Privacy-Preserving Authentication Protocol for Wireless Body Area Networks in Healthcare Applications
Abstract
:1. Introduction
2. Preliminaries
2.1. System Configuration
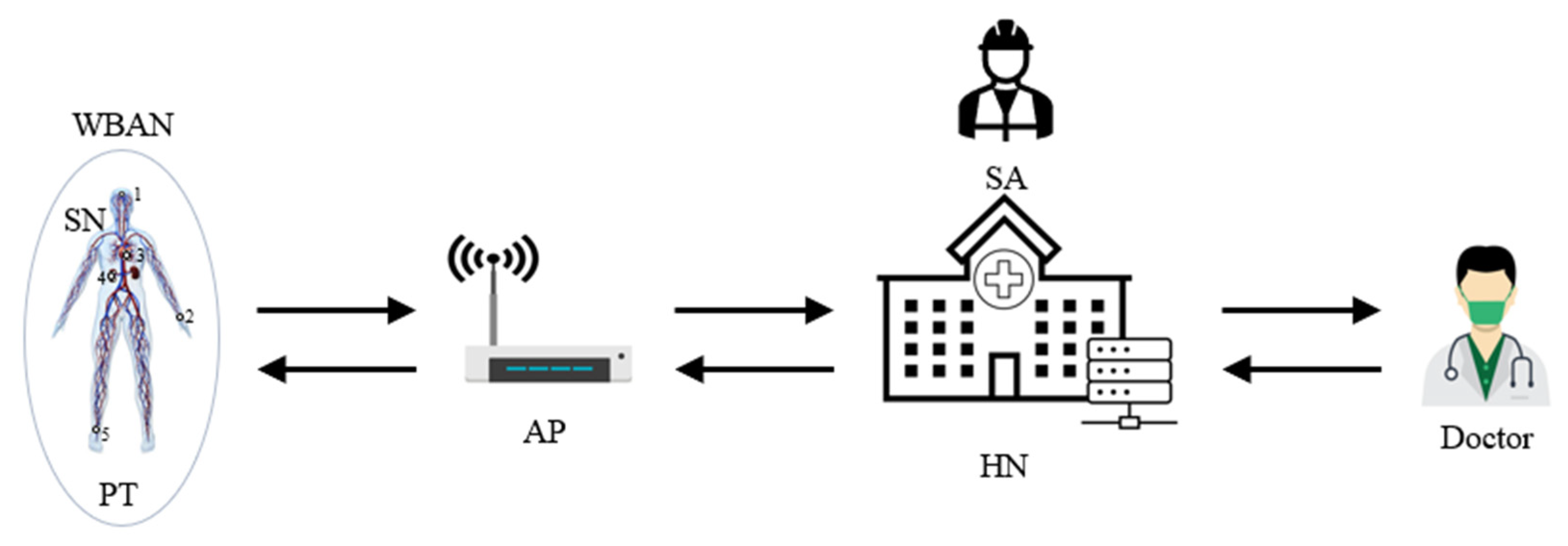
- SA: It sets up system parameters and registers participants by deploying important secret values in the memory of each party.
- HN: It has a very important role as the central server for the healthcare service, which collects and keeps a database of electronic health records (EHRs) for the registered PTs. In addition to this, it works also as a registration center for all network participants and issues SNs and APs for PTs. Furthermore, it works as an authentication server to check the authenticity of system entities.
- AP: AP works as a communication gateway from SN to HN and vice versa via wireless communication link. Thereby, it does not perform any validation of messages. It is assumed that an AP belongs to a specific PT only.
- SN: Some SNs are deployed on a PT, as notated as 1, 2, 3, 4 and 5 in the left part of Figure 1, to form a WBAN by HN or SA, which do the role of collecting EHR data of the PT and transmitting them to HN. An SN has sensors to check the purposed health status such as body temperature, blood pressure, electrocardiogram and so on. It needs to consider EHR privacy because the healthcare service is data sensitive.
- PT: PT is a subject of the remote healthcare service. Normally, PT does not take part in the network communication directly but subscribes the service to SA or HN. Then, SA or HN issues some SNs and an AP of the PT for the service.
- Doctor: Doctors make the diagnosis based on PT’s EHRs by accessing HN. Doctors need to regularly check the health status of PTs and provide proper medical treatments via on-line.
2.2. CK Threat Model
2.3. Design Goals
3. Proposed Authentication Protocol
3.1. Initialization Phase
- Step 1. SA selects a long-term master key KSHN for HN.
- Step 2. SA stores KSHN in the memory of HN.
3.2. Registration Phase
- Step 1.
- PT chooses two identities IDSN and IDAP for SN and AP, respectively, and sends them to HN. After receiving the information, HN generates four random numbers aSN, S1SN, S2SN and HCi for SN, forms a set <IDSN, S1SN, S2SN, HCi> and stores it in the memory.
- Step 2.
- After that, HN calculates XSN = aSN ⊕ KSHN, YSN = IDSN ⊕ h(KSHN||aSN) and PIDAP = IDAP ⊕ h(aSN||KSHN), composes a set <IDSN, XSN, YSN, S1SN, S2SN, HCi> and stores it in the memory of SN. They are used for authenticity check of PT.
- Step 3.
- HN stores PIDAP in the memory of AP.
3.3. Authentication Phase
- Step 1.
- SN gets the current timestamp T1SN, calculates a message authentication code RIDS = (IDSN||XSN||YSN||S2SN||HCi||T1SN) and composes a message {XSN, YSN, RIDS, T1SN} to submit to AP.
- Step 2.
- When AP receives the message, it adds a session dependent pseudo identity PIDAP to the message {XSN, YSN, RIDS, T1SN, PIDAP} and sends the message to HN.
- Step 3.
- When HN receives the message, it gets the current timestamp T1HN and verifies the freshness of the message by validating T1HN − T1SN ≤ ∆t where ∆t is the allowed transmission delay of the network. If it does not hold, HN treats this message as a replay attack and aborts the session. Otherwise, HN calculates aSN′ = XSN ⊕ KSHN and IDAP′ = PIDAP ⊕ h(aSN′||KSHN). After that, HN calculates IDSN′ = YSN ⊕ h(KSHN||aSN′) and compares it with IDSN stored in its memory. Only if the verification is successful, HN calculates RIDS′ = h(IDSN′||XSN||YSN||S2SN||HCi||T1SN) using the parameters in its repository. Finally, HN checks whether RIDS′ is equal to RIDS or not.
- Step 4.
- Only after all verifications are successful, HN could believe the authenticity of SN and AP and forms a reply message with two options, one is to be authenticated to SN and AP and another is to update the authentication parameters for the next authentication for SN and AP, respectively. For this, HN gets the current timestamp T2HN, generates two random numbers q and naSN, and calculates XSN′ = naSN ⊕ KSHN, YSN′ = IDSN′ ⊕ h(KSHN||naSN), NPIDAP = IDAP′ ⊕ h(naSN||KSHN), j = IDSN′ ⊕ YSN ⊕ XSN, r = q ⊕ j, g = h(q||j||S2SN), ZAP = h(PIDAP||NPIDAP||IDAP′), NXSN = XSN′ ⊕ g, NYSN = YSN′ ⊕ g, CSN = h(q||IDSN′||j||XSN′||YSN′||T2HN) and KS = h(q||S1SN||S2SN||HCi). After that, HN overwrites S1SN into S2SN and changes S2SN with KS in its memory, which are used for the next authentication for privacy provision. And then, HN calculates HCi′ = h(HCi) and replaces it to HCi as HCi = HCi′, which is for updating the session key parameter. After that, HN composes a message {r, NXSN, NYSN, CSN, T2HN, NPIDAP, ZAP} and sends it to AP.
- Step 5.
- After receiving the message, AP checks the freshness of message by calculating ZAP′ = h(PIDAP||NPIDAP||IDAP) and verifying whether ZAP′ is the same as ZAP in the message or not. Only if the verification is successful, AP overwrites NPIDAP into PIDAP in its memory. After that, AP drops NPIDAP and ZAP from the message and sends the reformed message {r, NXSN, NYSN, CSN, T2HN} to SN.
- Step 6.
- When SN receives the message, it gets the current timestamp T2SN and verifies the freshness of the message by validating T2SN − T2HN ≤ ∆t. If it is not successful, SN aborts the session, which is treated as a replay attack. Otherwise, it calculates j′ = IDSN ⊕ YSN ⊕ XSN, q′ = r ⊕ j′, g′ = h(q||j′||S2SN), XSN″ = NXSN ⊕ g′, YSN″ = NYSN ⊕ g′ and CSN′ = h(q′||IDSN||j′||XSN″||YSN″||T2HN) and validates CSN′ by comparing it with CSN in the message. It aborts the session if the validation fails. Otherwise, SN implicitly accept the authenticity of HN and calculates a session key KS′ = h(q′||S1SN||S2SN|| HCi) and overwrite S1SN into S2SN and changes S2SN with KS. SN replaces the two parameters, XSN″ and YSN″ into XSN and YSN, respectively, which are the next authentication parameters. Finally, SN calculates HCi′ = h(HCi) and replaces it to HCi as HCi = HCi′, which is for updating the session key parameter.
3.4. Identity Modification Phase
- Step 1.
- SN sets the current timestamp T1SN, selects a new identity IDSNNEW, calculates NIDSN = IDSNNEW ⊕ S2SN and RIDS = h(IDSN||XSN||YSN||S2SN||NIDSN||HCi||T1SN), composes a message {XSN, YSN, RIDS, T1SN, NIDSN} and submits it to AP.
- Step 2.
- When AP receives the message, it adds PIDAP to the message {XSN, YSN, RIDS, T1SN, NIDSN, PIDAP} and sends the message to HN.
- Step 3.
- When HN receives the message, it sets the current timestamp T1HN. And HN validates the freshness of the message by verifying T1HN − T1SN ≤ ∆t. If TSN is not fresh, HN aborts the session. Otherwise, HN calculates authentication parameters aSN′ = XSN ⊕ KSHN and IDAP′ = PIDAP ⊕ h(aSN′||KSHN). After that, HN calculates IDSN′ = YSN ⊕ h(KSHN||aSN′) and compares it with IDSN stored in its memory. Only if the verification is successful, HN calculates RIDS′ = h(IDSN′||XSN||YSN||S2SN||NIDSN|| HCi||T1SN) using the parameters in its repository. Finally, HN checks whether RIDS′ is equal to RIDS.
- Step 4.
- Only after all verifications are successful, HN withdraws the new identity from SN by computing IDSNNEW′ = NIDSN ⊕ S2SN. After that, HN generates current timestamp T2HN and random numbers q and calculates the new identity related authentication parameters YSN′ = IDSNNEW′ ⊕ h(KSHN||aSN′), j = IDSN ⊕ YSN ⊕ XSN, r = q ⊕ j, g = h(q||j||S2SN), NYSN = YSN′ ⊕ g and CSN = h(q||IDSN||j||YSN′||T2HN). Then HN overwrites IDSN NEW′ into IDSN in its memory. Next HN composes a message {r, NYSN, CSN, T2HN} and sends it to AP.
- Step 5.
- After receiving the message, AP sends the message {r, NYSN, CSN, T2HN} to SN.
- Step 6.
- When SN receives the message, it sets the current timestamp T2SN. And SN validates the freshness of the message by verifying T2SN − T2HN ≤ ∆t. If T2HN is not fresh, SN aborts the session. Otherwise, SN calculates j′ = IDSN ⊕ YSN ⊕ XSN, q′ = r ⊕ j′, g′ = h(q||j′||S2SN), YSN″ = NYSN ⊕ g′ and CSN′ = h(q′||IDSN||j′||YSN″||T2HN), which are withdrawing the new identity related authentication parameters. After that, SN validates CSN′ by comparing it with CSN in the message. It aborts the session if the validation fails. Otherwise, SN replaces YSN with YSN″ in its memory.
4. Security and Privacy Results
4.1. BAN Logic Result
- Q|≡ X: Principal Q believes the statement X.
- #(X): Formula X is fresh.
- Q|X: Principal Q has jurisdiction over the statement X.
- QX: Principal Q sees the statement X.
- Q|X: Principal Q once said the statement X.
- (X, Y): Formula X or Y is one part of the formula (X, Y).
- : Formula P combined with the formula Q.
- : Principal Q and R may use the shared session key, SK to communicate among each other. SK is good, in that any principal except Q and R will never discover it.
- -
- Message-meaning rule:
- -
- Nonce-verification rule:
- -
- Jurisdiction rule:
- -
- Freshness rule:
- Based on Message 1, we could derive:
- Step 1. AP(<XSN>KSHN, <YSN>KSHN, <RIDs>KSHN, T1SN)
- Based on Step 1, AP adds <PIDAP>KSHN to the message and sends it to HN. Based on Message 2, we could derive:
- Step 2. HN(<XSN>KSHN, <YSN>KSHN, <RIDs>KSHN, T1SN, <PIDAP>KSHN)
- According to assumption A6 and the message-meaning rule, we get:
- Step 3. HN|≡AP|(<XSN>KSHN, <YSN>KSHN, <RIDs>KSHN, T1SN, <PIDAP>KSHN)
- According to assumptions A1 and A2 and the freshness concatenation rule, we get:
- Step 4. HN|≡#(<XSN>KSHN, <YSN>KSHN, <RIDs>KSHN, T1SN, <PIDAP>KSHN)
- According to Steps 3 and 4 and the nonce verification rule, we get:
- Step 5. HN|≡SN|≡(<XSN>KSHN, <YSN>KSHN, <RIDs>KSHN, T1SN, <PIDAP>KSHN)
- According to Step 5, assumption A6 and the believe rule, we get:
- Step 6. HN|≡SN|≡(HNSN)
- According to assumption A8 and the jurisdiction rule, we get:
- Step 7. HN|≡(HNSN)
- According to Steps 5, 6 and 7 and the nonce verification rule, we conclude:
- Step 8. HN|≡SN|≡(SNHN) (Goal 3)
- According to assumption A8 and the jurisdiction rule, we get:
- Step 9. HN|≡(HNSN) (Goal 1)
- Based on Message 3, we could derive:
- Step 10. AP(<r>KSHN, <NXSN>KSHN, <NYSN>KSHN, <CSN>KSHN, <NPIDAP>KSHN, <ZAP>KSHN, T2HN)
- According to the message meaning rule, we get:
- Step 11. AP|≡HN|(<r>KSHN, <NXSN>KSHN, <NYSN>KSHN, <CSN>KSHN, <NPIDAP>KSHN, <ZAP>KSHN, T2HN)
- Based on Step 10, AP drops <NPIDAP>KSHN and <ZAP>KSHN to the message and sends it to HN.
- Based on Message 4, we derive:
- Step 12. SN(<r>KSHN, <NXSN>KSHN, <NYSN>KSHN, <CSN>KSHN, T2HN)
- According to assumption A5 and the message-meaning rule, we get:
- Step 13. SN|≡AP|(<r>KSHN, <NXSN>KSHN, <NYSN>KSHN, <CSN>KSHN, T2HN)
- According to assumptions A3 and A4 and the freshness concatenation rule, we get:
- Step 14. SN|≡#(<r>KSHN, <NXSN>KSHN, <NYSN>KSHN, <CSN>KSHN, T2HN)
- According to Steps 12 and 13 and the nonce verification rule, we get:
- Step 15. SN|≡HN|≡(<r>KSHN, <NXSN>KSHN, <NYSN>KSHN, <CSN>KSHN, T2HN)
- According to Step 14, assumption A5 and the believe rule, we get:
- Step 16. SN|≡HN|≡(HNSN)
- According to assumption A7 and the jurisdiction rule, we get:
- Step 17. SN|≡(HNSN)
- According to Steps 14, 15 and 16 and the nonce verification rule, we get:
- Step 18. SN|≡HN|≡(HNN) (Goal 4)
- According to assumption A7 and the jurisdiction rule, we get:
- Step 19. SN|≡(SNHN) (Goal 2)
4.2. ProVerif Result
4.3. Informal Privacy and Security Analysis
5. Performance Results
5.1. Computation Result
5.2. Communication Result
6. Discussion
6.1. Challenges and Soluitons
6.2. Future Work
7. Conclusions
Author Contributions
Funding
Institutional Review Board Statement
Informed Consent Statement
Data Availability Statement
Conflicts of Interest
References
- Dua, A.; Kumar, N.; Das, A.K.; Susilo, W. Secure Message Communication Protocol among Vehicles in Smart City. IEEE Trans. Veh. Technol. 2018, 127, 4359–4373. [Google Scholar] [CrossRef]
- Roy, S.; Chatterjee, S.; Das, A.K.; Chappopadhyay, S.; Kumar, N.; Vasilakos, A.V. On the Design of Provably Secure Lightweight Remote User Authentication Scheme for Mobile Cloud Computing Services. IEEE Access 2017, 5, 25808–25825. [Google Scholar] [CrossRef]
- Bali, R.S.; Kumar, N.S. Secure clustering for efficient data dissemination in vehicular cyber-physical systems. Future Gener. Comput. Syst. 2016, 56, 476–492. [Google Scholar] [CrossRef]
- Li, X.; Liu, T.; Obaidat, M.S.; Wu, F.; Vijayakumar, P.; Kumar, N. A Lightweight Privacy-Preserving Authentication Protocol for VANETs. IEEE Syst. J. 2020, 14, 3547–3557. [Google Scholar] [CrossRef]
- Vijayakumar, P.; Azees, M.; Chang, V.; Deborah, J.; Balusamy, B. Computationally efficient privacy preserving authentication and key distribution techniques for vehicular ad hoc networks. Clust. Comput. 2017, 20, 2439–2450. [Google Scholar] [CrossRef]
- Pradhan, B.; Bhattacharyya, S.; Pal, K. IoT-Based Applications in Healthcare Devices. J. Helathcare Eng. 2021, 2021, 6632599. [Google Scholar]
- Paek, J.; Gaglione, O.; Gnawali, O.; Vierira, M.A.M.; Hao, S. Advances in Mobile Networking for IoT Leading the 4th industrial Revolution. Mob. Inf. Syst. 2018, 2018, 8176158. [Google Scholar] [CrossRef] [Green Version]
- Malik, N.N.; Alosaimi, W.; Uddin, M.I.; Alouffi, B.; Alyami, H. Wireless Sensor Network Applications in Healthcare and Precision Agriculture. J. Healthc. Eng. 2020, 2020, 8836613. [Google Scholar] [CrossRef]
- Cho, S.; Kim, H. Secure Authenticated Key Agreement for Telecare Health Services using Ubiquitous IoT. Int. J. Adv. Electron. Comput. Sci. 2019, 6, 28–32. [Google Scholar]
- Zhang, N.; Ning, W.; Xie, T.; Liu, J.; He, R.; Zhu, B.; Mao, Y. Spatial Disparities in Access to Healthcare Professionals in Sichuan: Evidence from County-Level Data. Healthcare 2021, 9, 1053. [Google Scholar] [CrossRef]
- Park, B.; Lee, H. Healthcare Safety Nets during the COVID-19 Pandemic Based on Double Diamond Model: A Concept Analysis. Healthcare 2021, 9, 1014. [Google Scholar] [CrossRef]
- McDonald, Y.J.; Goldberg, D.W.; Scarinci, I.C.; Castle, P.E.; Cuzick, J.; Robertson, M.; Wheeler, C.M. Health Service Accessibility and Risk in Cervical Cancer Prevention: Comparing Rural Versus Nonrural Residence in New Mexico: Health Service Accessibility. J. Rural. Health 2017, 33, 382–392. [Google Scholar] [CrossRef] [PubMed] [Green Version]
- Kaluski, D.N.; Stojanovski, K.; McWeeney, G.; Paunovic, E.; Ostlin, P.; Licari, L.; Jakab, Z. Health insurance and accessibility to health services among Roma in settlements in Belgrade, Serbia—The journey from data to policy making. Health Policy Plan. 2015, 30, 976–984. [Google Scholar] [CrossRef] [PubMed] [Green Version]
- Ganann, R.; Sword, W.; Newbold, K.B.; Thabane, L.; Armour, L.; Kint, B. Influences on mental health and health services accessibility in immigrant women with post-partum depression: An interpretive descriptive study. J. Psychiatr. Ment. Health Nurs. 2020, 27, 87–96. [Google Scholar] [CrossRef] [PubMed]
- Cookson, R.; Propper, C.; Asaria, M.; Raine, R. Socio-Economic Inequalities in Health Care in England. Fisc. Stud. 2016, 37, 371–403. [Google Scholar] [CrossRef] [Green Version]
- Bisio, I.; Lavagetto, F.; Marchese, M.; Sciarrone, A. A smartphone-centric platform for remote health monitoring of heart failure. Int. J. Commun. Syst. 2015, 28, 1753–1771. [Google Scholar] [CrossRef]
- Kalid, N.; Zaidan, A.A.; Zaidan, B.B.; Salman, O.H.; Hashim, M.; Albahri, O.S.; Albahri, A.S. Based on Real Time Remote Health Monitoring Systems: A New Approach for Prioritization “Large Scales Data” Patients with Chronic Heart Diseases Using Body Sensors and Communication Technology. J. Med Syst. 2018, 42, 1–37. [Google Scholar] [CrossRef]
- Wang, P.; Tsao, L.; Chen, Y.; Lo, Y.; Sun, H. “Hesitating and Puzzling”: The Experiences and Decision Process of Acute Ischemic Stroke Patients with Prehospital Delay after the Onset of Symptoms. Healthcare 2021, 9, 1061. [Google Scholar] [CrossRef]
- Rahman, M.Z.U.; Karthik, G.V.S.; Fathima, S.Y.; Lay-Ekuakille, A. An efficient cardiac signal enhancement using time–frequency realization of leaky adaptive noise cancelers for remote health monitoring systems. Measurement 2013, 46, 3815–3835. [Google Scholar] [CrossRef]
- Majumder, S.; Mondal, T.; Deen, M.J. Wearable Sensors for Remote Health Monitoring. Sensors 2017, 17, 130. [Google Scholar] [CrossRef]
- Gu, D.; Humbatova, G.; Xie, Y.; Yang, X.; Zolotarev, O.; Zhang, G. Different Roles of Telehealth and Telemedicine on Medical Tourism: An Empirical Study from Azerbaijan. Healthcare 2021, 9, 1073. [Google Scholar] [CrossRef]
- Al-Janabi, S.; Al-Shourbaji, I.; Shojafar, M.; Shamshirband, S. Survey of main challenges (security and privacy) in wireless body area networks for healthcare applications. Egypt. Inform. J. 2017, 18, 113–122. [Google Scholar] [CrossRef] [Green Version]
- Liu, Q.; Mkongwa, K.G.; Zhang, C. Performance issues in wireless body area networks for the healthcare application: A survey and future prospects. SN Appl. Sci. 2021, 3, 1–19. [Google Scholar] [CrossRef]
- Formica, D.; Schena, E. Smart Sensors for Healthcare and Medical Applications. Sensors 2021, 21, 543. [Google Scholar] [CrossRef] [PubMed]
- Tovino, S.A. Privacy and Security Issues with Mobile Health Research Applications. J. Law Med. Ethics 2019, 47, 154–158. [Google Scholar]
- Kim, H. Research Issues on Data Centric Security and Privacy Model for Intelligent Internet of Things based Healthcare. ICSES Trans. Comput. Netw. Commun. 2019, 5, 1–3. [Google Scholar] [CrossRef]
- Kim, H. Data Centric Security and Privacy Research Issues for Intelligent Internet of Things. ICSES Interdisiplinary Trans. Cloud Comput. IoT Big Data 2017, 1, 1–2. [Google Scholar]
- Vijayakumar, P.; Chang, V.; Deborah, L.J.; Balusamy, B.; Shynu, P.G. Computationally efficient privacy preserving anonymous mutual and batch authentication schemes for vehicular ad hoc networks. Future Gener. Comput. Syst. 2018, 78, 943–955. [Google Scholar] [CrossRef]
- Vora, J.; Italiya, P.; Tanwar, S.; Tyagi, S.; Kumar, N.; Obaidat, M.S.; Hsiao, K.-F. Ensuring Privacy and Security in E-Health Records. In Proceedings of the 2018 International Conferecne on Computer, Information and Telecommunication Systems, Colmar, France, 11–13 July 2018. [Google Scholar]
- Zhu, J.; Ma, J. A new authentication scheme with anonymity for wireless environments. IEEE Trans. Consum. Electron. 2004, 50, 231–235. [Google Scholar]
- Lee, C.C.; Hwang, M.S.; Liao, I.E. Security enhancement on a new authentication scheme with anonymity for wireless environments. IEEE Trans. Ind. Electron. 2006, 53, 1683–1687. [Google Scholar] [CrossRef] [Green Version]
- Memon, I.; Hussain, I.; Akhtar, R.; Chen, G. Enhanced Privacy and Authentication: An Efficient and Secure Anonymous Communication for Location Based Service Using Asymmetric Cryptography Scheme. Wirel. Pers. Commun. 2015, 84, 1487–1508. [Google Scholar] [CrossRef]
- Reddy, A.G.; Das, A.K.; Yoon, E.J.; Yoo, K.Y. A Secure Anonymous Authentication Protocol for Mobile Services on Elliptic Curve Cryptography. IEEE Access 2016, 4, 4394–4407. [Google Scholar] [CrossRef]
- Khatoon, S.; Rahman, S.M.M.; Alrubaian, M.; Alamri, A. Privacy-Preserved, Provable Secure, Mutually Authenticated Key Agreement Protocol for Healthcare in a Smart City Environment. IEEE Access 2019, 7, 47962–47971. [Google Scholar] [CrossRef]
- Ostad-Sharif, A.; Abbasinezhad-Mood, D.; Kikooghadam, M. An enhanced anonymous and unlinkable user authentication and key agreement protocol for TMIS by utilization of ECC. Int. J. Commun. Syst. 2019, 32, e3913. [Google Scholar] [CrossRef]
- Ali, Z.; Ghani, A.; Khan, I.; Chaudhry, S.A.; Islam, H.; Giri, D. A robust authentication and access control protocol for securing wireless healthcare sensor networks. J. Inf. Secur. Appl. 2020, 52. [Google Scholar] [CrossRef]
- Burrows, M.; Abadi, M.; Needham, R. A logic of authentication. R. Soc. Lond. Math. Phys. Eng. Sci. 1989, 426, 233–271. [Google Scholar]
- Khan, I.; Chaudhry, S.A.; Sher, M.; Khan, J.I.; Khan, M.K. An anonymous and provably secure biometric-based authentication scheme using chaotic maps for accessing medical drop box data. J. Supercomput. 2018, 74, 3685–3703. [Google Scholar] [CrossRef]
- Aman, M.N.; Chua, K.C.; Sikdar, B. A light-weight mutual authentication protocol for IoT systems. In Proceedings of the 2017 IEEE Global Communications Conference, Singapore, 4–18 December 2017. [Google Scholar]
- Xu, Z.; Xu, C.; Chen, H.; Yang, F. A lightweight anonymous mutual authentication and key agreement scheme for WBAN. Concurr. Comput. Pract. Exp. 2019, 31, e5295. [Google Scholar] [CrossRef]
- Alzahrani, B.A.; Irshad, A.; Albeshri, A.; Alsubhi, K. A Provably Secure and Lightweight Patient-Healthcare Authentication Protocol in Wireless Body Area Networks. Wirel. Pers. Commun. 2021, 117, 47–69. [Google Scholar] [CrossRef]
- Blanchet, B. Automatic Verification of Security Protocols in the Symbolic Model: The Verifier ProVerif. Lect. Notes Comput. Sci. 2013, 8604, 54–87. [Google Scholar]
- Liu, B.; Han, B.; Zheng, H.; Liu, H.; Zhao, T.; Wan, Y.; Cui, F. Who Is the Most Vulnerable to Anxiety at the Beginning of the COVID-19 Outbreak in China? A Cross-Sectional Nationwide Survey. Healthcare 2021, 9, 970. [Google Scholar] [CrossRef]
- Canetti, R.; Krawczyk, H. Analysis of Key-Exchange Protocols and Their Use for Building Secure Channels. In Proceedings of the EUROCRYPT 2001, Innsbruck, Austria, 6–10 May 2001; Springer: Berlin/Heidelberg, Germany, 2001; pp. 453–474. [Google Scholar]
- Sarr, A.P.; Elbaz-Vincent, P.; Bajard, J.-C. A New Security Model for Authenticated Key Agreement. In Proceedings of the Security and Cryptography for Networks, Amalfi, Italy, 13–15 September 2010; Springer: Berlin/Heidelberg, Germany, 2010; pp. 219–234. [Google Scholar]
- Xu, Z.; Luo, M.; Kumar, N.; Vijayakumar, P.; Li, L. Privacy-Protection Scheme Based on Sanitizable Signature for Smart Mobile Medical Scenarios. Wirel. Commun. Mob. Comput. 2020, 2020, 8877405. [Google Scholar] [CrossRef]
- Klumpp, M.; Hintze, M.; Immonen, M.; Ródenas-Rigla, F.; Pilati, F.; Aparicio-Martínez, F.; Çelebi, D.; Liebig, T.; Jirstrand, M.; Urbann, O.; et al. Artificial Intelligence for Hospital Health Care: Application Cases and Answers to Challenges in European Hospitals. Healthcare 2021, 9, 961. [Google Scholar] [CrossRef]
- Wang, D.; He, D.; Wang, P.; Chu, C. Anonymous Two-Factor Authentication in Distributed Systems: Certain Goals Are Beyond Attainment. IEEE Trans. Dependable Secur. Comput. 2015, 12, 428–442. [Google Scholar] [CrossRef]
- Avoine, G.; Canard, S.; Ferreira, L. Symmetric-kay Authenticated Key Exchange (SAKE) with Perfect Forward Secrecy. In Proceedings of the CT-RSA, San Francisco, CA, USA, 24–28 February 2020; Springer: Cham, Switzerland, 2020; pp. 24–28. [Google Scholar]
- Bellare, M.; Yee, B.B. Forward-security in private-key cryptography. In Proceedings of the CT-RSA, San Francisco, CA, USA, 13–17 April 2003; Springer: Berlin/Heidelberg, Germany, 2003; pp. 1–18. [Google Scholar]
- Brier, E.; Peyrin, T. A forward-secure symmetric-key derivation protocol—How to improve classical DUKPT. In Proceedings of the ASIACRYPT, Singapore, 5–9 December 2010; Springer: Berlin/Heidelberg, Germany, 2010; pp. 250–257. [Google Scholar]
- Abdalla, M.; Bellare, M. Increasing the lifetime of a key: A comparative analysis of the security of re-keying techniques. In Proceedings of the ASIACRYPT, Kyoto, Japan, 3–7 December 2000; Springer: Berlin/Heidelberg, Germany, 2000; pp. 546–559. [Google Scholar]
- Nikooghadam, M.; Admintoosi, H. Cryptanalysis of Khatoon et al.’s ECC-based Authentication Protocol for Healthcare System. arXiv 2019, arXiv:190608424N. [Google Scholar]
- Li, W.; Wang, P. Two-factor authentication in industrial Internet-of_things: Attacks, evaluation and new construction. Future Gener. Comput. 2019, 101, 694–708. [Google Scholar] [CrossRef]
- Babamir, F.; Kirci, M. Dynamic digest based authentication for client–server systems using biometric verification. Future Gener. Comput. Syst. 2019, 101, 112–126. [Google Scholar] [CrossRef]
- Kaplan, B. How Should Health Data Be Used? Privacy, Secondary Use, and Big Data Sales. Camb. Q. Healthc. Ethics 2016, 25, 312–329. [Google Scholar] [CrossRef] [Green Version]
- Richens, J.G.; Lee, C.M.I. Improving the accuracy of medical diagnosis with causal machine learning. Nat. Commun. 2021, 12, 3923. [Google Scholar] [CrossRef]
- How AI Technologies Accelerate Progress in Medical Diagnosis. Available online: https://roboticsandautomationnews.com/2020/03/09/how-ai-technologies-accelerate-progress-in-medical-diagnosis/31184/ (accessed on 26 August 2021).





| Notation | Descriptions |
|---|---|
| SA | System administrator |
| HN | Healthcare central server |
| PT | Patient |
| SN | Sensor node |
| AP | Access point |
| IDSN | Identity of SN |
| IDAP | Identity of AP |
| YSN | Pseudonym identity of SN |
| PIDAP | Pseudonym identity of AP |
| KSHN | Long-term master key of HN |
| KS | Established session key |
| Tij | i-th timestamp of an entity j |
| Sij | i-th random number of an entity j |
| aSN, naSN, q | Random numbers |
| HCi | Hash chain value of SN |
| h() | Secure one-way hash function |
| || | Concatenation operation |
| ⊕ | Exclusive-or operation |
| ∆t | Allowed transmission delay |
| Protocol | Khatoon et al. [34] | Ostad-Sharif et al. [35] | Khan et al. [38] | Xu et al. [40] | Alzahrani et al. [41] | Proposed | |
|---|---|---|---|---|---|---|---|
| Feature | |||||||
| SP1 | O | O | O | O | O | O | |
| SP2 | O | O | O | O | O | O | |
| SP3 | O | O | O | O | O | O | |
| SP4 | O | O | X | X | X | O | |
| SP5 | X | X | X | X | X | O | |
| PP1 | O | O | O | X | O | O | |
| PP2 | O | O | O | X | X | O | |
| Protocol | Khatoon et al. [34] | Ostad-Sharif et al. [35] | Khan et al. [38] | Xu et al. [40] | Alzahrani et al. [41] | Proposed | |
|---|---|---|---|---|---|---|---|
| Entity | |||||||
| SN | 5Th + 1Tbp + 1Tsym + 3Tecc | 7Th + 2Tecc | 7Th | 4Th | 4Th | 4Th | |
| AP | - | - | - | - | - | 1Th | |
| HN | 4Th + 1Tbp + 1Tsym + 2Tecc | 7Th + 2Tsym + 2Tecc | 4Th | 6Th | 6Th | 9Th | |
| Total | 9Th + 2Tbp + 2Tsym + 5Tecc | 14Th + 2Tsym + 4Tecc | 11Th | 10Th | 10Th | 14Th | |
| Protocol | Khatoon et al. [34] | Ostad-Sharif et al. [35] | Khan et al. [38] | Xu et al. [40] | Alzahrani et al. [41] | Proposed | |
|---|---|---|---|---|---|---|---|
| Feature | |||||||
| Message length | SN | 832 bits | 1408 bits | 1120 bits | 896 bits | 896 bits | 896 bits |
| AP | - | - | - | 1024 bits + 544 bits | 1024 bits + 544 bits | 1312 bits + 480 bits | |
| HN | 640 bits | 1120 bits | 640 bits | 672 bits | 672 bits | 1184 bits | |
| Total | 1472 bits | 2528 bits | 1760 bits | 3136 bits | 3136 bits | 3872 bits | |
| Number of messages | 2 messages | 2 messages | 2 messages | 4 messages | 4 messages | 4 messages | |
Publisher’s Note: MDPI stays neutral with regard to jurisdictional claims in published maps and institutional affiliations. |
© 2021 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).
Share and Cite
Ryu, H.; Kim, H. Privacy-Preserving Authentication Protocol for Wireless Body Area Networks in Healthcare Applications. Healthcare 2021, 9, 1114. https://doi.org/10.3390/healthcare9091114
Ryu H, Kim H. Privacy-Preserving Authentication Protocol for Wireless Body Area Networks in Healthcare Applications. Healthcare. 2021; 9(9):1114. https://doi.org/10.3390/healthcare9091114
Chicago/Turabian StyleRyu, Hyunho, and Hyunsung Kim. 2021. "Privacy-Preserving Authentication Protocol for Wireless Body Area Networks in Healthcare Applications" Healthcare 9, no. 9: 1114. https://doi.org/10.3390/healthcare9091114
APA StyleRyu, H., & Kim, H. (2021). Privacy-Preserving Authentication Protocol for Wireless Body Area Networks in Healthcare Applications. Healthcare, 9(9), 1114. https://doi.org/10.3390/healthcare9091114







