Data Preprocessing for Evaluation of Recommendation Models in E-Commerce
Abstract
1. Introduction
2. Related Work
2.1. General Sources of Errors and Data Cleaning Strategies
- Data entry errors: data entries recorded by humans from speech or written context, where most often there are fields of data stored that might not always have a value present; hence an improper default value may be assigned to this field without much consideration to whether or not the default value is a possible outcome of real data.
- Distillation errors: data that should be preprocessed before storing them onto a database to reduce complexity and noise of raw data, which if not considered, may impede final analysis. For example, incremental revenue or the conversion metrics calculated may be invalid if the prices utilized for each product varies in the currency they are stored against. It can then be beneficial to assert this when recording data for e-commerce businesses who have a global dominance, to standardize the currency used against one system (such as the USD) for all customer interactions. This notion serves as the background to Section 4.2.4 Uniform Data Management.
- Data Integration errors: when the data collected stems from various servers or sources where the merging of records into a single database may cause inconsistencies. For example, it is crucial that the timestamps of each user interaction on the database are stored against a standard time zone, such as using Coordinated Universal Time (UTC), and not against the time zone of the IP registering the interaction. This is discussed in Section 4.2.4.
2.2. Data Records Duplication
2.3. Web Bot Detection
3. Data Description
3.1. Data Collected
- A list of products shown to a user as recommendations are recorded along with DateTime and user information and is referred to as a hit.
- A click, add-to-cart, and buy action performed on products on the e-commerce website is recorded along with DateTime and user information.
- Each different web-element on the page of an e-commerce website that displays recommendation products referred to as a widget.
- To identify a unique visitor on the site, the cookie ID of the browser session is stored in the data along with the account username (i.e., user ID) in case the user is logged into his or her account.
- Cust ID is a mapping identifier created (Section 4.2.2) for the purposes of associating activity data under a unique ID using cookie and user ID.
3.2. Definition of Terms:
- Customer and visitor are used interchangeably to refer to an individual on an e-commerce website who performs activities on the website and is provided with recommendations.
- The webpages where widgets are located and personalized products are re-ordered on an e-commerce website are identified by one of the following categories:
- ○
- Home page: This is the first page visible when visiting an e-commerce site
- ○
- Product List Page (PLP): This is the page that re-orders a list of personalized products within a unique department of products (e.g., Home and Kitchen)
- ○
- Product Display Page (PDP): This page displays a specific product that was clicked on where similar products based on a defined relation to the viewed product are displayed (e.g., widgets like “You May Also Like”, “Similar products”)
- ○
- Cart page: The page on an e-commerce site that displays products that are currently in a customer’s purchase cart and might showcase products attributed to the class “People who bought this also bought”
3.3. Definitions of the Basic Evaluation Metrics
- Click-through rate (CTR) is a ratio that shows how often people who see your products end up clicking it. It can be computed by dividing the number of times a recommended product was clicked by the number of times recommendations are seen. This metric is ideally reflective of the influence personalized recommendations have had on a customer’s journey on the website.
- Add-to-cart-through rate (ATC-TR) and Buy-through rate (BTR) are defined similarly as CTR but using add to carts and buys, respectively.
- Conversion revenue is defined to be the total revenue earned through the purchase of recommended products.
4. Data Cleaning and Validation Methods
4.1. Issues Pertaining to Customer Behavior
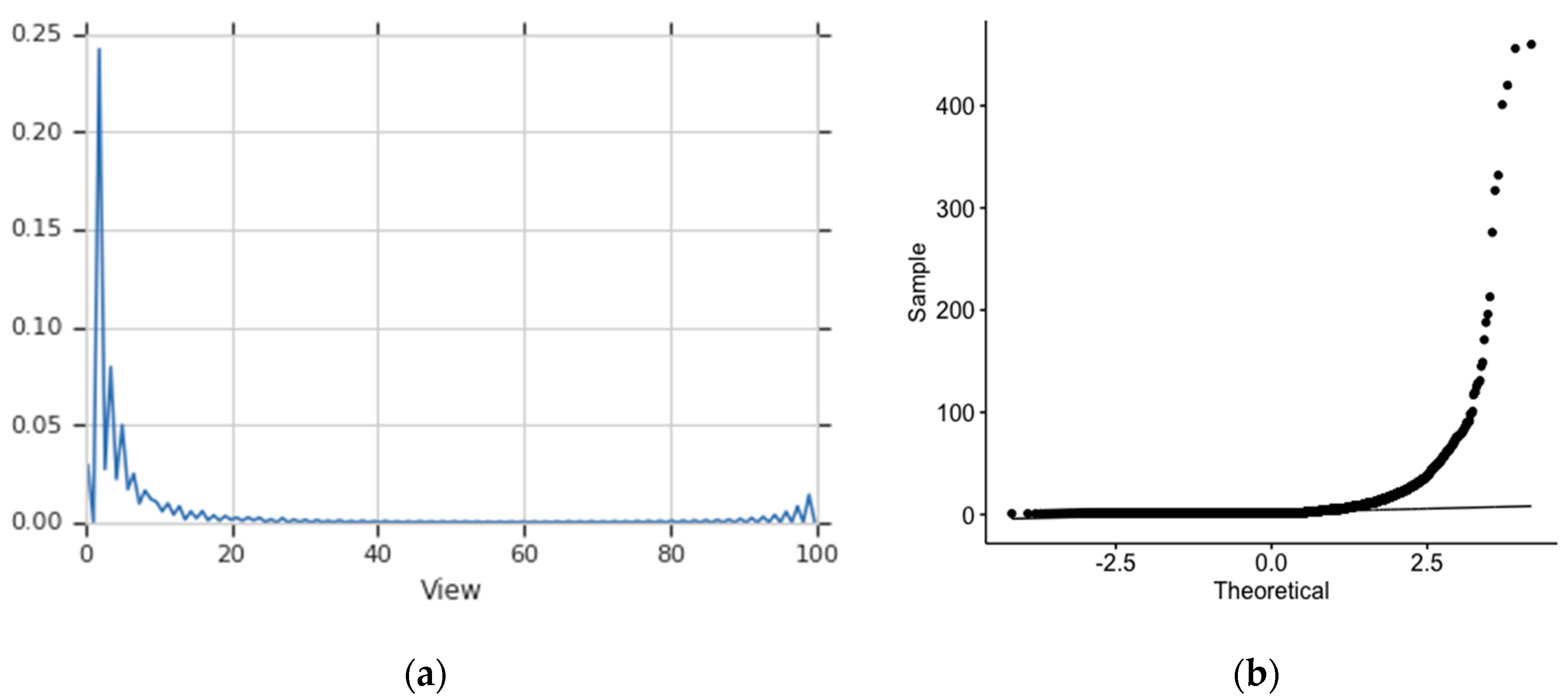
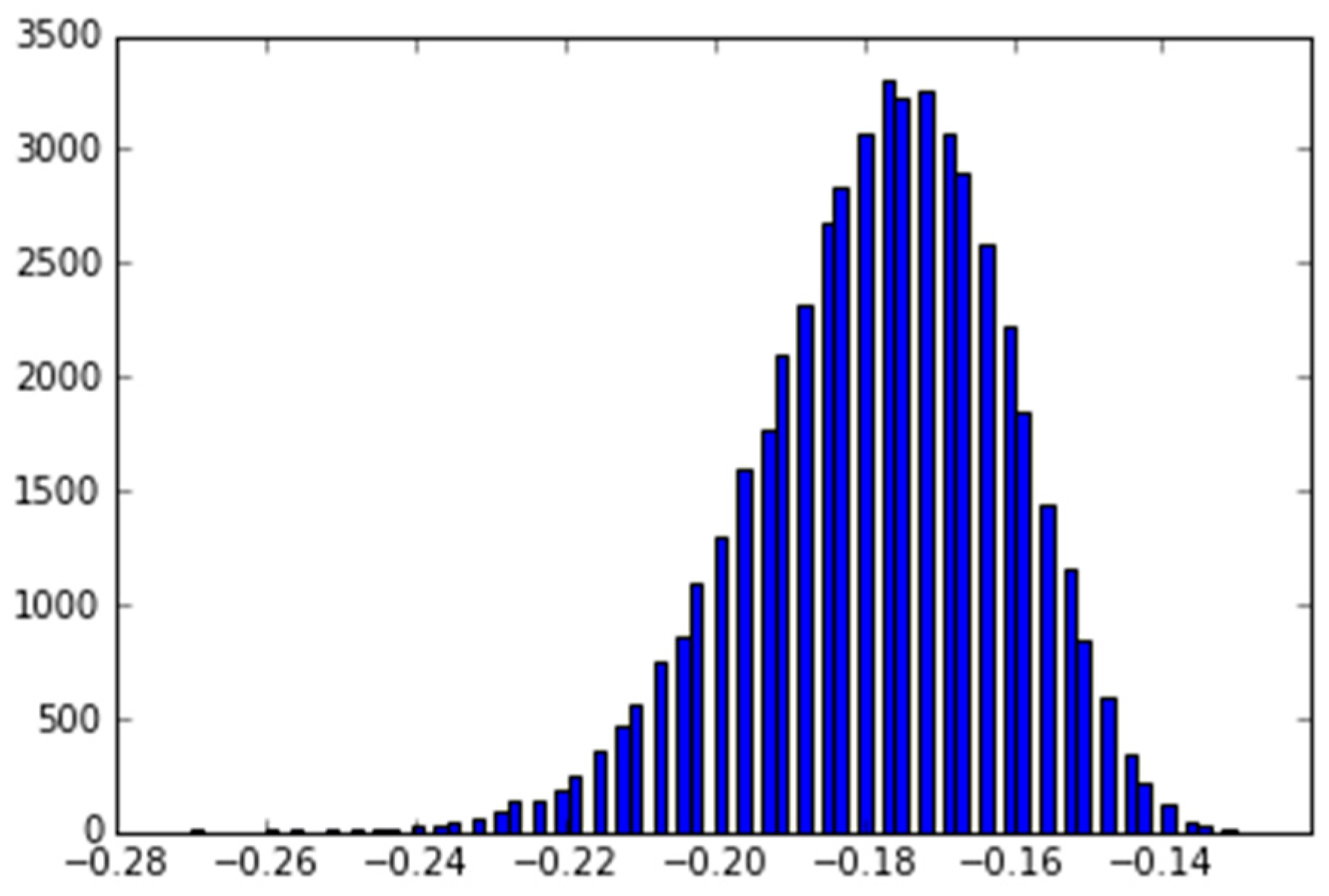
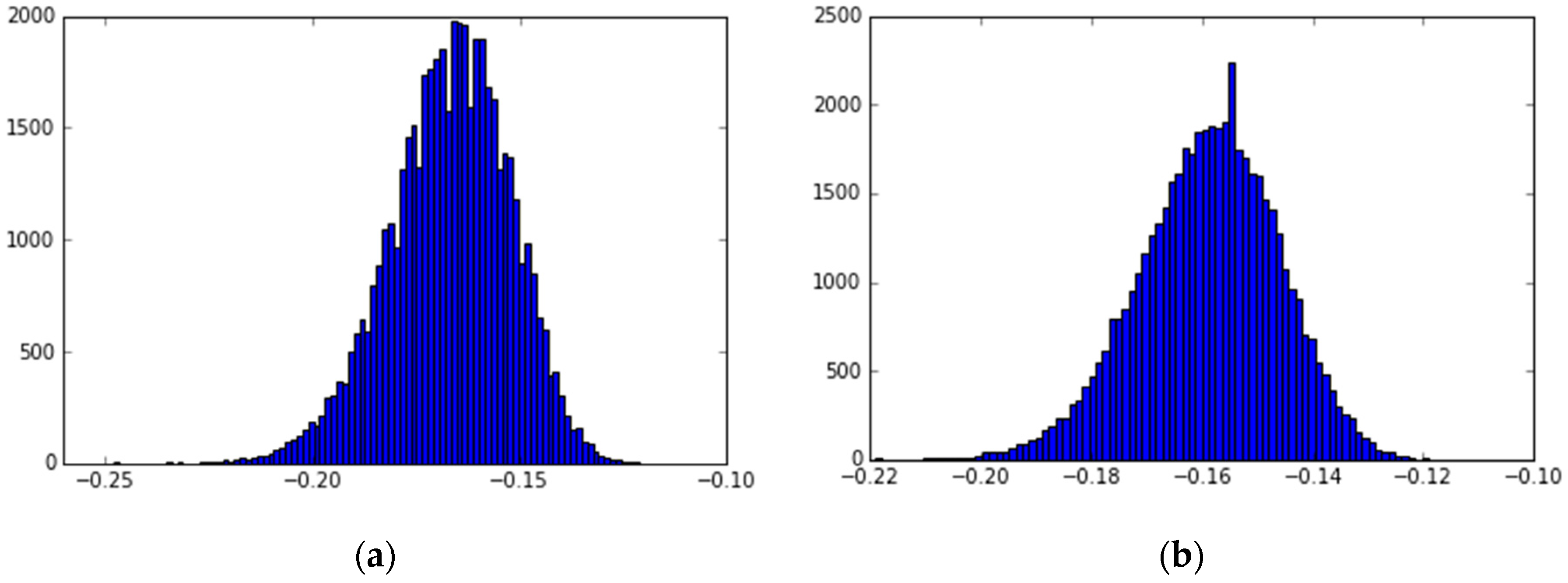
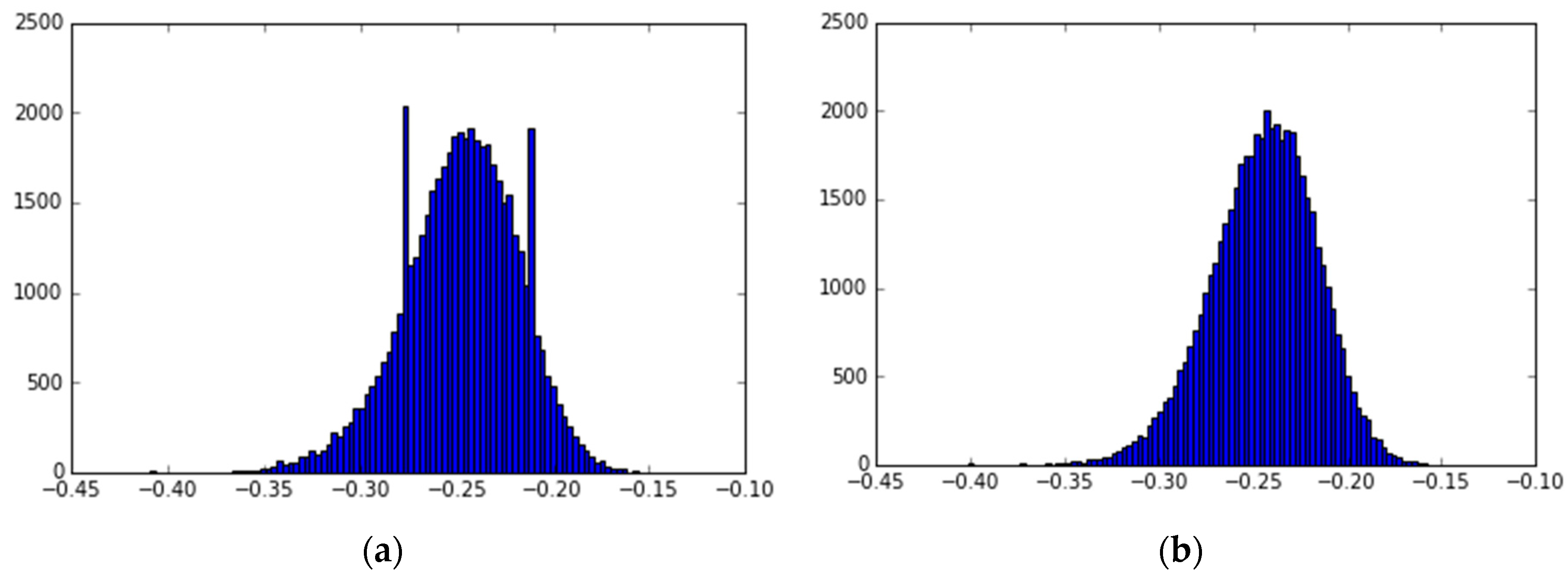
4.1.1. Outlier Customers
- The parameter N is the size of the randomly selected samples with replacement for a chosen number of bootstrapping iterations. It is set depending on the expected number of outliers in the distribution [25].
- The variable k is a trimming factor used to compute mean-trimmed means for each bootstrap sample, which in turn helps make the presence of rare outliers visible in those samples. As we increase k, the Bootlier plot advances to a smoother bell curve, and therefore it must be set to an appropriate value depending upon sample size and type of trimming, as suggested by Singh and Xie [25].
- The iterating factor i is the number of times samples of size N are randomly generated with replacement to compute mean trimmed mean post each iteration. For our results, we use i = 50,000 as a sufficient number of iterations.
4.1.2. B2B Customers
4.1.3. Duplicate Online Activity
- Erroneous data gathering process could result in multiple records of the same action being stored with a small difference in timestamp [15]. In this case, it is essential to drop duplicate actions to maintain data integrity.
- Products that have been bought or added to cart multiple times could be continually recommended because of the large quantity of interactions performed on them (e.g., click, buy) [30]. Dropping duplicates proves to be important here as well, because the recommendation model has led the customer to find only one unique product in his or her exploration. Thus, disregarding such instances is necessary for both model evaluation and training.
4.1.4. Visitors Bounced off the Home or Product Listing Page
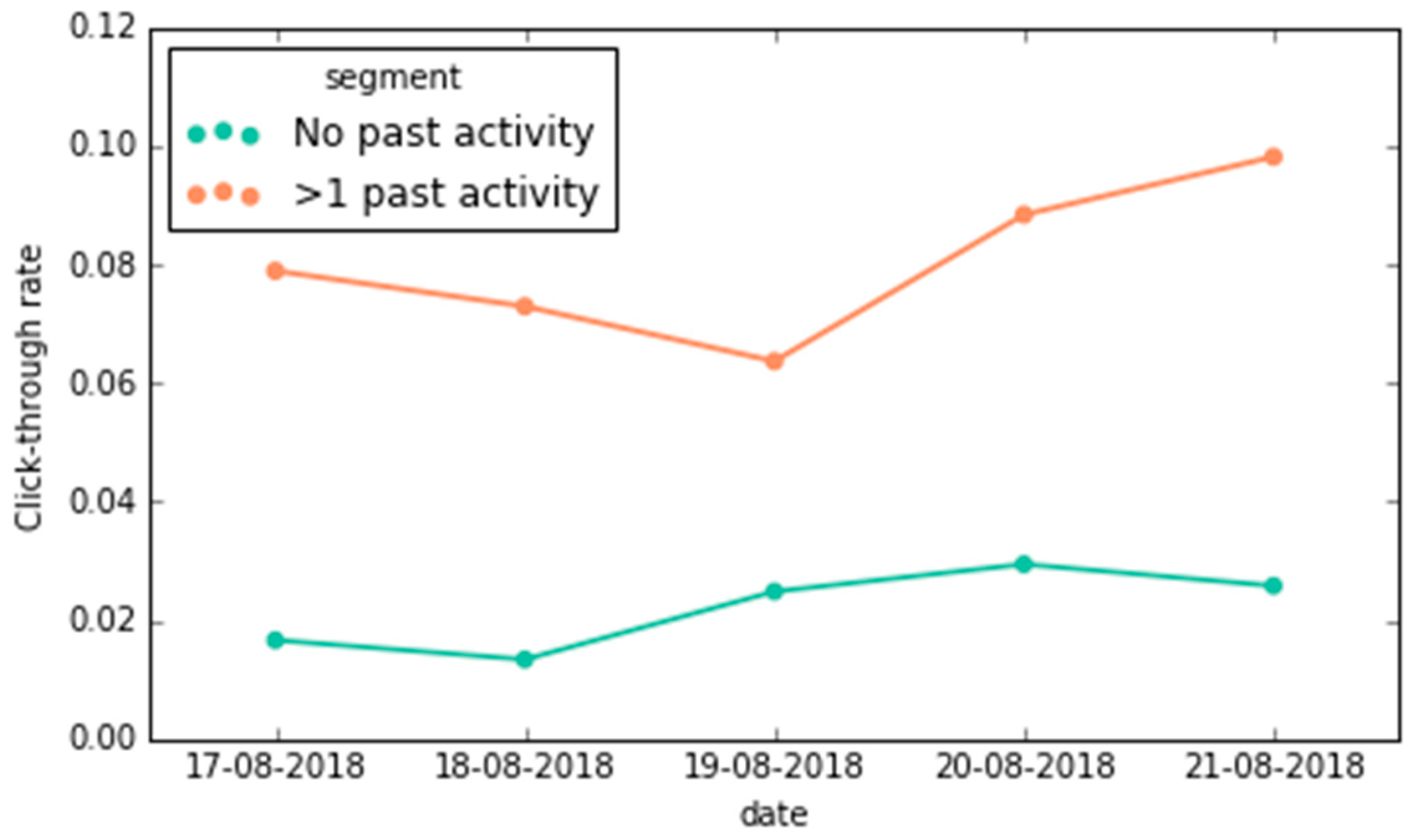
4.1.5. Dealing with Initial Clicks of New Customers on a Website
4.2. Issues Pertaining to Technical or Data Collection Problems
4.2.1. Online Bots and Web Crawlers
- (i)
- Bots leave specific signatures that can be detected in User Agents and known bot IP addresses. Tan and Kumar [8] list some known User Agents and bot IPs, as well as how to detect ethical bots using HEAD requests (type of request that a web server responds to by sending only the message header) and HTTP requests (a request message sent to a web server on page load) with unassigned referrers.
- (ii)
- Bots compared to human users tend to have very high navigation speeds on an e-commerce website or exhibit some sort of recurring behavior, even with moderate speeds.
- (a)
- Therefore, one can compute clicks or ATCs per second, and theoretically, a value close to or greater than 1 can indicate an online bot.
- (b)
- Another technique could be to record and observe recurring patterns in the time difference between two simultaneous clicks or ATCs or effective session durations [24]. Unique users exhibiting such behavior can also be categorized as a bot.
4.2.2. Track a Unique Visitor
- Incognito browsing, clearing of cookies, or use of multiple devices. In either case, a new cookie ID is registered for all following interactions of a customer, thereby disassociating a link to the customer and his past interactions against the older cookie ID. In this case, it would be possible to identify a unique customer through his or her user ID, given the customer has logged in once prior or created an account on the website. However, this cannot be employed on the interactions on a private browsing session when a customer never logged in; hence, this data would, by default, get mapped under a new visitor. Additionally, if a customer were to complete certain transactions under a cookie ID and then log in (thereby registering the user ID to the cookie ID), it is crucial that those pre-login interactions reflected only under the cookie ID are mapped accordingly to the user ID.
- A cookie ID is linked to multiple user IDs. If there are any interactions or hits recorded for a cookie ID with multiple user IDs present across data, then it is possible that multiple individuals are using the same browser on a device. In such cases, it is impossible to identify the true customer behind an action when the customer is not logged in and we advise that such cases should be eliminated.
| Algorithm: |
| Let Data be the dataset containing all hits and interactions |
| Let Map be a unique mapping of all cookie IDs and user IDs created from Data |
| Pseudocode |
| 1. Eliminate entries from Data where both cookie ID and user ID are NULL/Missing |
| 2. Eliminate entries from Data where both user ID is NULL/Missing and the cookie ID in the record has multiple unique user IDs as indicated by Map |
| 3. For each row in Data: |
| Create a field called Cust ID |
| If user ID ≄NULL: |
| b. Cust ID = user ID |
| Else: |
| If cookie ID found in Map: |
| c. Cust ID = user ID in Map cookie ID |
| Else: |
| d. Cust ID = cookie ID |
4.2.3. Error in Capturing Online Activity Data
4.2.4. Uniform Data Management
4.2.5. Dealing with Activity on Combo/Bundle Products
4.3. Issues Associated with the User-Interface of the Website
4.3.1. Visibility of Recommendation Widgets
4.3.2. Design of the PLP
5. Method to Validate Effectiveness of a Recommendation Model
6. Conclusions and Evaluation
7. Limitations
8. Future Work
Supplementary Materials
Author Contributions
Acknowledgments
Conflicts of Interest
Appendix A
Appendix B
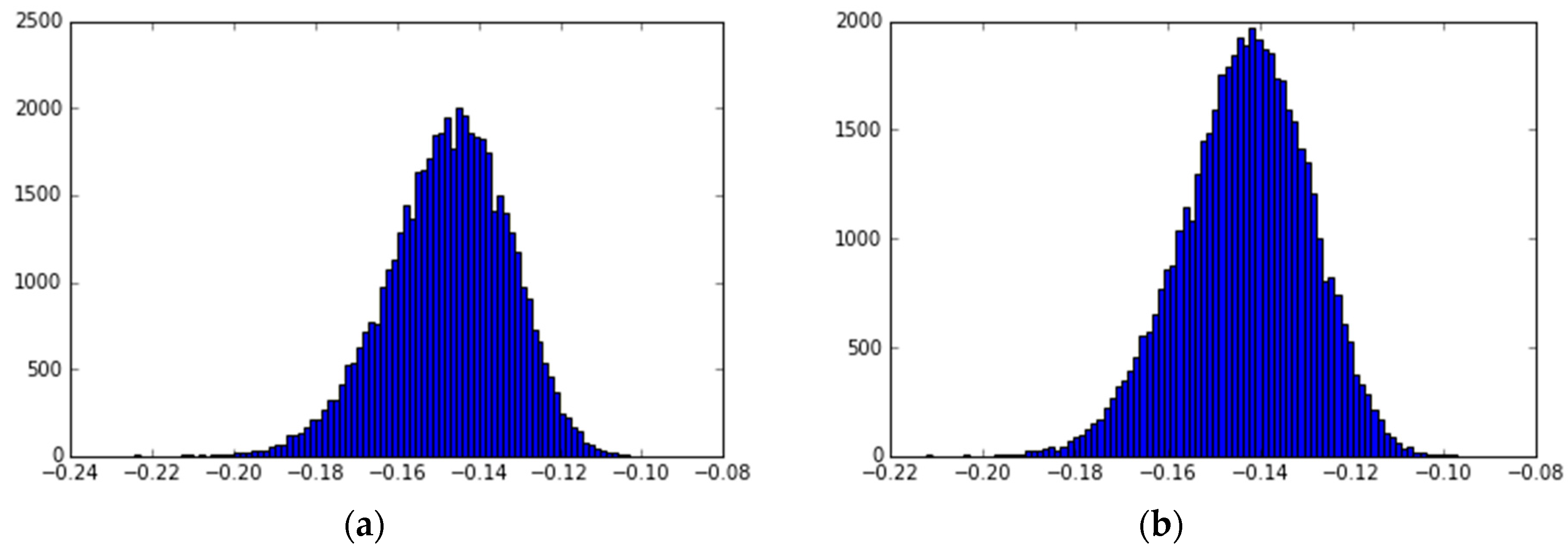
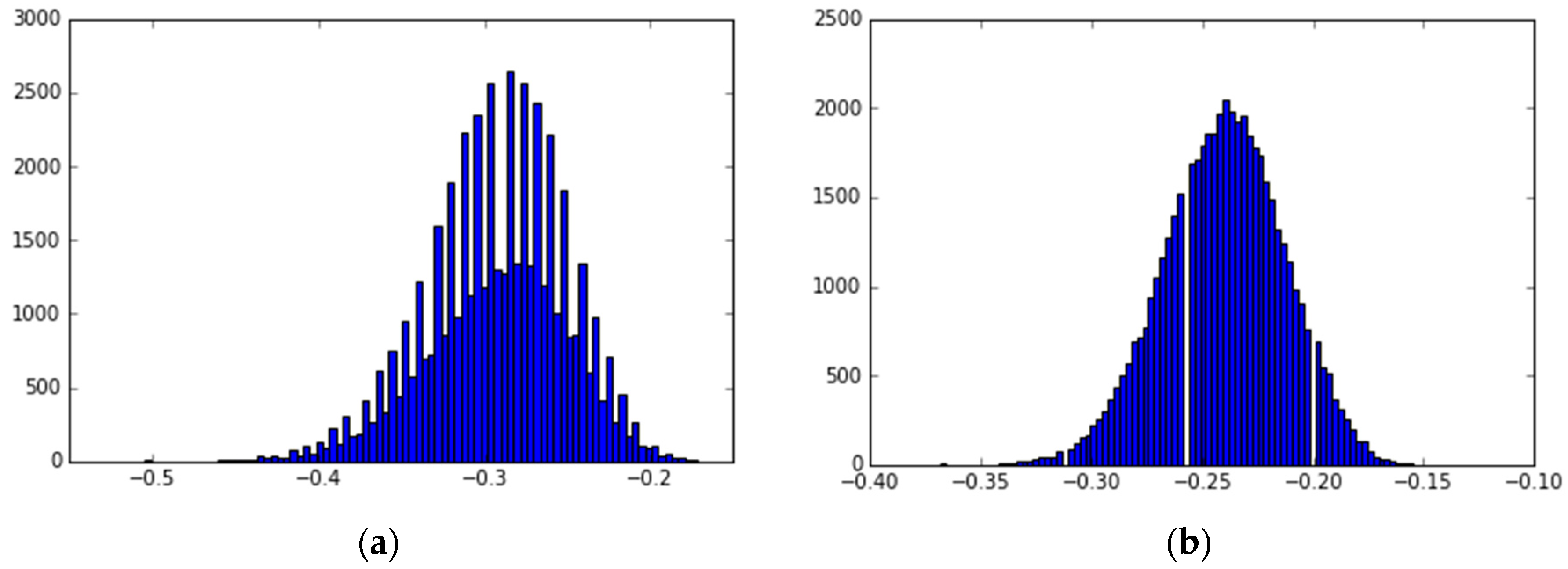
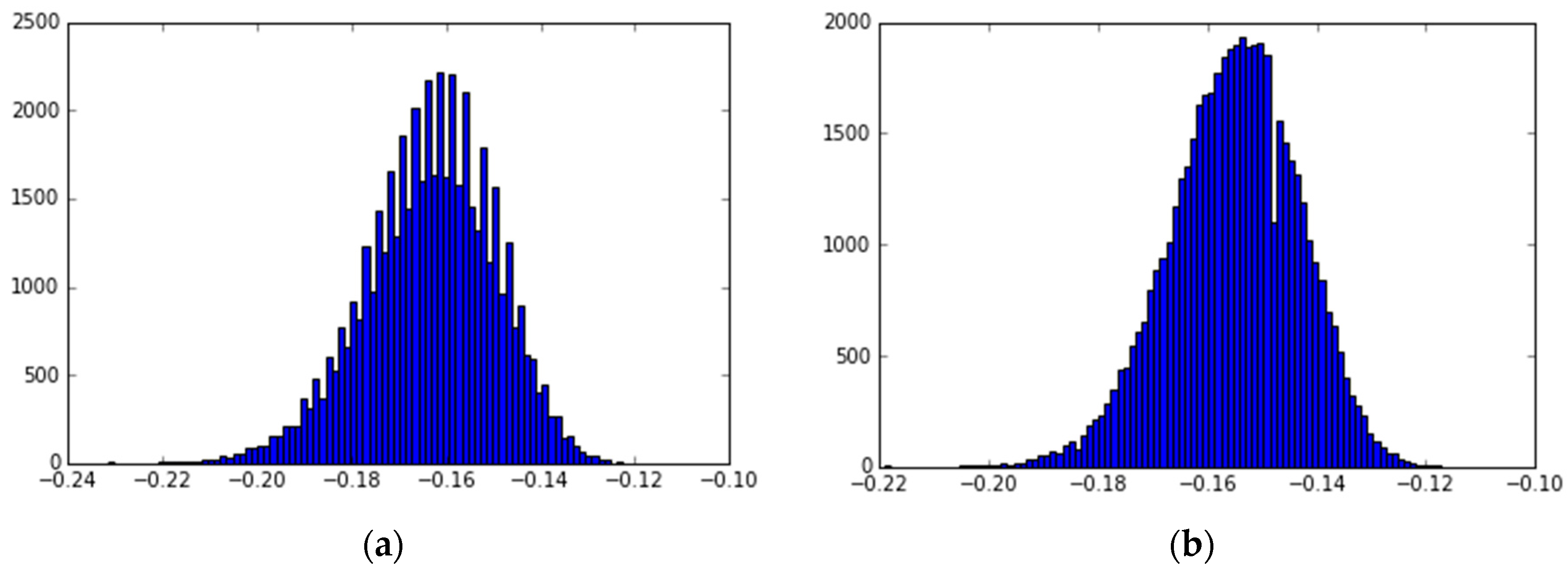
| Cases | Products Type | Total Customers | Time Period | Max Buys/Day by a Customer | Max Views/Day by a Customer |
|---|---|---|---|---|---|
| Case 1 | Fashion clothing and accessories | 29,357 | 10 days | 24 | 460 |
| Case 2 | Traditional Indian wear | 31,767 | 5 days | 20 | 382 |
| Case 3 | Plus-size fashion clothes | 19,111 | 10 days | 13 | 361 |
References
- Konstan, J.A.; Riedl, J. Recommender systems: From algorithms to user experience. User Model. User-Adapt. Interact. 2012, 22, 101–123. [Google Scholar] [CrossRef]
- Pu, P.; Chen, L.; Hu, R. A user-centric evaluation framework for recommender systems. In Proceedings of the Fifth ACM Conference on Recommender Systems (RecSys’11), Chicago, IL, USA, 23–27 October 2011; ACM: New York, NY, USA, 2011; pp. 57–164. [Google Scholar]
- Polatidis, N.; Georgiadis, C. Recommender Systems: The Importance of Personalization in E-Business Environments. Int. J. E-Entrep. Innov. 2013, 4, 32–46. [Google Scholar] [CrossRef]
- Shani, G.; Gunawardana, A. Evaluating Recommendation Systems. In Recommender Systems Handbook; Ricci, F., Rokach, L., Shapira, B., Kantor, P., Eds.; Springer: Boston, MA, USA, 2011. [Google Scholar]
- Herlocker, J.L.; Konstan, J.A.; Terveen, L.G.; Riedl, J.T. Evaluating collaborative filtering recommender systems. ACM Trans. Inf. Syst. 2004, 22, 5–53. [Google Scholar] [CrossRef]
- Adomavicius, G.; Zhang, J. Impact of data characteristics on recommender systems performance. ACM Trans. Manag. Inf. Syst. 2012, 3, 1–17. [Google Scholar] [CrossRef]
- Amatriain, X.; Pujol, J.; Oliver, N. I like it... I like it not: Evaluating user ratings noise in recommender systems. In Proceedings of the 17th International Conference on User Modeling, Adaptation and Personalization (UMAP), Trento, Italy, 22–26 June 2009; pp. 247–258. [Google Scholar]
- Tan, P.N.; Kumar, V. Discovery of Web Robot Sessions Based on Their Navigational Patterns. In Intelligent Technologies for Information Analysis; Springer: Berlin/Heidelberg, Germany, 2004; pp. 193–222. [Google Scholar]
- Kohavi, R.; Parekh, R. Ten Supplementary Analyses to Improve E-commerce Web Sites. In Proceedings of the WebKDD Workshop: Web Mining as a Premise to Effective and Intelligent Web Applications, International Conference on Knowledge Discovery and Data Mining (KDD), Washington, DC, USA, 24–27 August 2003. [Google Scholar]
- Srivastava, J.; Cooley, R.; Deshpande, M.; Tan, P.N. Web Usage Mining: Discovery and Applications of Usage Patterns from Web Data. SIGKDD Explor. 2000, 1, 12–23. [Google Scholar] [CrossRef]
- Kaushik, A. Bounce Rate as Sexiest Web Metric Ever. MarketingProfs, August 2007. Available online: http://www.marketingprofs.com/7/bounce-rate-sexiest-web-metric-ever-kaushik.asp?sp=1 (accessed on 15 January 2019).
- Kaushik, A. Excellent Analytics Tip 11: Measure Effectiveness of Your Web Pages. Occam’s Razor (blog), May 2007. Available online: https://www.kaushik.net/avinash/excellent-analytics-tip-11-measure-effectiveness-of-your-web-pages/ (accessed on 15 January 2019).
- Robinson, B. B2C and B2B Ecommerce: What’s the Difference Anyway? Business.com, February 2017. Available online: https://www.business.com/articles/b2c-and-b2b-ecommerce-whats-the-difference-anyway/ (accessed on 15 January 2019).
- Hellerstein, J.M. Quantitative Data Cleaning for Large Databases, EECS Computer Science Division, UC Berkeley. 2008. Available online: http://db.cs.berkeley.edu/jmh (accessed on 27 February 2008).
- Kohavi, R.; Mason, L.; Parekh, R.; Zheng, Z. Lessons and Challenges from Mining Retail E-Commerce Data. Mach. Learn. 2004, 57, 83–113. [Google Scholar] [CrossRef]
- Campbel, K. How to Track Ecommerce Shoppers Across Devices. Practical Ecommerce (blog), June 2015. Available online: https://www.practicalecommerce.com/How-to-Track-Ecommerce-Shoppers-Across-Devices (accessed on 15 January 2019).
- Kauffman, R.J.; Walden, E.A. Economics and Electronic Commerce: Survey and Directions for Research. Int. J. Electron. Commer. 2001, 5, 5–116. [Google Scholar] [CrossRef]
- Cunliffe, D. Developing usable Web sites ± a review and model. Internet Res. Electron. Netw. Appl. Policy 2000, 10, 295–307. [Google Scholar] [CrossRef]
- Deshmukh, R.; Wangikar, V. Data Cleaning: Current Approaches and Issues. In Proceedings of the Conference: IEEE International Conference on Knowledge Engineering, Aurangabad, India, 8–10 April 2011. [Google Scholar]
- Xu, H.; Li, Z.; Chu, C.; Chen, Y.; Yang, Y.; Lu, H.; Wang, H.; Stavrou, A. Detecting and Characterizing Web Bot Traffic in a Large E-commerce Marketplace. In Proceedings of the 23rd European Symposium on Research in Computer Security, ESORICS 2018, Barcelona, Spain, 3–7 September 2018. [Google Scholar]
- Suchacka, G. Analysis of aggregated bot and human traffic on e-commerce site. In Proceedings of the 2014 Federated Conference on Computer Science and Information Systems, Warsaw, Poland, 7–10 September 2014; pp. 1123–1130. [Google Scholar] [CrossRef]
- Tyagi, N.K.; Solanki, A.K.; Tyagi, S. An Algorithmic Approach to Data Preprocessing in Web Usage Mining. Int. J. Inf. Technol. Knowl. Manag. 2010, 2, 279–283. [Google Scholar]
- Kohavi, R. Mining E-Commerce Data: The Good, the Bad, and the Ugly. In Advances in Knowledge Discovery and Data Mining. PAKDD 2001; Lecture Notes in Computer Science; Springer: Berlin/Heidelberg, Germany, 2001; Volume 2035. [Google Scholar]
- Suchacka, G.; Sobków, M. Detection of Internet robots using a Bayesian approach. In Proceedings of the 2015 IEEE 2nd International Conference on Cybernetics (CYBCONF), Gdynia, Poland, 24–26 June 2015; pp. 365–370. [Google Scholar] [CrossRef]
- Singh, K.; Xie, M. Bootlier-Plot: Bootstrap Based Outlier Detection Plot. Sankhyā: Indian J. Stat. (2003–2007) 2003, 65, 532–559. [Google Scholar]
- Candelon, B.; Metiu, N. A Distribution-Free Test for Outliers (2013). Bundesbank Discussion Paper No. 02/2013. Available online: https://ssrn.com/abstract=2796894 (accessed on 15 January 2019).
- Genson, R. The B2B Ecommerce Trends Report: Millennial Buyers, Payment Options and a Maturing Market. BigCommerce Blog, January 2018. Available online: https://www.bigcommerce.com/blog/b2b-ecommerce-trends/#b2b-customer-acquisition-trends (accessed on 15 January 2019).
- Oro Team. B2C vs B2B Customers: How to Handle the Difference, B2B eCommerce Tips & Trends. OroCommerce Blog, November 2016. Available online: https://oroinc.com/b2b-ecommerce/blog/b2c-vs-b2b-customers-how-handle-difference (accessed on 15 January 2019).
- Bailey, M. 7 Wholescale eCommerce Features You Cannot Overlook. Handshake, December 2018. Available online: https://www.handshake.com/blog/wholesale-ecommerce (accessed on 15 January 2019).
- Beel, J.; Langer, S.; Genzmehr, M.; Nürnberger, A. Persistence in Recommender Systems: Giving the Same Recommendations to the Same Users Multiple Times. In Research and Advanced Technology for Digital Libraries. TPDL 2013; Aalberg, T., Papatheodorou, C., Dobreva, M., Tsakonas, G., Farrugia, C.J., Eds.; Lecture Notes in Computer Science; Springer: Berlin/Heidelberg, Germany, 2013; pp. 386–390. [Google Scholar]
- Hasan, L.; Morris, A.; Probets, S. Using Google Analytics to Evaluate the Usability of E-Commerce Sites. In Human Centered Design. HCD 2009; Kurosu, M., Ed.; Lecture Notes in Computer Science; Springer: Berlin/Heidelberg, Germany, 2009; Volume 5619. [Google Scholar]
- Sculley, D.; Malkin, R.G.; Basu, S.; Bayardo, R.J. Predicting bounce rates in sponsored search advertisements. In Proceedings of the 15th ACM SIGKDD International Conference on Knowledge Discovery and Data Mining, Paris, France, 28 June–1 July 2009; pp. 1325–1334. [Google Scholar] [CrossRef]
- Mikalef, P.; Giannakos, M.N.; Pateli, A.G. Exploring the Business Potential of Social Media: An Utilitarian and Hedonic Motivation Approach. In Proceedings of the Bled eConference, Bled, Slovenia, 17–20 June 2012; p. 21. [Google Scholar]
- Doran, D.; Gokhale, S. Web robot detection techniques: Overview and limitations. Data Min. Knowl. Discov. 2011, 22, 183–210. [Google Scholar] [CrossRef]
- Koshy, J. Web Scraping: Challenges and Roadblocks. Promptcloud, August 2017. Available online: https://www.promptcloud.com/blog/challenges-roadblocks-in-web-scraping (accessed on 15 January 2019).
- Seroussi, Y. The Wonderful World of Recommender Systems. Data Science and Beyond, October 2015. Available online: https://yanirseroussi.com/2015/10/02/the-wonderful-world-of-recommender-systems/ (accessed on 15 January 2019).
- Episerver. A Guide to Intelligent Personalization: Part 2—Personalizing Product and Basket Pages. Available online: https://www.episerver.com/learn/guides/guide-to-intelligent-ecommerce-personalization/personalized-product-recommendations-and-product-pages/ (accessed on 15 January 2019).
- Tackett, J. Online Testing: How to Use A/A Testing to Break through the Noise. Marketing Experiments, June 2014. Available online: https://marketingexperiments.com/a-b-testing/use-variance-testing-break-through-noise (accessed on 15 January 2019).
- A/A Testing. Optimization Glossary. Available online: https://www.optimizely.com/optimization-glossary/aa-testing/ (accessed on 15 January 2019).
| Min | Max | Median | MAD | Outlier-Upper Limit | |
|---|---|---|---|---|---|
| Views per day | 1 | 460 | 1 | 3.22 | 10.5 |
| Buys per day | 1 | 24 | 1 | 1.62 | 5.83 |
© 2019 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Chaudhary, N.; Roy Chowdhury, D. Data Preprocessing for Evaluation of Recommendation Models in E-Commerce. Data 2019, 4, 23. https://doi.org/10.3390/data4010023
Chaudhary N, Roy Chowdhury D. Data Preprocessing for Evaluation of Recommendation Models in E-Commerce. Data. 2019; 4(1):23. https://doi.org/10.3390/data4010023
Chicago/Turabian StyleChaudhary, Namrata, and Drimik Roy Chowdhury. 2019. "Data Preprocessing for Evaluation of Recommendation Models in E-Commerce" Data 4, no. 1: 23. https://doi.org/10.3390/data4010023
APA StyleChaudhary, N., & Roy Chowdhury, D. (2019). Data Preprocessing for Evaluation of Recommendation Models in E-Commerce. Data, 4(1), 23. https://doi.org/10.3390/data4010023





