Engineering Human–Machine Teams for Trusted Collaboration
Abstract
:1. Introduction
2. Example Scenario: Disassembling a (Simple) Complex Product
3. Background and State of the Art
3.1. Collaborative Human Machine Teams
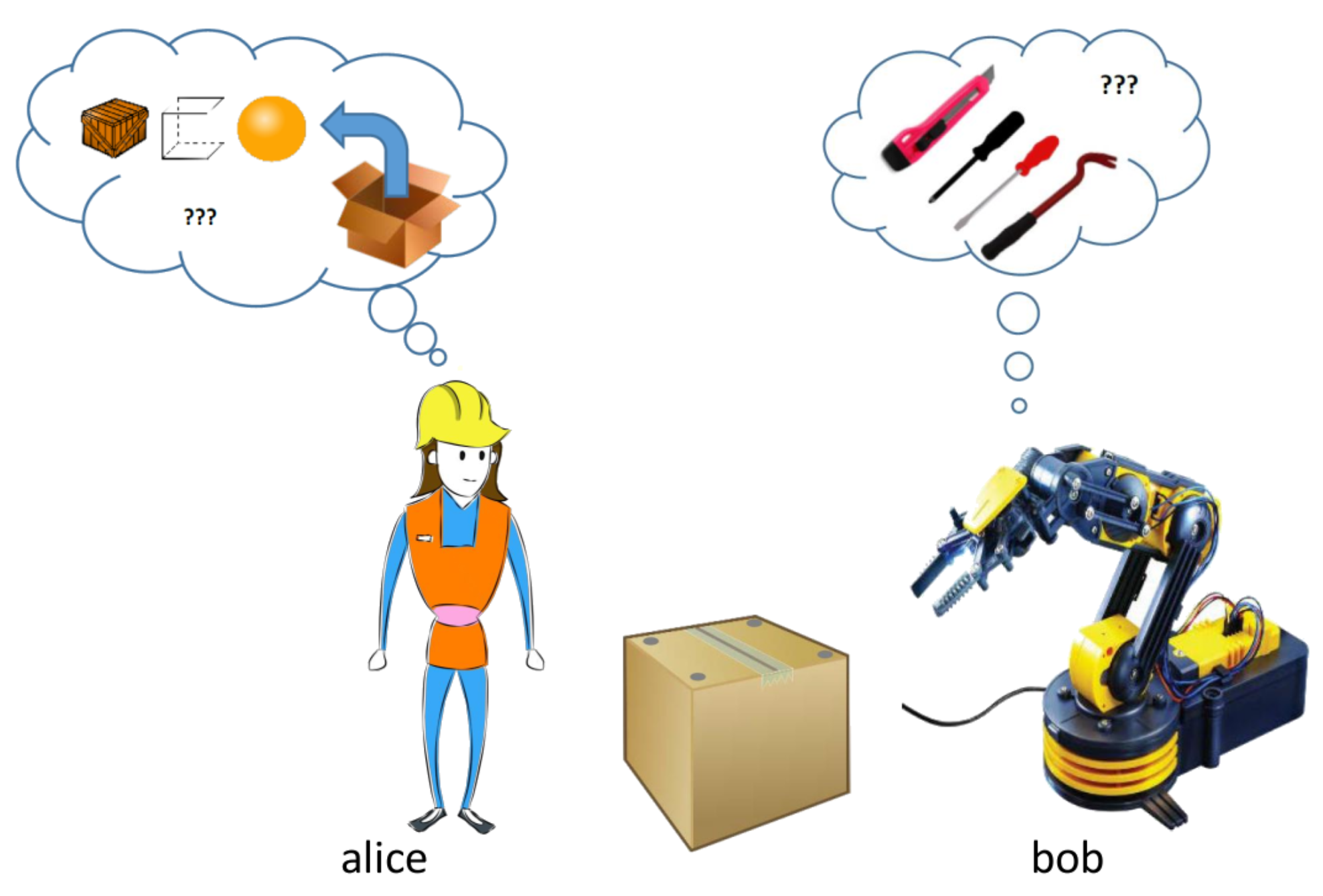
3.1.1. Team Collaboration
- Symmetry in collaboration is higher than in cooperation: In collaborative work, all actors are allowed to perform the same activities (symmetry of action), they possess (roughly) similar knowledge regarding the execution of the activity, and all individuals have a similar status regarding the collaborative process. On the contrary, in cooperation, individuals may perform different actions (e.g., actions that follow each other), they may have different knowledge (e.g., performing parts of their activity based on their knowledge), and there may be hierarchies for the overall process or parts of it. Regarding our example, the difference between a collaborative or cooperative disassembly process would be whether all participants are allowed to replace the lid, whether they possess enough knowledge to do all tasks and whether they decide collectively on sharing work or based on some hierarchy.
- In collaboration, it can be assumed that collaborators follow an overarching common goal in their collaboration, which goes beyond their (shared) individual goals. For cooperative processes, it would be enough if the individuals share similar goals (e.g., fulfilling their part of the processes with high quality).
- The division of labor is potentially the most obvious difference between cooperation and collaboration: “In cooperation, partners split the work, solve sub-tasks individually and then assemble the partial results into the final output. In collaboration, partners do the work together” [8] (p. 8). As described above, in our example, collaboration would describe a process in which the robot and human work conduct joint activities such as one teammate holding the object and the other dismantling it, or whether they perform them in sequential steps that happen after each other.
3.1.2. Human–Machine Teams
3.2. Trust between Humans and Technology
3.2.1. What Is Trust?
3.2.2. Human–Machine Trust Models
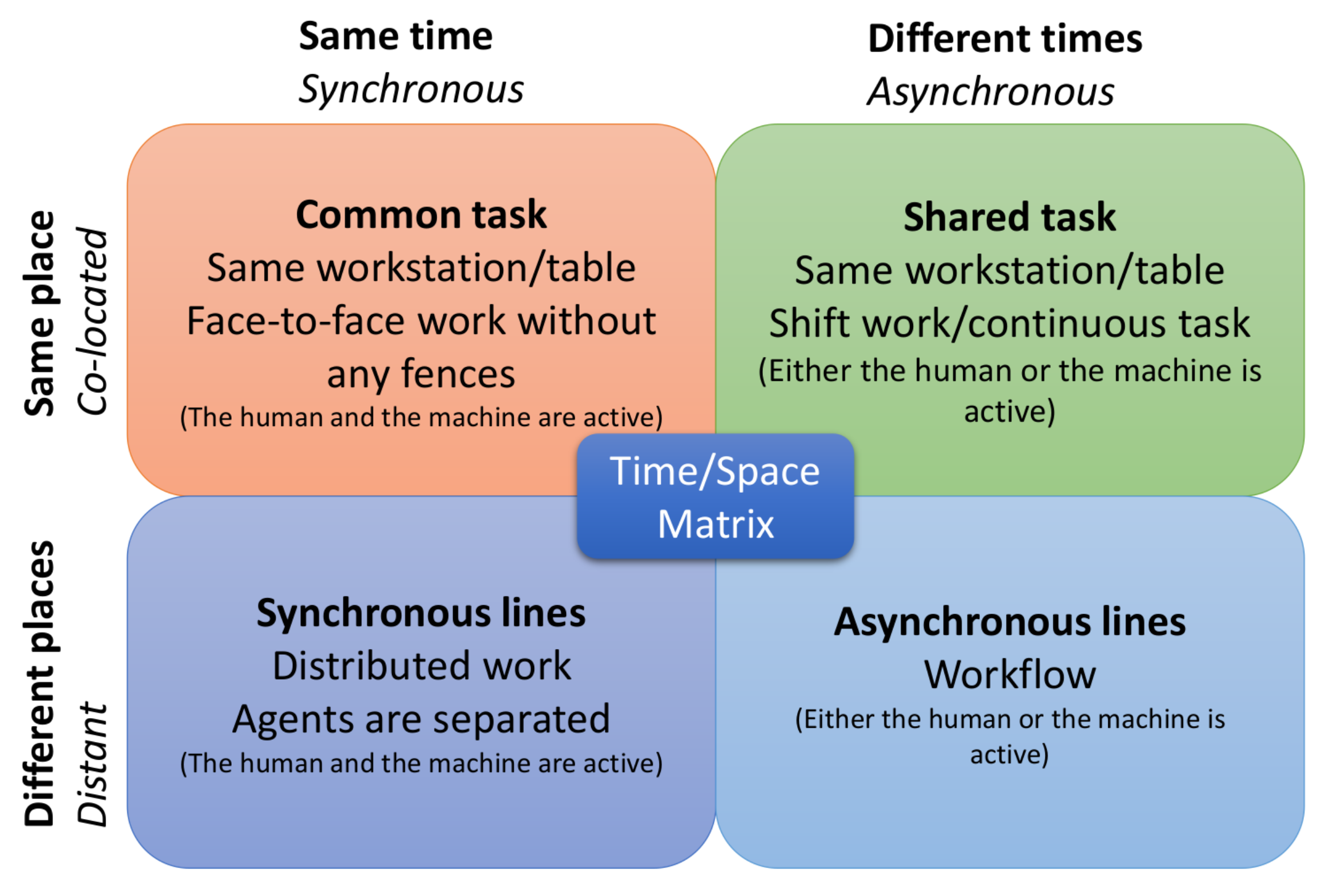
3.2.3. Mutual Trust and Trust Cycles
3.3. Engineering AI-Based Cyber-Physical Systems
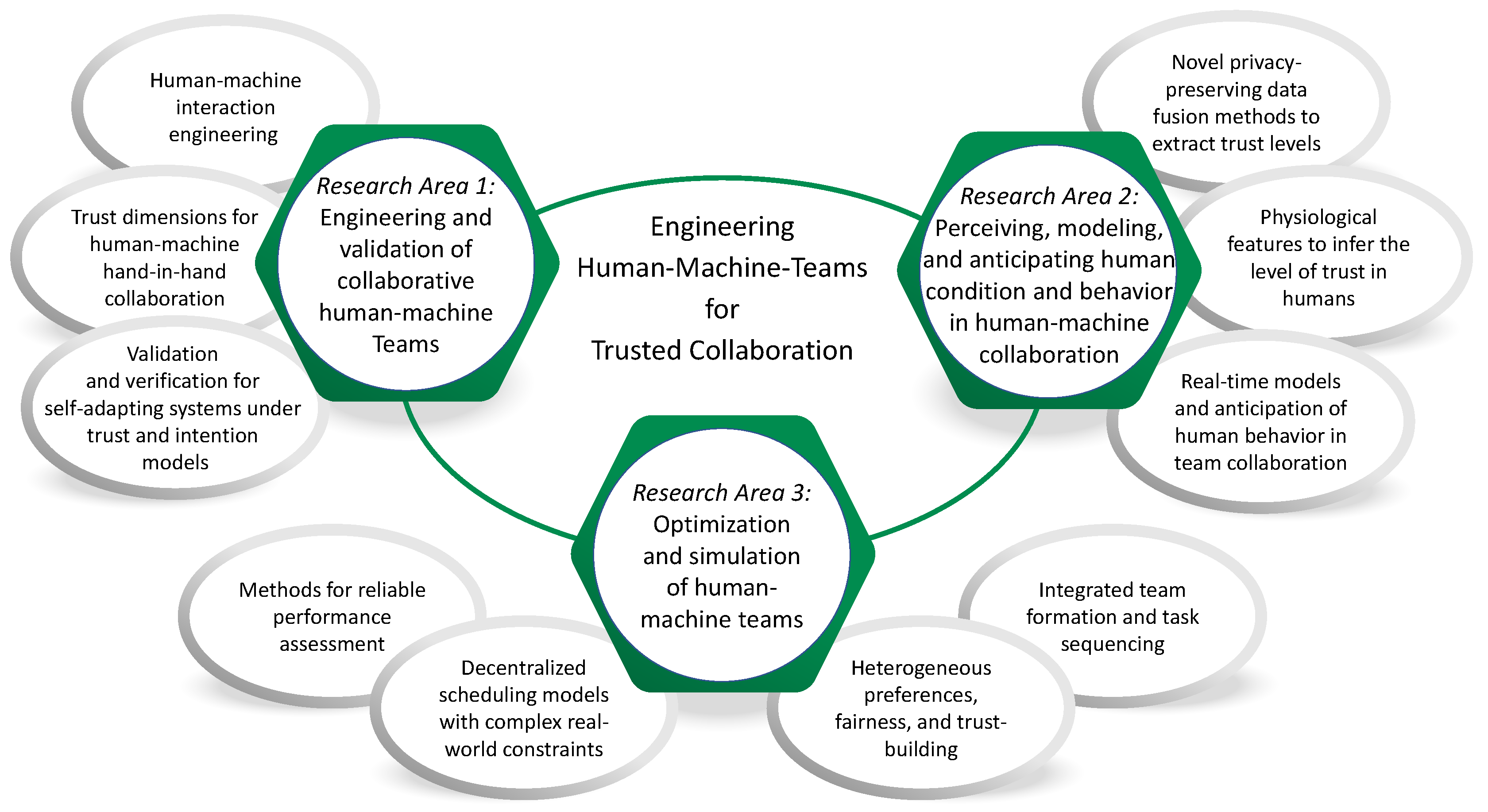
4. Research Opportunities
4.1. Engineering and Validation of Collaborative Human–Machine Teams
4.1.1. Trust Dimensions for Human–Machine Hand-in-Hand Collaboration
4.1.2. Human–Machine Interaction Engineering
4.1.3. Validation and Verification for Self-Adapting Systems under Trust and Intention Models
4.2. Perceiving, Modeling, and Anticipating Human Condition and Behavior in Human–Machine Collaboration
4.2.1. Physiological Features to Infer the Level of Trust in Humans
4.2.2. Novel Privacy-Preserving Data Fusion Methods to Extract Trust Levels
4.2.3. Real-Time Models and Anticipation of Human Behavior in Team Collaboration
4.3. Optimization and Simulation of Collaborative Human–Machine Teams
4.3.1. Integrated Team Formation and Task Sequencing/Planning
4.3.2. Heterogeneous Preferences, Fairness, and Trust-Building
4.3.3. Decentralized Scheduling Models with Complex Real-World Constraints
4.3.4. Methods for Reliable Performance Assessment
5. Conclusions
Author Contributions
Funding
Acknowledgments
Conflicts of Interest
References
- Klaus, D.J.; Glaser, R. Reinforcement determinants of team proficiency. Organ. Behav. Hum. Perform. 1970, 5, 33–67. [Google Scholar]
- Schmidt, K.; Bannon, L. Taking CSCW Seriously: Supporting Articulation Work. Comput. Support. Coop. Work (CSCW) Int. J. 1992, 1, 7–40. [Google Scholar]
- Israelsen, B.W.; Ahmed, N.R. “Dave…I can assure you…that it’s going to be all right…” A Definition, Case for, and Survey of Algorithmic Assurances in Human-Autonomy Trust Relationships. ACM Comput. Surv. 2019, 51, 1–37. [Google Scholar] [CrossRef] [Green Version]
- Falcone, R.; Castelfranchi, C. Social trust: A cognitive approach. In Trust and Deception in Virtual Societies; Springer: Dordrecht, The Netherlands, 2001; pp. 55–90. [Google Scholar]
- Schleibaum, S.; Greve, M.; Lembcke, T.B.; Azaria, A.; Fiosina, J.; Hazon, N.; Kolbe, L.; Kraus, S.; Müller, J.P.; Vollrath, M. How Did You Like This Ride? An Analysis of User Preferences in Ridesharing Assignments. In Proceedings of the 6th International Conference on Vehicle Technology and Intelligent Transport Systems, VEHITS 2020, Prague, Czech Repulic, 2–4 May 2020; pp. 157–168. [Google Scholar] [CrossRef]
- McGrath, J. Groups and Human Behavior (Excerpt). In Groups: Interaction and Performance; Prentice Hall: Englewood Cliffs, NJ, USA, 1984; pp. 113–115. [Google Scholar]
- Baker, D.P.; Salas, E. Principles for Measuring Teamwork Skills. Hum. Factors 1992, 34, 469–475. [Google Scholar] [CrossRef]
- Dillenbourg, P. What do you mean by ‘collaborative learning’? In Collaborative Learning: Cognitive and Computational Approaches; Elsevier: Oxford, UK, 1999; pp. 1–19. [Google Scholar]
- Surdilovic, D.; Bastidas-Cruz, A.; Radojicic, J.; Heyne, P. Interaktionsfähige intrinsisch sichere Roboter für vielseitige Zusammenarbeit mit dem Menschen. In baua: Fokus; Bundesanstalt für Arbeitsschutz und Arbeitsmedizin: Dortmund, Germany, 2018. [Google Scholar]
- Johansen, R. Groupware: Computer Support for Business Teams; The Free Press: New York, NY, USA, 1988. [Google Scholar]
- Cortés, J.; Egerstedt, M. Coordinated control of multi-robot systems: A survey. SICE J. Control Meas. Syst. Integr. 2017, 10, 495–503. [Google Scholar]
- Rizk, Y.; Awad, M.; Tunstel, E.W. Cooperative heterogeneous multi-robot systems: A survey. ACM Comput. Surv. (CSUR) 2019, 52, 1–31. [Google Scholar]
- Candea, C.; Hu, H.; Iocchi, L.; Nardi, D.; Piaggio, M. Coordination in multi-agent RoboCup teams. Robot. Auton. Syst. 2001, 36, 67–86. [Google Scholar]
- Marsella, S.; Adibi, J.; Al-Onaizan, Y.; Kaminka, G.A.; Muslea, I.; Tambe, M. On being a teammate: Experiences acquired in the design of RoboCup teams. In Proceedings of the Third Annual Conference on Autonomous Agents, Seattle, WA, USA, 19–21 April 1999; pp. 221–227. [Google Scholar]
- Kinny, D.; Sonenberg, E.; Ljungberg, M.; Tidhar, G.; Rao, A.; Werner, E. Planned team activity. In European Workshop on Modelling Autonomous Agents in A Multi-Agent World; Springer: Heidelberg, Germany, 1992; pp. 227–256. [Google Scholar]
- Pynadath, D.V.; Tambe, M.; Chauvat, N.; Cavedon, L. Toward team-oriented programming. In International Workshop on Agent Theories, Architectures, and Languages; Springer: Berlin/Heidelberg, Germany, 1999; pp. 233–247. [Google Scholar]
- Norouzi, N.; Kim, K.; Hochreiter, J.; Lee, M.; Daher, S.; Bruder, G.; Welch, G. A systematic survey of 15 years of user studies published in the intelligent virtual agents conference. In Proceedings of the 18th International Conference on Intelligent Virtual Agents, Sydney, Australia, 5–8 November 2018; pp. 17–22. [Google Scholar]
- Rosenfeld, A.; Agmon, N.; Maksimov, O.; Kraus, S. Intelligent agent supporting human–multi-robot team collaboration. Artif. Intell. 2017, 252, 211–231. [Google Scholar] [CrossRef]
- Ramchurn, S.D.; Wu, F.; Jiang, W.; Fischer, J.E.; Reece, S.; Roberts, S.; Rodden, T.; Greenhalgh, C.; Jennings, N.R. Human–agent collaboration for disaster response. Auton. Agents Multi-Agent Syst. 2016, 30, 82–111. [Google Scholar]
- Rosenfeld, A.; Richardson, A. Why, Who, What, When and How about Explainability in Human-Agent Systems. In Proceedings of the 19th International Conference on Autonomous Agents and MultiAgent Systems, Auckland, New Zealand, 9–13 May 2020; pp. 2161–2164. [Google Scholar]
- Schilling, M.; Kopp, S.; Wachsmuth, S.; Wrede, B.; Ritter, H.; Brox, T.; Nebel, B.; Burgard, W. Towards A Multidimensional Perspective on Shared Autonomy. In The 2016 AAAI Fall Symposium Series: Shared Autonomy in Research and Practice; Technical Report FS-16-05; The AAAI Press: Palo Alto, CA, USA, 2016; pp. 338–344. [Google Scholar]
- Schilling, M.; Burgard, W.; Muelling, K.; Wrede, B.; Ritter, H. Editorial: Shared Autonomy— Learning of Joint Action and Human-Robot Collaboration. Front. Neurorobot. 2019, 13. [Google Scholar] [CrossRef]
- Rousseau, D.M.; Sitkin, S.B.; Burt, R.S.; Camerer, C. Not so different after all: A cross-discipline view of trust. Acad. Manag. Rev. 1998, 23, 393–404. [Google Scholar]
- Mayer, R.C.; Davis, J.H.; Schoorman, F.D. An Integrative Model of Organizational Trust. Acad. Manag. Rev. 1995, 20, 709–734. [Google Scholar] [CrossRef]
- McAllister, D.J. Affect- and Cognition-Based Trust as Foundations for Interpersonal Cooperation in Organizations. Acad. Manag. J. 1995, 38, 24–59. [Google Scholar] [CrossRef] [Green Version]
- Schwaninger, I.; Fitzpatrick, G.; Weiss, A. Exploring Trust in Human-Agent Collaboration. In Proceedings of the 17th European Conference on Computer-Supported Cooperative Work, Salzburg, Austria, 8–12 June 2019; p. 12. [Google Scholar]
- Gefen, D.; Straub, D.W. Consumer trust in B2C e-Commerce and the importance of social presence: Experiments in e-Products and e-Services. Omega 2004, 32, 407–424. [Google Scholar]
- Handy, C. Trust and the virtual organization. Long Range Plan. 1995, 28, 126. [Google Scholar]
- Bente, G.; Rüggenberg, S.; Krämer, N.C.; Eschenburg, F. Avatar-Mediated Networking: Increasing Social Presence and Interpersonal Trust in Net-Based Collaborations. Hum. Commun. Res. 2008, 34, 287–318. [Google Scholar] [CrossRef]
- Johnson, D.; Grayson, K. Cognitive and affective trust in service relationships. J. Bus. Res. 2005, 58, 500–507. [Google Scholar] [CrossRef]
- Lewis, J.D.; Weigert, A. Trust as a social reality. Soc. Forces 1985, 63, 967–985. [Google Scholar]
- Lee, J.D.; See, K.A. Trust in Automation: Designing for Appropriate Reliance. Hum. Factors 2004, 46, 50–80. [Google Scholar]
- Gulati, S.; Sousa, S.; Lamas, D. Modelling Trust: An Empirical Assessment. In Human-Computer Interaction—INTERACT 2017; Lecture Notes in Computer Science; Bernhaupt, R., Dalvi, G., Joshi, A.K., Balkrishan, D., O’Neill, J., Winckler, M., Eds.; Springer International Publishing: Cham, Switzerland, 2017; Volume 10516, pp. 40–61. [Google Scholar] [CrossRef] [Green Version]
- Kok, B.C.; Soh, H. Trust in Robots: Challenges and Opportunities. Curr. Robot. Rep. 2020. [Google Scholar] [CrossRef]
- Hancock, P.A.; Billings, D.R.; Schaefer, K.E.; Chen, J.Y.C.; de Visser, E.J.; Parasuraman, R. A Meta-Analysis of Factors Affecting Trust in Human-Robot Interaction. Hum. Factors 2011, 53, 517–527. [Google Scholar] [CrossRef] [PubMed]
- Lee, J.; Moray, N. Trust, control strategies and allocation of function in human–machine systems. Ergonomics 1992, 35, 1243–1270. [Google Scholar] [CrossRef] [PubMed]
- Rahman, S.M.M.; Sadrfaridpour, B.; Wang, Y. Trust-Based Optimal Subtask Allocation and Model Predictive Control for Human-Robot Collaborative Assembly in Manufacturing. In Volume 2: Diagnostics and Detection; Drilling; Dynamics and Control of Wind Energy Systems; Energy Harvesting; Estimation and Identification; Flexible and Smart Structure Control; Fuels Cells/Energy Storage; Human Robot Interaction; HVAC Building Energy Management; Industrial Applications; Intelligent Transportation Systems; Manufacturing; Mechatronics; Modelling and Validation; Motion and Vibration Control Applications; American Society of Mechanical Engineers: Columbus, OH, USA, 2015; p. V002T32A004. [Google Scholar] [CrossRef]
- Rahman, S.M.M.; Wang, Y.; Walker, I.D.; Mears, L.; Pak, R.; Remy, S. Trust-based compliant robot-human handovers of payloads in collaborative assembly in flexible manufacturing. In Proceedings of the 2016 IEEE International Conference on Automation Science and Engineering (CASE), Fort Worth, TX, USA, 21–25 August 2016; pp. 355–360. [Google Scholar] [CrossRef]
- Law, T. Measuring Relational Trust in Human-Robot Interactions. In Proceedings of the Companion of the 2020 ACM/IEEE International Conference on Human-Robot Interaction, L’Aquila, Italy, 7–9 October 2020; pp. 579–581. [Google Scholar] [CrossRef]
- Jung, M.F. Affective Grounding in Human-Robot Interaction. In Proceedings of the 2017 ACM/IEEE International Conference on Human-Robot Interaction—HRI ‘17, Vienna, Austria, 6–9 March 2017; pp. 263–273. [Google Scholar] [CrossRef]
- Walker, I.D.; Mears, L.; Mizanoor, R.S.M.; Pak, R.; Remy, S.; Wang, Y. Robot-Human Handovers Based on Trust. In Proceedings of the 2015 Second International Conference on Mathematics and Computers in Sciences and in Industry (MCSI), Sliema, Malta, 17 August 2015; pp. 119–124. [Google Scholar] [CrossRef]
- Vinanzi, S.; Patacchiola, M.; Chella, A.; Cangelosi, A. Would a robot trust you? Developmental robotics model of trust and theory of mind. Philos. Trans. R. Soc. B Biol. Sci. 2019, 374, 20180032. [Google Scholar] [CrossRef]
- Argall, B.D.; Murphy, T.D. Computable Trust in Human Instruction. In Proceedings of the AAAI Fall Symposia, Arlington, VA, USA, 13–15 November 2014; p. 2. [Google Scholar]
- Basu, C.; Singhal, M. Trust Dynamics in Human Autonomous Vehicle Interaction: A Review of Trust Models; 2016 AAAI Spring Symposium Series; The AAAI Press: Palo Alto, CA, USA, 2016; p. 7. [Google Scholar]
- Alhaji, B.; Rausch, A.; Prilla, M. Toward Mutual Trust Modeling in Human-Robot Collaboration. arXiv 2020, arXiv:2011.01056. [Google Scholar]
- Alam, M.; Samad, M.D.; Vidyaratne, L.; Glandon, A.; Iftekharuddin, K.M. Survey on Deep Neural Networks in Speech and Vision Systems. arXiv 2019, arXiv:1908.07656. [Google Scholar]
- Grigorescu, S.; Trasnea, B.; Cocias, T.; Macesanu, G. A survey of deep learning techniques for autonomous driving. J. Field Robot. 2020, 37, 362–386. [Google Scholar]
- Li, J.; Cheng, H.; Guo, H.; Qiu, S. Survey on artificial intelligence for vehicles. Automot. Innov. 2018, 1, 2–14. [Google Scholar]
- Singh, H.P.; Dimri, P.; Tiwari, S.; Saraswat, M. Segmentation Techniques through Machine Based Learning for Latent Fingerprint Indexing and Identification. JSIR 2020, 79, 201–208. [Google Scholar]
- ISO. 26262: Road Vehicles—Functional Safety; Standard, International Organization for Standardization: Geneva, Switzerland, 2011. [Google Scholar]
- ISO. 21448: Road Vehicles—Safety of the Intended Functionality; Standard, International Organization for Standardization: Geneva, Switzerland, 2019. [Google Scholar]
- Fulton, N.; Platzer, A. Safe Reinforcement Learning via Formal Methods: Toward Safe Control through Proof and Learning. In Proceedings of the Thirty-Second AAAI Conference on Artificial Intelligence (AAAI-18), New Orleans, LA, USA, 2–7 February 2018; pp. 6485–6492. [Google Scholar]
- Alshiekh, M.; Bloem, R.; Ehlers, R.; Könighofer, B.; Niekum, S.; Topcu, U. Safe Reinforcement Learning via Shielding. In Proceedings of the Thirty-Second AAAI Conference on Artificial Intelligence (AAAI-18), New Orleans, LA, USA, 2–7 February 2018; pp. 2669–2678. [Google Scholar]
- Aniculaesei, A.; Grieser, J.; Rausch, A.; Rehfeldt, K.; Warnecke, T. Towards a holistic software systems engineering approach for dependable autonomous systems. In Proceedings of the 1st International Workshop on Software Engineering for AI in Autonomous Systems—SEFAIS ‘18, Madrid, Spain, 22–30 May 2018; pp. 23–30. [Google Scholar] [CrossRef] [Green Version]
- Wagner, A.R.; Robinette, P.; Howard, A. Modeling the Human-Robot Trust Phenomenon: A Conceptual Framework based on Risk. ACM Trans. Interact. Intell. Syst. 2018, 8, 1–24. [Google Scholar] [CrossRef]
- Schlossman, R.; Kim, M.; Topcu, U.; Sentis, L. Toward Achieving Formal Guarantees for Human-Aware Controllers in Human-Robot Interactions. arXiv 2019, arXiv:1903.01350. [Google Scholar]
- Askarpour, M.; Mandrioli, D.; Rossi, M.; Vicentini, F. SAFER-HRC: Safety Analysis through Formal vERification in Human-Robot Collaboration. In Computer Safety, Reliability, and Security; Lecture Notes in Computer Science; Skavhaug, A., Guiochet, J., Bitsch, F., Eds.; Springer International Publishing: Cham, Switzerland, 2016; pp. 283–295. [Google Scholar] [CrossRef] [Green Version]
- Askarpour, M.; Mandrioli, D.; Rossi, M.; Vicentini, F. Formal model of human erroneous behavior for safety analysis in collaborative robotics. Robot. Comput. Integr. Manuf. 2019, 57, 465–476. [Google Scholar] [CrossRef]
- Stankovic, J. Research directions for the internet of things. IEEE Internet Things J. 2014, 1, 3–9. [Google Scholar]
- Stankovic, J.; Munir, S.; Liang, C.; Lin, S. Cyber physical system challenges for human-in-the-loop control. In Proceedings of the 8th International Workshop on Feedback Computing, San Jose, CA, USA, 24–28 June 2013. [Google Scholar]
- McRuer, D.; Jex, H. A review of quasi-linear pilot models. IEEE Trans. Hum. Factors Electron. 1967, 3, 231–249. [Google Scholar]
- McRuer, D.; Krendel, E. The human operator as a servo system element. J. Frankl. Inst. 1959, 267, 381–403. [Google Scholar]
- McRuer, D.; Krendel, E. Mathematical Models of Human Pilot Behavior; Advisory Group for Aerospace Research and Development Neuilly-Sur-Seine: Neuilly-Sur-Seine, France, 1974. [Google Scholar]
- Wray, R.E.; Chong, R.S. Comparing Cognitive Models and Human Behavior Models: Two Computational Tools for Expressing Human Behavior. J. Aerosp. Comput., Inf. Commun. 2007, 4, 836–852. [Google Scholar] [CrossRef]
- Shanahan, M. Perception as abduction: Turning sensor data into meaningful representation. Cogn. Sci. 2005, 29, 103–134. [Google Scholar] [PubMed] [Green Version]
- Winfield, A. Experiments in artificial theory of mind: From safety to story-telling. Front. Robot. AI 2018, 5, 75. [Google Scholar]
- Nunes, D.S.; Zhang, P.; Sa Silva, J. A Survey on Human-in-the-Loop Applications Towards an Internet of All. IEEE Commun. Surv. Tutor. 2015, 17, 944–965. [Google Scholar] [CrossRef]
- Eskins, D.; Sanders, W.H. The Multiple-Asymmetric-Utility System Model: A Framework for Modeling Cyber-Human Systems. In Proceedings of the 2011 Eighth International Conference on Quantitative Evaluation of SysTems, Aachen, Germany, 5–8 September 2011; pp. 233–242. [Google Scholar] [CrossRef]
- Jacq, A.; Johal, W.; Dillenbourg, P.; Paiva, A. Cognitive Architecture for Mutual Modelling. arXiv 2016, arXiv:1602.06703. [Google Scholar]
- Braunagel, C.; Rosenstiel, W.; Kasneci, E. Ready for take-over? A new driver assistance system for an automated classification of driver take-over readiness. IEEE Intell. Transp. Syst. Mag. 2017, 9, 10–22. [Google Scholar]
- Mioch, T.; Kroon, L.; Neerincx, M. Driver readiness model for regulating the transfer from automation to human control. In Proceedings of the 22nd International Conference on Intelligent User Interfaces, Limassol, Cyprus, 13–16 March 2017; pp. 205–213. [Google Scholar]
- Deo, N.; Trivedi, M. Looking at the driver/rider in autonomous vehicles to predict take-over readiness. IEEE Trans. Intell. Veh. 2019, 5, 41–52. [Google Scholar]
- Watson, J.M.; Memmott, M.G.; Moffitt, C.C.; Coleman, J.; Turrill, J.; Fernández, Á.; Strayer, D.L. On working memory and a productivity illusion in distracted driving. J. Appl. Res. Mem. Cogn. 2016, 5, 445–453. [Google Scholar]
- Lenskiy, A.; Lee, J.S. Driver’s eye blinking detection using novel color and texture segmentation algorithms. Int. J. Control Autom. Syst. 2012, 10, 317–327. [Google Scholar]
- Liu, A.; Li, Z.; Wang, L.; Zhao, Y. A practical driver fatigue detection algorithm based on eye state. In Proceedings of the 2010 Asia Pacific Conference on Postgraduate Research in Microelectronics and Electronics (PrimeAsia), Shanghai, China, 22–24 September 2010; pp. 235–238. [Google Scholar]
- Yan, C.; Coenen, F.; Zhang, B. Driving posture recognition by convolutional neural networks. IET Comput. Vis. 2016, 10, 103–114. [Google Scholar]
- Yüce, A.; Gao, H.; Cuendet, G.; Thiran, J.P. Action Units and Their Cross-Correlations for Prediction of Cognitive Load during Driving. IEEE Trans. Affect. Comput. 2017, 8, 161–175. [Google Scholar]
- Satyanarayanan, M. Pervasive computing: Vision and challenges. IEEE Pers. Commun. 2001, 8, 10–17. [Google Scholar]
- Schmidt, A.; Beigl, M.; Gellersen, H.W. There is more to context than location. Comput. Graph. 1999, 23, 893–901. [Google Scholar] [CrossRef] [Green Version]
- Lance, B.J.; Kerick, S.E.; Ries, A.J.; Oie, K.S.; McDowell, K. Brain–Computer Interface Technologies in the Coming Decades. Proc. IEEE 2012, 100, 1585–1599. [Google Scholar] [CrossRef]
- McCaffrey, C.; Chevalerias, O.; O’Mathuna, C.; Twomey, K. Swallowable-capsule technology. IEEE Pervasive Comput. 2008, 7, 23–29. [Google Scholar]
- Scalise, L.; Bernacchia, N.; Ercoli, I.; Marchionni, P. Heart rate measurement in neonatal patients using a webcamera. In Proceedings of the 2012 IEEE International Symposium on Medical Measurements and Applications Proceedings, Budapest, Hungary , 18–19 May 2012; pp. 1–4. [Google Scholar]
- Morbiducci, U.; Scalise, L.; De Melis, M.; Grigioni, M. Optical vibrocardiography: A novel tool for the optical monitoring of cardiac activity. Ann. Biomed. Eng. 2007, 35, 45–58. [Google Scholar]
- Chen, M.; O’Sullivan, J.A.; Singla, N.; Sirevaag, E.J.; Kristjansson, S.D.; Lai, P.H.; Kaplan, A.D.; Rohrbaugh, J.W. Laser doppler vibrometry measures of physiological function: Evaluation of biometric capabilities. IEEE Trans. Inf. Forensics Secur. 2010, 5, 449–460. [Google Scholar]
- Mignanelli, L.; Rembe, C. Non-contact Health Monitoring with LDV. In Laser Doppler Vibrometry for Non-Contact Diagnostics; Kroschel, K., Ed.; Springer International Publishing: Cham, Switzerland, 2020; Volume 9, pp. 1–8. [Google Scholar] [CrossRef]
- Endsley, M. Direct measurement of situation awareness: Validity and use of SAGAT. In Situational Awareness; Routledge: London, UK, 2017; pp. 129–156. [Google Scholar]
- Endsley, M. Situation awareness global assessment technique (SAGAT). In Proceedings of the IEEE 1988 National Aerospace and Electronics Conference, Dayton, OH, USA, 23–27 May 1988; pp. 789–795. [Google Scholar]
- Czerwinski, M.; Cutrell, E.; Horvitz, E. Instant messaging and interruption: Influence of task type on performance. In Proceedings of the OZCHI 2000 Conference Proceedings, Sydney, Australia, 4–8 December 2000; Volume 356, pp. 361–367. [Google Scholar]
- Khushaba, R.; Kodagoda, S.; Lal, S.; Dissanayake, G. Driver drowsiness classification using fuzzy wavelet-packet-based feature-extraction algorithm. IEEE Trans. Biomed. Eng. 2011, 58, 121–131. [Google Scholar] [PubMed] [Green Version]
- Lin, F.C.; Ko, L.W.; Chuang, C.H.; Su, T.P.; Lin, C.T. Generalized EEG-Based Drowsiness Prediction System by Using a Self-Organizing Neural Fuzzy System. IEEE Trans. Circuits Syst. I Regul. Pap. 2012, 59, 2044–2055. [Google Scholar] [CrossRef]
- Borghini, G.; Astolfi, L.; Vecchiato, G.; Mattia, D.; Babiloni, F. Measuring neurophysiological signals in aircraft pilots and car drivers for the assessment of mental workload, fatigue and drowsiness. Neurosci. Biobehav. Rev. 2014, 44, 58–75. [Google Scholar] [PubMed]
- Park, S.; Whang, M. Infrared camera-based non-contact measurement of brain activity from pupillary rhythms. Front. Physiol. 2018, 9, 1400. [Google Scholar] [PubMed]
- Rohweder, N.O.; Gertheiss, J.; Rembe, C. Towards a remote EEG for human–machine-interfaces. In Forum Bildverarbeitung 2020; Längle, T., Ed.; KIT Scientific Publishing: Karlsruhe, Germany, 2020. [Google Scholar]
- Akyildiz, I.F.; Su, W.; Sankarasubramaniam, Y.; Cayirci, E. Wireless sensor networks: A survey. Comput. Netw. 2002, 38, 393–422. [Google Scholar] [CrossRef] [Green Version]
- Chen, M.; Gonzalez, S.; Vasilakos, A.; Cao, H.; Leung, V.C.M. Body Area Networks: A Survey. Mobile Netw. Appl. 2011, 16, 171–193. [Google Scholar] [CrossRef]
- Xu, B.; Li, J.; Wong, Y.; Zhao, Q.; Kankanhalli, M.S. Interact as You Intend: Intention-Driven Human-Object Interaction Detection. IEEE Trans. Multimed. 2020, 22, 1423–1432. [Google Scholar] [CrossRef] [Green Version]
- Van Laerhoven, K.; Gellersen, H.W. Spine versus Porcupine: A Study in Distributed Wearable Activity Recognition. In Proceedings of the Eighth International Symposium on Wearable Computers, Arlington, VA, USA, 31 October–3 November 2004; pp. 142–149. [Google Scholar] [CrossRef] [Green Version]
- Schilit, B.; Adams, N.; Want, R. Context-aware computing applications. In Proceedings of the 1994 First Workshop on Mobile Computing Systems and Applications, Santa Cruz, CA, USA, 8–9 December 1994; pp. 85–90. [Google Scholar]
- Paganelli, F.; Giuli, D. An Evaluation of Context-Aware Infomobility Systems. In Context-Aware Mobile and Ubiquitous Computing for Enhanced Usability; IGI Global: Hershey, PA, USA, 2009. [Google Scholar] [CrossRef] [Green Version]
- Sørensen, H.; Goldsmith, J.; Sangalli, L. An introduction with medical applications to functional data analysis. Stat. Med. 2013, 32, 5222–5240. [Google Scholar]
- Scheipl, F.; Gertheiss, J.; Greven, S. Generalized functional additive mixed models. Electron. J. Stat. 2016, 10, 1455–1492. [Google Scholar] [CrossRef]
- Xue, H.; Huynh, D.Q.; Reynolds, M. SS-LSTM: A hierarchical LSTM model for pedestrian trajectory prediction. In Proceedings of the 2018 IEEE Winter Conference on Applications of Computer Vision (WACV), Lake Tahoe, NV, USA, 12–15 March 2018; pp. 1186–1194. [Google Scholar]
- Karim, F.; Majumdar, S.; Darabi, H.; Chen, S. LSTM Fully Convolutional Networks for Time Series Classification. IEEE Access 2018, 6, 1662–1669. [Google Scholar] [CrossRef]
- Mummadi, C.K.; Leo, F.P.P.; Verma, K.D.; Kasireddy, S.; Scholl, P.M.; Kempfle, J.; Laerhoven, K.V. Real-time and embedded detection of hand gestures with an IMU-based glove. Inform. Multidiscip. Digit. Publ. Inst. 2018, 5, 28. [Google Scholar]
- Carlson, T.; Demiris, Y. Collaborative control for a robotic wheelchair: Evaluation of performance, attention, and workload. IEEE Trans. Syst., Man Cybern. Part B (Cybern.) 2012, 42, 876–888. [Google Scholar]
- Ajoudani, A.; Zanchettin, A.M.; Ivaldi, S.; Albu-Schäffer, A.; Kosuge, K.; Khatib, O. Progress and prospects of the human–robot collaboration. Auton. Robots 2018, 42, 957–975. [Google Scholar] [CrossRef] [Green Version]
- Pereira, A.; Althoff, M. Calculating human reachable occupancy for guaranteed collision-free planning. In Proceedings of the IEEE/RSJ International Conference on Intelligent Robots and Systems (IROS), Vancouver, BC, Canada, 24–28 September 2017; pp. 4473–4480. [Google Scholar] [CrossRef] [Green Version]
- Zanchettin, A.M.; Rocco, P. Probabilistic inference of human arm reaching target for effective human–robot collaboration. In Proceedings of the 2017 IEEE/RSJ International Conference on Intelligent Robots and Systems (IROS), Vancouver, BC, Canada, 24–28 September 2017; pp. 6595–6600. [Google Scholar]
- Johora, F.T.; Müller, J.P. Zone-Specific Interaction Modeling of Pedestrians and Cars in Shared Spaces. Transp. Res. Procedia 2020, 47, 251–258. [Google Scholar] [CrossRef]
- Vizzari, G.; Manenti, L.; Ohtsuka, K.; Shimura, K. An agent-based pedestrian and group dynamics model applied to experimental and real-world scenarios. J. Intell. Transp. Syst. 2015, 19, 32–45. [Google Scholar]
- Schöbel, A.; Pätzold, J.; Müller, J.P. The Trickle-In Effect: Modeling Passenger Behavior in Delay Management. In Proceedings of the 19th Symposium on Algorithmic Approaches for Transportation Modelling, Optimization, and Systems (ATMOS 2019), Munich, Germany, 12–13,September 2019; pp. 1–15. [Google Scholar] [CrossRef]
- Zhang, J.; Liu, H.; Chang, Q.; Wang, L.; Gao, R.X. Recurrent neural network for motion trajectory prediction in human–robot collaborative assembly. CIRP Ann. 2020, 69, 9–12. [Google Scholar]
- Richter, A.; Reinhardt, A.; Reinhardt, D. Privacy-Preserving Human-Machine Co-existence on Smart Factory Shop Floors. In International Workshop on Simulation Science; Springer: Cham, Germany, 2019; pp. 3–20. [Google Scholar]
- Li, Y.; Chen, M.; Dou, Z.; Zheng, X.; Cheng, Y.; Mebarki, A. A review of cellular automata models for crowd evacuation. Phys. A Stat. Mech. Appl. 2019, 526, 120752. [Google Scholar]
- Rudenko, A.; Palmieri, L.; Lilienthal, A.J.; Arras, K.O. Human motion prediction under social grouping constraints. In Proceedings of the 2018 IEEE/RSJ International Conference on Intelligent Robots and Systems (IROS), Madrid, Spain, 1–5 October 2018; pp. 3358–3364. [Google Scholar]
- Coscia, P.; Castaldo, F.; Palmieri, F.A.; Alahi, A.; Savarese, S.; Ballan, L. Long-term path prediction in urban scenarios using circular distributions. Image Vis. Comput. 2018, 69, 81–91. [Google Scholar]
- Kooij, J.F.; Flohr, F.; Pool, E.A.; Gavrila, D.M. Context-based path prediction for targets with switching dynamics. Int. J. Comput. Vis. 2019, 127, 239–262. [Google Scholar]
- Chen, X.; Treiber, M.; Kanagaraj, V.; Li, H. Social force models for pedestrian traffic–state of the art. Transp. Rev. 2018, 38, 625–653. [Google Scholar]
- Johora, F.T.; Cheng, H.; Müller, J.P.; Sester, M. An Agent-Based Model for Trajectory Modelling in Shared Spaces: A Combination of Expert-Based and Deep Learning Approaches. In Proceedings of the 19th International Conference on Autonomous Agents and Multiagent Systems, AAMAS ‘20, Auckland, New Zealand, 9–13 May 2020; pp. 1878–1880. [Google Scholar]
- Kucner, T.P.; Magnusson, M.; Schaffernicht, E.; Bennetts, V.H.; Lilienthal, A.J. Enabling flow awareness for mobile robots in partially observable environments. IEEE Robot. Autom. Lett. 2017, 2, 1093–1100. [Google Scholar]
- Rehder, E.; Wirth, F.; Lauer, M.; Stiller, C. Pedestrian prediction by planning using deep neural networks. In Proceedings of the 2018 IEEE International Conference on Robotics and Automation (ICRA), Brisbane, QLD, Australia, 21–25 May 2018; pp. 1–5. [Google Scholar]
- Kato, Y.; Nagano, Y.; Yokoyama, H. A pedestrian model in human–robot coexisting environment for mobile robot navigation. In Proceedings of the 2017 IEEE/SICE International Symposium on System Integration (SII), Taipei, Taiwan, 11–14 December 2017; pp. 992–997. [Google Scholar] [CrossRef]
- Antonucci, A.; Fontanelli, D. Towards a Predictive Behavioural Model for Service Robots in Shared Environments. In Proceedings of the 2018 IEEE Workshop on Advanced Robotics and its Social Impacts (ARSO), Genova, Italy, 27–29 September 2018; pp. 9–14. [Google Scholar]
- Medina, J.R.; Lorenz, T.; Hirche, S. Considering Human Behavior Uncertainty and Disagreements in Human–Robot Cooperative Manipulation. In Trends in Control and Decision-Making for Human–Robot Collaboration Systems; Wang, Y., Zhang, F., Eds.; Springer International Publishing: Cham, Switzerland, 2017; pp. 207–240. [Google Scholar] [CrossRef]
- Krüger, J.; Lien, T.K.; Verl, A. Cooperation of human and machines in assembly lines. CIRP Ann. 2009, 58, 628–646. [Google Scholar] [CrossRef]
- Donadio, F.; Frejaville, J.; Larnier, S.; Vetault, S. Human-robot collaboration to perform aircraft inspection in working environment. In Proceedings of the 5th International Conference on Machine Control and Guidance (MCG 2016), Vichy, France, 5–6,October 2016; p. 9. [Google Scholar]
- Gely, C.; Trentesaux, D.; Le Mortellec, A. Maintenance of the Autonomous Train: A Human-Machine Cooperation Framework. In Towards User-Centric Transport in Europe 2; Müller, B., Meyer, G., Eds.; Springer International Publishing: Cham, Switzerland, 2020; pp. 135–148. [Google Scholar] [CrossRef]
- Bogue, R. Robots in recycling and disassembly. Ind. Robot 2019, 46, 461–466. [Google Scholar] [CrossRef]
- Bogue, R. Robots in healthcare. Ind. Robot 2011, 38, 218–223. [Google Scholar] [CrossRef]
- Delmerico, J.; Mintchev, S.; Giusti, A.; Gromov, B.; Melo, K.; Horvat, T.; Cadena, C.; Hutter, M.; Ijspeert, A.; Floreano, D.; et al. The current state and future outlook of rescue robotics. J. Field Robot. 2019, 36, 1171–1191. [Google Scholar] [CrossRef]
- Schwindt, C. Resource Allocation in Project Management; GOR-Publications, Springer: Berlin/Heidelberg, Germany, 2005. [Google Scholar]
- Schwindt, C.; Zimmermann, J. (Eds.) Handbook on Project Management and Scheduling Vol. 2; International Handbooks on Information Systems; Springer International Publishing: Cham, Switzerland, 2015. [Google Scholar] [CrossRef]
- Gombolay, M.; Bair, A.; Huang, C.; Shah, J. Computational design of mixed-initiative human–robot teaming that considers human factors: Situational awareness, workload, and workflow preferences. Int. J. Robot. Res. 2017, 36, 597–617. [Google Scholar] [CrossRef]
- Mohan, S. Scheduling part-time personnel with availability restrictions and preferences to maximize employee satisfaction. Math. Comput. Model. 2008, 48, 1806–1813. [Google Scholar] [CrossRef]
- Längle, T.; Wörn, H. Human-Robot Cooperation Using Multi-Agent-Systems. J. Intell. Robot. Syst. 2001, 32, 143–160. [Google Scholar] [CrossRef]
- Damacharla, P.; Javaid, A.Y.; Gallimore, J.J.; Devabhaktuni, V.K. Common metrics to benchmark human–machine teams (HMT): A review. IEEE Access 2018, 6, 38637–38655. [Google Scholar] [CrossRef]
- Mas-Colell, A.; Whinston, M.D.; Green, J.R. Microeconomic Theory; Oxford University Press: Oxford, UK, 1995. [Google Scholar]
- Bruni, M.E.; Beraldi, P.; Guerriero, F. The Stochastic Resource-Constrained Project Scheduling Problem. In Handbook on Project Management and Scheduling Vol. 2; Schwindt, C., Zimmermann, J., Eds.; International Handbooks on Information Systems; Springer International Publishing: Cham, Switzerland, 2015; pp. 811–835. [Google Scholar] [CrossRef]
- Möhring, R.H. Scheduling under Uncertainty: Optimizing against a Randomizing Adversary. In Approximation Algorithms for Combinatorial Optimization; Goos, G., Hartmanis, J., van Leeuwen, J., Jansen, K., Khuller, S., Eds.; Springer: Berlin/Heidelberg, Germany, 2000; Volume 1913, pp. 15–26. [Google Scholar] [CrossRef]
- Artigues, C.; Leus, R.; Nobibon, F.T. Robust Optimization for the Resource-Constrained Project Scheduling Problem with Duration Uncertainty. In Handbook on Project Management and Scheduling Vol. 2; Schwindt, C., Zimmermann, J., Eds.; International Handbooks on Information Systems; Springer International Publishing: Cham, Switzerland, 2015; pp. 875–908. [Google Scholar] [CrossRef]
- Özdamar, L.; Alanya, E. Uncertainty modelling in software development projects (with case study). Ann. Oper. Res. 2001, 102, 157–178. [Google Scholar] [CrossRef]
- T’kindt, V.; Billaut, J.C. Multicriteria Scheduling: Theory, Models and Algorithms; Springer: Berlin/Heidelberg, Germany, 2006. [Google Scholar]
- Agnetis, A.; Billaut, J.C.; Gawiejnowicz, S.; Pacciarelli, D.; Soukhal, A. Multiagent Scheduling; Springer: Berlin/Heidelberg, Germany, 2014. [Google Scholar] [CrossRef]
- Immorlica, N.; Li, L.E.; Mirrokni, V.S.; Schulz, A.S. Coordination mechanisms for selfish scheduling. Theor. Comput. Sci. 2009, 410, 1589–1598. [Google Scholar] [CrossRef] [Green Version]
- Fink, A.; Homberger, J. Decentralized Multi-Project Scheduling. In Handbook on Project Management and Scheduling Vol. 2; Schwindt, C., Zimmermann, J., Eds.; International Handbooks on Information Systems; Springer International Publishing: Cham, Switzerland, 2015; pp. 685–706. [Google Scholar] [CrossRef]
- Wellman, M.P.; Walsh, W.E.; Wurman, P.R.; MacKie-Mason, J.K. Auction protocols for decentralized scheduling. Games Econ. Behav. 2001, 35, 271–303. [Google Scholar] [CrossRef] [Green Version]
- Homberger, J. A (μ, λ)-coordination mechanism for agent-based multi-project scheduling. OR Spectr. 2012, 34, 107–132. [Google Scholar] [CrossRef]
- Merz, F.; Schwindt, C.; Westphal, S.; Zimmermann, J. A multi-round auction for staff to job assignment under myopic best response dynamics. In Proceedings of the International Conference of Industrial Engineering and Engineering Management (IEEM 2020), Singapore, 14–17 December 2020. [Google Scholar]
- Brandt, F.; Conitzer, V.; Endriss, U.; Lang, J.; Procaccia, A.D. Handbook of Computational Social Choice; Cambridge University Press: Cambridge, UK, 2016. [Google Scholar]
- Gallien, J.; Wein, L.M. A smart market for industrial procurement with capacity constraints. Manag. Sci. 2005, 51, 76–91. [Google Scholar] [CrossRef] [Green Version]
- Sabater-Mir, J.; Vercounter, L. Chapter 9: Trust and reputation in multiagent systems. In Multiagent Systems; Weiss, G., Ed.; MIT Press: Cambridge, CA, USA, 2013. [Google Scholar]
- Alos-Ferrer, C.; Farolfi, F. Trust games and beyond. Front. Neurosci. 2019, 13, 865–889. [Google Scholar] [CrossRef]
- Hartmann, S.; Briskorn, D. A survey of variants and extensions of the resource-constrained project scheduling problem. Eur. J. Oper. Res. 2010, 207, 1–14. [Google Scholar] [CrossRef] [Green Version]
- Neumann, K.; Schwindt, C. Project scheduling with inventory constraints. Math. Methods Oper. Res. (ZOR) 2002, 56, 513–533. [Google Scholar] [CrossRef]
- Neumann, K.; Schwindt, C.; Zimmermann, J. Project Scheduling with Time Windows and Scarce Resources, 2nd ed.; Lecture Notes in Economics and Mathematical Systems; Springer: Berlin/Heidelberg, Germany, 2003. [Google Scholar]
- Weiss, I. The Resource Transfer Problem: A Framework for Integrated Scheduling and Routing Problems; Springer International Publishing: Basel, Switzerland, 2019. [Google Scholar]
- Macal, C.M.; North, M.J. Tutorial on agent-based modelling and simulation. J. Simul. 2010, 4, 151–162. [Google Scholar] [CrossRef]
- Briem, L.; Mallig, N.; Vortisch, P. Creating an integrated agent-based travel demand model by combining mobiTopp and MATSim. Procedia Comput. Sci. 2019, 151, 776–781. [Google Scholar]
- Ziemke, D.; Kaddoura, I.; Nagel, K. The MATSim Open Berlin Scenario: A multimodal agent-based transport simulation scenario based on synthetic demand modeling and open data. Procedia Comput. Sci. 2019, 151, 870–877. [Google Scholar]
- Ahmed, S.; Johora, F.T.; Müller, J.P. Investigating the Role of Pedestrian Groups in Shared Spaces through Simulation Modeling; Simulation, S., Gunkelmann, N., Baum, M., Eds.; Springer International Publishing: Cham, Switzerland, 2020; pp. 52–69. [Google Scholar]
- Sebe, S.M.; Kraus, P.; Müller, J.P.; Westphal, S. Cross-provider Platoons for Same-day Delivery. In Proceedings of the 5th International Conference on Vehicle Technology and Intelligent Transport Systems, VEHITS 2019, Heraklion, Crete, Greece, 3–5 May 2019; pp. 106–116. [Google Scholar] [CrossRef]
- Hesselmann, C.; Kehl, S.; Stiefel, P.; Müller, J.P. Decentralized handling of conflicts in multi-brand engineering change management. In Proceedings of the 21st International Conference on Engineering Design (ICED 17), Vancouver, BC, Canada, 21–25 August 2017; Volume 4, pp. 683–692. [Google Scholar]
- Kraus, S.; Azaria, A.; Fiosina, J.; Greve, M.; Hazon, N.; Kolbe, L.; Lembcke, T.B.; Müller, J.P.; Schleibaum, S.; Vollrath, M. AI for Explaining Decisions in Multi-Agent Environment. In Proceedings of the Thirty-Fourth AAAI Conference on Artificial Intelligence, AAAI 2020, New York, NY, USA, 7–12 February 2020. [Google Scholar]
Publisher’s Note: MDPI stays neutral with regard to jurisdictional claims in published maps and institutional affiliations. |
© 2020 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Alhaji, B.; Beecken, J.; Ehlers, R.; Gertheiss, J.; Merz, F.; Müller, J.P.; Prilla, M.; Rausch, A.; Reinhardt, A.; Reinhardt, D.; et al. Engineering Human–Machine Teams for Trusted Collaboration. Big Data Cogn. Comput. 2020, 4, 35. https://doi.org/10.3390/bdcc4040035
Alhaji B, Beecken J, Ehlers R, Gertheiss J, Merz F, Müller JP, Prilla M, Rausch A, Reinhardt A, Reinhardt D, et al. Engineering Human–Machine Teams for Trusted Collaboration. Big Data and Cognitive Computing. 2020; 4(4):35. https://doi.org/10.3390/bdcc4040035
Chicago/Turabian StyleAlhaji, Basel, Janine Beecken, Rüdiger Ehlers, Jan Gertheiss, Felix Merz, Jörg P. Müller, Michael Prilla, Andreas Rausch, Andreas Reinhardt, Delphine Reinhardt, and et al. 2020. "Engineering Human–Machine Teams for Trusted Collaboration" Big Data and Cognitive Computing 4, no. 4: 35. https://doi.org/10.3390/bdcc4040035
APA StyleAlhaji, B., Beecken, J., Ehlers, R., Gertheiss, J., Merz, F., Müller, J. P., Prilla, M., Rausch, A., Reinhardt, A., Reinhardt, D., Rembe, C., Rohweder, N.-O., Schwindt, C., Westphal, S., & Zimmermann, J. (2020). Engineering Human–Machine Teams for Trusted Collaboration. Big Data and Cognitive Computing, 4(4), 35. https://doi.org/10.3390/bdcc4040035