Enhancing Security and Efficiency: A Fine-Grained Searchable Scheme for Encryption of Big Data in Cloud-Based Smart Grids
Abstract
1. Introduction
1.1. Motivation
1.2. Contributions
1.3. Related Work
1.4. Organization
2. Preliminaries
2.1. Notations
2.2. Bilinear Pairs
- (1)
- Bilinearity: , such that holds.
- (2)
- Non-degeneracy: , such that , where 1 is the unit element of .
- (3)
- Computability: For , there exist efficient algorithms that can compute .
2.3. Difficult Assumptions
2.4. Access Tree
- (1)
- When x is a leaf node, if and only if is an attribute in attribute set S.
- (2)
- When x is an internal node, we compute for each child z of x. if and only if there are at least children.
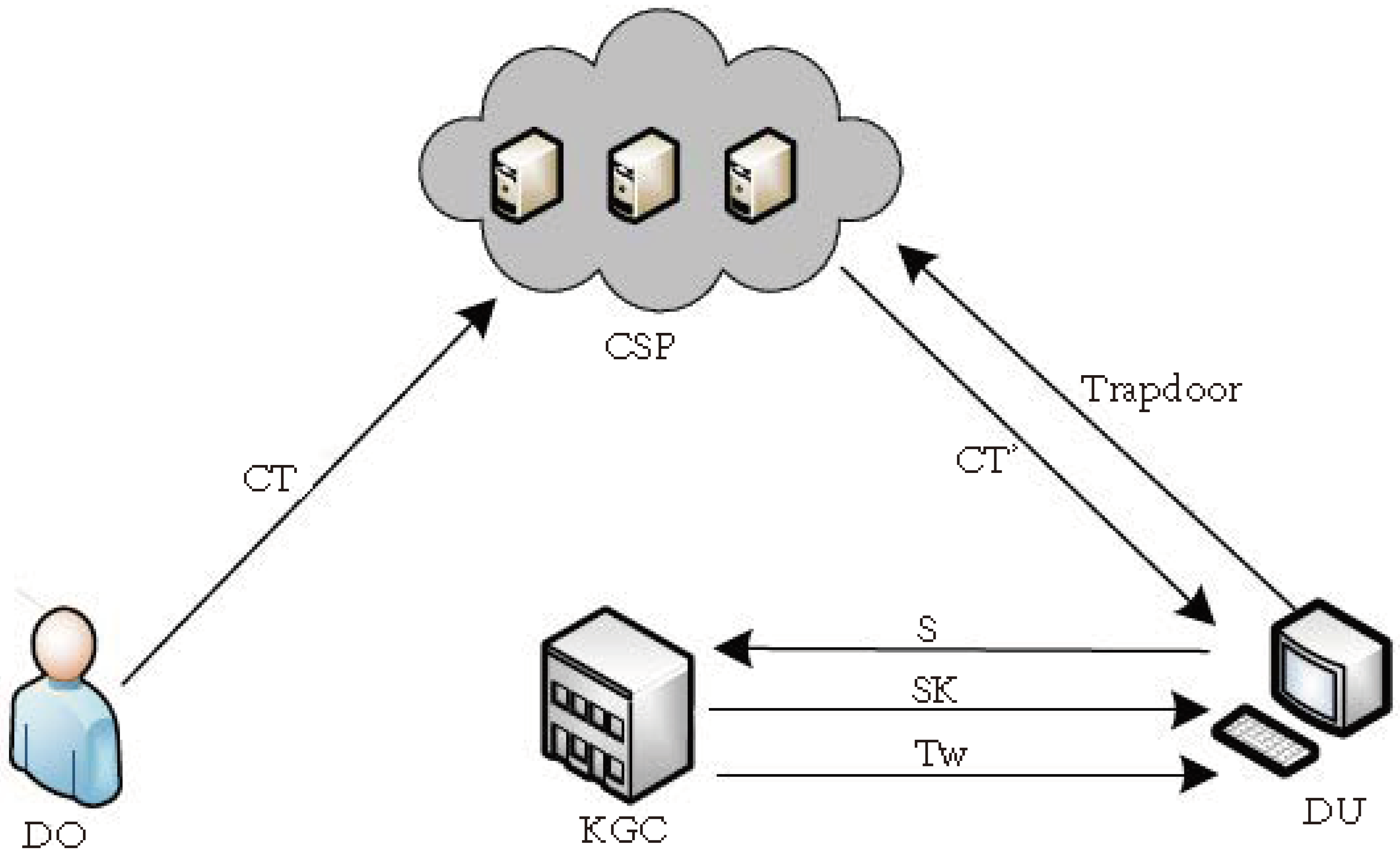
3. System Model and Security Model
3.1. System Model
- (1)
- System Initialization: This PPT algorithm is executed by the to initialize the global system. Taking security parameter λ as input, it outputs the system master key, , and the system public parameters, .
- (2)
- Encryption: This PPT algorithm is executed by the to perform encryption. Taking the system public parameters, , data m, keywords and access structure T as input, it outputs the ciphertext, , which is then uploaded to the cloud.
- (3)
- User Private Key Generation: This PPT algorithm is executed by the to generate a user private key. Taking the system public parameters, , the system master key, , and attribute set S as input, it outputs a user private key, .
- (4)
- Trapdoor Generation: This PPT algorithm is executed by the to generate a search trapdoor. Taking the system public parameters, , the user private key, , and keyword w as input, it outputs the trapdoor, .
- (5)
- Search and Transformation: This PPT algorithm is executed by the to perform search and transformation operations. Taking the system public parameters, , the keyword ciphertext, , and trapdoor as input, it outputs the search result and server-aided decrypted ciphertext and returns them to the search user.
- (6)
- Decryption: This PPT algorithm is executed by the to perform decryption. Taking the system public parameters, , the ciphertext, , and private key as input, it outputs plaintext data m.
3.2. Security Model
- (1)
- If attribute set S satisfies access tree , key queries of S are prohibited.
- (2)
- If attribute set S satisfies access tree , trapdoor queries with and are prohibited.
- (1)
- Encryption of data m, , and access structures T ( satisfies T) is not permitted.
- (2)
- Private key queries on attribute set are not permitted.
4. Construction of the SA-CP-SABE Scheme
- 1.
- System initialization: this algorithm selects two multiplicative groups with the same prime order q. We define bilinear map , and g is the generator of group . We choose four random numbers and compute , and . We define hash function . Finally, PKG publishes system parameters and the secret system master key . We use to denote the Lagrange coefficients of and .
- 2.
- Encryption: Given data and keyword , the DO selects a symmetric encryption algorithm and encryption key and encrypts m with algorithm and key represented as . Then, we define access structure T and encrypt and keyword according to T in the following steps:
- (1)
- We randomly select and calculate , , .
- (2)
- Using a top-down approach, we start from the root node, and for each node x, we select polynomial of degree . When x is the root node, we make . Otherwise, we let where is the parent of node x and is the index of node x. We let Y denote the set of all leaf nodes. Each leaf node y corresponds to a specific attribute value, which is denoted as . We compute .
- (3)
- Finally, we upload ciphertext to the cloud.
- 3.
- User Private Key Generation: Once the KGC receives a request from a data user (with attribute set S) to generate a key, it first randomly selects and calculates and . Then, we randomize and calculate . Finally, we send to the data user.
- 4.
- Trapdoor Generation: When the data user requests the search permission of keyword w from the KGC, the KGC randomly selects k and calculates and , and returns it to the data user. After receiving it, the data user calculates the trapdoor,and sends it to the cloud server.
- 5.
- Search and Transform: Upon receiving , the cloud first verifies whether the user’s attribute set S satisfies access control tree T in ciphertext . If not, it returns ⊥. Otherwise, the search is conducted as follows:
- (1)
- The cloud defines two recursive algorithms, and , which take as input ciphertext , trapdoor , attribute set S, and node x in access tree T and return the result as follows. The actual attribute is used to represent leaf node x.
- (i)
- If x is a leaf node and , then we define
- (ii)
- If x is a leaf node and , then we define , .
- (iii)
- If x is a non-terminal node, then we create the set where z is the left child of node x. When is less than the threshold , we make . Otherwise, we choose a subset of that satisfies , and denote the set by . Finally, we define
- (2)
- The cloud calls and to obtain and , respectively, where R is the root node.
- (3)
- Ciphertext Verification.The cloud server verifies whether holds.
- (i)
- If it holds, it implies that the keyword of the ciphertext matches the keyword in the trapdoor. Therefore, the cloud returns the ciphertext as follows:
- (ii)
- If it does not hold, it indicates that the ciphertext is not the one searched by the data user.In fact, here are
- 6.
- Decryption: The data user receives and calculates . Finally, the data user can obtain the plaintext .
5. Analysis of the SA-CP-SABE Scheme
5.1. Security Analysis
- (1)
- If attribute set S satisfies access tree , key queries of S are prohibited.
- (2)
- If attribute set S satisfies access tree , trapdoor queries with and are prohibited.
- (1)
- We randomly select and calculate
- (2)
- We calculate .
- (3)
- We return .
- (1)
- It is not possible to encrypt data m, and access structures T ( meets T).
- (2)
- Private key queries cannot be performed on attribute set .
5.2. Performance Analysis
5.2.1. Functionality Comparison
5.2.2. Storage Cost
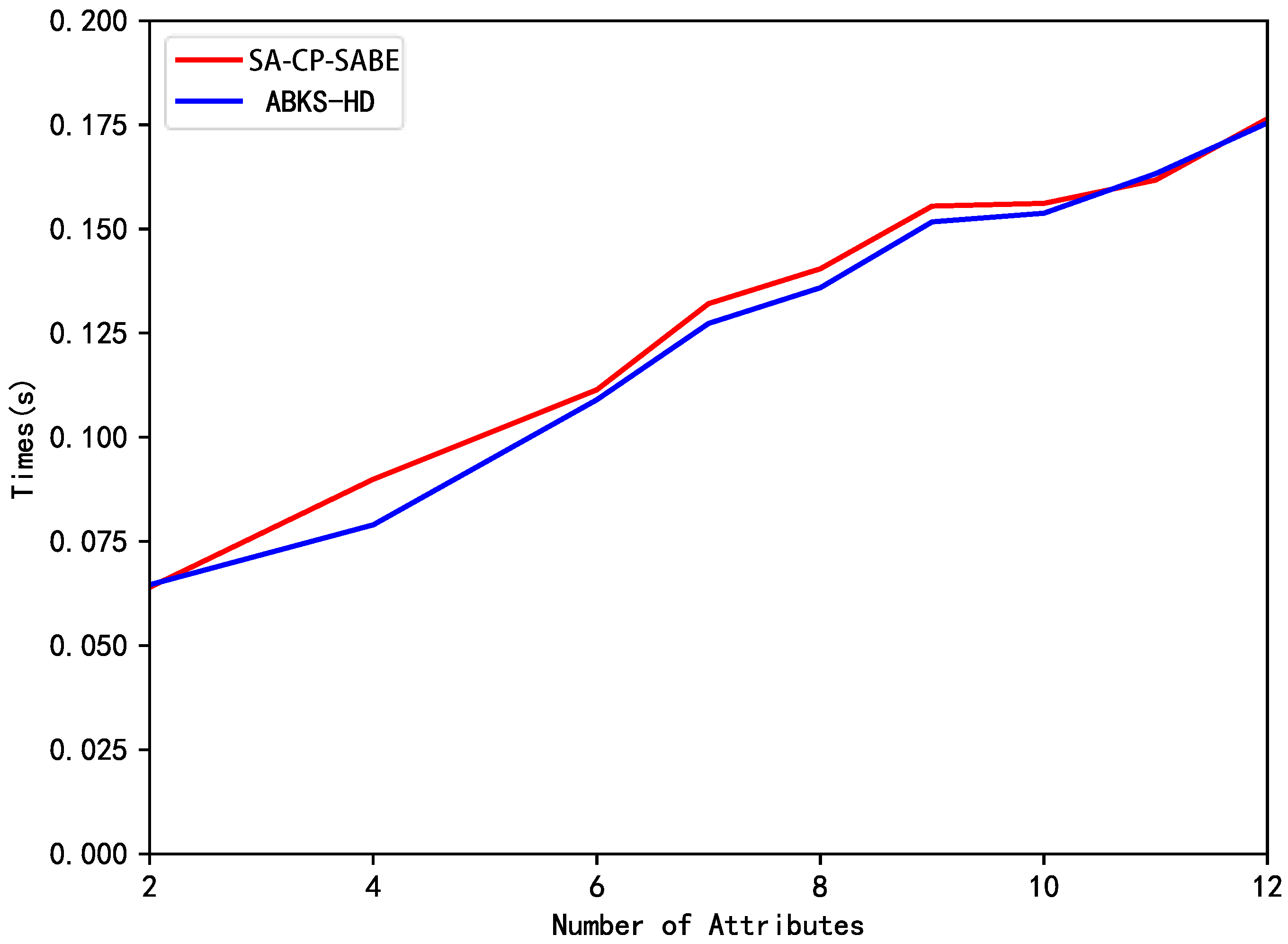
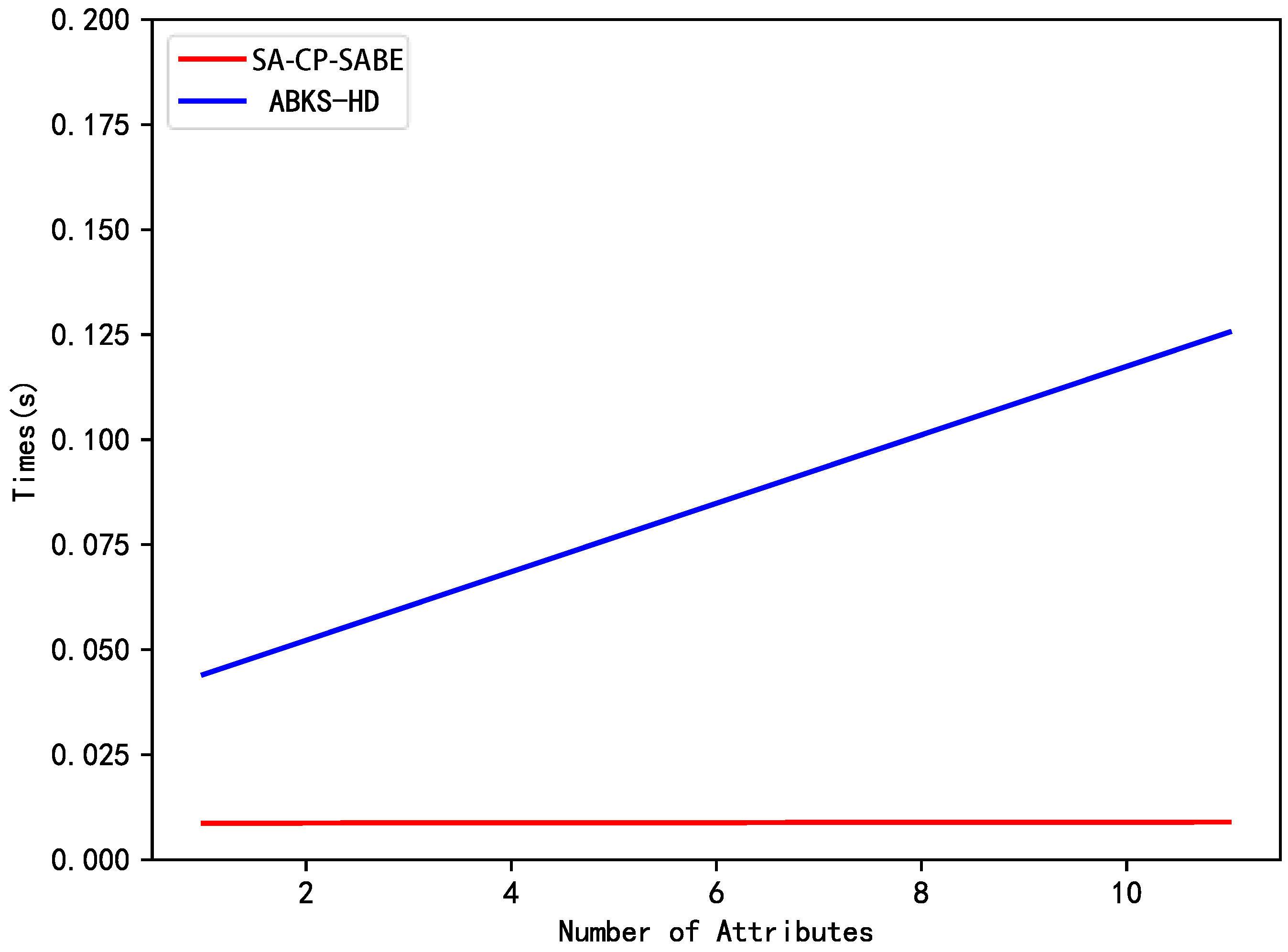
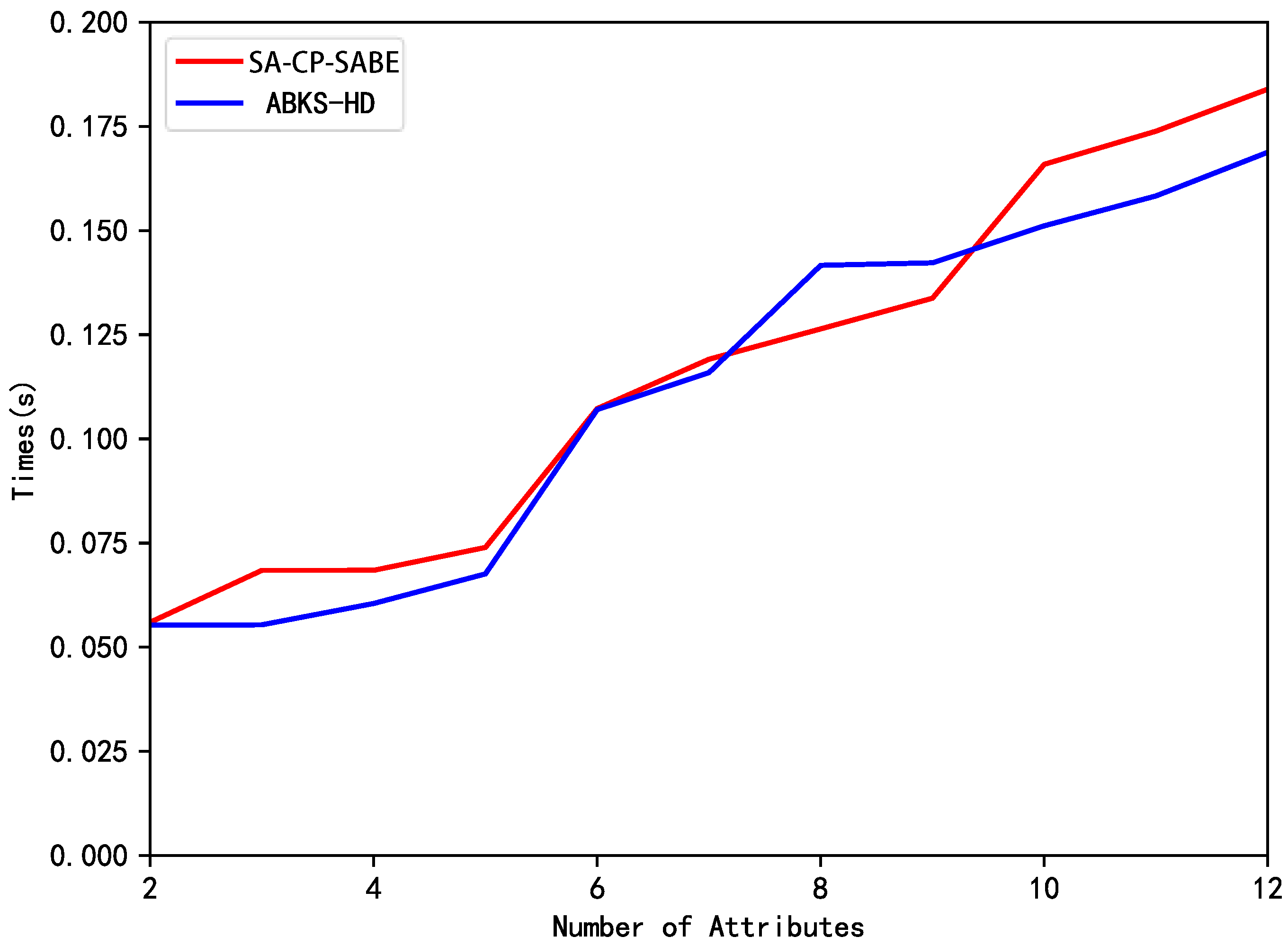
5.2.3. Computation Cost
5.2.4. Discussion
6. Conclusions
Author Contributions
Funding
Data Availability Statement
Conflicts of Interest
Abbreviations
| ABE | Attribute-Based Encryption |
| KP-ABE | Key-Policy Attribute-Based Encryption |
| CP-ABE | Ciphertext-Policy Attribute-Based Encryption |
| PEKS | Public Key Searchable Encryption |
| SABE | Searchable Attribute-Based Encryption |
| KGC | Key Generation Center |
| DO | Data Owner |
| DU | Data User |
| CSP | Cloud Server Provider |
References
- Mell, P.; Grance, T. The NIST Definition of Cloud Computing. Available online: http://nvlpubs.nist.gov/nistpubs/Legacy/SP/nistspecialpublication800-145.pdf (accessed on 7 May 2024).
- Tabrizchi, H.; Rafsanjani, M.K. A survey on security challenges in cloud computing: Issues, threats, and solutions. J. Supercomput. 2020, 76, 9493–9532. [Google Scholar] [CrossRef]
- Sahai, A.; Waters, B. Fuzzy Identity-Based Encryption. In Advances in Cryptology—EUROCRYPT 2005; Cramer, R., Ed.; Springer: Berlin/Heidelberg, Germany, 2005; pp. 457–473. [Google Scholar]
- Goyal, V.; Pandey, O.; Sahai, A.; Waters, B. Attribute-based encryption for fine-grained access control of encrypted data. In Proceedings of the 13th ACM Conference on Computer and Communications Security, OCT 2006, Alexandria, VA, USA, 30 October–3 November 2006. [Google Scholar] [CrossRef]
- Bethencourt, J.; Sahai, A.; Waters, B. Ciphertext-Policy Attribute-Based Encryption. In Proceedings of the 2007 IEEE Symposium on Security and Privacy (SP ’07), Oakland, CA, USA, 20–23 May 2007; pp. 321–334. [Google Scholar] [CrossRef]
- Wang, S.; Ye, J.; Zhang, Y. A keyword searchable attribute-based encryption scheme with attribute update for cloud storage. PLoS ONE 2018, 13, e0197318. [Google Scholar] [CrossRef] [PubMed]
- Li, H.; Jing, T. A lightweight fine-grained searchable encryption scheme in fog-based healthcare IoT networks. Wirel. Commun. Mob. Comput. 2019, 2019, 1019767. [Google Scholar] [CrossRef]
- Zhang, K.; Long, J.; Wang, X.; Dai, H.N.; Liang, K.; Imran, M. Lightweight Searchable Encryption Protocol for Industrial Internet of Things. IEEE Trans. Ind. Inform. 2021, 17, 4248–4259. [Google Scholar] [CrossRef]
- Miao, Y.; Tong, Q.; Choo, K.K.R.; Liu, X.; Deng, R.H.; Li, H. Secure Online/Offline Data Sharing Framework for Cloud-Assisted Industrial Internet of Things. IEEE Internet Things J. 2019, 6, 8681–8691. [Google Scholar] [CrossRef]
- Miao, Y.; Ma, J.; Liu, X.; Li, X.; Jiang, Q.; Zhang, J. Attribute-Based Keyword Search over Hierarchical Data in Cloud Computing. IEEE Trans. Serv. Comput. 2020, 13, 985–998. [Google Scholar] [CrossRef]
- Chen, D.; Cao, Z.; Dong, X. Online/offline ciphertext-policy attribute-based searchable encryption. J. Comput. Res. Dev. 2016, 53, 2365–2375. [Google Scholar] [CrossRef]
- Niu, S.; Xie, Y.; Yang, P.; Du, X. Cloud-Assisted Attribute-Based Searchable Encryption Scheme on Blockchain. J. Comput. Res. Dev. 2021, 50, 811–821. [Google Scholar] [CrossRef]
- Yin, H.; Zhang, J.; Xiong, Y.; Ou, L.; Li, F.; Liao, S.; Li, K. CP-ABSE: A Ciphertext-Policy Attribute-Based Searchable Encryption Scheme. IEEE Access 2019, 7, 5682–5694. [Google Scholar] [CrossRef]
- Li, J.; Lin, X.; Zhang, Y.; Han, J. KSF-OABE: Outsourced Attribute-Based Encryption with Keyword Search Function for Cloud Storage. IEEE Trans. Serv. Comput. 2017, 10, 715–725. [Google Scholar] [CrossRef]
- Wang, H.; Ning, J.; Huang, X.; Wei, G.; Poh, G.S.; Liu, X. Secure Fine-Grained Encrypted Keyword Search for E-Healthcare Cloud. IEEE Trans. Dependable Secur. Comput. 2021, 18, 1307–1319. [Google Scholar] [CrossRef]
- Bao, Y.; Qiu, W.; Cheng, X. Secure and lightweight fine-grained searchable data sharing for IoT-oriented and cloud-assisted smart healthcare system. IEEE Internet Things J. 2022, 9, 2513–2526. [Google Scholar] [CrossRef]
- Song, D.X.; Wagner, D.; Perrig, A. Practical techniques for searches on encrypted data. In Proceedings of the Proceeding 2000 IEEE Symposium on Security and Privacy, S&P 2000, Berkeley, CA, USA, 14–17 May 2000; pp. 44–55. [Google Scholar] [CrossRef]
- Boneh, D.; Di Crescenzo, G.; Ostrovsky, R.; Persiano, G. Public Key Encryption with Keyword Search. In Advances in Cryptology—EUROCRYPT 2004; Cachin, C., Camenisch, J.L., Eds.; Springer: Berlin/Heidelberg, Germany, 2004; pp. 506–522. [Google Scholar]
- Rhee, H.S.; Park, J.H.; Susilo, W.; Lee, D.H. Trapdoor security in a searchable public-key encryption scheme with a designated tester. J. Syst. Softw. 2010, 83, 763–771. [Google Scholar] [CrossRef]
- Yang, N.; Zhou, Q.; Xu, S. Public-Key Authenticated Encryption with Keyword Search without Pairings. J. Comput. Res. Dev. 2020, 57, 2125–2135. [Google Scholar] [CrossRef]
- Chen, R.; Mu, Y.; Yang, G.; Guo, F.; Huang, X.; Wang, X.; Wang, Y. Server-Aided Public Key Encryption With Keyword Search. IEEE Trans. Inf. Forensics Secur. 2016, 11, 2833–2842. [Google Scholar] [CrossRef]
- Yu, S.; Ren, K.; Lou, W.; Li, J. Defending against Key Abuse Attacks in KP-ABE Enabled Broadcast Systems. In Security and Privacy in Communication Networks; Chen, Y., Dimitriou, T.D., Zhou, J., Eds.; Springer: Berlin/Heidelberg, Germany, 2009; pp. 311–329. [Google Scholar]
- Wei, J.; Chen, X.; Huang, X.; Hu, X.; Susilo, W. RS-HABE: Revocable-Storage and Hierarchical Attribute-Based Access Scheme for Secure Sharing of e-Health Records in Public Cloud. IEEE Trans. Dependable Secur. Comput. 2021, 18, 2301–2315. [Google Scholar] [CrossRef]
- Liang, K.; Liu, J.K.; Lu, R.; Wong, D.S. Privacy Concerns for Photo Sharing in Online Social Networks. IEEE Internet Comput. 2015, 19, 58–63. [Google Scholar] [CrossRef]
- Li, S.; Xu, M. Attribute-based public encryption with keyword search. Chin. J. Comput. 2014, 37, 1017–1024. [Google Scholar]
- Zhou, R.; Zhang, X.; Du, X.; Wang, X.; Yang, G.; Guizani, M. File-centric multi-key aggregate keyword searchable encryption for industrial internet of things. IEEE Trans. Ind. Inform. 2018, 14, 3648–3658. [Google Scholar] [CrossRef]
- Lai, J.; Deng, R.H.; Guan, C.; Weng, J. Attribute-Based Encryption With Verifiable Outsourced Decryption. IEEE Trans. Inf. Forensics Secur. 2013, 8, 1343–1354. [Google Scholar] [CrossRef]
- Delerablée, C.; Pointcheval, D. Dynamic Threshold Public-Key Encryption. In Advances in Cryptology—CRYPTO 2008; Wagner, D., Ed.; Springer: Berlin/Heidelberg, Germany, 2008; pp. 317–334. [Google Scholar]

| Schemes | Consistent with Data Access and Search Permissions | Supporting Trapdoor Queries | Based on the Strategy | Server-Aided Decryption |
|---|---|---|---|---|
| Literature [6] | × | √ | CP-ABE | √ |
| LFSE [7] | × | √ | CP-ABE | √ |
| LSABE [8] | × | - | CP-ABE | √ |
| DSF [9] | √ | √ | CP-ABE | √ |
| ABKS-HD [10] | √ | √ | CP-ABE | √ |
| Literature [12] | √ | × | CP-ABE | √ |
| Literature [11] | √ | × | CP-ABE | √ |
| Literature [13] | √ | √ | CP-ABE | × |
| LABSE [16] | √ | √ | KP-ABE | √ |
| KSF-OABE [14] | × | √ | KP-ABE | √ |
| FKS-HPABE [15] | √ | √ | CP-ABE | × |
| Literature [25] | - | √ | KP-ABE | × |
| Notation | Meaning | Notation | Meaning |
|---|---|---|---|
| q | a large prime | system parameters | |
| denotes the residue group modulo, | T | the access structure | |
| two multiplicative cyclic groups with the equal prime order p | x | a node of the access tree T | |
| e | the bilinear pair map between the two groups | an attribute associated with the leaf node x in the access tree | |
| g | the generator of the group | the original ciphertext/the transformed ciphertext | |
| two elements of the group | S | the attribute set | |
| the system master key/the user’s private key | the search trapdoor |
| Schemes | Ciphertext Indistinguishability | Trapdoor Indistinguishability | Keyword Guessing Attack | Based on the Strategy | Server-Aided Decryption |
|---|---|---|---|---|---|
| DSF [9] | No | No | Yes | CP-ABE | Yes |
| Literature [13] | No | No | Yes | CP-ABE | No |
| ABKS-HD [10] | No | No | Yes | CP-ABE | Yes |
| LABSE [16] | No | No | Yes | KP-ABE | Yes |
| Ours | Yes | Yes | No | CP-ABE | Yes |
| Schemes | Size of User Key | Size of Ciphertext | Size of Trapdoor |
|---|---|---|---|
| DSF [9] | |||
| ABKS-HD [10] | |||
| Ours |
| Stage | ABKS-HD [10] | Ours |
|---|---|---|
| Encryption | ||
| Trapdoor Generation | ||
| Search and Transform | ||
| User Decryption |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2024 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).
Share and Cite
Wen, J.; Li, H.; Liu, L.; Lan, C. Enhancing Security and Efficiency: A Fine-Grained Searchable Scheme for Encryption of Big Data in Cloud-Based Smart Grids. Mathematics 2024, 12, 1512. https://doi.org/10.3390/math12101512
Wen J, Li H, Liu L, Lan C. Enhancing Security and Efficiency: A Fine-Grained Searchable Scheme for Encryption of Big Data in Cloud-Based Smart Grids. Mathematics. 2024; 12(10):1512. https://doi.org/10.3390/math12101512
Chicago/Turabian StyleWen, Jing, Haifeng Li, Liangliang Liu, and Caihui Lan. 2024. "Enhancing Security and Efficiency: A Fine-Grained Searchable Scheme for Encryption of Big Data in Cloud-Based Smart Grids" Mathematics 12, no. 10: 1512. https://doi.org/10.3390/math12101512
APA StyleWen, J., Li, H., Liu, L., & Lan, C. (2024). Enhancing Security and Efficiency: A Fine-Grained Searchable Scheme for Encryption of Big Data in Cloud-Based Smart Grids. Mathematics, 12(10), 1512. https://doi.org/10.3390/math12101512






