Decoding China’s COVID-19 Health Code Apps: The Legal Challenges
Abstract
:1. Introduction
2. Materials and Methods
2.1. Research Data
2.2. Research Methods
3. Results
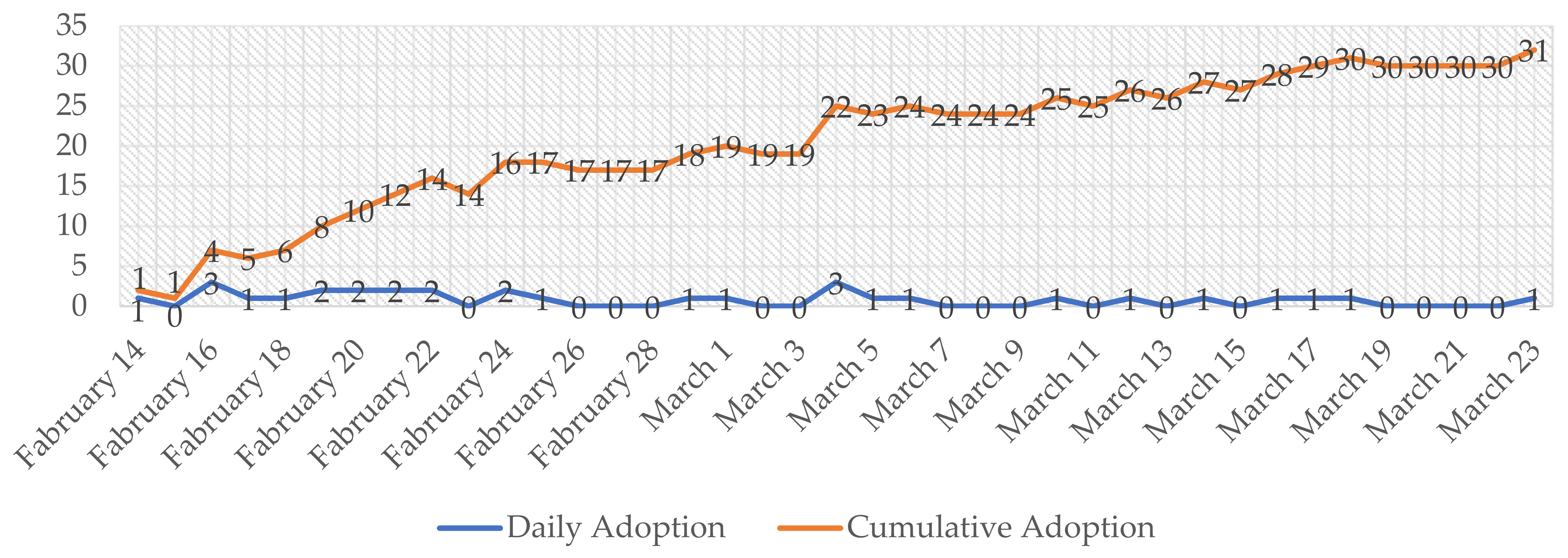
3.1. The Course That Health Code Apps Went National
3.2. Data Collected for Generating a Personal Health Code
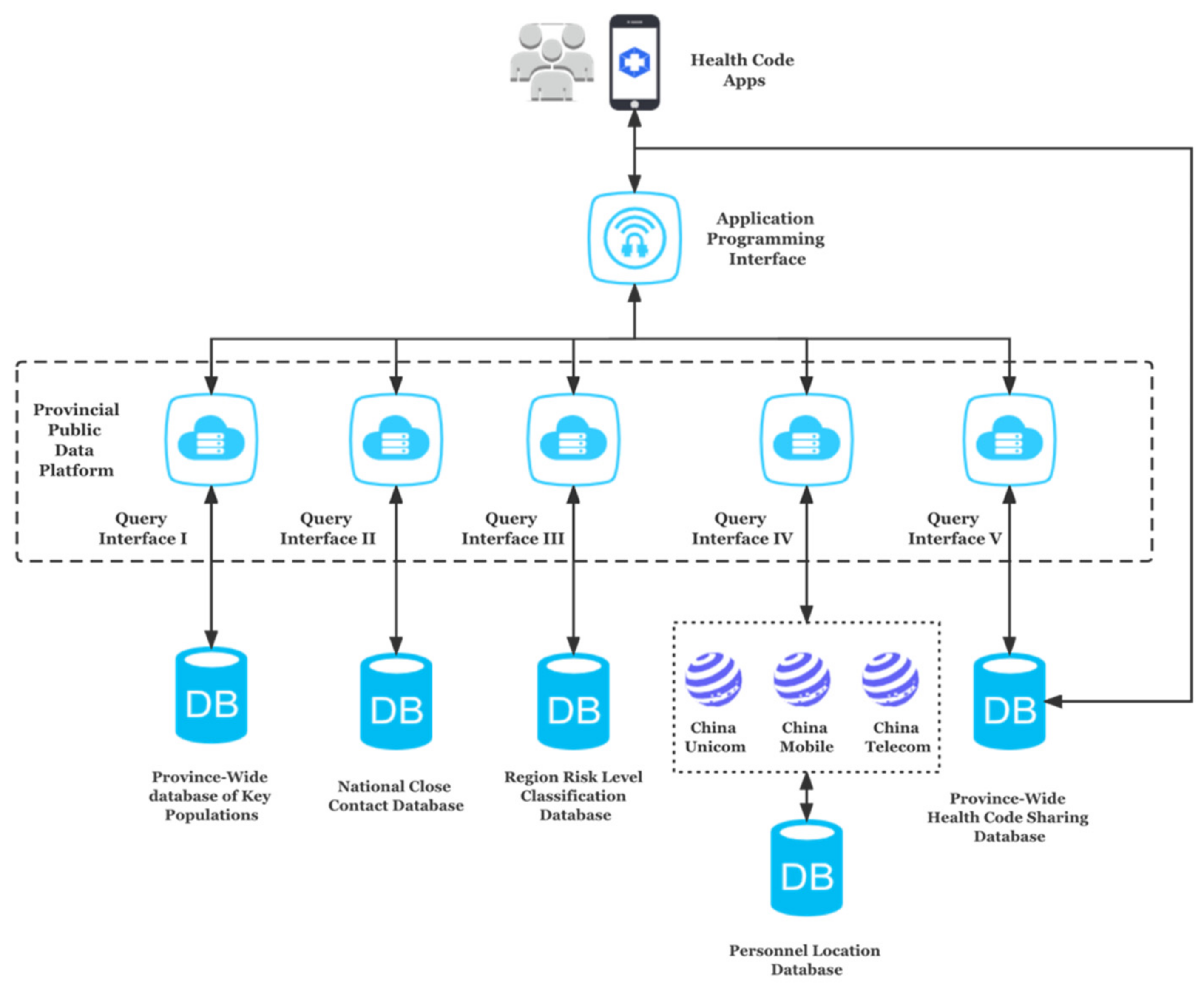
3.3. Databases That a Health Code System Can Access—The Hangzhou Health Code System as an Example
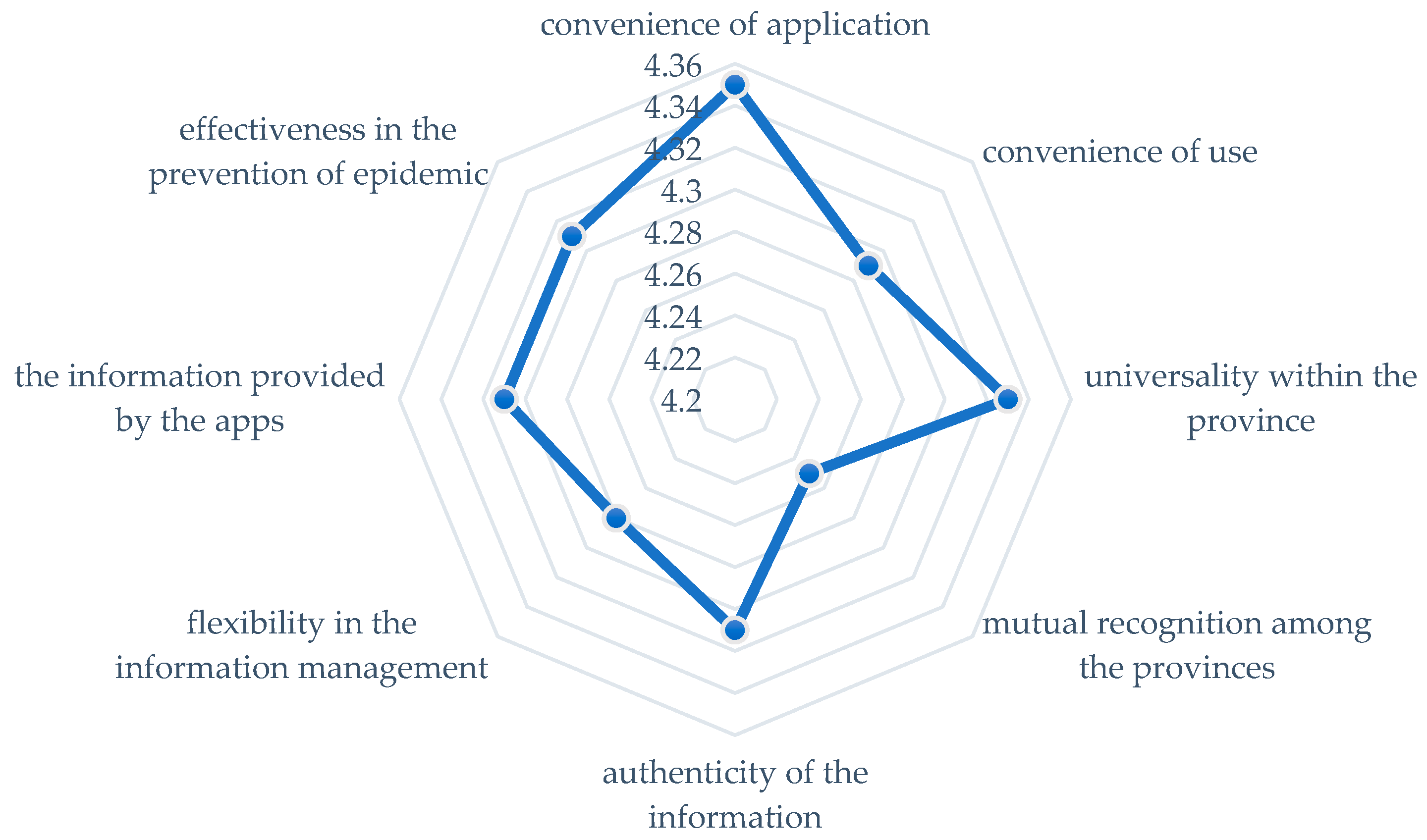
3.4. Public Acceptance of the Health Code Apps
4. Discussion
4.1. The Introduction of the PIPL
4.2. Seven Key Principles Set out by the PIPL
4.3. Gaps in Addressing Personal Information Harms
4.3.1. User Consent
4.3.2. Transparency
4.3.3. Data Minimization
4.3.4. Storage Duration
4.3.5. Data Security
5. Conclusions
- the legal basis for collecting and processing the personal data in these apps;
- whether the apps are implemented in a transparent, accountable, and comprehensive manner;
- whether the personal data gathering is necessary and proportionate, taking into consideration the amount of personal data collected, the specific purposes of the collection, and how the data will be processed and shared;
- the period within which these apps will be in effect, as well as whether the apps have made any reference to the data retention term;
- whether the data controller has taken strict management and technical measures to prevent a data leakage.
Funding
Institutional Review Board Statement
Informed Consent Statement
Data Availability Statement
Conflicts of Interest
References
- WHO. Coronavirus Dashboard. Available online: https://covid19.who.int/ (accessed on 16 June 2022).
- Budd, J.; Miller, B.S.; Manning, E.M.; Lampos, V.; Zhuang, M.; Edelstein, M.; Rees, G.; Emery, V.C.; Stevens, M.M.; Keegan, N.; et al. Digital technologies in the public-health response to COVID-19. Nat. Med. 2020, 26, 1183–1192. [Google Scholar] [CrossRef] [PubMed]
- Council of Europe. Joint Statement on Digital Contact Tracing by Data Protection Commission. Available online: https://rm.coe.int/covid19-joint-statement-28-april/16809e3fd7 (accessed on 28 July 2022).
- Lewis, D. Contact-tracing apps help reduce COVID infections, data suggest. Nature 2021, 591, 18–19. [Google Scholar] [CrossRef] [PubMed]
- Paul, M.; Zhong, R.; Krolik, A. In Coronavirus Fight, China Gives Citizens a Color Code with Red Flags. The New York Times. Available online: https://www.nytimes.com/2020/03/01/business/china-coronavirus-surveillance.html (accessed on 16 June 2022).
- Norton Rose Fulbright. Contact Tracing Apps: A New World for Data Privacy. Available online: https://www.nortonrosefulbright.com/en-cn/knowledge/publications/d7a9a296/contact-tracing-apps-a-new-world-for-data-privacy (accessed on 28 July 2022).
- Wang, X. China’s COVID-19 Health Code System Is Ripe for Abuse and Must Not Outlast the Pandemic. Available online: https://www.scmp.com/week-asia/opinion/article/3182072/chinas-covid-19-health-code-system-ripe-abuse-and-must-not?module=perpetual_scroll_0&pgtype=article&campaign=3182072 (accessed on 28 July 2022).
- Cong, W. From Pandemic control to data-driven governance: The case of China’s health code. Front. Polit. Sci. 2021, 3, 627959. [Google Scholar] [CrossRef]
- Ahmed, N.; Michelin, R.A.; Xue, W.; Ruj, S.; Malaney, R.; Kanhere, S.S.; Seneviratne, A.; Hu, W.; Janicke, H.; Jha, S.K. A Survey of COVID-19 Contact Tracing Apps. IEEE Access 2020, 8, 134577–134601. [Google Scholar] [CrossRef]
- Albergotti, R. Apple and Google Expand Coronavirus Warning Software. Available online: https://www.washingtonpost.com/technology/2020/09/01/apple-google-exposure-notification-express/ (accessed on 29 July 2022).
- Braithwaite, I.; Callender, T.; Bullock, M.; Aldridge, R.W. Automated and partly automated contact tracing: A systematic review to inform the control of COVID-19. Lancet Digit. Health 2020, 2, e607–e621. [Google Scholar] [CrossRef]
- Cho, H.; Ippolito, D.; Yu, Y.W. Contact Tracing Mobile Apps for COVID-19: Privacy Considerations and Related Trade-offs. arXiv 2020. [CrossRef]
- Sun, Y.; Wang, W.Y. Governing with health code: Standardising China’s data network systems during COVID-19. Policy Internet 2022. [CrossRef] [PubMed]
- Zhejiang Daily. The Special Class That Can Work across Departments to Coordinate. Available online: https://baijiahao.baidu.com/s?id=1688857189022997210&wfr=spider&for=pc (accessed on 16 June 2022).
- Zhu, G.; Yang, H. Analysis of factors influencing the diffusion of technological governance innovations in public health crises: An empirical study of the diffusion of “health code apps”. Leadersh. Sci. Forum. 2021, 11, 13–21. (In Chinese) [Google Scholar]
- The Series of National Standard Documents of “Personal Health Information Code” Include “Reference Model of Personal Health Information Code (GB/T 38961-2020)”, “Data Format of Personal Health Information Code (GB/T 38962-2020)” and “Application Interface of Personal Health Information Code (GB/T 38963-2020)”, The General Administration of Market Supervision Issued a Series of National Standards for Personal Health Information Code. Available online: https://www.cn-healthcare.com/article/20200511/content-536118.html (accessed on 4 August 2022).
- WHO. Contact Tracing in the Context of COVID-19. Quarantine of Persons Is the Restriction of Activities and the Separation of Persons Who Are Not Ill but Who May Have Been Exposed to an Infectious Agent or Disease, with the Objective of Monitoring Their Symptoms and Ensuring the Early Detection of Cases. Quarantine Is Different from Isolation, which Is the Separation of Ill or Infected Persons from Others to Prevent the Spread of Infection or Contamination. Available online: https://www.who.int/publications-detail-redirect/contact-tracing-in-the-context-of-covid-19 (accessed on 16 June 2022).
- Global Digital Platform for Professionals. COVID-19 Health Code Reveals China’s Big Data Edge. Available online: https://www.fidelity.com.hk/en/articles/investment-spotlight/2020-07-20-covid19-health-code-reveals-chinas-big-data-edge-1595221646046 (accessed on 16 June 2022).
- Georgia Public Broadcasting. Twitter Will Pay a $150 Million Fine over Accusations It Improperly Sold User Data. Available online: https://www.gpb.org/news/2022/05/26/twitter-will-pay-150-million-fine-over-accusations-it-improperly-sold-user-data (accessed on 16 June 2022).
- People’s Daily. Investigation Report: The “Health Code Apps” May Become More Useful after the Epidemic. Available online: http://www.rmlt.com.cn/2020/0728/588265.shtml (accessed on 16 June 2022).
- Kendall, M.; Milsom, L.; Abeler-Dörner, L.; Wymant, C.; Ferretti, L.; Briers, M.; Holmes, C.; Bonsall, D.; Abeler, J.; Fraser, C. Epidemiological Changes on the Isle of Wight after the Launch of the NHS Test and Trace Programme: A Preliminary Analysis. Lancet Digit. Health 2020, 2, e658–e666. [Google Scholar] [CrossRef]
- Gasser, U.; Ienca, M.; Scheibner, J.; Sleigh, J.; Vayena, E. Digital Tools against COVID-19: Taxonomy, Ethical Challenges, and Navigation Aid. Lancet Digit. Health 2020, 2, e425–e434. [Google Scholar] [CrossRef]
- CNNIC. The 49th Statistical Report on China’s Internet Development; CNNIC: Beijing, China, 2022. [Google Scholar]
- Qianjiang Evening News. Within 72 Hours, the Hangzhou Health Code Application Rate Reached 95.2%. Available online: https://baijiahao.baidu.com/s?id=1658769009421405075&wfr=spider&for=pc (accessed on 16 June 2022).
- Feng, C. China Launches Coronavirus “Close Contact Detector” in Effort to Reassure Public over Health Risks. South China Morning Post. 2020. Available online: https://www.scmp.com/tech/apps-social/article/3050054/china-launches-coronavirus-close-contact-detector-effort-reassure (accessed on 16 June 2022).
- Blakely, D.E. Social Construction of Three Influenza Pandemics in the New York Times. J. Mass Commun. Q. 2003, 80, 884–902. [Google Scholar] [CrossRef]
- Parker, M.J.; Fraser, C.; Abeler-Dörner, L.; Bonsall, D. Ethics of Instantaneous Contact Tracing Using Mobile Phone Apps in the Control of the COVID-19 Pandemic. J. Med. Ethics. 2020, 46, 427–431. [Google Scholar] [CrossRef]
- Chen, J.; Sun, J. Understanding the Chinese Data Security Law. Int. Cybersecur. Law Rev. 2021, 2, 209–221. [Google Scholar] [CrossRef]
- Cate, F.H.; Mayer-Schönberger, V. Notice and consent in a world of Big Data. Int. Data Priv. Law 2013, 3, 67–73. [Google Scholar] [CrossRef] [Green Version]
- Peto, J.; Fletcher, O.; Gilham, C. Data protection, informed consent, and research. BMJ 2004, 7447, 1029–1030. [Google Scholar] [CrossRef] [PubMed]
- OECD. The OECD’s Guidelines on the Protection of Privacy and Transborder Flows of Personal Data in 1980 Constituted the First Internationally Agreed upon Set of Privacy Principles. Guidelines on the Protection of Privacy and Transborder Flows of Personal Data. The Guidelines Were Revised as the OECD Privacy Framework in 2013. Available online: https://www.oecd.org/internet/ieconomy/oecdguidelinesontheprotectionofprivacyandtransborderflowsofpersonaldata.htm (accessed on 16 June 2022).
- WHO. Ethical Considerations to Guide the Use of Digital Proximity Tracking Technologies for COVID-19 Contact Tracing. Available online: https://www.who.int/publications-detail-redirect/WHO-2019-nCoV-Ethics_Contact_tracing_apps-2020 (accessed on 16 June 2022).
- Shanghai Rule of Law News. Are Health Code Apps “Unrestrained” for Personal Information Processing? 16 November 2021. Available online: https://new.qq.com/omn/20211115/20211115A0E48M00.html (accessed on 4 August 2022).
- Ryan, M.; Cheng, L. Digital Handcuffs’: China’s Covid Health Apps Govern Life but Are Ripe for Abuse. Available online: https://www.ft.com/content/dee6bcc6-3fc5-4edc-814d-46dc73e67c7e (accessed on 24 July 2022).
- Jung, C. China’s Political Surveillance System Keeps Growing. Available online: https://thediplomat.com/2022/06/chinas-political-surveillance-system-keeps-growing/ (accessed on 25 July 2022).
- The News Indicates That Some of the Clients of These Banks Saw Their Health Code Turn Red, upon Arrival in Henan or Even before Embarking on Their Journey. Quartz. A Chinese Province May Be Targeting People through Its Covid App. Available online: https://qz.com/2177959/a-chinese-province-may-be-targeting-people-through-its-covid-app/ (accessed on 16 June 2022).
- Article 51 of the PIPL Stipulates That Personal Information Processors Shall Ensure That Personal Information Processing Activities Comply with the Provisions of Laws and Administrative Regulations, and Prevent Unauthorized Access to as Well as the Leakage, Tampering, or Loss of Personal Information by Taking Corresponding Security Technical Measures Such as En-Cryption and De-identification. “De-identification”, as Defined by Article 73.3 of the PIPL, Is the Process of Processing Per-Sonal Data to Make It Impossible to Identify Individual Natural People without Additional Information. Personal Information Protection Law of China. Available online: http://www.customs.gov.cn/kjs/zcfg73/4265285/index.html (accessed on 4 August 2022).
- These Three Questions Are Worth Pondering about Health Code Apps. Available online: https://baijiahao.baidu.com/s?id=1670913465217337836&wfr=spider&for=pc. (accessed on 16 June 2022).
- Redmiles, E.M. User Concerns Tradeoffs in Technology-Facilitated COVID-19 Response. Digit. Gov. Res. Pract. 2020, 6, 1–12. [Google Scholar] [CrossRef]
- Grundy, Q.; Chiu, K.; Held, F.; Continella, A.; Bero, L.; Holz, R. Data Sharing Practices of Medicines Related Apps and the Mobile Ecosystem: Traffic, Content, and Network Analysis. BMJ 2019, 364, l920. [Google Scholar] [CrossRef] [PubMed] [Green Version]
- Wang, B. Celebrities’ Photos, Other Info Leaked Due to Privacy Flaw in Beijing’s Health Code. Available online: https://en.pingwest.com/a/8168 (accessed on 28 July 2022).
- Garasic, M.D. Informed consent, clinical research, COVID-19 and contact tracing apps: Some neuroethical concerns. BioLaw J. 2021, 2S, 85–95. [Google Scholar]
- World Economic Forum. Redesigning Data Privacy: Reimagining Notice & Consent for Human Technology Interaction. Available online: https://www3.weforum.org/docs/WEF_Redesigning_Data_Privacy_Report_2020.pdf (accessed on 30 July 2022).

| No. | Data Type | Illustrations |
|---|---|---|
| 1 | data of confirmed and suspected cases | name, age, and body temperature |
| 2 | data of close contacts | name, place of residence, and travel history |
| 3 | medical testing data | nucleic acid test results and antibody test results |
| 4 | data from fever clinic | name, body temperature, and time of fever onset |
| 5 | location tracking data | location information archived by the telecom operators |
| 6 | transportation information | train/flight/bus number, transfer time, and boarding and alighting time |
| 7 | information on immigration | arrival time, port of entry, and flight information |
| 8 | customs inspection data | item name, entry time, and test results |
| 9 | community data | place name, community name, and risk level |
| 10 | information recorded by the community | residence information, family member information, and residents’ travel information recorded by the community council |
| 11 | personal information collected in the public places | body temperature information and access records reported by each public place |
| 12 | information filled in by the users themselves | user-reported personal health data and brief medical history |
| 13 | other data | other data related to the epidemic prevention |
| Principle | Illustrations |
|---|---|
| Lawfulness | Personal information must be processed per the principles of lawfulness, legitimacy, necessity, and good faith, and not in any manner that is misleading, fraudulent, or coercive. |
| Purpose specification | Personal information must be processed for a clear and reasonable purpose that is directly related to the processing purpose and in a manner that has the most negligible impact on persons’ rights and interests. |
| Data minimization | Scope limitation: the collection of personal information shall be limited to the minimum scope necessary for the processing purpose and shall not be excessive. Storage limitation: unless any applicable legislation or administrative rule specifies otherwise, the storage duration for personal information shall be the shortest time necessary to achieve the processing objective. |
| Transparency | Personal information shall be processed under the principles of openness and transparency, with the rules of processing of personal information disclosed and the purposes, methods, and scope of processing expressly stated. |
| Accuracy | The quality of personal information shall be guaranteed in processing the personal information to avoid adverse impacts on the rights and interests of individuals due to inaccuracy or incompleteness of the personal information. |
| Accountability | Personal information processors must be accountable for their personal information processing operations |
| Data security | Personal information processors must take necessary measures (such as encryption and de-identification) to ensure the security of the personal information processed. |
Publisher’s Note: MDPI stays neutral with regard to jurisdictional claims in published maps and institutional affiliations. |
© 2022 by the author. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).
Share and Cite
Zhang, X. Decoding China’s COVID-19 Health Code Apps: The Legal Challenges. Healthcare 2022, 10, 1479. https://doi.org/10.3390/healthcare10081479
Zhang X. Decoding China’s COVID-19 Health Code Apps: The Legal Challenges. Healthcare. 2022; 10(8):1479. https://doi.org/10.3390/healthcare10081479
Chicago/Turabian StyleZhang, Xiaohan. 2022. "Decoding China’s COVID-19 Health Code Apps: The Legal Challenges" Healthcare 10, no. 8: 1479. https://doi.org/10.3390/healthcare10081479
APA StyleZhang, X. (2022). Decoding China’s COVID-19 Health Code Apps: The Legal Challenges. Healthcare, 10(8), 1479. https://doi.org/10.3390/healthcare10081479






