasive Computing and Applications, ICPCA 2008, Alexandria, VA, USA, 6–8 October 2008; pp. 747–752.
- Aiello, F.; Fortino, G.; Gravina, R.; Guerrieri, A. A java-based agent platform for programming wireless sensor networks. Comput. J. 2011, 54, 439–454. [Google Scholar] [CrossRef]
- McDonald, H.; Nugent, C.D.; Finlay, D.D.; Moore, G.; Burns, W.; Hallberg, J. Assessing the impact of the homeml format and the homeml suite within the research community. J. UCS 2013, 19, 2559–2576. [Google Scholar]
- Gonçalves, B.; Pereira Filho, J.G.; Andreão, R.V. ECGWARE: An ECG Markup Language for Ambulatory Telemonitoring and Decision Making Support. In Proceedings of the International Conference on Health Informatics, Funchal, Portugal, 28–31 January 2008; pp. 37–43.
- Rialle, V.; Lamy, J.-B.; Noury, N.; Bajolle, L. Telemonitoring of patients at home: A software agent approach. Comput. Meth. Prog. Biol. 2003, 72, 257–268. [Google Scholar] [CrossRef]
- Henricksen, K.; Indulska, J. A software engineering framework for context-aware pervasive computing. In Proceedings of the Second IEEE Annual Conference on Pervasive Computing and Communications, Orlando, FL, USA, 14–17 March 2004; pp. 77–86.
- Zhang, D.; Gu, T.; Wang, X. Enabling context-aware smart home with semantic web technologies. Int. J. Hum. Welf. Robot. Syst. 2005, 6, 12–20. [Google Scholar]
- Bouchard, B.; Giroux, S.; Bouzouane, A. A smart home agent for plan recognition of cognitively-impaired patients. J. Comput. 2006, 1, 53–62. [Google Scholar] [CrossRef]
- Chen, L.; Nugent, C.; Mulvenna, M.; Finlay, D.; Hong, X.; Poland, M. Using event calculus for behaviour reasoning and assistance in a smart home. In Smart Homes and Health Telematics; Springer: Berlin/Heidelberg, Germany, 2008; Volume 5120, pp. 81–89. [Google Scholar]
- Okeyo, G.; Chen, L.; Wang, H. Combining ontological and temporal formalisms for composite activity modelling and recognition in smart homes. Future Gener. Comput. Syst. 2014, 39, 29–43. [Google Scholar] [CrossRef]
- Chen, H.; Perich, F.; Finin, T.; Joshi, A. SOUPA: Standard ontology for ubiquitous and pervasive applications. In Proceedings of the First Annual International Conference on Mobile and Ubiquitous Systems: Networking and Services, Boston, MA, USA, 22–26 August 2004; pp. 258–267.
- Ye, J.; Stevenson, G.; Dobson, S. USMART: An unsupervised semantic mining activity recognition technique. ACM Trans Interact. Intell. Syst. 2014, 4, 16:1–16:27. [Google Scholar] [CrossRef]
- Lukasiewicz, T.; Straccia, U. Managing uncertainty and vagueness in description logics for the Semantic Web. Web Semant. 2008, 6, 291–308. [Google Scholar] [CrossRef]
- Liang, G.Q.; Cao, J.N. Social context-aware middleware: A survey. Pervasive Mob. Comput. 2015, 17, 207–219. [Google Scholar] [CrossRef]
- Bobillo, F.; Straccia, U. Fuzzy ontology representation using OWL 2. Int. J. Approx. Reason. 2011, 52, 1073–1094. [Google Scholar] [CrossRef]
- Bikakis, A.; Patkos, T.; Antoniou, G.; Plexousakis, D. A survey of semantics-based approaches for context reasoning in ambient intelligence. In Constructing Ambient Intelligence; Mühlhäuser, M., Ferscha, A., Aitenbichler, E., Eds.; Springer: Berlin/Heidelberg, Germany, 2008; Volume 11, pp. 14–23. [Google Scholar]
- Mamei, M.; Nagpal, R. Macro Programming through Bayesian Networks: Distributed Inference and Anomaly Detection. In Proceedings of the Fifth Annual IEEE International Conference on Pervasive Computing and Communications. PerCom ‘07, White Plains, NY, USA, 19–23 March 2007; pp. 87–96.
- Roman, M.; Hess, C.; Cerqueira, R.; Ranganathan, A.; Campbell, R.H.; Nahrstedt, K. A middleware infrastructure for active spaces. IEEE Pervasive Comput. 2002, 1, 74–83. [Google Scholar] [CrossRef]
- Marius Mikalsen, A.K.-P. Representing and reasoning about context in a mobile environment. Rev. Intell. Artif. 2005, 19, 479–498. [Google Scholar]
- Goix, L.W.; Valla, M.; Cerami, L.; Falcarin, P. Situation inference for mobile users: A rule based approach. In Proceedings of the 2007 International Conference on Mobile Data management, Mannheim, Germany, 1 May 2007; pp. 299–303.
- Wang, X.H.; da Qing, Z.; Tao, G.; Pung, H.K. Ontology based context modeling and reasoning using owl. In Proceedings of the 2nd IEEE Annual Conference on Pervasive Computing and Communications Workshops, Orlando, FL, USA, 14–17 March 2004; pp. 18–22.
- Van Kranenburg, H.; Bargh, M.; Iacob, S.; Peddemors, A. A context management framework for supporting context-aware distributed applications. IEEE Commun. Mag. 2006, 44, 67–74. [Google Scholar] [CrossRef]
- Katifori, A.; Halatsis, C.; Lepouras, G.; Vassilakis, C.; Giannopoulou, E. Ontology visualization methods—A survey. ACM Comput. Surv. (CSUR) 2007. [Google Scholar] [CrossRef]
- Priyantha, N.B.; Miu, A.K.L.; Teller, S. The cricket compass for context-aware mobile applications. In Proceedings of the 7th Annual International Conference on Mobile Computing and Networking, Rome, Italy, 16–21 July 2001.
- Dey, A.K.; Abowd, G.D. A conceptual framework and a toolkit for supporting the rapid prototyping of context-aware applications. Hum. Comput. Interact. 2001, 16, 97–166. [Google Scholar] [CrossRef]
- Roman, M.; Campbell, R.H. Gaia: Enabling active spaces. In Proceedings of the 9th Workshop on ACM SIGOPS European Workshop: Beyond the PC: New Challenges for the Operating System, Kolding, Denmark, 17–20 September 2000; ACM: Kolding, Denmark, 2000; pp. 229–234. [Google Scholar]
- Chen, H.; Finin, T.; Joshi, A.; Kagal, L. Intelligent agents meet the semantic web in smart spaces. IEEE Internet Comput. 2004, 8, 69–79. [Google Scholar] [CrossRef]
- Gu, T.; Pung, H.K.; Zhang, D.Q. A service-oriented middleware for building context-aware services. J. Netw. Comput. Appl. 2005, 28, 1–18. [Google Scholar] [CrossRef]
- Ellebak, K. A survey of context-aware middleware. In Proceedings of the 25th Conference on IASTED International Multi-Conference: Software Engineering, Innsbruck, Austria, 13–15 February 2007; ACTA Press: Innsbruck, Austria, 2007; pp. 148–155. [Google Scholar]
- Saeed, A.; Waheed, T. An extensive survey of context-aware middleware architectures. In Proceedings of the 2010 IEEE International Conference on Electro/Information Technology (EIT), Normal, IL, USA, 20–22 May 2010; pp. 1–6.
- Yurur, O.; Chi, L.; Moreno, W. A survey of context-aware middleware designs for human activity recognition. Commun. Mag. 2014, 52, 24–31. [Google Scholar] [CrossRef]
- Garlan, D.; Siewiorek, D.P.; Smailagic, A.; Steenkiste, P. Project aura: Toward distraction-free pervasive computing. IEEE Pervasive Comput. 2002, 1, 22–31. [Google Scholar] [CrossRef]
- Azcorra, A.; Banniza, T.; Chieng, D.; Fitzpatrick, J.; von-Hugo, D.; Natkaniec, M.; Robitzsch, S.; Zdarsky, F. Supporting carrier grade services over wireless mesh networks: The approach of the european fp-7 strep carmen [very large projects]. IEEE Commun. Mag. 2009, 47, 14–16. [Google Scholar] [CrossRef]
- Capra, L.; Emmerich, W.; Mascolo, C. Reflective middleware solutions for context-aware applications. In Proceedings of the Third International Conference on Metalevel Architectures and Separation of Crosscutting Concerns, Kyoto, Japan, 25–28 September 2001; Springer-Verlag: Berlin/Heidelberg, Germany, 2001; pp. 126–133. [Google Scholar]
- Barton John, K.T. The Cooltown User Experience; Hewlett Packard: Palo Alto, CA, USA, 2001. [Google Scholar]
- Sorensen, C.-F.; Wu, M.; Sivaharan, T.; Blair, G.S.; Okanda, P.; Friday, A.; Duran-Limon, H. A context-aware middleware for applications in mobile ad hoc environments. In Proceedings of the 2nd Workshop on Middleware for Pervasive and ad-hoc Computing, Toronto, ON, Canada, 18–24 October 2004; ACM: Toronto, ON, Canada, 2004; pp. 107–110. [Google Scholar]
- Ranganathan, A.; al-Muhtadi, J.; Chetan, S.; Campbell, R.; Mickunas, M.D. Middlewhere: A middleware for location awareness in ubiquitous computing applications. In Proceedings of the 5th ACM/IFIP/USENIX International Conference on Middleware, Toronto, ON, Canada, 18–24 October 2004; Springer-Verlag New York, Inc.: New York, NY, USA, 2004; pp. 397–416. [Google Scholar]
- Chan, A.T.S.; Siu-Nam, C. Mobipads: A reflective middleware for context-aware mobile computing. IEEE Trans. Softw. Eng. 2003, 29, 1072–1085. [Google Scholar] [CrossRef]
- Martínez, J.F.; Rodríguez-Molina, J.; Castillejo, P.; de Diego, R. Middleware Architectures for the Smart Grid: Survey and Challenges in the Foreseeable Future. Energies 2013, 6, 3593–3621. [Google Scholar] [CrossRef]
- Bondi, A.B. Characteristics of scalability and their impact on performance. In Proceedings of the 2nd International Workshop on Software and Performance, Oslo, Norway, 5 October 2000.
- IEEE. IEEE Standard Computer Dictionary: A Compilation of IEEE Standard Computer Glossaries; Institute of Electrical and Electronics Engineers: Piscataway, NJ, USA, 1990. [Google Scholar]
- Jie, W.; Dong, J. A simple service discovery and configuration protocol for embedded devices. In Proceedings of the 2006 International Conference on Communication Technology, ICCT ’06, Guilin, China, 27–30 November 2006.
- William, A.W.; Hari, B.; Lilley, J. The design and implementation of an intentional naming system. In Proceedings of the 17th ACM Symposium on Operating Systems Principles, Charleston, SC, USA, 12–15 December 1999.
- Big Data in the Cloud. Available online: http://www.ibm.com/developerworks/library/bd-bigdatacloud/bd-bigdatacloud-pdf.pdf (accessed on 9 July 2015).
- Pung, H.K.; Tao, G.; Xue, W.W. Context-aware Middleware for Pervasive Elderly Homecare. IEEE Sel. Areas Commun. 2009, 27, 510–524. [Google Scholar] [CrossRef]
- Hu, P.Z.; Chong, S.K.; Indulska, J.; Krishnaswamy, S. Context-aware and Resource Efficient Sensing Infrastructure for Context-aware Applications. In Proceedings of the 2010 8th IEEE International Conference on Pervasive Computing and Communications Workshops, Mannheim, Germany, 29 March–2 April 2010.
- Chong, S.K.; Gaber, M.M.; Loke, S.W.; Krishnaswamy, S. ARTS: Adaptive Rule Triggers on Sensors for Energy Conservation in Applications using Coarse-Granularity Data. In Proceedings of the ICESSS’ 08 International Coference on Embedded Software and Systems, Chengdu, China, 29–31 July 2008.
- Firner, B.; Moore, R.S.; Howard, R.; Martin, R.P.; Zhang, Y.Y. Poster: Smart buildings, sensor networks, and the Internet of Things. In Proceedings of the 9th ACM Conference on Embedded Networked Sensor Systems, NewYork, NY, USA, 1–4 Novembar 2011.
- The FIWARE Project. Available online: https://www.fiware.org/ (accessed on 30 July 2015).
- Perera, C.; Zaslavsky, A.; Christen, P.; Georgakopoulos, D. Ca4iot: Context awareness for internet of things. In Proceedings of the 2012 IEEE International Conference on Green Computing and Communications, Besançon, France, 20–23 November 2012; IEEE Computer Society: Washington, DC, USA, 2012; pp. 775–782. [Google Scholar]
- Wei, E.J.Y.; Chan, A.T.S. CAMPUS: A middleware for automated context-aware adaptation decision making at run time. Pervasive Mob. Comput. 2013, 9, 35–56. [Google Scholar] [CrossRef]
- Kang, J.; Park, S. Context-Aware Services Framework Based on Semantic Web Services for Automatic Discovery and Integration of Context. Int. J. Adv. Comput. Technol. (IJACT) 2013, 5. [Google Scholar] [CrossRef]
- Huertas Celdran, A.; Garcia Clemente, F.J.; Gil Perez, M.; Martinez Perez, G. SeCoMan: A Semantic-Aware Policy Framework for Developing Privacy-Preserving and Context-Aware Smart Applications. IEEE Syst. J. 2013. [Google Scholar] [CrossRef]
- Forkan, A.; Khalil, I.; Tari, Z. CoCaMAAL: A cloud-oriented context-aware middleware in ambient assisted living. Future Gener. Comput. Syst. 2014, 35, 114–127. [Google Scholar] [CrossRef]
- Forkan, A.R.M.; Khalil, I.; Ibaida, A.; Tari, Z. BDCaM: Big Data for Context-aware Monitoring—A Personalized Knowledge Discovery Framework for Assisted Healthcare. IEEE Trans. Cloud Comput. 2015, 99. [Google Scholar] [CrossRef]
- Wu, G.; Zhang, H.X.; Qiu, M.K.; Ming, Z.; Li, J.Y.; Qin, X. A decentralized approach for mining event correlations in distributed system monitoring. J. Parallel Distrib. Comput. 2012, 73, 330–340. [Google Scholar] [CrossRef]
- Khaddar, M.A.E.; Chraibi, M.; Harroud, H. A policy-based middleware for context-aware pervasive computing. Int. J. Pervasive Comput. Commun. 2015, 11, 43–68. [Google Scholar] [CrossRef]
- Antunes de Rocha, R.C.; Endler, M. Middleware: Context Management in Heterogeneous, Evolving Ubiquitous Environments. Distrib. Syst. Online 2006, 7. [Google Scholar] [CrossRef]
- Chaqfeh, M.A.; Mohamed, N. Challenges in middleware solutions for the internet of things. In Proceedings of the 2012 International Conference on Collaboration Technologies and Systems (CTS), Denver, CO, USA, 21–25 May 2012.
- Katasonov, A.; Kaykova, O.; Khriyenko, O. Smart semantic middleware for the Internet of Things. In Proceedings of the ICINCO-ICSO, Funchal, Portugal, 11–15 May 2008.
© 2015 by the authors; licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Li, X.; Eckert, M.; Martinez, J.-F.; Rubio, G. Context Aware Middleware Architectures: Survey and Challenges. Sensors 2015, 15, 20570-20607. https://doi.org/10.3390/s150820570
Li X, Eckert M, Martinez J-F, Rubio G. Context Aware Middleware Architectures: Survey and Challenges. Sensors. 2015; 15(8):20570-20607. https://doi.org/10.3390/s150820570
Chicago/Turabian StyleLi, Xin, Martina Eckert, José-Fernán Martinez, and Gregorio Rubio. 2015. "Context Aware Middleware Architectures: Survey and Challenges" Sensors 15, no. 8: 20570-20607. https://doi.org/10.3390/s150820570
APA StyleLi, X., Eckert, M., Martinez, J.-F., & Rubio, G. (2015). Context Aware Middleware Architectures: Survey and Challenges. Sensors, 15(8), 20570-20607. https://doi.org/10.3390/s150820570







