The Cybersecurity Focus Area Maturity (CYSFAM) Model
Abstract
1. Introduction
2. Related Work
2.1. Cybersecurity and Other Security Domains

2.2. Information Security and Cybersecurity Standards
- International standards are developed by international SDOs and made available to the public, possibly at cost. ISO (International Organization of Standardization) standards are the most well-known ones.
- Regional standards are adopted by a number of nations in a particular region. European Committee for Standardization (CEN) standards are examples of this category.
- National standards are developed for use in a particular country.
- Industry standards are adopted by a particular industry for common use. An example is the Security Industry Association (SIA) standard.
- Proprietary or company standards are constructed by organizations (mainly commercial) with little to no attention to external parties.
| Security Domain/Topic | Standard | Reference |
|---|---|---|
| Information security | ISO/IEC 27001:2013—Information technology—Security techniques—Information security management systems—Requirements | [20] |
| Cybersecurity | ISO/IEC 27032:2012—Information technology—Security techniques—Guidelines for cybersecurity | [17] |
| Network security | ISO/IEC 27033-1:2015—Information technology—Security techniques—Network security—Part 1: Overview and concepts | [21] |
| Application security | ISO/IEC 27034-1:2011—Information technology—Security techniques—Application security—Part 1: Overview and concepts | [22] |
| Incident management | ISO/IEC 27035-1:2016—Information technology—Security techniques—Information security incident management—Part 1: Principles of incident management | [23] |
| Supplier relationships security | ISO/IEC 27036-1:2014—Information technology—Security techniques—Information security for supplier relationships—Part 1: Overview and concepts | [24] |
| Privacy | ISO/IEC 29100:2011—Information technology—Security techniques—Privacy framework | [25] |
2.3. Information Security and Cybersecurity Maturity Models
- CYSFAM: The Cybersecurity Focus Area Maturity Model introduced in the present paper.
- C2M2: Cybersecurity Capability Maturity Model [30].
- SSE-CMM: System Security Engineering Capability Maturity Model [31].
- NICE: National Initiative for Cybersecurity Education (NICE) Cybersecurity Workforce Framework [32].
- O-ISM3: The Open Group Information Security Management Maturity Model [33].
- ISFAM: The Information Security Focus Area Maturity Model [15].
| Features | CYSFAM | C2M2 [30] | SSE-CMM [31] | NICE [32] | O-ISM3 [33] | ISFAM [15] |
|---|---|---|---|---|---|---|
| Cybersecurity-focused | Yes | Yes | No | Yes | No | No |
| FAM or CMM | FAM | CMM | CMM | CMM | CMM | FAM |
| Target sector | Generic | Critical infrastructures | Security engineering | Workforce | Generic | Generic |
| Incorporates standards | Mainly | Partly | No | No | Partly | Mainly |
| Analysis of interdependencies between the processes/capabilities | Yes | No | No | No | No | Yes |
2.4. Focus Area Maturity Models (FAMs)
2.5. ISFAM: The Information Security Focus Area Maturity Model
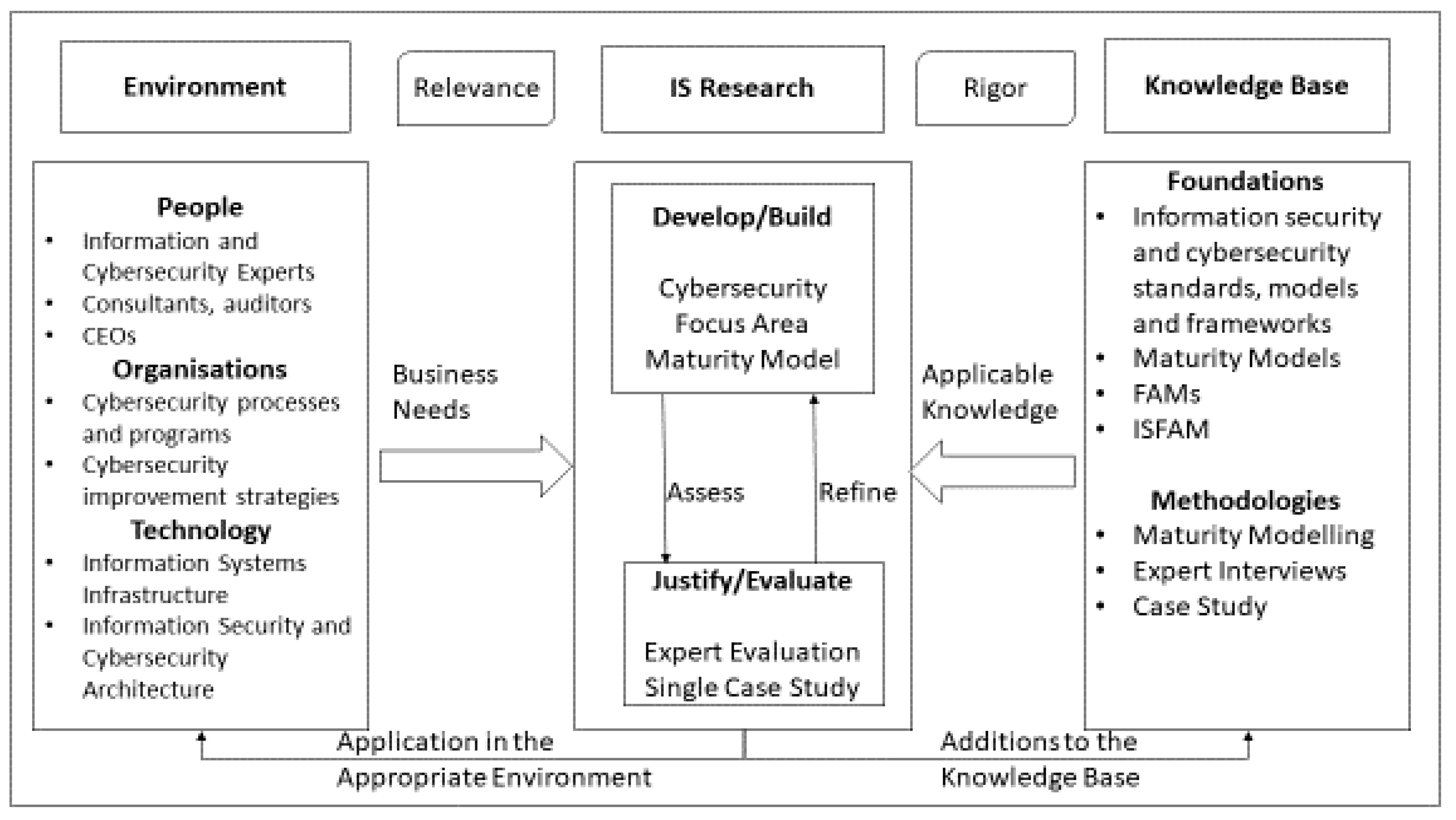
3. Materials and Methods
4. Artifact Development
4.1. Identifying the Initial Set of Focus Areas, Relevant Standards and Frameworks
| Standard or Framework | References |
|---|---|
| ITU-T ICT Security Standards Roadmap | [39] |
| Guidebook on National Cyber Security Strategies | [40] |
| ISA/IEC-62443 | [41] |
| NIST 800-12 and NIST 800-14 | [42,43] |
| NERC Critical Infrastructure Protection (CIP) Standards | [44] |
| NERC Security Guidelines | [45] |
- Articles have to be written in the English language.
- Articles have to originate from a trustworthy source (e.g., a professional, specialized organization).
- Articles have to be published in the year 2010 or later.
- Articles have to be accessible without cost (note that institutional subscriptions were used).
| Standard or Framework | Reference |
|---|---|
| Critical Security Controls for Effective Cyber Defense | [46] |
| Cyber Security Self-Assessment Guidance | [47] |
| NIST 800-53 | [48] |
| Cybersecurity Capability Maturity Model (C2M2) | [30] |
| The IASME Governance Standard for Information and Cyber Security | [49] |
| A Maturity Model for Enterprise Key Management | [50] |
| ISF Standard of Good Practice for Information Security | [51] |
| Guidelines for Managing the Security of Mobile Devices in the Enterprise | [52] |
| Guide to Enterprise Patch Management Technologies | [53] |
4.2. Defining the Cybersecurity Focus Areas and Capabilities
- The findings from the ISO/IEC 2703x were translated to an initial number of focus areas (Table 4).
- The additional 15 standards and frameworks (Table 5 and Table 7) were analysed and translated to a number of focus areas. These standards and frameworks were to identify the focus-areas that the ISO/IEC standards did not explicitly have in scope. This led to a long list of focus areas (77 in total) that could serve as an augmentation of CYSFAM.
- This long list of candidates CYSFAM focus areas was analysed to define the final set of CYSFAM focus areas. Within this set of focus areas, the decision to either adopt or exclude a focus area was based on the following criteria.
- ◦
- The focus area is meaningful to CYSFAM; it concerns a cybersecurity-related area.
- ◦
- The focus area is not yet adequately represented in existing focus areas in the ISFAM (see Section 2) or CYSFAM.
- ◦
- The focus area is not specific to a particular domain or organization-type; it serves a broad range of organizations.
- 4.
- The next step was to determine the capabilities under each focus area by analysing the resources that led the authors to the focus areas. The number of capability statements identified for each focus area and related standards, models, and frameworks are given in Table 8. The total number of capability statements was 144.
| # | Focus Area | Number of Capability Assessment Questions | Standard/Model/Framework |
|---|---|---|---|
| 1 | Server protection | 16 | ISO/IEC 27032 [17], The ISF Standard of Good Practice for Information Security [51,53] |
| 2 | End-user controls | 15 | ISO/IEC 27032 [17] |
| 3 | Controls against Social Engineering | 7 | ISO/IEC 27032 [17] |
| 4 | Network security | 12 | ISO/IEC 27033 [21] |
| 5 | Application security | 8 | ISO/IEC 27034 [22] |
| 6 | Cybersecurity Incident Management | 16 | ISO/IEC 27035 [23] |
| 7 | Cybersecurity awareness | 16 | Security Awareness Roadmap [54], ISO/IEC 27001 [20] |
| 8 | Cryptography | 16 | A Maturity Model for Enterprise Key Management [50] |
| 9 | Cybersecurity governance | 14 | Cyber Security Self-Assessment Guidance [47] |
| 10 | Mobile security | 16 | Guidelines for Managing the Security of Mobile Devices in the Enterprise [52] |
| 11 | Vulnerability management | 8 | Critical Security Controls for Effective Cyber Defense [46] |
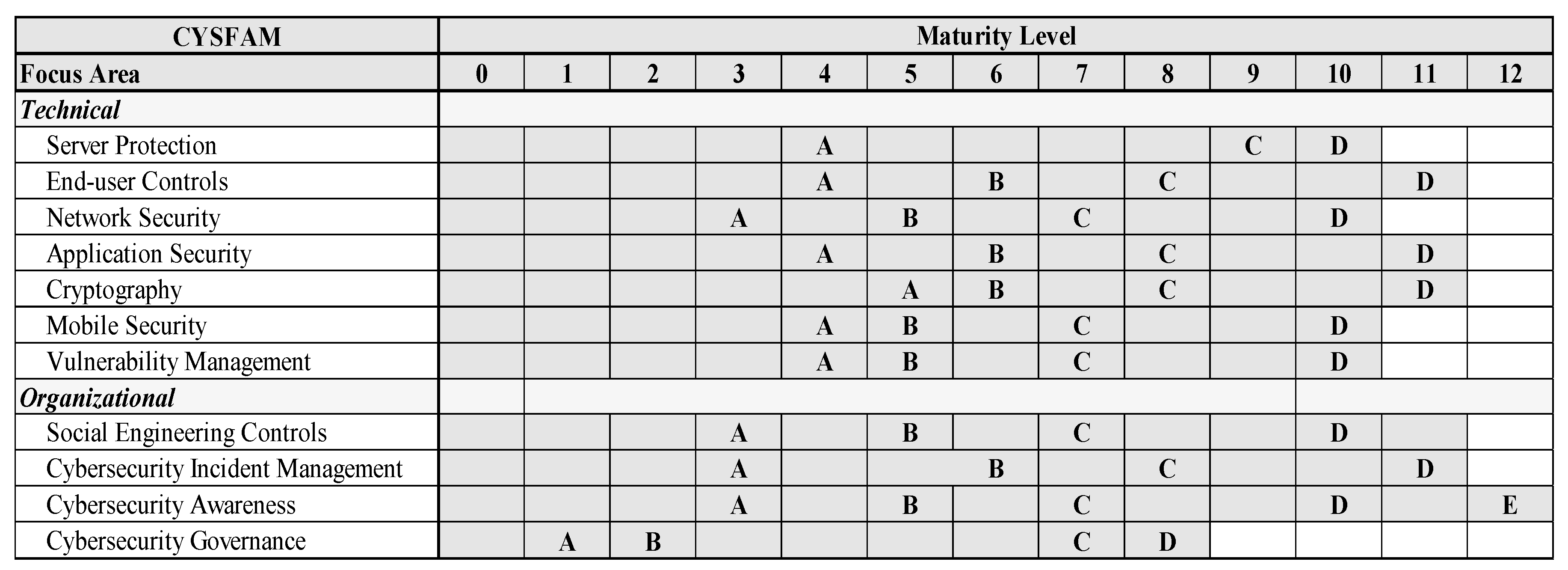
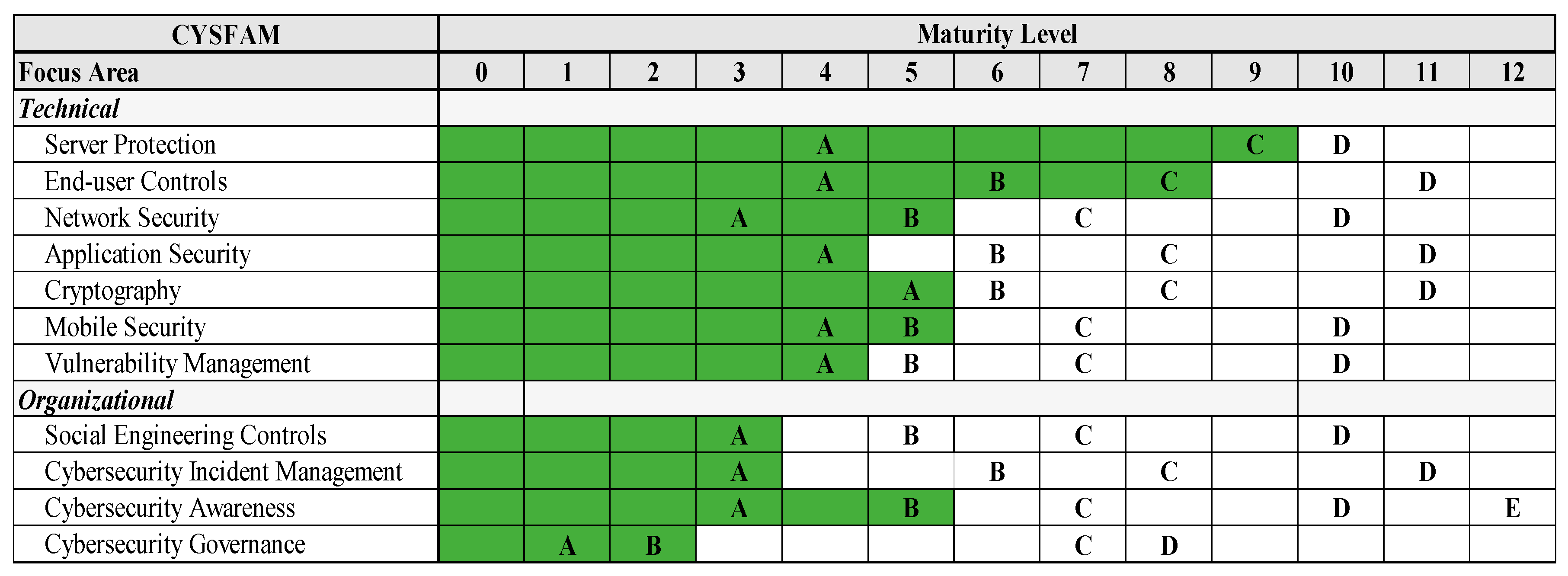
4.3. Identifying the Dependencies and Positioning the Capabilities in the Maturity Matrix
4.4. Focus Area Scoring
- Every achieved step A capability represents a worth of 0.25.
- Every achieved step B capability represents a worth of 0.5.
- Every achieved step C capability represents a worth of 0.75.
- Every achieved step D capability represents a worth of 1.
- Every achieved step E capability represents a worth of 1.25.
- If the assessment of any focus area results in a total score that has decimals behind the point, the score is rounded to its nearest natural number.
- A value of 0.25 is subtracted per unachieved capability at a previous level, when at least one of the capabilities from a higher level is met.
5. Results
Focus Area Example: Server Protection
6. Evaluation
6.1. Expert Evaluation and Results
- The interviewee is experienced in the information or cybersecurity domain—a minimum of 5 years of experience is required.
- The interviewee is capable of thinking outside of the context of the case study company.
- The interviewee can prove their knowledge by providing Certified Information Systems Security Professional (CISSP) certification [61].
- CYSFAM entirely lacks a module on security in Cloud Computing, which is one of the most prevalent security concerns for now and in the upcoming years. That certainly needs to be included in the final model.
- The scoring method is hard to grasp and, in its rigidness, it is somewhat harsh. However, compliance agencies and auditors are usually also harsh; thus, that warrants such a setup.
- CYSFAM is very control-based. It would be an idea to introduce two dimensions per focus area: control-based and process-based (or process maturity).
- CYSFAM contains quite some jargon. That is not necessarily an issue, but you need to be clear about the intended target audience of CYSFAM (security experts, rather than management—upper level or not).
- There are a number of capabilities that could be better rephrased in CYSFAM.
6.2. Case Study and Results
- The case study company is sufficiently large; there is a grounded possibility that the concepts found in the literature are part of the case study company’s routine.
- The case study company is active in a “security-sensitive” domain; the case study company manages and/or governs systems usually containing data that are of value.
- The case study company can provide the resources (time, money) and the conditions (culture) which are required to carry out the research.
- CYSFAM assessment can be performed within a 4 h timeframe provided that the conditions are suitable (timely communication with experts where needed is guaranteed).
- The questions make sense—at least to information and cybersecurity domain experts. This is the most significant target audience for CYSFAM, notwithstanding that other information technology professionals could consider CYSFAM beneficial.
- The case study organization recognizes itself in the assessment results.
7. Discussion
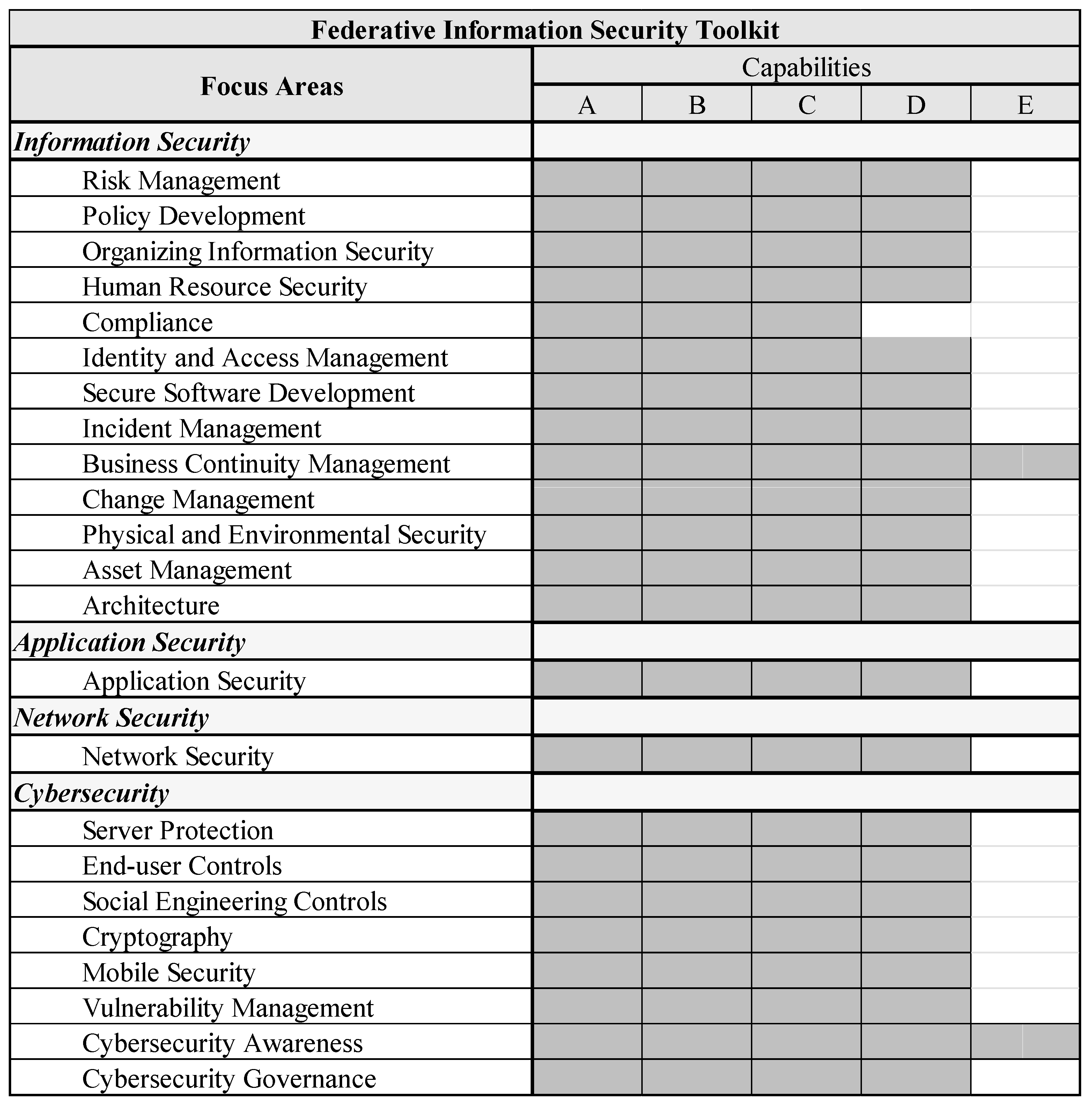
Federated Information Security Toolkit
8. Conclusions
Author Contributions
Funding
Conflicts of Interest
Abbreviations
| CEN | European Committee for Standardization |
| CMM | Capability Maturity Model |
| CIRT | Computer Incident Response Team |
| CISSP | Certified Information Systems Security Professional |
| ECSO | European Cybersecurity Organisation |
| FAM | Focus area Maturity Model |
| FIST | Federative Information Security Toolkit |
| IASME | Information Assurance for Small and Medium-sized Enterprises |
| ICT | Information and Communications Technology |
| IEC | International Electrotechnical Commission |
| IS | Information Systems |
| ISA | International Society of Automation |
| ISO | International Organization of Standardization |
| ITU | International Telecommunication Union |
| NERC | North American Electric Reliability Corporation |
| NIST | National Institute of Standards and Technology |
| SDO | Standards Developing Organizations |
| SME | Small and Medium-sized Enterprises |
| SIEM | Security Information and Event Management |
| SOC | Security Operations Center |
References
- World Economic Forum. The Global Risks Report 2020; World Economic Forum: Cologny, Switzerland, 2020. [Google Scholar]
- Center for Strategic and International Studies (CSIS). Significant Cyber Incidents Since 2006; Center for Strategic and International Studies: Washington, DC, USA, 2019. [Google Scholar]
- Symantec. Internet Security Threat Report; Symantec: Mountain View, CA, USA, 2018. [Google Scholar]
- Kour, R.; Karim, R.; Thaduri, A. Cybersecurity for Railways—A Maturity Model. Proc. Inst. Mech. Eng. Part F J. Rail Rapid Transit 2020, 234, 1129–1148. [Google Scholar] [CrossRef]
- Khan, S.K.; Shiwakoti, N.; Stasinopoulos, P.; Chen, Y. Cyber-Attacks in the next-Generation Cars, Mitigation Techniques, Anticipated Readiness and Future Directions. Accid. Anal. Prev. 2020, 148, 105837. [Google Scholar] [CrossRef] [PubMed]
- Choo, K.-K.R.; Gai, K.; Chiaraviglio, L.; Yang, Q. A Multidisciplinary Approach to Internet of Things (IoT) Cybersecurity and Risk Management. Comput. Secur. 2021, 102, 102136. [Google Scholar] [CrossRef]
- Radanliev, P.; de Roure, D.; Walton, R.; van Kleek, M.; Montalvo, R.M.; Maddox, L.; Santos, O.; Burnap, P.; Anthi, E. Artificial Intelligence and Machine Learning in Dynamic Cyber Risk Analytics at the Edge. SN Appl. Sci. 2020, 2, 1773. [Google Scholar] [CrossRef]
- Williams, C.M.; Chaturvedi, R.; Chakravarthy, K. Cybersecurity Risks in a Pandemic. J. Med. Internet Res. 2020, 22, e23692. [Google Scholar] [CrossRef] [PubMed]
- Bhuyan, S.S.; Kabir, U.Y.; Escareno, J.M.; Ector, K.; Palakodeti, S.; Wyant, D.; Kumar, S.; Levy, M.; Kedia, S.; Dasgupta, D.; et al. Transforming Healthcare Cybersecurity from Reactive to Proactive: Current Status and Future Recommendations. J. Med. Syst. 2020, 44, 98. [Google Scholar] [CrossRef] [PubMed]
- International Organization for Standardization (ISO). Benefits of Standards. Available online: http://www.iso.org/cms/render/live/en/sites/isoorg/home/standards/benefits-of-standards.html (accessed on 8 June 2019).
- Paulk, M.C.; Curtis, B.; Chrissis, M.B.; Weber, C.V. Capability Maturity Model, Version 1.1. IEEE Softw. Los Alamitos 1993, 10, 18–27. [Google Scholar] [CrossRef]
- Capability Maturity Model Institute (CMMI). CMMI Development; CMMI Institute: Illinois, IL, USA, 2018. [Google Scholar]
- Poeppelbuss, J.; Niehaves, B.; Simons, A.; Becker, J. Maturity Models in Information Systems Research: Literature Search and Analysis. CAIS 2011, 29, 2927. [Google Scholar] [CrossRef]
- van Steenbergen, M.; Bos, R.; BrinkkemperInge, S.; van de Weerd, I.; Bekkers, W. The Design of Focus Area Maturity Models. In Global Perspectives on Design Science Research; Springer: Berlin/Heidelberg, Germany, 2010; pp. 317–332. [Google Scholar]
- Spruit, M.; Roeling, M. ISFAM: The Information Security Focus Area Maturity Model. In Proceedings of the European Conference on Information Systems (ECIS) 2014, Tel Aviv, Israel, 9–11 June 2014; p. 15. [Google Scholar]
- European Union Agency for Cybersecurity (ENISA). Definition of Cybersecurity—Gaps and Overlaps in Standardisation. Available online: https://www.enisa.europa.eu/publications/definition-of-cybersecurity (accessed on 24 December 2020).
- International Organization for Standardization (ISO)/International Electrotechnical Commission (IEC). ISO/IEC 27032:2012-Information—Security Techniques—Guidelines for Cybersecurity. Available online: https://www.iso.org/standard/44375.html (accessed on 14 December 2017).
- Scarfone, K.; Benigni, D.; Grance, T. Cyber Security Standards. In Wiley Handbook of Science and Technology for Homeland Security; American Cancer Society: Atlanta, GA, USA, 2009; pp. 1–10. ISBN 978-0-470-08792-3. [Google Scholar]
- European Cyber Security Organisation (ECSO). State of the Art Syllabus V2; ESCO: Essex, UK, 2017. [Google Scholar]
- International Organization for Standardization (ISO)/International Electrotechnical Commission (IEC). ISO/IEC 27001:2013-Information Technology—Security Techniques—Information Security Management Systems—Requirements. Available online: https://www.iso.org/standard/54534.html (accessed on 15 December 2017).
- International Organization for Standardization (ISO)/International Electrotechnical Commission (IEC). ISO/IEC 27033-1:2015-Information Technology—Security Techniques—Network Security—Part 1: Overview and Concepts. Available online: https://www.iso.org/standard/63461.html (accessed on 15 December 2017).
- International Organization for Standardization (ISO)/International Electrotechnical Commission (IEC). ISO/IEC 27034-1:2011-Information Technology—Security Techniques—Application Security—Part 1: Overview and Concepts. Available online: https://www.iso.org/standard/44378.html (accessed on 15 December 2017).
- International Organization for Standardization (ISO)/International Electrotechnical Commission (IEC). ISO/IEC 27035-1:2016-Information Technology—Security Techniques—Information Security Incident Management—Part 1: Principles of Incident Management. Available online: https://www.iso.org/standard/60803.html (accessed on 15 December 2017).
- International Organization for Standardization (ISO)/International Electrotechnical Commission (IEC). ISO/IEC 27036-1:2014. Available online: https://www.iso.org/cms/render/live/en/sites/isoorg/contents/data/standard/05/96/59648.html (accessed on 19 February 2020).
- International Organization for Standardization (ISO)/International Electrotechnical Commission (IEC). ISO/IEC. ISO/IEC 29100:2011(En), Information Technology—Security Techniques—Privacy Framework. Available online: https://www.iso.org/obp/ui/#iso:std:iso-iec:29100:ed-1:v1:en (accessed on 19 February 2020).
- Rea-Guaman, A.M.; San Feliu, T.; Calvo-Manzano, J.A.; Sanchez-Garcia, I.D. Comparative Study of Cybersecurity Capability Maturity Models. In Proceedings of the Software Process Improvement and Capability Determination; Mas, A., Mesquida, A., O’Connor, R.V., Rout, T., Dorling, A., Eds.; Springer International Publishing: Cham, Switzerland, 2017; pp. 100–113. [Google Scholar]
- Akinsanya, O.O.; Papadaki, M.; Sun, L. Current Cybersecurity Maturity Models: How Effective in Healthcare Cloud? In Proceedings of the 5th Collaborative European Research Conference (CERC 2019), Darmstadt, Germany, 29–30 March 2019. [Google Scholar]
- Rabii, A.; Assoul, S.; Ouazzani Touhami, K.; Roudies, O. Information and Cyber Security Maturity Models: A Systematic Literature Review. Inf. Comput. Secur. 2020, 28, 627–644. [Google Scholar] [CrossRef]
- Ozkan, B.Y.; Spruit, M.; Wondolleck, R.; Burriel Coll, V. Modelling Adaptive Information Security for SMEs in a Cluster. JIC 2019, 21, 235–256. [Google Scholar] [CrossRef]
- Christopher, J.D.; Gonzalez, D.; White, D.W.; Stevens, J.; Grundman, J.; Mehravari, N.; Dolan, T. Cybersecurity Capability Maturity Model (C2M2); U.S. Department of Energy: Washington, DC, USA, 2014; pp. 1–76.
- SSE-CMM Project. Systems Security Engineering Capability Maturity Model SSE-CMM Model Description Document; U.S. Department of Defense: Washington, DC, USA, 2003; p. 338.
- Newhouse, W.; Keith, S.; Scribner, B.; Witte, G. National Initiative for Cybersecurity Education (NICE) Cybersecurity Workforce Framework; National Institute of Standards and Technology: Gaithersburg, MD, USA, 2017.
- The Open Group. Open Information Security Management Maturity Model (O-ISM3), Version 2.0.; The Open Group: Berkshire, UK, 2017. [Google Scholar]
- Koomen, T.; Pol, M. Test Process Improvement: A Practical Step-by-Step Guide to Structured Testing; Addison-Wesley Longman Publishing Co., Inc.: Boston, MA, USA, 1999; ISBN 978-0-201-59624-3. [Google Scholar]
- van Steenbergen, M.; Bos, R.; Brinkkemper, S.; de van Weerd, I.; Bekkers, W. Improving IS Functions Step by Step: The Use of Focus Area Maturity Models. Scand. J. Inf. Syst. 2013, 25, 35–56. [Google Scholar]
- Hevner, A.R.; March, S.T.; Park, J.; Ram, S. Design Science in Information Systems Research. MIS Q. 2004, 28, 75–105. [Google Scholar] [CrossRef]
- Peffers, K.; Tuunanen, T.; Rothenberger, M.A.; Chatterjee, S. A Design Science Research Methodology for Information Systems Research. J. Manag. Inf. Syst. 2007, 24, 45–77. [Google Scholar] [CrossRef]
- Baskerville, R.; Pries-Heje, J.; Venable, J. Soft Design Science Methodology. In Proceedings of the 4th International Conference on Design Science Research in Information Systems and Technology; Association for Computing Machinery: New York, NY, USA, 2009; pp. 1–11. [Google Scholar]
- International Telecommunication Union (ITU). ICT Security Standards Roadmap. Available online: https://www.itu.int/en/ITU-T/studygroups/com17/ict/Pages/default.aspx (accessed on 21 February 2020).
- European Union Agency for Cybersecurity (ENISA). National Cyber Security Strategies: An Implementation Guide; ENISA: Heraklion, Greece, 2012. [Google Scholar]
- International Electrotechnical Commission (IEC). Industrial Communication Networks: Network and System Security. Pt. 3,3: System Security Requirements and Security Levels; International Electrotechnical Commission (IEC): Geneva, Switzerland, 2013; ISBN 978-2-8322-1036-9. [Google Scholar]
- Nieles, M.; Dempsey, K.; Pillitteri, V.Y. An Introduction to Information Security; National Institute of Standards and Technology: Gaithersburg, MD, USA, 2017.
- Swanson, M.; Guttman, B. Generally Accepted Principles and Practices for Securing Information Technology Systems; National Institute of Standards and Technology: Gaithersburg, MD, USA, 1996.
- North American Electric Reliability Corporation (NERC). Critical Infrastructure Protection Standards; NERC: Atlanta, GA, USA, 2010. [Google Scholar]
- North American Electric Reliability Corporation (NERC). NERC Security Guidelines. Available online: https://www.nerc.com/comm/CIPC/SecurityGuidelinesCurrent/Electricity%20Sector%20Physical%20Security%20Guideline%20(Approved%20by%20CIPC%20-%20October%2028,%202013).pdf (accessed on 30 August 2018).
- SANS Institute. Critical Security Controls for Effective Cyber Defense; SANS Institute: Bethesda, MD, USA, 2018. [Google Scholar]
- Office of the Superintendent of Financial Institutions (OSFI). Cyber Security Self-Assessment Guidance; OSFI: Toronto, ON, Canada, 2013. [Google Scholar]
- National Institute of Standards and Technology (NIST). Security and Privacy Controls for Federal Information Systems and Organizations; National Institute of Standards and Technology: Gaithersburg, MD, USA, 2013.
- Information Assurance for Small and Medium Enterprises (IASME) Consortium. The IASME Governance Standard for Information and Cyber Security; IASME: Malvern, UK, 2018. [Google Scholar]
- Kostick, C. A Maturity Model for Enterprise Key Management; Ernst & Young: Baltimore, MD, USA, 2010. [Google Scholar]
- Information Security Forum (ISF). The ISF Standard of Good Practice for Information Security; ISF: Surrey, UK, 2018. [Google Scholar]
- Souppaya, M.; Scarfone, K. Guidelines for Managing the Security of Mobile Devices in the Enterprise; National Institute of Standards and Technology: Gaithersburg, MD, USA, 2013.
- Souppaya, M.; Scarfone, K. Guide to Enterprise Patch Management Technologies; National Institute of Standards and Technology: Gaithersburg, MD, USA, 2013.
- SANS Institute. Security Awareness Roadmap; SANS Institute: Bethesda, MD, USA, 2016. [Google Scholar]
- Parsons, K.; McCormac, A.; Butavicius, M.; Pattinson, M.; Jerram, C. Determining Employee Awareness Using the Human Aspects of Information Security Questionnaire (HAIS-Q). Comput. Secur. 2014, 42, 165–176. [Google Scholar] [CrossRef]
- Marble, J.L.; Lawless, W.F.; Mittu, R.; Coyne, J.; Abramson, M.; Sibley, C. The Human Factor in Cybersecurity: Robust & Intelligent Defense. In Cyber Warfare: Building the Scientific Foundation; Jajodia, S., Shakarian, P., Subrahmanian, V.S., Swarup, V., Wang, C., Eds.; Springer International Publishing: Cham, Switzerland, 2015; pp. 173–206. ISBN 978-3-319-14039-1. [Google Scholar]
- Hadlington, L. Human Factors in Cybersecurity; Examining the Link between Internet Addiction, Impulsivity, Attitudes towards Cybersecurity, and Risky Cybersecurity Behaviours. Heliyon 2017, 3, e00346. [Google Scholar] [CrossRef] [PubMed]
- Spruit, M.; de Boer, T. Business Intelligence as a Service: A Vendor’s Approach. Available online: www.igi-global.com/article/business-intelligence-as-a-service/126896 (accessed on 25 February 2020).
- Spruit, M.; van Lingen, S.; Ozkan, B.Y. The CYSFAM Questionnaire: Assessing Cyber Security Focus Area Maturity. Available online: http://www.cs.uu.nl/research/techreps/UU-CS-2019-003.html (accessed on 6 June 2019).
- Muskat, M.; Blackman, D.; Muskat, B. Mixed Methods: Combining Expert Interviews, Cross-Impact Analysis and Scenario Development. Electron. J. Bus. Res. Methods 2012, 10, 9–21. [Google Scholar] [CrossRef][Green Version]
- (ISC)2. Cybersecurity Certification|CISSP-Certified Information Systems Security Professional|(ISC)2. Available online: https://www.isc2.org:443/Certifications/CISSP (accessed on 21 February 2020).
- Ngoc, L.; Hoang, D. Capability Maturity Model and Metrics Framework for Cyber Cloud Security. Scalable Comput. Pract. Exp. 2017, 18, 1329. [Google Scholar] [CrossRef]
- Guenther, J.; Falk, I. Generalising from Qualitative Research: Case Studies from VET in Contexts. In Proceedings of the AVETRA 10th Annual Conference, Footscray, VIC, Australia, 8–10 April 2007. [Google Scholar]
- Kertysova, K.; Bhattacharyya, K.; Frinking, E.; van der Dool, K.; Maričić, A.; Bhattacharyya, K. Cybersecurity: Ensuring Awareness and Resilience of the Private Sector across Europe in Face of Mounting Cyber Risks-Study; European Economic and Social Committee: Bruxelles, Belgium, 2018.
- Mayer, N. A Cluster Approach to Security Improvement According to ISO/IEC 27001. In Proceedings of the 17th European Systems & Software Process Improvement and Innovation Conference (EUROSPI’10), Grenoble, France, 1–3 September 2010. [Google Scholar]
- Baars, T.; Mijnhardt, F.; Vlaanderen, K.; Spruit, M. An Analytics Approach to Adaptive Maturity Models Using Organizational Characteristics. Decis. Anal. 2016, 3, 1–26. [Google Scholar] [CrossRef]

| Standard | Reference |
|---|---|
| ISO/IEC 27032:2012—Information technology—Security techniques—Guidelines for cybersecurity | [17] |
| ISO/IEC 27033-1:2015—Information technology—Security techniques—Network security—Part 1: Overview and concepts | [21] |
| ISO/IEC 27034-1:2011—Information technology—Security techniques—Application security—Part 1: Overview and concepts | [22] |
| ISO/IEC 27035-1:2016—Information technology—Security techniques—Information security incident management—Part 1: Principles of incident management | [23] |
| Focus Area | Reference |
|---|---|
| Server protection (elaborated upon in ISO/IEC 27032) | [17] |
| End-user controls (elaborated upon in ISO/IEC 27032) | [17] |
| Controls against Social Engineering (elaborated upon in ISO/IEC 27032) | [17] |
| Network security (the main focus of ISO/IEC 27033) | [21] |
| Application security (the main focus of ISO/IEC 27034) | [22] |
| Cyber/Information Security Incident Management (the main focus of ISO/IEC 27035) | [23] |
| Search Platforms | Most Prominent Keywords |
|---|---|
| Google Scholar | [information/cyber] security frameworks |
| [information/cyber] security risks | |
| Mendeley | [information/cyber] security controls |
| CIO.com | [information/cyber] security vulnerabilities |
| Gartner | [information/cyber] security maturity model |
| [information/cyber] security capability |
| # | Prerequisite Capability | Dependent Capability |
|---|---|---|
| 1 | Cybersecurity Governance A | Cybersecurity Governance B |
| 2 | Cybersecurity Governance B | Network Security A |
| 3 | Cybersecurity Governance B | Social Engineering Controls A |
| 4 | Cybersecurity Governance B | Incident Management A |
| 5 | Cybersecurity Governance B | Cybersecurity Awareness A |
| 6 | Network Security A | Server Protection A |
| 7 | Network Security A | End-user Controls A |
| 8 | Network Security A | Application Security A |
| 9 | Network Security A | Cryptography A |
| 10 | Network Security A | Mobile Security A |
| 11 | Network Security A | Vulnerability Management A |
| 12 | Incident Management B | Cybersecurity Governance C |
| 13 | Vulnerability Management B | Incident Management B |
| 14 | Server Protection A | Vulnerability Management B |
| 15 | Cybersecurity Awareness A | Mobile Security A |
| 16 | Cybersecurity Awareness B | Social Engineering Controls C |
| 17 | Server Protection A | End-user Controls B |
| 18 | Application Security A | Cryptography A |
| 19 | Cybersecurity Awareness A | Application Security B |
| 20 | Cybersecurity Awareness B | Incident Management C |
| 21 | Cybersecurity Governance D | Social Engineering Controls D |
| 22 | Incident Management B | Server Protection D |
| Capability | Reference |
|---|---|
| Configuration according to a baseline security configuration | ISO/IEC 27032 [17] |
| Testing and deployment of updates for the server operating system and the applications | [53] |
| Implementing security incident event monitoring (SIEM) | [51] |
| Implementing technical state compliance monitoring (TSCM) | [51] |
| Capability Statements | Capability |
|---|---|
| A |
| B |
| C |
| D |
Publisher’s Note: MDPI stays neutral with regard to jurisdictional claims in published maps and institutional affiliations. |
© 2021 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Yigit Ozkan, B.; van Lingen, S.; Spruit, M. The Cybersecurity Focus Area Maturity (CYSFAM) Model. J. Cybersecur. Priv. 2021, 1, 119-139. https://doi.org/10.3390/jcp1010007
Yigit Ozkan B, van Lingen S, Spruit M. The Cybersecurity Focus Area Maturity (CYSFAM) Model. Journal of Cybersecurity and Privacy. 2021; 1(1):119-139. https://doi.org/10.3390/jcp1010007
Chicago/Turabian StyleYigit Ozkan, Bilge, Sonny van Lingen, and Marco Spruit. 2021. "The Cybersecurity Focus Area Maturity (CYSFAM) Model" Journal of Cybersecurity and Privacy 1, no. 1: 119-139. https://doi.org/10.3390/jcp1010007
APA StyleYigit Ozkan, B., van Lingen, S., & Spruit, M. (2021). The Cybersecurity Focus Area Maturity (CYSFAM) Model. Journal of Cybersecurity and Privacy, 1(1), 119-139. https://doi.org/10.3390/jcp1010007





