Blockchain-Based Solutions for UAV-Assisted Connected Vehicle Networks in Smart Cities: A Review, Open Issues, and Future Perspectives
Abstract
1. Introduction
- We review the IoV concept, its architectures, benefits, and flaws, how applications are grouped for development in this technology, quickly introducing the rising Social Internet of Vehicles, and presenting the main challenges and problems to be solved.
- We present the concept of UAV and smart cities and how UAV-assisted IoV can help realize the smart cities concept and the underlying technologies it requires.
- We review the Blockchain concept, its origins, and the technologies behind it that give it its properties and how they do it. We also list the properties of the three types of Blockchain, explain how the Blockchain assures certain security properties and how these properties correlate to the security challenges of the IoV.
- We present Blockchain-enabled solutions for IoV that offer various functionalities, such as safe data transmission, transport, or increase the performance of network communications. We also present Blockchain and UAV-assisted IoV based applications for smart cities, focusing on what opportunities there are for their implementations given their attributes and the smart cities’ requirements.
- We highlight and compare popular tools used to develop Blockchain-based solutions and network simulations, detailing some of their benefits and downsides, such as uniqueness, availability, pluggability, and efficiency.
- We discuss major challenges and open issues yet to be solved. We also present future perspectives such as the integration of novel network paradigms or machine learning.
2. Internet of Vehicles and Smart Cities
2.1. Definition
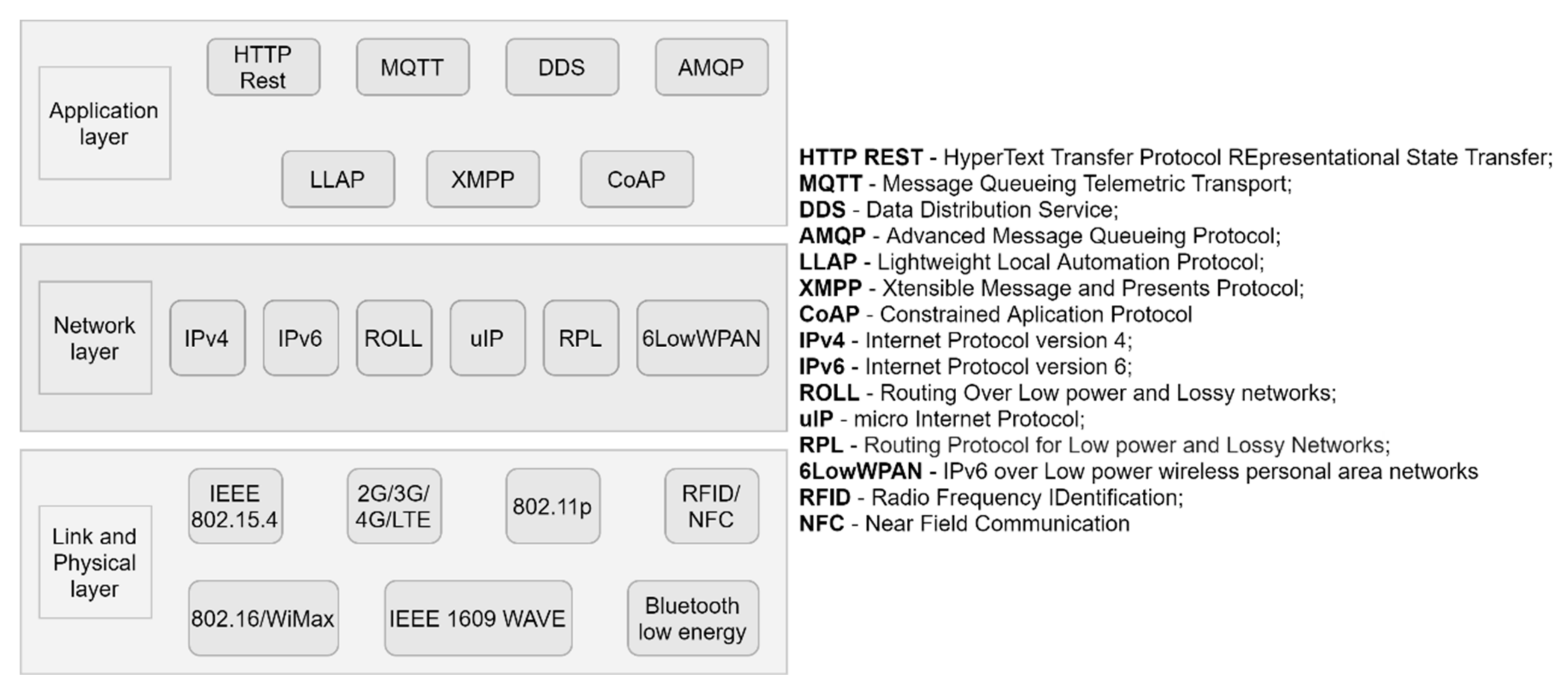
2.2. Architecture
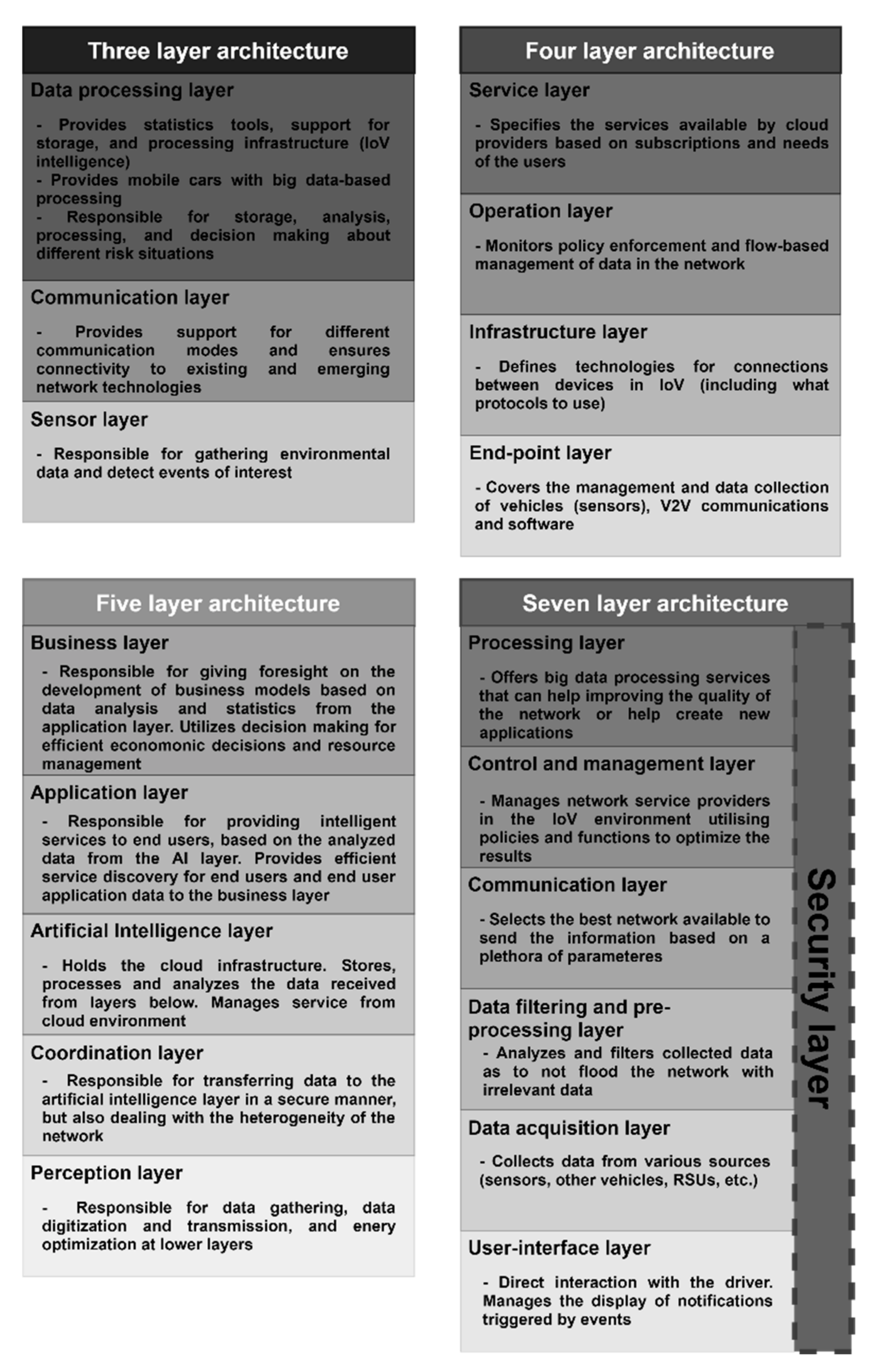
2.2.1. Three-Layer Architecture
- Sensor layer is responsible for the sensors in the vehicles and surrounding infrastructure.
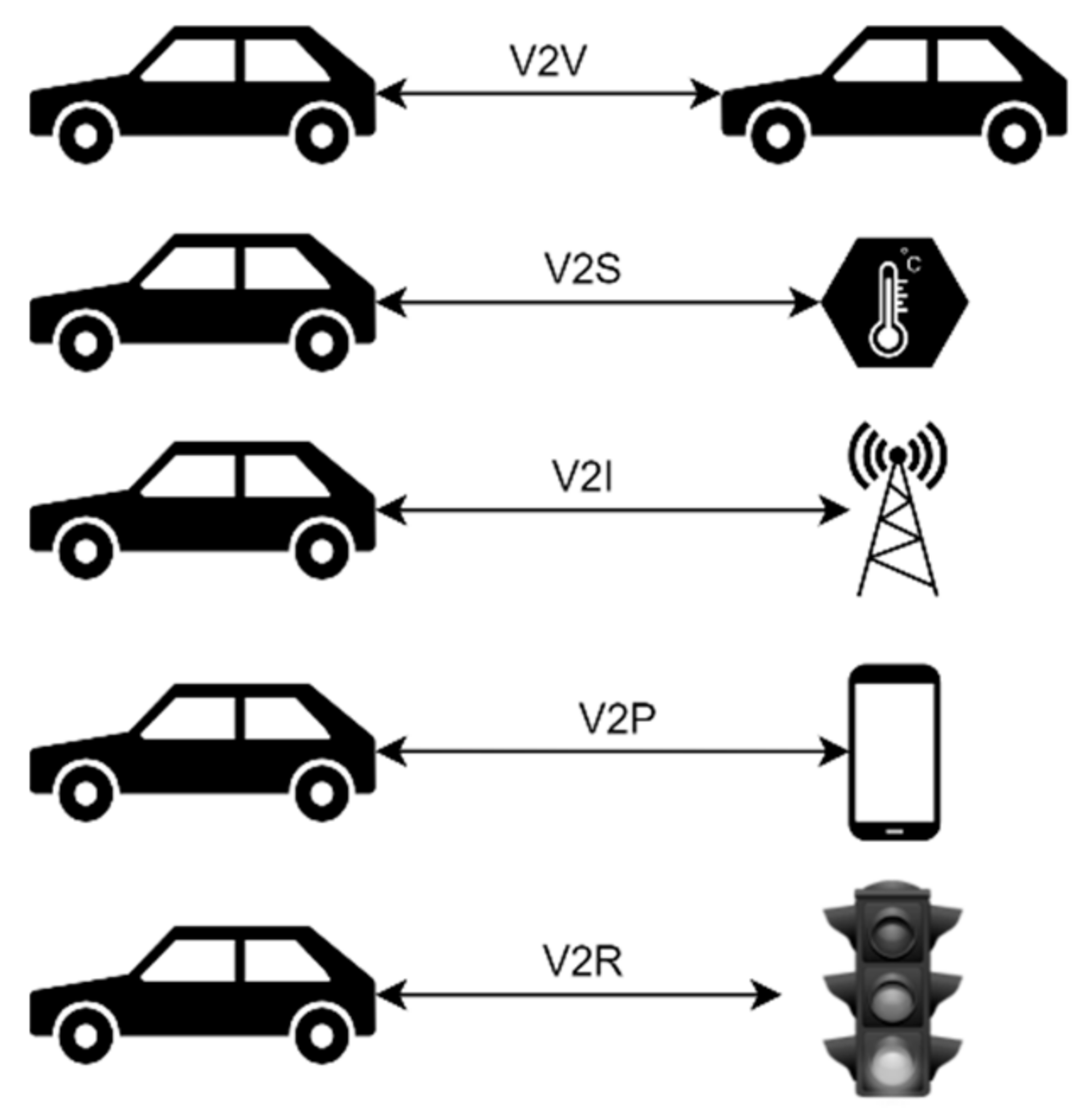
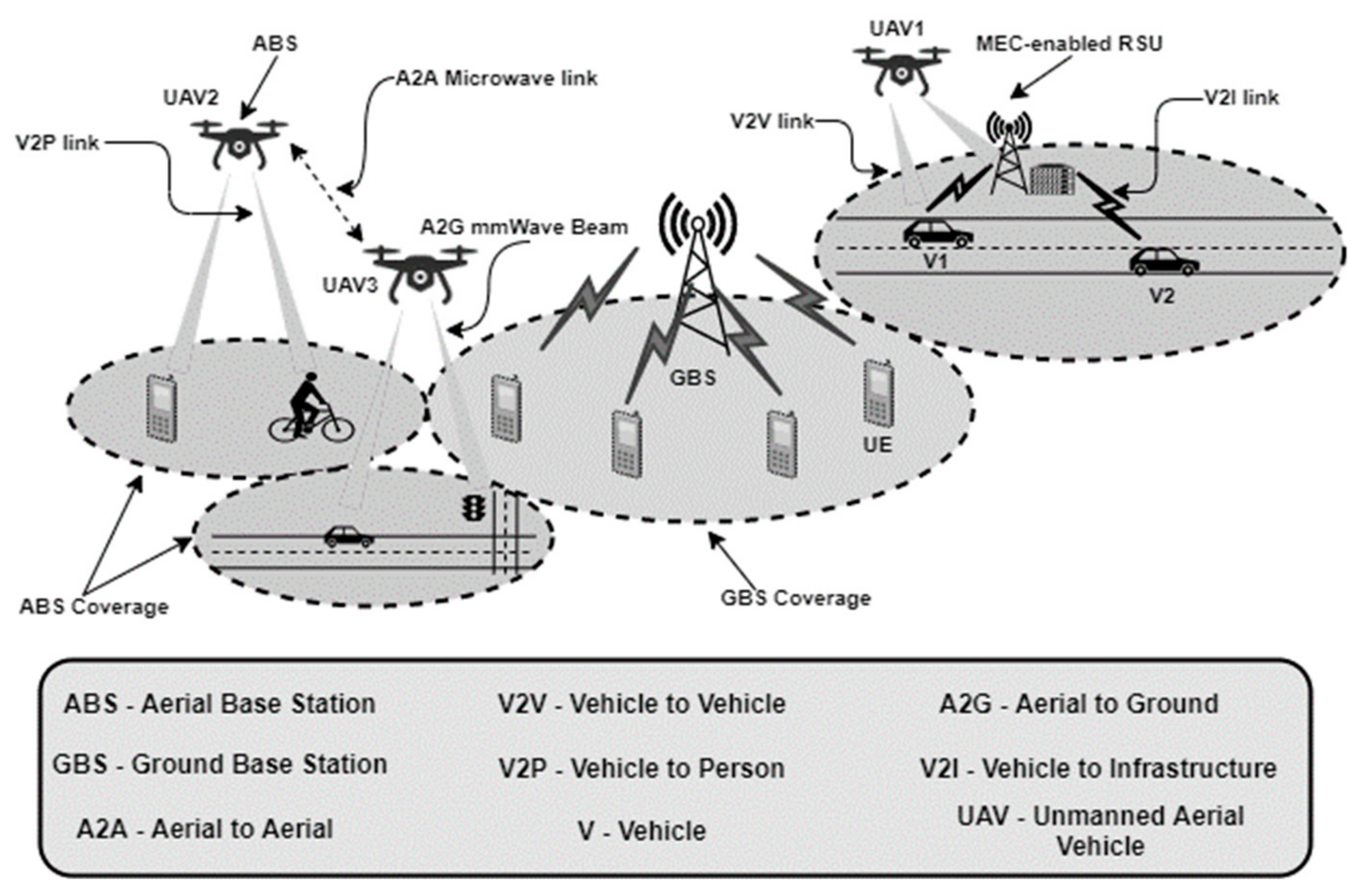
- Communication layer is responsible for the wireless connections between entities in various vehicle-to-everything (V2X) modes (see Figure 1).
- Data processing layer is responsible for holding statistics tools and storage (acts as the IoV network’s intelligence and provides big data processing to vehicles, providing decision making in risk situations).
2.2.2. Four-Layer Architecture
- End-point layer, which is responsible for the vehicles (and sensors), V2V communications, and software.
- Infrastructure layer, which handles all communication technologies used by entities.
- Operation layer, responsible for policy enforcement and flow-based management of network providers.
- Service layer that handles the services offered by the cloud infrastructure that is connected to the network.
2.2.3. Five-Layer Architecture
- Perception layer that handles data gathering, data digitization, and transmission, and energy optimization at lower layers.
- The coordination layer is not only responsible for transferring data to the artificial intelligence (AI) layer in a secure manner but also being responsible for dealing with the heterogeneity of the network structure, unifying received information.
- The artificial intelligence layer holds the cloud infrastructure, which stores, processes, and analyzes the data from layers below, utilizing this analysis for decision making while also managing cloud systems’ services.
- The application layer is responsible for providing intelligent services to end-users, based on the processed and analyzed information of the AI layer, which serves for service discovery from smart applications.
- Business layer, a novelty from the last two architectures, which is responsible for giving foresight on the development of business models, based on data analysis and statistics, which come from the application layer and is later transformed by analysis tools, while utilizing decision making for budgeting and optimization usage of resources.
2.2.4. Seven-Layer Architecture
- Processing layer that, as the name suggests, is responsible for big data processing using various cloud computing technologies, which helps develop strategies for business models.
- The control and management layer manages the network service providers in IoV, utilizing policies and functions for that objective.
- The communication layer is responsible for selecting the best network to serve the needs of the user.
- The data filter and pre-processing layer analyze data to avoid network congestion by the transmission of irrelevant information.
- The data acquisition layer collects data from their respective sources (i.e., sensors, infrastructure connection points, other vehicles).
- The user interface layer is responsible for dealing with how the information is passed from the vehicle and sensors to the driver and users inside the car.
- Finally, the Security layer, transversal to the six ones noted before, and is one of the major differences between this architecture and the first two presented before, being responsible for all security properties guaranteed, using proposed solutions to mitigate the damage from cyberattacks and malfunctions.
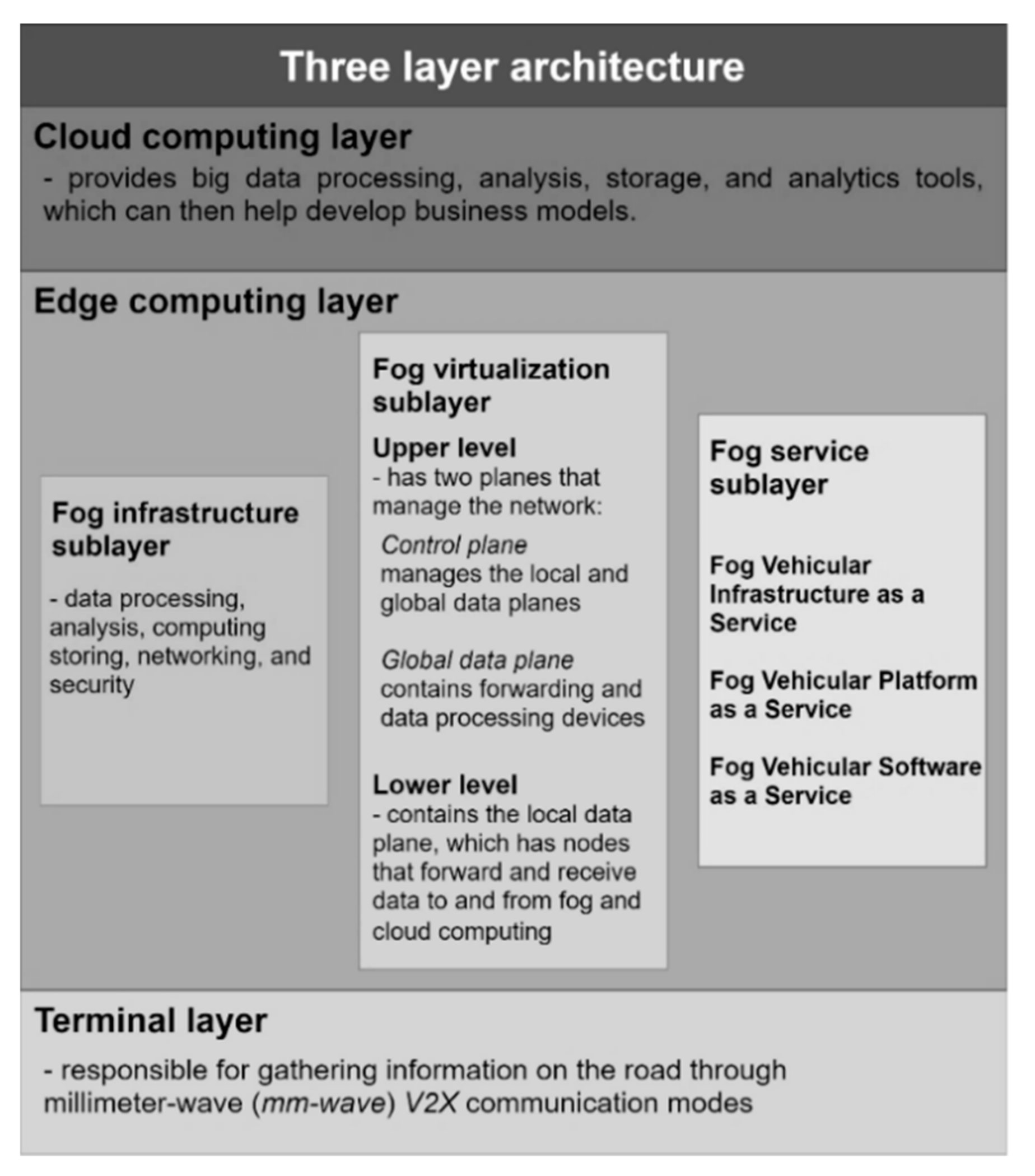
2.2.5. Comparison
- Terminal layer (or IoV layer) that is responsible for gathering information on the road through millimeter-wave (mm-wave) V2X communication modes (mm-wave is a new 5G network technique that can promise multigigabit communication services [17]).
- Edge computing layer that has:
- ○
- Fog infrastructure sublayer that is responsible for data processing, analysis, computing storing, networking, and security.
- ○
- Fog virtualization sublayer, which is further divided in:
- ▪
- the upper level has two planes that manage the network (control plane that manages the local and global data planes and provides programmability and flexible management, and global data plane that contains forwarding and data processing devices).
- ▪
- the lower level contains the local data plane, which has nodes that forward and receive data to and from fog and cloud computing.
- ○
- Fog service sublayer which offers traditional fog services adapted to IoV, such as:
- ▪
- Fog Vehicular Infrastructure as a Service (offers data processing, storage, and analysis while having the capability of adopting another infrastructure to serve other needs).
- ▪
- Fog Vehicular Platform as a Service (offers different operational systems and computational environments to ensure the fulfillment of the heterogeneous needs of drivers and vehicles).
- ▪
- Fog Vehicular Software as a Service (offers fog-based software divided into user applications and safety applications, which is be explained below).
- The cloud computing layer provides services similar to the latter four mentioned architectures: big data processing, analysis, storage, and analytics tools, which can then help develop business models.
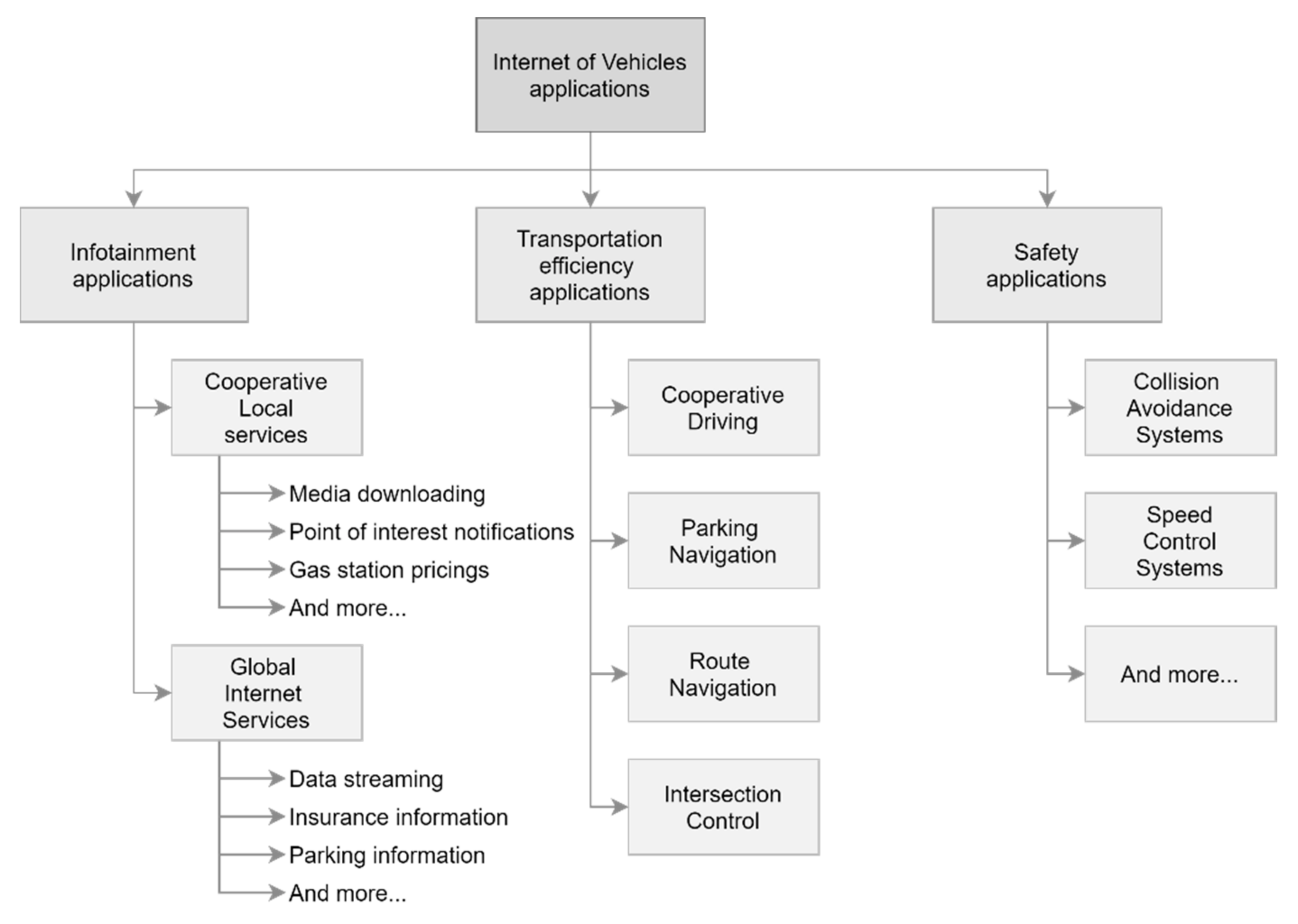
2.3. Applications
2.3.1. Taxonomy
- cooperative local services—relates to infotainment from local-based services (i.e., point of interest notification and media downloading).
- global internet services—relates to data obtained from services like insurance management and parking zone information, which are constantly updated.
- collision warning—warns the driver that a collision is about to occur, and it can also warn when a collision happened down the road to prevent congestion.
- driver assistance—controls the car for steady-state or emergency intervention (e.g., braking before a collision).
- intersection control is the biggest research area in efficiency solutions. These applications aim at controlling traffic at intersections, which requires complex solutions to reduce waiting time and retain fairness. They can be split into two types of approaches:
- ○
- traffic-light-based applications schedule traffic lights based on traffic volume with V2V (the cluster of vehicles at the intersection makes decisions) or V2I (a controller makes the decisions) communication approaches.
- ○
- non-traffic-light-based applications apply maneuver manipulation, controlled by the intersection controller, to drive on the intersection or vehicle scheduling algorithms.
- route navigation, also known as vehicular network-based navigation, it is investigated to avoid the negatives of using GPS-based approaches. It utilizes parameters such as real-time traffic information, fuel consumption, speed, and road condition data, among others, to choose the best route for the vehicle.
- cooperative driving applications that aim at coordinating a group of vehicles, so they drive in the same way as one. This improves energy efficiency, traffic flow and helps prevent accidents.
- parking navigation applications that use algorithms to track optimal routes that lead to the closest available parking zones.
2.3.2. Social Internet of Vehicles
2.4. Main Challenges
2.4.1. Standardization
2.4.2. Resource Constraints
2.4.3. Service Management
2.4.4. Node Mobility
2.4.5. Scalability
2.4.6. Data Dissemination, Routing, and Management
2.4.7. Security
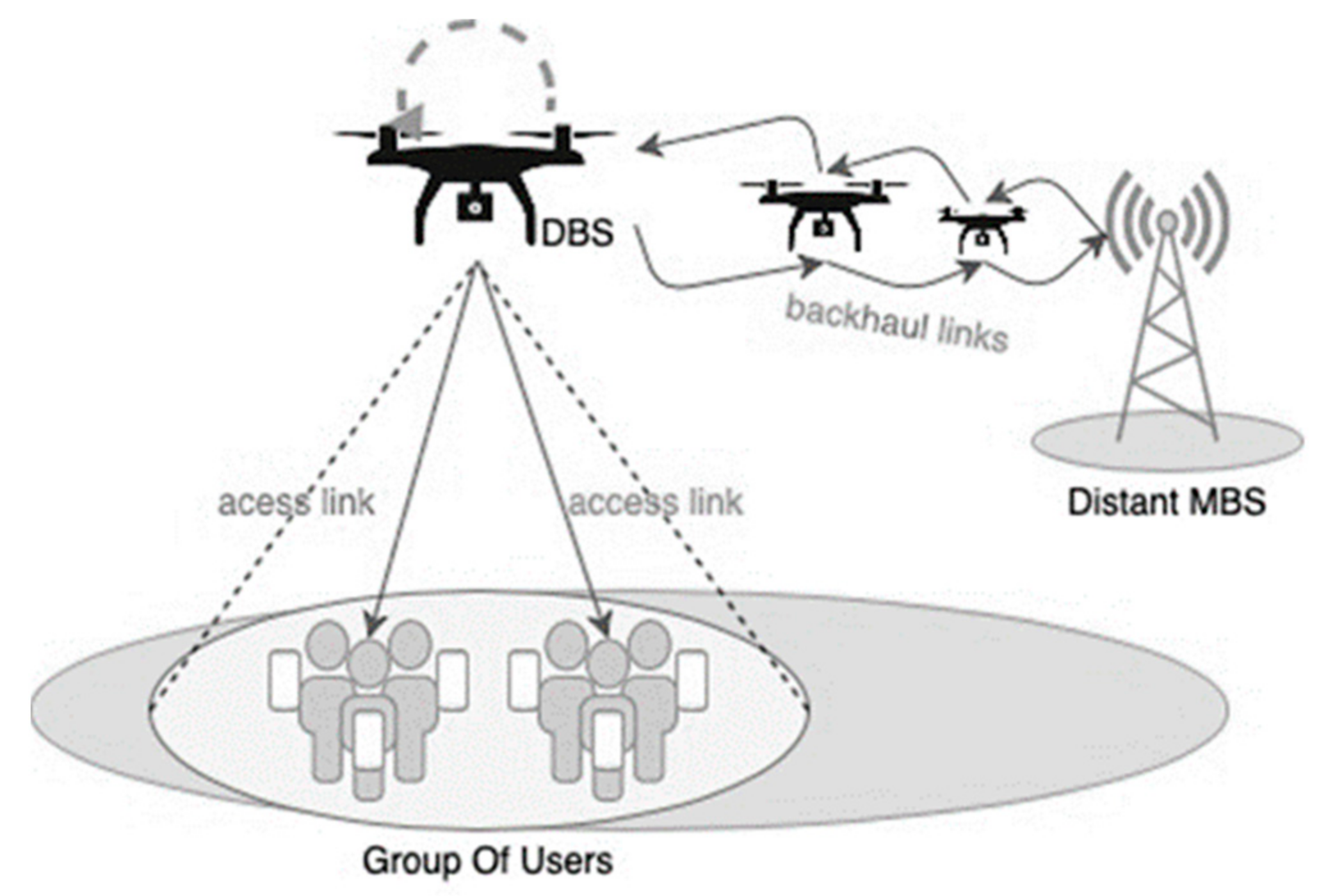
2.5. The UAV and the Smart City Paradigm
2.5.1. UAV
- Drones can move immediately, in real-time, to provide dynamic coverage according to necessity. This makes the overall connectivity robust as they can change as the environment does too.
- As the deployment is through the air, it is not necessary to rent sites. Moreover, costs related to cables, towers will diminish or simply be non-existent.
- Line-of-Sight (LoS) is one reliable communication among the possible types of connections since both transmitter and receiver are aligned, and the connection is direct. LoS’ connections are much easier through open space where drones are supposed to be. So, reliable connections, at least at a certain level, would be possible even inside cities.
- UAV swarms is a novel multi-purpose technique to provide services. A connected swarm can guarantee ubiquitous connectivity to end-users on the ground. In a nutshell, end-users benefit from higher data rates with lower latency, and providers can lower their costs and raise profits simultaneously.
2.5.2. Smart Cities
- Smart Living—any individual should be able to have quality health conditions, safety, and cultural and educational access, also good accessibility in its housings.
- Smart Mobility—any individual should be able to access its territory from local to a national scope. Intelligent Transportation Systems intermediate these accesses so that they can be made safely and sustainably.
- Smart Environment—any smart city should deliver good land use planning, reasonable pollution control, proper natural resource usage.
- Smart Economy—any smart city should promote local product use (local economy), incentivize entrepreneurship, and innovation culture based on e-services.
- Smart People—any individual should be invited to incorporate life-long learning precepts, social and ethnic diversity precepts, community and creativity sense, and a citizen-level awareness.
- Smart Governance—any smart city should be governed with transparent, public decisions and have public and social services.
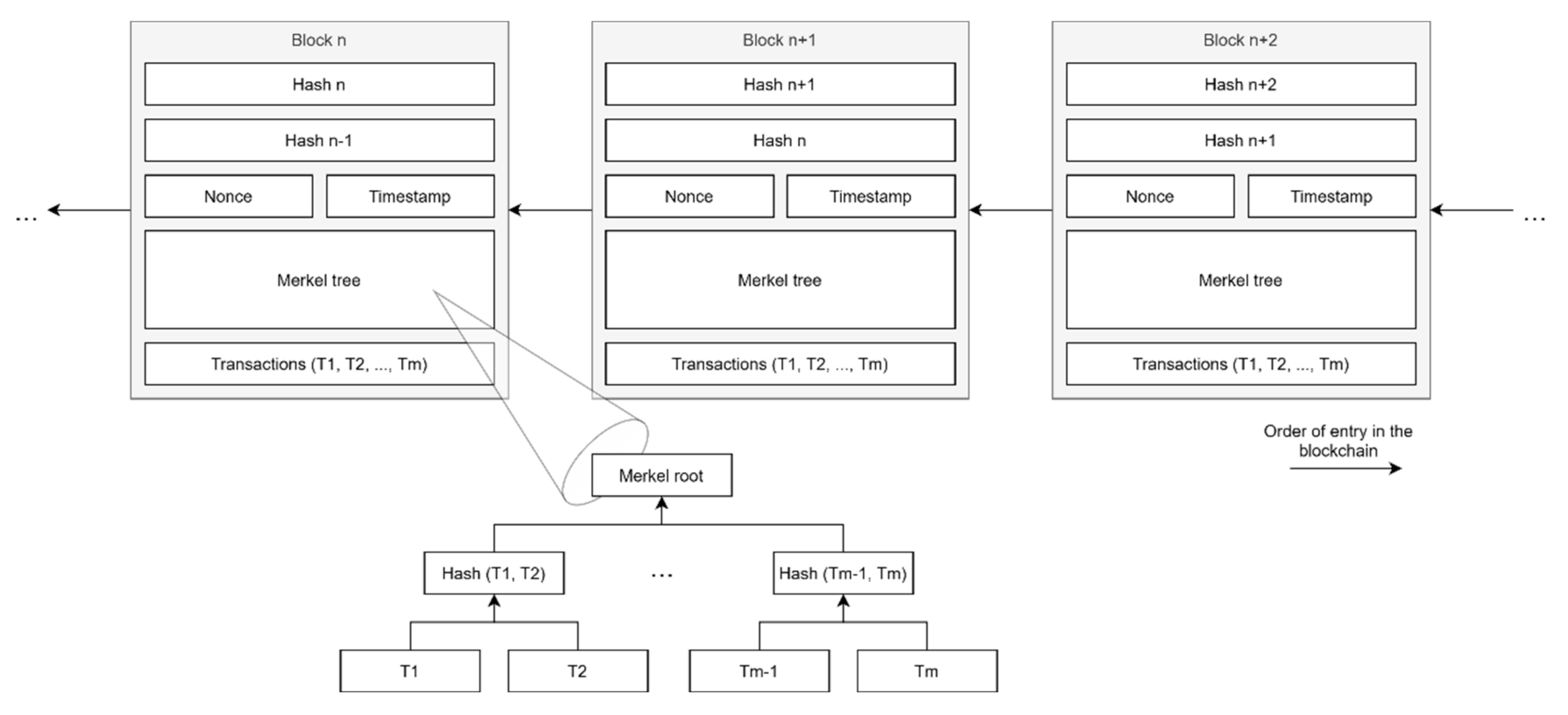
3. Blockchain
3.1. Definition
- its hash,
- the hash of the previously added block,
- a timestamp,
- a nonce (for calculations),
- the number of transactions,
- a Merkel tree of transactions.
3.1.1. Merkel Tree
3.1.2. Chain Forks/Discrepancy
3.2. Technologies
3.2.1. Cryptography
3.2.2. Consensus Protocols
Proof-of-Work
Proof-of-Stake
Byzantine Fault Tolerance
Proof-of-Activity
Proof-of-Burn
Proof-of-Elapsed-Time
Proof of Capacity
Proof of Authority
Proof of Importance
Proof of Luck
Proof of Exercise
3.2.3. Smart Contracts
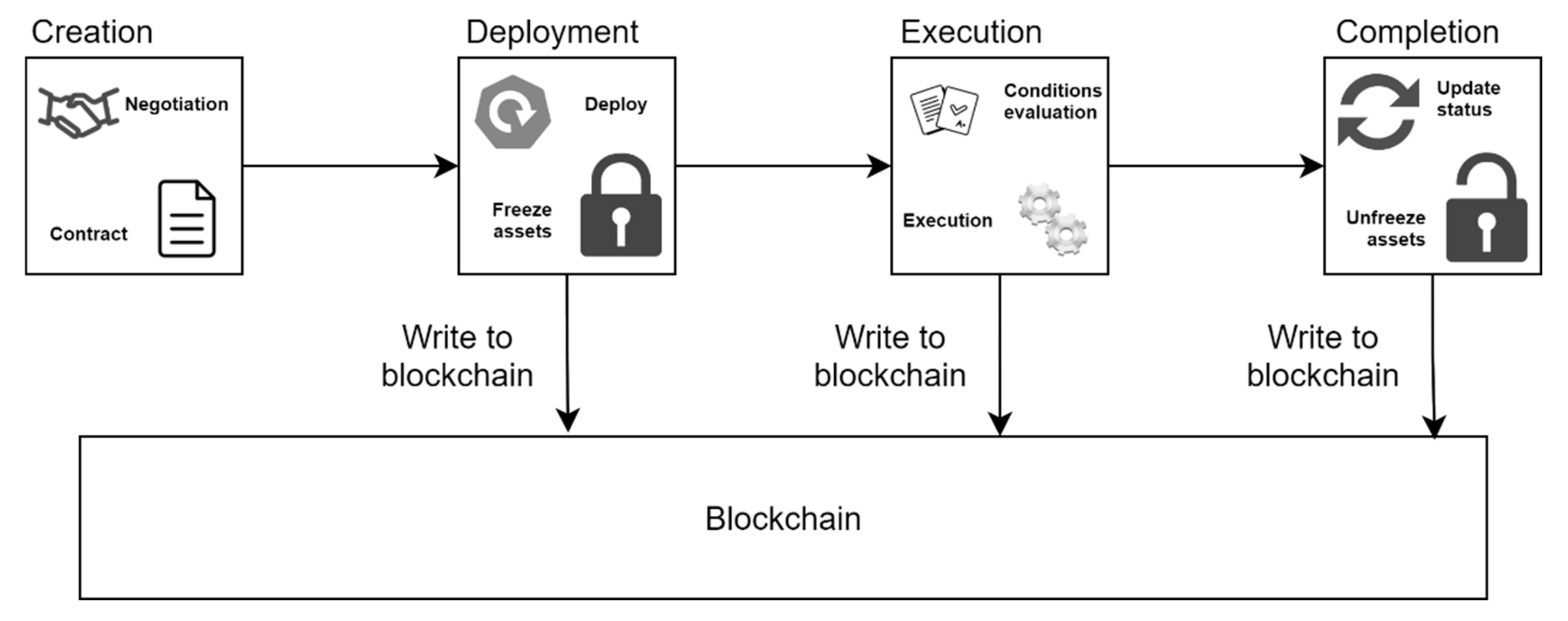
- Creation:
- Negotiation of obligations, prohibitions, and rights.
- It is an iterative process with multiple rounds until an agreement is reached.
- Deployment:
- Deployed to platforms on top of Blockchains.
- Digital assets of involving parties are locked.
- A new contract has to be created for emendations due to the immutability property of Blockchains.
- Execution:
- Automatically executed when the previously negotiated conditions are met.
- Resulting transactions and updates are stored in the Blockchain.
- Completion:
- Every transaction has been completed, and the currency has been transferred/removed to/from the involving wallets.
- The digital assets are unlocked and available for other transactions.
3.3. Benefits and Challenges
Types of Blockchain
3.4. Applications
3.4.1. Finance
3.4.2. Healthcare
3.4.3. Governance
3.4.4. Business and Industry
3.4.5. Internet of Things
3.4.6. Other Areas
4. Blockchain-Based Solutions on the Internet of Vehicles
5. UAV-Assisted IoV and Blockchain Solutions for Smart Cities
5.1. Coordinated UAV Services
5.2. Decentralized Storage
5.3. Blockchain-Based UAV Network for Mobile Edge Computing
6. Tools
6.1. Network Simulators
6.1.1. MATLAB/Simulink
6.1.2. NS-2
6.1.3. NS-3
6.1.4. NCTUns
6.1.5. Veins
6.1.6. Summary
6.2. Blockchain Platforms
6.2.1. Hyperledger
Hyperledger Besu
Hyperledger Burrow
Hyperledger Fabric
Hyperledger Iroha
Hyperledger Sawtooth
6.2.2. Ethereum
6.2.3. Corda
6.2.4. Tezos
7. Challenges and Open Issues
- Real-life physics (aerodynamics, weather),
- Technology development (sensors, actuators, types of engines, blades, wings),
- Policy and laws (compliances, regulations, licensing),
- Energy management (computing, engines versus battery),
- Computing,
- Standardization (protocols, services, networks, and data).
8. Future Perspectives
9. Conclusions
Author Contributions
Funding
Institutional Review Board Statement
Informed Consent Statement
Data Availability Statement
Conflicts of Interest
References
- Eze, E.C.; Zhang, S.; Liu, E. Vehicular ad hoc networks (VANETs): Current state, challenges, potentials and way forward. In Proceedings of the 2014 20th International Conference on Automation and Computing, Cranfield, UK, 12–13 September 2014. [Google Scholar] [CrossRef]
- Singh, A.; Gaba, L.; Sharma, A. Internet of Vehicles: Proposed Architecture, Network Models, Open Issues and Challenges. In Proceedings of the 2019 Amity International Conference on Artificial Intelligence AICAI 2019, Dubai, United Arab Emirates, 4–6 February 2019; pp. 632–636. [Google Scholar] [CrossRef]
- Benalia, E.; Bitam, S.; Mellouk, A. Data dissemination for Internet of vehicle based on 5G communications: A survey. Trans. Emerg. Telecommun. Technol. 2020, 31, e3881. [Google Scholar] [CrossRef]
- Zhang, T. Cisco Confidential Challenges and Opportunities. 2015. Available online: https://site.ieee.org/denver-com/files/2016/02/IoV-Security-Challenges-and-Opportunities-zhang.pdf (accessed on 10 November 2020).
- Zanella, A.; Bui, N.; Castellani, A.; Vangelista, L.; Zorzi, M. Internet of Things for Smart Cities. IEEE Internet Things J. 2014, 1, 22–32. [Google Scholar] [CrossRef]
- Nakamoto, S. Bitcoin: A Peer-to-Peer Electronic Cash System; Satoshi Nakamoto Institute, 2008; Available online: https://bitcoin.org/bitcoin.pdf (accessed on 18 November 2020).
- Mollah, M.B.; Zhao, J.; Niyato, D.; Guan, Y.L.; Yuen, C.; Sun, S.; Lam, K.; Koh, L.H. Blockchain for the Internet of Vehicles towards Intelligent Transportation Systems: A Survey. IEEE Internet Things J. 2020, 8, 4157–4185. [Google Scholar] [CrossRef]
- Skiba, D.J. The Internet of Things: A study in Hype, Reality, Disruption, and Growth. Nurs. Educ. Perspect. 2014, 34, 63–64. Available online: http://www.ncbi.nlm.nih.gov/pubmed/23586210 (accessed on 15 October 2020).
- Davis, G. 2020: Life with 50 billion connected devices. In Proceedings of the 2018 IEEE International Conference on Consumer Electronics (ICCE), Las Vegas, NV, USA, 12–14 January 2018. [Google Scholar] [CrossRef]
- Kaiwartya, O.; Abdullah, A.H.; Cao, Y.; Altameem, A.; Prasad, M.; Lin, C.; Liu, X. Internet of Vehicles: Motivation, Layered Architecture, Network Model, Challenges, and Future Aspects. IEEE Access 2016, 4, 5356–5373. [Google Scholar] [CrossRef]
- Contreras-Castillo, J.; Zeadally, S.; Guerrero-Ibanez, J.A. Internet of Vehicles: Architecture, Protocols, and Security. IEEE Internet Things J. 2018, 5, 3701–3709. [Google Scholar] [CrossRef]
- Islam, A.; Hossan, M.T.; Jang, Y.M. Introduction of optical camera communication for Internet of vehicles (IoV). In Proceedings of the International Conference on Ubiquitous and Future Networks, ICUFN, Porto, Portugal, 29 June–2 July 2017; pp. 122–125. [Google Scholar] [CrossRef]
- Yang, F.; Wang, S.; Li, J.; Liu, Z.; Sun, Q. An overview of Internet of Vehicles. China Commun. 2014, 11, 1–15. [Google Scholar] [CrossRef]
- Meeting, W.G. White Paper of Internet of Vehicles (IoV). In Proceedings of the 50th Telecommunications and Information Working Group Meeting, Brisbane, Australia, 29 September–3 October 2014. [Google Scholar]
- Nanjie, L. Internet of Vehicles: Your Next Connection. 2011. Available online: https://www.huawei.com/mediafiles/CORPORATE/PDF/Magazine/WinWin/HW_110848.pdf (accessed on 20 October 2020).
- Bonomi, F. The Smart and Connected Vehicle and the Internet of Things. In Invited Talk, Workshop on Synchronization in Telecommunication Systems; 2013. [Google Scholar]
- Feng, W.; Li, Y.; Jin, D.; Su, L.; Chen, S. Millimetre-wave backhaul for 5G networks: Challenges and solutions. Sensors 2016, 16, 892. [Google Scholar] [CrossRef] [PubMed]
- Silva, L.; Magaia, N.; Sousa, B.; Kobusinska, A.; Casimiro, A.; Mavromoustakis, C.X.; Mastorakis, G.; Albuquerque, V.H. Computing Paradigms in Emerging Vehicular Environments: A Review. IEEE CAA J. Autom. Sin. 2021, 8, 491–511. [Google Scholar] [CrossRef]
- Wu, W.; Yang, Z.; Li, K. Internet of Vehicles and applications. In Internet of Things: Principles and Paradigms; Morgan Kaufmann: Burlington, MA, USA, 2016. [Google Scholar]
- Lee, C.H.; Huang, C.M.; Yang, C.C.; Wang, T.H. A cooperative video streaming system over the integrated cellular and DSRC networks. In Proceedings of the 2011 IEEE Vehicular Technology Conference (VTC Fall), San Francisco, CA, USA, 5–8 September 2011. [Google Scholar] [CrossRef]
- Abdelsalam, M.; Bonny, T. IoV Road Safety: Vehicle Speed Limiting System. In Proceedings of the 2019 3rd International Conference on Communications, Signal Processing, and Their Applications, Sharjah, United Arab Emirates, 19–21 March 2019; pp. 1–6. [Google Scholar] [CrossRef]
- Reichardt, D.; Miglietta, M.; Moretti, L.; Morsink, P.; Schulz, W. CarTALK 2000: Safe and comfortable driving based upon inter-vehicle-communication. In Proceedings of the Intelligent Vehicle Symposium, Versailles, France, 17–21 June 2002; pp. 545–550. [Google Scholar] [CrossRef]
- Huang, R.H.; Chang, B.J.; Tsai, Y.L.; Liang, Y.H. Mobile Edge Computing-Based Vehicular Cloud of Cooperative Adaptive Driving for Platooning Autonomous Self Driving. In Proceedings of the 2017 IEEE 7th International Symposium on Cloud and Service Computing (SC2), Kanazawa, Japan, 22–25 November 2017; pp. 32–39. [Google Scholar] [CrossRef]
- Kowshik, H.; Caveney, D.; Kumar, P.R. Provable systemwide safety in intelligent intersections. IEEE Trans. Veh. Technol. 2011, 60, 804–818. [Google Scholar] [CrossRef]
- Wu, W.; Zhang, J.; Luo, A.; Cao, J. For Intersection Traffic Control. IEEE Trans. Parallel Distrib. Syst. 2015, 26, 65–74. Available online: http://www.scopus.com/inward/record.url?eid=2-s2.0-84919485495&partnerID=tZOtx3y1 (accessed on 16 October 2020). [CrossRef]
- Chen, P.Y.; Guo, Y.M.; Chen, W.T. Fuel-saving navigation system in VANETs. In Proceedings of the 2010 IEEE 72nd Vehicular Technology Conference, Ottawa, ON, Canada, 6–9 September 2010. [Google Scholar] [CrossRef]
- Collins, K.; Muntean, G.M. Route-based vehicular traffic management for wireless access in vehicular environments. In Proceedings of the 2008 IEEE 68th Vehicular Technology Conference, Calgary, AB, Canada, 21–24 September 2008; pp. 3–7. [Google Scholar] [CrossRef]
- Alam, K.M.; Saini, M.; El Saddik, A. Toward social internet of vehicles: Concept, architecture, and applications. IEEE Access 2015, 3, 343–357. [Google Scholar] [CrossRef]
- Butt, T.A.; Iqbal, R.; Shah, S.C.; Umar, T. Social Internet of Vehicles: Architecture and enabling technologies. Comput. Electr. Eng. 2018, 69, 68–84. [Google Scholar] [CrossRef]
- Magaia, N.; Fonseca, R.; Muhammad, K.; Segundo, A.H.; Neto, A.V.; Albuquerque, V.H. Industrial Internet of Things Security enhanced with Deep Learning Approaches for Smart Cities. IEEE Internet Things J. 2020, 1–14. [Google Scholar] [CrossRef]
- Al-Fuqaha, A.; Guizani, M.; Mohammadi, M.; Aledhari, M.; Ayyash, M. Internet of Things: A Survey on Enabling Technologies, Protocols, and Applications. IEEE Commun. Surv. Tutor. 2015, 17, 2347–2376. [Google Scholar] [CrossRef]
- Cheng, J.; Cheng, J.; Zhou, M.; Liu, F.; Gao, S.; Liu, C. Routing in internet of vehicles: A review. IEEE Trans. Intell. Transp. Syst. 2015, 16, 2339–2352. [Google Scholar] [CrossRef]
- Magaia, N.; Borrego, C.; Pereira, P.R.; Correia, M. EPRIVO: An enhanced PRIvacy-preserving opportunistic routing protocol for vehicular delay-tolerant networks. IEEE Trans. Veh. Technol. 2018, 67, 11154–11168. [Google Scholar] [CrossRef]
- Mokhtar, B.; Azab, M. Survey on Security Issues in Vehicular Ad Hoc Networks. Alex. Eng. J. 2015, 54, 1115–1126. [Google Scholar] [CrossRef]
- Sharma, S.; Kaushik, B. A survey on internet of vehicles: Applications, security issues & solutions. Veh. Commun. 2019, 20, 100182. [Google Scholar] [CrossRef]
- Mehta, P.; Gupta, R.; Tanwar, S. Blockchain envisioned UAV networks: Challenges, solutions, and comparisons. Comput. Commun. 2020, 151, 518–538. [Google Scholar] [CrossRef]
- Li, B.; Fei, Z.; Zhang, Y. UAV Communications for 5G and Beyond: Recent Advances and Future Trends. IEEE Internet Things J. 2019, 6, 2241–2263. [Google Scholar] [CrossRef]
- Zeng, Y.; Wu, Q.; Zhang, R. Accessing From the Sky: A Tutorial on UAV Communications for 5G and Beyond. Proc. IEEE 2019, 107, 2327–2375. [Google Scholar] [CrossRef]
- Feng, W.; Wang, J.; Chen, Y.; Wang, X.; Ge, N.; Lu, J. UAV-aided MIMO communications for 5g internet of things. IEEE Internet Things J. 2019, 6, 1731–1740. [Google Scholar] [CrossRef]
- Shi, W.; Zhou, H.; Li, J.; Xu, W.; Zhang, N.; Shen, X. Drone Assisted Vehicular Networks: Architecture, Challenges and Opportunities. IEEE Netw. 2018, 32, 130–137. [Google Scholar] [CrossRef]
- Founon, A.; Hayar, A. Evaluation of the concept of the smart city through local regulation and the importance of local initiative. In Proceedings of the 2018 IEEE International Smart Cities Conference (ISC2), Kansas City, MO, USA, 16–19 September 2018; pp. 1–6. [Google Scholar] [CrossRef]
- Wang, H.; Zheng, Z.; Xie, S.; Dai, H.N.; Chen, X. Blockchain challenges and opportunities: A survey. Int. J. Web Grid Serv. 2018, 14, 352. [Google Scholar] [CrossRef]
- Dai, H.N.; Zheng, Z.; Zhang, Y. Blockchain for Internet of Things: A Survey. IEEE Internet Things J. 2019. [Google Scholar] [CrossRef]
- King, S.; Nadal, S. Ppcoin: Peer-to-Peer Crypto-Currency with Proof-of-Stake. 2012. Available online: https://decred.org/research/king2012.pdf (accessed on 20 November 2020).
- Ferrag, M.A.; Derdour, M.; Mukherjee, M.; Derhab, A.; Maglaras, L.; Janicke, H. Blockchain technologies for the internet of things: Research issues and challenges. IEEE Internet Things J. 2019, 6, 2188–2204. [Google Scholar] [CrossRef]
- Dorri, A.; Steger, M.; Kanhere, S.S.; Jurdak, R. BlockChain: A Distributed Solution to Automotive Security and Privacy. IEEE Commun. Mag. 2017, 55, 119–125. [Google Scholar] [CrossRef]
- Nguyen, C.T.; Hoang, D.T.; Nguyen, D.N.; Niyato, D.; Nguyen, H.T.; Dutkiewicz, E. Proof-of-Stake Consensus Mechanisms for Future Blockchain Networks: Fundamentals, Applications and Opportunities. IEEE Access 2019, 7, 85727–85745. [Google Scholar] [CrossRef]
- Bach, L.M.; Mihaljevic, B.; Zagar, M. Comparative analysis of blockchain consensus algorithms. In Proceedings of the 2018 41st International Convention on Information and Communication Technology, Electronics and Microelectronics (MIPRO), Opatija, Croatia, 21–25 May 2018. [Google Scholar] [CrossRef]
- Leased Proof of Stake|Waves Documentation. Available online: https://docs.waves.tech/en/blockchain/leasing#leasing-benefits-for-the-node-owner (accessed on 11 November 2020).
- Castro, M.; Liskov, B. Practical Byzantine Fault Tolerance and proactive recovery. ACM Trans. Comput. Syst. 2002, 20. [Google Scholar] [CrossRef]
- Buchman, E. Tendermint: Byzantine Fault Tolerance in the Age of Blockchains. Ph.D. Thesis, The University of Guelph, Guelph, ON, Canada, 2016. [Google Scholar]
- dBFT 2.0 Algorithm. Available online: https://docs.neo.org/docs/en-us/tooldev/consensus/consensus_algorithm.html (accessed on 11 November 2020).
- Bentov, I.; Lee, C.; Mizrahi, A.; Rosenfeld, M. Proof of activity: Extending bitcoin’s proof of work via proof of stake [extended abstract]. ACM Sigmetrics Perform. Eval. Rev. 2014, 42, 34–37. [Google Scholar] [CrossRef]
- Proof of Burn—Bitcoin Wiki. Available online: https://en.bitcoin.it/wiki/Proof_of_burn (accessed on 11 November 2020).
- P4Titan. Slimcoin: A Peer-to-Peer Crypto-Currency with Proof-of-Burn. Whitepaper. 2014. Available online: https://slimcoin.info/whitepaperSLM.pdf (accessed on 20 November 2020).
- Karantias, K.; Kiayias, A.; Zindros, D. Proof-of-Burn. In Financial Cryptography and Data Security; Springer: Cham, Switzerland, 2020. [Google Scholar] [CrossRef]
- Chen, L.; Xu, L.; Shah, N.; Gao, Z.; Lu, Y.; Shi, W. On security analysis of proof-of-elapsed-time (PoET). In Stabilization, Safety, and Security of Distributed Systems; Lecture Notes in Computer Science; Springer: Cham, Switzerland, 2017; pp. 282–297. [Google Scholar] [CrossRef]
- Tschorsch, F.; Scheuermann, B. Bitcoin and beyond: A technical survey on decentralized digital currencies. IEEE Commun. Surv. Tutor. 2016, 18, 2084–2123. [Google Scholar] [CrossRef]
- De Angelis, S.; Aniello, L.; Baldoni, R.; Lombardi, F.; Margheri, A.; Sassone, V. PBFT vs proof-of-authority: Applying the CAP theorem to permissioned blockchain. In Proceedings of the Italian Conference on Cyber Security, Milan, Italy, 6–9 February 2018; Volume 2058, pp. 1–11. [Google Scholar]
- What Is POI|NEM Documentation. Available online: https://docs.nem.io/en/gen-info/what-is-poi (accessed on 12 November 2020).
- Milutinovic, M.; He, W.; Wu, H.; Kanwal, M. Proof of luck: An efficient blockchain consensus protocol. arXiv 2017, arXiv:1703.05435. [Google Scholar] [CrossRef]
- Shoker, A. Sustainable blockchain through proof of exercise. In Proceedings of the 16th IEEE International Symposium on Network Computing and Applications NCA 2017, Cambridge, MA, USA, 30 October–1 November 2017; pp. 1–9. [Google Scholar] [CrossRef]
- Christidis, K.; Devetsikiotis, M. Blockchains and Smart Contracts for the Internet of Things. IEEE Access 2016, 4, 2292–2303. [Google Scholar] [CrossRef]
- Croman, K.; Decker, C.; Eyal, I.; Gencer, A.E.; Juels, A.; Kosba, A.; Miller, A.; Saxena, P.; Shi, E.; Sirer, E.G.; et al. On Scaling Decentralized Blockchains Initiative for CryptoCurrencies and Contracts (IC3). In Proceedings of the 3rd Workshop on Bitcoin and Blockchain Research, Accra Beach Hotel & Spa, Barbados, 16–26 February 2016; pp. 106–125. Available online: http://fc16.ifca.ai/bitcoin/papers/CDE+16.pdf (accessed on 15 November 2020).
- Casino, F.; Dasaklis, T.K.; Patsakis, C. A systematic literature review of blockchain-based applications: Current status, classification and open issues. Telemat. Inform. 2019, 36, 55–81. [Google Scholar] [CrossRef]
- Tama, B.A.; Kweka, B.J.; Park, Y.; Rhee, K.H. A critical review of blockchain and its current applications. In Proceedings of the ICECOS 2017—International Conference on Electrical Engineering and Computer Science, Sustaining the Cultural Heritage toward the Smart Environment for Better Future, Palembang, Indonesia, 22–23 August 2017; pp. 109–113. [Google Scholar] [CrossRef]
- Di Francesco Maesa, D.; Mori, P. Blockchain 3.0 applications survey. J. Parallel Distrib. Comput. 2020, 138, 99–114. [Google Scholar] [CrossRef]
- Nguyen, Q.K. Blockchain-A Financial Technology for Future Sustainable Development. In Proceedings of the 2016 3rd International Conference on Green Technology and Sustainable Development (GTSD), Kaohsiung, Taiwan, 24–25 November 2016. [Google Scholar] [CrossRef]
- Mettler, M. Blockchain technology in healthcare: The revolution starts here. In Proceedings of the 2016 IEEE 18th International Conference on e-Health Networking, Applications and Services (Healthcom), Munich, Germany, 14–16 September 2016. [Google Scholar] [CrossRef]
- Ekblaw, A.; Azaria, A.; Halamka, J.D.; Lippman, A.; Vieira, T. A Case Study for Blockchain in Healthcare: ‘MedRec’ prototype for electronic health records and medical research data. Proc. IEEE Open Big Data Conf. 2016, 13, 13. [Google Scholar]
- The Secure Mobile Voting Platform of The Future—Follow My Vote. Available online: https://followmyvote.com/ (accessed on 16 November 2020).
- Rockwell, M. BitCongress—Blockchain Based Voting System. Ethereum. 2014. Available online: https://forum.ethereum.org/discussion/110/bitc%20ongress-blockchain-based-voting-system (accessed on 25 November 2020).
- Walmart Blockchain Pilot Aims to Make China’s Pork Market Safer—CoinDesk. Available online: https://www.coindesk.com/walmart-blockchain-pilot-china-pork-market (accessed on 16 November 2020).
- Mengelkamp, E.; Notheisen, B.; Beer, C.; Dauer, D.; Weinhardt, C. A blockchain-based smart grid: Towards sustainable local energy markets. Comput. Sci. Res. Dev. 2018, 33, 207–214. [Google Scholar] [CrossRef]
- Han, T.; Ribeiro, I.; Magaia, N.; Preto, J.; Segundo, A.H.; Macêdo, A.R.; Muhammad, K.; Albuquerque, V.H. Emerging Drone Trends for Blockchain-Based 5G Networks: Open Issues and Future Perspectives. IEEE Netw. 2021, 35, 38–43. [Google Scholar] [CrossRef]
- Rathee, G.; Sharma, A.; Iqbal, R.; Aloqaily, M.; Jaglan, N.; Kumar, R. A blockchain framework for securing connected and autonomous vehicles. Sensors 2019, 19, 3165. [Google Scholar] [CrossRef]
- Wang, X.; Zeng, P.; Patterson, N.; Jiang, F.; Doss, R. An improved authentication scheme for internet of vehicles based on blockchain technology. IEEE Access 2019, 7, 45061–45072. [Google Scholar] [CrossRef]
- Gao, J.; Agyekum, K.; Sifah, E.; Acheampong, K.; Xia, Q.; Du, X.; Guizani, M.; Xia, H. A Blockchain-SDN-Enabled Internet of Vehicles Environment for Fog Computing and 5G Networks. IEEE Internet Things J. 2020, 7, 4278–4291. [Google Scholar] [CrossRef]
- Kamal, M.; Srivastava, G.; Tariq, M. Blockchain-Based Lightweight and Secured V2V Communication in the Internet of Vehicles. IEEE Trans. Intell. Transp. Syst. 2020, 1–8. [Google Scholar] [CrossRef]
- Technology, C. MICAz: Wireless Measurement System. Prod. Datasheet 2008, 4–5. Available online: http://courses.ece.ubc.ca/494/files/MICAz_Datasheet.pdf (accessed on 27 November 2020).
- Alladi, T.; Chamola, V.; Sahu, N.; Guizani, M. Applications of blockchain in unmanned aerial vehicles: A review. Veh. Commun. 2020, 23, 100249. [Google Scholar] [CrossRef]
- Orecchini, F.; Santiangeli, A.; Zuccari, F.; Pieroni, A.; Suppa, T. Blockchain Technology in Smart City: A New Opportunity for Smart Environment and Smart Mobility. In Intelligent Computing & Optimization; Vasant, P., Zelinka, I., Weber, G.W., Eds.; ICO 2018; Advances in Intelligent Systems and Computing; Springer: Cham, Switzerland, 2018; Volume 866. [Google Scholar] [CrossRef]
- Kota, S.; Giambene, G. Satellite 5G: IoT Use Case for Rural Areas Applications. In Proceedings of the SPACOMM 2019 International Conference on Advances in Satellite and Space Communications, Valencia, Spain, 24–28 March 2019; pp. 7–14. [Google Scholar]
- Lin, X.; Wu, J.; Mumtaz, S.; Garg, S.; Li, J.; Guizani, M. Blockchain-based On-Demand Computing Resource Trading in IoV-Assisted Smart City. IEEE Trans. Emerg. Top. Comput. 2020. [Google Scholar] [CrossRef]
- VANET Toolbox: A Vehicular Network Simulator Based on DES—File Exchange—MATLAB Central. Available online: https://www.mathworks.com/matlabcentral/fileexchange/68437-vanet-toolbox-a-vehicular-network-simulator-based-on-des?s_tid=srchtitle (accessed on 19 November 2020).
- 5G Toolbox Documentation. Available online: https://www.mathworks.com/help/5g/index.html (accessed on 19 November 2020).
- LTE Toolbox Documentation. Available online: https://www.mathworks.com/help/lte/index.html (accessed on 19 November 2020).
- WLAN Toolbox Documentation. Available online: https://www.mathworks.com/help/wlan/index.html (accessed on 18 November 2020).
- The Network Simulator—ns-2. Available online: https://www.isi.edu/nsnam/ns/ (accessed on 18 November 2020).
- ns-3|A Discrete-Event Network Simulator for Internet Systems. Available online: https://www.nsnam.org/ (accessed on 18 November 2020).
- EstiNet Network Simulator and Emulator (NCTUns). Available online: http://nsl.cs.nctu.edu.tw/NSL/nctuns.html (accessed on 18 November 2020).
- Veins. Available online: https://veins.car2x.org/ (accessed on 18 November 2020).
- OMNeT++ Discrete Event Simulator. Available online: https://omnetpp.org/ (accessed on 18 November 2020).
- SUMO Documentation. Available online: https://sumo.dlr.de/docs/ (accessed on 18 November 2020).
- Announcing Hyperledger Besu—Hyperledger. Available online: https://www.hyperledger.org/blog/2019/08/29/announcing-hyperledger-besu (accessed on 18 November 2020).
- Hyperledger Burrow—Hyperledger. Available online: https://www.hyperledger.org/use/hyperledger-burrow (accessed on 18 November 2020).
- Hyperledger Fabric—Hyperledger. Available online: https://www.hyperledger.org/use/fabric (accessed on 18 November 2020).
- Hyperledger Iroha—Hyperledger. Available online: https://www.hyperledger.org/use/iroha (accessed on 18 November 2020).
- Hyperledger Sawtooth—Hyperledger. Available online: https://www.hyperledger.org/use/sawtooth (accessed on 18 November 2020).
- Ethereum Whitepaper|ethereum.org. Available online: https://ethereum.org/en/whitepaper/#ethereum (accessed on 18 November 2020).
- How does Ethereum Work, Anyway? Introduction|by Preethi Kasireddy|Medium. Available online: https://medium.com/@preethikasireddy/how-does-ethereum-work-anyway-22d1df506369 (accessed on 18 November 2020).
- Home|Corda Documentation. Available online: https://docs.corda.net/ (accessed on 18 November 2020).
- Tezos|Get Started. Available online: https://tezos.com/get-started/ (accessed on 18 November 2020).
- Magaia, N.; Sheng, Z. ReFIoV: A novel reputation framework for information-centric vehicular applications. IEEE Trans. Veh. Technol. 2019, 68, 1810–1823. [Google Scholar] [CrossRef]
| Security Requirement | Description |
|---|---|
| Data authentication | Vehicles identities should be verified when transferring data |
| Data integrity | Sent and received data should be verified to ensure correct data transferal |
| Data confidentiality | Data transmission between vehicles should be secret |
| Access control | Vehicles should be allowed to access services they are entitled to |
| Data non-repudiation | Vehicles should not be able to deny the authenticity of another vehicle |
| Availability | Communication between vehicles should be ensured even under bad conditions in the event of an attack |
| Anti-jamming | Malicious vehicles cannot interrupt communications between other vehicles |
| Impersonation | A vehicle cannot impersonate another entity in the network |
| ID traceability | A vehicle’s identity can be retrieved from sent messages |
| Vehicle privacy/anonymity | Sent messages can only be accessed by authorized vehicles and remote nodes. The vehicle’s identity should be hidden. |
| Property | Type of Blockchain | ||
|---|---|---|---|
| Public | Private | Consortium | |
| Centralization | Decentralized | Centralized | Partially decentralized |
| Transparency | Transparent | Nontransparent | Partially transparent |
| Traceability | Traceable | Traceable | Partially traceable |
| Mutability | Immutable | Mutable | Partially immutable |
| Data Repudiation | Non-refusable | Refusable | Partially refusable |
| Scalability | Low | High | Good |
| Flexibility | Low | High | Good |
| Permission | Permissionless | Permissioned | Permissioned |
| Blockchain Solution | Motivation | Proposed Solution | Evaluation Tools |
|---|---|---|---|
| Rathee et al. [76] | Ensure security, safety, and transparency | Blockchain framework with smart contracts | NS-2, Blockchain platform not specified |
| Wang et al. [77] | Reduce impact of malicious nodes efficiently | Authentication and registration scheme | Veins |
| Gao et al. [78] | Increase performance with new paradigms | Blockchain-SDN-enabled solution with fog computing | MATLAB, NS-3, and Hyperledger Fabric |
| Kamal et al. [79] | Decrease power consumption | Various (lightweight algorithms, lesser complexity) | MICAz motes and MATLAB |
| Blockchain Platform | Type of Networks | Consensus Protocol | Programming Language | Smart Contract Language |
|---|---|---|---|---|
| Hyperledger Besu | Public (Ethereum) and private networks | PoW, PoA, IBFT | Java | Truffle, Remix, web3j (Tools) |
| Hyperledger Burrow | Public (optimal), private, and consortium | BFT (Tendermint algorithm) | Go | Various |
| Hyperledger Fabric | Private | Various (pluggable) | Go | Golang (<1.0)/Javascript (>1.1) |
| Hyperledger Iroha | Private | YAC | C++ | Various |
| Hyperledger Sawtooth | Private | Raft, PBFT, PoET | Various | Various |
| Ethereum | Public | PoW, PoS (2.0) | Various | Solidity, Serpent, LLL |
| Corda | Private | Various (pluggable) | Java | Java |
| Tezos | Public | PoS (delegated) | Various | Various (Michelson) |
Publisher’s Note: MDPI stays neutral with regard to jurisdictional claims in published maps and institutional affiliations. |
© 2021 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Álvares, P.; Silva, L.; Magaia, N. Blockchain-Based Solutions for UAV-Assisted Connected Vehicle Networks in Smart Cities: A Review, Open Issues, and Future Perspectives. Telecom 2021, 2, 108-140. https://doi.org/10.3390/telecom2010008
Álvares P, Silva L, Magaia N. Blockchain-Based Solutions for UAV-Assisted Connected Vehicle Networks in Smart Cities: A Review, Open Issues, and Future Perspectives. Telecom. 2021; 2(1):108-140. https://doi.org/10.3390/telecom2010008
Chicago/Turabian StyleÁlvares, Paulo, Lion Silva, and Naercio Magaia. 2021. "Blockchain-Based Solutions for UAV-Assisted Connected Vehicle Networks in Smart Cities: A Review, Open Issues, and Future Perspectives" Telecom 2, no. 1: 108-140. https://doi.org/10.3390/telecom2010008
APA StyleÁlvares, P., Silva, L., & Magaia, N. (2021). Blockchain-Based Solutions for UAV-Assisted Connected Vehicle Networks in Smart Cities: A Review, Open Issues, and Future Perspectives. Telecom, 2(1), 108-140. https://doi.org/10.3390/telecom2010008







