MalCaps: A Capsule Network Based Model for the Malware Classification
Abstract
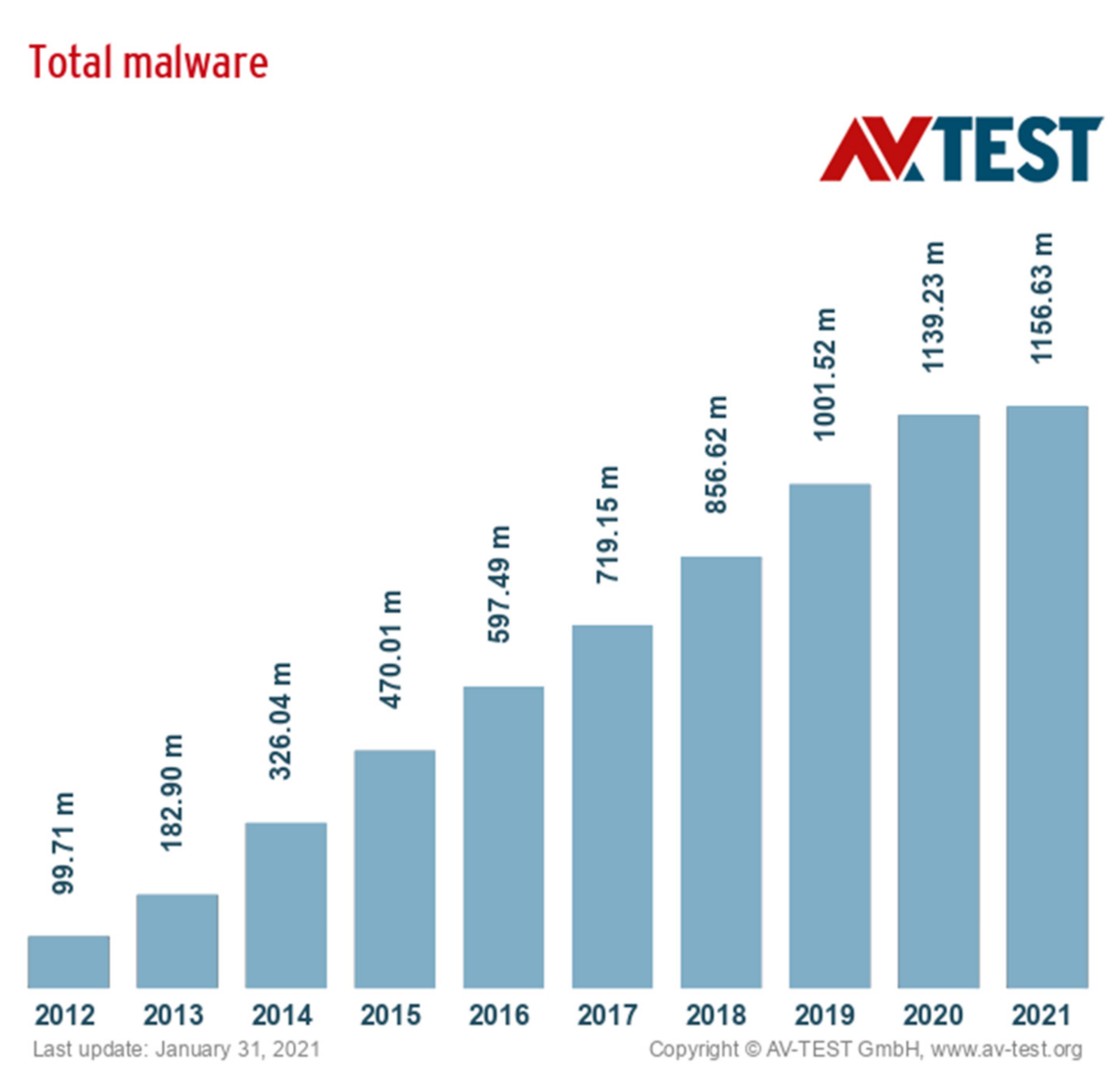
1. Introduction
- Introduce malware image generation technology into the field of malware detection, which can completely store the feature information of malware;
- Propose a new architecture in the domain of malware classification by implementing a novel modified Capsule Neural Network architecture;
- Compare the Capsule Neural Network with convolutional neural network and demonstrates it’s effectiveness in malware detection.
2. Related Work
- traditional malware detection approaches;
- shallow machine learning-based malware detection approaches;
- deep learning-based malware detection approaches.
2.1. Traditional Malware Detection Approaches
2.2. Shallow Machine Learning Based Malware Detection Approaches
2.3. Deep Learning Based Malware Detection Approaches
- the detection rate of traditional static detection algorithm is obviously reduced in the face of code obfuscation, shell, signature, and other camouflage technologies;
- the dynamic detection method has higher requirements on the system resources;
- feature extraction and screening based on machine learning is too complicated;
- the convolutional neural network detection method loses information in the process of feature extraction and has a large demand on the data of training samples.
3. Method Descriptions
3.1. Microsoft Malware Classification Challenge Dataset
3.2. Transforming Malware Byte Files into Images
3.3. Capsule Neural Networks
- , is the input of lower capsule, where n represents the number of capsules, k represents the number of neurons in each capsule (vector length).
- Apply a transformation matrix (or a matrix multiplication, , to the lower layerto the lower layer’s vector which represents important spatial information between low-level and high-level features, p represents the number of neurons in the output capsule, and converts the input into a “prediction vector” :The weighting matrix is learned during the back propagation procedure.
- Then the weighted sum of all the obtained prediction vectors is carried out:where sj is called the total input of higher capsule, cij is the coupling coefficient calculated by dynamic routing, andconceptually, the cij represents the probability distribution of the capsule i activating the capsule j.
- Finally, the output of higher capsule j is obtained by activating a non-linear “squashing” function, it is used to transform short vectors to almost zero length and long vectors close to 1, and the direction of the vector remains the same.
3.4. Our Proposed Capsule Network
4. Experiments
4.1. Evaluation Metrics
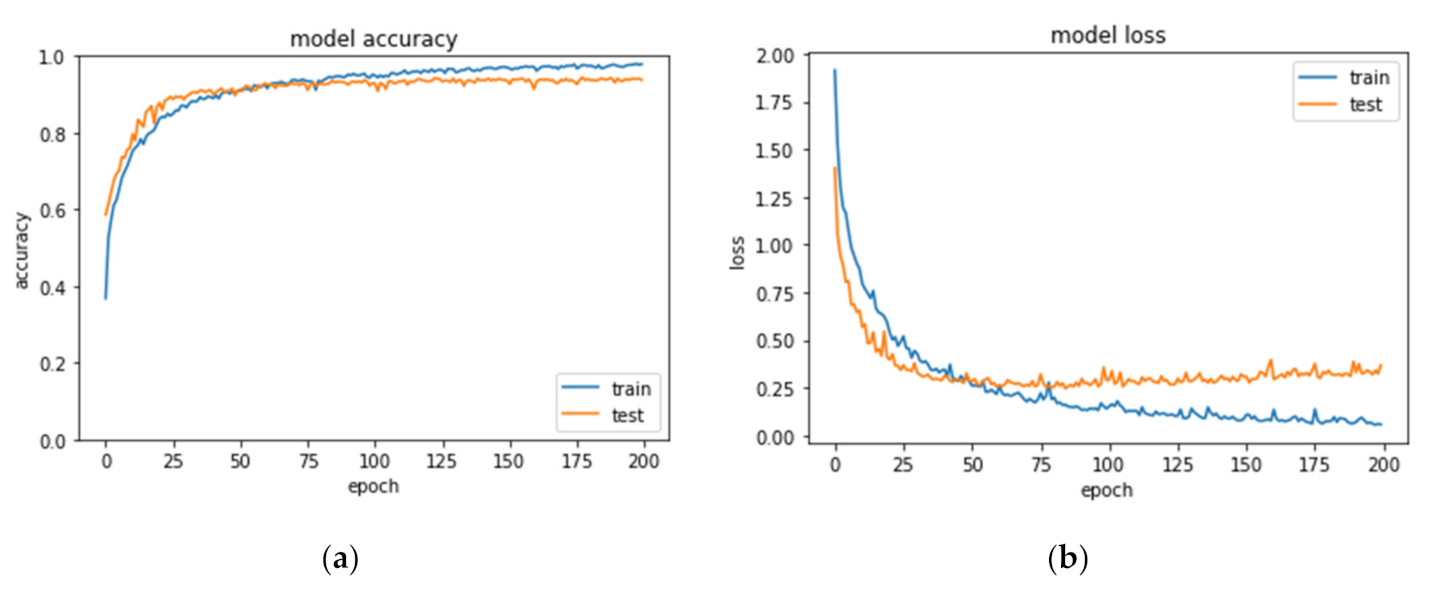
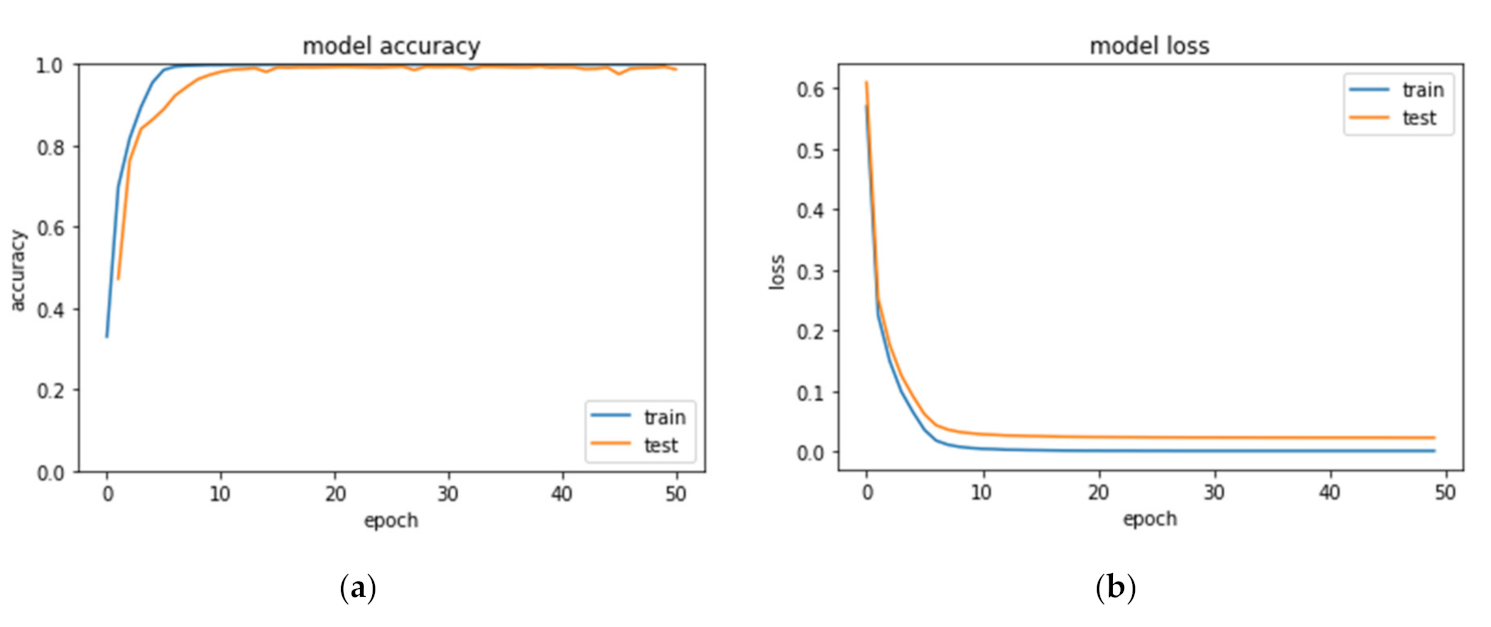
4.2. Results
5. Discussion
6. Conclusions
Author Contributions
Funding
Institutional Review Board Statement
Informed Consent Statement
Data Availability Statement
Conflicts of Interest
References
- Liu, L.; Wang, B.-S.; Yu, B.; Zhong, Q.-X. Automatic malware classification and new malware detection using machine learning. Front. Inf. Technol. Electron. Eng. 2017, 18, 1336–1347. [Google Scholar] [CrossRef]
- Available online: https://www.av-test.org/en/statistics/malware/ (accessed on 6 April 2021).
- National Computer Network Emergency Response Technical Team/Coordination Center of China. 2019 China Internet Cybersecurity Report. Available online: http://www.cac.gov.cn/2020-08/11/c_1598702053181221.htm (accessed on 6 April 2021).
- Denkins, P.; LeGrand, S. A model for the protection of reusable software. ACM SIGSAC Rev. 1991, 9, 3–18. [Google Scholar] [CrossRef]
- Weiping, W. Researeh on Mechanism and Defense of Malicious Code. Ph.D. Thesis, The Chinese Academy of Science, Guangzhou, China, 2005. [Google Scholar]
- Kolosnjaji, B.; Zarras, A.; Webster, G.; Eckert, C. Deep Learning for Classification of Malware System Call Sequences; Springer: Cham, Switzerland, 2016. [Google Scholar]
- Sabour, S.; Frosst, N.; Hinton, G.E. Dynamic Routing Between Capsules. Adv. Neur. 2017, 30. [Google Scholar]
- Caviglione, L.; Choras, M.; Corona, I.; Janicki, A.; Mazurczyk, W.; Pawlicki, M.; Wasielewska, K. Tight Arms Race: Overview of Current Malware Threats and Trends in Their Detection. IEEE Access 2021, 9, 5371–5396. [Google Scholar] [CrossRef]
- Griffin, K.; Schneider, S.; Hu, X.; Chiueh, T.C. Automatic Generation of String Signatures for Malware Detection. In Recent Advances in Intrusion Detection, Proceedings; Kirda, E., Jha, S., Balzarotti, D., Eds.; Springer: Berlin, German, 2009; pp. 101–120. [Google Scholar]
- Rafique, M.Z.; Caballero, J. FIRMA: Malware Clustering and Network Signature Generation with Mixed Network Behaviors. In Research in Attacks, Intrusions, and Defenses; Stolfo, S.J., Stavrou, A., Wright, C.V., Eds.; Springer: Berlin, German, 2013; pp. 144–163. [Google Scholar]
- Aslan, O.; Samet, R. A Comprehensive Review on Malware Detection Approaches. IEEE Access 2020, 8, 6249–6271. [Google Scholar] [CrossRef]
- Jamalpur, Y.S.N.S.; Raja, P.; Tagore, G.; Rao, G.R.K. Dynamic Malware Analysis Using Cuckoo Sandbox. In Proceedings of the 2018 Second International Conference on Inventive Communication and Computational Technologies (ICICCT), Coimbatore, India, 20–21 April 2018. [Google Scholar]
- Willems, G.H.; Holz, T.; Freiling, F. Toward automated dynamic malware analysis using cwsandbox. IEEE Secur. Priv. 2007, 5, 32–39. [Google Scholar] [CrossRef]
- Dinaburg, A.; Paul, R.; Shari, M.; Lee, W. Ether: Malware analysis via hardware virtualization extensions. In Proceedings of the 15th ACM Conference on Computer and Communications Security, Alexandria, VA, USA, 27–31 October 2008. [Google Scholar]
- Kozachok, A.V.; Kozachok, V.I. Construction and evaluation of the new heuristic malware detection mechanism based on executable files static analysis. J. Comput. Virol. Hacking Tech. 2017. [Google Scholar] [CrossRef]
- Alkhateeb, E.M.; Stamp, M. A Dynamic Heuristic Method for Detecting Packed Malware Using Naive Bayes. IEEE 2019, 2019, 1–6. [Google Scholar]
- Merlo, A.; Migliardi, M.; Caviglione, L. A survey on energy-aware security mechanisms. Pervasive Mob. Comput. 2015, 24, 77–90. [Google Scholar] [CrossRef]
- Fatima, A.; Maurya, R.; Dutta, M.K.; Burget, R.; Masek, J. Android Malware Detection Using Genetic Algorithm based Optimized Feature Selection and Machine Learning. IEEE 2019, 2019, 220–223. [Google Scholar]
- Abawajy, J.H.; Kelarev, A. Iterative Classifier Fusion System for the Detection of Android Malware. IEEE Trans. Big Data 2019, 5, 282–292. [Google Scholar] [CrossRef]
- Rais, H.M.; Mehmood, T. Dynamic Ant Colony System with Three Level Update Feature Selection for Intrusion Detection. Int. J. Netw. Secur. 2018, 20, 184–192. [Google Scholar]
- Ren, Z.; Wu, H.; Ning, Q.; Hussain, I.; Chen, B. End-to-end malware detection for android IoT devices using deep learning. Ad Hoc Netw. 2020, 101, 102098. [Google Scholar] [CrossRef]
- Cesare, S.; Xiang, Y.; Zhou, W. Control Flow-Based Malware VariantDetection. IEEE Trans. Dependable Secur. Comput. 2014, 11, 307–317. [Google Scholar] [CrossRef]
- Bai, L.; Pang, J.; Zhang, Y.; Fu, W.; Zhu, J. Detecting Malicious Behavior Using Critical API-Calling Graph Matching. In Proceedings of the 2009 First International Conference on Information Science and Engineering, Nanjing, China, 26–28 December 2009. [Google Scholar]
- Santos, I.; Devesa, J.; Brezo, F.; Nieves, J.; Bringas, P.G. OPEM: A Static-Dynamic Approach for Machine-Learning-Based Malware Detection. In Proceedings of the International Joint Conference CISIS’12-ICEUTE’ 12-SOCO’ 12 Special Sessions, Ostrava, Czech Republic, 5–8 September 2012. [Google Scholar]
- Hughes, K.; Qu, Y. A Theoretical Model: Using Logistic Regression for Malware Signature Based Detection. 2012. Available online: https://www.researchgate.net/publication/271020436_A_Theoretical_Model_Using_Logistic_Regression_for_Malware_Signature_based_Detection (accessed on 6 April 2021).
- Islam, R.; Tian, R.H.; Batten, L.M.; Versteeg, S. Classification of malware based on integrated static and dynamic features. J. Netw. Comput. Appl. 2013, 36, 646–656. [Google Scholar] [CrossRef]
- Kilgallon, S.; De La Rosa, L.; Cavazos, J. Improving the Effectiveness and Efficiency of Dynamic Malware Analysis with Machine Learning. IEEE 2017, 2017, 30–36. [Google Scholar]
- Kozachok, A.V.; Bochkov, M.V.; Kochetkov, E.V. Heuristic Malware Detection Mechanism Based on Executable Files Static Analysis. In Proceedings of the 3rd International Conference Information Technology and Nanotechnology 2017, Samara, Russia, 24–27 April 2017. [Google Scholar]
- Morales-Molina, C.D.; Santamaria-Guerrero, D.; Sanchez-Perez, G.; Perez-Meana, H.; Hernandez-Suarez, A. Methodology for Malware Classification Using a Random Forest Classifier. In Proceedings of the 2018 IEEE International Autumn Meeting on Power, Electronics and Computing (ROPEC), Ixtapa, Mexico, 14–16 November 2018. [Google Scholar]
- Mohanasruthi, V.; Chakraborty, A.; Thanudas, B.; Sreelal, S.; Manoj, B.S. An Efficient Malware Detection Technique Using Complex Network-Based Approach. In Proceedings of the 2020 National Conference on Communications (NCC), Kharagpur, India, 21–23 February 2020. [Google Scholar]
- Farrokhmanesh, M.; Hamzeh, A. Music classification as a new approach for malware detection. J. Comput. Virol. Hacking Tech. 2018, 15, 77–96. [Google Scholar] [CrossRef]
- Krizhevsky, A.; Sutskever, I.; Hinton, G.E. ImageNet classification with deep convolutional neural networks. In Proceedings of the 26th Annual Conference on Neural Information Processing Systems 2012, NIPS 2012, Lake Tahoe, NV, USA, 3–6 December 2012. [Google Scholar]
- Nataraj, L.; Karthikeyan, S.; Jacob, G.; Manjunath, B.S. Malware Images: Visualization and Automatic Classification; Association for Computing Machinery: New York, NY, USA, 2011; pp. 1–7. [Google Scholar]
- Sun, G.; Qian, Q. Deep Learning and Visualization for Identifying Malware Families. IEEE Trans. Dependable Secur. Comput. 2021, 18, 283–295. [Google Scholar] [CrossRef]
- Yue, S. Imbalanced Malware Images Classification: A CNN Based Approach; University of Wisconsin: Madison, WI, USA, 2017. [Google Scholar]
- Rezende, E.; Ruppert, G.; Carvalho, T.; Ramos, F.; de Geus, P. Malicious Software Classification Using Transfer Learning of ResNet-50 Deep Neural Network. In Proceedings of the 2017 16th IEEE International Conference on Machine Learning and Applications (ICMLA), Cancun, Mexico, 18–21 December 2017. [Google Scholar]
- Li, W.; Zhang, R.; Wen, Q. A Malicious Code Variants Detection Method Based on Self-attention. In Proceedings of the 2020 6th International Conference on Computer and Technology Applications, Antalya, Turkey, 14–16 April 2020. [Google Scholar]
- Priyadarsini, K.; Mishra, N.; Prasad, M.; Gupta, V.; Khasim, S. Detection of malware on the internet of things and its applications depends on long short-term memory network. J. Ambient Intell. Humaniz. Comput. 2021, 1, 1–12. [Google Scholar]
- Nisa, M.; Shah, J.H.; Kanwal, S.; Raza, M.; Khan, M.A.; Damaševičius, R.; Blažauskas, T. Hybrid Malware Classification Method Using Segmentation-Based Fractal Texture Analysis and Deep Convolution Neural Network Features. Appl. Sci. 2020, 10, 4966. [Google Scholar] [CrossRef]
- Damaševičius, R.; Venčkauskas, A.; Toldinas, J.; Grigaliūnas, Š. Ensemble-Based Classification Using Neural Networks and Machine Learning Models for Windows PE Malware Detection. Electronics 2021, 10, 485. [Google Scholar] [CrossRef]
- Sezer, A.; Sezer, H.B. Capsule network-based classification of rotator cuff pathologies from MRI. Comput. Electr. Eng. 2019, 80, 106480. [Google Scholar] [CrossRef]
- Hinton, G.; Sabour, S.; Frosst, N. Matrix capsules with em routing. In Proceedings of the ICLR 2018, Vancouver, BC, Canada, 30 April–3 May 2018. [Google Scholar]
- Yang, M.; Zhao, W.; Chen, L.; Qu, Q.; Zhao, Z.; Shen, Y. Investigating the transferring capability of capsule networks for text classification. Neural. Netw. 2019, 118, 247–261. [Google Scholar] [CrossRef] [PubMed]
- Qiao, K.; Zhang, C.; Wang, L.; Chen, J.; Zeng, L.; Tong, L.; Yan, B. Accurate Reconstruction of Image Stimuli from Human Functional Magnetic Resonance Imaging Based on the Decoding Model With Capsule Network Architecture. Front. Neurosci. 2018, 12, 62. [Google Scholar] [CrossRef]
- Afshar, P.; Plataniotis, K.N.; Mohammadi, A. Capsule Networks’ Interpretability for Brain Tumor Classification Via Radiomics Analyses. In Proceedings of the 2019 IEEE International Conference on Image Processing, Taipei, Taiwan, 22–25 September 2019; pp. 3816–3820. [Google Scholar]
- Jaiswal, A.; AbdAlmageed, W.; Wu, Y.; Natarajan, P. CapsuleGAN: Generative Adversarial Capsule Network. In Computer Vision-Eccv 2018 Workshops, Pt Iii’; Leal-Taixé, L., Roth, S., Eds.; Springer International Publishing Ag: Marina del Rey, CA, USA, 2019; pp. 526–535. [Google Scholar]
- Andersen, P.A. Deep Reinforcement Learning Using Capsules in Advanced Game Environments; University of Agder: Grimstad, Norway, 2018. [Google Scholar]
- Çayır, A.; Ünal, U.; Dağ, H. Random CapsNet forest model for imbalanced malware type classification task. Comput. Secur. 2021, 102, 102133. [Google Scholar] [CrossRef]
- Wang, S.W.; Zhou, G.; Lu, J.C.; Zhang, F.J. A Novel Malware Detection and Classification Method Based on Capsule Network (China State Key Laboratory of Mathematical Engineering and Advanced Computer Zhengzhou 450001 China). Artif. Intell. Secur. 2019, 573–584. [Google Scholar]
- Phaye, S.; Sikka, A.; Dhall, A.; Bathula, D. Dense and Diverse Capsule Networks: Making the Capsules Learn Better; Indian Institute of Technology: Ropar, Punjab, India, 2018. [Google Scholar]
- Ronen, R.; Radu, M.; Feuerstein, C.; Yom-Tov, E. Microsoft Malware Classification Challenge; Researchgate: Berlin, Germany, 2018. [Google Scholar]
- Zhao, Y.T.; Cui, W.J.; Geng, S.N.; Bo, B.; Feng, Y.X.; Zhang, W.B. A Malware Detection Method of Code Texture Visualization Based on an Improved Faster RCNN Combining Transfer Learning. IEEE Access 2020, 8, 166630–166641. [Google Scholar] [CrossRef]
- Foster, D.J. Artificial Intelligence in Cybersecurity: A Novel Deep Learning Architecture for Image-Based; University of London: London, UK, 2020. [Google Scholar]
- Guo, X. A Keras Implementation of CapsNet. Available online: https://github.com/XifengGuo/CapsNet-Keras/tree/tf2.2 (accessed on 6 April 2021).
- Ahmadi, M.; Ulyanov, D.; Semenov, S.; Trofimov, M.; Giacinto, G. Novel Feature Extraction, Selection and Fusion for Effective Malware Family Classification. In Proceedings of the Sixth ACM Conference on Data and Application Security and Privacy, New York, NY, USA, 9–11 March 2016. [Google Scholar]
- Narayanan, B.N.; Djaneye-Boundjou, O.; Kebede, T.M. Performance Analysis of Machine Learning and Pattern Recognition Algorithms for Malware Classification; IEEE: New York, NY, USA, 2016; pp. 338–342. [Google Scholar]
- Fu, J.; Xue, J.; Wang, Y.; Liu, Z.; Shan, C. Malware Visualization for Fine-Grained Classification. IEEE Access 2018, 6, 14510–14523. [Google Scholar] [CrossRef]
- Cui, Z.; Xue, F.; Cai, X.; Cao, Y.; Wang, G.G.; Chen, J. Detection of Malicious Code Variants Based on Deep Learning. IEEE Trans. Ind. Inform. 2018, 14, 3187–3196. [Google Scholar] [CrossRef]
- Gibert, D.; Mateu, C.; Planes, J.; Vicens, R. Using convolutional neural networks for classification of malware represented as images. J. Comput. Virol. Hacking Tech. 2019, 15, 15–28. [Google Scholar] [CrossRef]
- Narayanan, B.N.; Davuluru, V.S.P. Ensemble Malware Classification System Using Deep Neural Networks. Electronics 2020, 9, 721. [Google Scholar] [CrossRef]
- Roseline, S.A.; Geetha, S.; Kadry, S.; Nam, Y. Intelligent Vision-Based Malware Detection and Classification Using Deep Random Forest Paradigm. IEEE Access 2020, 8, 206303–206324. [Google Scholar] [CrossRef]






| Class No. | Family Name | Train Samples | Malware Type |
|---|---|---|---|
| 0 | Gatak | 1013 | Backdoor |
| 1 | Kelihos_ver1 | 398 | Backdoor |
| 2 | Kelihos_ver3 | 2942 | Backdoor |
| 3 | Lollipop | 2478 | Adware |
| 4 | Obfuscator.ACY | 1228 | Any kind of obfuscated malware |
| 5 | Ramnit | 1541 | Worm |
| 6 | Simda | 42 | Backdoor |
| 7 | Tracur | 751 | TrojanDownloader |
| 8 | Vundo | 475 | Trojan |
| Class No. | Precision | Recall | Accuracy | F1 |
|---|---|---|---|---|
| 0 | 0.7866 | 0.9307 | 0.9701 | 0.8526 |
| 1 | 0.9888 | 0.9167 | 0.9959 | 0.9514 |
| 2 | 0.9847 | 0.9949 | 0.9945 | 0.9898 |
| 3 | 0.9835 | 0.9246 | 0.9784 | 0.9531 |
| 4 | 0.9174 | 0.8889 | 0.9802 | 0.9029 |
| 5 | 0.9241 | 0.8933 | 0.9752 | 0.9085 |
| 6 | 0.6667 | 0.2857 | 0.9972 | 0.4000 |
| 7 | 0.8561 | 0.8500 | 0.9811 | 0.8530 |
| 8 | 0.8264 | 0.9615 | 0.9885 | 0.8889 |
| neurons1 | neurons2 | epochs | batch_size | Accuracy |
|---|---|---|---|---|
| 25 | 100 | 200 | 1000 | 0.9436 |
| 100 | 25 | 200 | 1000 | 0.9655 |
| 20 | 50 | 150 | 200 | 0.9592 |
| 20 | 25 | 200 | 100 | 0.9770 |
| 20 | 10 | 100 | 20 | 0.9764 |
| 100 | 30 | 50 | 500 | 0.9776 |
| 25 | 10 | 100 | 50 | 0.9839 |
| 5 | 100 | 100 | 20 | 0.9850 |
| 100 | 20 | 200 | 500 | 0.9799 |
| 5 | 5 | 100 | 50 | 0.9903 |
| Class No. | Precision | Recall | Accuracy | F1 |
|---|---|---|---|---|
| 0 | 0.8263 | 0.9653 | 0.9779 | 0.8904 |
| 1 | 0.9889 | 0.9271 | 0.9963 | 0.9570 |
| 2 | 0.9949 | 0.9966 | 0.9977 | 0.9957 |
| 3 | 0.9743 | 0.9516 | 0.9825 | 0.9628 |
| 4 | 0.9657 | 0.8756 | 0.9839 | 0.9184 |
| 5 | 0.9331 | 0.9300 | 0.9811 | 0.9316 |
| 6 | 1.0000 | 0.5714 | 0.9986 | 0.7273 |
| 7 | 0.8897 | 0.8643 | 0.9844 | 0.8768 |
| 8 | 0.8707 | 0.9712 | 0.9917 | 0.9182 |
| Approach | Feature Type | Classification Algorithm | Accuracy | F1 |
|---|---|---|---|---|
| Ahmadi et al.,2016 [55] | Haralick features | XGBoost | 0.9690 | 0.9282 |
| Ahmadi et al.,2016 [55] | Local Binary Pattern features | XGBoost | 0.9724 | 0.9530 |
| Narayanan et al., 2016 [56] | PCA features | 1-NN | 0.9660 | 0.9102 |
| Fu, 2018 [57] | Gray-image | KNN-3 | 0.931 | 0.920 |
| Cui, 2018 [58] | Gray-image | OtherCNN | 0.945 | 0.945 |
| Gibert et al., 2019 [59] | 128 × 128 Grayscale Image | CNN | 0.9750 | 0.9400 |
| Narayanan et al., 2020 [60] | Grayscale Image and Opcodes | Ensemble Approach using SVM | 0.9980 | - |
| Çayır et al., 2020 [48] | Images from BYTE and ASM | RCNF Ensemble Model | 0.9872 | 0.9661 |
| Roseline et al., 2020 [61] | Grayscale Image | Deep Forest Model | 0.9720 | 0.9720 |
| MalCaps | Three channel Image | Capsule Neural Network | 0.9934 | 0.9443 |
Publisher’s Note: MDPI stays neutral with regard to jurisdictional claims in published maps and institutional affiliations. |
© 2021 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).
Share and Cite
Zhang, X.; Wu, K.; Chen, Z.; Zhang, C. MalCaps: A Capsule Network Based Model for the Malware Classification. Processes 2021, 9, 929. https://doi.org/10.3390/pr9060929
Zhang X, Wu K, Chen Z, Zhang C. MalCaps: A Capsule Network Based Model for the Malware Classification. Processes. 2021; 9(6):929. https://doi.org/10.3390/pr9060929
Chicago/Turabian StyleZhang, Xiaoliang, Kehe Wu, Zuge Chen, and Chenyi Zhang. 2021. "MalCaps: A Capsule Network Based Model for the Malware Classification" Processes 9, no. 6: 929. https://doi.org/10.3390/pr9060929
APA StyleZhang, X., Wu, K., Chen, Z., & Zhang, C. (2021). MalCaps: A Capsule Network Based Model for the Malware Classification. Processes, 9(6), 929. https://doi.org/10.3390/pr9060929






