Improving the Authentication Scheme and Access Control Protocol for VANETs
Abstract
:1. Introduction
2. Cryptanalysis of A PAACP
3. Improved Scheme
3.1. The Registration Phase
- Vi → St : VIDi,A Vi, who submits his/her identity VIDi and his/her to the St for registration.
- St → Vi : h(), eiThe St also creates and as Yeh et al. proposed. The St then computes Vi’s secret information yi = h(VIDi, x) and and writes h() and ei into the smart card of on-board units (OBUs) and issues the card to Vi.
- St → Rj : yi,The St also performs a multicast to send messages yi and to their road side units (RSUs) Rj.
3.2. The Authentication Phase
- Vi → St : VIDi, C, NiWhen Vi wishes to access services provided by St, Vi generates a nonce Ni, where Ni is a random and fresh number. Then, Vi computes and sends an authentication request message (VIDi, C, Ni) to the St.
- St → Vi : MAfter receiving the authentication request message (VIDi,C, Ni), the St and Vi execute the following steps to facilitate a mutual authentication between the vehicle and the service provider. The St performs the following operations:
- –
- Verifies that VIDi is a valid vehicle identity. If not, the authentication request is rejected.
- –
- Computes and verifies whether . If the verification fails, the request is rejected.
- –
- Checks whether it received . If not, the request is rejected; otherwise, the request proceeds to the next step.
- –
- Generates a nonce Ns, where Ns is a random and fresh number.
- –
- Encrypts the message and sends it back.
- –
- After Vi receives the message M, Vi will decrypt the message to derive and verify whether . If the answer is yes, the mutual authentication is done. The portable authorized credential is , and we propose that is not equal to . Either St may reduce access privileges for some reason (for example, not paying before the deadline or breaking a contract) or Vi may disable access privileges himself/herself for some reason (for example, privacy issue or lower communication costs). Therefore, ACi is and performs an exclusive operation with that is reasonable and makes sense.
3.3. The Access Phase
- Vi → Rj : WiVi computes and sends Wi to Rj, where is a random number.
- Rj → Vi : SiSimilarly, Rj computes and sends Si to Vi, where is a random number. Vi computes , and Rj computes . Then, both of them check whether KV =KR. If yes, a new session will be created. This is because:
- Vi → Rj : (Service request message)If Vi wants to access service, it encrypts with KV as the service request message and sends it to Rj. After Rj receives the message, Rj will decrypt the message:with KR to gain (SVID1 || ACi) and then derive ACi and SVID1, because of KV = KR. When Rj derives ACi, Rj verifies it and is then convinced that Vi is a legal user.
- Vi → Rj : (Service request message)nthWhen Vi continues to access the n-th service, it encrypts the n-th service request message with KV + n and sends it to Rj. After Rj receives the n-th service request message, Rj will decrypt the message:with KR + n to derive ACi and SVIDn. Rj examines whether SIDt, as well as SVIDn are included in and checks the validity of the authorized credential by Texpired. If the verification succeeds, ACi is legitimate and Vi is authorized; otherwise, Rj terminates this session.
4. Analysis of the New Scheme
4.1. Comparison
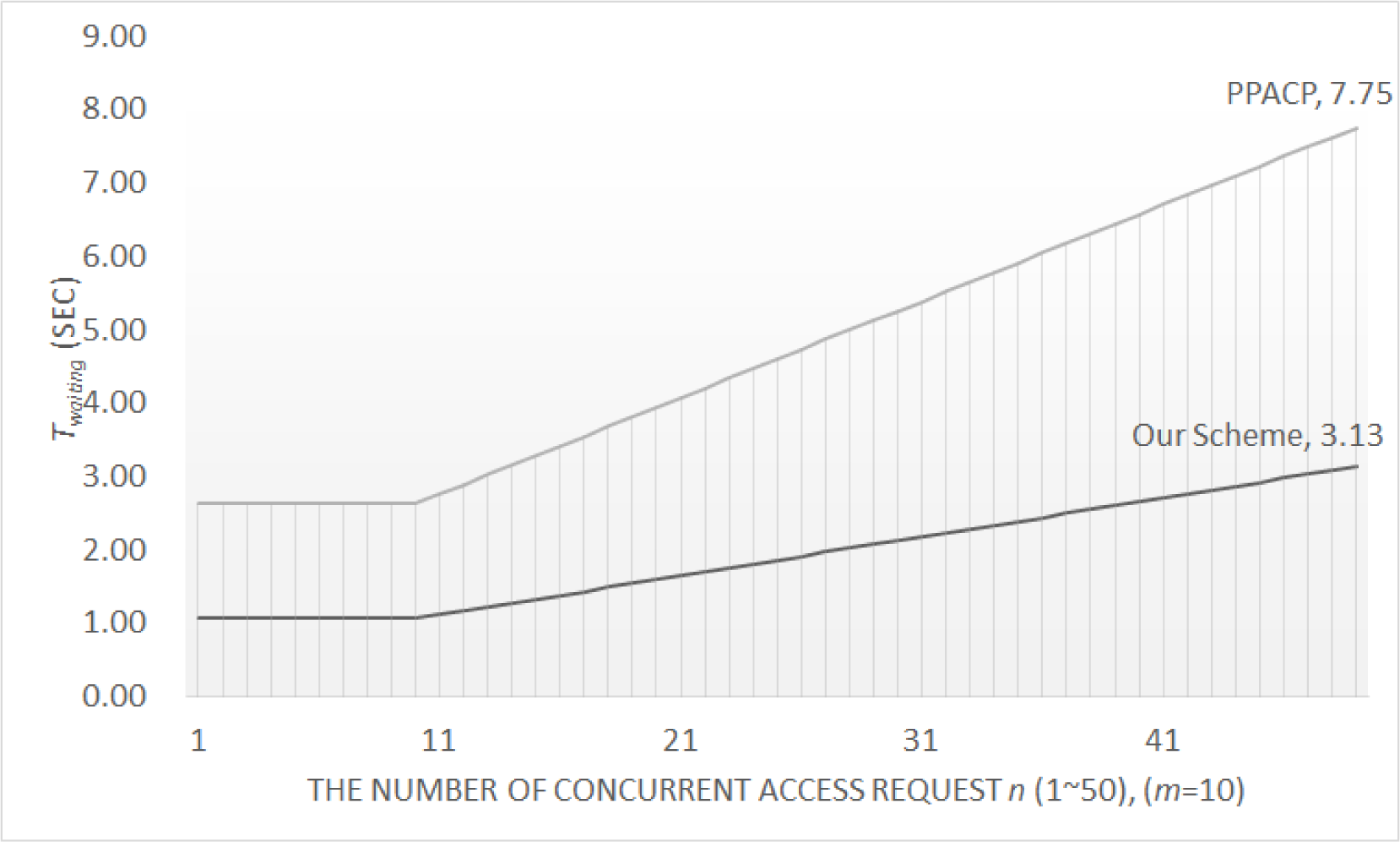
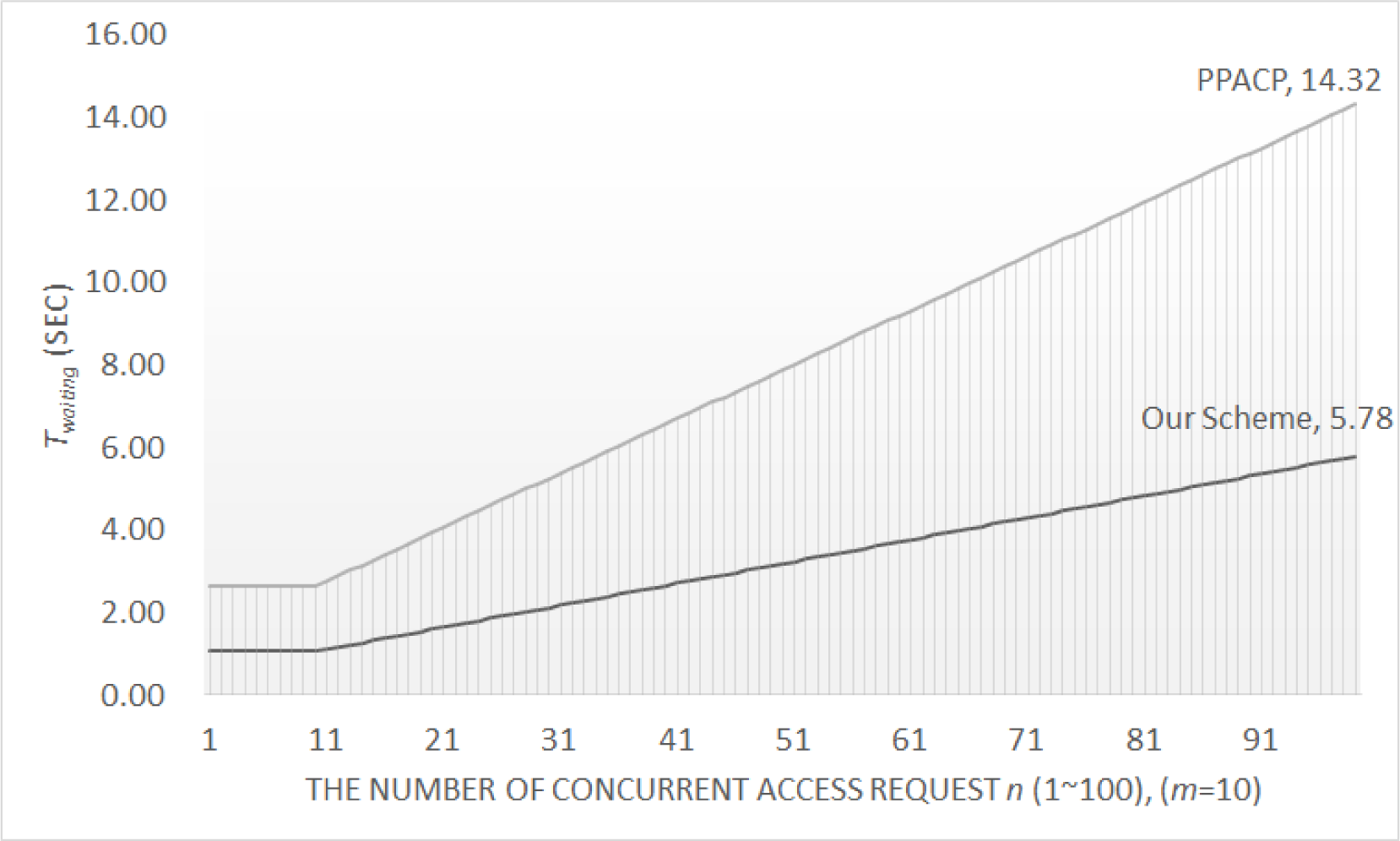
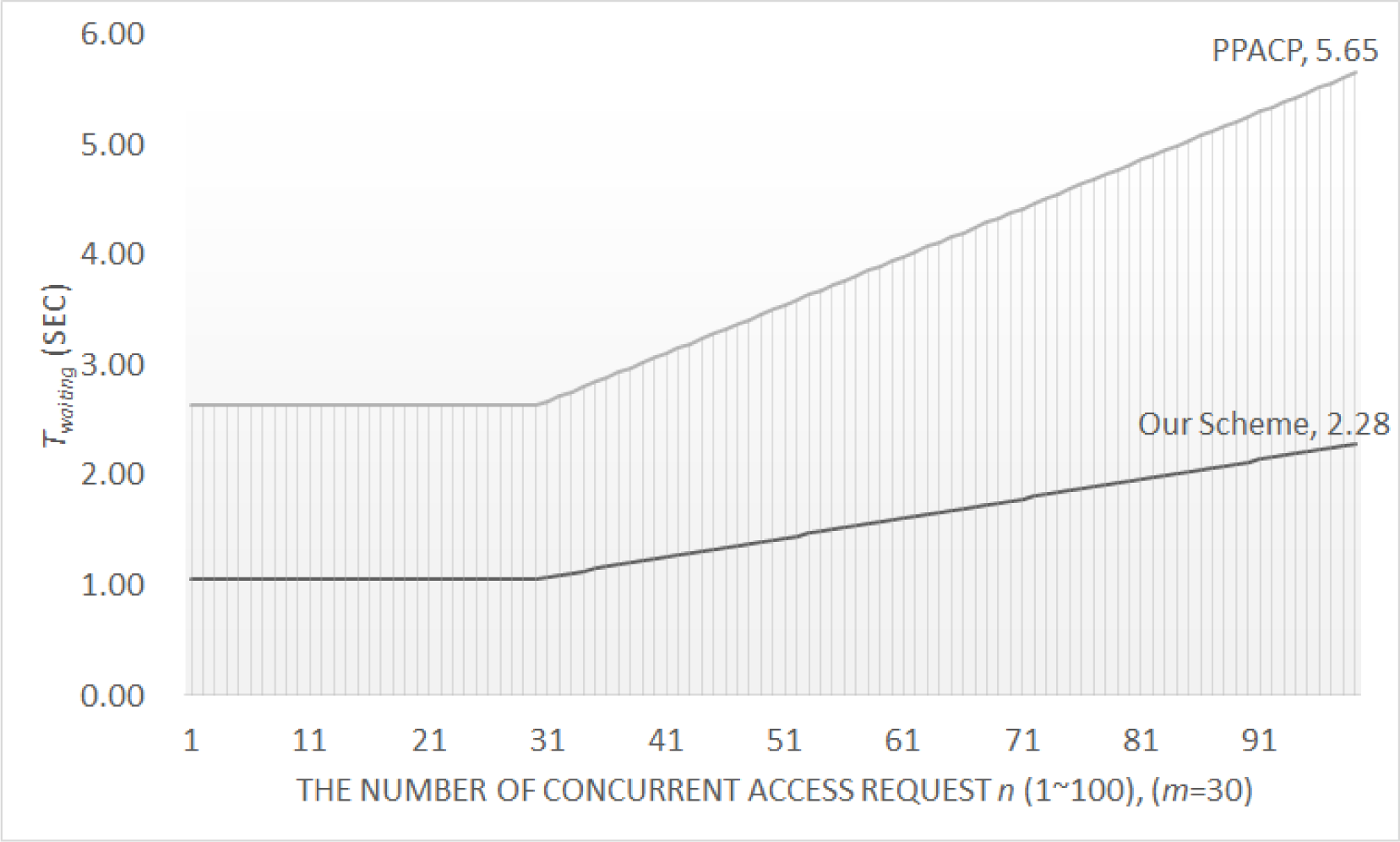
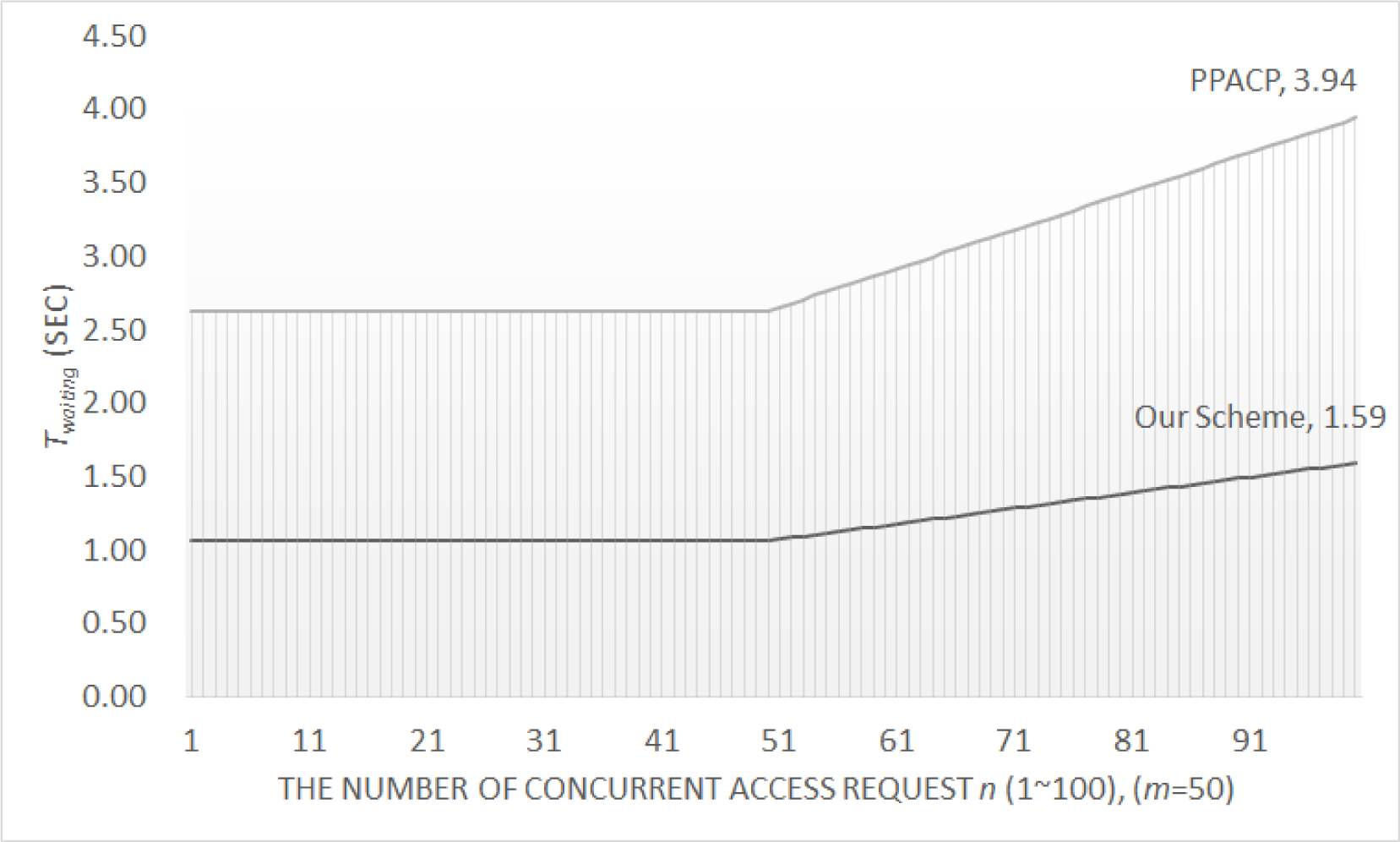
4.2. Performance
4.3. Security Analysis
5. Conclusion
Author Contributions
Conflicts of Interest
References
- Chung, Y.; Choi, S.; Won, D. Lightweight anonymous authentication scheme with unlinkability in global mobility networks. J. Converg. 2013, 4, 23–29. [Google Scholar]
- Taysi, Z.C.; Yavuz, A.G. ETSI compliant GeoNetworking protocol layer implementation for IVC simulations. Hum.-Centric Comput. Inf. Sci. 2013, 3, 1–12. [Google Scholar]
- Singh, R.; Singh, P.; Duhan, M. An effective implementation of security based algorithmic approach in mobile adhoc networks. Hum.-Centric Comput. Inf. Sci. 2014, 4, 1–14. [Google Scholar]
- Peng, K. A secure network for mobile wireless service. J. Inf. Process. Syst. 2013, 9, 247–258. [Google Scholar]
- Chen, Y.M.; Wei, Y.C. SafeAnon: A safe location privacy scheme for vehicular networks. Telecommun. Syst. 2012, 50, 339–354. [Google Scholar]
- Wei, Y.C.; Chen, Y.M. Safe distance based location privacy in vehicular networks, In Proceedings of the 2010 IEEE 71st Vehicular Technology Conference (VTC 2010-Spring), Taipei, Taiwan, 16–19 May 2010; pp. 1–5.
- Raya, M.; Hubaux, J. The security of vehicular ad hoc networks, In Proceedings of the 3rd ACM Workshop on Security of Ad hoc and Sensor Networks, Alexandria, VA, USA, 7–10 November 2005.
- Wang, N.; Huang, Y.; Chen, W. A novel secure communication scheme in vehicular ad hoc networks. Comput. Commun. 2008, 31, 2827–2837. [Google Scholar]
- Wischhof, L.; Ebner, A.; Rohling, H. Information dissemination in self-organizing intervehicle networks. IEEE Trans. Intell. Transp. Syst. 2005, 6, 90–101. [Google Scholar]
- Isaac, J.; Camara, J.; Zeadally, S.; Marquez, J. A secure vehicle-to-roadside communication payment protocol in vehicular ad hoc networks. Comput. Commun. 2008, 31, 2478–2484. [Google Scholar]
- Yousefi, S.; Mousavi, M.; Fathy, M. Vehicular ad hoc networks (VANETs): Challenges and perspectives, In Proceedings of the 6th International Conference on ITS Telecommunications, Chengdu, China, 21–23 June 2006; pp. 761–766.
- Zhang, C.; Lin, X.; Lu, R.; Ho, P.; Shen, X. An efficient message authentication scheme for vehicular communications. IEEE Trans. Veh. Tech. 2008, 57, 3357–3368. [Google Scholar]
- Yeh, L.; Chen, Y.; Huang, J. PAACP: A portable privacy-preserving authentication and access control protocol in vehicular ad hoc networks. Comput. Commun. 2011, 34, 447–456. [Google Scholar]
- Li, C.; Hwang, M.; Chu, Y. A secure and efficient communication scheme with authenticated key establishment and privacy preserving for vehicular ad hoc networks. Comput. Commun. 2008, 31, 2803–2814. [Google Scholar]
- Wu, W.; Chen, Y. Cryptanalysis of a PAACP: A portable privacy-preserving authentication and access control protocol in Vehicular Ad Hoc Networks. Appl. Math. Inf. Sci. 2012, 6, 463S–469S. [Google Scholar]
- Diffie, W.; Hellman, M. New directions in cryptography. IEEE Trans. Inf. Theory. 1976, 22, 644–654. [Google Scholar]
- Schneier, B. Applied Cryptography: Protocols, Algorithms, and Source Code in C, 2nd ed; John Wiley & Sons: New York, NY, USA, 1996. [Google Scholar]
- Chen, H.B.; Hsueh, S.C. Light-weight authentication and billing in mobile communications, In Proceedings of the IEEE 37th Annual 2003 International Carnahan Conference on Security Technology, Taipei, Taiwan, 4–16 October 2003; pp. 245–252.
- Kim, H.I.; Kim, Y.K.; Chang, J.W. A grid-based cloaking area creation scheme for continuous LBS queries in distributed systems. J. Converg. 2013, 4, 23–30. [Google Scholar]
- Oh, J.S.; Park, C.U.; Lee, S.B. NFC-based mobile payment service adoption and diffusion. J. Converg. 2014, 5, 8–14. [Google Scholar]
- Følstad, A.; Hornbæk, K.; Ulleberg, P. Social design feedback: Evaluations with users in online ad-hoc groups. Hum.-Centric Comput. Inf. Sci. 2013, 3, 1–27. [Google Scholar]
- Park, S.W.; Lee, I.Y. Anonymous authentication scheme based on NTRU for the protection of payment information in NFC mobile environment. J. Inf. Process. Syst. 2013, 9, 461–476. [Google Scholar]
- Gohar, M.; Koh, SJ. A network-based handover scheme in HIP-based mobile metworks. J. Inf. Process. Syst. 2013, 9, 651–659. [Google Scholar]
| Notation | Description |
|---|---|
| Vi | the i-th vehicle |
| VIDi | i-th vehicular node’s real identification |
| St | the t-th service provider |
| SIDt | t-th service provider’s real identification |
| SVIDk | k-th service’s identification |
| ARk | the access privilege of SVIDk |
| ACi | authorized credential for vehicle Vi |
| , | authorized credential made by St and Vi, respectively |
| portable authorized credential for vehicle Vi | |
| , | service right list made by St and Vi, respectively |
| Dk() | a corresponding symmetric cryptosystem that uses the secret key k for decryption |
| Ek() | a secure symmetric cryptosystem that uses the secret key k for encryption |
| Ni | fresh nonce, randomly generated by VIDi |
| Ns | fresh nonce, randomly generated by the service provider |
| h() | a collision-free and public one-way hash function |
| || | a string concatenation |
| X →Y :Z | a sender X sends a message Z to receiver Y |
| Requirements | Our Scheme | PAACP | SECSPP |
|---|---|---|---|
| Mutual Authentication | Yes | Yes | Yes |
| Context Privacy | Yes | No | Yes |
| Session Key Agreement | Yes | Yes | Partially Yes |
| Differentiated Service Access Control | Yes | Yes | No |
| Confidentiality and Integrity | Yes | Yes | N/A |
| Preventing Eavesdropping | Yes | No | Yes |
| Scalability | Fully Distributed | Fully Distributed | Bottleneck at Service |
| Lower Communication and Computational Cost | Low | High | Extremely High |
| Our Scheme | PAACP | SECSPP | |
|---|---|---|---|
| Authorization Phase | 2Tsym + 2Thash+ 5Txor | 4Tasym + Thash | 2Tasym + 2Texp+ 3Thash + 4Txor |
| Access Service Phase | 2Tsym + 2Texp+ 3Txor | 3Tasym + 2Tsym+ Thash | 3Tasym + 2Texp+ 6Thash + 5Txor |
| Computational Costs | ≈ 124Tsym | ≈ 702Tsym | ≈ 740Tsym |
| Rounds | 4 | 3 | 5 |
| Authorization (TAuthorization) | ≈ 0.0174s | ≈ 3.48s | ≈ 2.784s |
| Access Service (TAccss verification) | ≈ 1.0614s | ≈ 2.6274s | ≈ 3.654s |
| Total Costs | ≈ 1.0788s | ≈ 6.1074s | ≈ 6.438s |
© 2014 by the authors; licensee MDPI, Basel, Switzerland This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Wu, W.-C.; Chen, Y.-M. Improving the Authentication Scheme and Access Control Protocol for VANETs. Entropy 2014, 16, 6152-6165. https://doi.org/10.3390/e16116152
Wu W-C, Chen Y-M. Improving the Authentication Scheme and Access Control Protocol for VANETs. Entropy. 2014; 16(11):6152-6165. https://doi.org/10.3390/e16116152
Chicago/Turabian StyleWu, Wei-Chen, and Yi-Ming Chen. 2014. "Improving the Authentication Scheme and Access Control Protocol for VANETs" Entropy 16, no. 11: 6152-6165. https://doi.org/10.3390/e16116152
APA StyleWu, W.-C., & Chen, Y.-M. (2014). Improving the Authentication Scheme and Access Control Protocol for VANETs. Entropy, 16(11), 6152-6165. https://doi.org/10.3390/e16116152




