- Article
Leveraging Confidential Computing to Enhance Data Privacy in Hyperledger Fabric
- Stefano Avola,
- Pierpaolo Baglietto and
- Andrea Parodi
- + 1 author
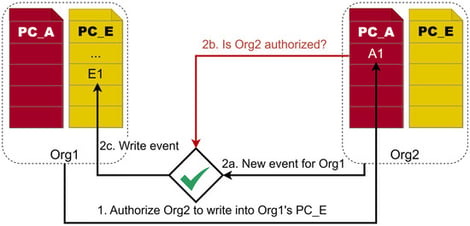
In this paper, we present a system built on Hyperledger Fabric (HLF) that leverages Confidential Computing (CC) technologies to strengthen data privacy guarantees beyond those achievable through application-level mechanisms alone. While HLF natively supports data confidentiality through Private Collections (PCs), which restrict data visibility to a subset of authorized network participants, these mechanisms do not protect data at the hardware level: a privileged or compromised hosting platform can access plaintext data in memory and on the filesystem irrespective of HLF access control policies. To address this limitation, we integrate CC into HLF by adopting Intel Software Guard Extensions (SGX) in conjunction with the Gramine framework. This integration enables the execution of HLF components—peer nodes, orderers, Chaincodes and client applications—within Trusted Execution Environments (TEEs). Furthermore, to securely grant access to selected data to a trusted third-party software (TPS) external to the blockchain network, we leverage the Remote Attestation (RA) feature provided by CC, as streamlined by Gramine and enforced on a per-request basis, ensuring that only verified enclaves (or “SGX enclaves”) with expected measurements may access private data. In addition, the Sealing mechanism is employed to persistently store cryptographic material required by HLF components on the filesystem while preserving both confidentiality and integrity. Together, PCs, RA, Sealing, and enclave-based execution establish a layered privacy guarantee: PCs enforce application-level data segregation among channel participants; RA provides measurement-based access control for an external TPS; Sealing ensures that cryptographic material and blockchain state remain encrypted on the filesystem; and enclave-based execution protects data in use through hardware-level memory encryption. The proposed system has been applied and experimentally validated in a logistics use case in the Port of Genoa: benchmarks against an experimental HLF deployment demonstrate an average 95th-percentile (p95) performance overhead of approximately 1.3× attributable to SGX memory encryption and Gramine-based enclave execution, whereas an elevated memory usage footprint (33–35 GB per organization) has been measured, mainly due to the Gramine environment: this remains an open direction for future work.
16 April 2026