An Extended Reselling Protocol for Existing Anti-Counterfeiting Schemes
Abstract
1. Introduction
2. Literature Review
2.1. Related Work
2.2. Ghaith et al. Scheme Analysis
2.3. The Significance of Reselling Items in Retailer Environments
3. The Reselling Protocol
4. Security Analysis
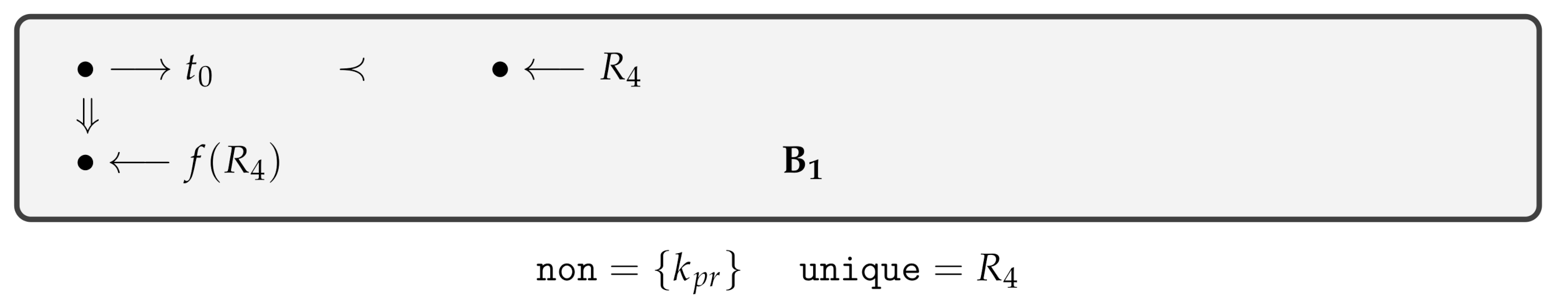
4.1. The Nonce Test
- The private key has been revealed before transpires, so that can be mined by the challenger; or
- other regular strand comprises a node where is communicated outside of or , yet in all former nodes , occurs before , and was found only through this encryption.
- If is compromised, an attacker would be able later to determine from . For this to take place, must originate. Since is never transmitted in the protocol, it is therefore non-originating.

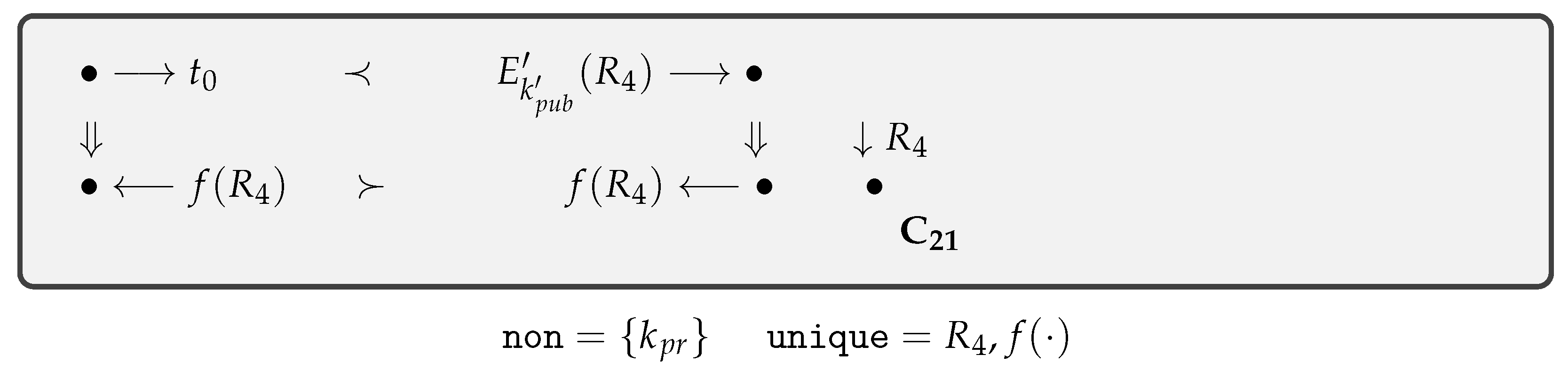
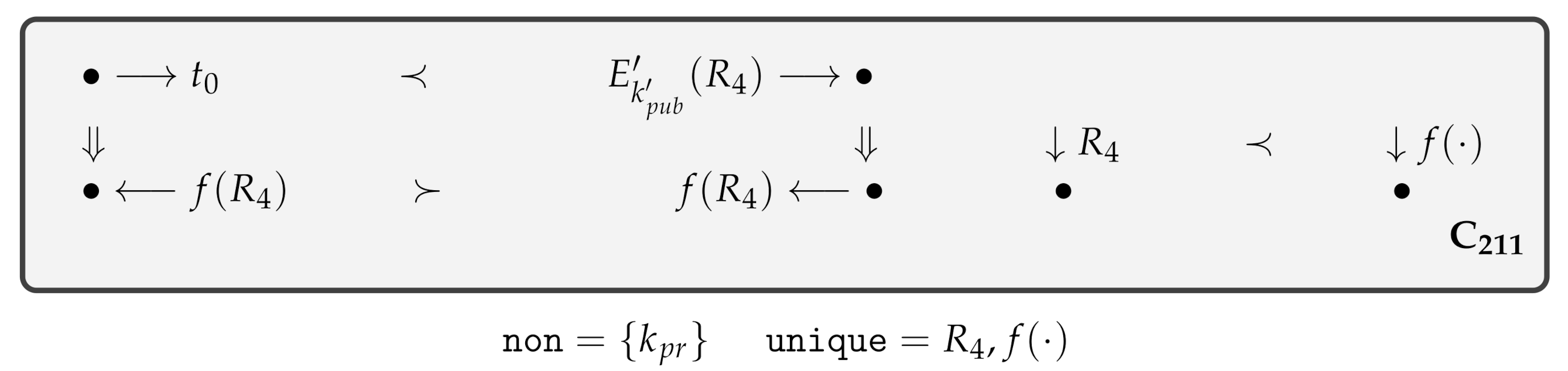
4.2. The Authentication Guarantee
- To monitor the discovery of the decryption key , a listener node can be added to test this further elaboration in case is discovered by the attacker who prepares a message.
- Otherwise, adding a strand of the protocol which needs to be the second node in the strand to send . Yet, other possibilities for the terms in are unconstrained and need further elaboration.
4.3. The Secrecy of
5. Conclusions
Author Contributions
Funding
Conflicts of Interest
References
- Tran, D.T.; Hong, S.J. RFID anti-counterfeiting for retailing systems. J. Appl. Math. Phys. 2015, 3, 1. [Google Scholar] [CrossRef]
- Khalil, G.; Doss, R.; Chowdhury, M. A New Secure RFID Anti-Counterfeiting and Anti-Theft Scheme for Merchandise. J. Sens. Actuator Netw. 2020, 9, 16. [Google Scholar] [CrossRef]
- Khalil, G.D.A. A Novel RFID Based Anti-Counterfeiting Scheme for Retailer Environments; Technical Report; Deakin University: Victoria, Australia, 2019. [Google Scholar]
- Khalil, G.; Doss, R.; Chowdhury, M. A Novel RFID-Based Anti-Counterfeiting Scheme for Retail Environments. IEEE Access 2020, 8, 47952–47962. [Google Scholar] [CrossRef]
- Hargreaves, S. Counterfeit Goods Becoming More Dangerous; Tech. Rep. Press12, CNN; CNN Money: Atlanta, GA, USA, 2012. [Google Scholar]
- Bloch, P.H.; Bush, R.F.; Campbell, L. Consumer ‘accomplices’ in product counterfeiting: a demand side investigation. J. Consum. Mark. 1993, 10, 27–36. [Google Scholar] [CrossRef]
- McKinney, G.F., Jr. Monitoring the Ligand-Nanopartcle Interaction for the Development of SERS Tag Materials Prepared by. Ph.D. Thesis, University of South Dakota, Vermillion, SD, USA, 2014. [Google Scholar]
- Choi, S.; Poon, C. An RFID-based anti-counterfeiting system. IAENG Int. J. Comput. Sci. 2008, 35, 1–12. [Google Scholar]
- Estacio, L.S. Showdown in Chinatown: Criminalizing the Purchase of Counterfeit Goods. Seton Hall Legis. J. 2012, 37, 381. [Google Scholar]
- AL, G.; Ray, B.; Chowdhury, M. RFID Tag Ownership Transfer Protocol for a Closed Loop System. In Proceedings of the 2014 IIAI 3rd International Conference on Advanced Applied Informatics (IIAIAAI), Kita-Kyushu, Japan, 31 August–4 September 2014; pp. 575–579. [Google Scholar] [CrossRef]
- AL, G.; Ray, B.; Chowdhury, M. Multiple Scenarios for a Tag Ownership Transfer protocol for A Closed Loop System. IJNDC 2015, 3, 128–136. [Google Scholar] [CrossRef]
- Al, G.; Al, T.; Chowdhury, M.; Doss, R. A Survey in RFID Ownership Transfer Protocols. In RFID Technology: Design Principles, Applications and Controversies; NOVA Science Publishers: Commack, NY, USA, 2017; pp. 83–91. [Google Scholar]
- Lee, J.D. Anti-Counterfeiting Mechanism Based on RFID Tag Ownership Transfer Protocol. J. Korea Multimed. Soc. 2015, 18, 710–722. [Google Scholar] [CrossRef]
- Al, G. RFID Technology: Design Principles, Applications and Controversies; NOVA Science Publishers, Inc.: Commack, NY, USA, 2018. [Google Scholar]
- Al, G.; Doss, R.; Chowdhury, M.; Ray, B. Secure RFID Protocol to Manage and Prevent Tag Counterfeiting with Matryoshka Concept. In Proceedings of the International Conference on Future Network Systems and Security, Paris, France, 23–25 November 2016; pp. 126–141. [Google Scholar]
- Al, G.; Doss, R.; Chowdhury, M. Adjusting Matryoshka Protocol to Address the Scalability Issue in IoT Environment. In Proceedings of the International Conference on Future Network Systems and Security, Paris, France, 23–25 November 2017; pp. 84–94. [Google Scholar]
- Khalil, G.; Doss, R.; Chowdhury, M. A Comparison Survey Study on RFID Based Anti-Counterfeiting Systems. J. Sens. Actuator Netw. 2019, 8, 37. [Google Scholar] [CrossRef]
- Al, T.; Al, G. The use of rfid systems in libraries. In RFID Technology: Design Principles, Applications and Controversies; NOVA Science Publishers: Commack, NY, USA, 2017; pp. 93–103. [Google Scholar]
- Al, T.; Al, G.K. A Case Study in Developing the ICT Skills for a Group of Mixed Abilities and Mixed Aged Learners at ITEP in Dubai-UAE and Possible Future RFID Implementations. In Envisioning the Future of Online Learning; Springer: Berlin/Heidelberg, Germany, 2016; pp. 133–146. [Google Scholar]
- Al, T.; Al, G.; Ayoob, A.; Su, G. A Survey Study in the use of RFID Technology in smart labs. In RFID Technology: Desin Principles, Applications and Controversies; NOVA Science Publishers: Commack, NY, USA, 2017; pp. 71–82. [Google Scholar]
- Yuan, Y.; Cao, L. Liquor Product Anti-counterfeiting System Based on RFID and Two-dimensional Barcode Technology. J. Converg. Inf. Technol. 2013, 8, 88–96. [Google Scholar]
- Bu, K.; Liu, X.; Xiao, B. Approaching the time lower bound on cloned-tag identification for large RFID systems. Ad Hoc Netw. 2014, 13, 271–281. [Google Scholar] [CrossRef]
- Finkenzeller, K. RFID Handbook: Fundamentals and Applications in Contactless Smart Cards, Radio Frequency Identification and Near-Field Communication; John Wiley & Sons: Hoboken, NJ, USA, 2010. [Google Scholar]
- Janz, B.D.; Pitts, M.G.; Otondo, R.F. Information systems and health care-II: Back to the future with RFID: Lessons learned-some old, some new. Commun. Assoc. Inf. Syst. 2005, 15, 7. [Google Scholar] [CrossRef]
- Kerschbaum, F.; Sorniotti, A. RFID-based supply chain partner authentication and key agreement. In Proceedings of the Second ACM Conference on Wireless Network Security, Zurich, Switzerland, 16–18 March 2009; pp. 41–50. [Google Scholar]
- Wu, Y.; Sheng, Q.Z.; Shen, H.; Zeadally, S. Modeling object flows from distributed and federated RFID data streams for efficient tracking and tracing. IEEE Trans. Parallel Distrib. Syst. 2013, 24, 2036–2045. [Google Scholar]
- Al, T.; Al, G.; Doss, R. Survey on Rfid Security Issues and scalability. In RFID Technology: Desin Principles, Applications and Controversies; NOVA Science Publishers: Commack, NY, USA, 2017; pp. 37–50. [Google Scholar]
- Choi, S.; Yang, B.; Cheung, H.; Yang, Y. RFID tag data processing in manufacturing for track-and-trace anti-counterfeiting. Comput. Ind. 2015, 68, 148–161. [Google Scholar] [CrossRef]
- Cheung, H.; Choi, S. Implementation issues in RFID-based anti-counterfeiting systems. Comput. Ind. 2011, 62, 708–718. [Google Scholar] [CrossRef]
- Chen, Y.C.; Wang, W.L.; Hwang, M.S. RFID authentication protocol for anti-counterfeiting and privacy protection. In Proceedings of the The 9th International Conference on Advanced Communication Technology, Phoenix Park, Korea, 12–14 February 2007; Volume 1, pp. 255–259. [Google Scholar]
- Lehtonen, M.; Ostojic, D.; Ilic, A.; Michahelles, F. Securing RFID systems by detecting tag cloning. In Proceedings of the International Conference on Pervasive Computing, Nara, Japan, 11–14 May 2009; pp. 291–308. [Google Scholar]
- Arjona, L.; Landaluce, H.; Perallos, A.; Parks, A. Survey and analysis of RFID DFSA anti-collsion protocols and their physical implementation capabilities. In RFID Technology:Desin Principles, Applications and Controversies; NOVA Science Publishers: Commack, NY, USA, 2017; pp. 1–35. [Google Scholar]
- Ayoob, A.; Su, G.; Al, G.; Mohammed, M.; Mira, T.; Hammood, O. Analysis of radio access technology RFIS/IEEE802.11p FIR vanets. In RFID Technology: Design Principles, Applications and Controversies; NOVA Science Publishers: Commack, NY, USA, 2017; pp. 51–69. 11p. [Google Scholar]
- Kriara, L.; Alsup, M.; Corbellini, G.; Trotter, M.; Griffin, J.D.; Mangold, S. RFID shakables: pairing radio-frequency identification tags with the help of gesture recognition. In Proceedings of the Ninth ACM Conference on Emerging Networking Experiments and Technologies; ACM: New York, NY, USA, 2013; pp. 327–332. [Google Scholar]
- Repo, P.; Kerttula, M.; Salmela, M.; Huomo, H. Virtual product design case study: the Nokia RFID tag reader. IEEE Pervasive Comput. 2005, 4, 95–99. [Google Scholar] [CrossRef]
- Yuan, Y. Crowd monitoring using mobile phones. In Proceedings of the 2014 Sixth International Conference on Intelligent Human-Machine Systems and Cybernetics, Hangzhou, China, 26–27 August 2014; Volume 1, pp. 261–264. [Google Scholar]
- Caro, F.; Sadr, R. The Internet of Things (IoT) in retail: Bridging supply and demand. Bus. Horizons 2019, 62, 47–54. [Google Scholar] [CrossRef]
- Yilmaz, Y.; Do, V.; Halak, B. ARMOR: An anti-counterfeit security Mechanism for lOw cost Radio frequency identification systems. IEEE Trans. Emerg. Top. Comput. 2020, 1. [Google Scholar] [CrossRef]
- Özcanhan, M.H.; Dalkılıç, G.; Utku, S. Is NFC a Better Option Instead of EPC Gen-2 in Safe Medication of Inpatients. In Radio Frequency Identification; Hutter, M., Schmidt, J.M., Eds.; Springer: Berlin/Heidelberg, Germany, 2013; pp. 19–33. [Google Scholar]
- Fan, K.; Song, P.; Yang, Y. ULMAP: Ultralightweight NFC mutual authentication protocol with pseudonyms in the tag for IoT in 5G. Mob. Inf. Syst. 2017, 2017. [Google Scholar] [CrossRef]
- Kim, W.; Kim, B. The Critical Factors Affecting the Consumer Reselling of Limited Edition Products: A Case in the Korean Fashion Sector. Sustainability 2020, 12, 8181. [Google Scholar] [CrossRef]
- Chu, H.; Liao, S. Toward a conceptual model of consumer online resale behavior: An exploratory study in Taiwan. J. Internet Commer. 2008, 7, 220–252. [Google Scholar] [CrossRef]
- Jang, W.E.; Ko, Y.J.; Morris, J.D.; Chang, Y. Scarcity message effects on consumption behavior: Limited edition product considerations. Psychol. Mark. 2015, 32, 989–1001. [Google Scholar] [CrossRef]
- Brannon, L.A.; Brock, T.C. Limiting time for responding enhances behavior corresponding to the merits of compliance appeals: Refutations of heuristic-cue theory in service and consumer settings. J. Consum. Psychol. 2001, 10, 135–146. [Google Scholar] [CrossRef]
- Helm, S.; Subramaniam, B. Exploring Socio-Cognitive Mindfulness in the Context of Sustainable Consumption. Sustainability 2019, 11, 3692. [Google Scholar] [CrossRef]
- Ku, H.H.; Kuo, C.C.; Kuo, T.W. The effect of scarcity on the purchase intentions of prevention and promotion motivated consumers. Psychol. Mark. 2012, 29, 541–548. [Google Scholar] [CrossRef]
- Gierl, H.; Huettl, V. Are scarce products always more attractive? The interaction of different types of scarcity signals with products’ suitability for conspicuous consumption. Int. J. Res. Mark. 2010, 27, 225–235. [Google Scholar] [CrossRef]
- Foth, T.J.; Mcnab, C.S. Method for Returning and Reselling Merchandise. US Patent 7,299,198, 11 November 2007. [Google Scholar]
- Guttman, J.D. Shapes: Surveying crypto protocol runs. In Formal Models and Techniques for Analyzing Security Protocols; Cryptology and Information Security Series; IOS Press: Amsterdam, The Netherlands, 2011. [Google Scholar]
- Guttman, J.D. Cryptographic protocol composition via the authentication tests. In Proceedings of the International Conference on Foundations of Software Science and Computational Structures, York, UK, 22–29 March 2009; pp. 303–317. [Google Scholar]
- Guttman, J.D. Fair exchange in strand spaces. arXiv 2009, arXiv:0910.4342. [Google Scholar] [CrossRef]
- Paulson, L.C. Proving properties of security protocols by induction. In Proceedings of the 10th Computer Security Foundations Workshop, Rockport, MA, USA, 10–12 June 1997; pp. 70–83. [Google Scholar]


| ID of the tag attached to the item | |
| shared key between the seller and the server | |
| shared key between the buyer and the server | |
| public and private keys of the server | |
| f | hash function |
| asymmetric encryption and decryption functions | |
| random number generator | |
| item status (sold, unsold, stolen) | |
| buyer | |
| seller | |
| warranty card ID | |
| acknowledgment | |
| complete acknowledgment |
Publisher’s Note: MDPI stays neutral with regard to jurisdictional claims in published maps and institutional affiliations. |
© 2021 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Khalil, G.; Doss, R.; Chowdhury, M. An Extended Reselling Protocol for Existing Anti-Counterfeiting Schemes. J. Sens. Actuator Netw. 2021, 10, 12. https://doi.org/10.3390/jsan10010012
Khalil G, Doss R, Chowdhury M. An Extended Reselling Protocol for Existing Anti-Counterfeiting Schemes. Journal of Sensor and Actuator Networks. 2021; 10(1):12. https://doi.org/10.3390/jsan10010012
Chicago/Turabian StyleKhalil, Ghaith, Robin Doss, and Morshed Chowdhury. 2021. "An Extended Reselling Protocol for Existing Anti-Counterfeiting Schemes" Journal of Sensor and Actuator Networks 10, no. 1: 12. https://doi.org/10.3390/jsan10010012
APA StyleKhalil, G., Doss, R., & Chowdhury, M. (2021). An Extended Reselling Protocol for Existing Anti-Counterfeiting Schemes. Journal of Sensor and Actuator Networks, 10(1), 12. https://doi.org/10.3390/jsan10010012







