Electromagnetic and Power Side-Channel Analysis: Advanced Attacks and Low-Overhead Generic Countermeasures through White-Box Approach
Abstract
1. Introduction and Motivation
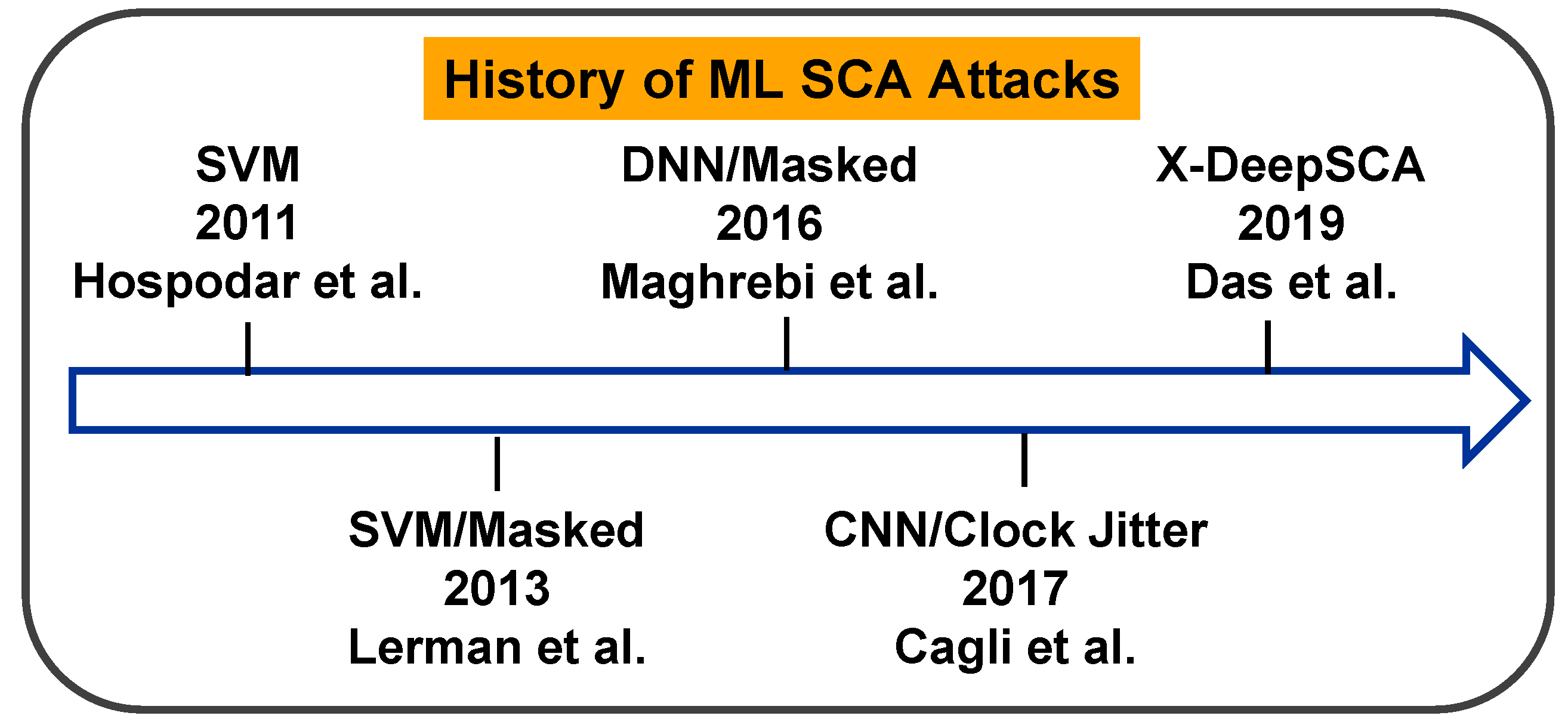
2. Background and Related Works
2.1. EM and Power SCA Attacks
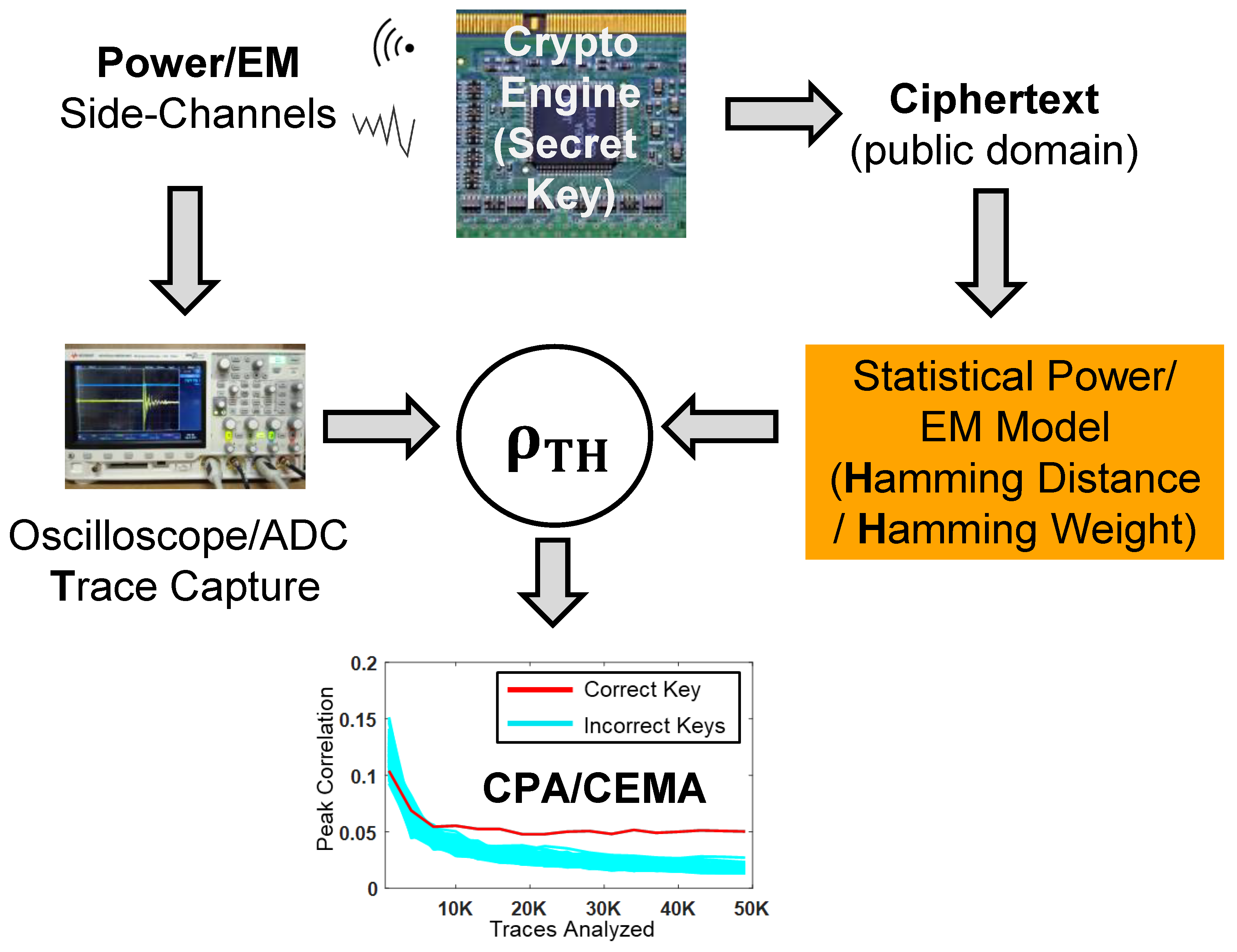
2.1.1. Non-Profiled SCA Attack
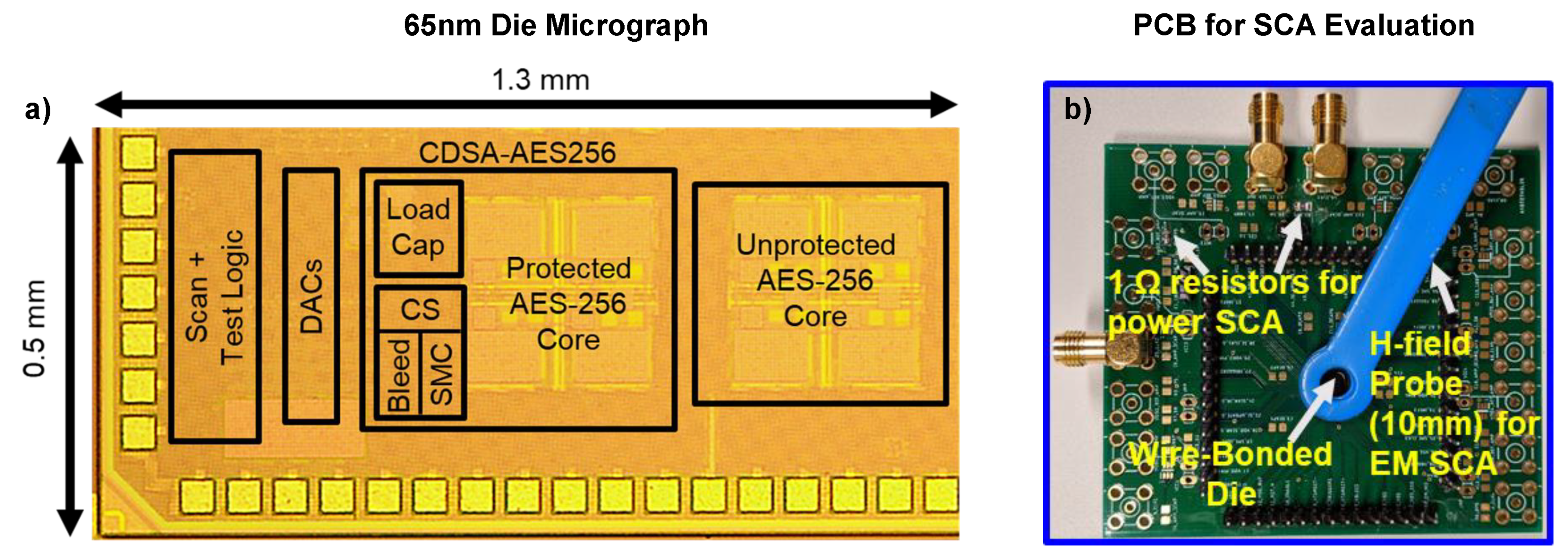
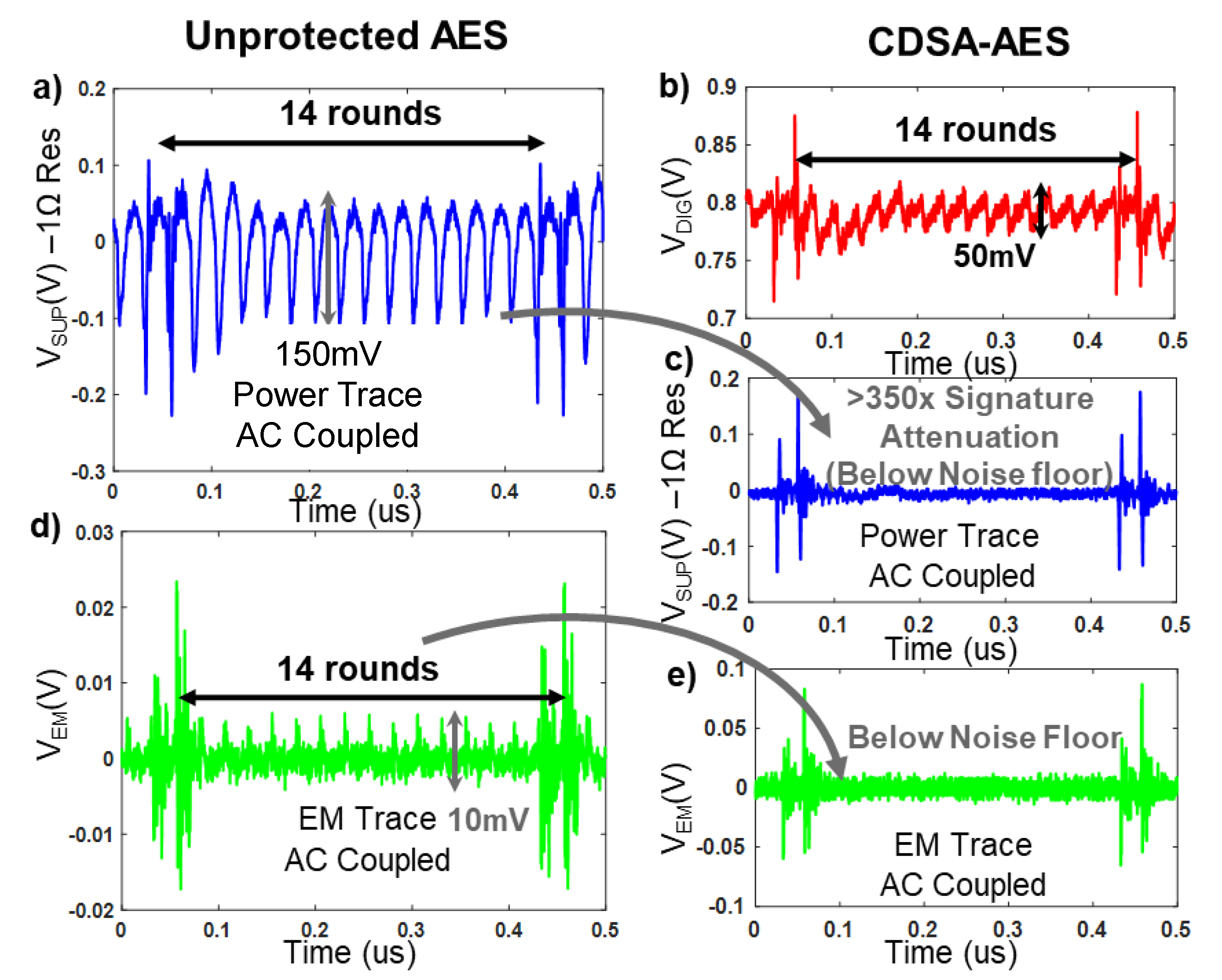
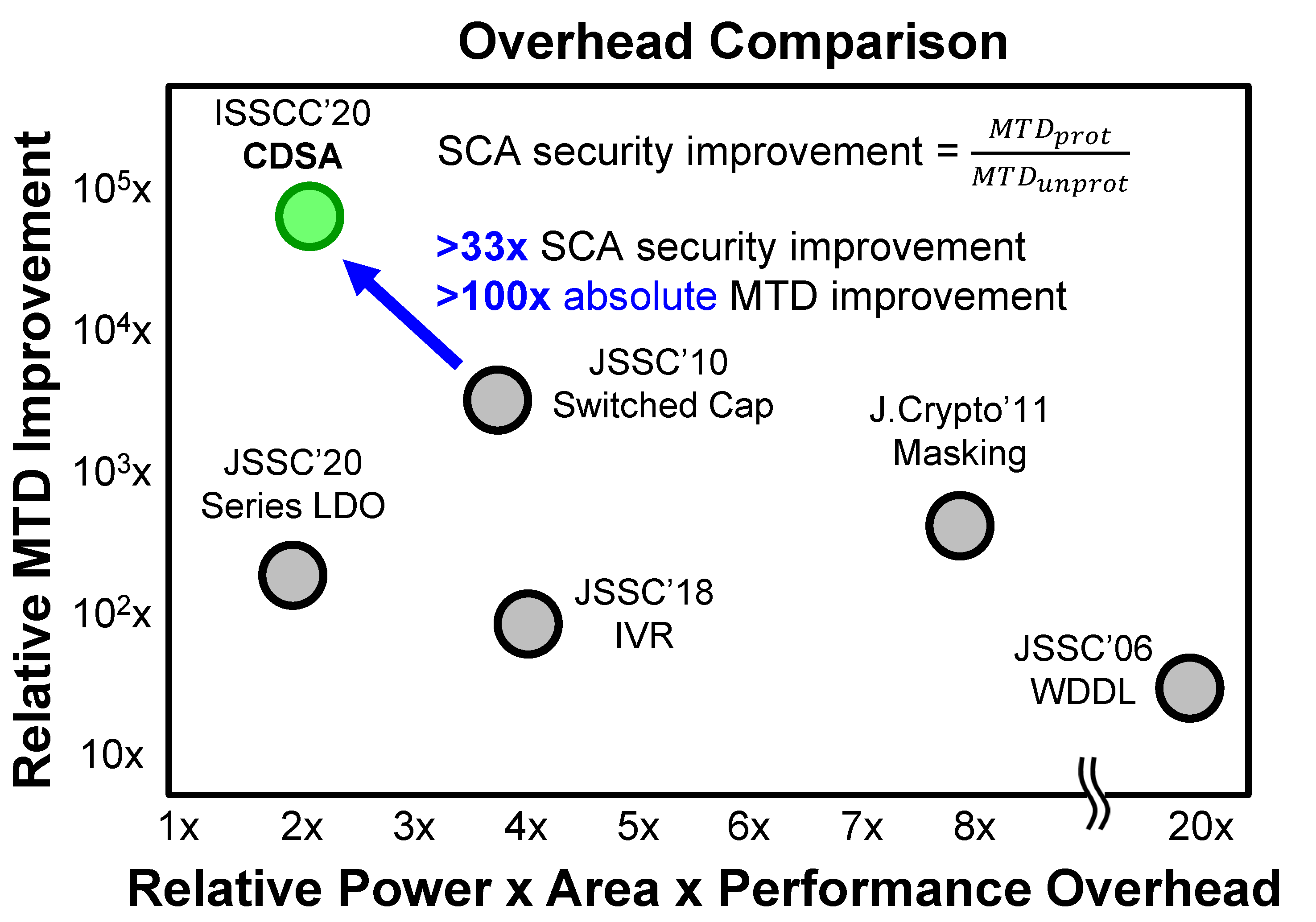
2.1.2. Profiled SCA Attack
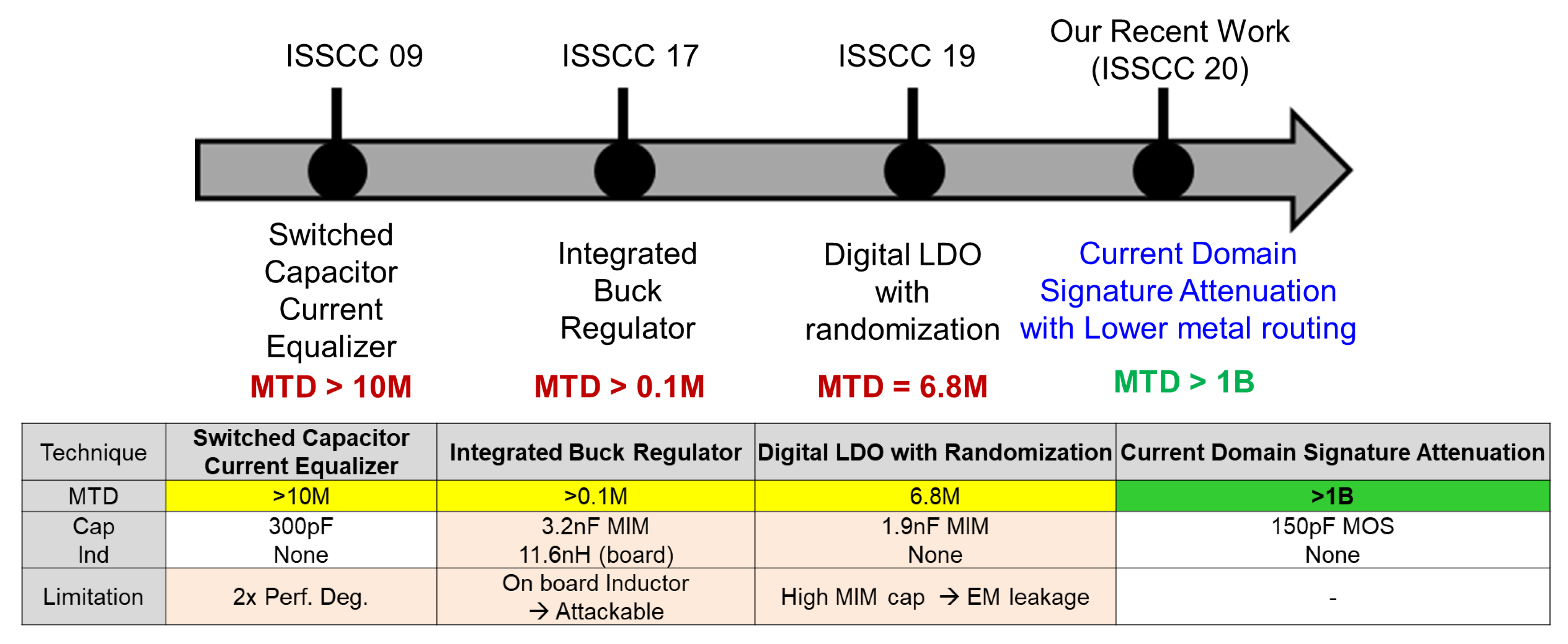
2.2. State-of-the-Art Countermeasures
2.2.1. Logical Countermeasures
2.2.2. Architectural Countermeasures
2.2.3. Circuit-Level Physical Countermeasures
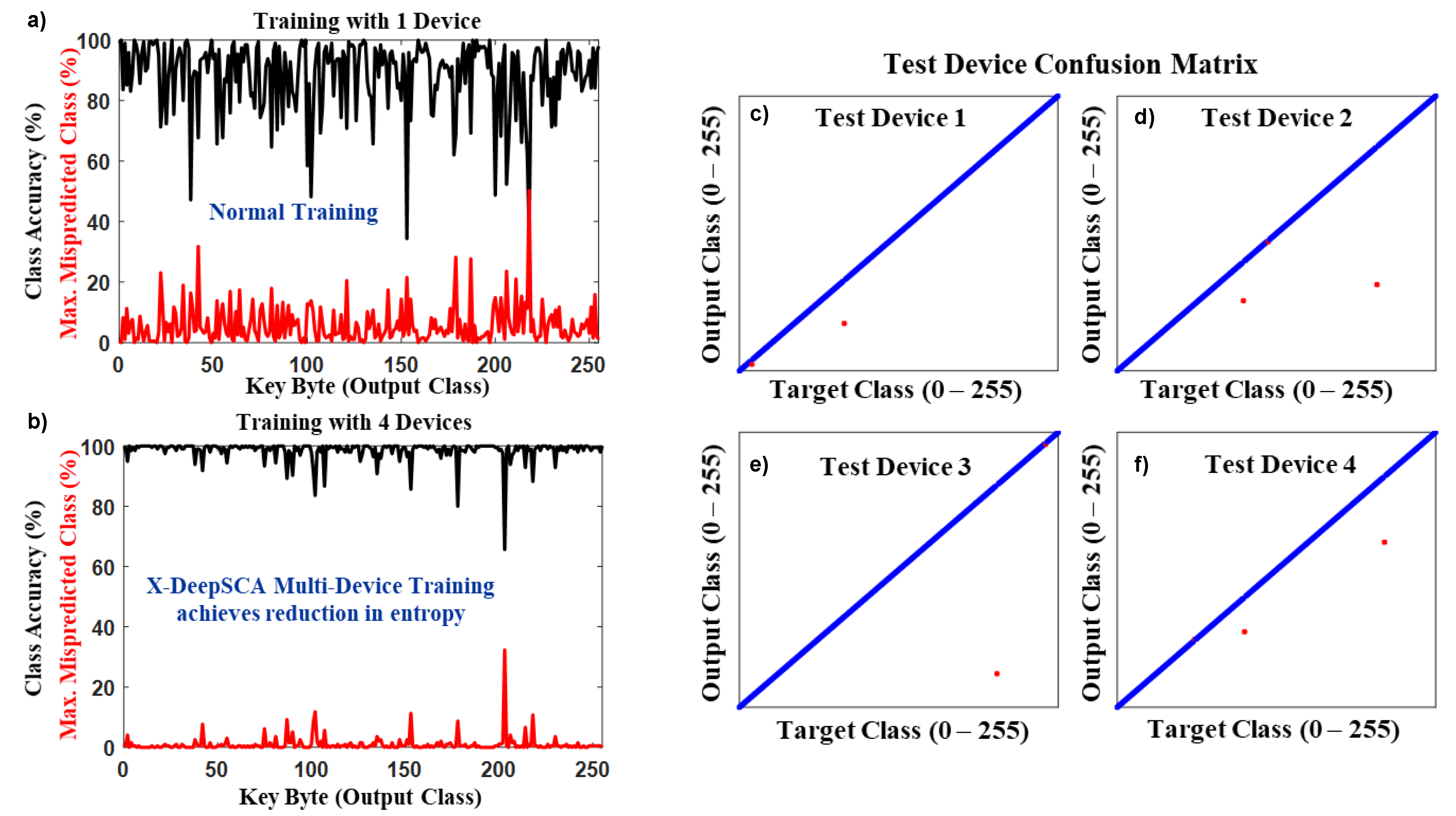
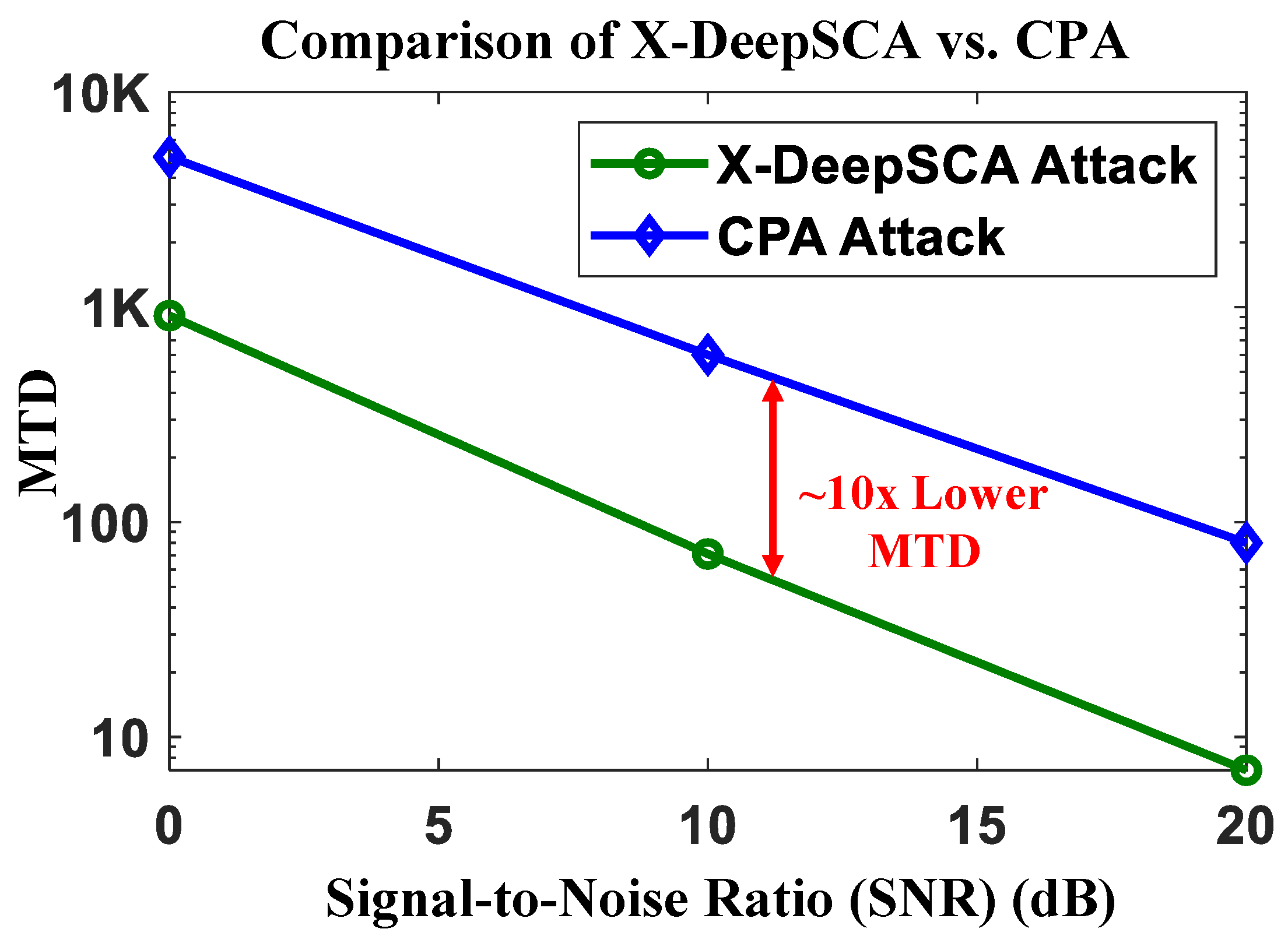
3. Cross-Device Deep-Learning Attack: X-DeepSCA
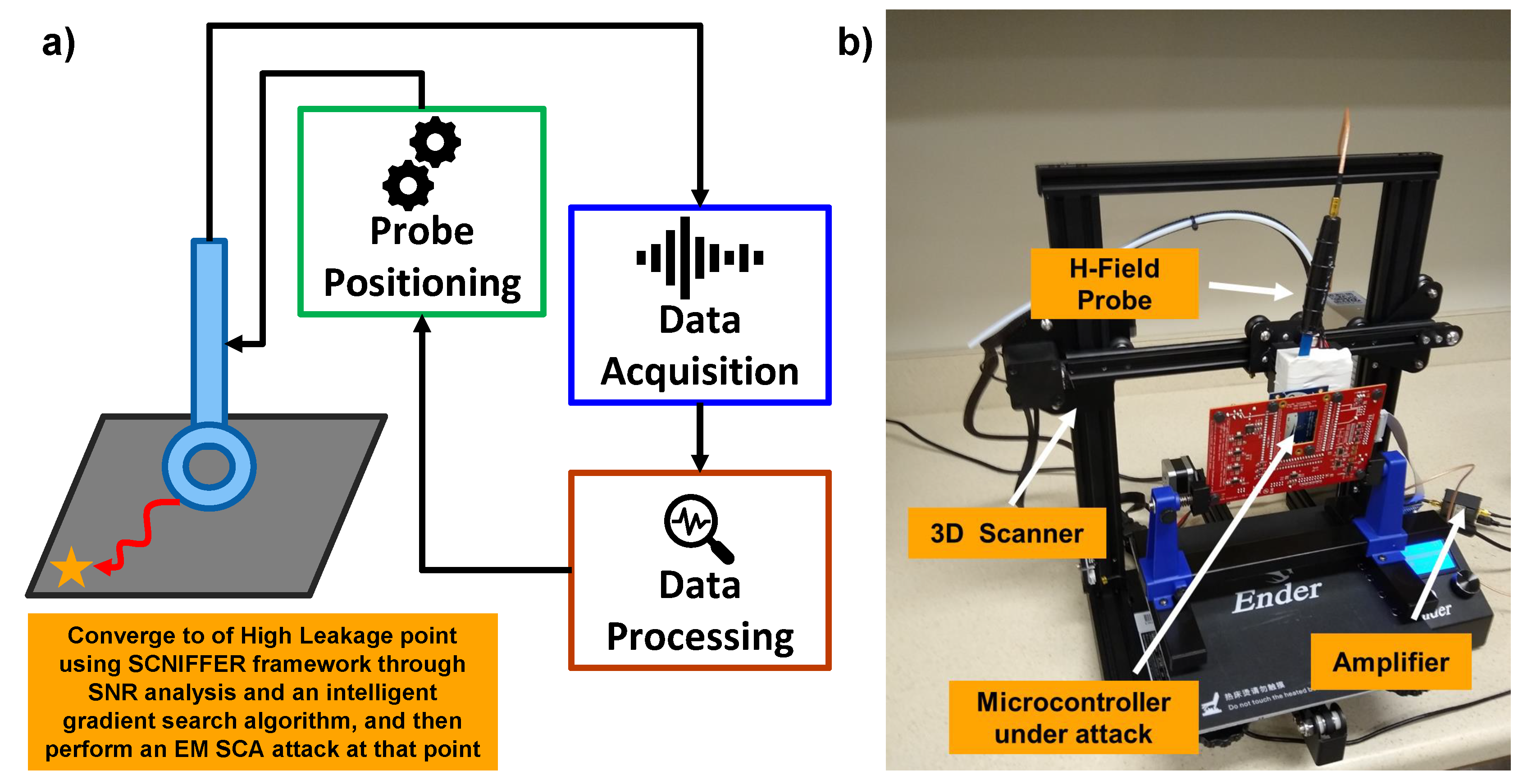
4. Low-Cost Automated EM SCA Attack Framework: SCNIFFER
5. Countermeasure against EM SCA
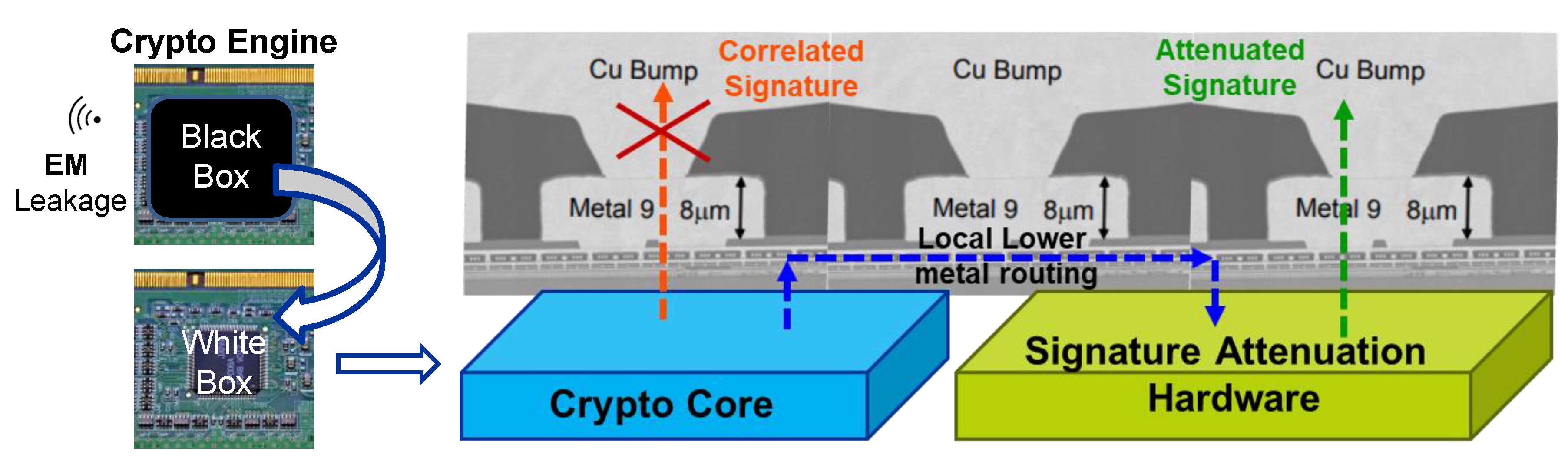
5.1. Ground-up Root-Cause Analysis of the EM Leakage
5.2. Local Lower Metal Routing: STELLAR
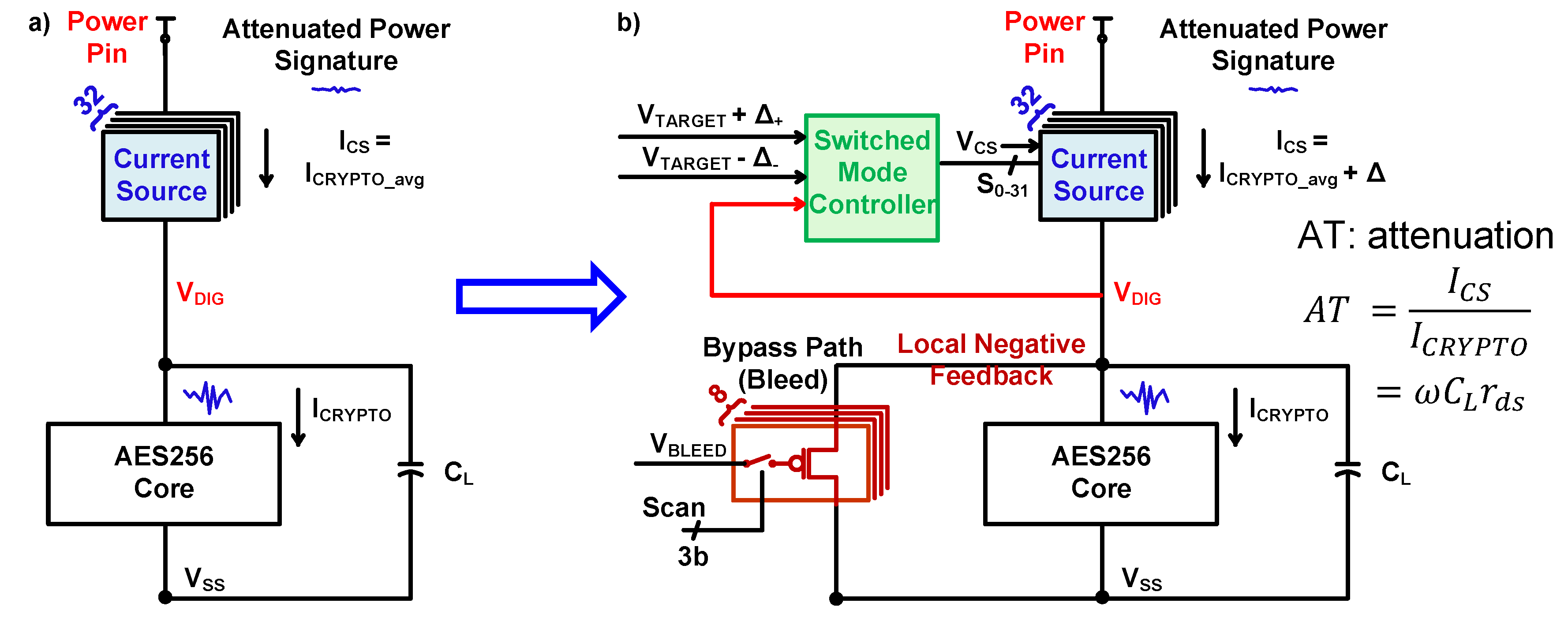
6. Current-Domain Signature Attenuation (CDSA) Hardware
Current-Domain Signature Attenuation (CDSA) Hardware
7. Measurement Results and Evaluation Metrics for Security and Overhead Comparison
8. Evaluation of CDSA against DL SCA Attacks
9. Future Work and Conclusions
Author Contributions
Funding
Acknowledgments
Conflicts of Interest
References
- McKinsey Global Institute. The Internet of Things: Mapping the Value Beyond the Hype; Technical Report; McKinsey Global Institute: New York, NY, USA, 2015. [Google Scholar]
- O’Flynn, C.; Dewar, A. On-Device Power Analysis Across Hardware Security Domains. IACR Trans. Cryptogr. Hardw. Embed. Syst. 2019, 126–153. [Google Scholar] [CrossRef]
- Schellenberg, F.; Gnad, D.R.; Moradi, A.; Tahoori, M.B. Remote Inter-Chip Power Analysis Side-Channel Attacks at Board-Level. In Proceedings of the 2018 IEEE/ACM International Conference on Computer-Aided Design (ICCAD), San Diego, CA, USA, 5–8 November 2018; pp. 1–7. [Google Scholar] [CrossRef]
- Zhao, M.; Suh, G.E. FPGA-Based Remote Power Side-Channel Attacks. In Proceedings of the 2018 IEEE Symposium on Security and Privacy (SP), San Francisco, CA, USA, 21–23 May 2018; pp. 229–244. [Google Scholar] [CrossRef]
- Camurati, G.; Poeplau, S.; Muench, M.; Hayes, T.; Francillon, A. Screaming Channels: When Electromagnetic Side Channels Meet Radio Transceivers. In Proceedings of the 2018 ACM SIGSAC Conference on Computer and Communications Security, Toronto, ON, Canada, 15–19 October 2018; Association for Computing Machinery: Toronto, ON, Canada, 2018; pp. 163–177. [Google Scholar] [CrossRef]
- Ronen, E.; Shamir, A.; Weingarten, A.O.; O’Flynn, C. IoT Goes Nuclear: Creating a ZigBee Chain Reaction. In Proceedings of the 2017 IEEE Symposium on Security and Privacy (SP), San Jose, CA, USA, 22–24 May 2017; pp. 195–212. [Google Scholar] [CrossRef]
- Krebs, B. Hacked Cameras, DVRs Powered Today’s Massive Internet Outage. 2016. Available online: krebsonsecurity.com (accessed on 30 September 2020).
- Kocher, P.; Jaffe, J.; Jun, B. Differential Power Analysis. In Advances in Cryptology — CRYPTO’ 99; Wiener, M., Ed.; Number 1666 in Lecture Notes in Computer Science; Springer: Berlin/Heidelberg, Germany, 1999; pp. 388–397. [Google Scholar] [CrossRef]
- Quisquater, J.J.; Samyde, D. ElectroMagnetic Analysis (EMA): Measures and Counter-measures for Smart Cards. In Smart Card Programming and Security; Lecture Notes in Computer Science; Springer: Berlin/Heidelberg, Germany, 2001; pp. 200–210. [Google Scholar] [CrossRef]
- Ramsay, C.; Lohuis, J. TEMPEST Attacks against AES. 2017. Available online: https://hardwear.io/document/slides-craig-ramsay.pdf (accessed on 30 September 2020).
- Brier, E.; Clavier, C.; Olivier, F. Correlation Power Analysis with a Leakage Model. In Cryptographic Hardware and Embedded Systems—CHES 2004; Joye, M., Quisquater, J.J., Eds.; Lecture Notes in Computer Science; Springer: Berlin/Heidelberg, Germany, 2004; pp. 16–29. [Google Scholar]
- Chari, S.; Rao, J.R.; Rohatgi, P. Template Attacks. In Cryptographic Hardware and Embedded Systems—CHES 2002; Kaliski, B.S., Koç, Ç.K., Paar, C., Eds.; Lecture Notes in Computer Science; Springer: Berlin/Heidelberg, Germany, 2003; pp. 13–28. [Google Scholar]
- Hospodar, G.; Gierlichs, B.; De Mulder, E.; Verbauwhede, I.; Vandewalle, J. Machine learning in side-channel analysis: A first study. J. Cryptogr. Eng. 2011, 1, 293. [Google Scholar] [CrossRef]
- Lerman, L.; Bontempi, G.; Markowitch, O. A machine learning approach against a masked AES. J. Cryptogr. Eng. 2015, 5, 123–139. [Google Scholar] [CrossRef]
- Maghrebi, H.; Portigliatti, T.; Prouff, E. Breaking Cryptographic Implementations Using Deep Learning Techniques. In Security, Privacy, and Applied Cryptography Engineering; Carlet, C., Hasan, M., Saraswat, V., Eds.; Springer: Cham, Switzerland, 2016; Volume 10076. [Google Scholar]
- Cagli, E.; Dumas, C.; Prouff, E. Convolutional Neural Networks with Data Augmentation against Jitter-Based Countermeasures—Profiling Attacks without Pre-Processing. In Cryptographic Hardware and Embedded Systems (CHES 2017); Fischer, W., Homma, N., Eds.; Springer: Cham, Switzerland, 2017; Volume 10529. [Google Scholar]
- Das, D.; Golder, A.; Danial, J.; Ghosh, S.; Raychowdhury, A.; Sen, S. X-DeepSCA: Cross-Device Deep Learning Side Channel Attack. In Proceedings of the 2019 56th ACM/IEEE Design Automation Conference (DAC), Las Vegas, NV, USA, 2–6 June 2019; pp. 1–6. [Google Scholar]
- Das, D.; Maity, S.; Nasir, S.B.; Ghosh, S.; Raychowdhury, A.; Sen, S. High efficiency power side-channel attack immunity using noise injection in attenuated signature domain. In Proceedings of the 2017 IEEE International Symposium on Hardware Oriented Security and Trust (HOST), Mclean, VA, USA, 1–5 May 2017; pp. 62–67. [Google Scholar] [CrossRef]
- Das, D.; Maity, S.; Nasir, S.B.; Ghosh, S.; Raychowdhury, A.; Sen, S. ASNI: Attenuated Signature Noise Injection for Low-Overhead Power Side-Channel Attack Immunity. IEEE Trans. Circuits Syst. Regul. Pap. 2018, 65, 3300–3311. [Google Scholar] [CrossRef]
- Das, D.; Nath, M.; Chatterjee, B.; Ghosh, S.; Sen, S. STELLAR: A Generic EM Side-Channel Attack Protection through Ground-Up Root-cause Analysis. In Proceedings of the 2019 IEEE International Symposium on Hardware Oriented Security and Trust (HOST), McLean, VA, USA, 5–10 May 2019; pp. 11–20. [Google Scholar] [CrossRef]
- Das, D.; Nath, M.; Ghosh, S.; Sen, S. Killing EM Side-Channel Leakage at its Source. In Proceedings of the 2020 IEEE 63rd International Midwest Symposium on Circuits and Systems (MWSCAS), Springfield, MA, USA, 9–12 August 2020; pp. 1108–1111. [Google Scholar] [CrossRef]
- Das, D.; Danial, J.; Golder, A.; Modak, N.; Maity, S.; Chatterjee, B.; Seo, D.; Chang, M.; Varna, A.; Krishnamurthy, H.; et al. 27.3 EM and Power SCA-Resilient AES-256 in 65nm CMOS Through >350× Current-Domain Signature Attenuation. In Proceedings of the 2020 IEEE International Solid-State Circuits Conference (ISSCC), San Francisco, CA, USA, 16–20 February 2020; pp. 424–426. [Google Scholar] [CrossRef]
- Hwang, D.D.; Tiri, K.; Hodjat, A.; Lai, B.C.; Yang, S.; Schaumont, P.; Verbauwhede, I. AES-Based Security Coprocessor IC in 0.18um CMOS With Resistance to Differential Power Analysis Side-Channel Attacks. IEEE J. Solid-State Circ. 2006, 41, 781–792. [Google Scholar] [CrossRef]
- Sen, S.; Raychowdhury, A. Electromagnetic and Machine Learning Side-Channel Attacks and Low-Overhead Generic Countermeasures. 2019. Available online: https://ches.iacr.org/2019/src/tutorials/ches2019tutorial_Sen.pdf (accessed on 30 September 2020).
- Akkar, M.L.; Bevan, R.; Dischamp, P.; Moyart, D. Power Analysis, What Is Now Possible... Advances in Cryptology— ASIACRYPT 2000; Okamoto, T., Ed.; Lecture Notes in Computer Science; Springer: Berlin/Heidelberg, Germany, 2000; pp. 489–502. [Google Scholar] [CrossRef]
- Poschmann, A.; Moradi, A.; Khoo, K.; Lim, C.W.; Wang, H.; Ling, S. Side-Channel Resistant Crypto for Less than 2300 GE. J. Cryptol. 2011, 24, 322–345. [Google Scholar] [CrossRef]
- Tokunaga, C.; Blaauw, D. Securing Encryption Systems With a Switched Capacitor Current Equalizer. IEEE J. Solid-State Circuits 2010, 45, 23–31. [Google Scholar] [CrossRef]
- Kar, M.; Singh, A.; Mathew, S.K.; Rajan, A.; De, V.; Mukhopadhyay, S. Reducing Power Side-Channel Information Leakage of AES Engines Using Fully Integrated Inductive Voltage Regulator. IEEE J. Solid-State Circuits 2018, 53, 2399–2414. [Google Scholar] [CrossRef]
- Singh, A.; Kar, M.; Chekuri, V.C.K.; Mathew, S.K.; Rajan, A.; De, V.; Mukhopadhyay, S. Enhanced Power and Electromagnetic SCA Resistance of Encryption Engines via a Security-Aware Integrated All-Digital LDO. IEEE J. Solid-State Circuits 2020, 55, 478–493. [Google Scholar] [CrossRef]
- Golder, A.; Das, D.; Danial, J.; Ghosh, S.; Sen, S.; Raychowdhury, A. Practical Approaches Toward Deep-Learning-Based Cross-Device Power Side-Channel Attack. IEEE Trans. Very Large Scale Integr. (VLSI) Syst. 2019, 27, 2720–2733. [Google Scholar] [CrossRef]
- Dataset/Framework. 2020. Available online: Https://github.com/SparcLab/X-DeepSCA (accessed on 30 September 2020).
- Danial, J.; Das, D.; Ghosh, S.; Raychowdhury, A.; Sen, S. SCNIFFER: Low-Cost, Automated, Efficient Electromagnetic Side-Channel Sniffing. IEEE Access 2020, 8, 173414–173427. [Google Scholar] [CrossRef]
- SCNIFFER Demo. 2019. Available online: Https://www.youtube.com/watch?v=5aVkcgyDJdE (accessed on 30 September 2020).
- Das, D.; Danial, J.; Golder, A.; Modak, N.; Maity, S.; Chatterjee, B.; Seo, D.; Chang, M.; Varna, A.; Krishnamurthy, H.; et al. EM and Power SCA-resilient AES-256 through >350× Current Domain Signature Attenuation & Local Lower Metal Routing. J. Solid State Circuits 2020. [Google Scholar] [CrossRef]
- Das, D.; Danial, J.; Golder, A.; Ghosh, S.; Wdhury, A.R.; Sen, S. Deep Learning Side-Channel Attack Resilient AES-256 using Current Domain Signature Attenuation in 65nm CMOS. In Proceedings of the 2020 IEEE Custom Integrated Circuits Conference (CICC), Boston, MA, USA, 22–25 March 2020; pp. 1–4. [Google Scholar] [CrossRef]
- ISSCC 2020 Demo: Hardware for Efficient Side-Channel Security. 2020. Available online: https://www.youtube.com/watch?v=sh5_SWM7o_U (accessed on 30 September 2020).










Publisher’s Note: MDPI stays neutral with regard to jurisdictional claims in published maps and institutional affiliations. |
© 2020 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Das, D.; Sen, S. Electromagnetic and Power Side-Channel Analysis: Advanced Attacks and Low-Overhead Generic Countermeasures through White-Box Approach. Cryptography 2020, 4, 30. https://doi.org/10.3390/cryptography4040030
Das D, Sen S. Electromagnetic and Power Side-Channel Analysis: Advanced Attacks and Low-Overhead Generic Countermeasures through White-Box Approach. Cryptography. 2020; 4(4):30. https://doi.org/10.3390/cryptography4040030
Chicago/Turabian StyleDas, Debayan, and Shreyas Sen. 2020. "Electromagnetic and Power Side-Channel Analysis: Advanced Attacks and Low-Overhead Generic Countermeasures through White-Box Approach" Cryptography 4, no. 4: 30. https://doi.org/10.3390/cryptography4040030
APA StyleDas, D., & Sen, S. (2020). Electromagnetic and Power Side-Channel Analysis: Advanced Attacks and Low-Overhead Generic Countermeasures through White-Box Approach. Cryptography, 4(4), 30. https://doi.org/10.3390/cryptography4040030





