Abstract
Decoherence is the fundamental obstacle limiting the performance of quantum information processing devices. The problem of transmitting a quantum state (known or unknown) from one place to another is of great interest in this context. In this work, by following the recent theoretical proposal, we study an application of quantum state-dependent pre- and post-processing unitary operations for protecting the given (multi-qubit) quantum state against the effect of decoherence acting on all qubits. We observe the increase in the fidelity of the output quantum state both in a quantum emulation experiment, where all protecting unitaries are perfect, and in a real experiment with a cloud-accessible quantum processor, where protecting unitaries themselves are affected by the noise. We expect the considered approach to be useful for analyzing capabilities of quantum information processing devices in transmitting known quantum states. We also demonstrate the applicability of the developed approach for suppressing decoherence in the process of distributing a two-qubit state over remote physical qubits of a quantum processor.
1. Introduction
During recent decades, remarkable progress in developing quantum information processing devices has been achieved [1]. Specifically, currently available quantum processing devices are able to solve computational problems close to the limits of what can be achieved with most powerful classical technologies [2,3,4,5,6,7,8]. However, available quantum information processing devices have serious limitations, the main fundamental reason for this being decoherence. As a result, the number of operations that can be implemented before the level of errors exceeds the critical level is modest [8,9,10]. The possibility to achieve substantial computational advances in practically relevant problems with noisy intermediate-scale quantum (NISQ) devices is questionable [4,9,10], so the path to useful quantum advantages requires noise suppression. A possible solution that addresses this problem is to use quantum error correction [11,12,13,14,15,16]. In the last decades, basic principles of error correction schemes in the quantum domain have been demonstrated in experiments with optical systems [17], trapped ions [18,19,20,21,22], neutral atoms [23], and superconducting qubits [24,25,26,27,28]. A remarkable idea of using qubit protection from errors at a “physical” level [29,30], which is at the heart of topological quantum computing (for a review, see Refs. [31,32,33,34,35]), is also under study [36,37,38,39].
In addition to quantum error correction and topological quantum computing, one may consider error suppression that would reduce, but not fully eliminate, the effect of decoherence while processing a quantum state [40]. A variety of methods have been considered to achieve this goal [41,42,43,44,45,46,47,48,49,50]; however, the efficiency of these methods is deeply related to the problems of preserving entanglement in (open) quantum systems [51,52,53,54,55,56,57,58] (for a review, see Ref. [59]). Albeit applying error suppression techniques, such as dynamical decoupling (see, e.g., Refs. [60,61,62]), is of help to extend the computational capabilities of quantum devices, the experimental challenges for their practical implementation require additional progress in studies of the workflow of quantum processors [44]. Issues related to the non-Markovian character of these dynamics have been considered [63,64,65,66,67]. We note that problems of preserving entanglement are also deeply linked to the characterization of decoherence-free subspaces of quantum systems [68,69].
A specific problem that appears within the context of quantum information processing is how to transmit a quantum state (known or unknown) from one place to another, taking into account the effect of decoherence. The importance of this problem, especially in the case of known quantum states, lies in the fundamental domain of quantum information science, although various schemes for its usage in quantum data buses between quantum registers and/or processors capable of transmitting arbitrary quantum states have been discussed [70]. Considerable attention has been paid to the theoretical analysis of using quantum spin chains for the purpose of quantum state transfer [70,71,72,73,74,75,76]. Such an interest can be explained by the possibility of transferring (known or unknown) quantum states without additional interfaces [71]. The question related to the role of decoherence in this case still remains crucial in this scope of tasks and generally for the field of quantum information [77,78,79].
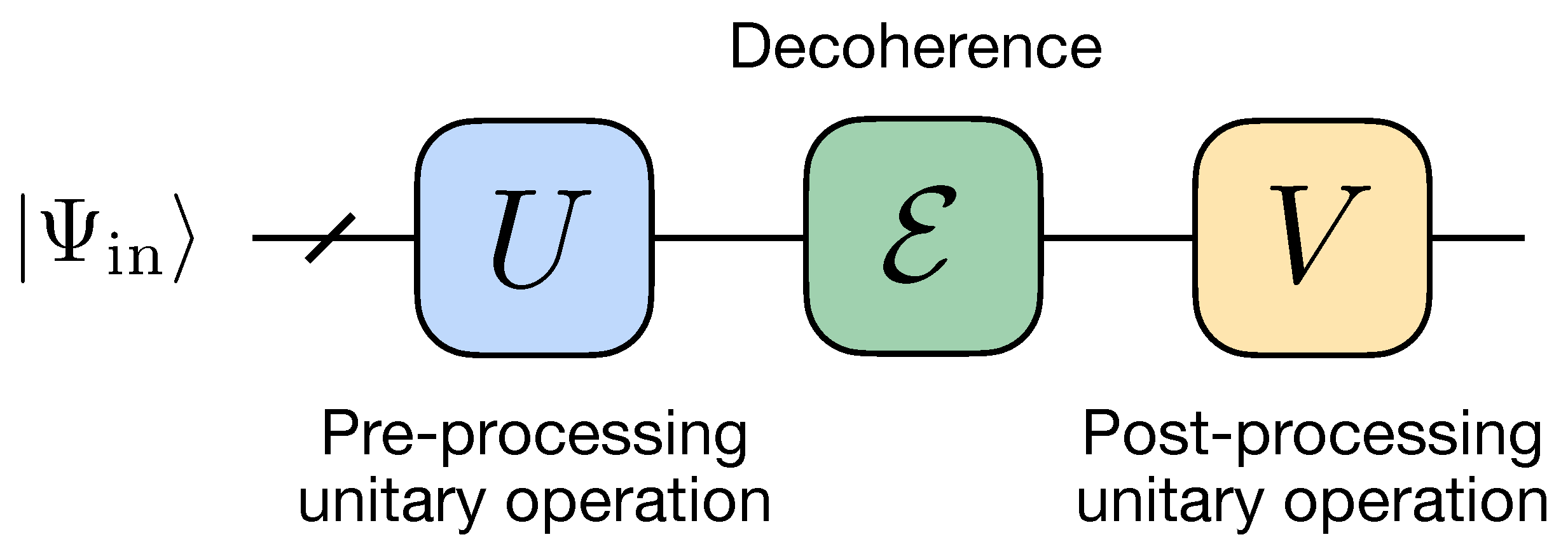
In this work, we stress a particular scheme for suppressing the effect of decoherence, which is based on the use of a unitary operation. This approach has been recently proposed theoretically in Ref. [80]. The general idea is to surround the decoherence channel by two unitary operators U and V (see Figure 1), which we refer to as pre- and post-processing, correspondingly, whose form is determined both by the decoherence channel and protected state . In contrast to the previous work [80], where was assumed to be acting non-trivially on one particular qubit, here we consider a more general case, where all qubits are affected by the decoherence process. First, we demonstrate a possibility to suppress decoherence effects in a quantum emulation experiment, where all qubits are affected by the same depolarizing, dephasing, or amplitude damping channels, and an implementation of all unitary gates is assumed to be ideal. We then implement the same protection scheme on a cloud-accessible quantum processor, where the used protecting gates are imperfect by themselves. In this case, we find that the protection scheme starts providing an advantage in the output fidelity starting from a certain threshold of the decoherence strength. Finally, we show how our scheme can be used for protecting two-qubit states during its distribution over remote physical qubits of a quantum processor, i.e., qubits which cannot be connected directly by native two-qubit gates. We note that the problem of recovering entanglement by local operations has been also considered in Ref. [51].
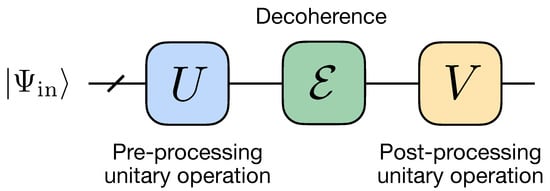
Figure 1.
Quantum circuit of error suppression based on pre-processing and post-processing unitary operations.
Our paper is organized as follows. In Section 2, we describe a general scheme of applying unitary operations for suppressing decoherence. In Section 3, we apply the scheme for emulators of quantum computers and analyze the efficiency of various schemes. In Section 4, we implement the same protection scheme on a cloud-accessible quantum processor. In Section 5, we analyze the applicability of the scheme for the case of quantum state transfer. We conclude in Section 6.
2. Error Suppression Using Unitary Operations
Let us consider a system of n two-level particles (qubits) initially prepared in a joint (perhaps, entangled) pure state . Due to an uncontrolled interaction with an external environment, this state suffers from a decoherence, which we describe by a completely positive trace-preserving (CPTP) map . In what follows, we refer to as a decoherence channel. The destructive effect of the decoherence channel can be quantified by fidelity:
Here, subscript indicates that this is the default case without applying the scheme described below.
In our work, we study possibilities to suppress decoherence, and thus increase the fidelity, by applying additional transformations to the system. These transformations take the form of additional unitary operators, U and V, named pre-processing and post-processing gates, and they act just before and after the action of the decoherence channel, correspondingly. Importantly, U and V are designed specifically for given initial state and decoherence channel . The expression for the resulting fidelity is given by the following expression:
In our consideration, we take U and V from certain, generally restricted, sets of unitaries and , respectively. One can see that as long as and contain identity operators
and so we expect an increase in fidelity compared to the default case (1).
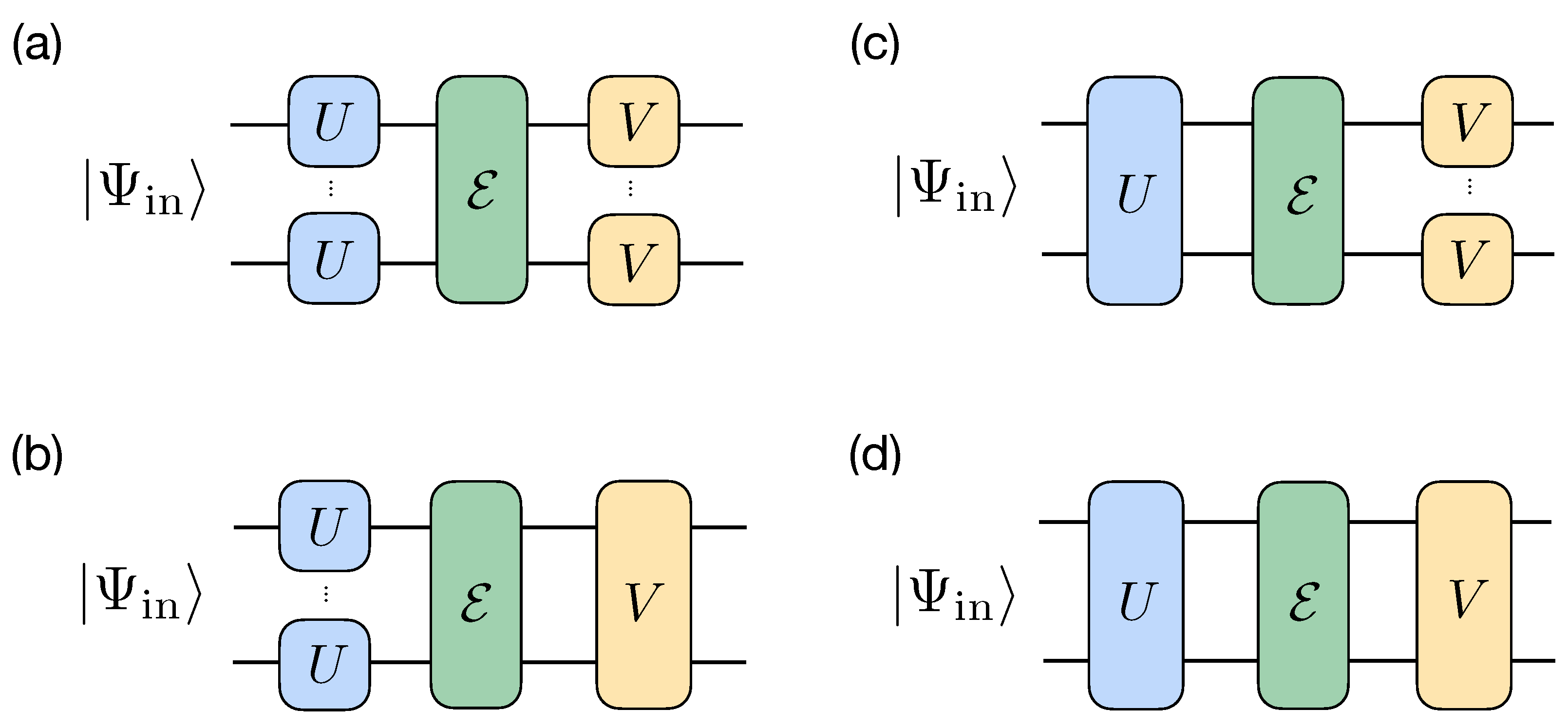
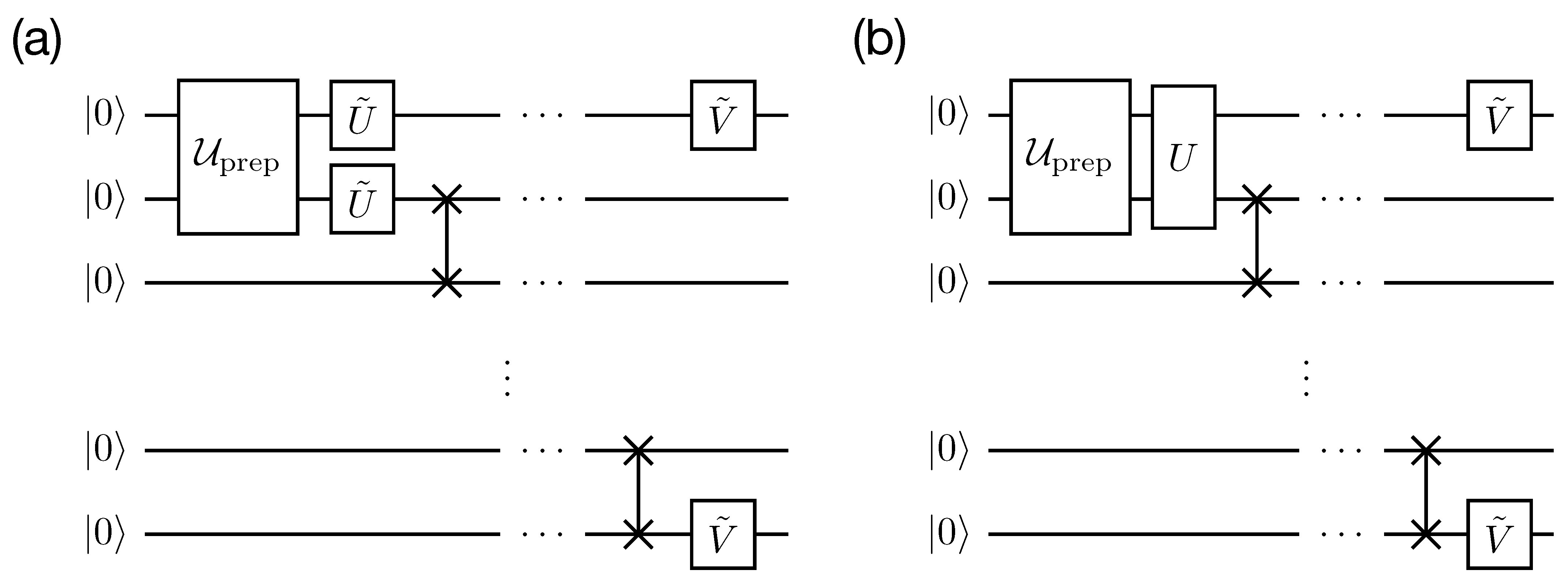
We consider two types of pre- and post-processing unitary operations: (i) individual operations, consisting of single-qubit unitaries, i.e., taken from group, and (ii) collective operations, represented as unitaries taken from the whole group. Since each of the pre- and post-processing operators can be either individual or collective, we obtain four possible combinations: (a) both unitary operations are individual; (b) the pre-processing unitary operation is individual, while the post-processing unitary operation is collective; (c) the pre-processing unitary operation is collective, while the post-processing unitary operation is individual; and (d) both unitary operations are collective. All four schemes are schematically shown in Figure 2. Since (b) and (c) include (a) as a special case, and (d) also includes (a–c), the maximal achievable fidelities in the schemes satisfy the following inequality:
where the first (second) subindex specifies the type of the pre- (post-) processing operator. We note that although replacing individual operators with collective ones leads to an increase in performance, constructing collective operators yields an additional overhead in the number of gates and the corresponding circuit depth: individual operators have a unit-depth and consist of no more than n single-qubit gates, while a transformation between two given pure n-qubit states, which is an aim of collective operators, generally requires an exponential in n number of single- and two-qubit gates or an exponential number of ancillary qubits for linear depth circuits [81,82].
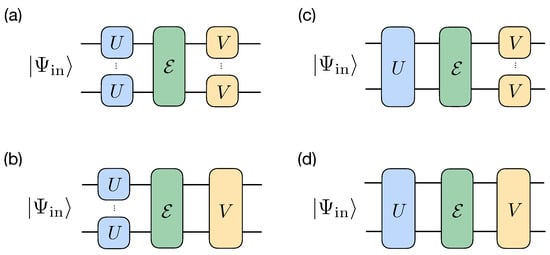
Figure 2.
Schemes for protecting a pure state from the decoherence channel : individual–individual (a), individual–collective (b), collective–individual scheme (c), and collective–collective (d). Note that single-qubit U and V can be different for different qubits.
The subject of how and are related to each other is rather intriguing. In Ref. [80], it has been demonstrated that for a single-qubit decoherence, i.e.,
where and are arbitrary and identity single-qubit channels correspondingly, one has . The maximal achievable fidelities for individual–collective and collective–individual schemes are also the same for an arbitrary self-dual . Indeed, since
if a certain value of fidelity is achieved in one scheme, the same value can be achieved in the other scheme by replacing , . Therefore, the maximal achievable values are the same. We leave the consideration of the relation between and in the case of a general decoherence channel for further studies.
In what follows, we analyze the performance of different schemes with respect to the fixed state
where , and we set .
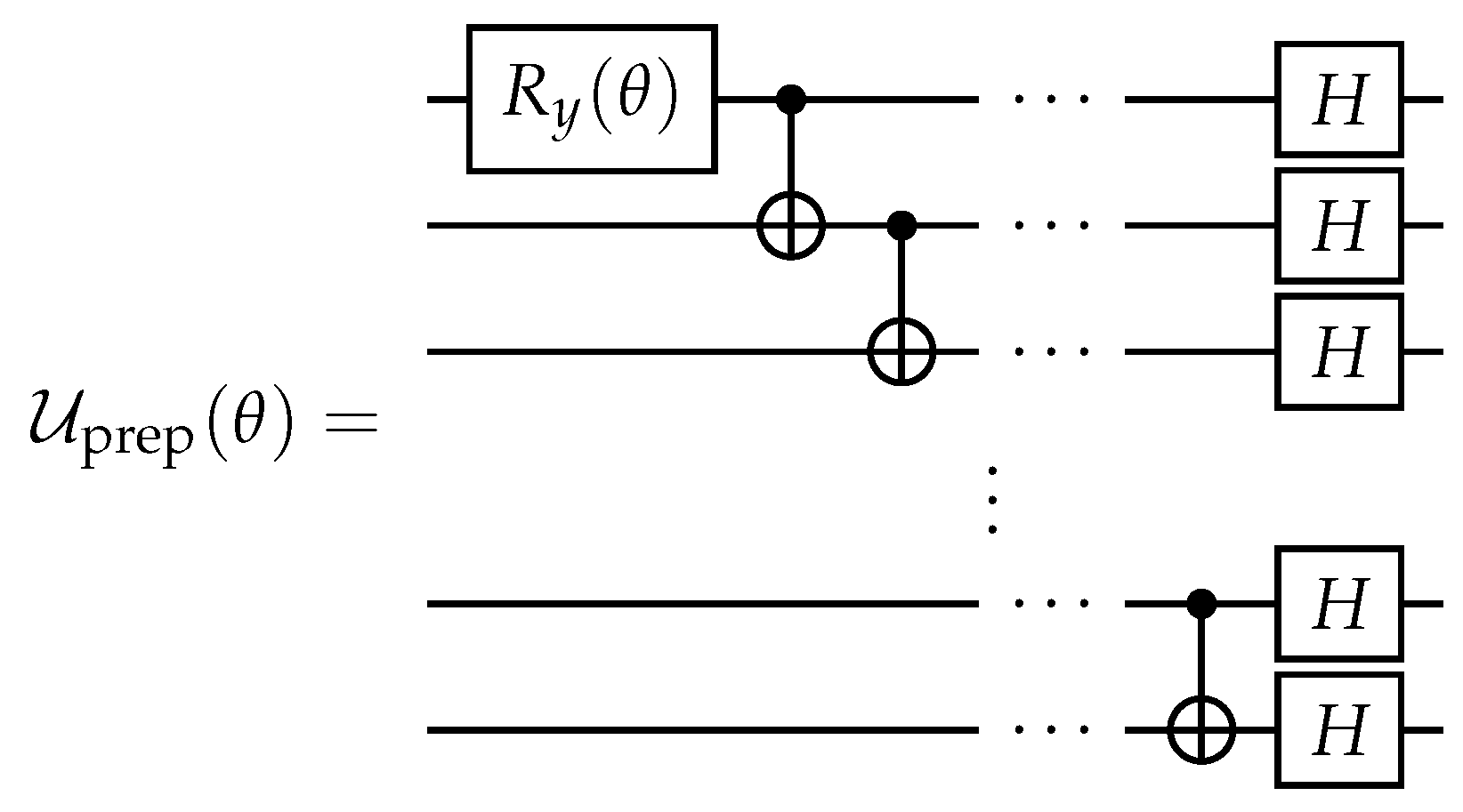
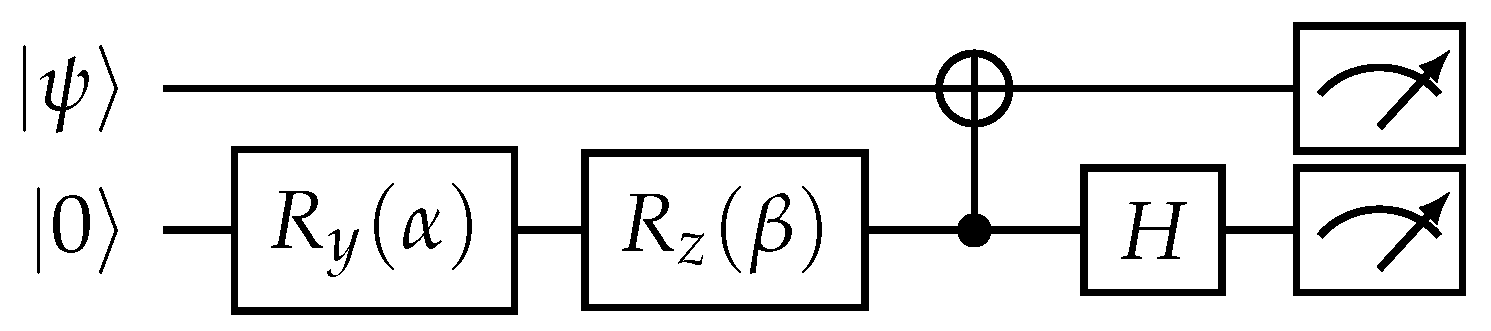
Our choice for this state is motivated by several reasons. The first is that it is entangled but it is not a maximally entangled state. According to the results of Ref. [80], it is the most interesting case for unitaries-based protection. The second reason is that the reduced single-qubit states of are not diagonal in the computational basis. It makes it interesting to consider these schemes concerning ‘basis-dependent’ decoherence channels, e.g., amplitude damping and dephasing. Third, can be easily prepared from by applying gate, whose decomposition into standard single- and two-qubit gates is shown in Figure 3. Here and after, standard notations for controlled-NOT (CNOT), Hadamard, and Pauli rotation gates are used. Next, we use as a template for constructing collective protecting operators.
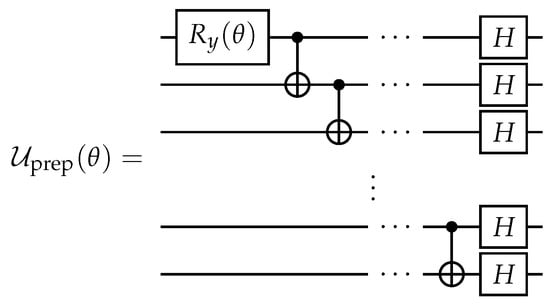
Figure 3.
Quantum circuit for the unitary operator performing preparation of the n-qubit input state .
Before proceeding, we would like to note that although from the practical point of view, the most interesting are individual–individual and collective–individual schemes, we consider all four scenarios to reveal the whole picture. We also note that in the presented consideration, the pre- and post-processing operations are assumed to be perfect. However, this may not be the case at all in real-world setups [43,44,45,46,48,49,50].
3. Demonstrating Error Suppression with a Quantum Emulator
Here, we demonstrate the performance of the considered error suppression scheme using an emulator of a quantum processor. Namely, we employ the AerSimulator emulator provided as part of the qiskit package [83]. We consider a simplified error model, where the decoherence channel is taken as a tensor power of a single-qubit channel , namely,
We also assume the ideal realization of employed pre- and post-processing unitaries.
Three basic decoherence channels are studied: (i) amplitude damping, (ii) dephasing, and (iii) depolarizing channels. Their Kraus operators () are respectively defined as:
where is a single-qubit identity matrix; , , stand for standard x, y, and z Pauli matrices, respectively; and an additional parameter determines the decoherence strength. We note that the form of the amplitude damping channel (9) corresponds to a spontaneous decay from to , dephasing channel corresponds to destruction of non-diagonal elements, and depolarizing is ‘basis-invariant’ in the sense that for any unitary u. We also note that the dephasing and depolarizing channels are self-dual, since their Kraus operators are Hermitian.
In what follows, we discuss the choice of unitaries for each type of protection scheme. The idea is that U and V should meet two conditions: (i) after the action of U, the input state should be maximally robust to noise, and (ii) the action of U and V together should preserve the input state as much as possible. We choose unitaries for each protection scheme based on these conditions.
In the case of individual–individual scheme, we take
where H is a standard Hadamard gate, and is a rotation around x-axis. The idea behind this choice is in turning each of reduced single-qubit states of into a diagonal form such that the population on is larger than the one on . This form of a density matrix is the most robust against considered decoherence channels [80].
In the case of an individual–collective scheme, we take
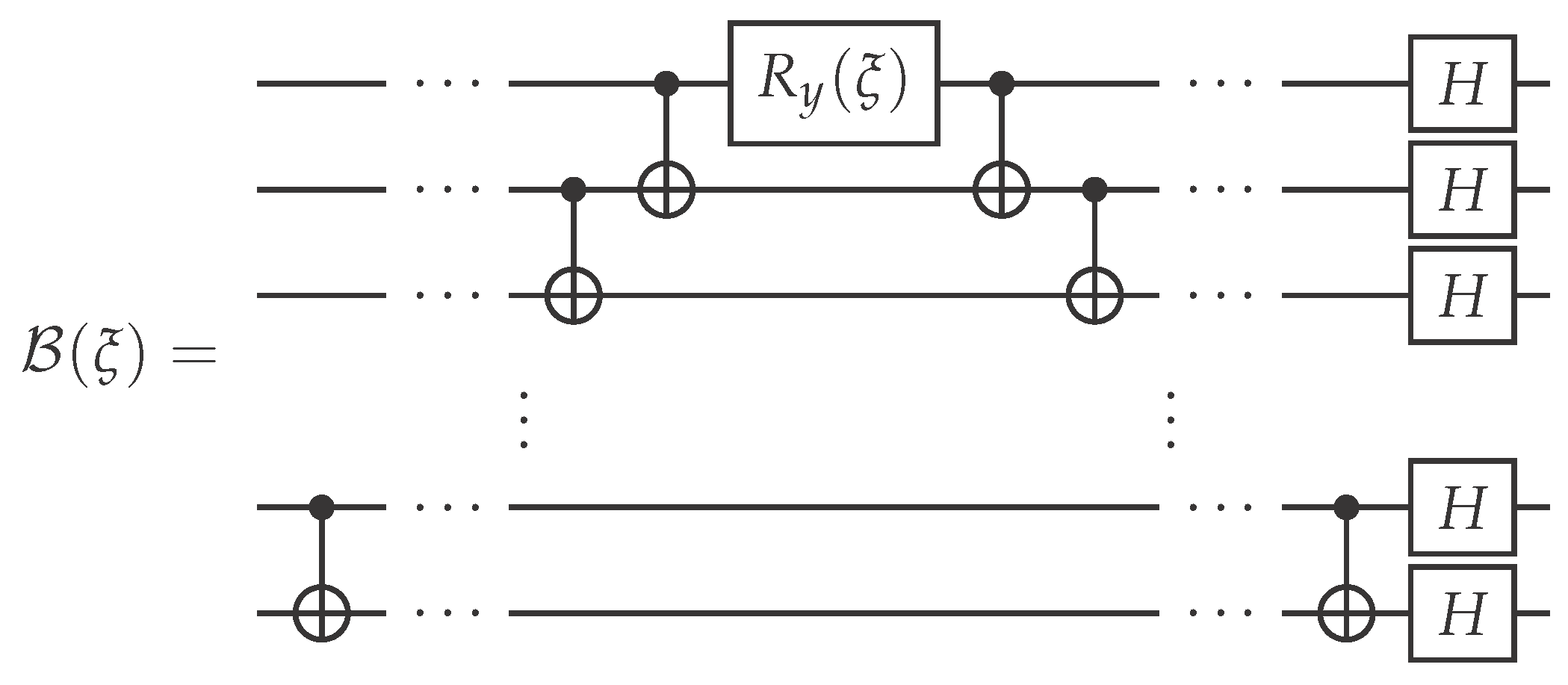
where is a unitary whose circuit is shown in Figure 4, and the angle is obtained by maximizing resulting fidelity value
over . The choice of the collective operator’s form is motivated by the state preparation circuit. In fact, it corresponds to a deconstruct-construct sequence with an additional rotation in the middle (defined by parameter ) corresponding to a change in an entanglement parameter initially specified by in the state preparation circuit.
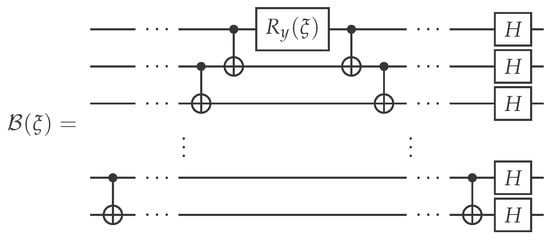
Figure 4.
Quantum circuit of the collective operation .
The case of the collective–individual scheme is similar to the individual–collective one and is obtained by taking
where is obtained by maximizing
Finally, the collective–collective scheme is obtained by taking
with . This choice corresponds to the deconstruction of back to , which is the most stable state with respect to the considered decoherence channels, and re-preparation of after the action of channel.
To measure fidelity values, we implement the circuit shown in Figure 5 for two- and four-qubit quantum systems. We consider four protection schemes, as well as a default scheme without protection, with respect to the three introduced types of decoherence channels, and different values of p. Simulation results are obtained for runs of each circuit with a fixed decoherence channel (and a fixed value of p). Fidelity values are calculated as frequencies of obtaining all-zeros outcomes in the read-out measurements. The results are shown in Figure 6. First of all, we note that the following inequalities hold for all decoherence models:
Moreover, for the self-dual dephasing and depolarizing channels, and for the covariant depolarizing channel. We also note that for amplitude damping and dephasing channels, since is not affected by the decoherence, yet for the depolarizing channel. The reason for the latter fact is that the depolarizing channel always increases the mixedness of input states, and there is no pure state that is preserved under the depolarizing channel. Therefore, even the collective–collective scheme does not provide unit fidelity in the case of depolarizing channels.
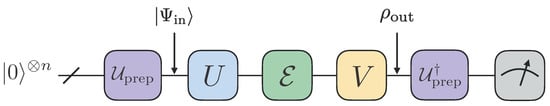
Figure 5.
Circuit for the measurement of the resulting fidelity. Parameter for the is taken to be equal to .
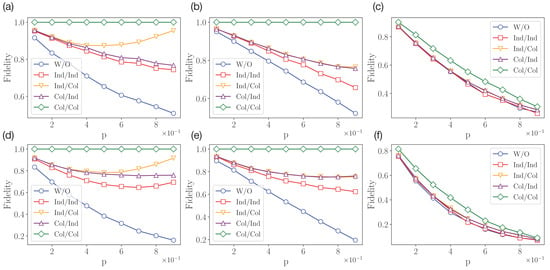
Figure 6.
Simulation results for qubit (a–c) and qubit (d–f) cases. The amplitude damping (a,d), dephasing (b,e), and depolarizing (c,f) channels are considered.
There is also an interesting effect of non-monotonic behaviour of fidelity as a function of p in the case of the amplitude damping channel in the individual–collective and individual–individual schemes. In the case of the individual–collective scheme, this behaviour can be explained by the fact the post-processing collective operator actually serves to re-prepare the state from the state coming from . The resulting fidelity is thus determined by the purity of . In the case of , the amplitude damping channel outputs pure , and so we achieve the unit fidelity.
For the individual–individual scheme, the resulting fidelity takes the following form:
where with , . For in the form of single-qubit amplitude damping channels of the same strength p, it transforms into:
which is non-monotonic for .
4. Validating Error Suppression with a Cloud-Based Quantum Processor
In this section, we implement circuits from the previous section on a cloud-accessible, five-qubit quantum processor ibmq_manila. To access the decoherence process on the real device, we utilize the Delay instructions in the natural time units (dt). Delay time can be seen as the strength of the decoherence distortion of the input state on the real device.
It is also important to note that the form of the decoherence channel is not exactly known. One can expect that has a tensor product form of single-qubit channels, each consisting of depolarizing, dephasing, and amplitude damping ones [84]. However, certain collective decoherence effects can also take place due to a qubits’ crosstalk. That is why, to optimize the parameter of the collective protecting operation , we perform additional measurements. We demonstrate the resulting dependence of the input–output fidelity on the angle in Figure 7. We observe the drift in the optimal parameter with the increase in delay time. This highlights the usefulness of utilizing the collective operator in this case.
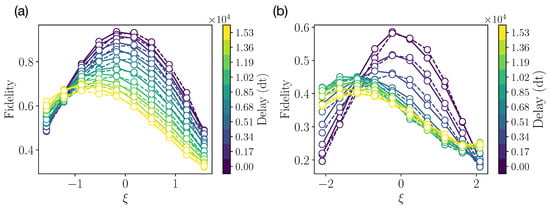
Figure 7.
Experimental results of angle calibration from IBMQ quantum processor for (a) two-qubit experiment and (b) four-qubit experiment. Solid and dashed lines stand for collective–individual and individual–collective schemes, respectively.
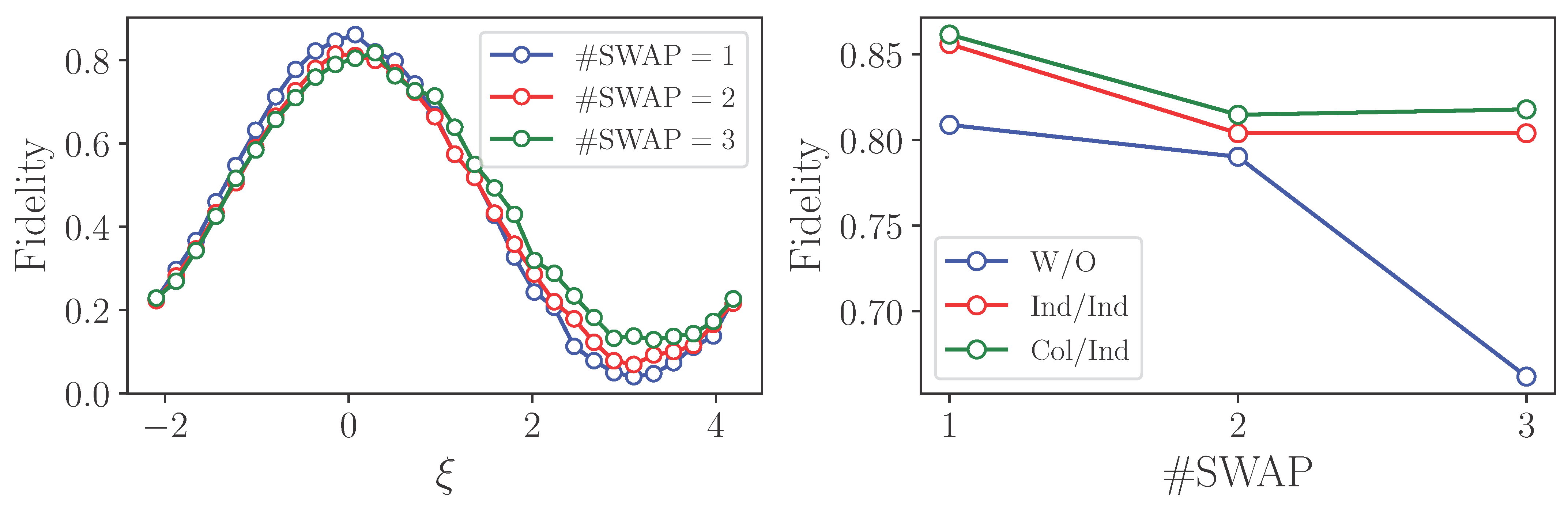
The results of the final fidelity measurements for and qubits are shown in Figure 8. We note that the resulting input–output fidelities, given in this section, are obtained experimentally without additional circuit transpilation. We can see that the resulting input–output fidelity is lower for any protection scheme compared with the unprotected case for weak decoherence action. This is due to the additional noise from single- and multiqubit gates in pre- and post-processing operators. However, with the enhancement of the decoherence, we observe the gain from protection schemes. This demonstrates the existence of a tradeoff between the use of additional unitary operations to prevent decoherence and the noise created by these operations. Similar to the results of the previous section, the collective–collective scheme shows the best performance starting from some large enough noise. This can be explained by the triviality of the protection operator’s action. At the same time, we observe that the individual–collective and collective–individual schemes have almost the same performance.
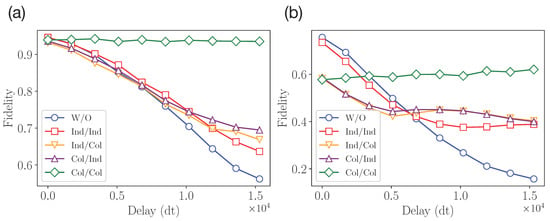
Figure 8.
Experimental results from IBMQ quantum processor for (a) two-qubit experiment and (b) four-qubit experiment.
5. Error Suppression in a State Transfer
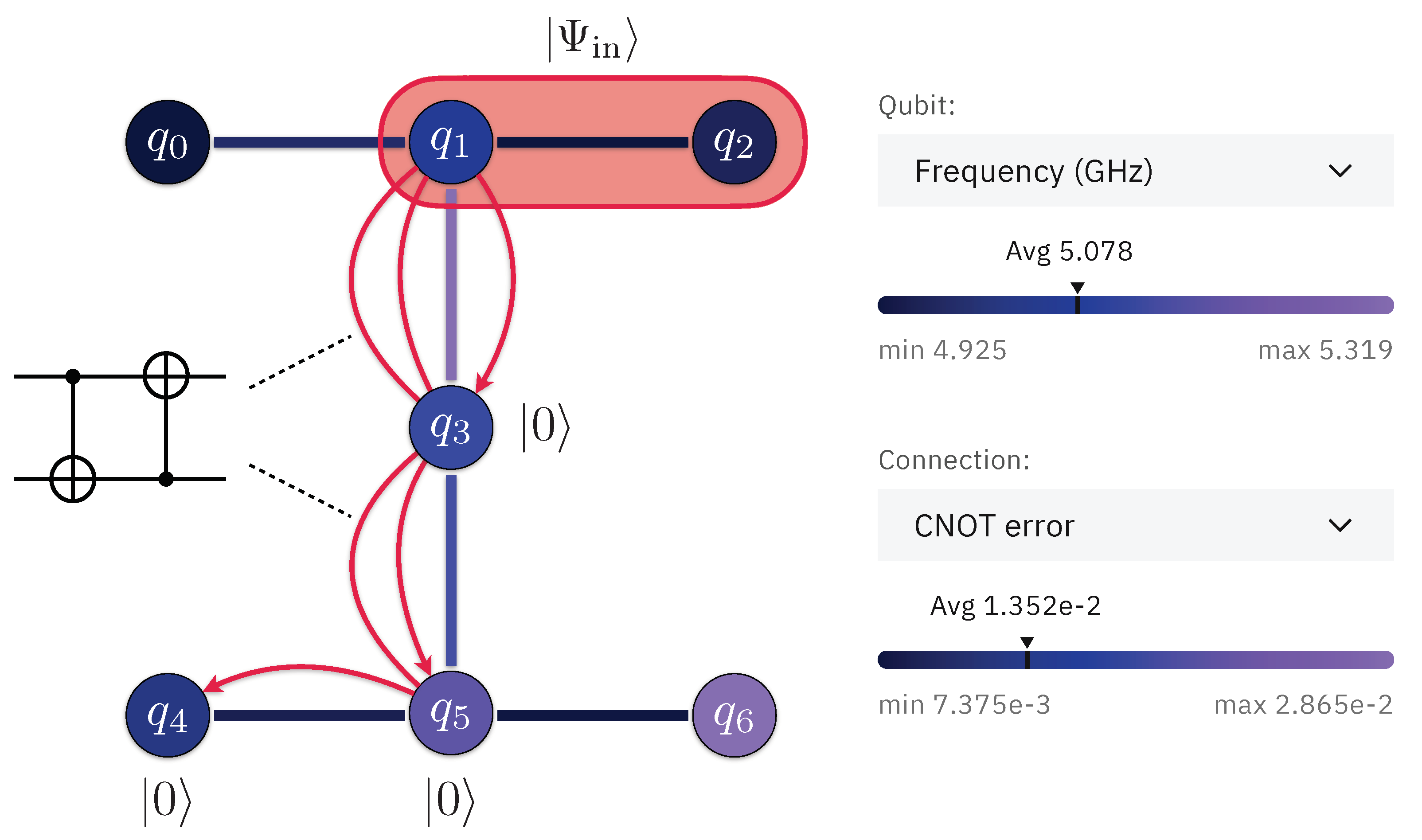
Here, we consider a practical problem of distributing a two-qubit state over remote physical qubits of a quantum processor. Specifically, we analyze distributing the entangled state inside the cloud-accessible seven-qubit ibm_oslo quantum processor (see Figure 9). This can be considered as a prototype experiment for realizing quantum state transfer between distinct quantum information processing devices connected via a quantum interface [1].
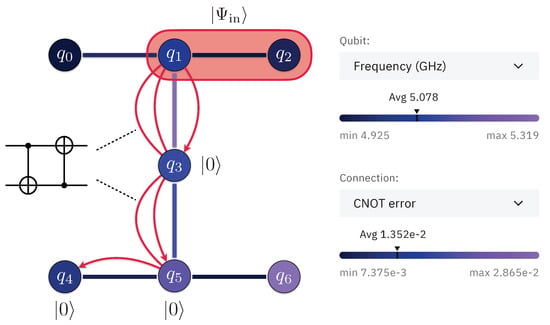
Figure 9.
Scheme of the ibm_oslo quantum processor experiment (inset is from quantum-computing.ibm.com, accessed on 26 December 2022).
In this setting, we consider two protection schemes: (i) individual–individual and (ii) collective–individual. Quantum circuits of the state transfer experiments are shown in Figure 10. As the individual–individual scheme’s protecting unitaries, we take:
In the case of the collective–individual protection scheme, we take"
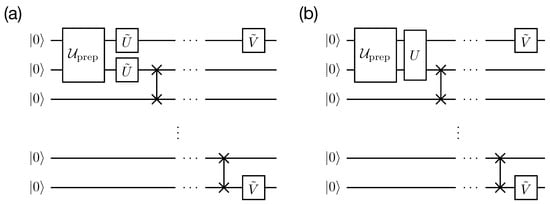
Figure 10.
Quantum circuits of state transfer experiments with (a) individual–individual protection scheme and (b) collective–individual protection scheme.
In our demonstrations, after preparing the input two-qubit state using the operator, we transfer the state of one qubit, via operations, through the environment initialized in the state. Then, we reconstruct the whole two-qubit state using the standard linear inversion technique, based on the symmetric informationally complete positive operator-valued measure (SIC-POVM) measurements, on each of the two qubits. The fidelity is calculated as .
The SIC-POVM quantum state tomography circuit is shown in Figure 11. The tomography circuit utilizes an ancilla qubit for each target qubit. The corresponding circuit parameters realizing SIC-POVM measurements are given by
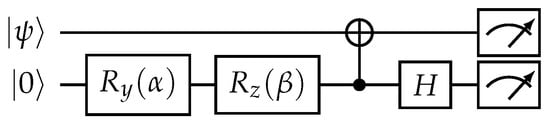
Figure 11.
Quantum circuit for input state tomography.
Physically, for tomography we use the same environment qubits as during state transfer since, after SWAP operations, the state of the mediated environment does not change. As we provide the real-world example, we optimize the transfer circuit to achieve maximally accessible fidelity. Therefore, we reduce the SWAP operations to two CNOT operations thanks to the knowledge of the initial state of the environment. The topology of the state transfer and optimized operations are shown in Figure 9.
The result of the optimization of the parameter and the resulting input–output fidelities are shown in Figure 12. We note that as this is a practical example, the experimental data was obtained from transpiled circuits. We provide the results of several protocol runs corresponding to a different number of SWAP operations. One can observe a sizable increase in fidelity compared to the unprotected case.
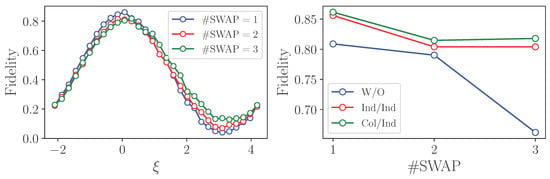
Figure 12.
Experimental results of state transfer from IBM quantum processor.
It is worth mentioning that the considered approach for a state propagation protection can be used in distributed computing architectures, where two or more ‘stationary’ quantum processors are physically separated and connected by means of ‘flying’ qubits. The appearing decoherence channel then consists of imperfections related to interactions between stationary and flying qubits, as well a decoherence during the transmission of flying qubits through some medium, e.g., optical fibres or free space. Anyway, individual–individual and a collective–individual schemes can be used in this case, where collective operations are realized within a single quantum processor.
6. Conclusions
We have demonstrated the implementation of the scheme for suppressing decoherence in multi-qubit quantum systems according to a recent theoretical proposal [80]. The simulation of the scheme for suppressing decoherence in two- and four-qubit quantum systems was carried out for three main types of decoherence: particularly, depolarizing, dephasing, and amplitude damping, which were presented as quantum channels acting on each qubit of two- and four-qubit systems. As a result, the dependencies of the fidelity of the output quantum state on the strength of decoherence have been obtained. It has been shown that the most advantageous scheme of suppression, as expected, is the collective–collective scheme, which effectively suppresses decoherence in all cases. The realization of collective operators in the general case, however, requires an exponential number of elementary single- and two-qubit gates, which limits their applicability in realistic conditions.
We have shown the paradigmatic example of decoherence effects suppression in experiments with a cloud-accessible, five-qubit quantum processor ibmq_manila, where the strength of the decoherence is controlled by the delay. We have observed the results of increasing the fidelity value both in the case of two-qubit decoherence and in the case of four-qubit decoherence for all types of schemes. We also have demonstrated the real-world example of quantum state transfer with a cloud-accessible, seven-qubit quantum processor ibm_oslo. We have observed the increase in fidelity for optimized state transfer protocol up to . We expect our findings to be useful for increasing the performance of current NISQ devices.
Author Contributions
E.O.K. developed the idea of the method. M.A.G. played the leading role in the development of the method. M.A.G., E.O.K. and A.S.M. realized the method and conducted demonstrations using emulators and quantum processors. E.O.K., A.S.M. and A.K.F. provided details from the analytical point of view. E.O.K. proposed the demonstration of the method to quantum state transfer. All the authors contributed to the discussion of the results. A.K.F. wrote the paper with the contribution from all coauthors. A.K.F. supervised the project. All authors have read and agreed to the published version of the manuscript.
Funding
This work was supported by the Russian Roadmap on Quantum Computing (the development of the method and experimental tests; Contract No. 868-1.3-15/15-2021, 5 October 2021), by the Priority 2030 program at the National University of Science and Technology “MISIS” under the project K1-2022-027 (analysis of the method), and by the Russian Science Foundation Grant No. 19-71-10091 (work of E.K., applying the error suppression scheme for quantum state transfer). The work of A.S.M is also supported by Scholarship of the Russian Federation President (No. SP-1351.2022.5).
Institutional Review Board Statement
Not applicable.
Data Availability Statement
All data available upon the reasonable request.
Acknowledgments
We acknowledge use of the IBM Q Experience for this work (our results were collected in September 2022). The views expressed are those of the authors and do not reflect the official policy or position of IBM or the IBM Q Experience team. We thank S. Straupe for the useful comments.
Conflicts of Interest
Owing to the employments and consulting activities of authors, the authors have financial interests in the commercial applications of quantum computing. The authors do not have any non-financial competing interest.
References
- Wehner, S.; Elkouss, D.; Hanson, R. Quantum internet: A vision for the road ahead. Science 2018, 362, eaam9288. [Google Scholar] [CrossRef]
- Montanaro, A. Quantum algorithms: An overview. Npj Quantum Inf. 2016, 2, 15023. [Google Scholar] [CrossRef]
- Harrow, A.W.; Montanaro, A. Quantum computational supremacy. Nature 2017, 549, 203–209. [Google Scholar] [CrossRef]
- Fedorov, A.K.; Gisin, N.; Beloussov, S.M.; Lvovsky, A.I. Quantum computing at the quantum advantage threshold: A down-to-business review. arXiv 2022, arXiv:2203.17181. [Google Scholar] [CrossRef]
- Arute, F.; Arya, K.; Babbush, R.; Bacon, D.; Bardin, J.C.; Barends, R.; Biswas, R.; Boixo, S.; Brandao, F.G.S.L.; Buell, D.A.; et al. Quantum supremacy using a programmable superconducting processor. Nature 2019, 574, 505–510. [Google Scholar] [CrossRef]
- Zhong, H.S.; Wang, H.; Deng, Y.H.; Chen, M.C.; Peng, L.C.; Luo, Y.H.; Qin, J.; Wu, D.; Ding, X.; Hu, Y.; et al. Quantum computational advantage using photons. Science 2020, 370, 1460–1463. [Google Scholar] [CrossRef]
- Biamonte, J.; Wittek, P.; Pancotti, N.; Rebentrost, P.; Wiebe, N.; Lloyd, S. Quantum machine learning. Nature 2017, 549, 195–202. [Google Scholar] [CrossRef]
- Huang, H.L.; Xu, X.Y.; Guo, C.; Tian, G.; Wei, S.J.; Sun, X.; Bao, W.S.; Long, G.L. Near-Term Quantum Computing Techniques: Variational Quantum Algorithms, Error Mitigation, Circuit Compilation, Benchmarking and Classical Simulation. arXiv 2022, arXiv:2211.08737. [Google Scholar] [CrossRef]
- Cerezo, M.; Arrasmith, A.; Babbush, R.; Benjamin, S.C.; Endo, S.; Fujii, K.; McClean, J.R.; Mitarai, K.; Yuan, X.; Cincio, L.; et al. Variational quantum algorithms. Nat. Rev. Phys. 2021, 3, 625–644. [Google Scholar] [CrossRef]
- Bharti, K.; Cervera-Lierta, A.; Kyaw, T.H.; Haug, T.; Alperin-Lea, S.; Anand, A.; Degroote, M.; Heimonen, H.; Kottmann, J.S.; Menke, T.; et al. Noisy intermediate-scale quantum algorithms. Rev. Mod. Phys. 2022, 94, 015004. [Google Scholar] [CrossRef]
- Shor, P.W. Scheme for reducing decoherence in quantum computer memory. Phys. Rev. A 1995, 52, R2493–R2496. [Google Scholar] [CrossRef]
- Calderbank, A.R.; Shor, P.W. Good quantum error-correcting codes exist. Phys. Rev. A 1996, 54, 1098–1105. [Google Scholar] [CrossRef]
- Shor, P. Fault-tolerant quantum computation. In Proceedings of the 37th Conference on Foundations of Computer Science, Burlington, VT, USA, 14–16 October 1996; pp. 56–65. [Google Scholar] [CrossRef]
- Bacon, D. Operator quantum error-correcting subsystems for self-correcting quantum memories. Phys. Rev. A 2006, 73, 012340. [Google Scholar] [CrossRef]
- Fowler, A.G.; Mariantoni, M.; Martinis, J.M.; Cleland, A.N. Surface codes: Towards practical large-scale quantum computation. Phys. Rev. A 2012, 86, 032324. [Google Scholar] [CrossRef]
- Antipov, A.V.; Kiktenko, E.O.; Fedorov, A.K. Realizing a class of stabilizer quantum error correction codes using a single ancilla and circular connectivity. arXiv 2022, arXiv:2207.13356. [Google Scholar] [CrossRef]
- Pittman, T.B.; Jacobs, B.C.; Franson, J.D. Demonstration of quantum error correction using linear optics. Phys. Rev. A 2005, 71, 052332. [Google Scholar] [CrossRef]
- Chiaverini, J.; Leibfried, D.; Schaetz, T.; Barrett, M.D.; Blakestad, R.B.; Britton, J.; Itano, W.M.; Jost, J.D.; Knill, E.; Langer, C.; et al. Realization of quantum error correction. Nature 2004, 432, 602–605. [Google Scholar] [CrossRef]
- Schindler, P.; Barreiro, J.T.; Monz, T.; Nebendahl, V.; Nigg, D.; Chwalla, M.; Hennrich, M.; Blatt, R. Experimental Repetitive Quantum Error Correction. Science 2011, 332, 1059–1061. [Google Scholar] [CrossRef]
- Stricker, R.; Vodola, D.; Erhard, A.; Postler, L.; Meth, M.; Ringbauer, M.; Schindler, P.; Monz, T.; Müller, M.; Blatt, R. Experimental deterministic correction of qubit loss. Nature 2020, 585, 207–210. [Google Scholar] [CrossRef]
- Egan, L.; Debroy, D.M.; Noel, C.; Risinger, A.; Zhu, D.; Biswas, D.; Newman, M.; Li, M.; Brown, K.R.; Cetina, M.; et al. Fault-tolerant control of an error-corrected qubit. Nature 2021, 598, 281–286. [Google Scholar] [CrossRef]
- Erhard, A.; Poulsen Nautrup, H.; Meth, M.; Postler, L.; Stricker, R.; Stadler, M.; Negnevitsky, V.; Ringbauer, M.; Schindler, P.; Briegel, H.J.; et al. Entangling logical qubits with lattice surgery. Nature 2021, 589, 220–224. [Google Scholar] [CrossRef]
- Bluvstein, D.; Levine, H.; Semeghini, G.; Wang, T.T.; Ebadi, S.; Kalinowski, M.; Keesling, A.; Maskara, N.; Pichler, H.; Greiner, M.; et al. A quantum processor based on coherent transport of entangled atom arrays. Nature 2022, 604, 451–456. [Google Scholar] [CrossRef]
- Reed, M.D.; DiCarlo, L.; Nigg, S.E.; Sun, L.; Frunzio, L.; Girvin, S.M.; Schoelkopf, R.J. Realization of three-qubit quantum error correction with superconducting circuits. Nature 2012, 482, 382–385. [Google Scholar] [CrossRef]
- Ofek, N.; Petrenko, A.; Heeres, R.; Reinhold, P.; Leghtas, Z.; Vlastakis, B.; Liu, Y.; Frunzio, L.; Girvin, S.M.; Jiang, L.; et al. Extending the lifetime of a quantum bit with error correction in superconducting circuits. Nature 2016, 536, 441–445. [Google Scholar] [CrossRef]
- Chen, Z.; Satzinger, K.J.; Atalaya, J.; Korotkov, A.N.; Dunsworth, A.; Sank, D.; Quintana, C.; McEwen, M.; Barends, R.; Klimov, P.V.; et al. Exponential suppression of bit or phase errors with cyclic error correction. Nature 2021, 595, 383–387. [Google Scholar] [CrossRef]
- Zhao, Y.; Ye, Y.; Huang, H.L.; Zhang, Y.; Wu, D.; Guan, H.; Zhu, Q.; Wei, Z.; He, T.; Cao, S.; et al. Realizing an Error-Correcting Surface Code with Superconducting Qubits. arXiv 2021, arXiv:2112.13505. [Google Scholar]
- Acharya, R.; Aleiner, I.; Allen, R.; Andersen, T.I.; Ansmann, M.; Arute, F.; Arya, K.; Asfaw, A.; Atalaya, J.; Babbush, R.; et al. Suppressing quantum errors by scaling a surface code logical qubit. arXiv 2022, arXiv:2207.06431. [Google Scholar] [CrossRef]
- Kitaev, A.Y. Quantum computations: Algorithms and error correction. Russ. Math. Surv. 1997, 52, 1191–1249. [Google Scholar] [CrossRef]
- Kitaev, A.Y. Fault-tolerant quantum computation by anyons. Ann. Phys. 2003, 303, 2–30. [Google Scholar] [CrossRef]
- Brennen, G.K.; Pachos, J.K. Why should anyone care about computing with anyons? Proc. R. Soc. A Math. Phys. Eng. Sci. 2008, 464, 1–24. [Google Scholar] [CrossRef]
- Nayak, C.; Simon, S.H.; Stern, A.; Freedman, M.; Das Sarma, S. Non-Abelian anyons and topological quantum computation. Rev. Mod. Phys. 2008, 80, 1083–1159. [Google Scholar] [CrossRef]
- Stern, A.; Lindner, N.H. Topological Quantum Computation. Science 2013, 339, 1179–1184. [Google Scholar] [CrossRef] [PubMed]
- Sarma, S.D.; Freedman, M.; Nayak, C. Majorana zero modes and topological quantum computation. Npj Quantum Inf. 2015, 1, 15001. [Google Scholar] [CrossRef]
- Field, B.; Simula, T. Introduction to topological quantum computation with non-Abelian anyons. Quantum Sci. Technol. 2018, 3, 045004. [Google Scholar] [CrossRef]
- Gladchenko, S.; Olaya, D.; Dupont-Ferrier, E.; Douçot, B.; Ioffe, L.B.; Gershenson, M.E. Superconducting nanocircuits for topologically protected qubits. Nat. Phys. 2009, 5, 48–53. [Google Scholar] [CrossRef]
- Nigg, D.; Müller, M.; Martinez, E.A.; Schindler, P.; Hennrich, M.; Monz, T.; Martin-Delgado, M.A.; Blatt, R. Quantum computations on a topologically encoded qubit. Science 2014, 345, 302–305. [Google Scholar] [CrossRef]
- Satzinger, K.J.; Liu, Y.J.; Smith, A.; Knapp, C.; Newman, M.; Jones, C.; Chen, Z.; Quintana, C.; Mi, X.; Dunsworth, A.; et al. Realizing topologically ordered states on a quantum processor. Science 2021, 374, 1237–1241. [Google Scholar] [CrossRef]
- Semeghini, G.; Levine, H.; Keesling, A.; Ebadi, S.; Wang, T.T.; Bluvstein, D.; Verresen, R.; Pichler, H.; Kalinowski, M.; Samajdar, R.; et al. Probing topological spin liquids on a programmable quantum simulator. Science 2021, 374, 1242–1247. [Google Scholar] [CrossRef]
- Suter, D.; Álvarez, G.A. Colloquium: Protecting quantum information against environmental noise. Rev. Mod. Phys. 2016, 88, 041001. [Google Scholar] [CrossRef]
- Maniscalco, S.; Francica, F.; Zaffino, R.L.; Lo Gullo, N.; Plastina, F. Protecting Entanglement via the Quantum Zeno Effect. Phys. Rev. Lett. 2008, 100, 090503. [Google Scholar] [CrossRef]
- Xu, J.S.; Sun, K.; Li, C.F.; Xu, X.Y.; Guo, G.C.; Andersson, E.; Lo Franco, R.; Compagno, G. Experimental recovery of quantum correlations in absence of system-environment back-action. Nat. Commun. 2013, 4, 2851. [Google Scholar] [CrossRef]
- Temme, K.; Bravyi, S.; Gambetta, J.M. Error Mitigation for Short-Depth Quantum Circuits. Phys. Rev. Lett. 2017, 119, 180509. [Google Scholar] [CrossRef]
- Kandala, A.; Temme, K.; Córcoles, A.D.; Mezzacapo, A.; Chow, J.M.; Gambetta, J.M. Error mitigation extends the computational reach of a noisy quantum processor. Nature 2019, 567, 491–495. [Google Scholar] [CrossRef]
- Li, Y.; Benjamin, S.C. Efficient Variational Quantum Simulator Incorporating Active Error Minimization. Phys. Rev. X 2017, 7, 021050. [Google Scholar] [CrossRef]
- Endo, S.; Benjamin, S.C.; Li, Y. Practical Quantum Error Mitigation for Near-Future Applications. Phys. Rev. X 2018, 8, 031027. [Google Scholar] [CrossRef]
- Mortezapour, A.; Lo Franco, R. Protecting quantum resources via frequency modulation of qubits in leaky cavities. Sci. Rep. 2018, 8, 14304. [Google Scholar] [CrossRef]
- Marvian, I.; Lidar, D.A. Quantum Error Suppression with Commuting Hamiltonians: Two Local is Too Local. Phys. Rev. Lett. 2014, 113, 260504. [Google Scholar] [CrossRef]
- Marvian, M.; Lidar, D.A. Error suppression for Hamiltonian quantum computing in Markovian environments. Phys. Rev. A 2017, 95, 032302. [Google Scholar] [CrossRef]
- Pokharel, B.; Anand, N.; Fortman, B.; Lidar, D.A. Demonstration of Fidelity Improvement Using Dynamical Decoupling with Superconducting Qubits. Phys. Rev. Lett. 2018, 121, 220502. [Google Scholar] [CrossRef]
- D’Arrigo, A.; Lo Franco, R.; Benenti, G.; Paladino, E.; Falci, G. Recovering entanglement by local operations. Ann. Phys. 2014, 350, 211–224. [Google Scholar] [CrossRef]
- Man, Z.X.; Xia, Y.J.; Lo Franco, R. Cavity-based architecture to preserve quantum coherence and entanglement. Sci. Rep. 2015, 5, 13843. [Google Scholar] [CrossRef] [PubMed]
- Perez-Leija, A.; Guzmán-Silva, D.; León-Montiel, R.d.J.; Gräfe, M.; Heinrich, M.; Moya-Cessa, H.; Busch, K.; Szameit, A. Endurance of quantum coherence due to particle indistinguishability in noisy quantum networks. Npj Quantum Inf. 2018, 4, 45. [Google Scholar] [CrossRef]
- Militello, B. Detuning-induced robustness of a three-state Landau-Zener model against dissipation. Phys. Rev. A 2019, 99, 063412. [Google Scholar] [CrossRef]
- Nosrati, F.; Castellini, A.; Compagno, G.; Lo Franco, R. Dynamics of spatially indistinguishable particles and quantum entanglement protection. Phys. Rev. A 2020, 102, 062429. [Google Scholar] [CrossRef]
- Piccolini, M.; Nosrati, F.; Compagno, G.; Livreri, P.; Morandotti, R.; Lo Franco, R. Entanglement Robustness via Spatial Deformation of Identical Particle Wave Functions. Entropy 2021, 23, 708. [Google Scholar] [CrossRef]
- Laneve, A.; Nosrati, F.; Geraldi, A.; Mahdavipour, K.; Pegoraro, F.; Khazaei Shadfar, M.; Lo Franco, R.; Mataloni, P. Enhancing nonclassical bosonic correlations in a quantum walk network through experimental control of disorder. Phys. Rev. Res. 2021, 3, 033235. [Google Scholar] [CrossRef]
- Xiong, H.N.; Li, L.; Sun, Z.; Yang, Z.; Le, Z.; Huang, Y.; Wang, X. Information preservation of two qubits in a structured environment. New J. Phys. 2022, 24, 123001. [Google Scholar] [CrossRef]
- Aolita, L.; de Melo, F.; Davidovich, L. Open-system dynamics of entanglement:a key issues review. Rep. Prog. Phys. 2015, 78, 042001. [Google Scholar] [CrossRef]
- Zanardi, P.; Rasetti, M. Noiseless Quantum Codes. Phys. Rev. Lett. 1997, 79, 3306–3309. [Google Scholar] [CrossRef]
- Lo Franco, R.; D’Arrigo, A.; Falci, G.; Compagno, G.; Paladino, E. Preserving entanglement and nonlocality in solid-state qubits by dynamical decoupling. Phys. Rev. B 2014, 90, 054304. [Google Scholar] [CrossRef]
- Lidar, D.A. Quantum Information and Computation for Chemistry; Wiley Online Library: Hoboken, NJ, USA, 2014. [Google Scholar] [CrossRef]
- Bellomo, B.; Lo Franco, R.; Compagno, G. Non-Markovian Effects on the Dynamics of Entanglement. Phys. Rev. Lett. 2007, 99, 160502. [Google Scholar] [CrossRef] [PubMed]
- Orieux, A.; D’Arrigo, A.; Ferranti, G.; Franco, R.L.; Benenti, G.; Paladino, E.; Falci, G.; Sciarrino, F.; Mataloni, P. Experimental on-demand recovery of entanglement by local operations within non-Markovian dynamics. Sci. Rep. 2015, 5, 8575. [Google Scholar] [CrossRef]
- Lorenzo, S.; Ciccarello, F.; Palma, G.M. Non-Markovian dynamics from band edge effects and static disorder. Int. J. Quantum Inf. 2017, 15, 1740026. [Google Scholar] [CrossRef]
- Lorenzo, S.; Lombardo, F.; Ciccarello, F.; Palma, G.M. Quantum non-Markovianity induced by Anderson localization. Sci. Rep. 2017, 7, 42729. [Google Scholar] [CrossRef] [PubMed]
- Luchnikov, I.A.; Kiktenko, E.O.; Gavreev, M.A.; Ouerdane, H.; Filippov, S.N.; Fedorov, A.K. Probing non-Markovian quantum dynamics with data-driven analysis: Beyond “black-box” machine-learning models. Phys. Rev. Res. 2022, 4, 043002. [Google Scholar] [CrossRef]
- Wu, L.A.; Zanardi, P.; Lidar, D.A. Holonomic Quantum Computation in Decoherence-Free Subspaces. Phys. Rev. Lett. 2005, 95, 130501. [Google Scholar] [CrossRef]
- Feng, Z.B.; Zhang, C.L.; Zhou, Y.Q. Robust Quantum Computing in Decoherence-Free Subspaces with Double-Dot Spin Qubits. Commun. Theor. Phys. 2014, 61, 181. [Google Scholar] [CrossRef]
- Bose, S. Quantum communication through spin chain dynamics: An introductory overview. Contemp. Phys. 2007, 48, 13–30. [Google Scholar] [CrossRef]
- Bose, S. Quantum Communication through an Unmodulated Spin Chain. Phys. Rev. Lett. 2003, 91, 207901. [Google Scholar] [CrossRef]
- Christandl, M.; Datta, N.; Ekert, A.; Landahl, A.J. Perfect State Transfer in Quantum Spin Networks. Phys. Rev. Lett. 2004, 92, 187902. [Google Scholar] [CrossRef]
- Campos Venuti, L.; Degli Esposti Boschi, C.; Roncaglia, M. Qubit Teleportation and Transfer across Antiferromagnetic Spin Chains. Phys. Rev. Lett. 2007, 99, 060401. [Google Scholar] [CrossRef] [PubMed]
- Godsil, C.; Kirkland, S.; Severini, S.; Smith, J. Number-Theoretic Nature of Communication in Quantum Spin Systems. Phys. Rev. Lett. 2012, 109, 050502. [Google Scholar] [CrossRef] [PubMed]
- Sousa, R.; Omar, Y. Pretty good state transfer of entangled states through quantum spin chains. New J. Phys. 2014, 16, 123003. [Google Scholar] [CrossRef]
- Fel’dman, E.; Pechen, A.; Zenchuk, A. Complete structural restoring of transferred multi-qubit quantum state. Phys. Lett. A 2021, 413, 127605. [Google Scholar] [CrossRef]
- Saffman, M.; Walker, T.G.; Mølmer, K. Quantum information with Rydberg atoms. Rev. Mod. Phys. 2010, 82, 2313–2363. [Google Scholar] [CrossRef]
- Weedbrook, C.; Pirandola, S.; García-Patrón, R.; Cerf, N.J.; Ralph, T.C.; Shapiro, J.H.; Lloyd, S. Gaussian quantum information. Rev. Mod. Phys. 2012, 84, 621–669. [Google Scholar] [CrossRef]
- Diep, D.N.; Nagata, K.; Wong, R. Continuous-Variable Quantum Computing and its Applications to Cryptography. Int. J. Theor. Phys. 2020, 59, 3184–3188. [Google Scholar] [CrossRef]
- Kiktenko, E.O.; Mastiukova, A.S.; Fedorov, A.K. Protecting quantum systems from decoherence with unitary operations. Opt. Eng. 2020, 59, 1–17. [Google Scholar] [CrossRef]
- Plesch, M.; Brukner, Č. Quantum-state preparation with universal gate decompositions. Phys. Rev. A 2011, 83, 032302. [Google Scholar] [CrossRef]
- Zhang, X.M.; Li, T.; Yuan, X. Quantum state preparation with optimal circuit depth: Implementations and applications. arXiv 2022, arXiv:2201.11495. [Google Scholar] [CrossRef]
- Qiskit Aer API Reference. Available online: https://qiskit.org/documentation/apidoc/aer.html (accessed on 26 December 2022).
- Georgopoulos, K.; Emary, C.; Zuliani, P. Modeling and simulating the noisy behavior of near-term quantum computers. Phys. Rev. A 2021, 104, 062432. [Google Scholar] [CrossRef]
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2022 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).