A Survey of Image Security in Wireless Sensor Networks
Abstract
:1. Introduction
2. Security Issues in WSN
- Confidentiality: Sensed data and control information may be confidential, since their content must not be accessible by intruders or external elements. Control information, such as sensors’ locations and even cryptography keys, is confidential in the sense that it may be exploited to compromise the network. Moreover, some sensed data, as in military applications, may be highly confidential.
- Integrity: While confidentiality avoids attackers stealing data, integrity will be concerned with data changing. If data are manipulated, this may compromise the network operation or even allow the exploitation of other vulnerabilities.
- Authenticity: Since additional packets may be inserted into the network, there should be a way to authenticate their origins. It is then not only necessary to assure that sensed data comes from valid nodes, but also to avoid malicious control information from foreign nodes being processed.
- Freshness: Control messages may propagate information that should only be valid in a defined time scope. Attackers should not be able to exploit old messages, containing, for example, cryptography keys.
- Localization: Sensor localization is a key functionality of wireless sensor networks, especially when they are randomly deployed. Secure localization is then required to allow only accurate information to be considered.
- Availability: Wireless sensor networks are subject to different availability attacks, which may severely compromise the network operation. Such attacks can disconnect nodes, part of the network or even avoid relevant areas of a monitored field being sensed by any sensor node [11].
2.1. Vulnerabilities and Attacks
- Interruption: when network availability is compromised, usually resulting from DoS attacks.
- Interception: when network confidentiality is compromised, allowing unauthorized access to sensor nodes and sensed data.
- Modification: when network integrity is compromised, with modified packets potentially leading to an unexpected and misled operation of the network.
- Fabrication: when network authentication is compromised, the trustworthiness of network elements and transmitted data may be affected by false information.
2.2. Defense Mechanisms
3. Image Cryptography
3.1. Symmetric Encryption
- Advanced Encryption Standard (AES): This is one of the most popular symmetric encryption algorithms [27]. Also known as Rijndael, AES is an encryption scheme by blocking used in large-scale systems. In WSN, this is the main mechanism of encryption adopted by the WirelessHART standard [28]. An energy-efficient security scheme that uses AES as the main encryption algorithm for WSN is presented in [29].
- Data Encryption Standard (DES): This is a low-complexity algorithm that uses a small 56-bit key [30]. Despite some failures, DES was studied more thoroughly in academia, motivating the development of modern systems of cryptanalysis.
- International Data Encryption Algorithm (IDEA): This algorithm is a block cipher designed to be the replacement for DES [31]. It exploits confusion and diffusion to produce the cipher text, with 128-bit keys and the use of XOR gates, 16-bit addition and multiplication (as operations are made with blocks of 16 bits, the algorithm is very efficient in 16-bit microprocessors, common in sensor motes).
3.2. Asymmetric Encryption
- RSA: Based on classical theories of numbers, this was also employed to provide support to the concept of the digital signature, becoming one of the major innovations in public-key cryptography [35].
- Elliptic curve cryptography (ECC): This is a collective term for multiple key exchange algorithms and agreement protocols [36,37] (e.g., ECDH (Elliptic Curve Diffie-Hellman), ECDSA (Elliptic Curve Digital Signature Algorithm) and ECMV (Elliptic Curve Menezes-Vanstone) [32]. ECC provides security equivalent to RSA, but with much smaller keys, becoming more attractive for WSN. In general, smaller keys generate less memory usage, more bandwidth savings and less computing overhead [38].
| Algorithm | Signature | Key exchange | ||
|---|---|---|---|---|
| - | Sign | Verify | Client | Server |
| RSA-1024 | 304 | 11.9 | 15.4 | 304 |
| ECC-160 | 22.82 | 45.09 | 22.3 | 22.3 |
| RSA-2048 | 2302.7 | 53.7 | 57.2 | 2302.7 |
| ECC-224 | 61.54 | 121.98 | 60.4 | 60.4 |
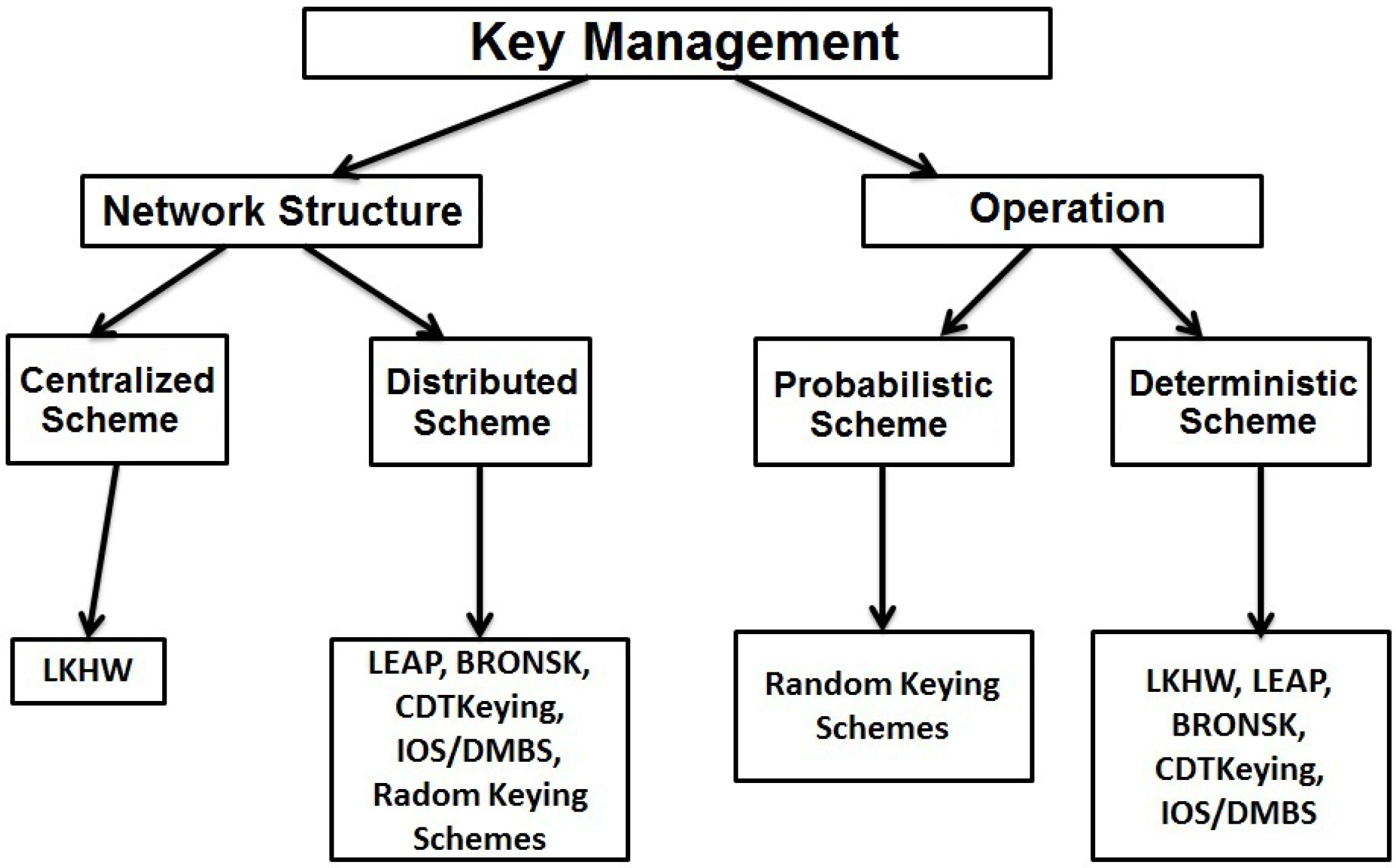
3.3. Key Management
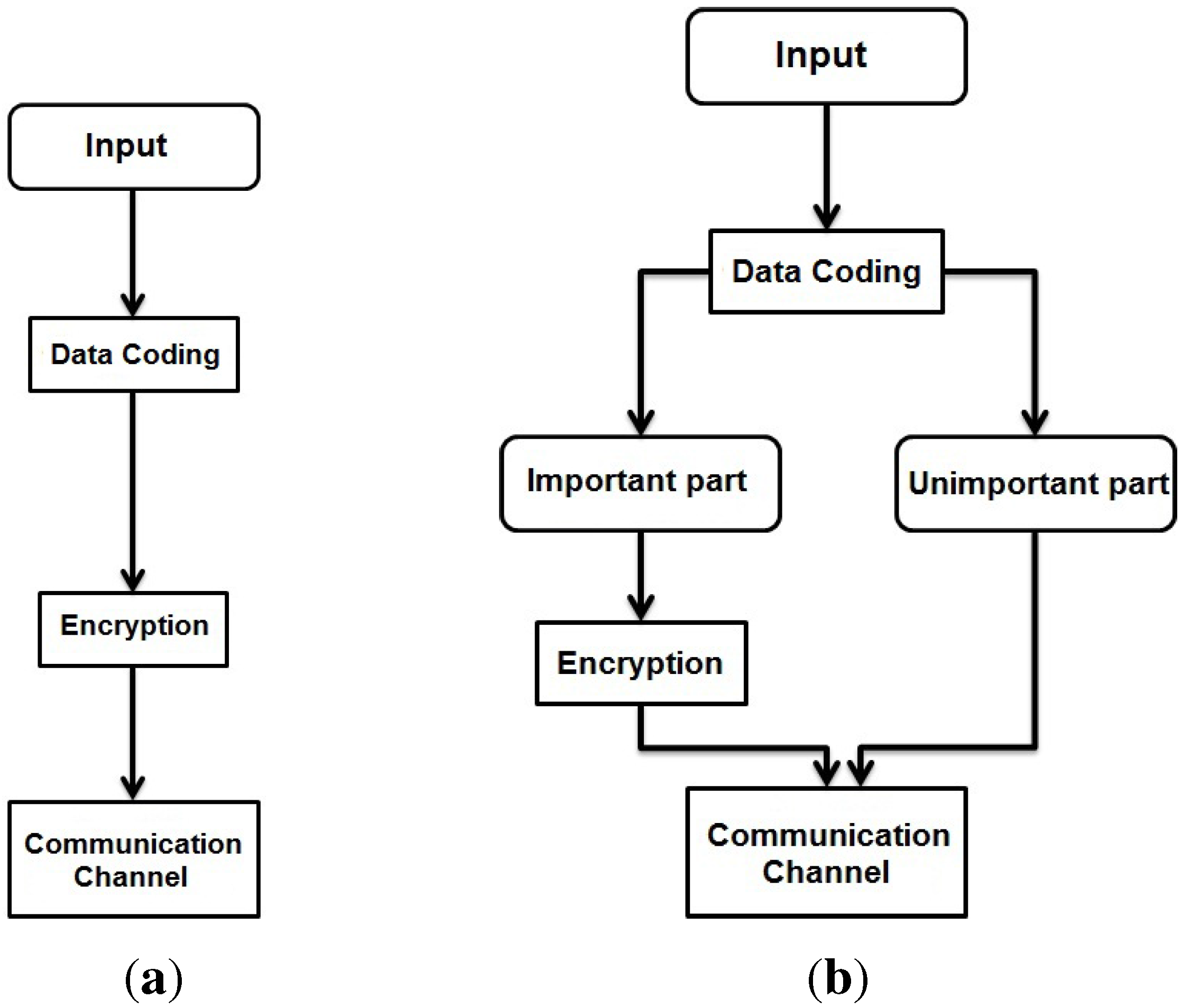
4. Selective Image Encryption
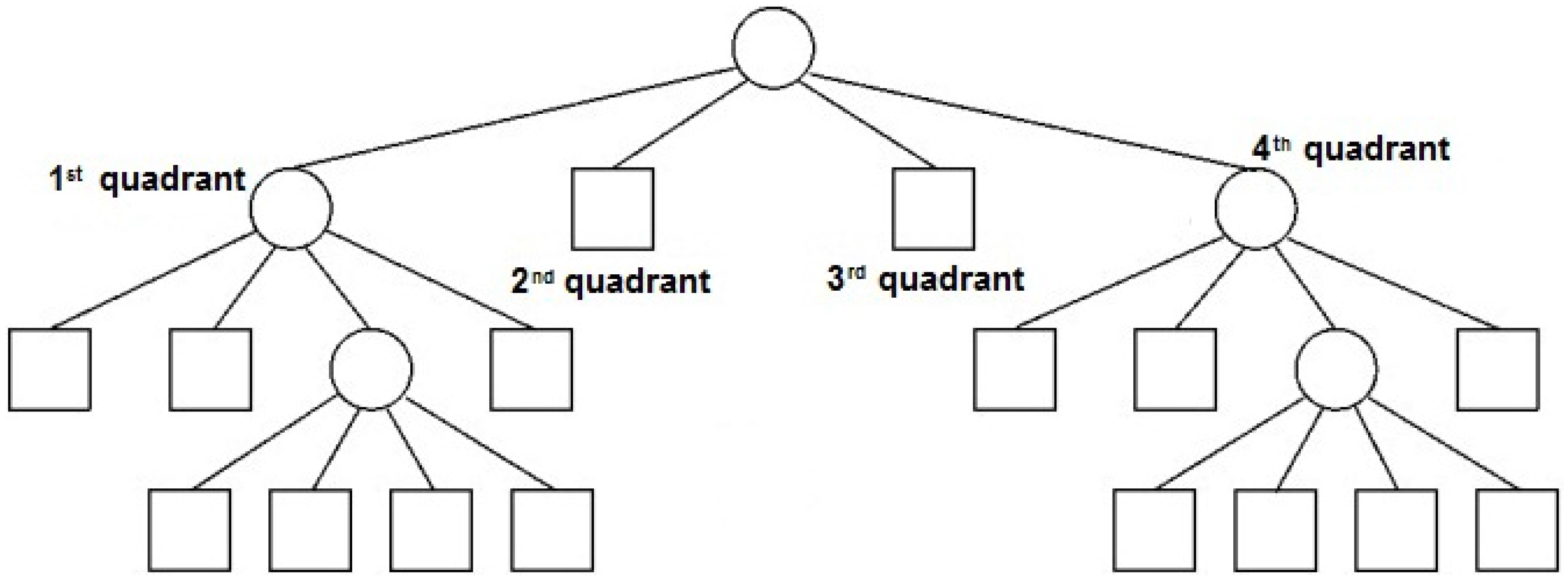
4.1. Quadtree-Based Image Coding

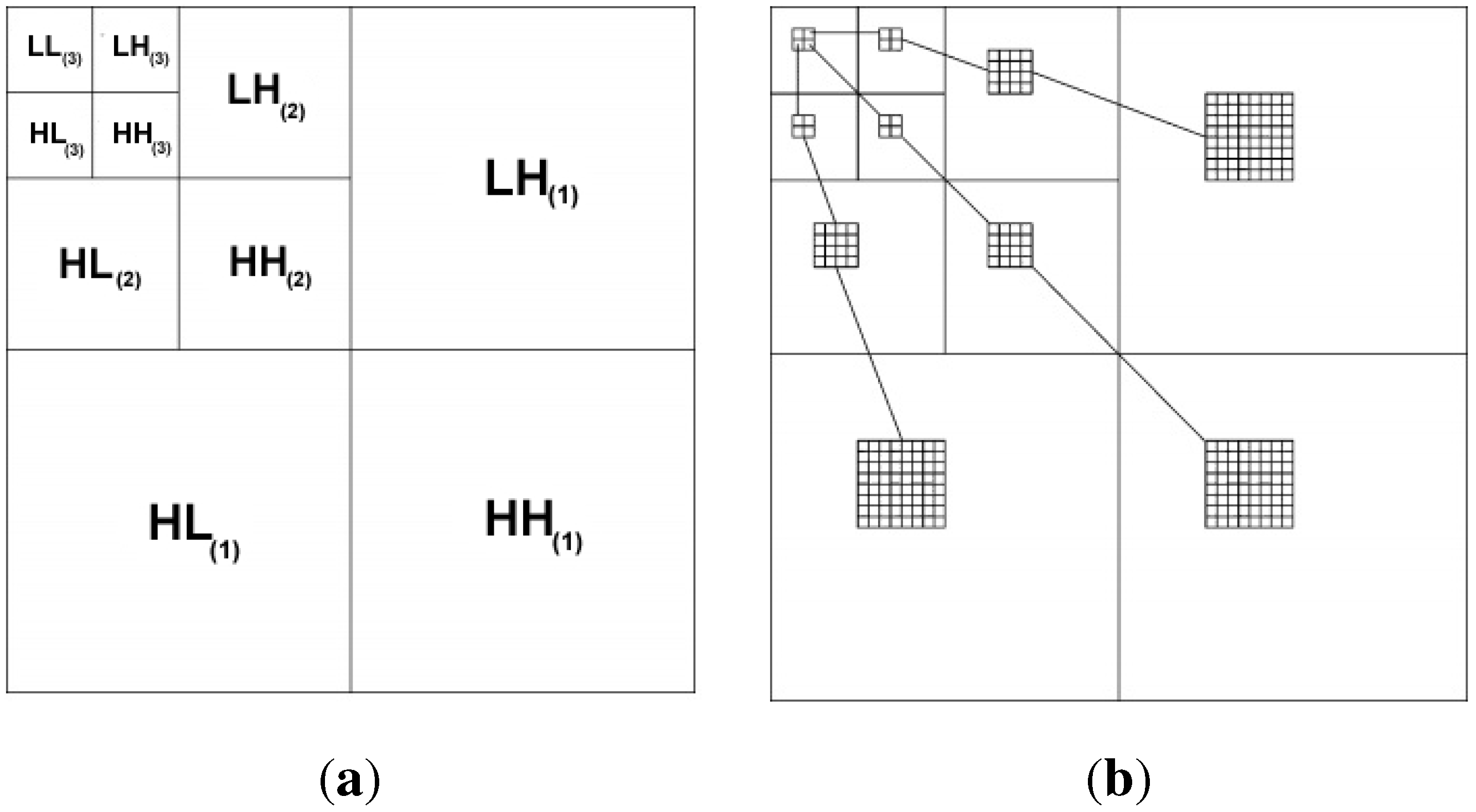
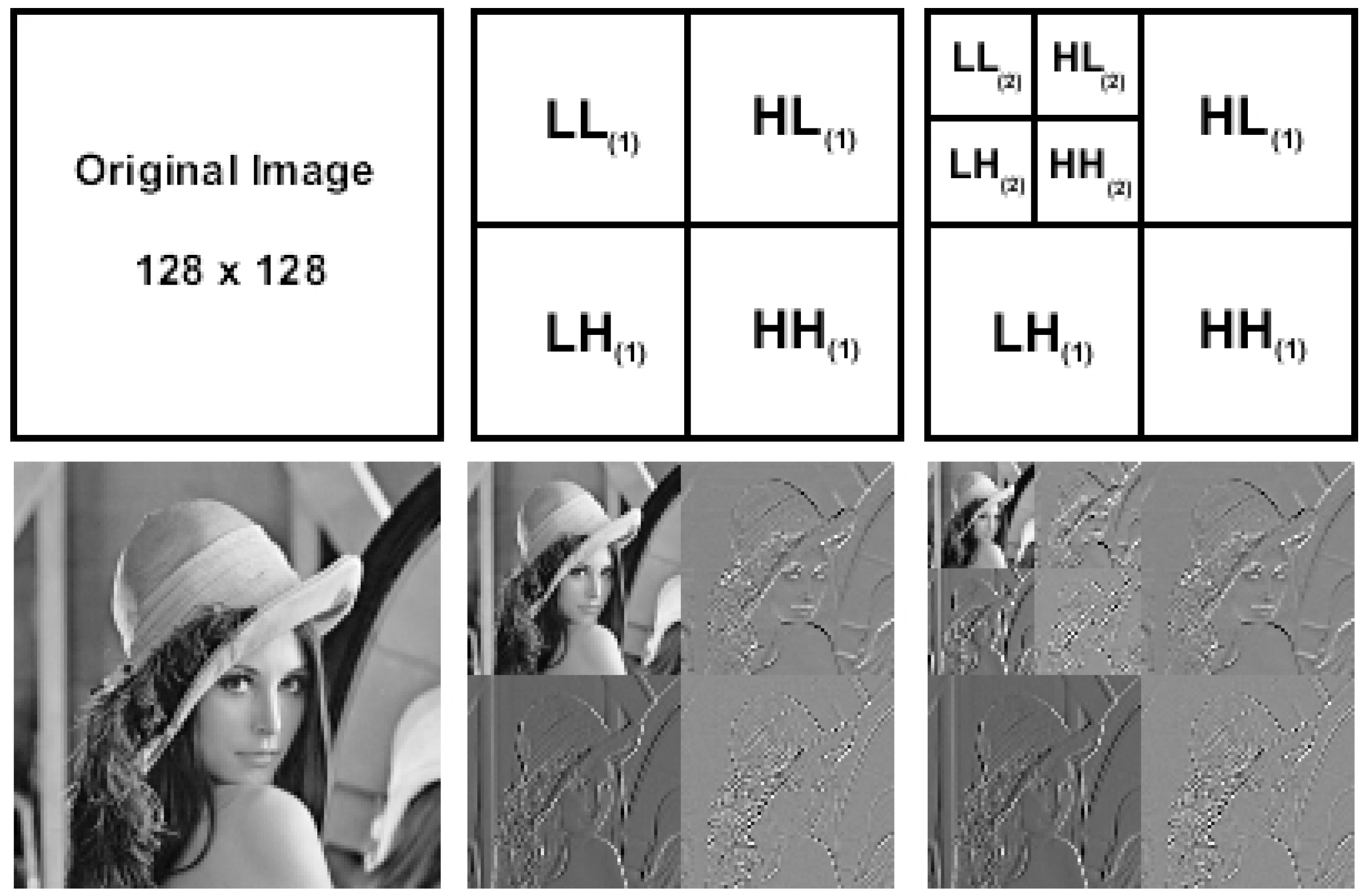
4.2. Wavelet-Based Image Coding
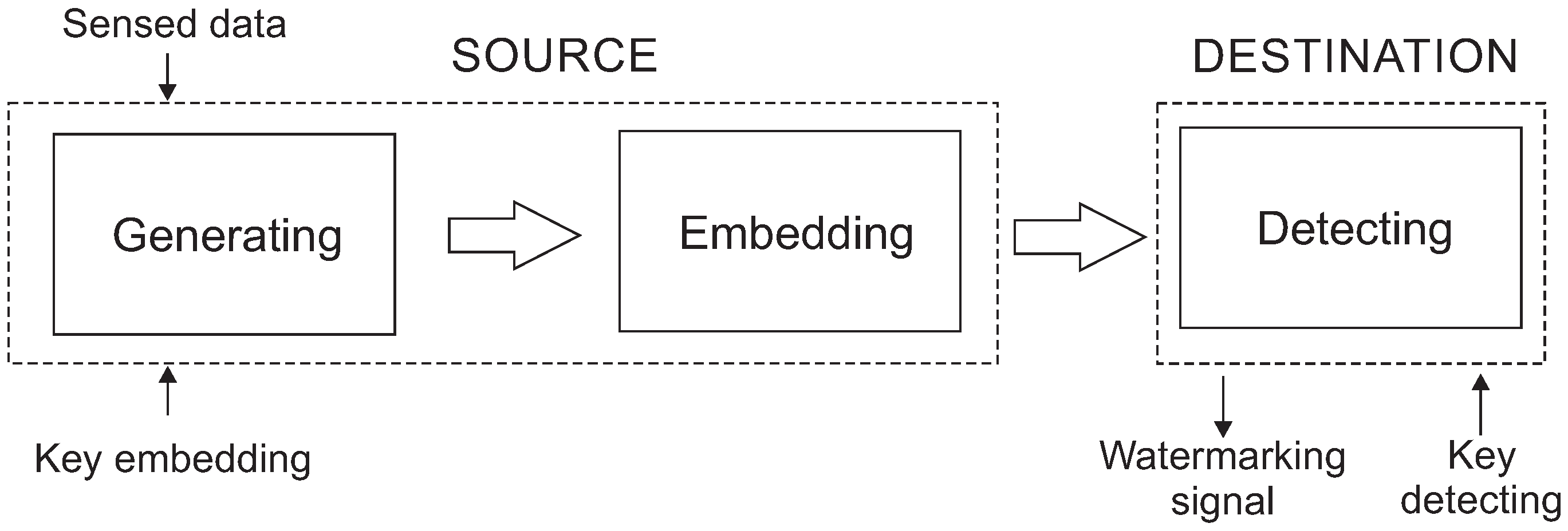
5. Watermarking
6. Secure Image Monitoring
6.1. Image Compression and Aggregation
6.2. Processing of Image Contents
6.3. Hardware Performance
7. Research Directions
8. Conclusions
Author Contributions
Conflicts of Interest
References
- Baronti, P.; Pillai, P.; Chook, V.W.; Chessa, S.; Gotta, A.; Hu, Y.F. Wireless sensor networks: A survey on the state of the art and the 802.15. 4 and ZigBee standards. Comput. Commun. 2007, 30, 1655–1695. [Google Scholar]
- Yick, J.; Mukherjee, B.; Ghosal, D. Wireless sensor network survey. Comput. Netw. 2008, 52, 2292–2330. [Google Scholar] [CrossRef]
- Costa, D.; Guedes, L. The coverage problem in video-based wireless sensor networks: A survey. Sensors 2010, 10, 8215–8247. [Google Scholar] [CrossRef] [PubMed]
- Almalkawi, I.; Zapata, M.; Al-Karaki, J.; Morillo-Pozo, J. Wireless multimedia sensor networks: Current trends and future directions. Sensors 2010, 10, 6662–6717. [Google Scholar] [CrossRef] [PubMed]
- Aziz, S.M.; Pham, D.M. Energy efficient image transmission in wireless multimedia sensor networks. IEEE Commun. Lett. 2013, 17, 1084–1087. [Google Scholar] [CrossRef]
- Sen, J. A Survey on Wireless Sensor Network Security. Int. J. Commun. Netw. Inf. Secur. 2009, 1, 55–78. [Google Scholar]
- Guerrero-Zapata, M.; Zilan, R.; Barcelo-Ordinas, J.M.; Bicakci, K.; Tavli, B. The future of security in wireless multimedia sensor networks. Telecommun. Syst. 2010, 45, 77–91. [Google Scholar] [CrossRef]
- Modares, H.; Salleh, R.; Moravejosharieh, A. Overview of security issues in wireless sensor networks. In Proceedings of International Conference on Computational Intelligence, Modelling & Simulation, Langkawi, Malaysia, 20–22 September 2011; pp. 308–311.
- Pathan, A.S.K.; Lee, H.W.; Hong, C.S. Wireless sensor networks: Security issues and challenges. Int. J. Comput. Inf. Technol. 2011, 2, 62–67. [Google Scholar]
- Kumar, V.; Jain, A.; Barwal, P.N. Wireless Sensor Networks: Security Issues, Challenges and Solutions. Int. J. Inf. Comput. Technol. 2014, 4, 859–868. [Google Scholar]
- Costa, D.G.; Silva, I.; Guedes, L.A.; Vasques, F.; Portugal, P. Availability Issues in Wireless Visual Sensor Networks. Sensors 2014, 14, 2795–2821. [Google Scholar] [CrossRef] [PubMed]
- Wang, Y.; Attebury, G.; Ramamurthy, B. Security issues in wireless sensor networks: A survey. Int. J. Future Gen. Commun. Netw. 2013, 6, 97–116. [Google Scholar] [CrossRef]
- Winkler, T.; Rinner, B. Security and privacy protection in visual sensor networks: A survey. ACM Comput. Surv. 2014, 47, 97–116. [Google Scholar] [CrossRef]
- Chen, X.; Makki, K.; Yen, K.; Pissinou, N. Sensor network security: A survey. IEEE Commun. Surv. Tutor. 2009, 11, 52–73. [Google Scholar] [CrossRef]
- Zhong, C.; Mo, Y.; Zhao, J.; Lin, C.; Lu, X. Secure clustering and reliable multi-path route discovering in wireless sensor networks. In Proceedings of the International Symposium on Parallel Architectures, Algorithms and Programming, Beijing, China, 13–15 July 2014; pp. 130–134.
- Lu, H.; Li, J.; Guizani, M. Secure and efficient data transmission for cluster-based wireless sensor networks. IEEE Trans. Parallel Distrib. Syst. 2014, 25, 750–761. [Google Scholar]
- Ameen, M.A.; Liu, J.; Kwak, K. Security and privacy issues in wireless sensor networks for healthcare applications. J. Med. Syst. 2012, 36, 93–101. [Google Scholar] [CrossRef] [PubMed]
- Harjito, B.; Han, S. Wireless multimedia sensor networks applications and security challenges. In Proceedings of International Conference on Broadband, Wireless Computing, Communication and Applications, Fukuoka, Japan, 4–6 November 2010; pp. 842–846.
- Costa, D.G.; Guedes, L.A.; Vasques, F.; Portugal, P. Research trends in wireless visual sensor networks when exploiting prioritization. Sensors 2015, 1, 1760–1784. [Google Scholar] [CrossRef] [PubMed]
- Naveenkumar, S.K.; Panduranga, H.T.; Kiran. Partial image encryption for smart camera. In Proceedings of the International Conference on Recent Trends in Information Technology, Chennai, India, 25–27 July 2013; pp. 126–132.
- Hill, J.; Szewczyk, R.; Woo, A.; Hollar, S.; Culler, D.; Pister, K. System architecture directions for networked sensors. In Proceedings of International Conference an Architectural Support for Programming Languages and Operation Systems, Cambridge, USA, 13–15 November 2010; pp. 93–104.
- Ganeriwal, S.; Balzano, L.K.; Srivastava, M.B. Reputation-based framework for high integrity sensor networks. ACM Trans. Sens. Netw. 2008, 4. Article No. 15. [Google Scholar] [CrossRef]
- Jiang, J.; Han, G.; Wang, F.; Shu, L.; Guizani, M. An efficient distributed trust model for wireless sensor networks. IEEE Trans. Parallel Distrib. Syst. 2014, 26, 1228–1237. [Google Scholar] [CrossRef]
- Butun, I.; Morgera, S.; Sankar, R. A survey of intrusion detection systems in wireless sensor networks. IEEE Commun. Surv. Tutor. 2014, 16, 266–282. [Google Scholar] [CrossRef]
- Zhou, Y.; Fang, Y.; Zhang, Y. Securing wireless sensor networks: A survey. IEEE Commun. Surv. Tutor. 2008, 10, 6–28. [Google Scholar] [CrossRef]
- Czarlinska, A.; Huh, W.; Kundur, D. On privacy and security in distributed visual sensor networks. In Proceedings of International Conference on Image Processing, San Diego, CA, USA, 12–15 October 2008; pp. 1692–1695.
- Wang, Q.X.; Xu, T.; Wu, P. Application research of the AES encryption algorithm on the engine anti-theft system. In Proceedings of IEEE International Conference on Vehicular Electronics and Safety, Beijing, China, 10–12 July 2011; pp. 25–29.
- Raza, S.; Slabbert, A.; Voigt, T.; Landernas, K. Security considerations for the WirelessHART protocol. In Proceedings of IEEE Emerging Technologies and Factory Automation, Mallorca, Spain, 22–25 September 2009; pp. 1–8.
- Mahmoud, N.E.; Taha, M.H.N.; mahdy, H.E.N.; Saroit, I.A. A Secure Energy Efficient Schema for Wireless Multimedia Sensor Networks. CiiT Int. J. Wirel. Commun. 2013, 5, 235–246. [Google Scholar]
- Mandal, A.K.; Parakash, C.; Tiwari, A. Performance evaluation of cryptographic algorithms: DES and AES. In Proceedings of IEEE Students’ Conference on Electrical, Electronics and Computer Science, Bhopal, India, 1–2 March 2012.
- Modugu, R.; Yong-Bin, K.; Minsu, C. Design and performance measurement of efficient IDEA (International Data Encryption Algorithm) crypto-hardware using novel modular arithmetic components. In Proceedings of IEEE Instrumentation and Measurement Technology Conference, Austin, TX, USA, 3–6 May 2010; pp. 1222–1227.
- Gaubatz, G.; Kaps, J.P.; Ozturk, E.; Sunar, B. State of the art in ultra-low power public key cryptography for wireless sensor networks. In Proceedings of IEEE International Conference on Pervasive Computing and Communications Workshops, Kauai Island, HI, USA, 8–12 March 2005; pp. 146–150.
- Lenstra, A.K.; Verhuel, E.R. Selecting cryptographic key sizes. J. Cryptol. 2001, 14, 255–293. [Google Scholar] [CrossRef]
- Al-Hamami, A.H.; Aldariseh, I.A. Enhanced method for RSA cryptosystem algorithm. In Proceedings of International Conference on Advanced Computer Science Applications and Technologies, Kuala Lumpur, Malaysia, 26–28 November 2012; pp. 402–408.
- Al-Haija, Q.A.; Tarayrah, M.A.; Al-Qadeeb, H.; Al-Lwaimi, A. A tiny RSA cryptosystem based on Arduino microcontroller useful for small scale networks. Procedia Comput. Sci. 2014, 34, 639–646. [Google Scholar] [CrossRef]
- Amara, M.; Siad, A. Elliptic Curve Cryptography and its applications. In Proceedings of International Workshop on Systems, Signal Processing and their Applications, Tipaza, Algeria, 9–11 May 2011; pp. 247–250.
- Rahuman, A.K.; Athisha, G. Reconfigurable architecture for Elliptic Curve Cryptography using FPGA. Math. Probl. Eng. 2013, 2013, 1–8. [Google Scholar] [CrossRef]
- Raju, G.V.S.; Akbani, R. Elliptic curve cryptosystem and its applications. In Proceedings of the IEEE International Conference on Systems, Man and Cybernetics, Washington, WA, USA, 5–8 October 2003; pp. 1540–1543.
- Wander, A.S.; Gura, N.; Eberle, H.; Gupta, V.; Shantz, S.C. Energy analysis of public-key cryptography for wireless sensor networks. In Proceedings of the IEEE International Conference on Pervasive Computing and Communications, Kauai, HI, USA, 8–12 March 2005; pp. 324–328.
- Macedonio, D.; Merro, M. A semantic analysis of key management protocols for wireless sensor networks. Sci. Comput. Program. 2014, 81, 53–78. [Google Scholar] [CrossRef]
- Di Pietro, R.; Mancini, L.V.; Law, Y.W.; Etalle, S.; Havinga, P.; et al. LKHW: A directed diffusion-based secure multicast scheme for wireless sensor networks. In Proceedings of the International Conference on Parallel Processing Workshops, Kaohsiung, Taiwan, 6–9 October 2003; pp. 397–406.
- Zhu, S.; Setia, S.; Jajodia, S. LEAP: Efficient security mechanisms for large-scale distributed sensor networks. In Proceedings of the ACM Conference on Computer and Communications Security, Washington, WA, USA, 27–30 October 2003; pp. 62–72.
- Wang, Y.; Attebury, G.; Ramamurthy, B. A survey of security issues in wireless sensor networks. IEEE Commun. Surv. Tutor. 2006, 8, 2–23. [Google Scholar] [CrossRef]
- Eschenauer, L.; Gligor, V.D. A key-management scheme for distributed sensor networks. In Proceedings of the ACM Conference on Computer and Communications Security, Washington, USA, 18–22 November 2002; pp. 41–47.
- Wang, Y.; Attebury, G.; Ramamurthy, B. Index-based selective audio encryption for wireless multimedia sensor networks. IEEE Trans. Multimed. 2010, 12, 215–223. [Google Scholar] [CrossRef]
- Sadourny, Y.; Conan, V. A proposal for supporting selective encryption in JPSEC. IEEE Trans. Consum. Electron. 2003, 49, 846–849. [Google Scholar] [CrossRef]
- Pfarrhofer, R.; Uhl, A. Selective image encryption using JBIG. Commun. Multimed. Secur. 2005, 3677, 98–107. [Google Scholar]
- Liu, J.L. Efficient selective encryption for JPEG 2000 images using private initial table. Pattern Recognit. 2006, 39, 1509–1517. [Google Scholar] [CrossRef]
- Grangetto, M.; Magli, E.; Olmo, G. Fast encryption of JPEG 2000 images in wireless multimedia sensor networks. IEEE Trans. Multimed. 2006, 8, 905–917. [Google Scholar] [CrossRef]
- Podesser, M.; Schmidt, H.P.; Uhl, A. Selective bitplane encryption for secure transmission of image data in mobile environments. In Proceedings of the 5th IEEE Nordic Signal Processing Symposium, TromsoTrondheim, Norway, 4–7 October 2002; pp. 1–20.
- Khashan, O.A.; Zin, A.M.; Sundarajan, E.A. Performance study of selective encryption in comparison to full encryption for still visual images. J. Zhejiang Univ. 2014, 15, 435–444. [Google Scholar] [CrossRef]
- Jinmei, L.; Guoyu, W. A refined quadtree-based automatic classification method for remote sensing image. In Proceedings of the International Conference on Computer Science and Network Technology, Harbin, China, 24–26 December 2011; pp. 1703–1706.
- Nikolakopoulos, G.; Fanakis, N. A reconfigurable transmission scheme for lossy image transmission over congested wireless sensor networks. In Proceedings of the International Congress on Image and Signal Processing, Tianjin, China, 17–19 October 2009.
- Nikolakopoulos, G.; Kandris, D.; Tzes, A. Adaptive compression of slowly varying images transmitted over wireless sensor networks. Sensors 2010, 10, 7170–7191. [Google Scholar] [CrossRef] [PubMed]
- Massoudi, A.; Lefebvre, F.; Vleeschouwer, C.D.; Macq, B.; Quisquater, J.J. Overview on selective encryption of image and video: Challenges and perspectives. EURASIP J. Inf. Secur. 2008, 10. [Google Scholar] [CrossRef]
- Wang, Y.; Rane, S.; Boufounos, P.; Vetro, A. Distributed compression of zerotrees of wavelet coefficients. In Proceedings of the IEEE International Conference on Image Processing, Brussels, Belgium, 11–14 September 2011; pp. 1821–1824.
- Costa, D.G.; Guedes, L.A. A Discrete Wavelet Transform (DWT)-based energy-efficient selective retransmission mechanism for wireless image sensor networks. J. Sens. Actuator Netw. 2012, 1, 3–35. [Google Scholar] [CrossRef]
- Rachedi, A.; Kaddar, L.; Mehaoua, A. EDES- Efficient dynamic selective encryption framework to secure multimedia traffic in wireless sensor networks. In Proceedings of the IEEE Communication and Information Systems Security Symposium, Ottawa, ON, Canada, 10–15 June 2012; pp. 1026–1030.
- Wang, W.; Hempel, M.; Peng, D.; Wang, H.; Sharif, H.; Chen, H.H. On energy efficient encryption for video streaming in wireless sensor networks. IEEE Trans. Multimed. 2010, 12, 417–426. [Google Scholar] [CrossRef]
- Wang, W.; Peng, D.; Wang, H.; Sharif, H.; Chen, H.H. Energy-constrained quality optimization for secure image transmission in wireless sensor networks. Adv. Multimed. 2007, 2007, 1–9. [Google Scholar] [CrossRef]
- Xiang, T.; Yu, C.; Chei, F. Fast encryption of JPEG 2000 images in wireless multimedia sensor networks. Lecture Notes Comput. Sci. 2013, 7992, 196–205. [Google Scholar]
- Harjito, B.; Potdar, V.; Singh, J. Watermarking technique for wireless multimedia sensor networks: A state of the art. In Proceedings of the CUBE International Information Technology Conference, Pune, India, 3–5 September 2012; pp. 832–840.
- Harjito, B.; Potdar, V.; Singh, J. Watermarking technique for wireless sensor networks: A state of the art. In Proceedings of 8th International Conference on Semantics, Knowledge and Grids, Beijing, China, 22–24 October 2012; pp. 253–256.
- Shi, X.; Xiao, D. A reversible watermarking authentication scheme for wireless sensor networks. Inf. Sci. 2013, 240, 173–183. [Google Scholar] [CrossRef]
- Xiao, R.; Sun, X.; Yang, Y. Copyright protection in wireless sensor networks by watermarking. In Proceedings of International Conference on Intelligent Information Hiding and Multimedia Signal Processing, Harbin, China, 15–17 August 2008; pp. 7–10.
- Harjito, B.; Han, S.; Potdar, V.; Chang, E.; Xie, M. Secure communication in wireless multimedia sensor networks using watermarking. In Proceedings of the IEEE International Conference on Digital Ecosystems and Technologies, Dubai, 13–16 April 2010; pp. 640–645.
- Yu, P.; Yao, S.; Xu, J.; Zhang, Y.; Chang, Y. Copyright protection for digital image in wireless sensor network. In Proceedings of International Conference on Wireless Communications, Networking and Mobile Computing, Beijing, China, 24–26 September 2009; pp. 1–4.
- Elsabi, E.; Ozdemir, S. Secure data aggregation in wireless multimedia sensor networks via watermarking. In Proceedings of the International Conference on Application of Information and Communication Technologies, Tbilisi, 17–19 October 2012; pp. 1–6.
- Wang, H. Communication-resource-aware adaptive watermarking for multimedia authentication in wireless multimedia sensor networks. J. Supercomput. 2013, 64, 883–897. [Google Scholar] [CrossRef]
- Grieco, L.A.; Boggia, G.; Sicari, S.; Colombo, P. Secure wireless multimedia sensor networks: A survey. In Proceedings of the International Conference on Mobile Ubiquitous Computing, Systems, Services and Technologies, Sliema, Malta, 11–16 October 2009.
- Misra, S.; Reisslein, M.; Guoliang, X. A survey of multimedia streaming in wireless sensor networks. IEEE Commun. Surv. Tutor. 2008, 10, 18–39. [Google Scholar] [CrossRef]
- Chew, L.W.; Ang, L.M.; Seng, K.P. Survey of image compression algorithms in wireless sensor networks. In Proceedings of International Symposium on Information Technology, Kuala Lumpur, Malaysia, 26–28 August 2008.
- Ozdemir, S.; Xiao, Y. Secure data aggregation in wireless sensor networks: A comprehensive overview. Comput. Netw. 2009, 53, 2022–2037. [Google Scholar] [CrossRef]
- Gao, R.; Wen, Y.; Zhao, H.; Meng, Y. Secure Data Aggregation in Wireless Multimedia Sensor Networks Based on Similarity Matching. Int. J. Distrib. Sens. Netw. 2014, 2014, 494853:1–494853:6. [Google Scholar] [CrossRef]
- Razzaque, M.A.; Dobson, S. Energy-Efficient Sensing in Wireless Sensor Networks Using Compressed Sensing. Sensors 2014, 14, 2822–2859. [Google Scholar] [CrossRef]
- Tong, Y.; Zhao, M.; Wei, Z.; Liu, L. Compressive sensing image-fusion algorithm in wireless sensor networks based on blended basis functions. EURASIP J. Wirel. Commun. Netw. 2014, 2014, 150:1–150:6. [Google Scholar] [CrossRef]
- Chen, D.; Chang, Y.; Yan, R.; Yang, J. Tools for Protecting the Privacy of Specific Individuals in Video. EURASIP J. Adv. Signal Process. 2007, 2007, 75427:1–75427:9. [Google Scholar] [CrossRef]
- Toure, M.; Beiji, Z. Intelligent sensor for image control point of eigenface for face recognition. In Proceedings of International Conference on Signal Processing Systems, Dalian, China, 5–7 July 2010; pp. 769–774.
- Utsumi, Y.; Iwai, Y. Face tracking and recognition by using omnidirectional sensor network. In Proceedings of ACM/IEEE International Conference on Distributed Smart Cameras, Como, 30 August–2 September 2009; pp. 1–8.
- Pham, D.M.; Aziz, S.M. Object extraction scheme and protocol for energy efficient image communication over wireless sensor networks. Comput. Netw. 2013, 57, 2949–2960. [Google Scholar] [CrossRef]
- Aziz, S.M.; Pham, D.M. Efficient parallel architecture for multi-level forward discrete wavelet transform processors. Comput. Electr. Eng. 2012, 38, 1325–1335. [Google Scholar] [CrossRef]
- Ali, N.A.; Drieberg, M.; Sebastian, P. Deployment of MICAz mote for Wireless Sensor Network applications. In Proceedings of the IEEE International Conference on Computer Applications and Industrial Electronics, Penang, Malaysia, 4–7 December 2011; pp. 303–308.
- Pham, D.M.; Aziz, S. An energy efficient image compression scheme for Wireless Sensor Networks. In Proceedings of IEEE International Conference on Intelligent Sensors, Sensor Networks and Information Processing, Melbourne, Victoria, 2–5 April 2013; pp. 260–264.
- Hasan, K.K.; Ngah, U.K.; Salleh, M.F. Efficient Hardware-Based Image Compression Schemes for Wireless Sensor Networks: A Survey. Wirel. Pers. Commun. Int. J. 2014, 77, 1415–1436. [Google Scholar] [CrossRef]
- Pham, D.M.; Aziz, S.M. FPGA-Based Image Processor Architecture for Wireless Multimedia Sensor Network. In Proceedings of the International Conference on Embedded and Ubiquitous Computing, Melbourne, Victoria, 24–26 October 2011; pp. 100–105.
- Ong, J.J.; Ang, L.M.; Seng, K.P. Selective secure error correction on SPIHT coefficients for pervasive wireless visual network. Int. J. Ad Hoc Ubiquitous Comput. 2013, 13, 73–82. [Google Scholar] [CrossRef]
- Lee, D.U.; Kim, H.; Tu, S.; Rahimi, M.; Estrin, D.; Villasenor, J. Energy-optimized image communication on resource-constrained sensor platforms. In Proceedings of the 6th International Symposium on Information Processing in Sensor Networks, Cambridge, MA, USA, 25–27 April 2007; pp. 216–225.
- Lee, S.; Jeong, S.; Chung, Y.; Cho, H. Secure and energy-efficient image transmission for wireless sensor networks. In Proceedings of IEEE International Symposium on Parallel and Distributed Processing with Applications Workshop, Busan, Korea, 26–28 May 2011; pp. 137–140.
- Costa, D.G.; Guedes, L.A. Exploiting the sensing relevancies of source nodes for optimizations in visual sensor networks. Multimed. Tools Appl. 2013, 64, 549–579. [Google Scholar] [CrossRef]
- Costa, D.G.; Guedes, L.A.; Vasques, F.; Portugal, P. Adaptive monitoring relevance in camera networks for critical surveillance applications. Int. J. Distrib. Sens. Netw. 2013, 2013, 836721:1–836721:14. [Google Scholar] [CrossRef]
- Granjal, J.; Monteiro, E.; Silva, J.S. Security in the integration of low-power wireless sensor networks with the internet: A survey. Ad Hoc Netw. 2015, 24, 264–287. [Google Scholar] [CrossRef]
© 2015 by the authors; licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Gonçalves, D.D.O.; Costa, D.G. A Survey of Image Security in Wireless Sensor Networks. J. Imaging 2015, 1, 4-30. https://doi.org/10.3390/jimaging1010004
Gonçalves DDO, Costa DG. A Survey of Image Security in Wireless Sensor Networks. Journal of Imaging. 2015; 1(1):4-30. https://doi.org/10.3390/jimaging1010004
Chicago/Turabian StyleGonçalves, Danilo De Oliveira, and Daniel G. Costa. 2015. "A Survey of Image Security in Wireless Sensor Networks" Journal of Imaging 1, no. 1: 4-30. https://doi.org/10.3390/jimaging1010004
APA StyleGonçalves, D. D. O., & Costa, D. G. (2015). A Survey of Image Security in Wireless Sensor Networks. Journal of Imaging, 1(1), 4-30. https://doi.org/10.3390/jimaging1010004







