Preliminaries of Orthogonal Layered Defence Using Functional and Assurance Controls in Industrial Control Systems
Abstract
1. Introduction
2. ICS Components
2.1. Software
2.2. ICS vs. IT Environments
3. Threats and Defence Technologies in Industrial Control Systems
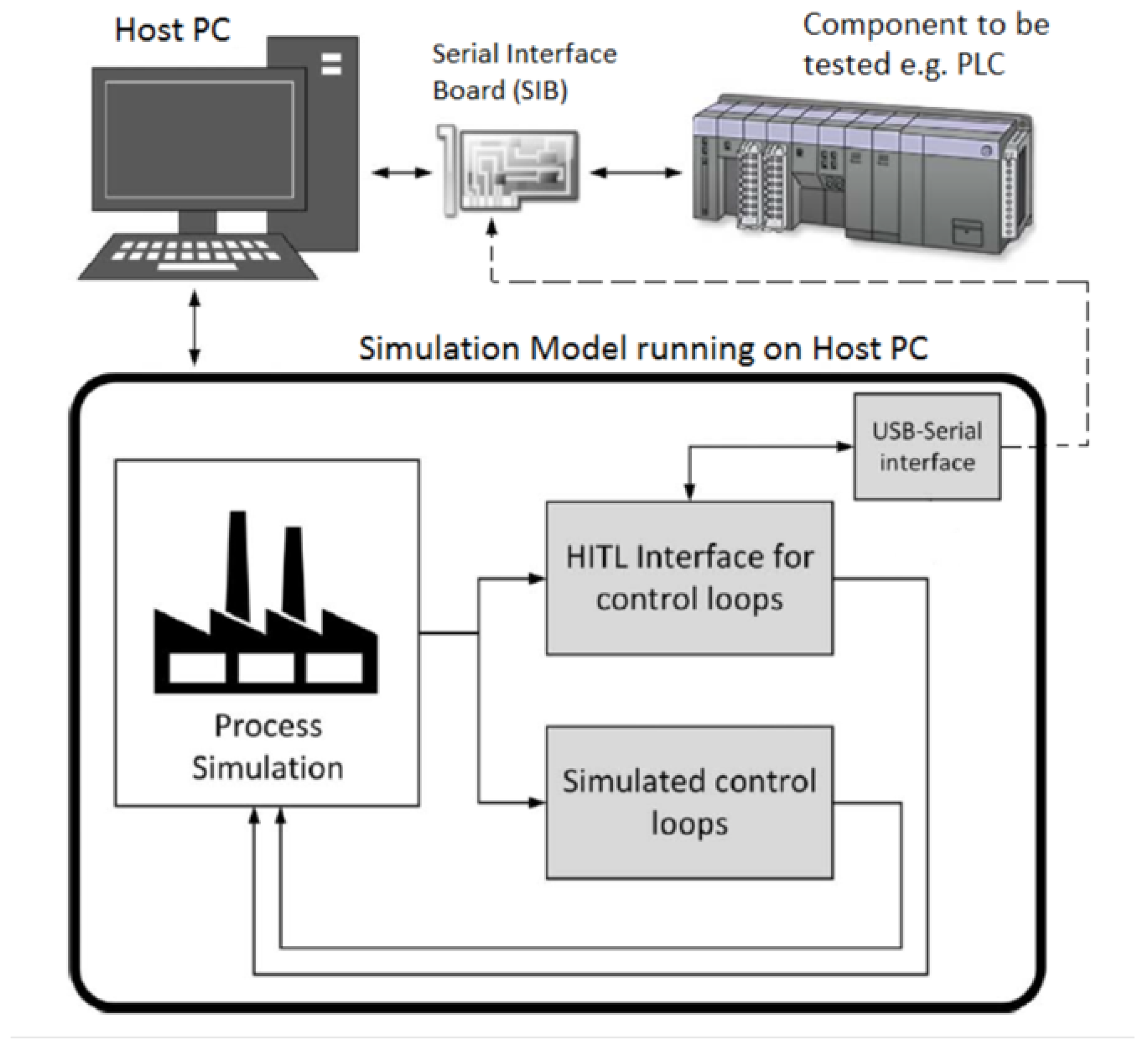
3.1. Hardware-in-the-Loop Testbeds
3.2. Virtual SCADA (VSCADA) Testbeds
- Scalability: You should be able to have a scalable environment while simultaneously supporting interaction with multiple users.
- Standardisation: The environment’s virtual model must integrate various communication protocols, such as Modbus and DNP3.
- Reconfigurability: The environment’s ability to simulate several network topologies and physical devices must be maintained.
- Effective virtualisation: The environment must provide an accurate representation of the physical system. This typically covers all main behavioural characteristics.
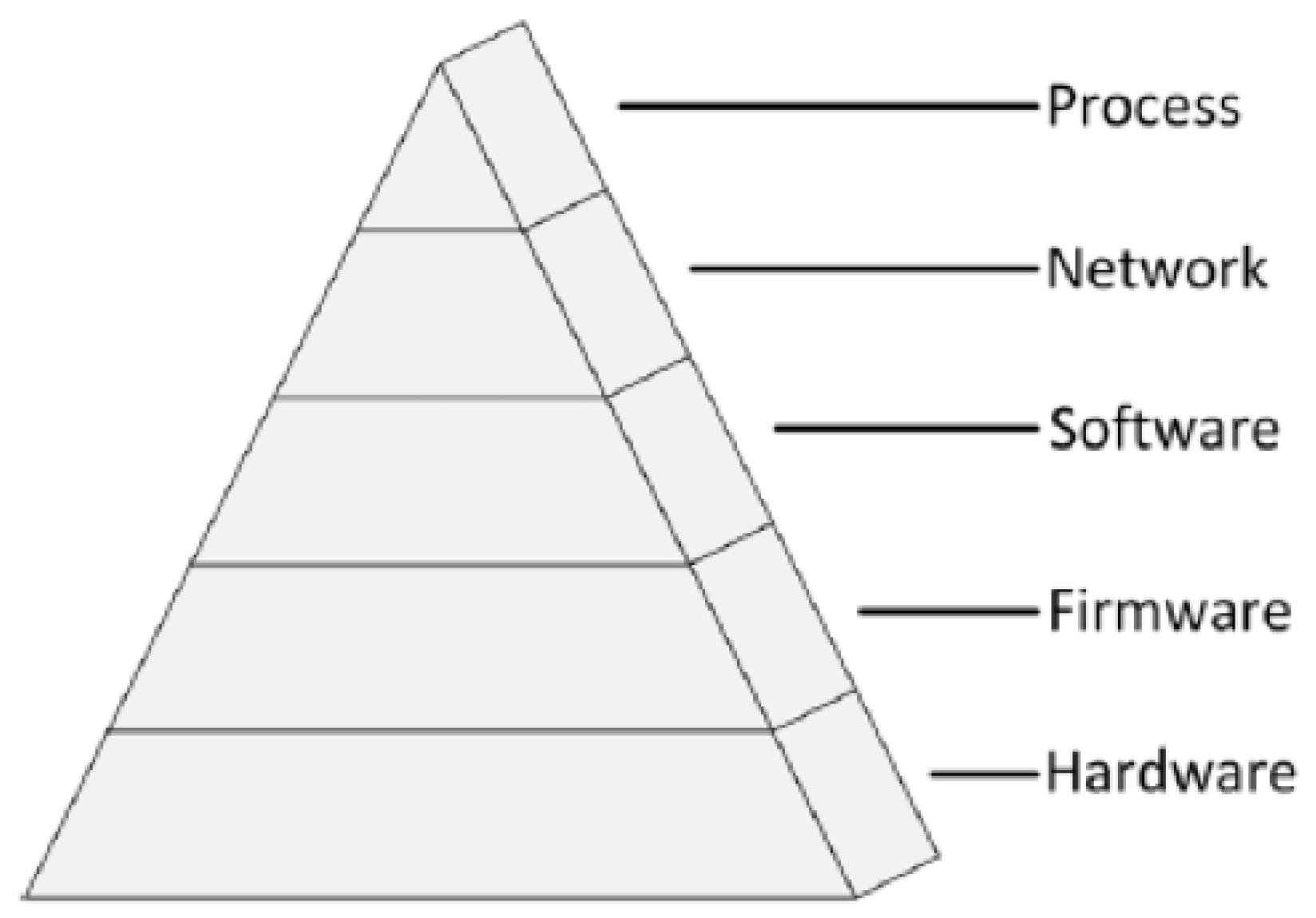
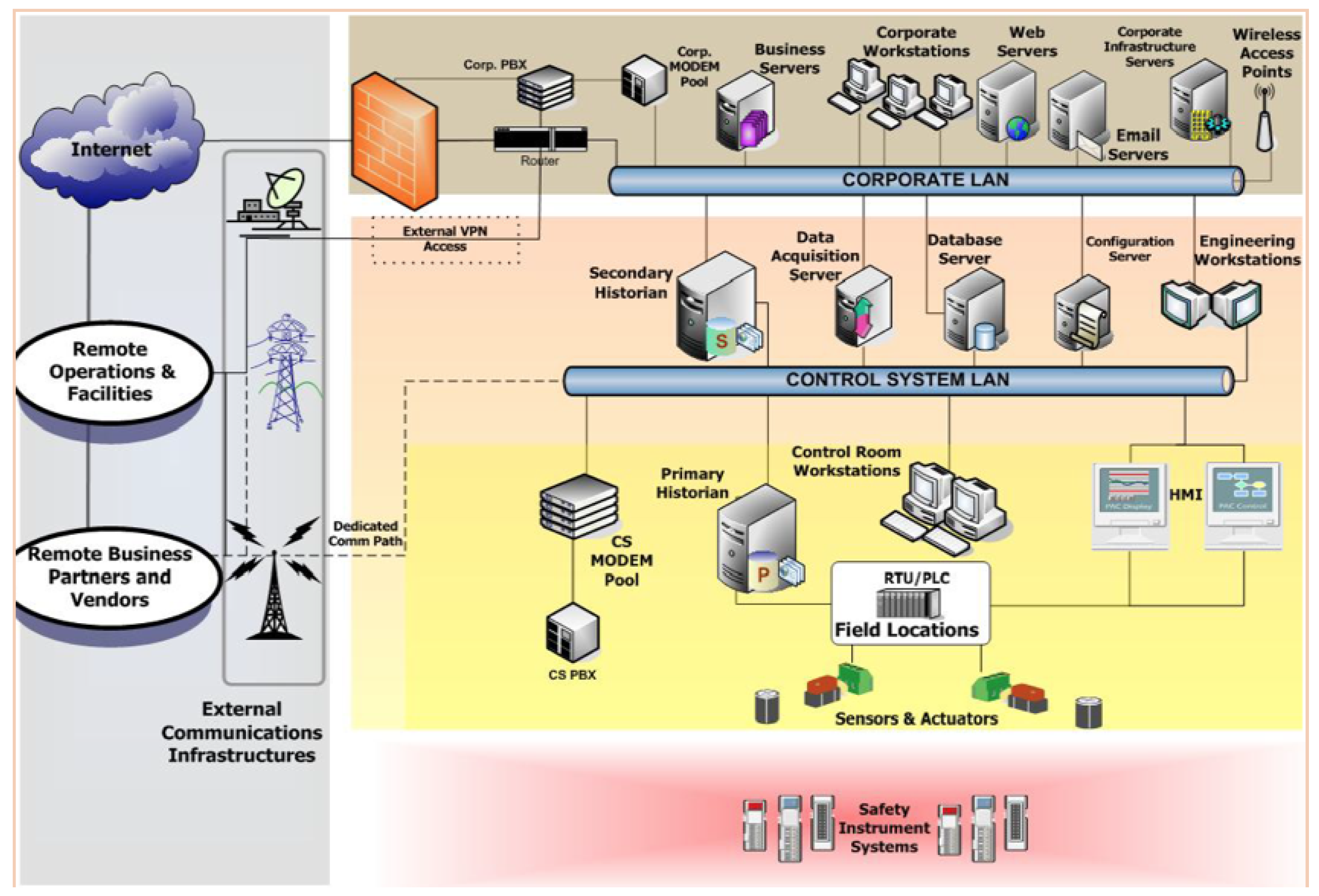
3.3. ICS Architecture Layers
- Firmware image acquisition: the attacker acquires a copy of the firmware code. Acquisition can either be a copy obtained directly from the manufacturer or by utilising the Joint Test Action Group (JTAG) testing port to extract the code.
- Binary analysis: Techniques such as “binwalk” and binary differentials can be used by the attacker to learn information about the used encoding, file systems, and checksum values.
- Binary disassembly: Further analysis, such as extracting and studying ASCII strings from the firmware, is performed to understand firmware functionality.
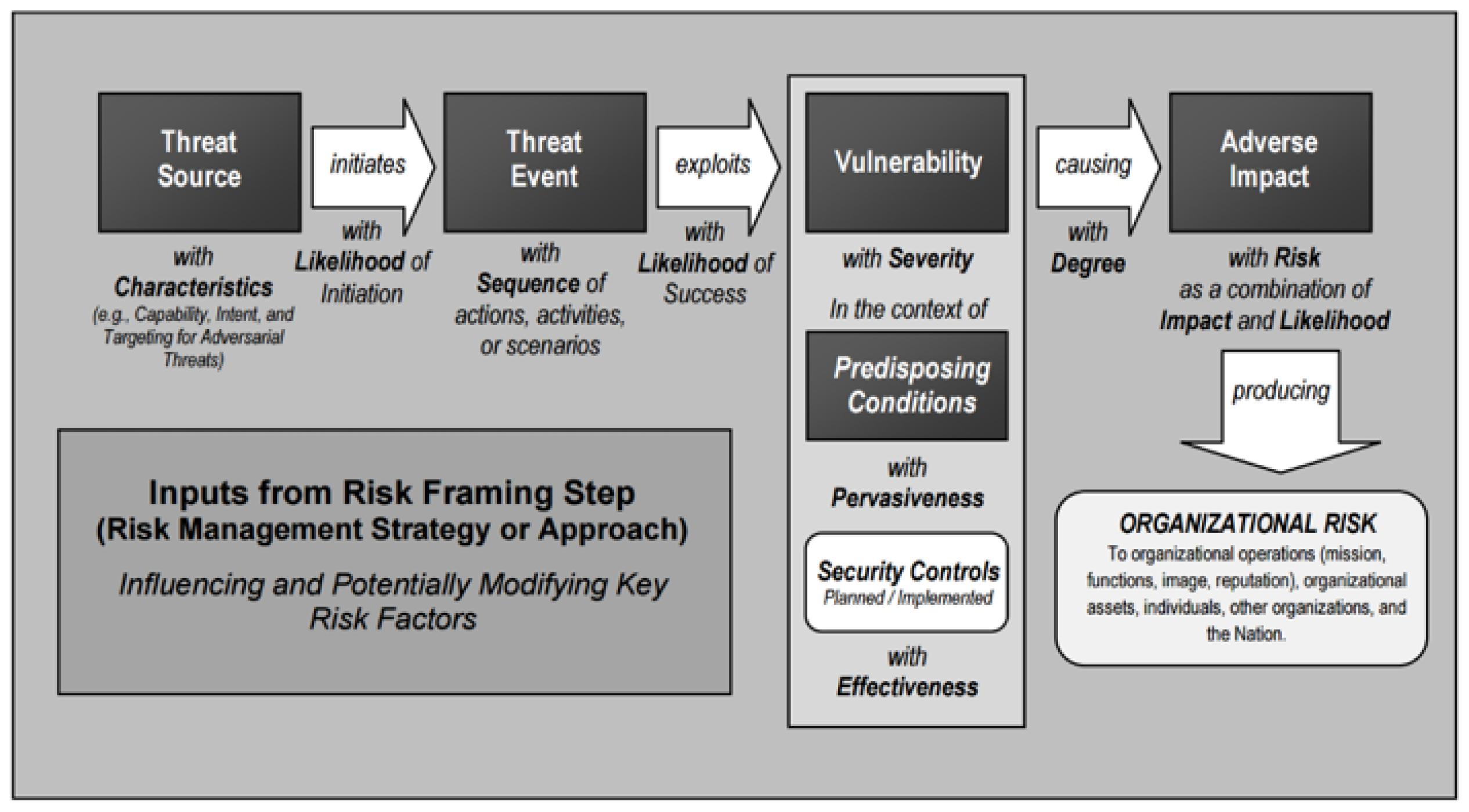
4. ICS Exploits and Defence Strategies
4.1. Traffic Encryption
4.2. Intrusion Detection and Prevention
4.3. Disaster Recovery and Business-Continuity Planning
5. Orthogonal Defence-in-Depth Framework
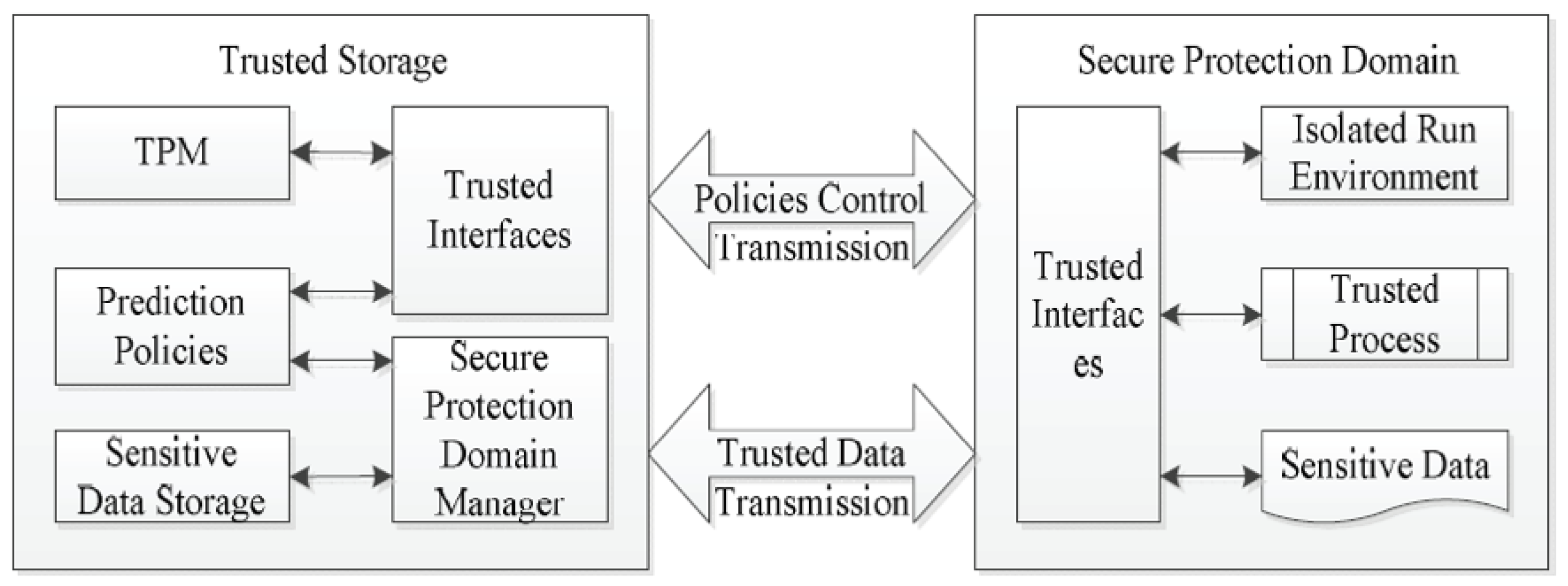
5.1. Integrated Trusted Protection
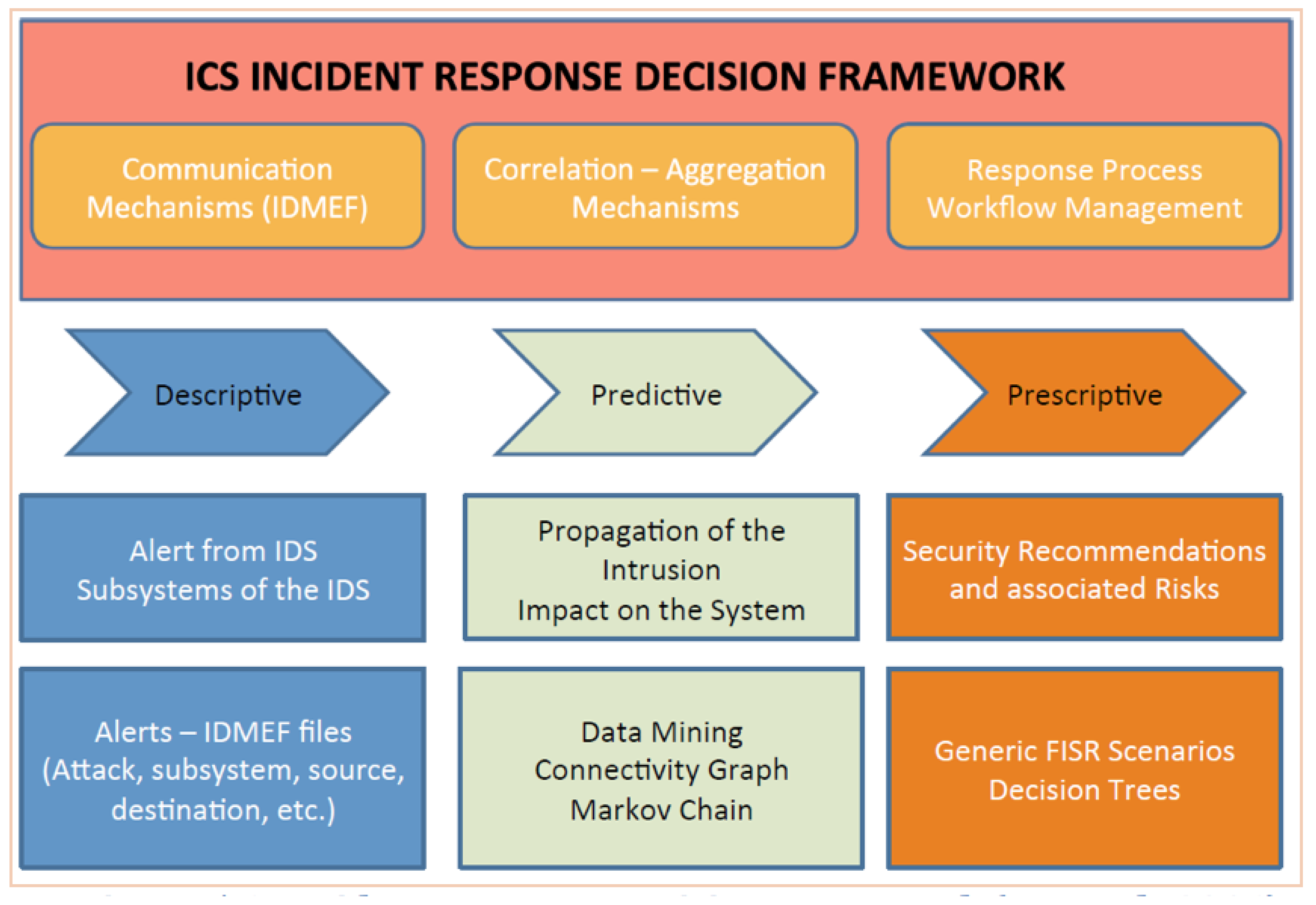
5.2. ICS and Incident Management
5.3. Orthogonality of Security Controls
5.4. Shortfalls of Existing Defence-in-Depth Strategies
5.5. Enhanced Defence-in-Depth Strategies
- Stateful firewall-inspection engines preventing access from untrusted zones. Commercially available and regularly updated databases preventing from malware infections using heuristic engines.
- Use of unidirectional gateways and application proxies to restrict access toward critical and sensitive layers using adequate instructions. and controls specific to ICS and SCADA systems.
- Use of IDPSs used transparently in the infrastructure.
- Auditing and logging security events with appropriate log management and automation and orchestration of security events.
6. Conclusions
Author Contributions
Funding
Conflicts of Interest
References
- Chikuni, E.; Dondo, M. Investigating the security of electrical power systems SCADA. In Proceedings of the AFRICON 2007, Windhoek, South Africa, 26–28 September 2007; pp. 1–7. [Google Scholar] [CrossRef]
- Epiphaniou, G.; Karadimas, P.; Ismail, D.K.B.; Al-Khateeb, H.; Dehghantanha, A.; Choo, K.R. Nonreciprocity Compensation Combined with Turbo Codes for Secret Key Generation in Vehicular Ad Hoc Social IoT Networks. IEEE Internet Things J. 2018, 5, 2496–2505. [Google Scholar] [CrossRef]
- Orojloo, H.; Azgomi, M.A. Evaluating the complexity and impacts of attacks on cyber-physical systems. In Proceedings of the 2015 CSI Symposium on Real-Time and Embedded Systems and Technologies (RTEST), Tehran, Iran, 7–8 October 2015; pp. 1–8. [Google Scholar] [CrossRef]
- Heo, Y.; Kim, B.; Kang, D.; Na, J. A design of unidirectional security gateway for enforcement reliability and security of transmission data in industrial control systems. In Proceedings of the 2016 18th International Conference on Advanced Communication Technology (ICACT), Pyeongchang, Korea, 31 January–3 February 2016; pp. 310–313. [Google Scholar] [CrossRef]
- Zhang, F.; Kodituwakku, H.A.D.E.; Hines, W.; Coble, J.B. Multi-Layer Data-Driven Cyber-Attack Detection System for Industrial Control Systems Based on Network, System and Process Data. IEEE Trans. Ind. Inform. 2019. [Google Scholar] [CrossRef]
- Venugopalan, V.; Patterson, C.D. Surveying the Hardware Trojan Threat Landscape for the Internet-of-Things. J. Hardw. Syst. Secur. 2018, 2, 131–141. [Google Scholar] [CrossRef]
- Mosterman, P.J.; Zander, J. Cyber-physical Systems Challenges: A Needs Analysis for Collaborating Embedded Software Systems. Softw. Syst. Model. 2016, 15, 5–16. [Google Scholar] [CrossRef]
- Fovino, I.N.; Carcano, A.; Murel, T.D.L.; Trombetta, A.; Masera, M. Modbus/DNP3 State-Based Intrusion Detection System. In Proceedings of the 2010 24th IEEE International Conference on Advanced Information Networking and Applications, Perth, Australia, 20–23 April 2010; pp. 729–736. [Google Scholar] [CrossRef]
- Ranathunga, D.; Roughan, M.; Nguyen, H.; Kernick, P.; Falkner, N. Case Studies of SCADA Firewall Configurations and the Implications for Best Practices. IEEE Trans. Netw. Serv. Manag. 2016, 13, 871–884. [Google Scholar] [CrossRef]
- Agre, J.; Clare, L.; Sastry, S. A Taxonomy of Distributed Real-time Control Systems. Adv. Comput. 1999, 49, 303–352. [Google Scholar] [CrossRef]
- Anoh, K.; Ikpehai, A.; Bajovic, D.; Jogunola, O.; Adebisi, B.; Vukobratovic, D.; Hammoudeh, M. Virtual Microgrids: A Management Concept for Peer-to-peer Energy Trading. In Proceedings of the 2nd International Conference on Future Networks and Distributed Systems (ICFNDS ’18), Amman, Jordan, 26–27 June 2018; ACM: New York, NY, USA, 2018; pp. 43:1–43:5. [Google Scholar] [CrossRef]
- Aldabbas, O.; Abuarqoub, A.; Hammoudeh, M.; Raza, U.; Bounceur, A. Unmanned ground vehicle for data collection in wireless sensor networks: Mobility-aware sink selection. Open Autom. Control Syst. J. 2016, 8, 35–46. [Google Scholar] [CrossRef]
- Benzerbadj, A.; Kechar, B.; Bounceur, A.; Hammoudeh, M. Surveillance of sensitive fenced areas using duty-cycled wireless sensor networks with asymmetrical links. J. Netw. Comput. Appl. 2018, 112, 41–52. [Google Scholar] [CrossRef]
- Talari, S.; Shafie-khah, M.; Siano, P.; Loia, V.; Tommasetti, A.; Catalão, J.P.S. A Review of Smart Cities Based on the Internet of Things Concept. Energies 2017, 10, 421. [Google Scholar] [CrossRef]
- Krotofil, M.; Gollmann, D. Industrial control systems security: What is happening? In Proceedings of the 2013 11th IEEE International Conference on Industrial Informatics (INDIN), Bochum, Germany, 29–31 July 2013; pp. 670–675. [Google Scholar] [CrossRef]
- Stouffer, K.A.; Falco, J.A.; Scarfone, K.A. Guide to Industrial Control Systems (ICS) Security: Supervisory Control and Data Acquisition (SCADA) Systems, Distributed Control Systems (DCS), and Other Control System Configurations such as Programmable Logic Controllers (PLC); SP 800-82; Technical Report; National Institute of Standards and Technology (NIST): Gaithersburg, MD, USA, 2011.
- Ramanathan, R. The IEC 61131-3 programming languages features for industrial control systems. In Proceedings of the 2014 World Automation Congress (WAC), Waikoloa, HI, USA, 3–7 August 2014; pp. 598–603. [Google Scholar] [CrossRef]
- John, K.H.; Tiegelkamp, M. IEC 61131-3: Programming Industrial Automation Systems Concepts and Programming Languages, Requirements for Programming Systems, Decision-Making Aids, 2nd ed.; Springer: Berlin/Heidelberg, Germany, 2010. [Google Scholar]
- Buciakowski, M.; Witczak, P. A new Matlab coder for generating Structured Text Language from matrix expression for PLC and PAC controllers. J. Phys. Conf. Ser. 2017, 783, 012062. [Google Scholar] [CrossRef]
- Palma, L.B.; Rosas, J.A.; Pecorelli, J.; Gil, P.S. Simulation of structured text language for PLC programming. In Proceedings of the 2015 3rd Experiment International Conference (exp.at’15), Ponta Delgada, Portugal, 2–4 June 2015; pp. 296–301. [Google Scholar] [CrossRef]
- Ani, U.P.D.; He, H.M.; Tiwari, A. Review of cybersecurity issues in industrial critical infrastructure: Manufacturing in perspective. J. Cyber Secur. Technol. 2017, 1, 32–74. [Google Scholar] [CrossRef]
- Kure, H.I.; Islam, S.; Razzaque, M.A. An Integrated Cyber Security Risk Management Approach for a Cyber-Physical System. Appl. Sci. 2018, 8, 898. [Google Scholar] [CrossRef]
- Kang, D.; Lee, J.; Kim, S.; Park, J. Analysis on cyber threats to SCADA systems. In Proceedings of the 2009 Transmission Distribution Conference Exposition: Asia and Pacific, Seoul, Korea, 26–30 October 2009; pp. 1–4. [Google Scholar] [CrossRef]
- Henry, M.H.; Layer, R.M.; Snow, K.Z.; Zaret, D.R. Evaluating the risk of cyber attacks on SCADA systems via Petri net analysis with application to hazardous liquid loading operations. In Proceedings of the 2009 IEEE Conference on Technologies for Homeland Security, Waltham, MA, USA, 11–12 May 2009; pp. 607–614. [Google Scholar] [CrossRef]
- Keliris, A.; Konstantinou, C.; Tsoutsos, N.G.; Baiad, R.; Maniatakos, M. Enabling multi-layer cyber-security assessment of Industrial Control Systems through Hardware-In-The-Loop testbeds. In Proceedings of the 2016 21st Asia and South Pacific Design Automation Conference (ASP-DAC), Macau, China, 25–28 January 2016; pp. 511–518. [Google Scholar] [CrossRef]
- Aghamolki, H.G.; Miao, Z.; Fan, L. A hardware-in-the-loop SCADA testbed. In Proceedings of the 2015 North American Power Symposium (NAPS), Charlotte, NC, USA, 4–6 October 2015; pp. 1–6. [Google Scholar] [CrossRef]
- Dayal, A.; Deng, Y.; Tbaileh, A.; Shukla, S. VSCADA: A reconfigurable virtual SCADA test-bed for simulating power utility control center operations. In Proceedings of the 2015 IEEE Power Energy Society General Meeting, Denver, CO, USA, 26–30 July 2015; pp. 1–5. [Google Scholar] [CrossRef]
- Hink, R.C.B.; Goseva-Popstojanova, K. Characterization of Cyberattacks Aimed at Integrated Industrial Control and Enterprise Systems: A Case Study. In Proceedings of the 2016 IEEE 17th International Symposium on High Assurance Systems Engineering (HASE), Washington, DC, USA, 1–7 January 2016; pp. 149–156. [Google Scholar] [CrossRef]
- Pricop, E.; Mihalache, S.F. Fuzzy approach on modelling cyber attacks patterns on data transfer in industrial control systems. In Proceedings of the 2015 7th International Conference on Electronics, Computers and Artificial Intelligence (ECAI), Bucharest, Romania, 25–27 June 2015; pp. SSS-23–SSS-28. [Google Scholar] [CrossRef]
- Tsoutsos, N.G.; Maniatakos, M. Fabrication Attacks: Zero-Overhead Malicious Modifications Enabling Modern Microprocessor Privilege Escalation. IEEE Trans. Emerg. Top. Comput. 2014, 2, 81–93. [Google Scholar] [CrossRef]
- Basnight, Z.; Butts, J.; Lopez, J.; Dube, T. Firmware modification attacks on programmable logic controllers. Int. J. Crit. Infrastruct. Prot. 2013, 6, 76–84. [Google Scholar] [CrossRef]
- Mahboob, A.; Zubairi, J. Intrusion avoidance for SCADA security in industrial plants. In Proceedings of the 2010 International Symposium on Collaborative Technologies and Systems, Chicago, IL, USA, 17–21 May 2010; pp. 447–452. [Google Scholar] [CrossRef]
- Kim, I.; Kim, D.; Kim, B.; Choi, Y.; Yoon, S.; Oh, J.; Jang, J. A case study of unknown attack detection against Zero-day worm in the honeynet environment. In Proceedings of the 2009 11th International Conference on Advanced Communication Technology, Phoenix Park, Korea, 15–18 February 2009; Volume 3, pp. 1715–1720. [Google Scholar]
- Langner, R. Stuxnet: Dissecting a Cyberwarfare Weapon. IEEE Secur. Priv. 2011, 9, 49–51. [Google Scholar] [CrossRef]
- Beecroft, A.J.; Michael, J.B. Passive Fingerprinting of Network Reconnaissance Tools. Computer 2009, 42, 91–93. [Google Scholar] [CrossRef]
- Daniela, T. Communication security in SCADA pipeline monitoring systems. In Proceedings of the 2011 RoEduNet International Conference 10th Edition: Networking in Education and Research, Iasi, Romania, 23–25 June 2011; pp. 1–5. [Google Scholar] [CrossRef]
- Jie, P.; Li, L. Industrial Control System Security. In Proceedings of the 2011 Third International Conference on Intelligent Human-Machine Systems and Cybernetics, Hangzhou, China, 26–28 August 2011; Volume 2, pp. 156–158. [Google Scholar] [CrossRef]
- Zhu, B.; Joseph, A.; Sastry, S. A Taxonomy of Cyber Attacks on SCADA Systems. In Proceedings of the 2011 International Conference on Internet of Things and 4th International Conference on Cyber, Physical and Social Computing, Dalian, China, 19–22 October 2011; pp. 380–388. [Google Scholar] [CrossRef]
- Cárdenas, A.A.; Amin, S.; Sastry, S. Research Challenges for the Security of Control Systems. In Proceedings of the 3rd Conference on Hot Topics in Security (HOTSEC’08), Berkeley, CA, USA, 29 July 2008; USENIX Association: Berkeley, CA, USA, 2008; pp. 6:1–6:6. [Google Scholar]
- Zineddine, M. The dilemma of securing industrial control systems: UAE context. In Proceedings of the 2016 International Conference on Information Technology for Organizations Development (IT4OD), Fez, Morocco, 30 March–1 April 2016; pp. 1–6. [Google Scholar] [CrossRef]
- Jillepalli, A.A.; Sheldon, F.T.; de Leon, D.C.; Haney, M.A.; Abercrombie, R.K. Security management of cyber physical control systems using NIST SP 800-82r2. In Proceedings of the IEEE IWCMC, Valencia, Spain, 26–30 June 2017; pp. 1864–1870. [Google Scholar]
- Cheminod, M.; Durante, L.; Seno, L.; Valenzano, A. On the description of access control policies in networked industrial systems. In Proceedings of the 2014 10th IEEE Workshop on Factory Communication Systems (WFCS 2014), Toulouse, France, 5–7 May 2014; pp. 1–10. [Google Scholar] [CrossRef]
- Mohd, B.J.; Hayajneh, T. Lightweight Block Ciphers for IoT: Energy Optimization and Survivability Techniques. IEEE Access 2018, 6, 35966–35978. [Google Scholar] [CrossRef]
- Schlegel, R.; Obermeier, S.; Schneider, J. Assessing the Security of IEC 62351. In Proceedings of the 3rd International Symposium for ICS & SCADA Cyber Security Research (ICS-CSR ’15), Ingolstadt, Germany, 17–18 September 2015; BCS Learning & Development Ltd.: Swindon, UK, 2015; pp. 11–19. [Google Scholar] [CrossRef]
- Jin, C.; Valizadeh, S.; van Dijk, M. Snapshotter: Lightweight intrusion detection and prevention system for industrial control systems. In Proceedings of the 2018 IEEE Industrial Cyber-Physical Systems (ICPS), Saint Petersburg, Russia, 15–18 May 2018; pp. 824–829. [Google Scholar] [CrossRef]
- Nazir, S.; Patel, S.; Patel, D. Assessing and augmenting SCADA cyber security: A survey of techniques. Comput. Secur. 2017, 70, 436–454. [Google Scholar] [CrossRef]
- Colbert, J.M.E.; Kott, A. Cyber-Security of SCADA and Other Industrial Control Systems; Springer: Berlin/Heidelberg, Germany, 2016. [Google Scholar]
- anssi. Managing Cybersecurity for Industrial Control Systems. 2016. Available online: https://www.ssi.gouv.fr/uploads/2014/01/Managing_Cybe_for_ICS_EN.pdf (accessed on 29 August 2018).
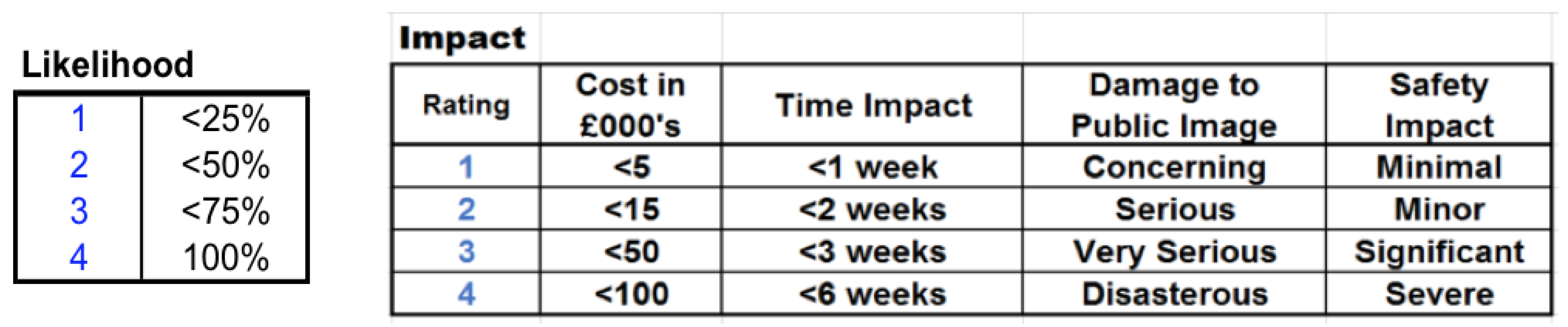
- StJohn-Green, M.; Piggin, R.; McDermid, J.A.; Oates, R. Combined security and safety risk assessment—What needs to be done for ICS and the IoT. In Proceedings of the 10th IET System Safety and Cyber-Security Conference 2015, Bristol, UK, 21–22 October 2015; pp. 1–7. [Google Scholar] [CrossRef]
- Cherdantseva, Y.; Burnap, P.; Blyth, A.; Eden, P.; Jones, K.; Soulsby, H.; Stoddart, K. A review of cyber security risk assessment methods for SCADA systems. Comput. Secur. 2016, 56, 1–27. [Google Scholar] [CrossRef]
- Frey, S.; Rashid, A.; Zanutto, A.; Busby, J.; Follis, K. On the Role of Latent Design Conditions in Cyber-physical Systems Security. In Proceedings of the 2nd International Workshop on Software Engineering for Smart Cyber-Physical Systems (SEsCPS ’16), Austin, TX, USA, 16 May 2016; ACM: New York, NY, USA, 2016; pp. 43–46. [Google Scholar] [CrossRef]
- Etigowni, S.; Tian, D.J.; Hernandez, G.; Zonouz, S.; Butler, K. CPAC: Securing Critical Infrastructure with Cyber-physical Access Control. In Proceedings of the 32nd Annual Conference on Computer Security Applications (ACSAC ’16), Los Angeles, CA, USA, 5–9 December 2016; ACM: New York, NY, USA, 2016; pp. 139–152. [Google Scholar] [CrossRef]
- Knowles, W.; Prince, D.; Hutchison, D.; Disso, J.F.P.; Jones, K. A Survey of Cyber Security Management in Industrial Control Systems. Int. J. Crit. Infrastruct. Prot. 2015, 9, 52–80. [Google Scholar] [CrossRef]
- Otuoze, A.O.; Mustafa, M.W.; Larik, R.M. Smart grids security challenges: Classification by sources of threats. J. Electr. Syst. Inf. Technol. 2018. [Google Scholar] [CrossRef]
- Bartman, T.; Carson, K. Securing communications for SCADA and critical industrial systems. In Proceedings of the 2016 69th Annual Conference for Protective Relay Engineers (CPRE), College Station, TX, USA, 4–7 April 2016; pp. 1–10. [Google Scholar] [CrossRef]
- Wang, J.; Lu, J.; Yang, S.; Li, D. Integrated trusted protection technologies for industrial control systems. In Proceedings of the 2015 IEEE Seventh International Conference on Intelligent Computing and Information Systems (ICICIS), Cairo, Egypt, 12–14 December 2015; pp. 418–423. [Google Scholar] [CrossRef]
- Genge, B.; Nai Fovino, I.; Siaterlis, C.; Masera, M. Analyzing Cyber-Physical Attacks on Networked Industrial Control Systems. In Critical Infrastructure Protection V; Butts, J., Shenoi, S., Eds.; Springer: Berlin/Heidelberg, Germany, 2011; pp. 167–183. [Google Scholar]
- He, Y.; Maglaras, L.A.; Janicke, H.; Jones, K. An Industrial Control Systems incident response decision framework. In Proceedings of the 2015 IEEE Conference on Communications and Network Security (CNS), Florence, Italy, 28–30 September 2015; pp. 761–762. [Google Scholar] [CrossRef]
- Hu, L.; Wang, Z.; Naeem, W. Security analysis of stochastic networked control systems under false data injection attacks. In Proceedings of the 2016 UKACC 11th International Conference on Control (CONTROL), Belfast, UK, 31 August–2 September 2016; pp. 1–6. [Google Scholar] [CrossRef]
- Zavarsky, P. High assurance cybersecurity plan templates for nuclear facilities: Two-dimensional layering of mutually orthogonal security controls for a high-assurance cybersecurity protection of critical computer-based systems in the post-Stuxnet era. In Proceedings of the International Conference on Information Society (i-Society 2014), London, UK, 10–12 November 2014; pp. 40–44. [Google Scholar] [CrossRef]
- Genge, B.; Haller, P.; Kiss, I. Cyber-Security-Aware Network Design of Industrial Control Systems. IEEE Syst. J. 2017, 11, 1373–1384. [Google Scholar] [CrossRef]
- Genge, B.; Haller, P. A hierarchical control plane for software-defined networks-based industrial control systems. In Proceedings of the 2016 IFIP Networking Conference (IFIP Networking) and Workshops, Vienna, Austria, 17–19 May 2016; pp. 73–81. [Google Scholar] [CrossRef]
- Kim, B.; Kang, D.; Na, J.; Chung, T. Abnormal traffic filtering mechanism for protecting ICS networks. In Proceedings of the 2016 18th International Conference on Advanced Communication Technology (ICACT), PyeongChang, Korea, 31 January–3 February 2016; pp. 436–440. [Google Scholar] [CrossRef]
| Taxonomy of Known Threats | |||
|---|---|---|---|
| Layer | Threat Category | Threats | Typical Examples of Known Exploits |
| Software | Memory attacks, control-flow attacks. | Modified software behaviour, buffer/stack overflows. | Data historian data compromised; buffer overflow attacks; software operation modified to perform unwanted actions. |
| Web attacks. | Open ports on firewall cross-side scripting, SQL injection, database attacks. | Reconnaissance of network to compromise devices; rootkits installed; privileges elevated; data confidentiality, integrity, and availability compromised; data stolen; denial-of-service (DOS) attacks; Smurf attacks; spyware; malware viruses, installed trojans. | |
| Access Control | No privilege segregation, credentials stolen. | Unauthorised access, privilege escalation. | |
| Zero-day vulnerabilities. | Inherent flaw in software exploited unbeknown to the vendor, exploited by attackers’ Kernel, design flaws; misconfigurations. | Zero-day attacks; viruses, worms, Trojans installed; buffer overflows; replay attacks; rootkits installed; privileges elevated; data compromised; spyware. | |
| Network | Firewall misconfiguration. | Firewall rules incorrectly configured, open ports. | Backdoors inserted; logic or time bombs installed; data/information stolen; sniffers installed. |
| Access control. | Unauthorised physical access, unauthorised logical access, Wi-Fi access points and communications. | Network traffic sniffed to steal credentials; man-in-the-middle attacks; malware installed from portable media; insider attacks; untrained employees subjected to phishing attacks. | |
| Protocol vulnerabilities. | Control signals modified, cryptographic attacks, communication hijacking and spoofing, communication stack attacks, Modbus and DNP3 vulnerabilities, covert channels exploited, replay attacks. | Syn/Ack attacks and flooding; fragmentation attacks; replay attacks; man-in-the-middle attacks; DOS attacks; bypassing controls; eavesdropping; traffic analysis; tunnelling; false command and control communications; exploits of TCP/lP stack; UDP port attacks; Smurf attacks; idle scans (e.g., Nmap); ARP spoofing; chain/loop attacks. | |
| Process | Internet-facing threats. | Similar to web attacks above cryptographic attacks. | Man-in-the-middle attacks; Cinderella attacks; DDOS attacks; rootkits installed; masquerading; spying and sniffers. |
| Process-aware malware. | Malware specifically designed to compromise/alter a specific process, sabotage/terrorism. | Stuxnet worm altered Programmable Logic Controller (PLC) operation. | |
| False-data injection. | Control logic-modified process variables and constants modified | Aurora vulnerability; modified state estimation in power grids. | |
| Automatic payload generation. | Malicious payload delivered to PLCs, Remote Terminal Units (RTUs), and Master Terminal Units (MTUs). | PLCs exploited, process hijacked. | |
| Taxonomy of Known Threats (Cont.) | |||
|---|---|---|---|
| Layer | Threat Category | Threats | Typical Examples of Known Exploits |
| Hardware | Hardware trojans. | Modification by: design architects, manufacturers, supply chain prior to operation, attacks during normal operation, stack-smashing, exceeding fixed memory allocation. | Backdoors for remote attacks; time-bombs; elevation of privileges; access to cryptographic keys; access to higher layers; degradation of performance; destruction of component or device. |
| Fault-injection attacks. | Faults injected. Computational results modified, low-accuracy fault injection—modification of operating environment without operator aware. lon beams causing bits to flip. | Device performance degraded; modification of operating temperatures; device clock modified; dataset points modified; false data passed to the controllers and data historian. | |
| Side-channel attacks. | Wireless snooping, electromagnetic emanations, acoustic vibrations, simple power analysis. | Information leakages to extract information such as cryptographic keys. | |
| Firmware | Firmware reverse-engineering. | Firmware image acquisition, binary analysis, binary disassembly cryptographic attacks. | Directly from manufacturer; from the JTAG testing port to obtain firmware, using “binwalk” and binary differentials to reverse-engineer firmware/ASCII strings analysed and disassembled/communications decrypted. |
| Firmware vulnerabilities. | Firmware updates and patches not applied, legacy systems with unsupported firmware. | Security vulnerabilities exploited and components compromised, higher layers compromised. | |
| Firmware modifications | Firmware modified to perform illegal processes. | Component malfunction/destruction. | |
| Enhanced Defence-in-Depth Strategy Using Orthogonality | |||
|---|---|---|---|
| Layer | Typical ICS Components | Functional Controls | Assurance Controls |
| Network | Network devices: modems, routers, firewalls; ICS communication protocols: Modbus, DNP3; standard network protocols: TCP/IP; ICS sublayers: device layer, monitoring and control layer, and management layer. | Vulnerability, risk assessment and treatment plan; encryption of ICS communication traffic., e.g., NTRU; encryption of TCP/lP traffic within VPN tunnels; use of shielded twisted pairs in sensitive areas; physical security preventing unauthorised access; role-based logical access control, staff-vetting procedures to minimise insider attacks; complete ban on removable-storage media; redundant critical network components for fail-over; defence in diversity; mitigation against DOS attacks; secure encryption and authentication of WiFi traffic: firewalls and unidirectional gateways for segregation; port blocking on network switches; establishment of DMZ between ICS and corporate network: VPNs terminate in DMZ; use of honeypots and honeynets. | Testing Environments: HIT1, VSCADA, NSTB, etc.; routine inspections and audit of access and error logs; use of biometrics to validate access; data-integrity checks; routine inspections of events and threat logs on firewalls; routine inspection of logs on honeypots and honeynets; intrusion detection and prevention; trusted network protection assurance; vulnerability and penetration testing; senior-management audits. |
| Process | MTUs; HMIs; data historian. | Vulnerability, risk assessment and treatment plan; physical security preventing unauthorised access; staff-vetting procedures to minimise insider attacks; ICS incident response and decision trees; disaster recovery and business-continuity planning; dedicated security team; data historian situated within DMZ; environmental-control systems. | Testing environments: HIT1, VSCADA, NSTB, etc.; inspection and audit of access logs; CCTV surveillance of sensitive areas; use of biometrics to validate access; routine testing of DR and business-continuity plans; routine backups of data-historian databases; senior-management audits. |
| Enhanced Defence-in-Depth Strategy Using Orthogonality | |||
|---|---|---|---|
| Layer | ICS Typical Components | Functional Controls | Assurance Controls |
| Hardware | IEDs: sensors, relays, actuators, microprocessors, microcontrollers; RTUs; PLCs; MTUs. | Vulnerability, risk assessment, and treatment plan; in-depth auditing of designers, manufacturers, and supply chain of all hardware; defence in diversity; physical security preventing unauthorised access; screening to prevent electromagnetic emanations; staff-vetting procedures to minimise insider attacks; redundant critical components for fail-over. | Testing environments: HIT1, VSCADA, NSTB., etc.; testing IEDs for hardware trojans; inspection and audit of access logs; CCTV surveillance of sensitive areas; asset tracking; trusted computing platform assurance; senior-management audits. |
| Firmware | IEDs: sensors, relays, actuators, microprocessors, microcontrollers, etc.; servers and computer BIOS. | Vulnerability, risk Assessment and treatment plan; physical security preventing unauthorised access; staff-vetting procedures to minimise insider threat; confidentiality agreements with architects and manufacturers; routine firmware patching. | Inspection and audit of access logs; CCTV surveillance of sensitive areas; testing environments: HIT1, VSCADA, NSTB, etc.; trusted computing platform assurance; testing of all firmware patches. |
| Software | PLC programming languages; operating systems. | Vulnerability, risk assessment, and treatment plan; physical security preventing unauthorised access; role-based logical access control; staff-vetting procedures to minimise insider threat; complete ban on removable-storage media; routine software patching; defence in Diversity; reprogramming conducted by highly trained developers; antimalware software. | Testing environments: HIT1, VSCADA, NSTB, etc.; inspection and audit of access logs; testing of all software patches; testing for logic errors and bugs; CCTV surveillance of sensitive areas; intrusion detection and prevention; trusted data-protection mechanism assurance; routine data backup; senior-management audit. |
© 2019 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Mackintosh, M.; Epiphaniou, G.; Al-Khateeb, H.; Burnham, K.; Pillai, P.; Hammoudeh, M. Preliminaries of Orthogonal Layered Defence Using Functional and Assurance Controls in Industrial Control Systems. J. Sens. Actuator Netw. 2019, 8, 14. https://doi.org/10.3390/jsan8010014
Mackintosh M, Epiphaniou G, Al-Khateeb H, Burnham K, Pillai P, Hammoudeh M. Preliminaries of Orthogonal Layered Defence Using Functional and Assurance Controls in Industrial Control Systems. Journal of Sensor and Actuator Networks. 2019; 8(1):14. https://doi.org/10.3390/jsan8010014
Chicago/Turabian StyleMackintosh, Mike, Gregory Epiphaniou, Haider Al-Khateeb, Keith Burnham, Prashant Pillai, and Mohammad Hammoudeh. 2019. "Preliminaries of Orthogonal Layered Defence Using Functional and Assurance Controls in Industrial Control Systems" Journal of Sensor and Actuator Networks 8, no. 1: 14. https://doi.org/10.3390/jsan8010014
APA StyleMackintosh, M., Epiphaniou, G., Al-Khateeb, H., Burnham, K., Pillai, P., & Hammoudeh, M. (2019). Preliminaries of Orthogonal Layered Defence Using Functional and Assurance Controls in Industrial Control Systems. Journal of Sensor and Actuator Networks, 8(1), 14. https://doi.org/10.3390/jsan8010014







