Hybrid Fuzzy Rule Algorithm and Trust Planning Mechanism for Robust Trust Management in IoT-Embedded Systems Integration
Abstract
1. Introduction
2. Literature Survey
2.1. Review Based on Internet of Things
2.2. Review Based on Embedded Systems
2.3. Review Based on Fuzzy Rule Algorithms
2.4. Reviews Based on Trust Planning Mechanism
3. Problem Statement
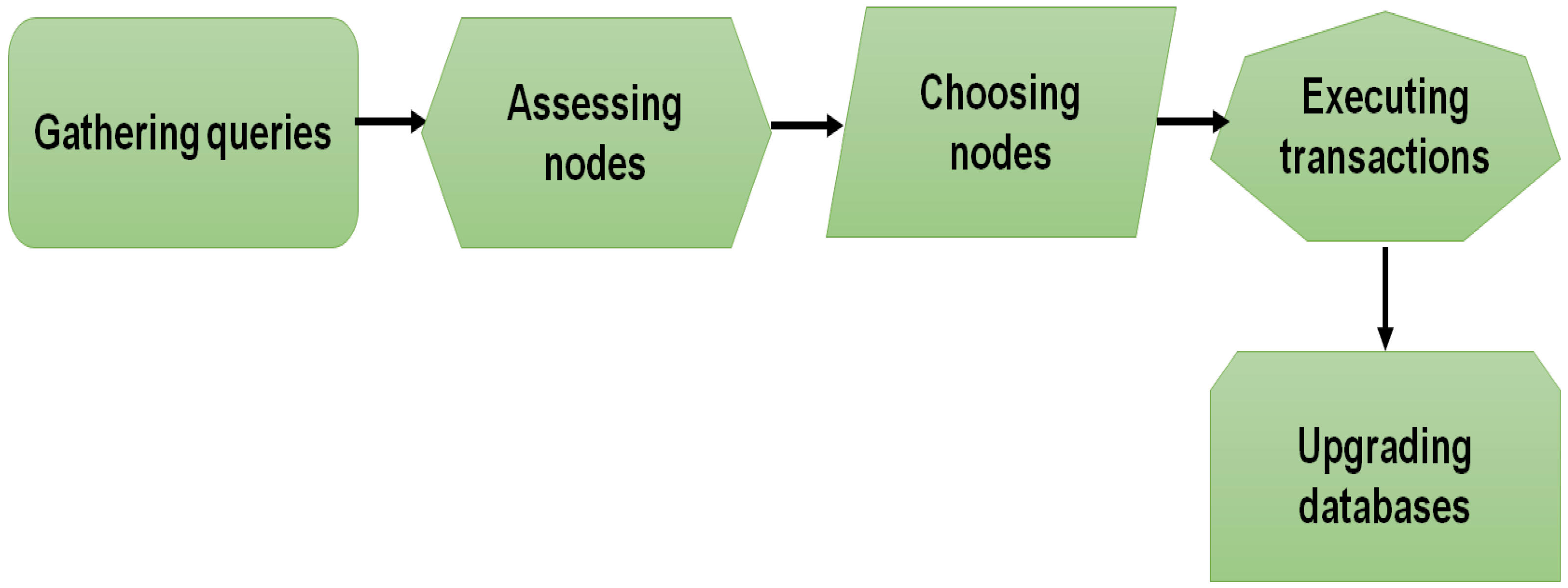
4. Research Methodology
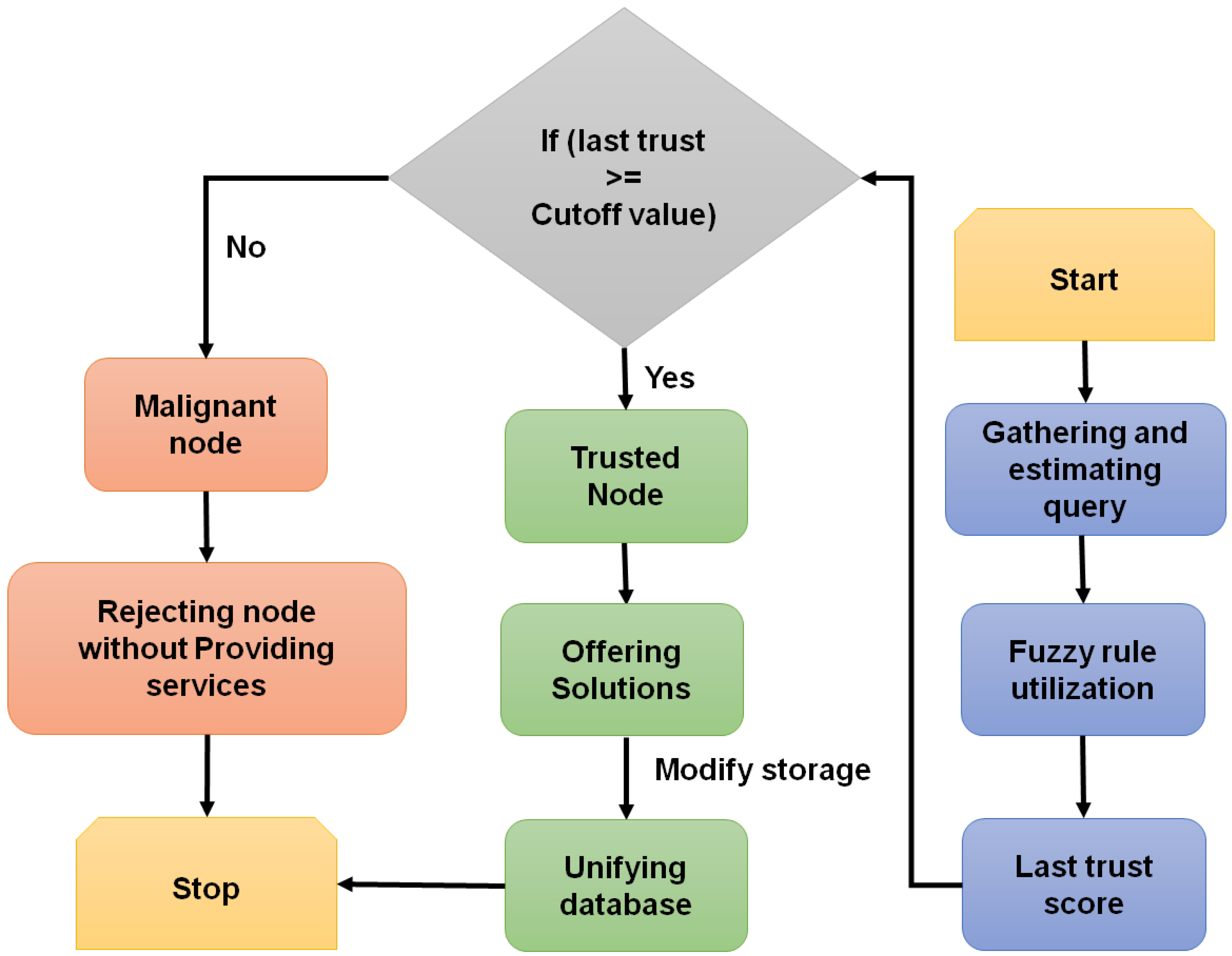
4.1. Fuzzy Rule Algorithm (FRA)
| Algorithm 1: Trust node prediction |
| Configuration -one Node for each query FC: Collection of fuzzy scores = First trust score = Last trust score = Prior determined cutoff score = Trusted node Outcome: Trusted Node Process Start then If Else if End if End if → Collection If then Solutions End if End |
| Algorithm 2: Malignant nodes detection |
| Configuration = Collection of fuzzy scores = Prior determined cutoff score = Novel trust score for malignant node detection U: Trust value up/down (0.05) per request Outcome: Malignant node Procedure: Initialize then then then Else End |
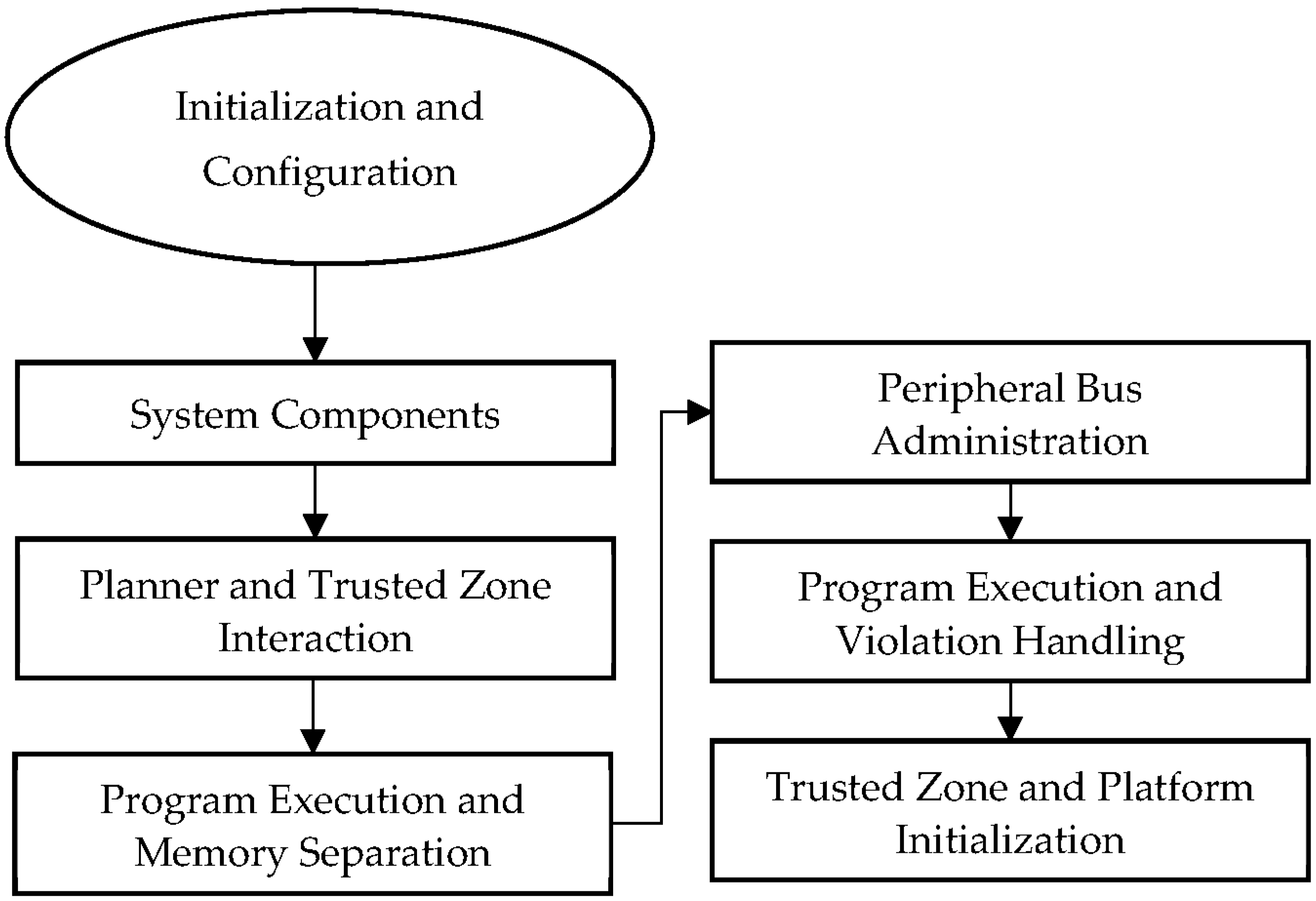
4.2. Trust Planning Mechanism (TPM)
5. Result and Discussion
5.1. Trust Prediction Accuracy (%)
5.2. Throughput (Mbps)
5.3. Latency (ms)
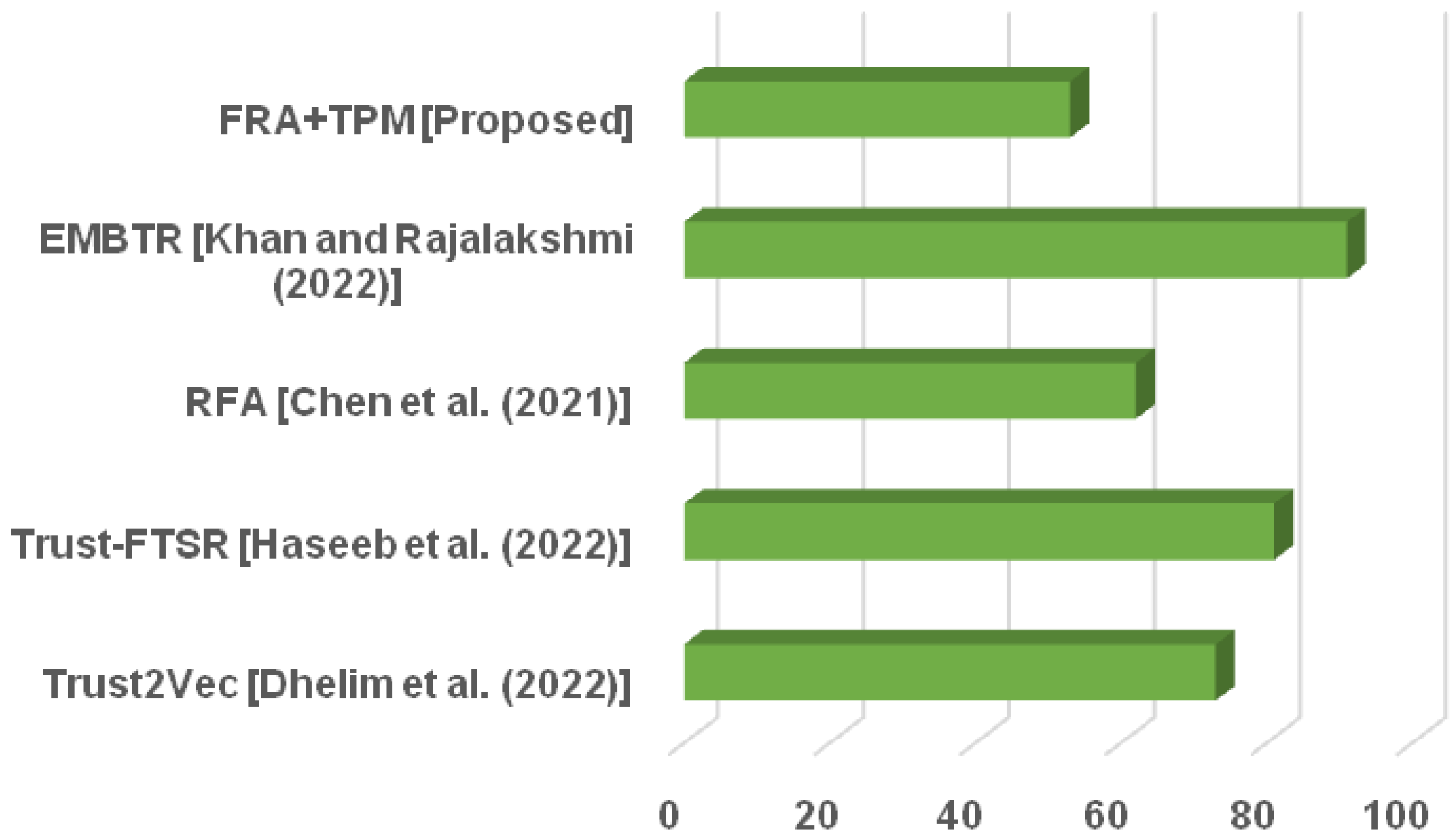
5.4. Energy Consumption (%)
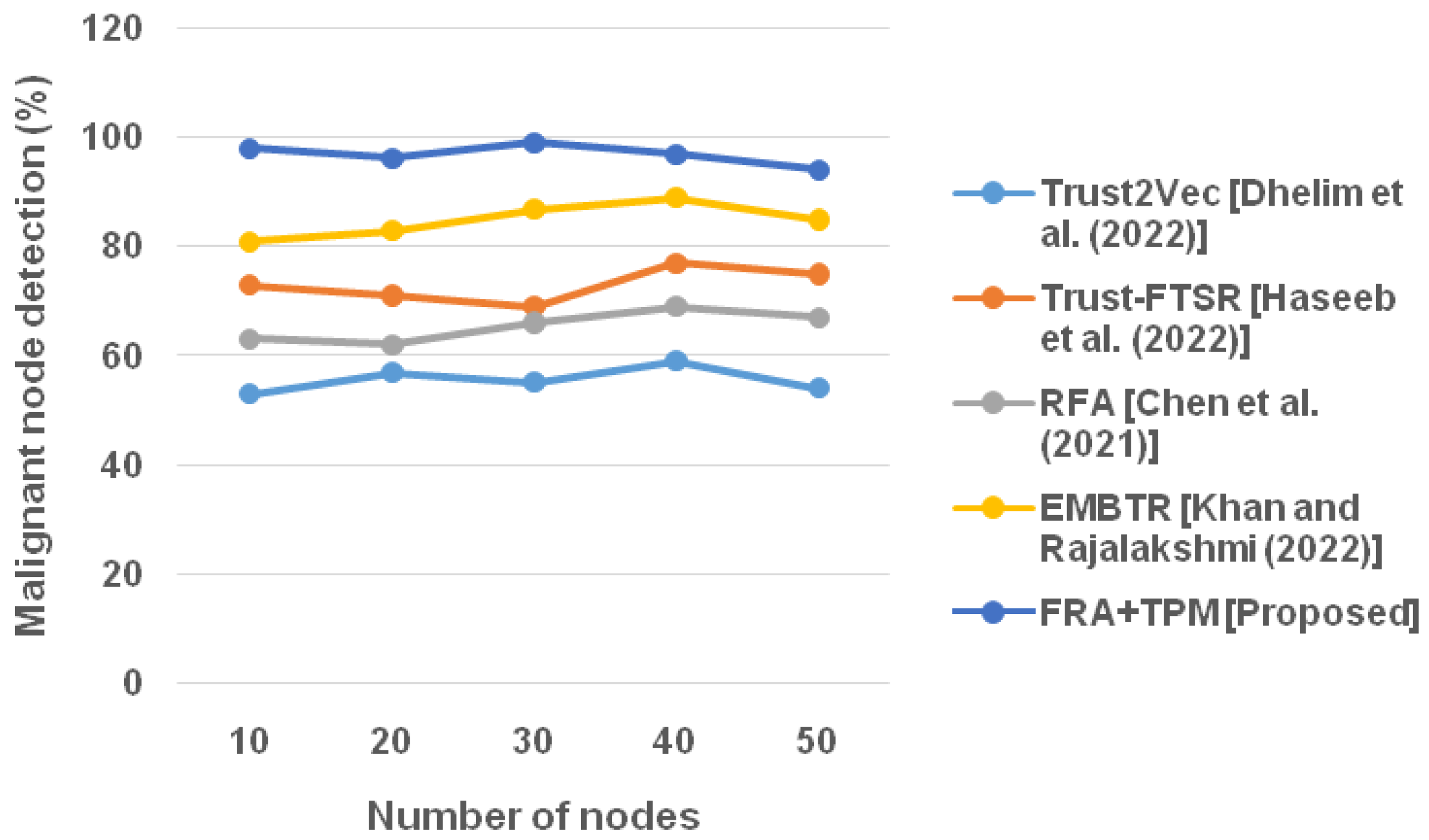
5.5. Malignant Node Detection (%)
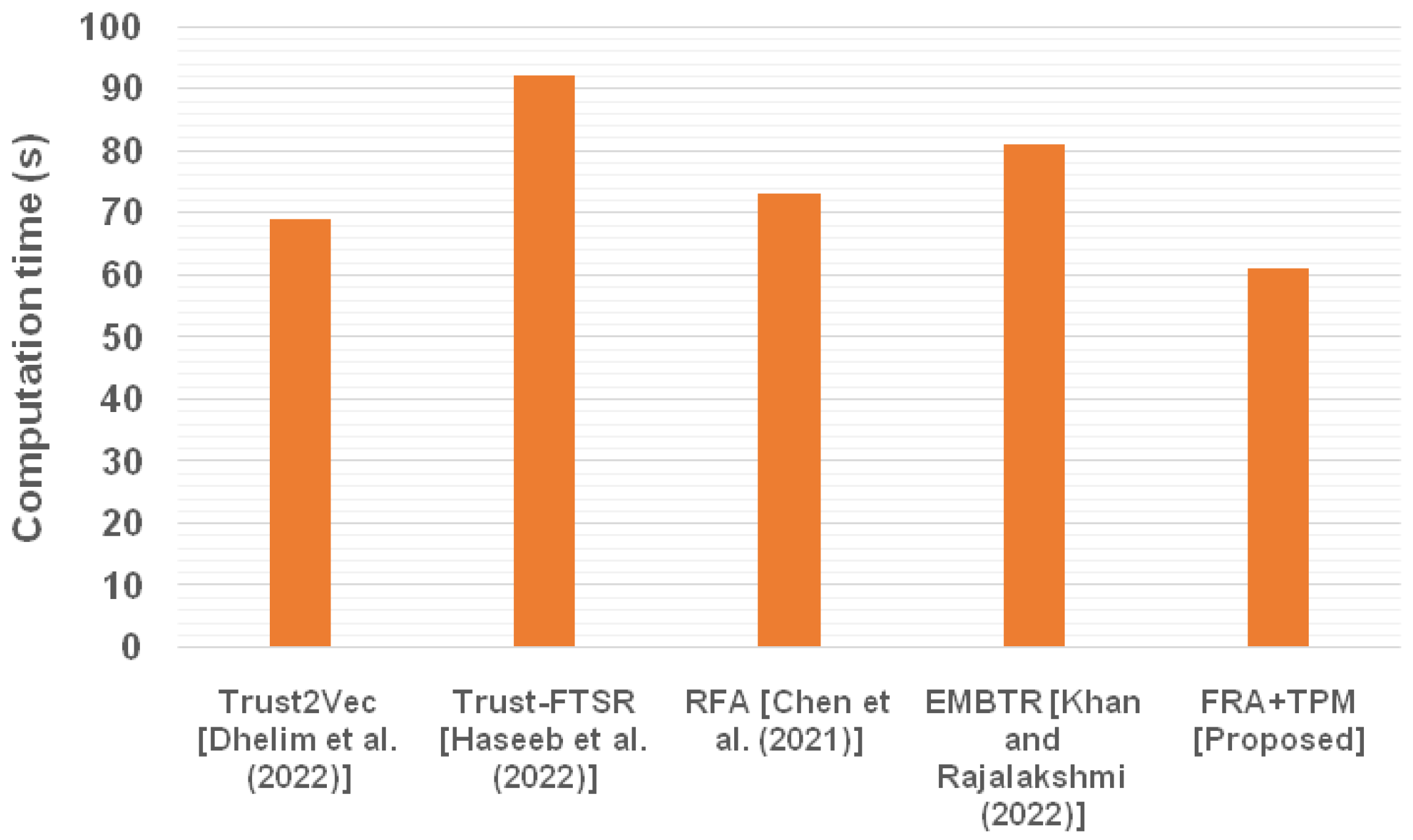
5.6. Computation Time (s)
6. Discussion
7. Discussion of Analysis of the Presented Fuzzy Method with the Exact Method
8. Conclusions
- The integration of the FRA and trust planning mechanism offers enhanced trust management capabilities in IoT-embedded systems. By incorporating fuzzy logic, the approach effectively handles uncertainty, imprecision, and complex relationships among entities, enabling more accurate and adaptive trust assessment. This can provide decision makers with valuable insights into the trustworthiness of IoT devices and facilitate informed decision making processes.
- The proposed approach’s ability to adapt to changing conditions and handle uncertainties contributes to the robustness of trust management in dynamic IoT environments. The fuzzy-logic-based reasoning allows for flexible adjustments to evolving trust relationships and varying levels of trustworthiness, ensuring the system’s resilience against environmental changes and potential threats.
- It is important to consider the computational complexity associated with the integration of FRA and trust planning mechanism. The process of fuzzy inference, rule evaluation, and defuzzification can introduce computational overhead, especially for large-scale IoT deployments or real-time applications. Further research and optimization techniques may be needed to mitigate potential performance issues.
- The proposed approach’s applicability may vary depending on the specific characteristics and requirements of the IoT-embedded systems integration. The effectiveness of the FRA and trust planning mechanism may depend on the availability and quality of input data, the complexity of trust relationships, and the nature of the IoT environment. Thorough evaluation and validation of the approach in various scenarios would help assess its suitability for different contexts.
- The integration of the hybrid fuzzy rule algorithm and trust planning mechanism offers valuable insights into trust management in IoT-embedded systems. The approach enhances trust assessment, provides robustness in dynamic environments, and enables decision makers to make informed choices. However, the computational complexity and context-specific limitations should be considered when applying the proposed approach, highlighting the need for further research and validation to fully realize its potential in practical IoT deployments.
Author Contributions
Funding
Data Availability Statement
Conflicts of Interest
References
- Lv, Z.; Song, H. Mobile Internet of Things Under Data Physical Fusion Technology. IEEE Internet Things J. 2019, 7, 4616–4624. [Google Scholar] [CrossRef]
- Lv, Z.; Cheng, C.; Song, H. Digital Twins Based on Quantum Networking. IEEE Netw. 2022, 36, 88–93. [Google Scholar] [CrossRef]
- Kumar, R.; Sharma, R. Leveraging blockchain for ensuring trust in IoT: A survey. J. King Saud Univ. Comput. Inf. Sci. 2022, 34, 8599–8622. [Google Scholar] [CrossRef]
- Lv, Z.; Qiao, L.; Li, J.; Song, H. Deep-Learning-Enabled Security Issues in the Internet of Things. IEEE Internet Things J. 2020, 8, 9531–9538. [Google Scholar] [CrossRef]
- Qu, Z.; Zhang, Z.; Liu, B.; Tiwari, P.; Ning, X.; Muhammad, K. Quantum detectable Byzantine agreement for distributed data trust management in blockchain. Inf. Sci. 2023, 637, 118909. [Google Scholar] [CrossRef]
- Rana, K.; Singh, A.V.; Vijaya, P. Recent Trust Management Models for Secure IoT Ecosystem. Int. J. Intell. Syst. Appl. Eng. 2022, 10, 23–33. [Google Scholar]
- Lv, Z.; Wu, J.; Li, Y.; Song, H. Cross-Layer Optimization for Industrial Internet of Things in Real Scene Digital Twins. IEEE Internet Things J. 2022, 9, 15618–15629. [Google Scholar] [CrossRef]
- Dai, X.; Xiao, Z.; Jiang, H.; Alazab, M.; Lui, J.C.S.; Dustdar, S.; Liu, J. Task Co-Offloading for D2D-Assisted Mobile Edge Computing in Industrial Internet of Things. IEEE Trans. Ind. Inform. 2022, 19, 480–490. [Google Scholar] [CrossRef]
- Liu, Y.; Yu, W.; Rahayu, W.; Dillon, T. An Evaluative Study on IoT ecosystem for Smart Predictive Maintenance (IoT-SPM) in Manufacturing: Multi-view Requirements and Data Quality. IEEE Internet Things J. 2023, 1. [Google Scholar] [CrossRef]
- Babaei, A.; Khedmati, M.; Jokar, M.R.A.; Tirkolaee, E.B. Designing an integrated blockchain-enabled supply chain network under uncertainty. Sci. Rep. 2023, 13, 1–19. [Google Scholar] [CrossRef]
- Mazumdar, H.; Kaushik, A.; Gohel, H.A. To mitigate primary user emulation attack trajectory using cognitive single carrier frequency division multiple access approaches: Towards next generation green IoT. Eng. Rep. 2023, e12672. [Google Scholar] [CrossRef]
- Mishra, N.; Pandya, S. Internet of Things Applications, Security Challenges, Attacks, Intrusion Detection, and Future Visions: A Systematic Review. IEEE Access 2021, 9, 59353–59377. [Google Scholar] [CrossRef]
- Praveena, J.; Arivazhagan; Reddy, P.V.P. Blockchain based sensor system design for embedded IoT. J. Comput. Inf. Syst. 2023, 1–18. [Google Scholar] [CrossRef]
- Din, I.U.; Bano, A.; Awan, K.A.; Almogren, A.; Altameem, A.; Guizani, M. LightTrust: Lightweight Trust Management for Edge Devices in Industrial Internet of Things. IEEE Internet Things J. 2021, 10, 2776–2783. [Google Scholar] [CrossRef]
- Bitencourt, H.V.; de Souza, L.A.F.; Santos, M.C.D.; Silva, R.; de Lima e Silva, P.C.; Guimarães, F.G. Combining embeddings and fuzzy time series for high-dimensional time series forecasting in internet of energy applications. Energy 2023, 271, 127072. [Google Scholar] [CrossRef]
- Shi, P.; Wang, H.; Yang, S.; Chen, C.; Yang, W. Blockchain-based trusted data sharing among trusted stakeholders in IoT. Softw. Pract. Exp. 2019, 51, 2051–2064. [Google Scholar] [CrossRef]
- Fahim, M.; El Mhouti, A.; Boudaa, T.; Jakimi, A. Modeling and implementation of a low-cost IoT-smart weather monitoring station and air quality assessment based on fuzzy inference model and MQTT protocol. Model. Earth Syst. Environ. 2023, 1–18. [Google Scholar] [CrossRef]
- Diwan, T.D.; Choubey, S.; Hota, H.S.; Goyal, S.B.; Jamal, S.S.; Shukla, P.K.; Tiwari, B. Feature Entropy Estimation (FEE) for Malicious IoT Traffic and Detection Using Machine Learning. Mob. Inf. Syst. 2021, 2021, 1–13. [Google Scholar] [CrossRef]
- Abawajy, J.; Darem, A.; Alhashmi, A.A. Feature Subset Selection for Malware Detection in Smart IoT Platforms. Sensors 2021, 21, 1374. [Google Scholar] [CrossRef]
- Zheng, W.; Deng, P.; Gui, K.; Wu, X. An Abstract Syntax Tree based static fuzzing mutation for vulnerability evolution analysis. Inf. Softw. Technol. 2023, 158, 107194. [Google Scholar] [CrossRef]
- Gong, J.; Rezaeipanah, A. A fuzzy delay-bandwidth guaranteed routing algorithm for video conferencing services over SDN networks. Multimed. Tools Appl. 2023, 1–30. [Google Scholar] [CrossRef] [PubMed]
- Rey, V.; Sánchez, P.M.S.; Celdrán, A.H.; Bovet, G. Federated learning for malware detection in IoT devices. Comput. Netw. 2022, 204, 108693. [Google Scholar] [CrossRef]
- Alkahtani, H.; Aldhyani, T.H.H. Artificial Intelligence Algorithms for Malware Detection in Android-Operated Mobile Devices. Sensors 2022, 22, 2268. [Google Scholar] [CrossRef] [PubMed]
- Dhelim, S.; Aung, N.; Kechadi, M.T.; Ning, H.; Chen, L.; Lakas, A. Trust2Vec: Large-Scale IoT Trust Management System Based on Signed Network Embeddings. IEEE Internet Things J. 2022, 10, 553–562. [Google Scholar] [CrossRef]
- Haseeb, K.; Saba, T.; Rehman, A.; Ahmed, Z.; Song, H.H.; Wang, H.H. Trust Management With Fault-Tolerant Supervised Routing for Smart Cities Using Internet of Things. IEEE Internet Things J. 2022, 9, 22608–22617. [Google Scholar] [CrossRef]
- Chen, G.; Zeng, F.; Zhang, J.; Lu, T.; Shen, J.; Shu, W. An adaptive trust model based on recommendation filtering algorithm for the Internet of Things systems. Comput. Netw. 2021, 190, 107952. [Google Scholar] [CrossRef]
- Khan, A.F.; Rajalakshmi, C.N. A multi-attribute based trusted routing for embedded devices in MANET-IoT. Microprocess. Microsyst. 2022, 89, 104446. [Google Scholar] [CrossRef]
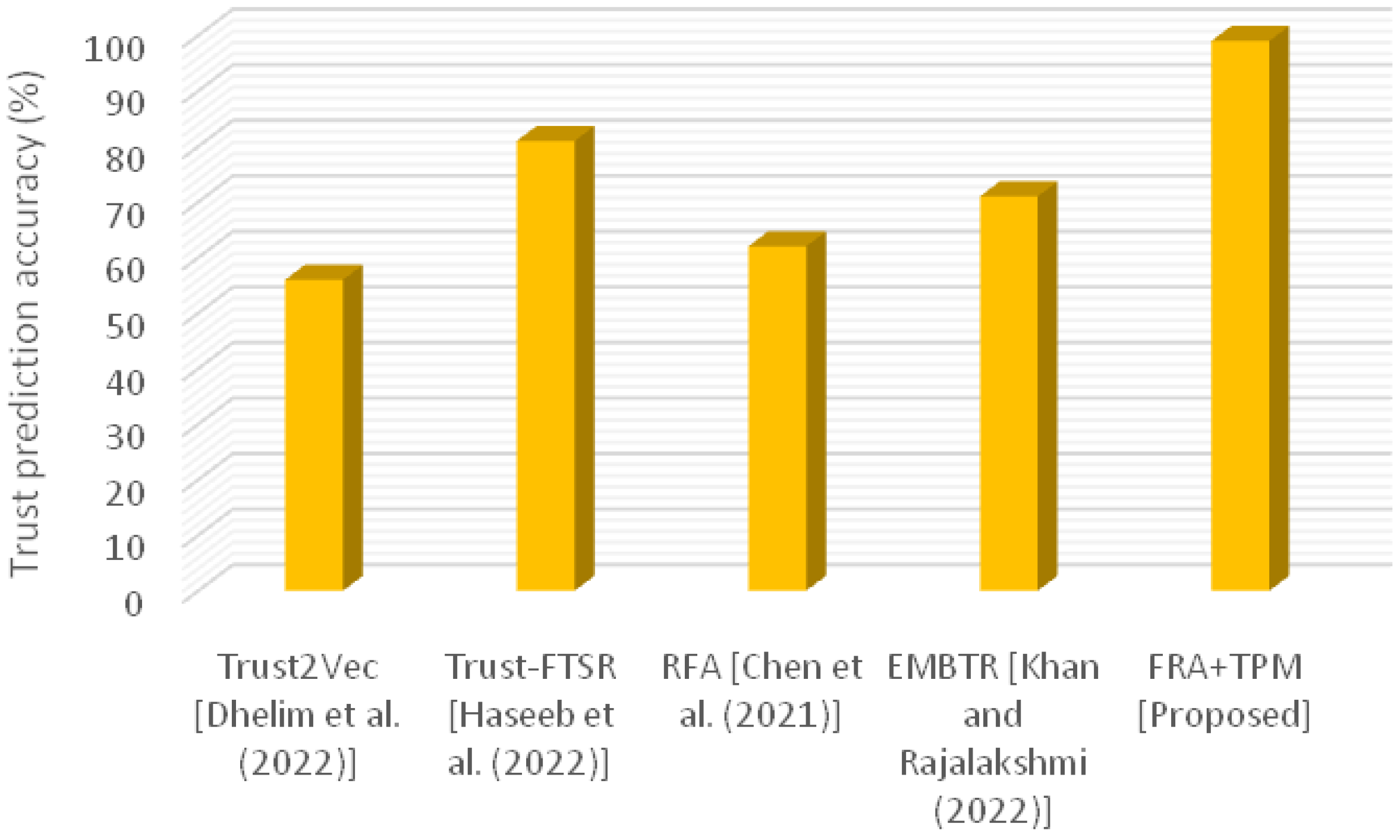


| Methods | Trust Prediction Accuracy (%) |
|---|---|
| Trust2Vec [24] | 56 |
| Trust-FTSR [25] | 81 |
| RFA [26] | 62 |
| EMBTR [27] | 71 |
| FRA + TPM [Proposed] | 99 |
| Number of Nodes | Throughput (Mbps) | ||||
|---|---|---|---|---|---|
| Trust2Vec [24] | Trust-FTSR [25] | RFA [26] | EMBTR [27] | FRA + TPM [Proposed] | |
| 10 | 3.2 | 6.2 | 9.2 | 5.9 | 10 |
| 20 | 3.1 | 6.9 | 8.1 | 4.5 | 9.7 |
| 30 | 2.6 | 6.2 | 8 | 4.3 | 8.2 |
| 40 | 1.5 | 6 | 7.3 | 4.1 | 9.9 |
| 50 | 1 | 5.3 | 7.5 | 4 | 9 |
| Number of Nodes | Latency (ms) | ||||
|---|---|---|---|---|---|
| Trust2Vec [24] | Trust-FTSR [25] | RFA [26] | EMBTR [27] | FRA + TPM [Proposed] | |
| 10 | 7 | 9.1 | 6.3 | 3.3 | 2.3 |
| 20 | 7.1 | 6.4 | 6.7 | 4.1 | 2 |
| 30 | 8.3 | 5.3 | 6.1 | 4 | 1.5 |
| 40 | 9.3 | 7.9 | 6 | 5 | 1.1 |
| 50 | 6.3 | 8.9 | 5 | 5.2 | 1.7 |
| Methods | Energy Consumption (%) |
|---|---|
| Trust2Vec [24] | 73 |
| Trust-FTSR [25] | 81 |
| RFA [26] | 62 |
| EMBTR [27] | 91 |
| FRA + TPM [Proposed] | 53 |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2023 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).
Share and Cite
Reddy, N.V.R.; Padmaja, P.; Mahdal, M.; Seerangan, S.; Vimal, V.; Talasila, V.; Cepova, L. Hybrid Fuzzy Rule Algorithm and Trust Planning Mechanism for Robust Trust Management in IoT-Embedded Systems Integration. Mathematics 2023, 11, 2546. https://doi.org/10.3390/math11112546
Reddy NVR, Padmaja P, Mahdal M, Seerangan S, Vimal V, Talasila V, Cepova L. Hybrid Fuzzy Rule Algorithm and Trust Planning Mechanism for Robust Trust Management in IoT-Embedded Systems Integration. Mathematics. 2023; 11(11):2546. https://doi.org/10.3390/math11112546
Chicago/Turabian StyleReddy, Nagireddy Venkata Rajasekhar, Pydimarri Padmaja, Miroslav Mahdal, Selvaraj Seerangan, Vrince Vimal, Vamsidhar Talasila, and Lenka Cepova. 2023. "Hybrid Fuzzy Rule Algorithm and Trust Planning Mechanism for Robust Trust Management in IoT-Embedded Systems Integration" Mathematics 11, no. 11: 2546. https://doi.org/10.3390/math11112546
APA StyleReddy, N. V. R., Padmaja, P., Mahdal, M., Seerangan, S., Vimal, V., Talasila, V., & Cepova, L. (2023). Hybrid Fuzzy Rule Algorithm and Trust Planning Mechanism for Robust Trust Management in IoT-Embedded Systems Integration. Mathematics, 11(11), 2546. https://doi.org/10.3390/math11112546






