1. Introduction
With the development of Information Technology (IT), the past half-century has witnessed the coming of a new age, namely, the Information Age. Almost everyone’s life has benefited tremendously from the evolution of wireless communication, and many novel techniques have optimized the performance of wireless networks. Among these techniques, cooperative communication is playing increasingly important roles in emerging wireless communication networks. So-called cooperative communication is a concept that enables wireless network users to communicate through one or multiple helper nodes, which are known as relays. With the help of cooperative relays, the system can obtain a better path loss gain, diversity gain, and multiplexing gain. These advantages have led to the increasing involvement of cooperation-based networks in the architecture of emerging mobile systems to an extent that is similar to that of Device-to-Device (D2D) networks [
1] and heterogeneous networks (HetNet) [
2,
3].
Although the evolution of wireless communication techniques has evidently improved their transmission efficiency, there are still many hidden risks that hamper further development. Among those risks, the security problem is a constant and significant issue. Wireless communication is more vulnerable to attacks than wired communication. In a wireless network, a trade-off is sometimes necessary, and transmission resources are reduced to satisfy security requirements. In particular, with the increasing development of many new techniques, such as supercomputers and cloud computing, the traditional cryptography-based security strategy will face unprecedented challenges [
4,
5]. Thus, a brand new direction, such as physical layer security (PHY security), should be considered to secure wireless communication systems. In a physical layer security approach, key sharing is unnecessary, so key management can be avoided. Besides that, PHY security can obtain a good balance between security, efficiency, and complexity to achieve high transmission efficiency as well as information-theoretic security at a limited cost.
With this motivation, we aim to investigate physical layer secure information exchange in a common cooperative communication model, namely, a multiuser relay channel. In addition, massive MIMO has been stipulated to be one of the key techniques for 5G, and multiple antennas have been equipped in mobile devices as well as giant equipment. These factors all reflect the significant value of multiple-antenna techniques, in both theory and practice, for future wireless systems. Thus, we consider the MIMO system in this work.
PHY security in cooperative relaying was first considered in [
6]. In [
7], the security problems in a cooperative relaying system were divided into two parts depending on the relay adversarial model: (1) the untrusted relay model and (2) the trusted relay model.
In the trusted relay model, the relay facilitates a secure transmission for legitimate users. PHY security was studied for one-way relay in [
8]. In [
8], different relaying protocols, namely, Amplify-and-Forward (AF), Decode-and-Forward (DF), Compute-and-Forward (CF), and Noise-and-Forward (NF), were discussed in the context of security. The letter [
9] proposed two cooperative beamforming schemes for the AF model: the secrecy rate maximization scheme and the null-space scheme. MIMO one-way relaying was investigated in [
10] using a scenario in which the attacker has access to the global CSI. Another approach to PHY security in cooperative communication is the use of a supportive jammer. In [
11], artificial noise signals were transmitted by supportive jammers to protect the transmission in a two-hop system. To maximize the secrecy capacity, the authors of [
12] proposed a scheme in which the best channel condition relay is in charge of information relaying, while other relays are in charge of sending jamming signals. The work in [
13] considered a more complex model in which multiple sources transmit signals to multiple destinations with multiple relays through a smart jamming algorithm.
In the untrusted relay model, the relay itself acts as an untrusted node that may attempt to illegitimately recover the information contained in messages from users. This is a common situation in the ad hoc network since many potential unfriendly devices exist in such networks, and some of them are eager to wiretap messages by providing fake assistance. In the context of security, relay selection is an effective way to prevent an active attack on the relays. However, it is difficult for the relay selection method to identify relays that will obey the transmission protocol but are curious about the information they are relaying. Thus, PHY security plays more roles in this type of model. Relay selection schemes in the context of security have been the focus of many studies [
14,
15,
16]. The secrecy capacity was investigated using the untrusted relay model in the pioneer work of [
6]. Following that, the work of [
17] showed that a higher secrecy capacity could be achieved with a CF strategy. A method that combined jamming and relay selection was proposed in [
18] to prevent untrusted relays in a two-hop cooperative network. An interesting scheme was proposed in [
19] in which the receiver acted as a helper by sending jamming signals to the untrusted relay. The work of [
20] extended the research on the signal antenna system to the MIMO system for untrusted relays.
The two-way trusted relay model is another system that has great potential for improving the overall network performance in terms of efficiency as well as security. Usually, a DF protocol is applied at the relay, and with the relay’s decoding, the information forms an integration at the relay (see [
21,
22]). The MIMO technique could provide more PHY redundancy for secure transmission. In [
23], an analog network coding scheme and distributed beamforming scheme were applied to obtain secure transmission and prevent one eavesdropper. Another null-space precoding approach was proposed in [
24], in which the secrecy sum-rates were optimized with different power constraints. The authors in [
25] presented a PHY network coding design with secure precoding for two-way MIMO trusted relay channels.
A number of recent works have focused on secure transmission in a MIMO multiuser relay channel. In [
26], multiple source nodes transmitted private information to multiple destination nodes with the help of multiple relays. The work in [
27] investigated multiuser secure communications with the Base Station using direct links as well as multiple relays. In [
28], secure transmission was obtained by trading off reliability for multiuser Single Input Multiple Output (SIMO) relay channels. Moreover, in [
29], secure downlink broadcasting was obtained with the help of a regenerative relay in a physical layer security approach. All these studies have proposed effective physical layer security protocols for multiuser relay channels; however, they have only focused on enabling one-way information forwarding instead of information exchange. Using a two-way untrusted relay model, the authors in [
30] proposed a beamforming method for secure information exchange. In particular, this paper considered the untrusted relay situation, which is the first for relay channels. Moreover, the concept is of great value because it utilizes the alignment of the transmitting signals to provide users with security. Furthermore, secure information exchange was extended to multi-hop in [
31,
32], in which security was the basis of PHY network coding.
Two types of secure information exchange exist in a multiuser relay channel on account of there being multiple users. On the one hand, users can exchange private information with other specified users. In this direction, several works have focused on signal processing methods for each information exchange pair [
33,
34,
35]. However, none of them have addressed the security problem in a multiuser relay channel. The authors of [
36] were the only ones to propose a physical layer security scheme that was based on interference alignment. On the other hand, users can also exchange public information with all other users. In other words, all users are broadcasting their information and receive information from all other users; thus, this type of exchange is also called group information exchange (see [
37]) or full information exchange (see [
38,
39]).
Another consideration is that cryptography approaches are still the main methods for securing a multiuser relay channel. In private information exchange, each communication pair shares a secret key to encrypt its own information. This situation is identical to typical end-to-end encryption. Since the conditions differ for public information exchange, algorithms have been developed for group situations particularly. The authors in [
40] proposed a broadcast encryption protocol that enables one sender to broadcast its information to all other users. However, this protocol cannot be used for private information exchange. Fast group key agreement is a development for public information exchange and was studied in [
41], but the generated key can only be used for encrypting public information, which can be decrypted by all other users in the group.
The literature review reveals that practical protocols have been proposed for either private information exchange or public information exchange, and none of these approaches enable the simultaneous occurrence of the two types of information exchange. Thus, it is desirable to design a novel protocol that allows for the secure exchange private information as well as public information. With this motivation, we propose a protocol for private and public information exchange using a physical layer security method. The core technique of the protocol is signal alignment, which forms a summed signal for each private information exchange partner and a coding chain for all public information.
The contribution of this work can be summarized as follows:
We propose a novel physical layer secure protocol that enables simultaneous private information exchange and public information exchange. With a designed precoding matrix for each user, the private information of one user is aligned with its exchange partner, and the public information forms a coding chain at the relay. For the relay, the summed signal and coding chain cannot be divided into separated individual information. To an external eavesdropper, each transmitted signal acts as interference for other signals. To the best of our knowledge, this proposed protocol is the first to enable simultaneous private information exchange and public information exchange.
We conducted a performance analysis of the proposed protocol. First, a transmission performance analysis was conducted from the perspective of time slot cost. We compared the time slot cost of the proposed protocol with that of the well-known Time Division Multiple Access (TDMA) protocol and network layer network coding protocol. Second, a security analysis was conducted. We analyzed attacks from different nodes for the both the private exchange and public exchange. Finally, a secrecy sum-rate analysis was conducted under three scenarios: an untrusted relay attack only, an eavesdropper attack only, and both an untrusted relay and eavesdropper attack.
We demonstrate the performance of the proposed protocol with simulated numerical results. First, we show the numerical difference in time slot cost between the proposed protocol and the well-known TDMA and network coding protocols. Second, we show the bit error ratio between the intended receive node and the untrusted relay and the external eavesdropper. Finally, we show the numerical results of the secrecy sum-rates under the three different attacks described in the previous item.
The rest of this paper is organized as follows.
Section 2 introduces the basic transmission model and the security model. With the described system model,
Section 3 proposes a novel physical layer secure protocol that enables simultaneous private and public information exchange for a MIMO multiuser relay channel.
Section 4 describes the performance analysis of the proposed information exchange protocol, and the performance analysis results from multiple simulations are demonstrated in
Section 5. Finally,
Section 6 concludes this work and describes possible future works that build on this paper.
2. System Model
In this section, we introduce the basic system model and some preliminaries for the proposed protocol. The transmission model, the security model, and basic conditions and definitions are introduced sequentially.
2.1. Transmission Model
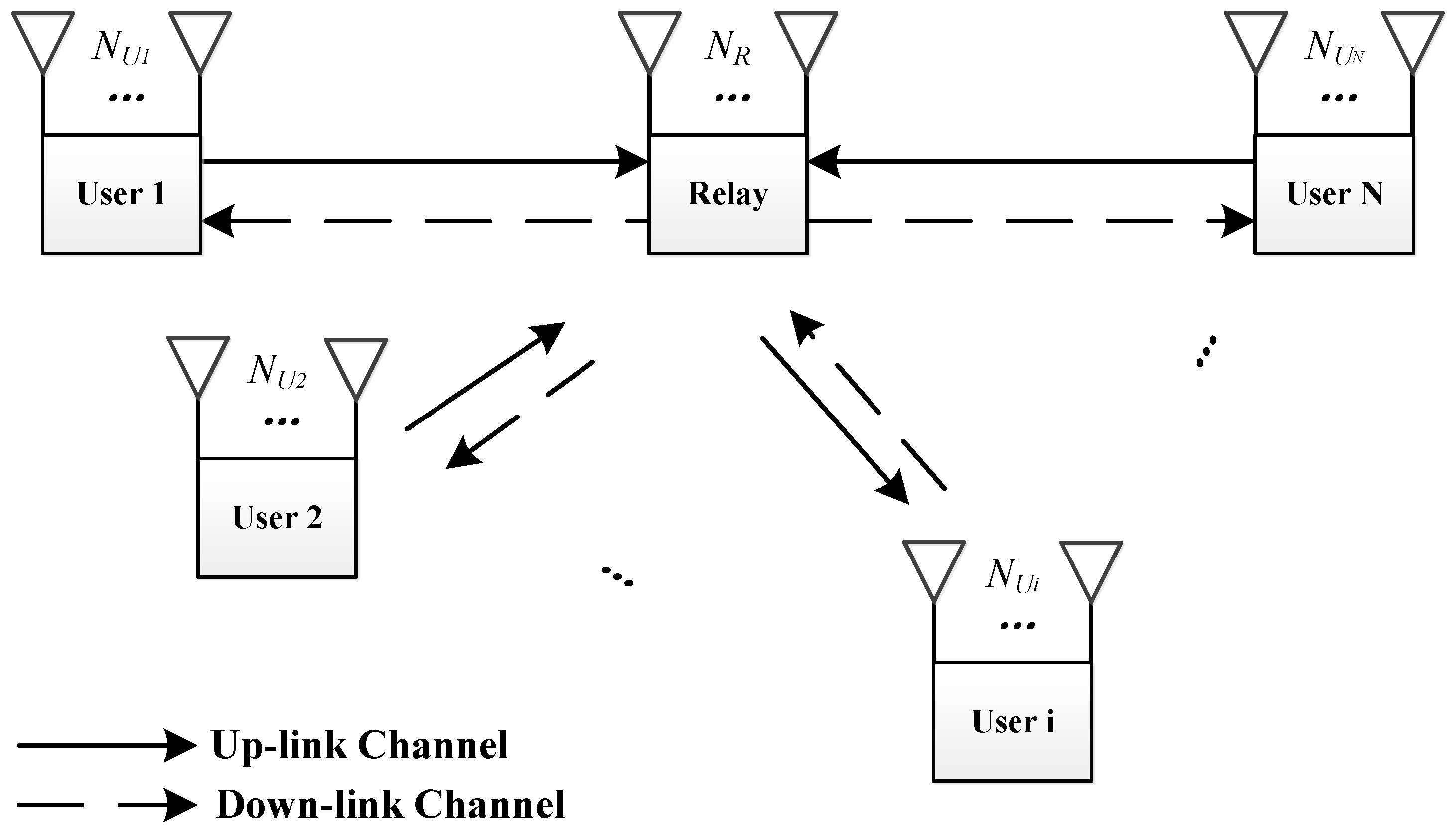
The basic model for the protocol is depicted in
Figure 1. In this model,
N users are willing to exchange information via one relay. In particular, we distinguish between information that is exchanged by a public message and a private message, and, to the best of our knowledge, this is a novel distinction. We discuss the details of these two types of messages in the section that addresses the security model.
The proposed protocol involves two time slots. In the first time slot, all N users send their signals simultaneously to the relay. After a simple operation, the relay broadcasts its signal to all N users. In our protocol, the relay does the physical layer network decoding first and then generates the signal to be broadcast in the second time slot. In other words, the proposed protocol is designed as a Decode-and-Forward (DF) model. Usually, the first time slot is called the uplink phase or multiple-access (MAC) phase, and the second time slot is called the downlink phase or broadcast (BC) phase.
If we consider the MIMO system, then all nodes in the system are equipped with multiple antennas. There are antennas equipped for user i and antennas equipped for the relay. We also assume that all the nodes work according to the half-duplex model.
We now move on to the formulation of this transmission model. In the MAC phase, each user applies physical layer network coding to its message. We use
to denote the message to be transmitted for user
i, and
denotes the coded message. Then, we have
, in which
denotes physical layer network coding. With the coded message, each user applies a precoding matrix
to form the transmitted signal
as
In addition, the power constraint for the uplink phase is
where
is the total transmission power of all users, and
is the input covariances for user
i.
is represented by
, where
is the expectation operator. Furthermore, the codewords are all independent, so
. Then,
is
. Each user’s transmitted signal must satisfy this constraint, which is adopted especially for power allocation. The allocated power directly affects the signal-to-noise ratio at the receiver, and it correspondingly affects the secrecy sum-rates. Thus, the optimization of power allocation is significant for the optimization of secrecy sum-rates.
After the transmission of the uplink phase channel, the relay obtains the receiving signal as
where
is the uplink channel state matrix. We assume that all channels are flat fading, so
remains constant during the scheme with the entry of symmetric complex Gaussian random variables with a zero mean and unit variance.
is the noise vector at the relay and modeled by
. The estimation of
will be discussed in the end of this subsection.
With the receipt of
, the relay decodes and broadcasts the converged messages to all users, and the signal to be broadcast in the downlink phase is denoted by
. Similar to the uplink phase channels, the downlink phase channels are also assumed to be flat fading channels, and the channel matrix between the relay and user
i is denoted by
. Thus, the received signal for user
i in the downlink phase
can be written as
where
is the noise vector at user
i and modeled by
.
With the received broadcast signal from the relay, each user recovers the message transmitted to it with the help of its own message. The decoding at the user is detailed in a later section.
We will have a very brief discussion on the channel estimation for our proposed protocol. The introduced estimation algorithm is designed with the least overhead and computation cost, so the accuracy of this estimation is limited. Just like the other trade-off problem, we must choose either accuracy or low cost. More complicated channel estimation may be found in [
42,
43,
44,
45]; however, these approaches must be modified before they directly use in the multiuser relay channel.
It is also takes two time slots for the channel estimation for multiuser relay channel. In the first time slot, all of the user nodes send their training vector to the relay. The training vectors are from a orthonormal set, so and .
By transmitting the training vector, the relay obtains the received signal as:
In the second time slot, the relay broadcasts the received signal to all the users. Then, for user
j, we have:
Right multiplying
, and recalling
and
, we have:
where
, is the equivalent noise vector at the user
j. In addition, we assume the up-link channels and down-link channels are reciprocal channels, then we have
. Thus, with (7), we can use maximum likelihood to decode and compute
.
2.2. Security Model
We propose a protocol that enables coinstantaneous private information exchange and public information exchange. These two types of information exchange face different potential security hazards.
Private Information Exchange
In the private information exchange, two of the multiple users exchange private information with the help of the relay. In this case, the attack can originate from three terminals: external eavesdroppers, untrusted relays, and other users.
External Eavesdroppers: Because of the broadcast nature of wireless communication, eavesdroppers exist in the network. External eavesdroppers try to recover private information from users by wiretapping the uplink phase channels as well as the downlink phase channels. In the uplink phase, we denote an eavesdropper that attacks user
j by
. We assume that multiple eavesdroppers cannot collude. This assumption is significant and reasonable given that the transmitted signals from the users are independent. Therefore, all the eavesdroppers are also independent of each other. Moreover, if one eavesdropper can wiretap two users at the same time, this eavesdropper can be viewed as two separate eavesdroppers. The received signal at the eavesdropper contains two parts: the desired signal from the user that the eavesdropper is attacking and the equivalent noise signal from other users. The channel matrix between user
i and eavesdropper
j is
. Therefore, the received signal at eavesdropper
j is
where
is the noise modeled by
.
Eavesdroppers can also wiretap the relay in the downlink phase; however, they cannot obtain more information because of the data processing inequality. Thus, we only consider uplink phase eavesdroppers in this work [
46].
Untrusted Relay: In a pessimistic assumption, the relay itself may launch attacks on the information to be exchanged. With an untrusted relay, the relay itself first obeys the transmission protocol to accomplish the information exchange. However, the relay may also be curious about the transmitted message from the users. This type of relay is also known as an honest-but-curious relay. The relay has some obvious advantages in launching an attack in this scenario. First, the relay participates in the transmission and is an authenticated node. Thus, the authentication-based strategy does not stop this attack. Second, the relay is the receiver in the first phase of the scheme and the transmitter in the second phase, so the classical wiretap channel model is not suitable in such a situation. Finally, the relay has the authority to establish direct contact with messages from users according to the protocol.
Untrusted Users: In private information exchange, some users may also be curious about the private information transmitted by other users. Thus, an attack by untrusted users is considered in the private information exchange in addition to the above two types of typical attacks. In this situation, every user could be serving two roles: one is as an exchanger of private information, and the other is as an attacker to obtain other users’ private information. With the assumption that all nodes work according to the half-duplex model, users can only launch an attack after receiving the broadcast signal in the downlink phase, after which they try to recover other users’ private information.
Public Information Exchange: In public information exchange, a group information exchange is formed for all users. With this consideration, attacks can only originate from external eavesdroppers and untrusted relays. These two attacks are similar to those for private information, but, in this case, the attacks are curious about the group information rather than private information. Thus, we do not go detail about the attack model for public information exchange.
External Eavesdroppers: Public information eavesdroppers try to recover public information from users by wiretapping the uplink phase channels as well as the downlink phase channels. The assumption for such eavesdroppers is identical to that for eavesdroppers in private information exchange. In fact, the received signal at the eavesdropper contains both private information and public information. Thus, we do not distinguish between the private information eavesdropper and the public information eavesdropper.
Untrusted Relay: We also consider an untrusted relay in public information exchange to be an honest-but-curious relay. Thus, the relay tries to recover public information from the coding chain formed after the uplink transmission.
3. Proposed Protocol
In this section, a novel physical layer secure protocol that enables simultaneous private and public information exchange for a MIMO multiuser relay channel is proposed. As the core design principle, the signal alignment technique and physical layer network coding are conducted at each user node.
3.1. Negotiation Phase
Before the real transmission process, each node negotiates with the relay to confirm the transmission status and obtain the subchannel order number allocated to the user to exchange its private message and public message.
The negotiation phase contains three steps:
Step 1: the users who wish to exchange information send a request to the relay. For each user, the request also contains the number of the private information exchange partner. For example, if user 2 is willing to exchange information with users 3 and 5, then user 2 will send number 3 and 5 inside the request.
Step 2: The relay collects the request from the users and computes the sorting of private information partners. Before sorting, the relay first matches the information partners. Notably, only the two users that send the request to the relay are allowed to exchange the private information. Users that fail to find a partner are fed back an invalid private information exchange sign with the partner number. The sorting rule is that a user with a small user number is sorted first. For two pairs of partners, the user numbers are first compared, and the smaller one is placed at the front of the sorting table. If the two pairs of partners have the same small user number (i.e., one user exchanging information with two different users), then we compare the other user’s number. After the sorting of all valid partners, a sorting table is formed.
Step 3: After sorting private information exchange partners, the relay feeds back information to the users. The information includes two parts: the sorting result for the private information partners and the information about the private data stream number. User i exchanges private messages, and the total number of private information partners is denoted by . Clearly, we have . We introduce how this information is used in detail in the section that describes the designing of the precoding matrix.
3.2. Uplink Phase
Similar to the description in the previous section, the message vector to be exchanged for user
i is
. Each user applies physical layer network coding before transmission. In this work, we consider the simplest physical layer network coding, namely, Binary Phase Shift Keying (BPSK) coding. The encoding progress for user
i can be written as
It is worth noting that this denotation does not distinguish between private information and public information. To distinguish these two types of information, we denote the message containing private information by
and the message containing public information by
. Accordingly, the coded vectors are
and
.
With the coded message, each user applies a precoding matrix to form the transmitting signal. The precoding matrix accomplishes three main functions: (1) it reduces the transmission interference, (2) aligns the private information of one exchange partner at the relay, and (3) forms a public information chain at the relay.
The three functions are carried out by designing the precoding matrix for user
i as
The precoding matrix contains four parts. The first part is the first three matrices that come from the Singular Value Decomposition (SVD) of the uplink channel matrix to reduce channel interference in the uplink channel. The second part is called rotation matrix to improve the power loss of naive zero-forcing. The third part is called channel allocation matrix , which allocates subchannels to intended users. The last part is the power allocation matrix, which allocates power to each subchannel.
With SVD, the uplink channel matrix
can be rewritten as
where
and
are orthogonal matrices defined by
,
and the rows and columns of these two matrices are orthonormal.
is a diagonal matrix that collects singular values of
, arranged in descending order.
With the first three matrices,
can be written as
It is known that the power loss is very serious with the zero-forcing approach; in particular, the channel matrix is ill-conditioned. Thus, it is desired to improve the naive zero-forcing approach to generate the subchannels. We review some literature which also concentrates on avoiding the power loss suffered with naive zero-forcing, especially the work in [
47] is designed for MIMO relay channel. However, the work in that paper is designed for only two users, so we must modify the precoder there to satisfy the multiusers relay channel.
With zero-forcing for the physical layer network coding in MIMO relay channel, each user conducts channel inversion. Orthogonal subchannels are generated with zero-forcing precoder. To improve the power loss suffered by the naive zero-forcing, the work in [
47] introduces a rotation by multiplying an orthogonal matrix for the eigendirections of the aligned subchannels. Because the rotation matrix is orthogonal, the orthogonality of the subchannels is preserved; however, the power loss is avoided. The detailed theoretical analysis for the benefit of such rotation can refer to [
47].
Before designing the rotation matrix
, we first define a transition matrix
as:
We take eigendecomposition to the transition matrix
as:
where
is an orthogonal matrix and
is a diagonal matrix containing the eigenvalues of
.
With Equation (14), we choose the rotation matrix as:
Finally, we have some complement explanation that the computational of rotation matrix is done by the relay, for only the relay is aware of all the channel states to compute the rotation matrix, and the relay is able to broadcast this matrix with least communication overhead.
The matrix is called the subchannel allocation matrix for user i. With this matrix, the user aligns its private information with its exchange partner(s) at the relay to form a superposition message. Simultaneously, the user aligns its public information with its two neighboring users to form a coding chain at the relay.
The design of the subchannel allocation matrix is relevant to the feedback from the relay in the negotiation phase. We take user
i as an example. The design of the subchannel allocation matrix contains two parts: one is the design for private information
, and the other is the design for public information
. With the sorting table, user
i computes the subchannel numerical order for the private information. Note that only the subchannels for user
1 are defined successively because of the sorting rule in the negotiation phase. We assume that user
i exchanges private information with user
u and user
v. Pair (
i,u) is the
mth pair in the sorting table, and pair (
i,v) is the
nth pair. Then,
for user
i is designed as
has a size of
. In fact, the design
chooses the
mth and
nth columns of an
identity matrix. With such a design, the message to be exchanged with
u is allocated to the
mth subchannel; similarly, the message to be exchanged with
v is allocated to the
nth subchannel.
The design principle for
is to allocate two successive subchannels to one user to form a coding chain. The subchannels for the public information exchange follow the subchannel of the previous private information exchange pair. The number of total private information pairs is
, which is broadcast to the users in the negotiation phase. Thus, user
1 first aligns its message with user
2 in the
th subchannel. Then, user
2 aligns its message with user
3 in the
th subchannel. Similarly, each user from user
3 to user
N − 1 aligns its message with the previous and subsequent user. User
N − 1 aligns its message with user
N in the
th subchannel, but user
N does not have a subsequent user. User
N aligns its message with the first user in the
th subchannel. Thus, user
1 is also allocated the
th subchannel. We show the mathematical expression of
for
in Equation (17):
For user
1,
is designed as
With
and
designed, user
i computes the channel allocation matrix as
The last part of the design of the precoding matrix is the power allocation matrix . For user i, the power allocation vector allocates power to each subchannel created by the former matrices. The allocated power can linearly amplify the coded message to successfully reach the receiver (i.e., the relay). If more power is allocated to one subchannel, the transmitted signal enjoys a better chance of resisting error. However, the total power must usually satisfy the power constraint in Equation (2). Thus, designing the power allocation matrix is also a significant problem.
Usually, we use secrecy sum-rates as performance metrics for power allocation. The optimization of power allocation is significant for secrecy sum-rates, but the optimization problem under such a constraint is non-convex. One possible solution to this problem contains two steps. In the first step, each user applies a water-filling algorithm to its own subchannels, and, in the second step, the system finds the optimal solution to the secrecy sum-rates of the whole system. We mainly focus on proposing a practical protocol in this paper, so we do not go into detail about the optimization of power allocation. Furthermore, we only consider unitary power allocation in this paper, so all the elements in the power allocation matrix are the same. Thus, we take it as one in the rest of this paper for a better analysis. The optimization problem will be a significant part of future work that builds on this paper.
3.3. Relay Operation
After the precoding, all the users transmit their signals to the relay. With the precoding design in (10), the received signal at the relay can be rewritten as
Due to the fact that
is an orthogonal matrix, we can obtain the equivalent received signal by left multiplying
. In addition, the subchannel allocation matrices are designed to align a user’s private information with its private information exchange partner and users’ public information with their two neighboring users. Then, the received signal at the relay can be rewritten as
From (21), we can clearly see that the received signal at the relay now is a summed signal plus the noise vector. In the next step, the relay removes the noise vector and decodes the summed signal back to the binary field. Recall that we assume that the noise vector is
and that the decoding rule is the threshold of the summed signal, so the decoded elements of the summed signal at the relay are
Note that
contains all private information as well as public information from all users. In addition, in view of the binary field, each bit of the decoded signal is a modulo-2 sum of two messages, that is,
or
.
The relay applies BPSK encoding for
as
Then, the transmitting signal is generated for the downlink phase as , where is the power allocation vector for the downlink phase channels. Similar to the case for the uplink phase, we only consider unitary power allocation in this work.
3.4. Downlink Phase
The relay broadcast in the downlink phase is presented here. We take user i as an example. The main function of the downlink phase is that all the users correctly recover and obtain the private and public information.
In contrast to the uplink phase, in which channel interference is reduced by the precoding, in the downlink phase, each user applies a detective matrix
to carry out this function. Additionally, the detective matrix divides the messages transmitting to user
i. For the received signal described in (4), we have
. By designing
and recalling that we have the reciprocal channel assumption defined by
, we have
It is worth noting that
contains all the aligned private information as well as the public coding chain. User
i obtains the aligned private information by left multiplying
as
where
.
For (25), user
i conducts decoding to recover the message from its private information exchange partner with the help of its own exchanged private messages. The decoding rule is
Thus,
is the recovered exchanged private message from user
i’s
jth exchange partner.
For the public exchange information, user
i obtains the coding chain and recovers all the other users’ public messages with the help of its own public message
. Recall that the design places the public information coding chain in the
th to
th subchannels. Thus, we left multiply the matrix
as
With
, we extract the coding chain as
where
.
With
, user
i recovers the public message from all other users with successive decoding. First, user
i decodes the messages from its two neighbors. Taking user
i − 1 as an example, we have
We can similarly recover
.
With recovered and , user i successively recovers and , followed by and until and . Thus, one round of information exchange is finished.
3.5. Example for
We use an example to show how the precoding matrix provides the expected result. We set the user number to 3, and we assume that each user exchanges one private message and one public message with the other two users.
From Equation (10), we can see that the first three matrices are designed to reduce interference from the channel, and the power allocation matrix is a unitary matrix with unitary power allocation. Then, we can only focus on the design of
. According to the design principle,
for user
1 is
With (30), the first, second, fourth, and last subchannels are allocated to user
1. These four subchannels are used to transmit user
1’s coded messages, and the detailed arrangement is that the first subchannel is used for aligning the private coded message
with user
2, the second subchannel is used for aligning the private coded message
with user
3, and the fourth and last subchannels are used for the public coded message
. Thus, the code vector of user
1 is
User
2 aligns
with user
1 in the first subchannel, aligns
with user
3 in the third subchannel, and aligns its public coded message
in the fourth and fifth subchannels. Thus,
Similarly, the design of
is
We now discuss the received signal at the relay. Recalling Equation (20) and
, we have
We can see that all the coded messages are all aligned in the desired subchannels. Thus, the uplink precoding matrix design can provide the expected result.
The relay broadcasts these aligned coded messages to the three users. After left multiplying the detective matrix for each user, the aligned coded messages can be obtained by the three users. According to Equations (25) and (28), each user extracts private aligned messages and the public coding chain. With user
1 as an example, the recovered private aligned messages are
With (35), user
1 conducts decoding and removes its own message following the rule in (26). Then, user
1 recovers the private messages
and
from users
2 and
3.
Similarly, the recovered public coding chain is
With (36), user
1 recovers the public messages from the two other users following the decoding rule in (26). The process is identical for users
2 and
3.
5. Numerical Results
In this section, we show the numerical results for the time slot cost and the secrecy sum-rate analysis of the proposed protocol. The simulation environment was set up with the following conditions. (1) The user number is 4. Each user node is equipped with four antennas, the relay is equipped with eight antennas, and each eavesdropper is equipped with four antennas. (2) BPSK physical layer network coding is applied as the design. (3) With the assumption of a flat fading channel, the coefficients of channel matrices are drawn from . (4) The results were obtained with 10,000 realizations by randomly generating 10,000 channels for each simulation.
5.1. The Simulation of Time Slot Cost
For the time slot cost, we compared the proposed protocol with the TDMA protocol and network layer network coding.
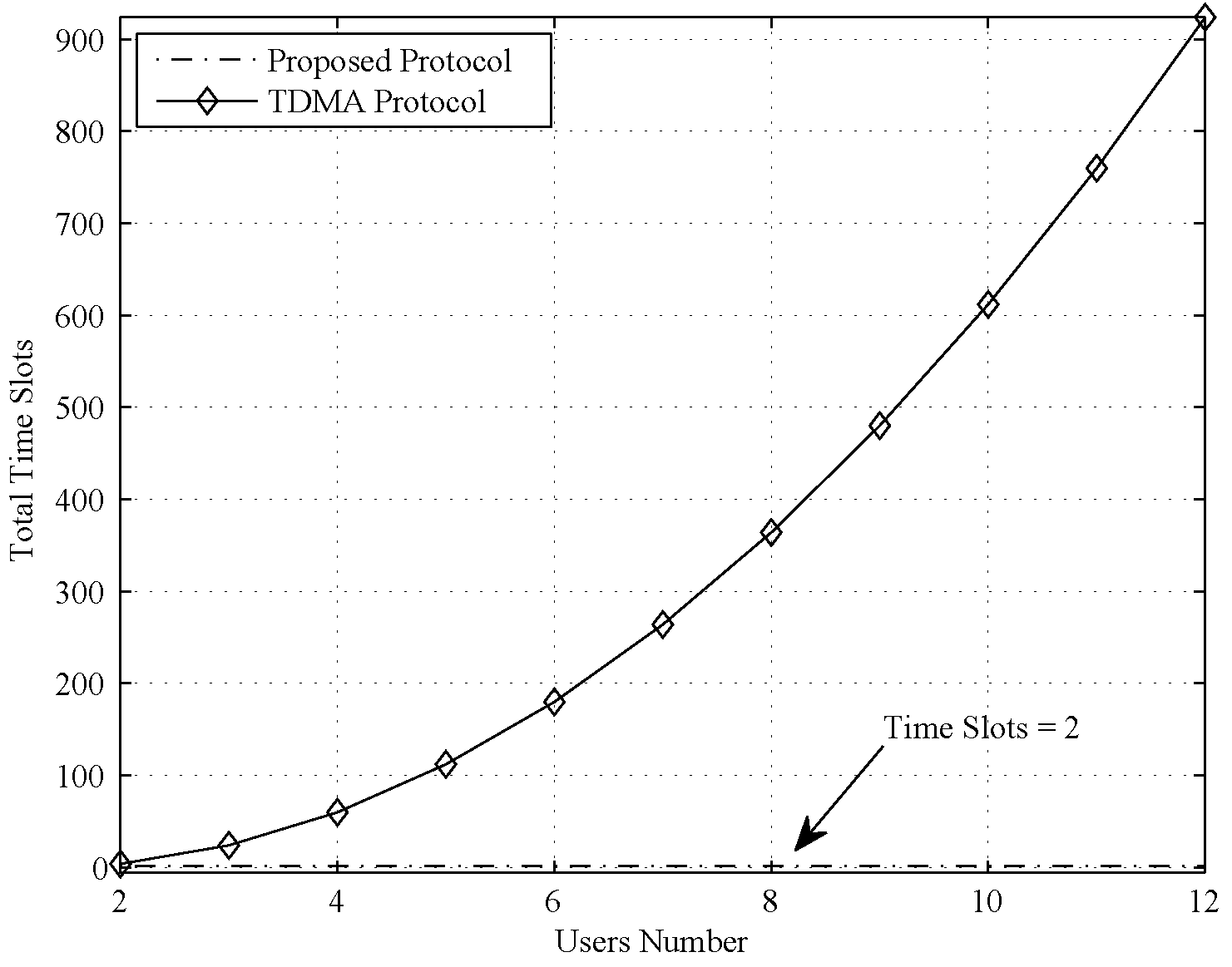
First, we compared the time slot cost of the proposed protocol with that of the naive TDMA protocol, and the comparison result is shown in
Figure 2. As clearly seen in
Figure 2, the time slot cost is larger than 100 when the user number is larger than 5. Moreover, for naive TMDA, users cannot exchange private information because the transmitted signal cannot find an equivalent noise signal in each time slot. The comparison result of the proposed protocol and network layer network coding is shown in
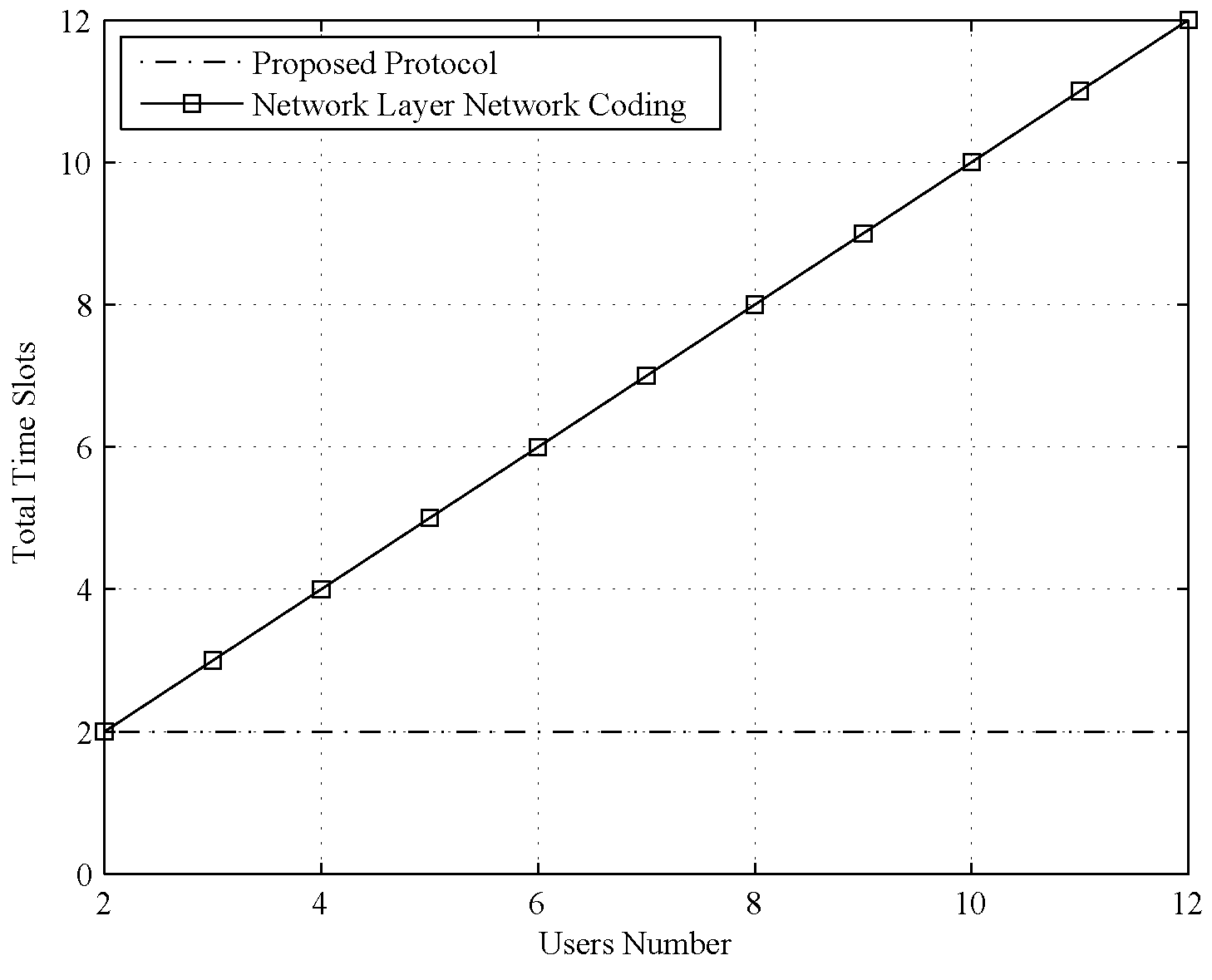
Figure 3.
Second, we compared the time slot cost of the proposed protocol with that of the network layer network coding protocol, and the result is shown in
Figure 3. The comparison result reveals that the time slot cost of the network coding protocol grows linearly with an increasing number of users. Although the cost of network coding is lower than that of the naive TDMA protocol, it is still several times larger than that of the proposed protocol. This benefit is pronounced when the user number is large.
5.2. The Simulation of the Bit Error Ratio
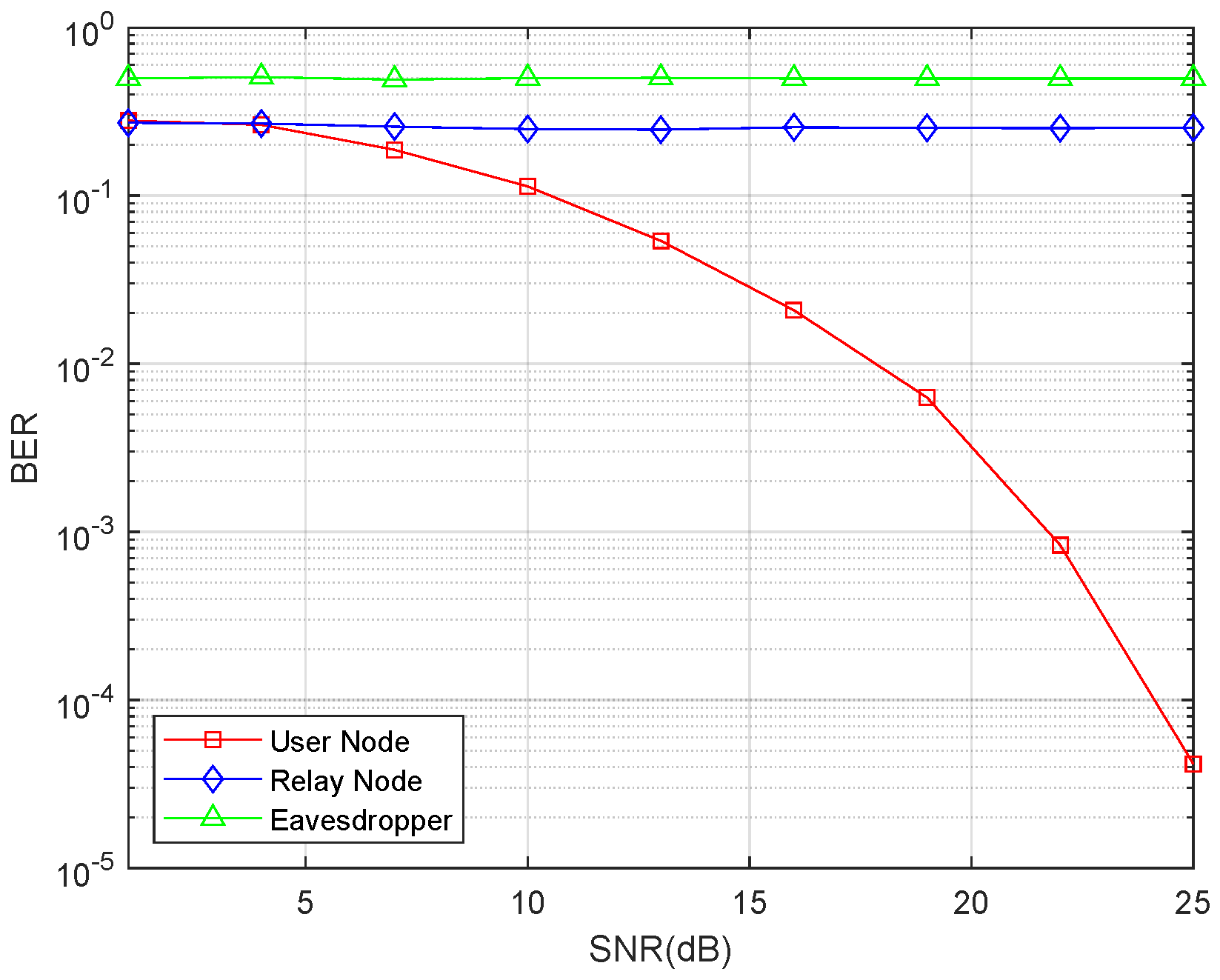
In the next simulation, we compared the bit error ratio (BER). We choose three types of nodes to compare, user node, relay node, and eavesdropper node. In the simulation, for all three of these types of nodes, we set the noise as 1 and adopt the transmission power to achieve the fixed SNR value and then obtain the BER.
Separately saying, for the user node, all the users only receive signal in the second phase. In each round, we randomly choose one user from the total N user nodes to compute the BER. For the SNR, according to the aforementioned, we set the noise at each antenna as 1, then the noise vector is an all 1 vector. In addition, we compute back the signal power for the relay and allocate the power to the relay. Such situation is all the same for the users including the chosen one. With each SNR, we obtain the error number and record it. After 10,000 rounds, we take the average BER as the final result for user node.
For the relay node, it only receives the signal in the first phase of the protocol. Because we have assumed that we only consider unitary power allocation in this work, we allocate the same power for each user. In addition, the allocated power will increase with the increasing of SNR. The BER of relay node is also obtained by 10,000 rounds.
For the eavesdropper node, it tries to recover the transmitted data in both phases. The first phase is similar to the situation of the relay node, and the second phase is similar to the situation of the user node. The result of the BER comparison is shown in
Figure 4.
Figure 4 illustrates that the BER markedly decreases as the Signal-to-Noise Ratio (SNR) increases. However, the BERs of the untrusted relay and eavesdropper remain high irrespective of changes in SNR. This result reveals that the information exchange would be successful with the proposed protocol, and the untrusted relay and external eavesdropper cannot recover the information.
5.3. The Simulation of Secrecy Sum-Rates
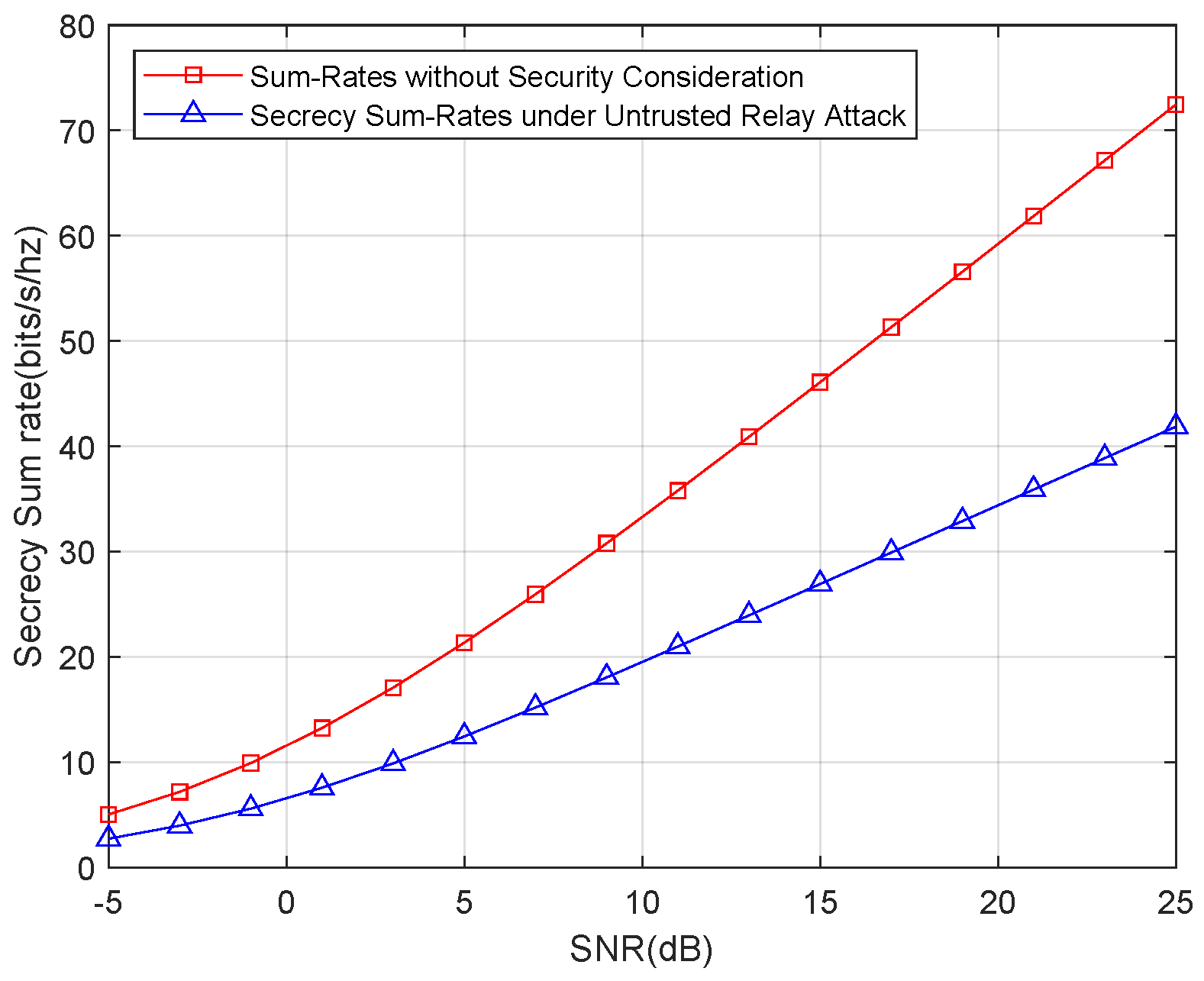
First, we show the secrecy sum-rates for only an untrusted relay attack. The result of the simulation is shown in
Figure 5. For a better illustration, we also show the sum rates without the security consideration.
Figure 5 shows that the secrecy sum-rates suffer a remarkable decline compared with the sum rates without the security consideration. This result highlights the trade-off between security and transmission efficiency; in other words, transmission rates are sacrificed to increase the security level.
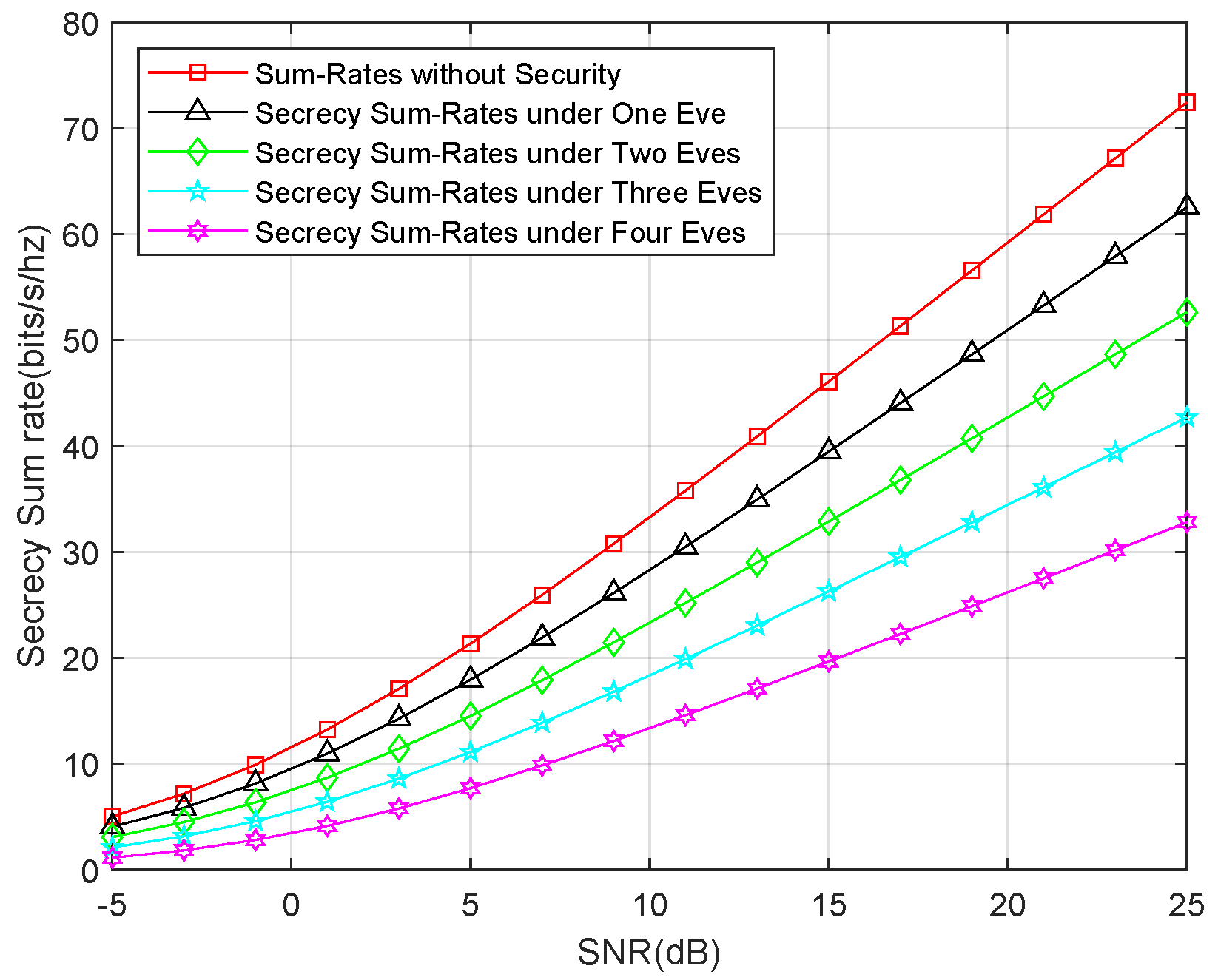
Second, we show the secrecy sum-rates for an external eavesdropper attack. We compared the sum rates for one eavesdropper, two eavesdroppers, three eavesdroppers, and four eavesdroppers, as well as the sum rates without the security consideration. The result is depicted in
Figure 6, which shows that the secrecy sum-rates linearly decrease as the number of eavesdroppers increase. Interestingly, the secrecy sum-rates for only the untrusted relay attack are approximately equal to the secrecy sum-rates for three eavesdroppers. This demonstrates that the untrusted relay can launch a stronger attack than an individual eavesdropper. This result is in accordance with the theoretical analysis.
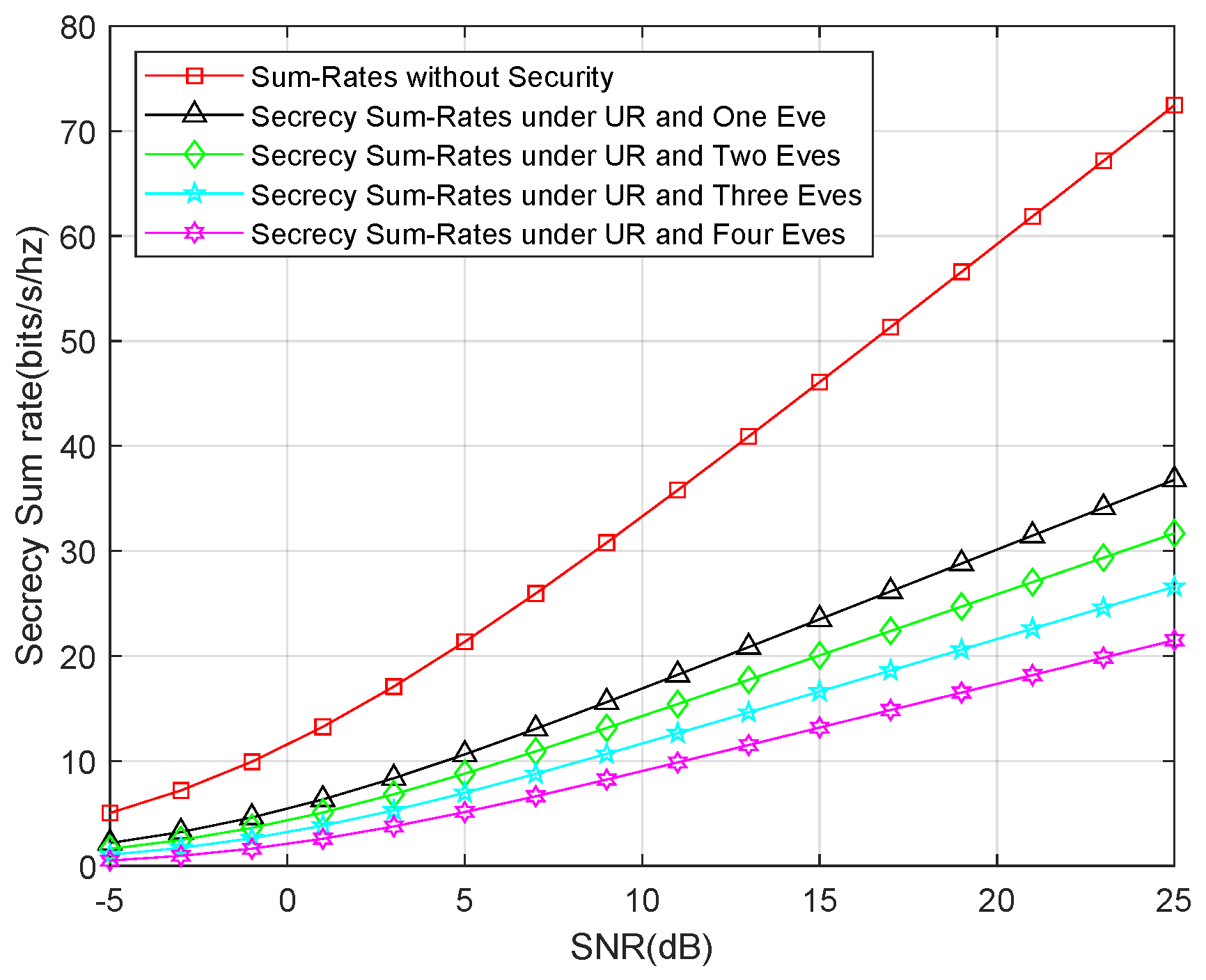
Finally, we show the secrecy sum-rates for both an untrusted relay and external eavesdropper attack. Similar to the last simulation, we also compared the sum rates for one eavesdropper, two eavesdroppers, three eavesdroppers, and four eavesdroppers, as well as the sum rates without the security consideration. The result is shown in
Figure 7, which shows that the secrecy sum-rates decline to one-third of the sum rates without the security consideration. This means that the security consideration is more important for this type of attack.
5.4. Comparisons with Well-Known Protocols
We compared our proposed protocol with some of the other four approaches in multiusers relay channel, i.e., cryptography approach, TMDA approach, network layer coding approach, and a physical layer network coding approach. The result has been shown in
Table 1.
For the attackers, the proposed protocol can resist the attacks from both the eavesdroppers and untrusted relay. The cryptography approach can resist both attacks with the encryption. In addition, the physical layer network coding can resist both attacks by signal alignment similar to the proposed protocol. The network layer coding can only resist the downlink eavesdropper because the summed signal is formed only in that phase. The TMDA approach is only designed for plain data exchange, and no security issues are considered in such approach.
Recalling the motivation of this work, we want to design the first protocol that can simultaneously exchange private data and public data. For the cryptography approach, there are existing group encryption algorithms for either private or public exchange. However, none of the algorithms are able to exchange simultaneously. Both the network layer coding and physical layer coding can exchange public data; however, neither of them can exchange private data.
The overhead is also important for the communication protocol. Because the cryptography approach needs all nodes to conduct encryption and decryption, the computation overhead for such approach is very high. For the other four approaches, each node only does some linear computation or simple encoding and decoding, so the computation is low. For the communication overhead, the time slot cost is the best indicator. With the simulation result in
Figure 2 and
Figure 3, we can clearly see that the communication overhead of TDMA and cryptography approach (equal to TDMA) is high; in particular, the user number is large. The communication overhead of network layer coding is a little higher than the proposed protocol or physical layer network coding, but it is still acceptable.
With the comparisons, we can clearly see that our proposed protocol is the first and only protocol enabling the simultaneous information exchange for both private exchange and public exchange, which satisfies the motivations of the paper. However, there are two drawbacks for the proposed protocol. The first one is that the cryptography approach, TDMA approach, and network layer coding have been introduced into communication for many years. Thus, it will take more money to deploy our protocol. The second drawback is that our protocol is designed particularly for MIMO communication. Thus, for the SISO, SIMO, or MISO situations, only a cryptography approach can be used for either private information or public information. However, the good news is that more and more devices, even the delicate mobile phones, are equipped with multiple antennas.