On the Possibility of Classical Client Blind Quantum Computing
Abstract
| Contents | ||
| 1 | Introduction and Related Works | 3 |
| 1.1 Related Work | 3 | |
| 1.2 Our Contributions | 4 | |
| 1.3 Applications | 5 | |
| 1.4 Overview of the Protocol and Proof | 6 | |
| 2 | Preliminaries | 9 |
| 2.1 Classical Definitions | 9 | |
| 2.2 Quantum Definitions | 11 | |
| 3 | CC − RSPθ Primitive | 11 |
| 4 | The Real Protocol | 12 |
| 5 | Security of HBC − QFactory | 15 |
| 5.1 Game-Based Security Definition | 15 | |
| 5.2 Game-Based Security of HBC − QFactory | 16 | |
| 5.3 Hardcore Function θ | 18 | |
| 6 | Function Constructions | 20 |
| 6.1 Obtaining Two-Regular, Collision Resistant/Second Preimage Resistant, Trapdoor One-Way Functions | 20 | |
| 6.2 Injective, Homomorphic Quantum-Safe Trapdoor One-Way Function from LWE | 24 | |
| 6.3 A Suitable δ-2 Regular Trapdoor Function | 25 | |
| 6.4 Parameter Choices | 27 | |
| 7 | Implementation of HBC−QFactory on IBM Quantum Cloud | 28 |
| 7.1 Function Construction for Simulation | 28 | |
| 7.2 Results of Implementation of HBC−QFactory | 29 | |
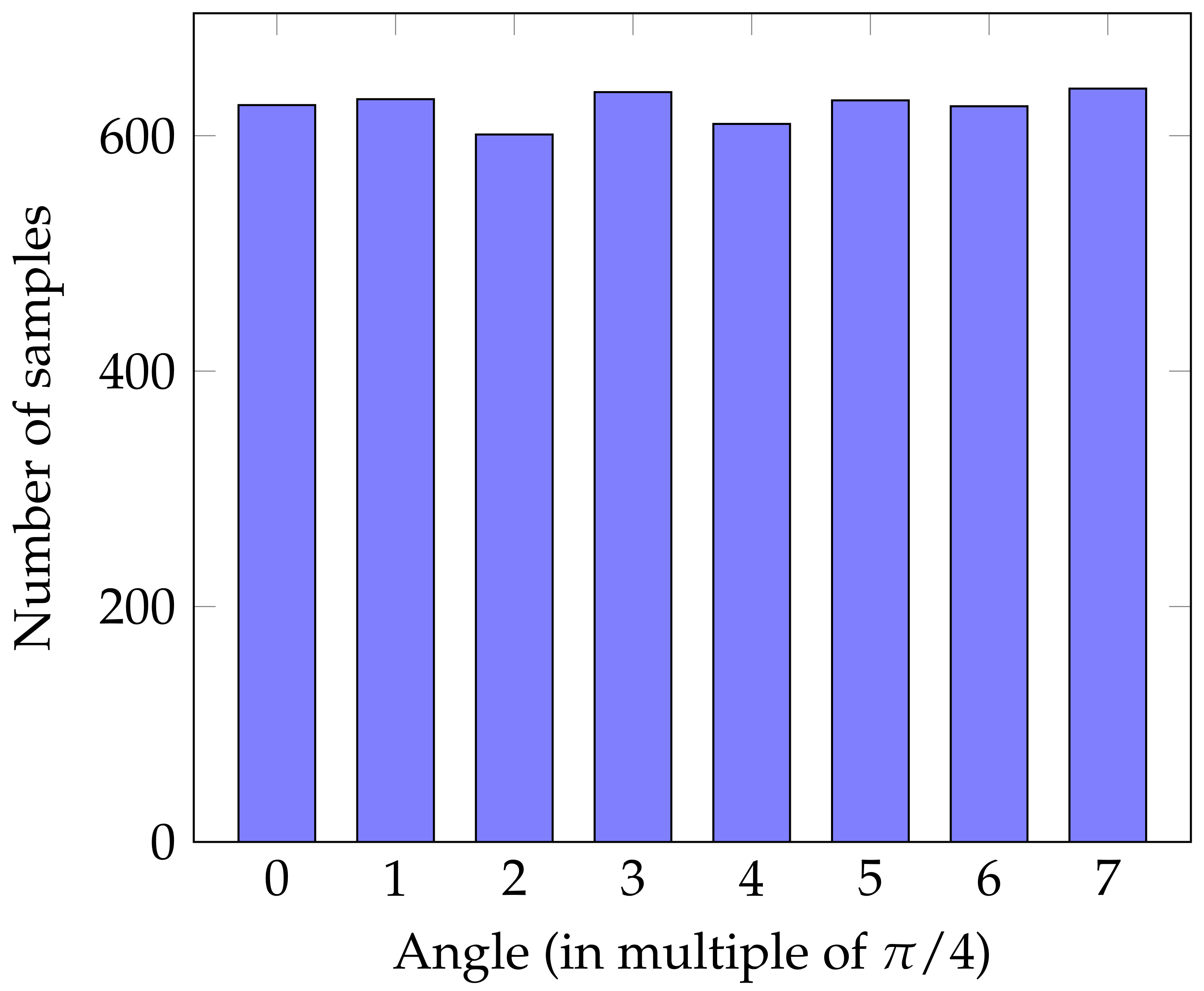
| 7.2.1 Randomness | 29 | |
| 7.2.2 Correctness | 29 | |
| 8 | Conclusions | 31 |
| 8.1 Summary of Results and Discussion | 31 | |
| 8.2 Future Directions | 32 | |
| A | CC−RSPθ within Several Applications | 33 |
| B | Full Proof of Theorem 7 | 34 |
| C | Proof of Theorem 9 | 41 |
| D | Proof of Theorem 11 | 42 |
| D.1 δ-2 Regularity | 43 | |
| D.2 Collision Resistance | 45 | |
| D.3 One-Wayness | 45 | |
| D.4 Trapdoor | 46 | |
| E | Proof of Lemma 7 | 46 |
| References | 48 | |
1. Introduction and Related Works
1.1. Related Work
1.2. Our Contributions
- We define the primitive classical client remote state preparation () in Section 3. In the earlier version of this work we called this primitive secret random qubit generator, but we switched to the term remote state preparation (RSP), which is the terminology established by the quantum cryptography community. The parameter refers to the set of quantum states produced by the primitive, which are the quantum states . can replace the need for quantum channel between parties in certain quantum communication protocols with the trade-off that the protocols become computationally secure (against quantum adversaries).
- We give a basic protocol () that achieves this functionality from a correctness point of view, given a trapdoor one-way function that is quantum-safe, two-regular and collision resistant in Section 4 and prove its correctness.
- We prove the security of the against honest-but-curious server (server follows the protocol specifications, but can try to infer any information about the secret from the classical transcripts) or against any malicious third party using a game-based security definition. To show the security, we prove that the classical description of the generated qubits is a hard-core function (following a reduction similar to that of the Goldreich–Levin Theorem) in Section 5.
- While the above-mentioned results do not depend on the specific function used, the existence of such specific functions (with all desired properties) makes the a practical primitive that can be employed as described in this paper. In Section 6, we first give methods for obtaining two-regular trapdoor one-way functions with extra properties (collision resistant or second preimage resistant) assuming the existence of simpler trapdoor one-way functions (permutation trapdoor or homomorphic, injective trapdoor functions). We use reductions to prove that the resulting functions maintain all the properties required. Furthermore, we give in Section 6.3 an explicit family of functions that respect all the required properties based on the security of the Learning-With-Errors problem as well as a possible instantiation of the parameters. This function is also quantum-safe, and thus directly applicable for our setting. Note, that other functions may also be used, such as the one in [28] or functions based on the Niederreither cryptosystem and the construction in [29].
- Finally, we implement on the quantum computer IBM Quantum Experience using a toy function (given the current limited number of available qubits we consider a 2-regular function acting on a small number of bits, consequently, it cannot be post-quantum secure). Hence, we provide in addition to the theoretical results, an experimental evidence of the correctness and output distribution of the protocol on a real quantum device. This is the first implementation of an protocol on a quantum cloud service.
1.3. Applications
1.4. Overview of the Protocol and Proof
2. Preliminaries
2.1. Classical Definitions
- There exists a PPT algorithm that can compute for any index function k, outcome of the PPT parameter-generation algorithm Gen and any input ;
- any PPT algorithm can invert with at most negligible probability over the choice of k:where represents the randomness used by ;
- There exists a PPT algorithm that can compute for any index function k, outcome of the PPT parameter-generation algorithm Gen and any input ;
- for any PPT algorithm , given an input x, it can find a different input such that with at most negligible probability over the choice of k:where is the randomness of ;
- There exists a PPT algorithm that can compute for any index function k, outcome of the PPT parameter-generation algorithm Gen and any input ;
- any PPT algorithm can find two inputs such that with at most negligible probability over the choice of k:where is the randomness of ( will be omitted from now).
- There exists a PPT algorithmGenwhich on input outputs , where k represents the index of the function;
- is a family of one-way functions;
- there exists a PPT algorithmInv, which on input (which is called the trapdoor information) output byGen() and can invert y (by returning all preimages of y) with non-negligible probability over the choice of and uniform choice of x. Note, that while in the standard definition of trapdoor functions it suffices for the inversion algorithmInvto return one of the preimages of any output of the function, in our case we require a two-regular trapdoor function where the inversion procedure returns both preimages for any function output.
- There exists a PPT algorithm that for any input x can compute ;
- any PPT algorithm when given , can compute with negligible better than probability:, where represents the randomness used by ;
- There exists a PPT algorithm that can compute for any input x;
- for any PPT algorithm when given , can distinguish between and a uniformly distributed element in E with at most negligible probability:
- is a one-way function, where .
- is a hard-core predicate for g.
2.2. Quantum Definitions
3. CC − RSPθ Primitive
| Algorithm 1 Primitive: Classical Channel Remote State Preparation () |
| Requirements: Client is a purely classical party with no access to quantum resources. Public Information: A distribution on pairs of lists M, intuitively containing the values of the classical variables used by the client and by the server. Trusted Party: – With some probability p returns to both parties , otherwise: – Samples – Samples – Prepares a qubit in state Outputs: – Either returns to both client and server – Or returns to the client, and to the server |
4. The Real Protocol
| Algorithm 2: Real Protocol |
| Requirements: Public: A family of trapdoor one-way functions that are quantum-safe, two-regular and collision resistant (or second preimage resistant, see Remark 1) Input: – Client: uniformly samples a set of random three-bits strings where , and runs the algorithm . The and k are public inputs (known to both parties), while is the “private” input of the client. Stage 1: Preimages superposition – Client: instructs server to prepare one register at and second register initiated at – Client: sends k to server and the server applies using the first register as control and the second as target – Server: measures the second register in the computational basis, obtains the outcome y and returns this result y to the client. Here, an honest server would have a state with and . Stage 2: Squeezing – Client: instructs the server to measure all the qubits (except the last one) of the first register in the basis. Server obtains the outcomes and returns the result b to the client – Client: using the trapdoor computes . Then check if the n-th bit of x and (corresponding to the y received in Stage 1) are the same or different. If they are the same, returns , otherwise, obtains the classical description of the server’s state. Output: If the protocol is run honestly, when there is no abort, the state that server has is , where the client (only) knows the classical description (see Theorem 5): |
Correctness and Intuition
5. Security of HBC − QFactory
5.1. Game-Based Security Definition
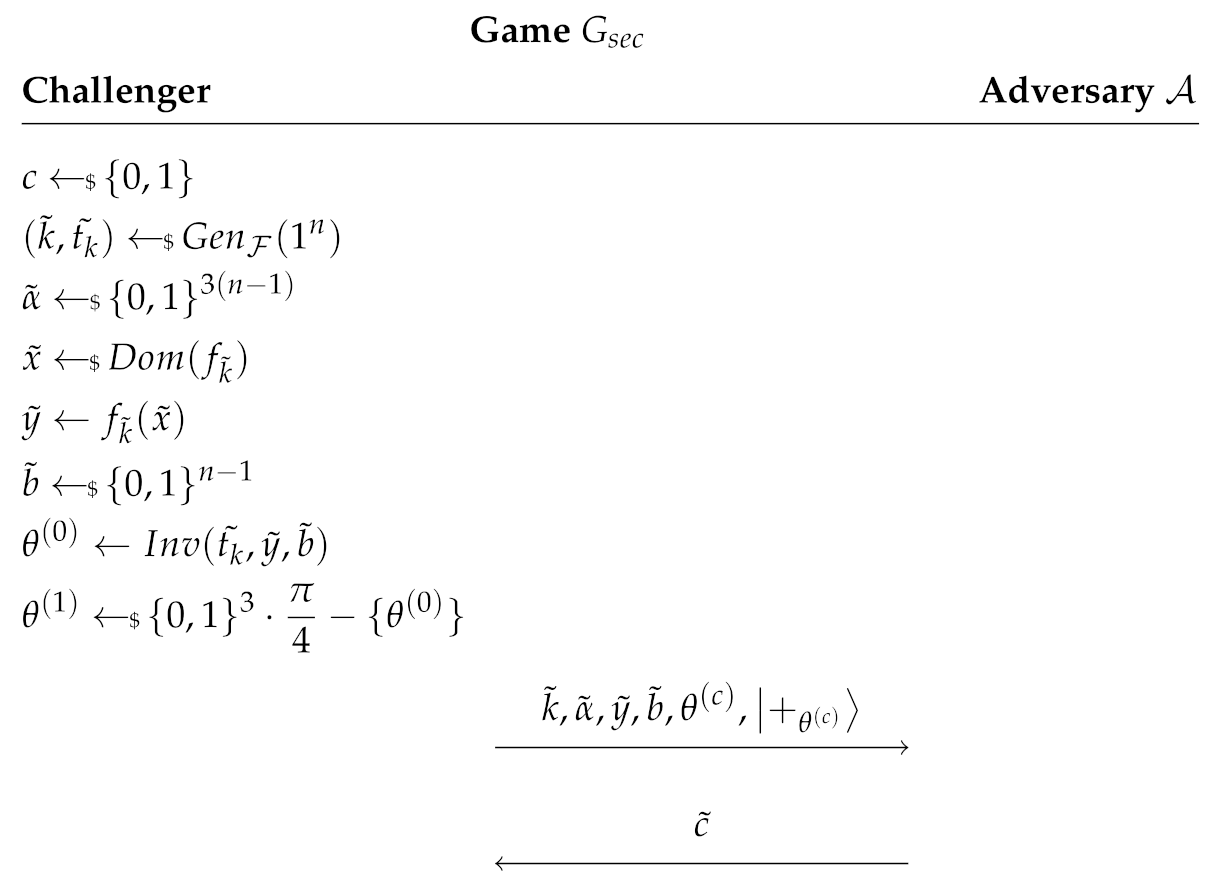
5.2. Game-Based Security of
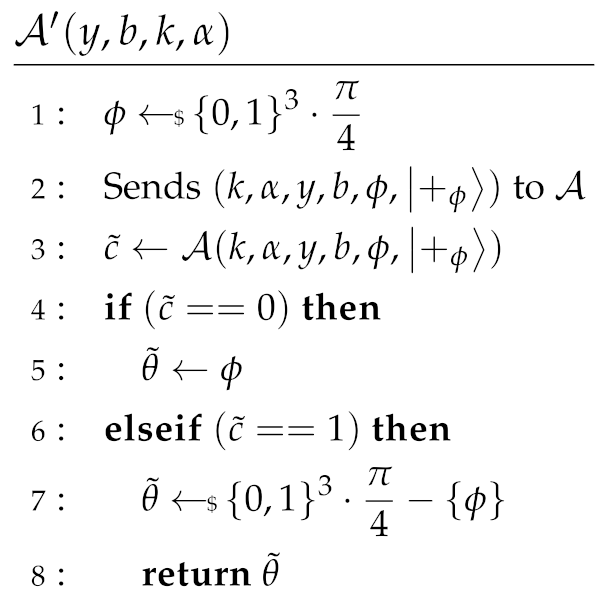
- (i)
- receives the “true” state (), so to win the game he needs to return . By definition, this happens with , and in this case also wins (since he outputs the correct state). The overall probability that all this happens, i.e., that succeeds in this case, is .
- (ii)
- receives one of the “false” states (), and thus to win he needs to return . By definition this happens with probability . Now, in this case, has essentially ruled-out one of the eight possible states. His random guess, after ruling-out one state, succeeds with probability . Combining all this together we see that succeeds with probability .
5.3. Hardcore Function θ
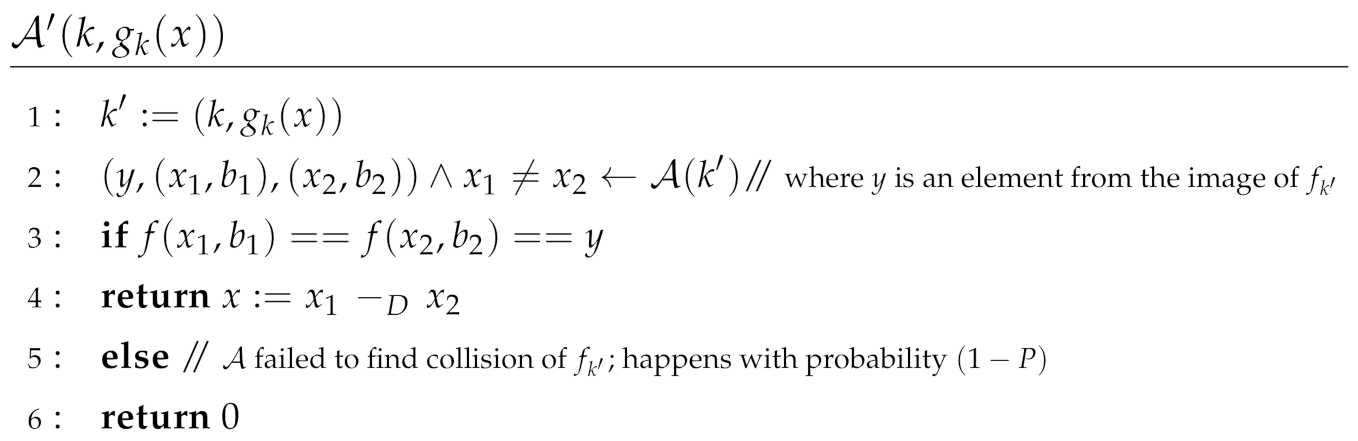
6. Function Constructions
- A general construction given either (i) an injective, homomorphic (with respect to any operation and in particular it is only required to be homomorphic once for this operation) trapdoor one-way function or (ii) a bijective trapdoor one-way function, to obtain a two-regular, second preimage resistant, trapdoor one-way function. In both cases the quantum-safe property is maintained (if the initial function has this property, so does the constructed function). We note that for (i) we prove the stronger collision resistant property.
- (Taken from [44]) A method of how to realise injective quantum-safe trapdoor functions derived from the LWE problem, that has certain homomorphic property.
- A way to use the first construction with the trapdoor from [44] that requires a number of modifications, including relaxation of the notion of two-regularity. The resulting function satisfies all the desired properties if a choice of parameters satisfying certain constraints can be found.
- A specific choice of these parameters satisfying all constraints, that leads to a concrete function with all the desired properties.
6.1. Obtaining Two-Regular, Collision Resistant/Second Preimage Resistant, Trapdoor One-Way Functions



- Since and is injective, there exists a unique such that .
- Assume such that . By definition , but is injective and by assumption, therefore there exists a unique such that




6.2. Injective, Homomorphic Quantum-Safe Trapdoor One-Way Function from LWE



6.3. A Suitable δ-2 Regular Trapdoor Function

- ,
- ,
- ,
- ,
- ,
- ,
- C the constant in Lemma 2.9 of [44] which is approximately ,
- if q is a power of 2, and otherwise.
- 1.
- m is such that (required for the injectivity of the function (see e.g., [50])),
- 2.
- ,
- 3.
- (required to have non-negligible probability to have two preimages),
- 4.
- (required for theLWEtoSIVPreduction),
- 5.
- is (representing, up to a constant factor, the approximation factor γ in the problem)—for the standard hardness of theSIVPproblem.
- 6.
- (required for the correctness of the inversion algorithm- represents the maximum length of an error vector that one can correct using the [44] function, and the last term is needed in the proof of collision resistance to ensure injectivity even when we add the trapdoor noise, as illustrated in Figure 2. We remark that we chose to use the computational definition of [44], but this theorem can be easily extended to other definitions of the same paper, or even to other construction of trapdoor short basis).
6.4. Parameter Choices
7. Implementation of HBC − QFactory on IBM Quantum Cloud
7.1. Function Construction for Simulation
7.2. Results of Implementation of HBC − QFactory
7.2.1. Randomness
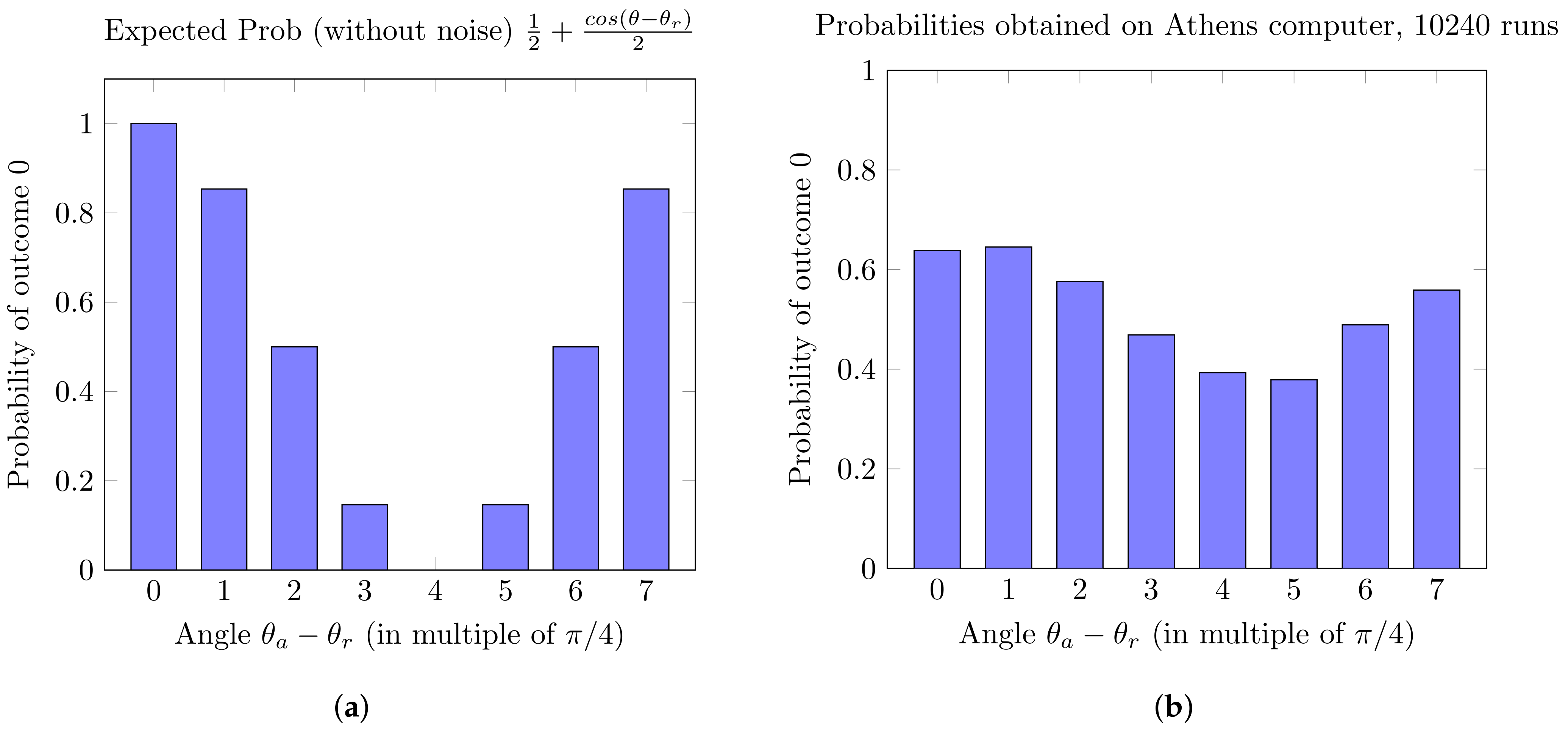
7.2.2. Correctness
- The server always obtains a type of state on his side;
- the client, by knowing the preimages of each image y, can always efficiently compute this .
- If , we should obtain measurement outcome 0 with probability 1;
- if we should obtain 1 with probability 1;
- if we should get 1 with probability ;
- if we should get 0 with probability ;
- and, in general, the probability of the outcome 0 is equal to: .
8. Conclusions
8.1. Summary of Results and Discussion
8.2. Future Directions
Author Contributions
Funding
Acknowledgments
Conflicts of Interest
Appendix A. CC−RSPθ within Several Applications
- In the quantum homomorphic encryption scheme AUX in [4], where the target quantum computation must have constant T-gate depth, using our QFactory protocol would allow a classical client to participate (delegate such computation) provided, of course, that the input/output are classical. Specifically, as the input is classical, the client will instruct the server to prepare a quantum state of the classical one-time pad of this input (and then the client will also send to the server a classical homomorphic encryption of the classical one-time pad key of each of the input’s bits). Moreover, for every T-gate in the quantum computation, the auxiliary qubits in the evaluation key can be produced using QFactory: .We note that due to the use of a classical fully homomorphic encryption scheme, the AUX protocol [4] has computationally security, thus, the computational security offered by the QFactory is not downgrading the security of this protocol.
- In the blind delegated quantum computation protocol of [21], the client needs to prepare and send to the server qubits, randomly chosen, from the set of states . This is exactly the set of states of Equation (3) which are given by the QFactory. It follows that our construction eliminates the need for quantum communication and thus any classical client can use this protocol.
- The verifiable blind quantum computation protocol in [32], the only quantum ability that the verifier needs is to prepare and send to the prover single qubits, randomly chosen, from the set of states . Again, this is exactly the set of states given by the QFactory. Therefore, the quantum communication, and thus quantum abilities of the verifier, can be completely replaced by the primitive.
- For the quantum key-distribution construction in [33], we can use two conjugate bases to realise this protocol, namely: the diagonal basis and the left-right handed circular basis . All these four quantum states can be obtained by the QFactory protocol. We note that if one was interested in obtaining exactly and only this set of states, we can modify the QFactory to do so, in a way that actually simplifies the proofs too. For example, we could simply ask to measure the qubits in the second stage in the basis . As the quantum coin flipping protocol of [33], the quantum money protocol of [34] or the quantum digital signatures protocol of [36] only require, as in [33], any pair of conjugate bases, this implies that we can use QFactory in a straight forward way. On the other hand, for the quantum coin flip construction in [35], the single qubit quantum states needed are of the form , which might be achieved by a different construction of the .
- In the multiparty quantum computation protocol of [39], the n clients need to send multiple copies of quantum states in the set to the server, who entangles and measures them all but one. Using QFactory all these states will be prepared by the server, which would enable the n clients to be fully classical.
- The verifiable blind quantum computation protocols in [30,31] or the two-party quantum computation protocols in [37,38], require the honest party to prepare single qubit states from the set of states . While the QFactory primitive can output the states, in order to make the honest party fully classical, we need to change the construction of QFactory in order to also be able to output the and states, and maintain the same guarantees in privacy as in the QFactory.
Appendix B. Full Proof of Theorem 7
Appendix C. Proof of Theorem 9
- Since and is bijective, there exist unique such that .
- Since and is bijective, there exist unique such that .



Appendix D. Proof of Theorem 11
Appendix D.1. δ-2 Regularity
- If , then:Now, what we require is that = c , where c is a constant, as then, we have that the probability of success is at least a constant .
- If (and less than 1, as ), then:
Appendix D.2. Collision Resistance
Appendix D.3. One-Wayness
Appendix D.4. Trapdoor
Appendix E. Proof of Lemma 7
- The first three requirements are trivially satisfied.
- In the forth condition, the only difficulty is to show that . By definition,
- Now, let us show the fifth condition, i.e., . First we note that . Then, by defining , the condition is satisfied.
- For the fifth condition, i.e., is , we just need to remark that , and that both m and q are .
- Finally, to show that the last condition is satisfied, we note that:if and only ifNow, let us suppose that with and and we need to find such that . Note that we will include v in some constants and then find the good v at the end. First, remark that:So now,Finally, we observe that if and , we have , which concludes the proof.
References
- Elkouss, D.; Lipinska, V.; Goodenough, K.; Rozpedek, F.; Kalb, N.; van Dam, S.; Le Phuc, T.; Murta, G.; Humphreys, P.; Taminiau, T.; et al. Quantum internet: The certifiable road ahead. In Proceedings of the APS Meeting Abstracts, New Orleans, LA, USA, 13–17 March 2017. [Google Scholar]
- Broadbent, A.; Schaffner, C. Quantum cryptography beyond quantum key distribution. Des. Codes Cryptogr. 2016, 78, 351–382. [Google Scholar] [CrossRef]
- Fitzsimons, J.F. Private quantum computation: An introduction to blind quantum computing and related protocols. Npj Quantum Inf. 2017, 3, 23. [Google Scholar] [CrossRef]
- Broadbent, A.; Jeffery, S. Quantum homomorphic encryption for circuits of low T-gate complexity. In Annual Cryptology Conference; Springer: Berlin/Heidelberg, Germany, 2015; pp. 609–629. [Google Scholar]
- Dulek, Y.; Schaffner, C.; Speelman, F. Quantum homomorphic encryption for polynomial-sized circuits. In Annual Cryptology Conference; Springer: Berlin/Heidelberg, Germany, 2016; pp. 3–32. [Google Scholar]
- Alagic, G.; Dulek, Y.; Schaffner, C.; Speelman, F. Quantum fully homomorphic encryption with verification. In International Conference on the Theory and Application of Cryptology and Information Security; Springer: Berlin/Heidelberg, Germany, 2017; pp. 438–467. [Google Scholar]
- Liang, M. Quantum fully homomorphic encryption scheme based on universal quantum circuit. Quantum Inf. Process. 2015, 14, 2749–2759. [Google Scholar] [CrossRef]
- Ouyang, Y.; Tan, S.H.; Fitzsimons, J. Quantum homomorphic encryption from quantum codes. arXiv 2015, arXiv:1508.00938. [Google Scholar] [CrossRef]
- Tan, S.H.; Kettlewell, J.A.; Ouyang, Y.; Chen, L.; Fitzsimons, J.F. A quantum approach to homomorphic encryption. Sci. Rep. 2016, 6, 33467. [Google Scholar] [CrossRef] [PubMed]
- Lai, C.Y.; Chung, K.M. On statistically-secure quantum homomorphic encryption. arXiv 2017, arXiv:1705.00139. [Google Scholar]
- Mantri, A.; Pérez-Delgado, C.A.; Fitzsimons, J.F. Optimal blind quantum computation. Phys. Rev. Lett. 2013, 111, 230502. [Google Scholar] [CrossRef]
- Giovannetti, V.; Maccone, L.; Morimae, T.; Rudolph, T.G. Efficient universal blind quantum computation. Phys. Rev. Lett. 2013, 111, 230501. [Google Scholar] [CrossRef]
- Armknecht, F.; Gagliardoni, T.; Katzenbeisser, S.; Peter, A. General impossibility of group homomorphic encryption in the quantum world. In International Workshop on Public Key Cryptography; Springer: Berlin/Heidelberg, Germany, 2014; pp. 556–573. [Google Scholar]
- Yu, L.; Pérez-Delgado, C.A.; Fitzsimons, J.F. Limitations on information-theoretically-secure quantum homomorphic encryption. Phys. Rev. A 2014, 90, 050303. [Google Scholar] [CrossRef]
- Aaronson, S.; Cojocaru, A.; Gheorghiu, A.; Kashefi, E. Complexity-Theoretic Limitations on Blind Delegated Quantum Computation. In Proceedings of the 46th International Colloquium on Automata, Languages, and Programming (ICALP 2019), Patras, Greece, 8–12 July 2019. [Google Scholar]
- Newman, M.; Shi, Y. Limitations on Transversal Computation through Quantum Homomorphic Encryption. arXiv 2017, arXiv:1704.07798. [Google Scholar]
- Mantri, A.; Demarie, T.F.; Menicucci, N.C.; Fitzsimons, J.F. Flow ambiguity: A path towards classically driven blind quantum computation. Phys. Rev. X 2017, 7, 031004. [Google Scholar] [CrossRef]
- Mahadev, U. Classical Homomorphic Encryption for Quantum Circuits. In Proceedings of the 59th IEEE Annual Symposium on Foundations of Computer Science (FOCS 2018), Paris, France, 7–9 October 2018; Thorup, M., Ed.; IEEE Computer Society: Washington, DC, USA, 2018; pp. 332–338. [Google Scholar]
- Brakerski, Z. Quantum FHE (Almost) As Secure As Classical. In Advances in Cryptology—CRYPTO 2018; Springer International Publishing: Cham, Switzerland, 2018; pp. 67–95. [Google Scholar]
- Badertscher, C.; Cojocaru, A.; Colisson, L.; Kashefi, E.; Leichtle, D.; Mantri, A.; Wallden, P. Security Limitations of Classical-Client Delegated Quantum Computing. In Advances in Cryptology—ASIACRYPT 2020; Springer: Berlin/Heidelberg, Germany, 2020. [Google Scholar] [CrossRef]
- Broadbent, A.; Fitzsimons, J.; Kashefi, E. Universal blind quantum computation. In Proceedings of the 50th Annual Symposium on Foundations of Computer Science (FOCS ’09), Atlanta, GA, USA, 25–27 October 2009; IEEE Computer Society: Washington, DC, USA, 2009; pp. 517–526. [Google Scholar] [CrossRef]
- Cojocaru, A.; Colisson, L.; Kashefi, E.; Wallden, P. On the possibility of classical client blind quantum computing. arXiv 2018, arXiv:1802.08759. [Google Scholar]
- Cojocaru, A.; Colisson, L.; Kashefi, E.; Wallden, P. QFactory: Classically-Instructed Remote Secret Qubits Preparation. In Advances in Cryptology—ASIACRYPT 2019; Galbraith, S.D., Moriai, S., Eds.; Springer International Publishing: Berlin/Heidelberg, Germany, 2019; pp. 615–645. [Google Scholar]
- Gheorghiu, A.; Vidick, T. Computationally-Secure and Composable Remote State Preparation. In Proceedings of the 2019 IEEE 60th Annual Symposium on Foundations of Computer Science (FOCS), Baltimore, MA, USA, 9–12 November 2019; pp. 1024–1033. [Google Scholar]
- Zhang, J. Succinct Blind Quantum Computation Using a Random Oracle. arXiv 2020, arXiv:2004.12621. [Google Scholar]
- Pirandola, S.; Andersen, U.L.; Banchi, L.; Berta, M.; Bunandar, D.; Colbeck, R.; Englund, D.; Gehring, T.; Lupo, C.; Ottaviani, C.; et al. Advances in quantum cryptography. Adv. Opt. Photon. 2020, 12, 1012–1236. [Google Scholar] [CrossRef]
- Wallden, P.; Kashefi, E. Cyber Security in the Quantum Era. Commun. ACM 2019, 62, 120. [Google Scholar] [CrossRef]
- Brakerski, Z.; Christiano, P.; Mahadev, U.; Vazirani, U.; Vidick, T. Certifiable Randomness from a Single Quantum Device. arXiv 2018, arXiv:1804.00640. [Google Scholar]
- Freeman, D.M.; Goldreich, O.; Kiltz, E.; Rosen, A.; Segev, G. More constructions of lossy and correlation-secure trapdoor functions. In International Workshop on Public Key Cryptography; Springer: Berlin/Heidelberg, Germany, 2010; pp. 279–295. [Google Scholar]
- Fitzsimons, J.F.; Kashefi, E. Unconditionally verifiable blind computation. arXiv 2012, arXiv:1203.5217. [Google Scholar]
- Broadbent, A. How to Verify a Quantum Computation. arXiv 2015, arXiv:1509.09180. [Google Scholar]
- Ferracin, S.; Kapourniotis, T.; Datta, A. Towards minimising resources for verification of quantum computations. arXiv 2017, arXiv:1709.10050. [Google Scholar]
- Bennett, C.H.; Brassard, G. Quantum cryptography: Public key distribution and coin tossing. Theor. Comput. Sci. 2014, 560, 7–11. [Google Scholar] [CrossRef]
- Bozzio, M.; Orieux, A.; Vidarte, L.T.; Zaquine, I.; Kerenidis, I.; Diamanti, E. Experimental investigation of practical unforgeable quantum money. Npj Quantum Inf. 2018, 4, 5. [Google Scholar] [CrossRef]
- Pappa, A.; Chailloux, A.; Diamanti, E.; Kerenidis, I. Practical quantum coin flipping. Phys. Rev. A 2011, 84, 052305. [Google Scholar] [CrossRef]
- Wallden, P.; Dunjko, V.; Kent, A.; Andersson, E. Quantum digital signatures with quantum-key-distribution components. Phys. Rev. A 2015, 91, 042304. [Google Scholar] [CrossRef]
- Kashefi, E.; Wallden, P. Garbled Quantum Computation. Cryptography 2017, 1, 6. [Google Scholar] [CrossRef]
- Kashefi, E.; Music, L.; Wallden, P. The Quantum Cut-and-Choose Technique and Quantum Two-Party Computation. arXiv 2017, arXiv:1703.03754. [Google Scholar]
- Kashefi, E.; Pappa, A. Multiparty Delegated Quantum Computing. Cryptography 2017, 1, 12. [Google Scholar] [CrossRef]
- Broadbent, A.; Gutoski, G.; Stebila, D. Quantum One-Time Programs. In Advances in Cryptology—CRYPTO 2013; Canetti, R., Garay, J., Eds.; Lecture Notes in Computer Science; Springer: Berlin/Heidelberg, Germany, 2013; Volume 8043, pp. 344–360. [Google Scholar] [CrossRef]
- Ciampi, M.; Cojocaru, A.; Kashefi, E.; Mantri, A. Secure Quantum Two-Party Computation: Impossibility and Constructions. arXiv 2020, arXiv:2010.07925. [Google Scholar]
- Goldreich, O.; Levin, L.A. A Hard-core Predicate for All One-way Functions. In Proceedings of the Twenty-First Annual ACM Symposium on Theory of Computing (STOC ’89), Washington, DC, USA, 15–17 May 1989; ACM: New York, NY, USA, 1989; pp. 25–32. [Google Scholar] [CrossRef]
- Vazirani, U.V.; Vazirani, V.V. Efficient and Secure Pseudo-Random Number Generation (Extended Abstract). In Advances in Cryptology; Blakley, G.R., Chaum, D., Eds.; Springer: Berlin/Heidelberg, Germany, 1985; pp. 193–202. [Google Scholar]
- Micciancio, D.; Peikert, C. Trapdoors for Lattices: Simpler, Tighter, Faster, Smaller. In Advances in Cryptology—EUROCRYPT 2012; Pointcheval, D., Johansson, T., Eds.; Springer: Berlin/Heidelberg, Germany, 2012; pp. 700–718. [Google Scholar]
- Katz, J.; Lindell, Y. Introduction to Modern Cryptography, 2nd ed.; Chapman & Hall/CRC: Boca Raton, FL, USA, 2014. [Google Scholar]
- Regev, O. On Lattices, Learning with Errors, Random Linear Codes, and Cryptography. In Proceedings of the Thirty-Seventh Annual ACM Symposium on Theory of Computing (STOC ’05), Baltimore, MD, USA, 22–24 May 2005; ACM: New York, NY, USA, 2005; pp. 84–93. [Google Scholar] [CrossRef]
- Peikert, C. Public-key Cryptosystems from the Worst-case Shortest Vector Problem: Extended Abstract. In Proceedings of the Forty-First Annual ACM Symposium on Theory of Computing (STOC ’09), Bethesda, MD, USA, 31 May–2 June 2009; ACM: New York, NY, USA, 2009; pp. 333–342. [Google Scholar] [CrossRef]
- Aaronson, S. Quantum computing, postselection, and probabilistic polynomial-time. Proc. R. Soc. Lond. Ser. A 2005, 461, 3473–3482. [Google Scholar] [CrossRef]
- Greenberger, D.M.; Horne, M.A.; Zeilinger, A. Going beyond Bell’s theorem. In Bell’s Theorem, Quantum Theory and Conceptions of the Universe; Springer: Berlin/Heidelberg, Germany, 1989; pp. 69–72. [Google Scholar]
- Vaikuntanathan, V. Advanced Topics in Cryptography: Lattices. Available online: https://people.csail.mit.edu/vinodv/6876-Fall2015/L13.pdf (accessed on 7 December 2018).



Publisher’s Note: MDPI stays neutral with regard to jurisdictional claims in published maps and institutional affiliations. |
© 2021 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Cojocaru, A.; Colisson, L.; Kashefi, E.; Wallden, P. On the Possibility of Classical Client Blind Quantum Computing. Cryptography 2021, 5, 3. https://doi.org/10.3390/cryptography5010003
Cojocaru A, Colisson L, Kashefi E, Wallden P. On the Possibility of Classical Client Blind Quantum Computing. Cryptography. 2021; 5(1):3. https://doi.org/10.3390/cryptography5010003
Chicago/Turabian StyleCojocaru, Alexandru, Léo Colisson, Elham Kashefi, and Petros Wallden. 2021. "On the Possibility of Classical Client Blind Quantum Computing" Cryptography 5, no. 1: 3. https://doi.org/10.3390/cryptography5010003
APA StyleCojocaru, A., Colisson, L., Kashefi, E., & Wallden, P. (2021). On the Possibility of Classical Client Blind Quantum Computing. Cryptography, 5(1), 3. https://doi.org/10.3390/cryptography5010003





