This section discusses the state-of-the-art and literature review of blockchain security, technology, its architecture, components, and various security systems. Blockchain systems comprise several essential elements. The distributed Ledger provides a replicated database maintained across multiple nodes, which provides redundancy and eliminates single points of failure [
2]. Each node maintains a complete copy of transaction history, enabling independent verification. The Cryptographic Hash Functions: One-way functions that map arbitrary-length input to fixed-length output, creating tamper-evident fingerprints of data. Bitcoin and Ethereum employ SHA-256 and Keccak-256, respectively, though the choice of hash function significantly impacts system properties [
18].
2.1. Application to Blockchain Security
Regarding the application of blockchain security, ref. [
10] analyzes the CIA triad in relation to blockchain technology in public sector contexts. The framework demonstrated how distributed ledgers address each of the CIA components while introducing unique challenges. Ref. [
11] presented a blockchain-based authentication system implementing CIA principles for e-health systems, demonstrating lightweight cryptographic techniques with 0.059 millisecond authentication delays, a 4000-fold improvement over contemporary approaches, while preserving CIA properties through Proof of Authority consensus. The authors integrated Ethereum blockchain, smart contracts, blind signatures, and one-way hash functions to enhance data integrity, security, and privacy in decentralized healthcare frameworks. Ref. [
21] explored cryptography algorithms in a network environment by applying secret keys, public keys, and hash functions to ensure data confidentiality, authentication, and non-repudiation. Ref. [
22] carried out a systematic review that examined blockchain vulnerabilities across network-level attacks, consensus-based exploits on smart contract vulnerabilities, and user-centric risks, including DeFi exploits, flash loan attacks, and how bridge vulnerabilities challenge traditional CIA assumptions.
2.2. Cryptographic Primitives in Blockchain
Cryptographic Primitives in blockchain provide the low-level mathematical algorithms used to provide secure CIA mechanisms in blockchain systems, including Digital Signature Algorithms, RSA vs. ECDSA. Furthermore, ref. [
20] examined how digital signatures facilitate authentication and non-repudiation in blockchain systems, thereby enabling transaction authorization without the need for centralized authorities. Two dominant approaches, RSA and ECDSA, present distinct trade-offs. RSA relies on the computational difficulty of factoring large composite numbers [
23]. RSA’s security derives from the RSA problem: given n = pq (the product of two large primes, p and q), and e (the public exponent), computing d (the private exponent) without knowing p and q is computationally infeasible. However, ECDSA bases security on the discrete logarithm problem in elliptic curve groups [
24]. RSA signatures require key sizes of 2048–4096 bits for adequate security, resulting in 256–512-byte signatures. Given point P = kG on an elliptic curve (where G is a generator point and k is a scalar), determining k is computationally demanding. ECDSA achieves equivalent security to RSA with dramatically fewer keys: 256-bit ECDSA provides security comparable to 3072-bit RSA [
13]. Comparative Analysis provides recent literature that demonstrates ECDSA’s superiority for blockchain applications across multiple dimensions:
Key and Signature Size: ECDSA generates 64-byte signatures (for secp256k1) versus 256-byte RSA-2048 signatures, reducing blockchain storage and bandwidth requirements by 75% [
14,
25]. This difference compounds significantly in high-transaction environments. Ethereum processes approximately 1.2 million transactions daily, where ECDSA’s compact signatures save around 230 MB daily compared to an equivalent RSA implementation.
Performance Characteristics: ECDSA signature generation is substantially faster than RSA signing. Benchmarks on contemporary hardware show ECDSA signing at ~0.2 milliseconds, compared to RSA-2048 at ~1.8 milliseconds [
26]. However, RSA verification (0.16 ms) outperforms ECDSA verification (8.53 ms) due to the use of small public exponents (typically e = 65,537), which enables efficient modular exponentiation. [
27].
Blockchain Adoption: Bitcoin, Ethereum, and the majority of modern blockchains employ ECDSA rather than RSA [
12,
14,
26]. This industry consensus reflects ECDSA’s practical advantages: reduced transaction size, enabling more transactions per block; lower bandwidth consumption for network propagation; and better alignment with the blockchain’s peer-to-peer architecture, which requires frequent signature operations.
Security Considerations: Both RSA and ECDSA algorithms are vulnerable to quantum-resistant threats such as side channel attacks, integer factorization attacks, if the attacker could find the modulus
N used to calculate the private keys in the RSA algorithm, as well as Denial of Service attacks, among others. Further, concerns are raised regarding quantum-resistance challenges, as it is able to resist threats but will not be able to prevent quantum attacks completely. Additionally, these algorithms may not be able to resist sufficiently powerful quantum computers and could allow threat actors to duplicate signatures, gain access, and modify content during blockchain transactions, leading to quantum-safe issues. For instance, Shor’s algorithm can break RSA and ECDSA with sufficiently powerful quantum computers [
16]. However, ECDSA’s current classical security advantage and smaller footprint position it favourably for hybrid post-quantum transition strategies [
28].
2.3. Hash Functions: SHA-256 vs. SHA-3 (Keccak)
Cryptographic hash functions form the backbone of blockchain integrity, creating collision-resistant fingerprints that link blocks into immutable chains. The choice between SHA-256 (SHA-2 family) and SHA-3 (Keccak) has a significant impact on system security and performance. SHA-256 (SHA-2 Family) was standardized by the National Institute of Standards and Technology (NIST) in 2002 as part of the Secure Hash Standard [
29]. It employs the Merkle–Damgård construction with Davies–Meyer compression function, processing 512-bit blocks through 64 rounds of ARX (Add-Rotate-XOR) operations to produce 256-bit digests. SHA-256 demonstrates strong security properties with no practical collision attacks discovered to date [
18]. SHA-3 (Keccak-256) represents a significant departure from the design philosophy of SHA-2. Selected as NIST’s SHA-3 standard in 2013 after a five-year competition, Keccak employs the sponge construction, a permutation-based approach fundamentally different from Merkle–Damgård [
30]. The sponge function absorbs input bits into a state through Exclusive OR (XOR) operations, applies the Keccak-f permutation, and squeezes output bits, providing flexible output lengths and inherent resistance to length extension attacks.
Cryptographic Diversity: SHA-3’s entirely different design from SHA-2 provides crucial cryptographic diversity. If cryptanalytic breakthroughs compromise the Merkle–Damgård construction (as occurred with Message Digest Algorithm (MD5) and SHA-1), SHA-3 remains unaffected due to its fundamentally distinct sponge architecture [
30,
31]. This “cryptographic hedge” motivated NIST’s standardization, despite the continued security of SHA-2. Further, ref. [
32] highlighted the historical pattern of blockchain vulnerability attacks on Merkle–Damgård designs (MD5, SHA-0, SHA-1), necessitating alternative constructions for long-term security.
Length Extension Attack Immunity: SHA-256, like all SHA-2 algorithms, is vulnerable to length extension attacks where an attacker, knowing H(m), can compute H(m || m’) for chosen m’ without knowing m [
33]. This vulnerability requires careful implementation, typically using HMAC constructions. SHA-3’s sponge construction is inherently immune to length extension attacks [
30], simplifying secure implementation and reducing the risk of developer error, a critical consideration given smart contract vulnerabilities [
34].
Equivalent Security Strength: Both SHA-256 and Keccak-256 provide 128-bit collision resistance and 256-bit preimage resistance, offering equivalent security for blockchain applications [
18,
30]. The collision resistance of 2^128 operations exceeds the feasibility of practical attacks, even with anticipated technological advances. [
35]. This equivalence means that the choice between algorithms rests on other factors, including architectural diversity of algorithms used in various blockchains, attack immunity, and ecosystem compatibility.
Performance Trade-offs: On traditional Central Processing Unit (CPU) architectures, SHA-256 generally outperforms Keccak-256. Benchmarks show SHA-256 at approximately 5.6 cycles per byte versus Keccak-256 at 11.7–12.25 cycles per byte on x86-64 processors [
30]. However, in hardware implementations (Application-Specific Integrated Circuits (ASICs), Field-Programmable Gate Array (FPGAs), SHA-3 demonstrates superior performance due to its permutation-based design, amenable to parallel processing [
30]. A recent study by [
36] regarding AI-driven blockchain optimization posited that as blockchain infrastructure increasingly employs specialized hardware accelerators, the architectural properties of SHA-3 become advantageous.
Blockchain Adoption and Rationale: While Bitcoin employs SHA-256, Ethereum made a deliberate choice to use Keccak-256 for several reasons [
12,
37]: (1) ASIC resistance during the design phase, as Keccak’s properties initially deterred specialized mining hardware; (2) flexibility in output length through Secure Hash Algorithm-Keccak (SHAKE) variants, enabling domain-specific hash sizes; (3) clean mathematical foundations providing confidence in long-term security. Furthermore, ref. [
38] examined the challenge of identifying vulnerabilities in smart contracts, which is crucial for preventing criminals from executing malicious exploits during DeFi transactions. A case study by [
37], regarding Ethereum Classic’s security responses to 51% attacks, recommended that switching to the Keccak-256 PoW algorithm, citing its NIST standardization, enhanced security as the latest SHA family member, and faster performance compared to Ethash.
Keccak vs. SHA-3 Clarification: A crucial technical distinction exists between original Keccak and standardized SHA-3. NIST modified Keccak’s padding scheme when standardizing SHA-3, changing the padding constant from 0x1 to 0x06 [
39]. This alteration produces different hash outputs despite identical core algorithms and security levels. Ethereum uses the original Keccak-256, rather than NIST’s SHA-3-256, which is a common source of confusion when interfacing with other systems [
37,
39].
2.4. Byzantine Fault Tolerance (BFT)
BFT has become a foundational concept in distributed computing and blockchain consensus research, designed to enable reliable agreement among network participants even when some nodes behave unpredictably or maliciously. Traditional fault-tolerant systems primarily handle simple crash failures, but BFT extends resilience to cover arbitrary and deceptive behaviours, as originally framed by the Byzantine Generals Problem. The central objective of BFT mechanisms is to ensure that honest nodes can still achieve agreement on the correct state of the system, provided that no more than one-third of participants are compromised. Early theoretical research into BFT laid the groundwork for dependable distributed systems, although these early models faced scalability and communication inefficiencies. The introduction of the Practical Byzantine Fault Tolerance (PBFT) algorithm marked a significant step forward by enabling consensus in asynchronous environments with lower latency. However, as noted in [
16], these early BFT solutions were primarily developed for closed and permissioned networks, making them unsuitable for decentralized public systems, such as blockchains.
Recent advancements in blockchain technology have redefined the application of BFT principles. Ref. [
2] emphasized that modern consensus protocols integrate BFT mechanisms with PoS and hybrid architectures to enhance efficiency, scalability, and energy conservation. These newer designs, such as Tendermint and HotStuff, achieve deterministic finality, meaning that once a block is validated, it becomes irreversible, unlike the probabilistic nature of PoW systems. Similarly, ref. [
19] explored scalability limitations in decentralized networks, highlighting that while BFT provides robust security, optimizing communication complexity remains critical to achieving higher throughput and real-time performance. Overall, the evolution of BFT from theoretical constructs to practical blockchain consensus mechanisms reflects the growing demand for decentralized yet reliable systems. Modern implementations strike a balance between security and scalability, underpinning a new generation of blockchain protocols that achieve distributed trust without relying on centralized authorities.
2.6. Research Gap Identification
While existing literature comprehensively addresses several aspects of blockchain security, several gaps remain due to technological changes, a changing attack surface, and evolving threats.
Cryptographic Transition Guidance: Limited practical guidance exists for migrating blockchain implementations from legacy cryptographic primitives (RSA, SHA-256) to modern alternatives (ECDSA, SHA-3), particularly regarding performance implications and compatibility management.
Integrated CIA Framework: Most research addresses confidentiality, integrity, or availability in isolation. Comprehensive frameworks that demonstrate practical implementation of the CIA triad with modern cryptography in working blockchain systems remain scarce.
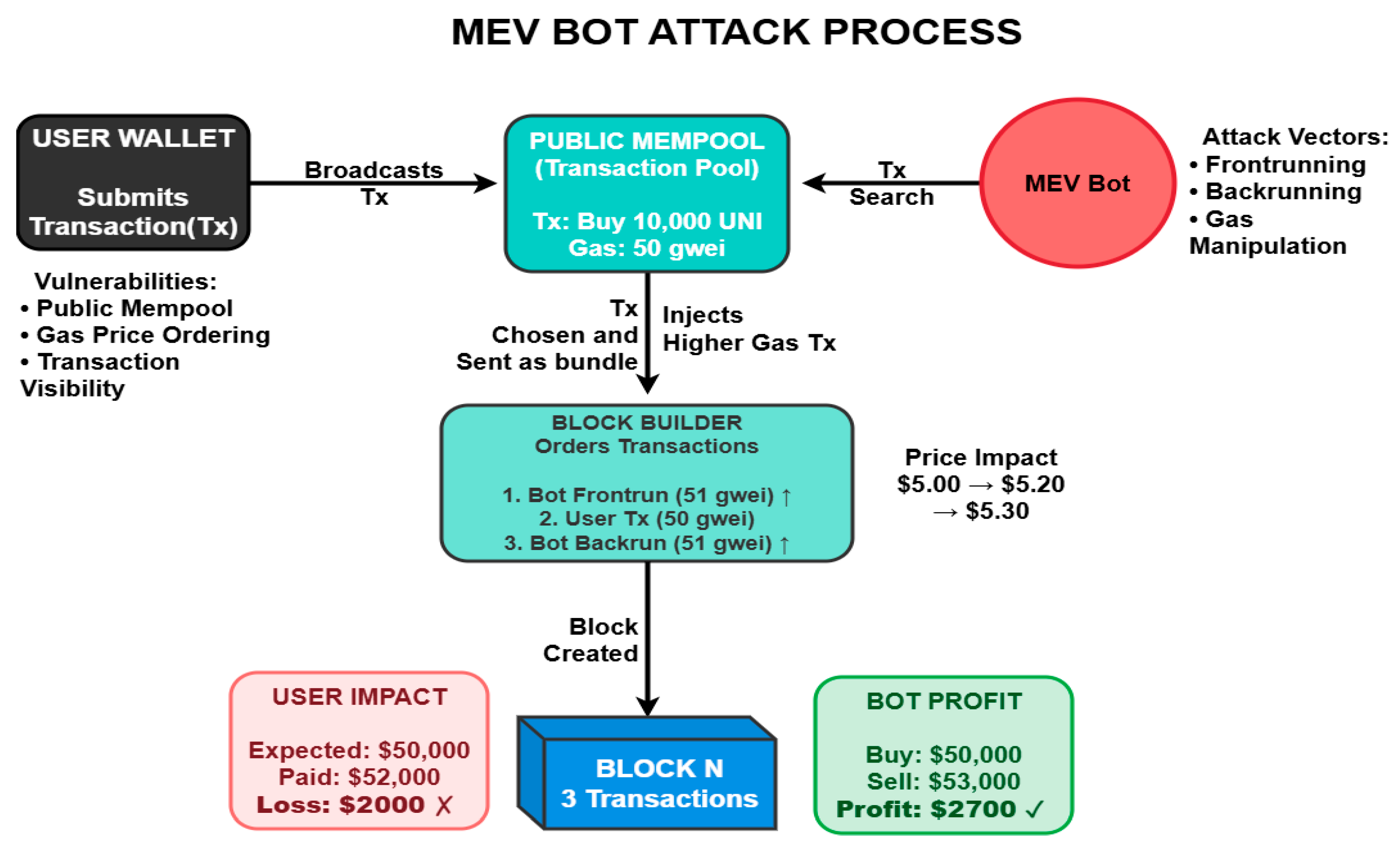
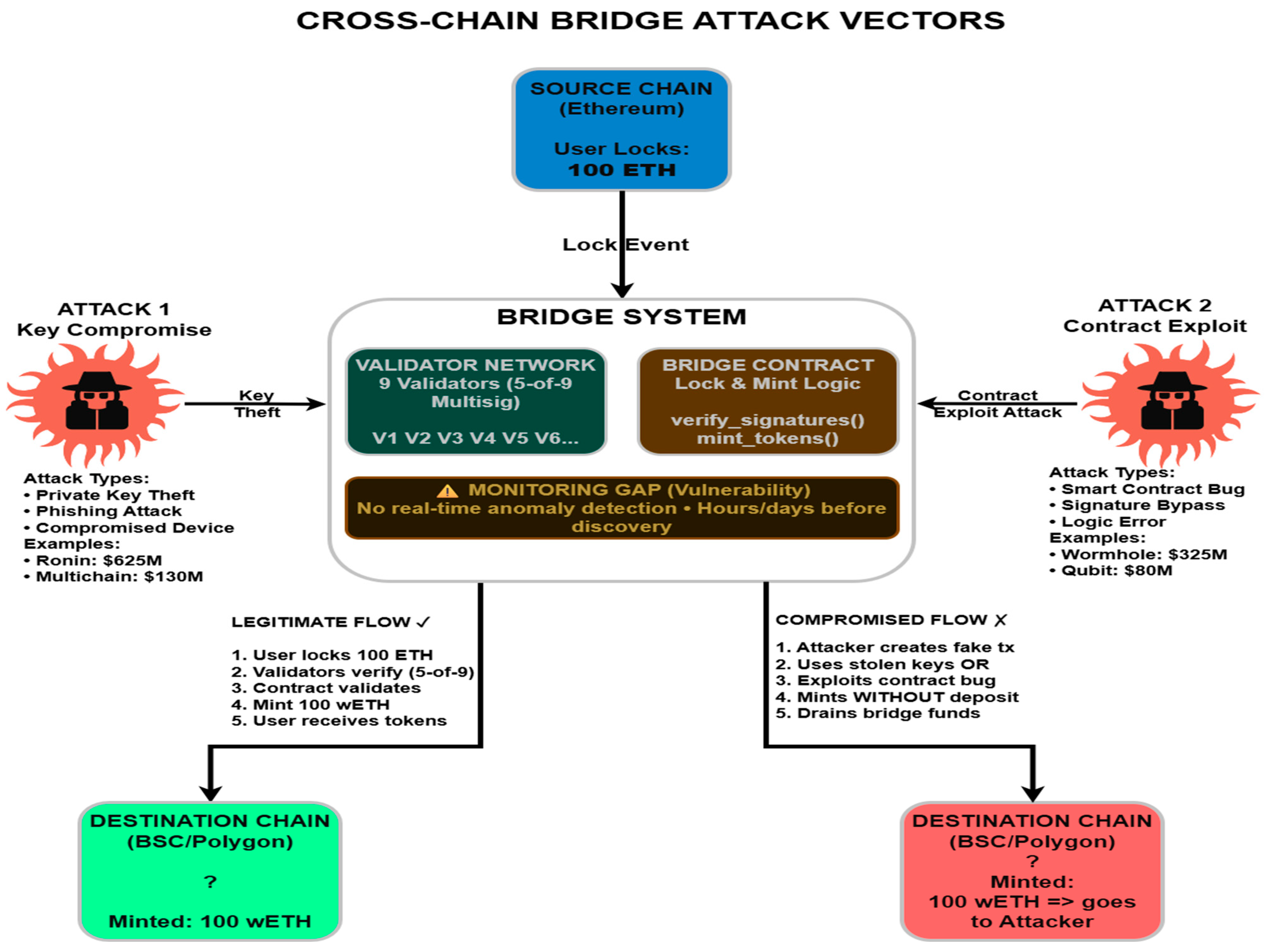
Contemporary Threat Integration: Recent vulnerabilities (MEV/BEV, 51% Attacks) are well-documented individually, but their integration into comprehensive blockchain security frameworks and mapping to CIA triad principles requires further investigation.
Practical Implementation Details: Academic blockchain research often remains theoretical or uses simplified implementations. Production-grade code examples demonstrated security patterns are limited, creating knowledge gaps for practitioners.
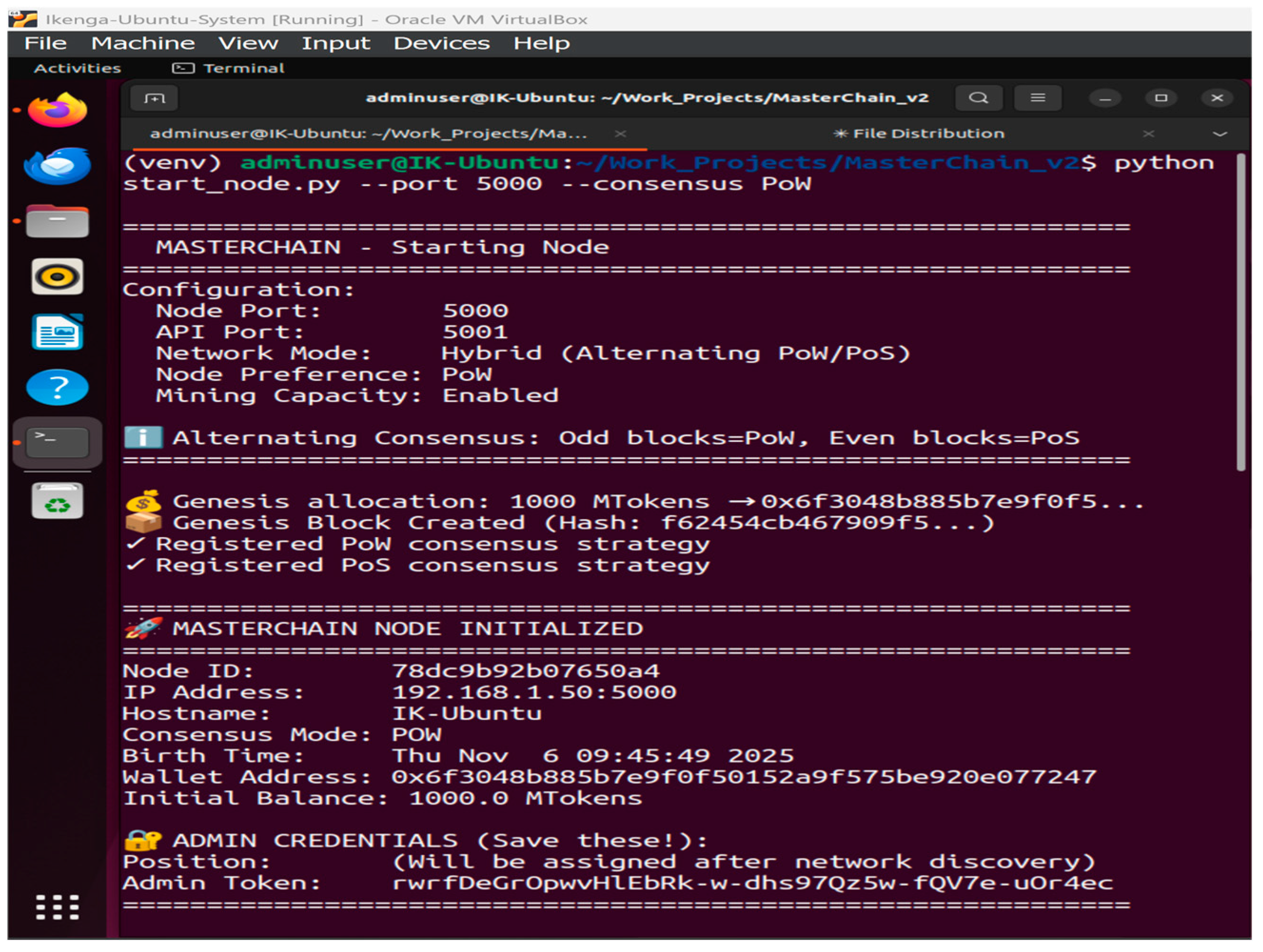
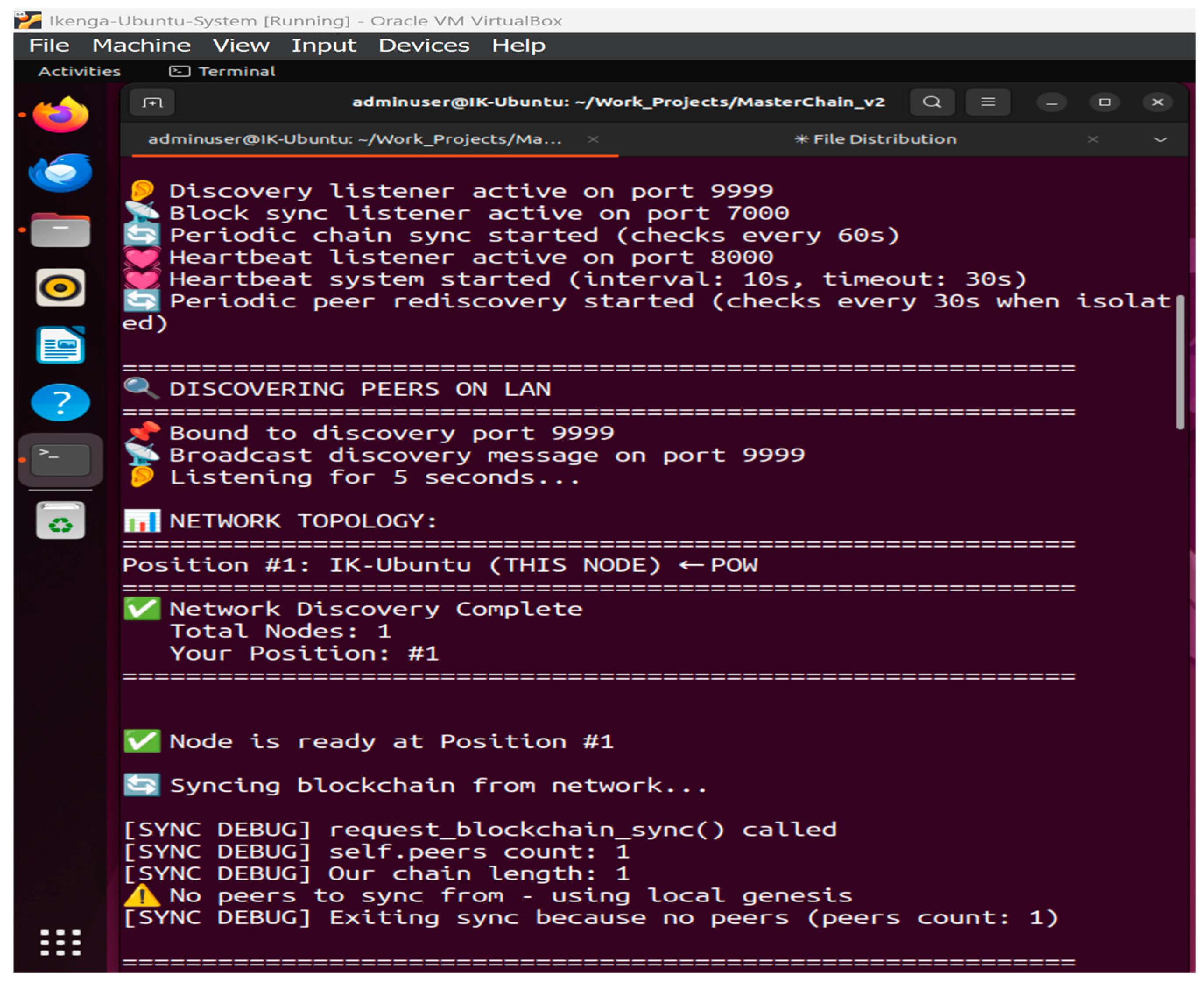
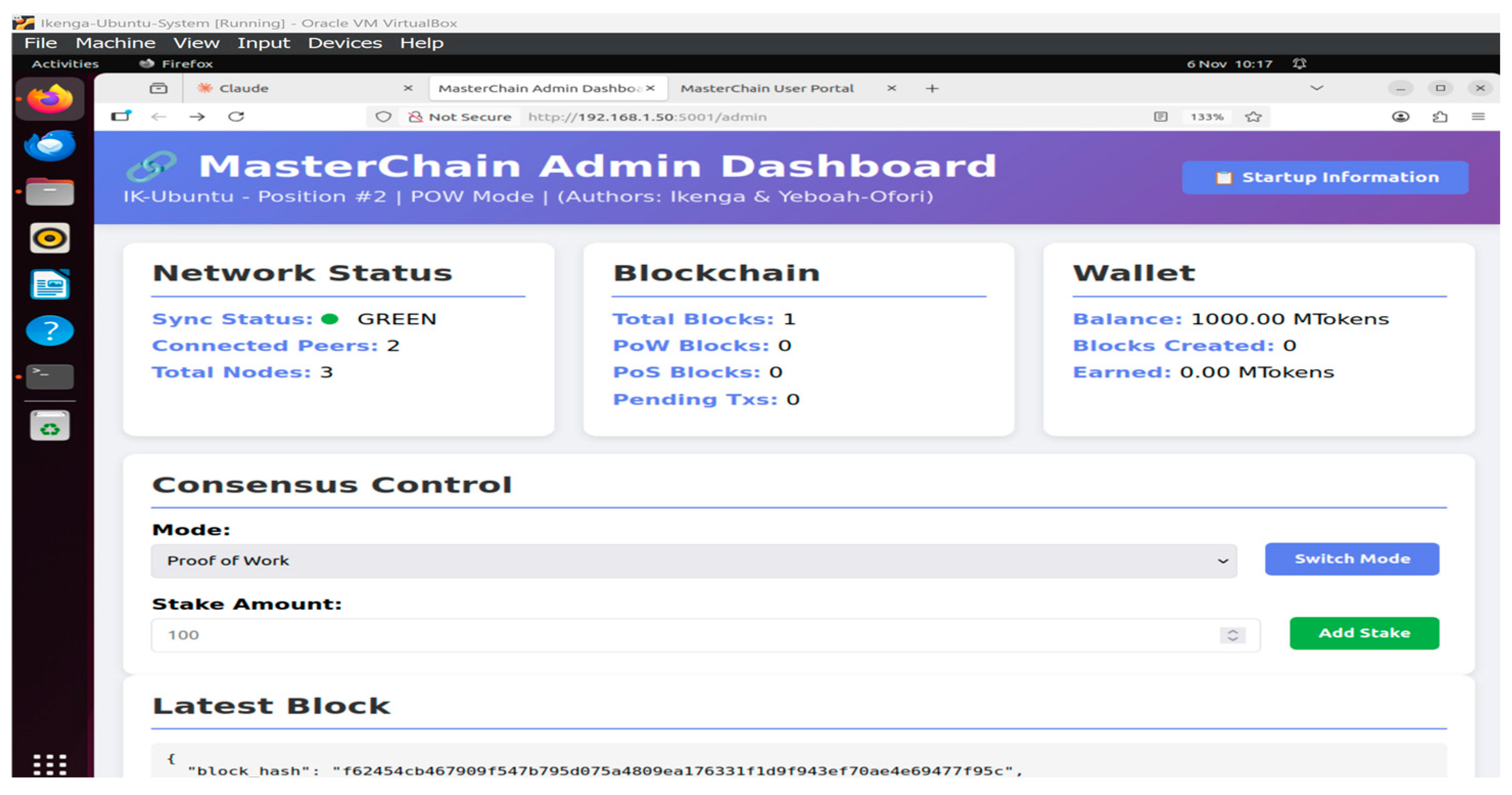
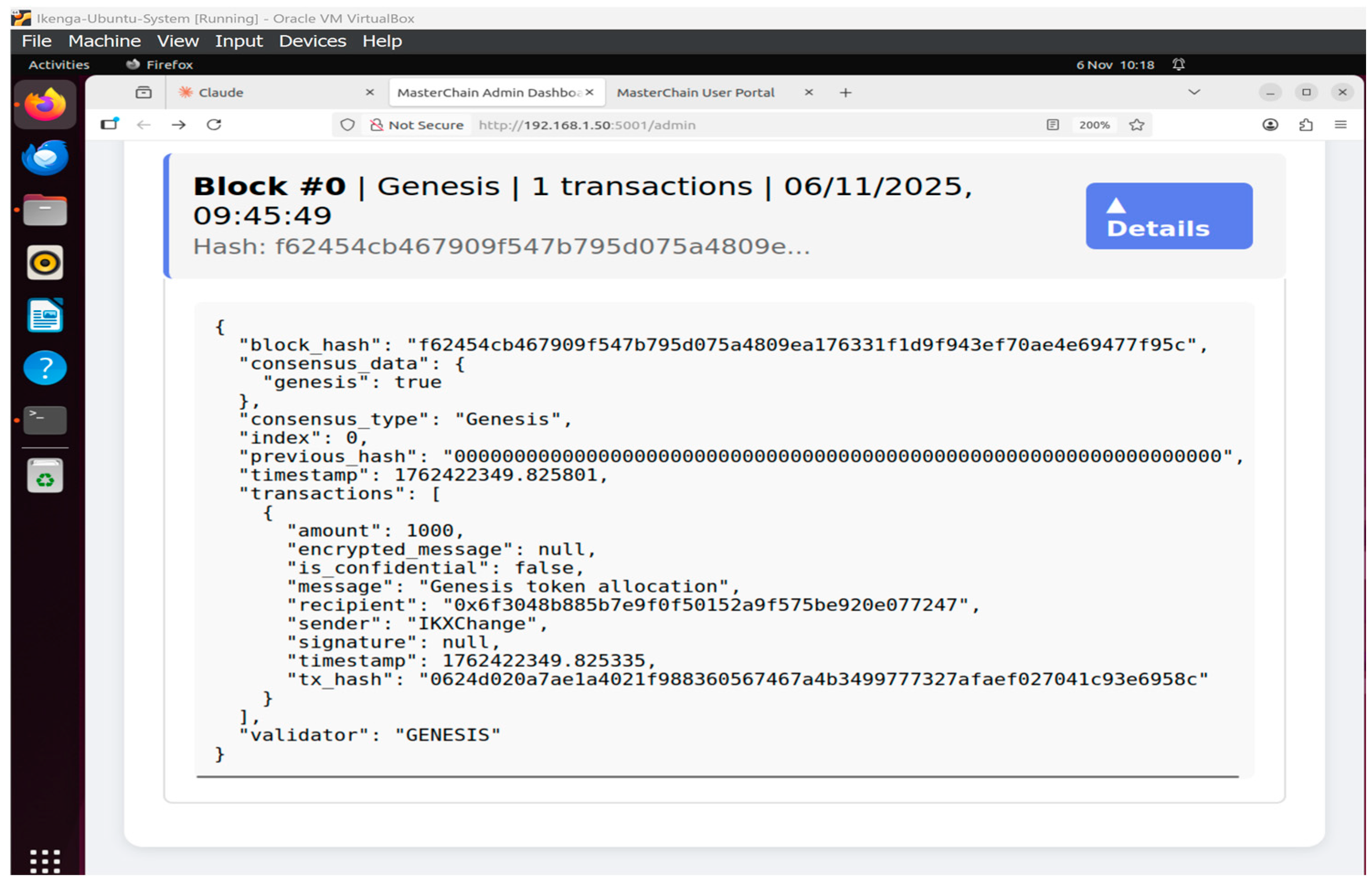
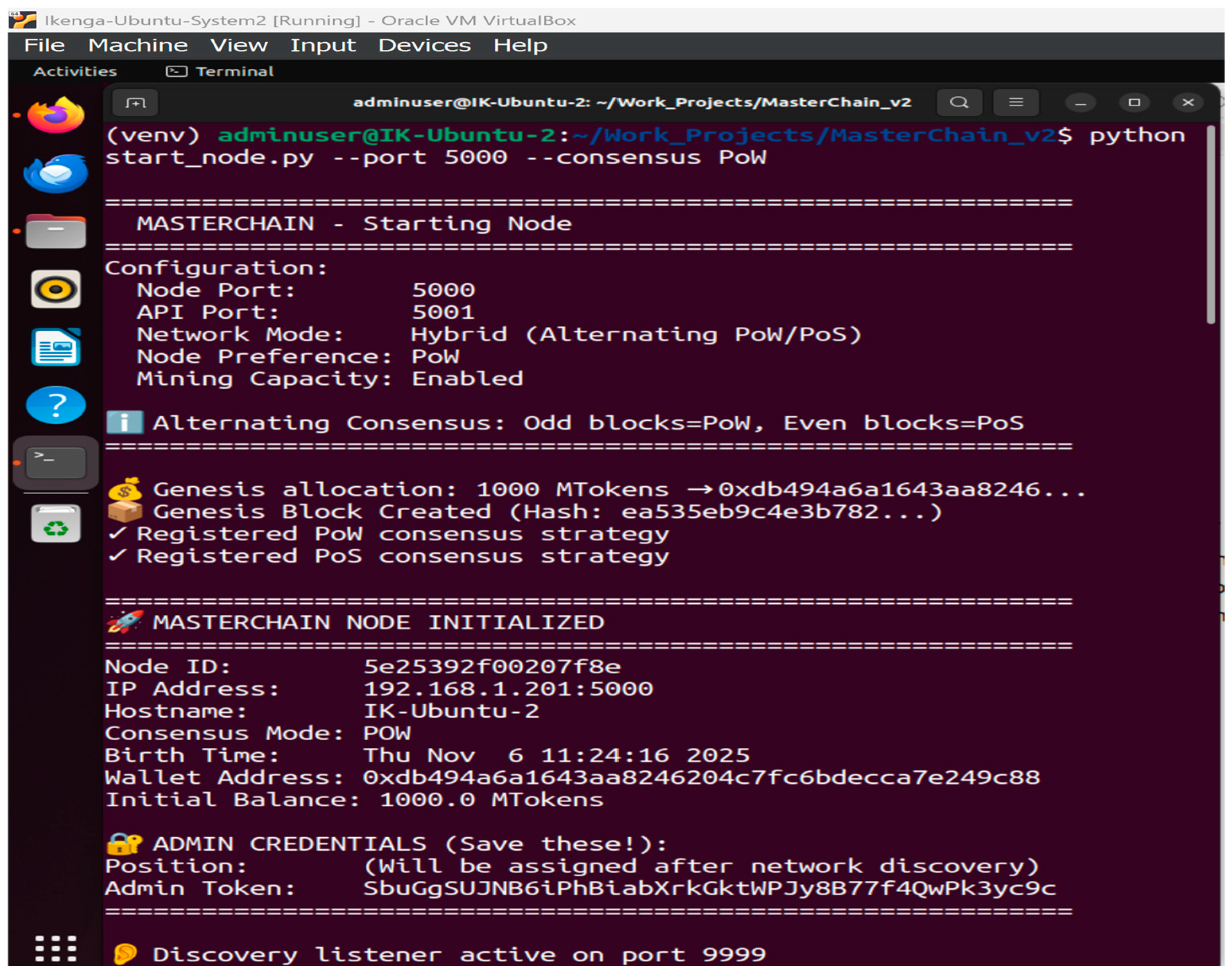
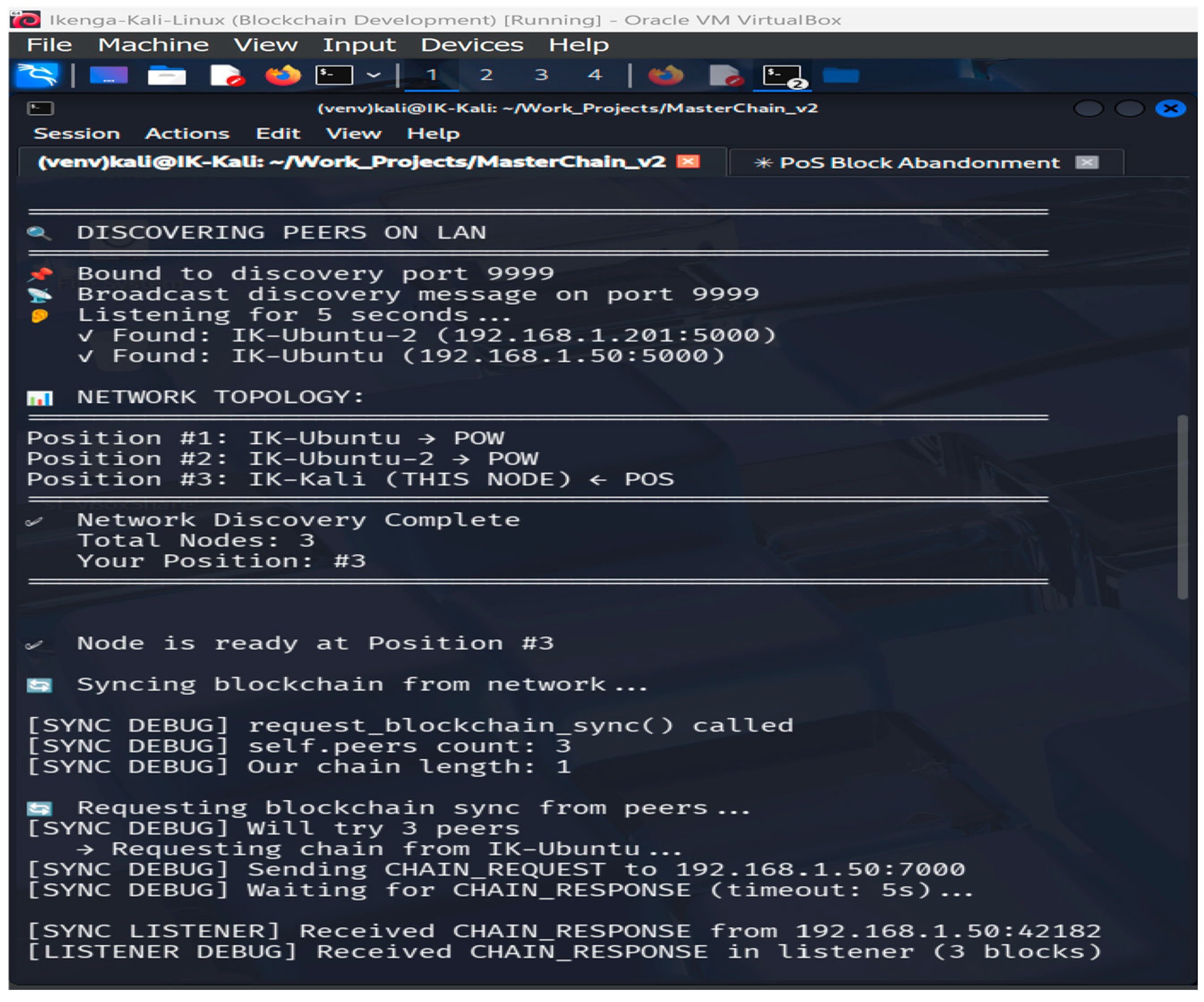
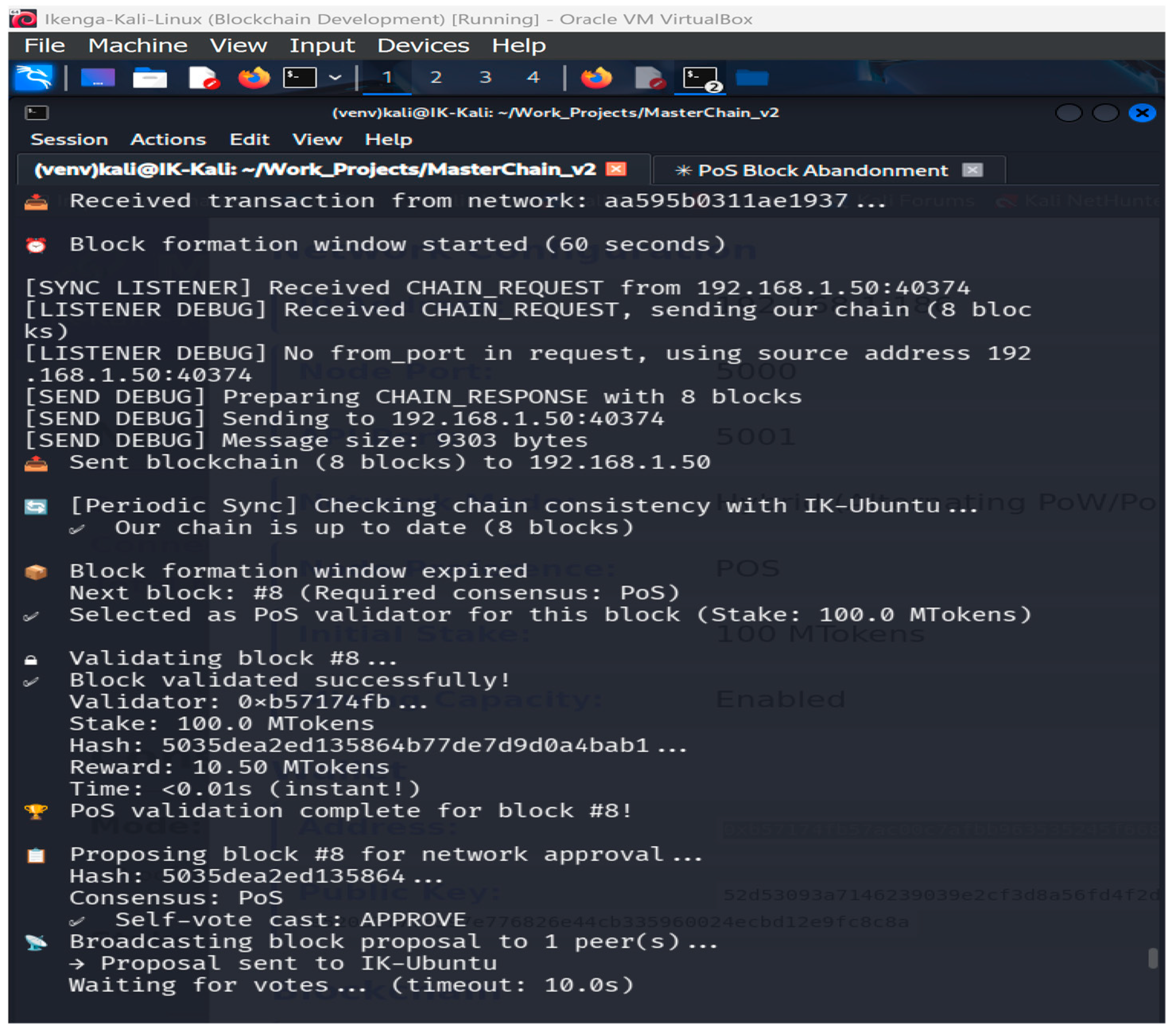
Hybrid Consensus Mechanism: This system is designed to utilize an alternating PoW and PoS mechanism for block generation, alternating between odd and even numbers in a sequence. It then uses BFT voting for block validation and confirmation. This three-level hybrid consensus mechanism is fully demonstrated to provide a comprehensive understanding of consensus mechanisms, a rarity in contemporary research.
This research addresses these gaps by providing MasterChain, a practical blockchain implementation featuring modern cryptographic primitives, comprehensive vulnerability analysis, and detailed implementation guidance for the CIA triad principles, which incorporates a hybrid consensus mechanism.
Limitations in Previous Works: Existing blockchain security research frequently references the CIA triad as a foundational security model. However, most studies apply it conceptually rather than operationally. Further, ref. [
5] employ the CIA triad as an evaluative lens to assess blockchain adoption in public sector applications, extending the model with non-repudiation. While insightful at a governance level, their work does not address the implementation of CIA properties within blockchain communication mechanisms. Furthermore, ref. [
6] provides a comprehensive survey of blockchain applications in CPS and IoT systems, highlighting how CIA can theoretically be maintained in distributed communication environments. However, the study remains architectural CPS and IoT systems and does not present an executable communication model or empirical validation. Additionally, [
46] propose a blockchain-based framework for secure IoT communication using smart contracts. Although the work addresses integrity and availability through permissioned blockchain infrastructure, confidentiality is largely enforced through access control assumptions rather than cryptographic protection of communication payloads. Moreover, ref. [
47] integrate the CIA triad with STRIDE (Spoofing, Tampering, Repudiation, Information Disclosure, Denial of Service, Elevation of Privilege) threat modelling to secure peer-to-peer networks via blockchain-based access control. Their focus is on authorization and policy enforcement rather than end-to-end communication security. However, this study implements the CIA triad directly within blockchain communication, demonstrating how CIA can be enforced and evaluated during transaction exchange and node interaction.
Recent blockchain security research [
7] has emphasized cryptographic, privacy-preserving, and trust-enhancing mechanisms across multiple application domains. While such studies provide valuable theoretical and methodological insights, they typically address security primitives in isolation. However, our work focused on the system-level enforcement of the CIA triad within blockchain communication. The proposed MasterChain implementation integrates CIA directly into transaction propagation and node interaction, rather than treating them as independent design considerations. Thus, our study contributes to the improvements made by [
7] and demonstrates how established security principles can be operationalized cohesively to secure blockchain communication, extending existing work from mechanism-centric analysis to communication-focused implementation.
Section 4.4 details the practical realization of these properties within the MasterChain testbed, addressing gaps between theoretical security models and real blockchain communication systems.