A Survey on Internet of Things and Cloud Computing for Healthcare
Abstract
1. Introduction
1.1. Contributions
- Present a comprehensive survey about IoT and cloud computing in the healthcare (From 2015 to present).
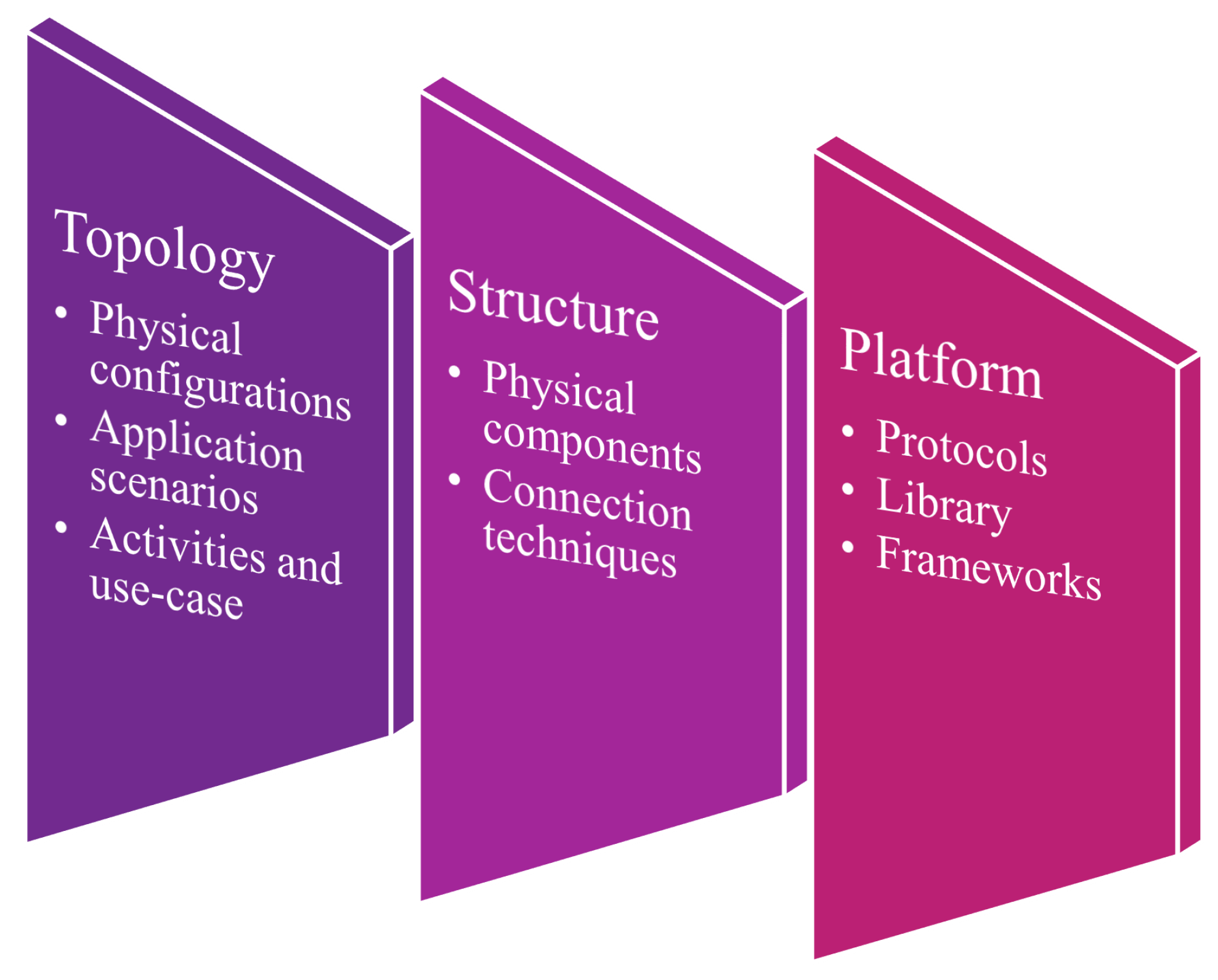
- Review IoT framework for the healthcare by discussing typologies, platforms, and structures.
- Survey cloud computing and especially the fog computing for healthcare, including standard architecture, remarkable fog-based healthcare applications.
- Discuss various concepts and existing applications in IoT and cloud computing in the healthcare.
- Describe healthcare latest industry trends and policies regarding IoT and cloud computing around the world.
- Discuss security issues of IoT and cloud computing in healthcare systems and summarize appropriate solutions.
- Show challenges and open research directions for the integration of IoT and cloud computing in healthcare.
1.2. Problem Statement
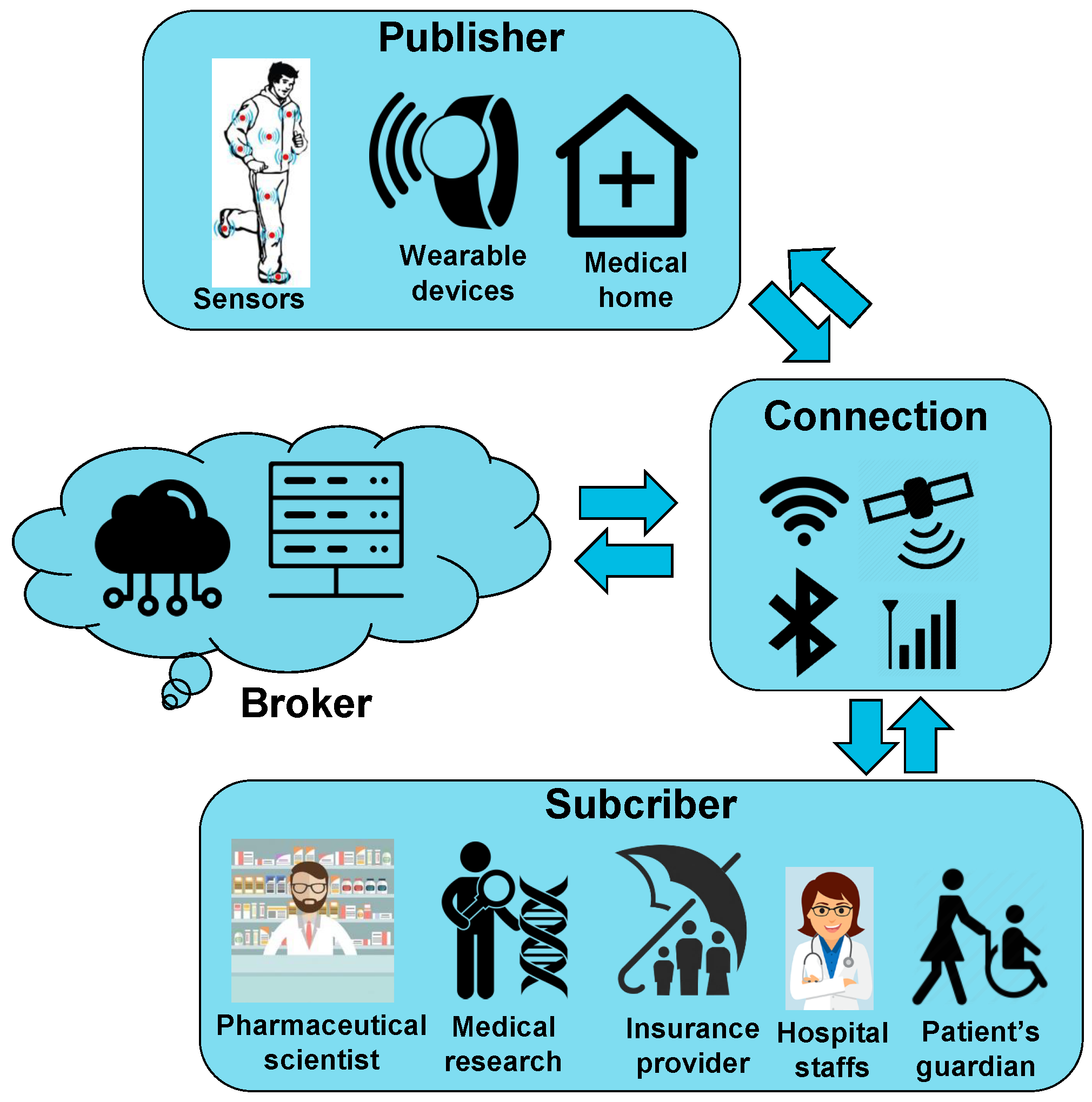
2. IoT Framework for Heathcare
2.1. IoTHeF Structure
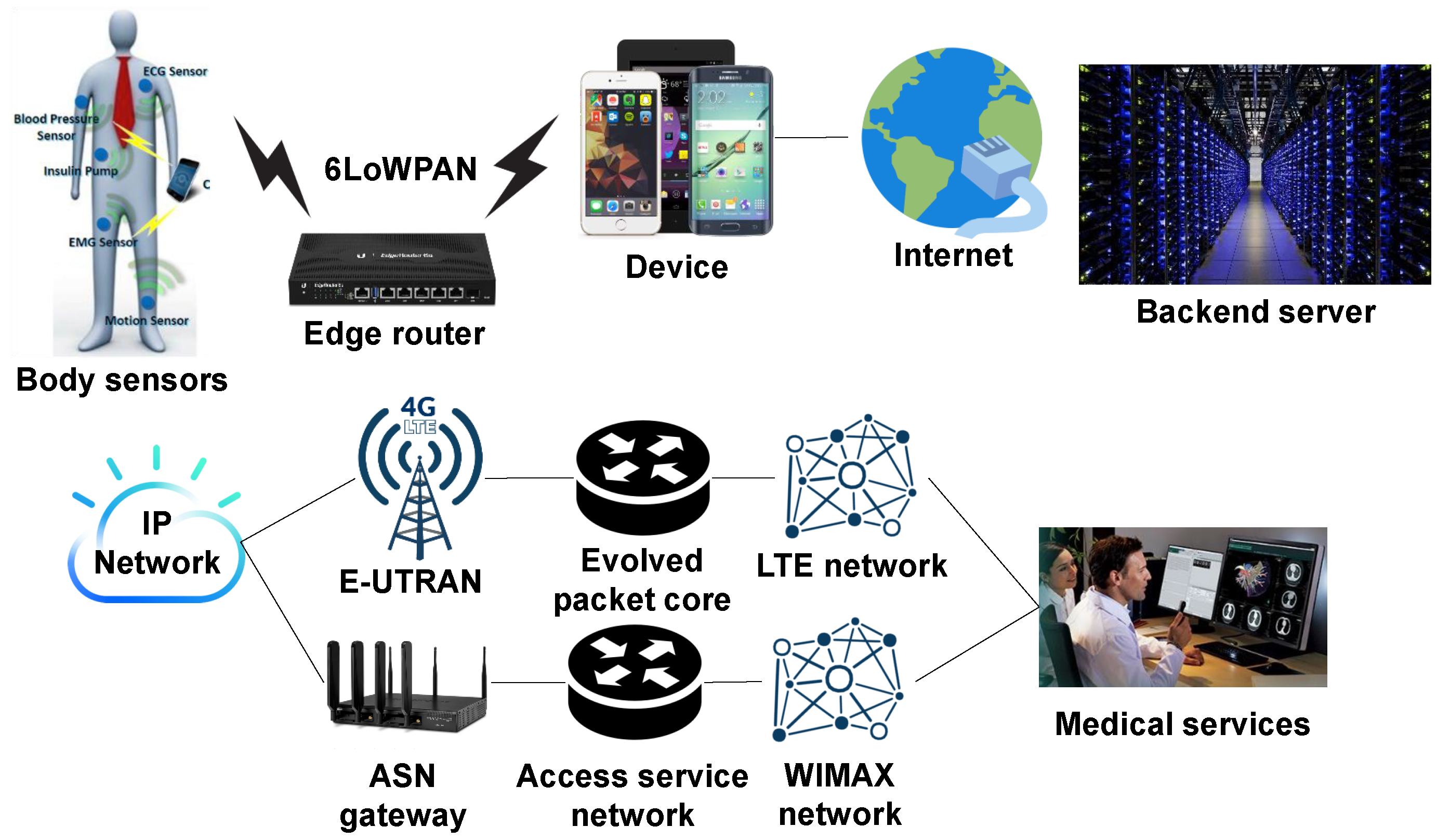
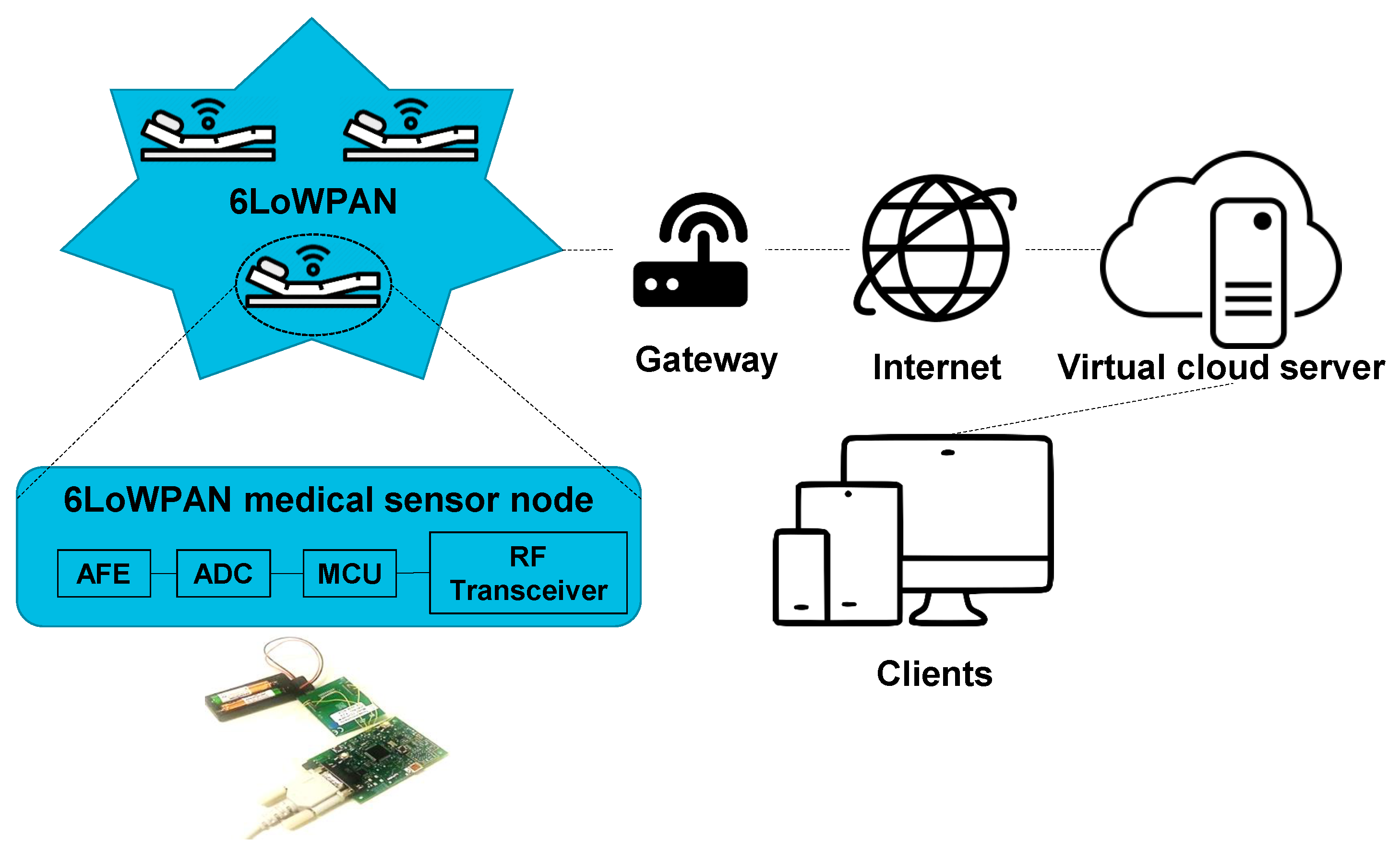
2.1.1. Short-Range Communication Techniques
2.1.2. Medium Range Communication Techniques
2.2. IoTHeF Platform
2.3. Discussion
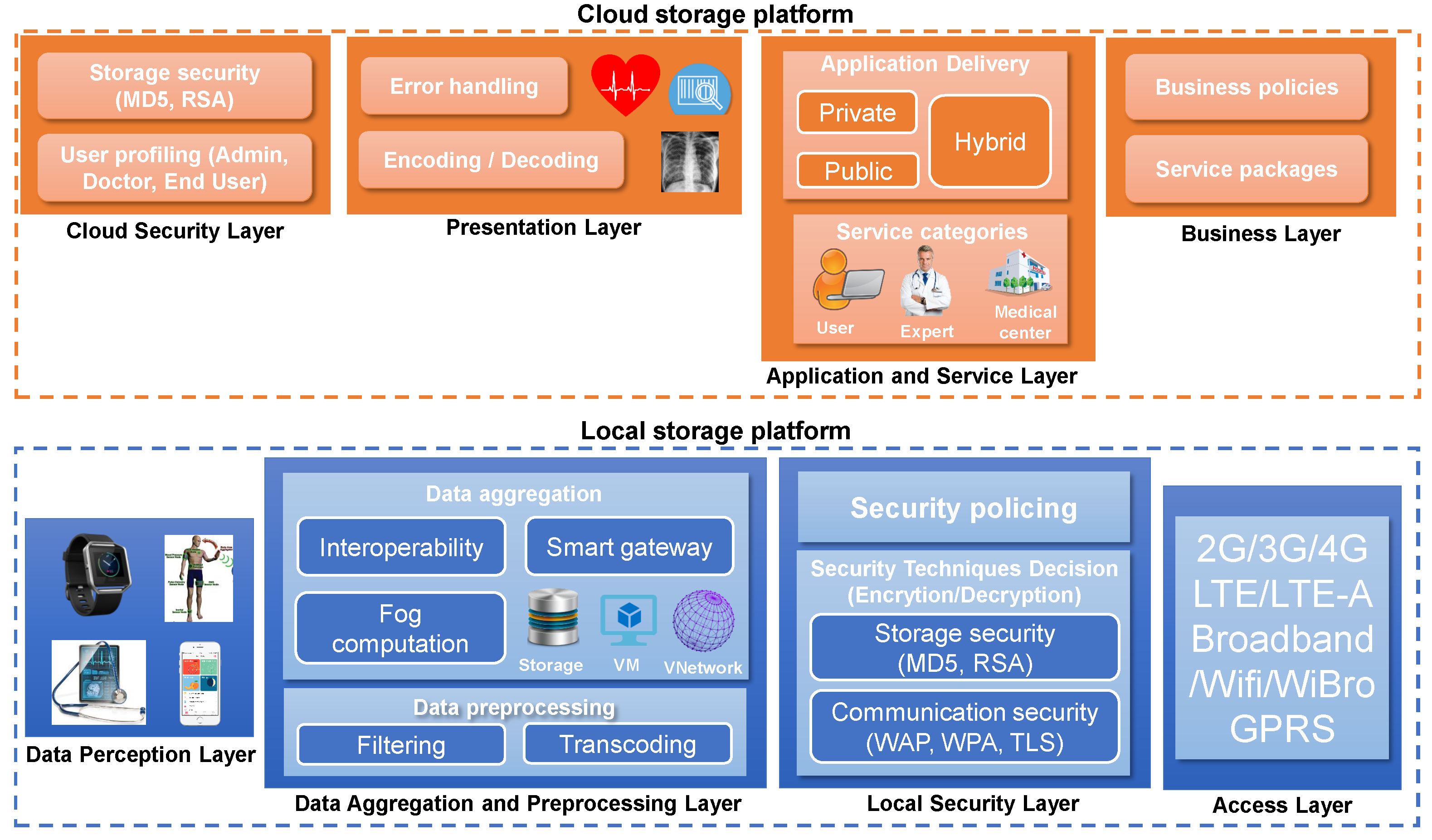
3. Cloud Computing for Heathcare
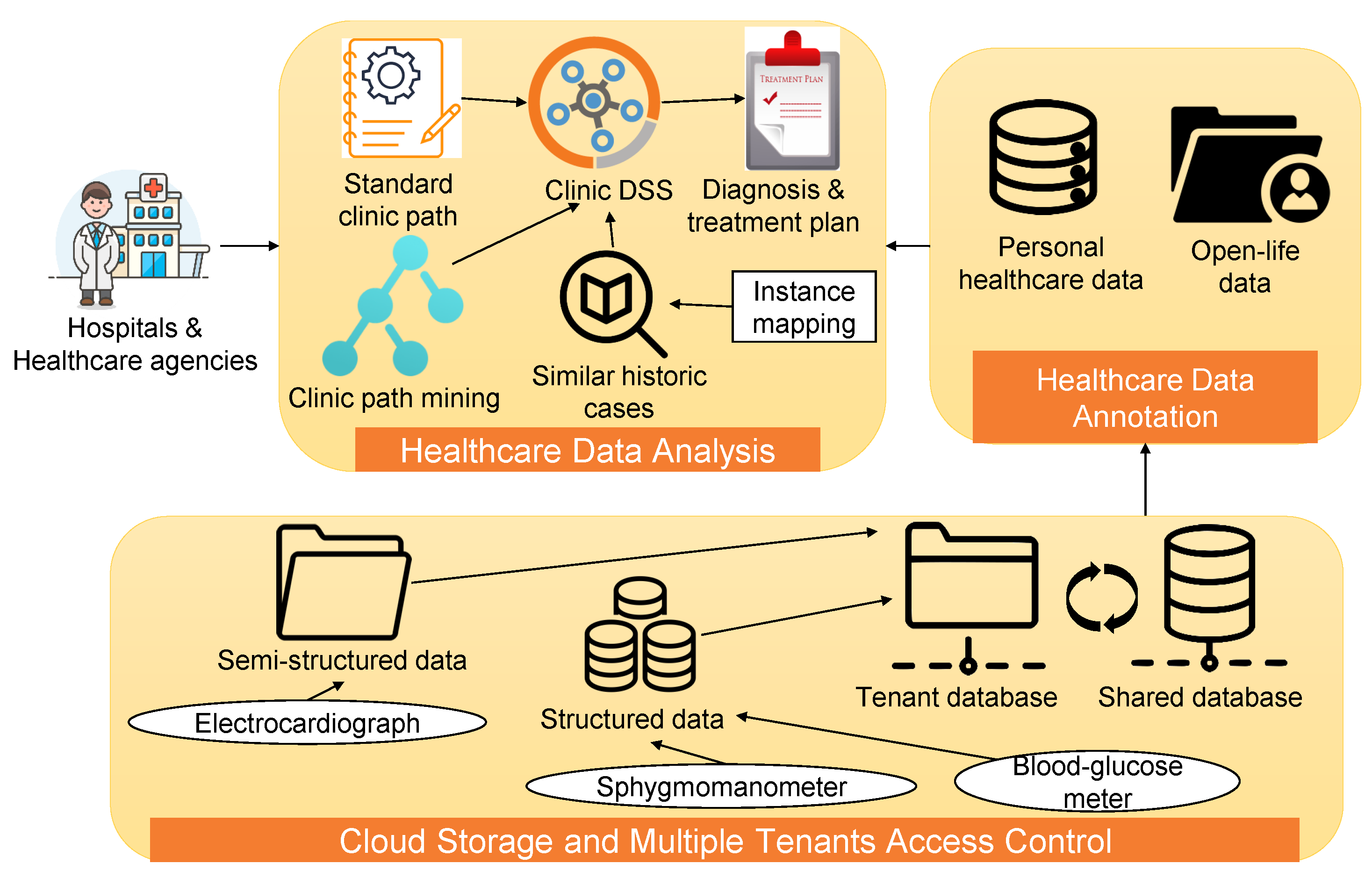
- The Cloud Storage and Multiple Tenants Access Control Layer is the backbone of the platform, which receives healthcare data collected by sensors such as BG and sphygmomanometers in daily activities. The authors reduced the cost of storing and managing data by adopting the cloud framework. Moreover, a multiple tenant access control module between tenant database and shared databased is implemented to enhance the security and privacy of patient data.
- The Healthcare Data Annotation Layer solves data heterogeneity issue that is commonly happened during data processing. Because equipment varied by hospitals, generated data are often heterogeneous, which increases the complexity of automatic healthcare data sharing and comprehending between medical agencies. The authors proposed an open Linked Life Data (LLD) sets to annotate personal healthcare data and integrate dispersed data in a patient-centric pattern for the cloud application.
- The Healthcare Data Analysis Layer analyses healthcare data stored in the cloud to assist in clinical decision making because similar historical data are valuable assets to make a treatment plan for a similar illness case. As shown in Figure 7, mining algorithms are implemented to induce clinic paths from personal healthcare data. After that, a similarity calculation module is designed to compare patients’ healthcare data with historical cases.
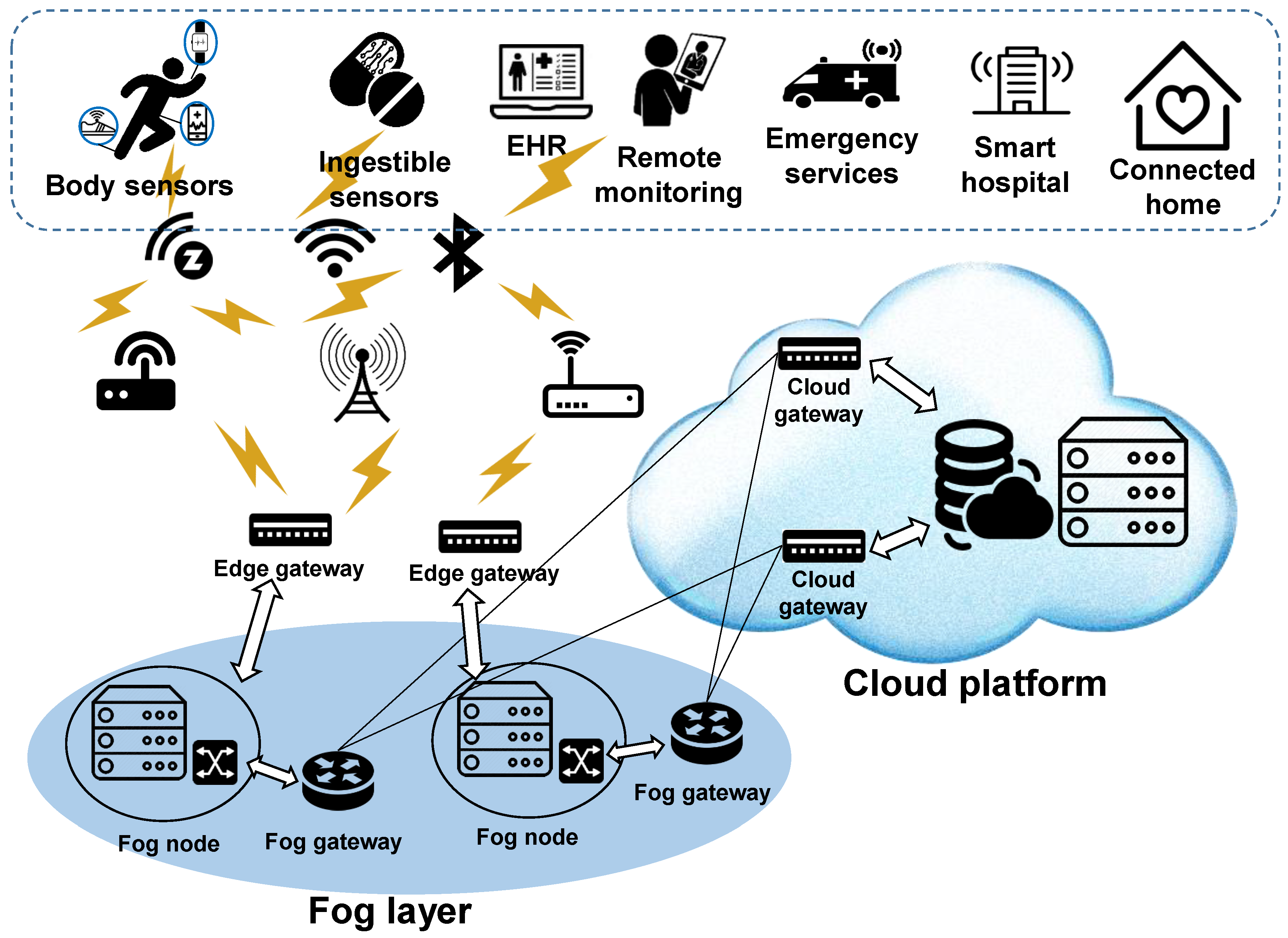
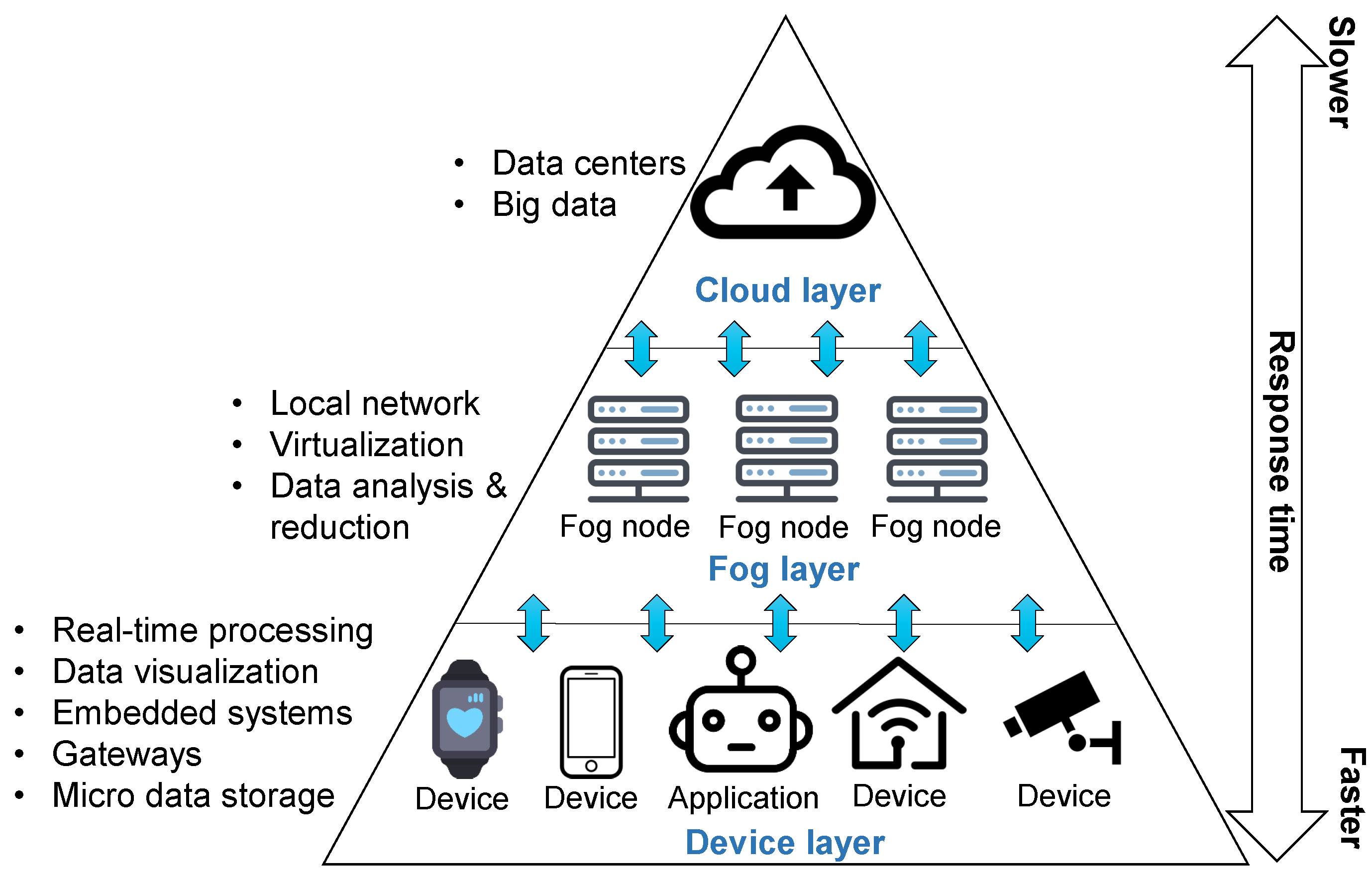
3.1. Fog Computing Architecture
- Device layer: The device layer is the closest layer to the end-users/devices. It consists of several devices, such as sensors and smart devices. These devices are widely geographically distributed and are responsible for sensing the physical object and sending data to the upper layer for processing and storage.
- Fog layer: The second layer is the fog layer located at the edge of the network, it contains a huge number of fog nodes, which commonly includes routers, gateways, access points, and base stations. Fog nodes are responsible for performing tasks such as scheduling, storing, and managing distributed computation.
- Cloud layer: The cloud layer is responsible for permanent storage and extensive computational analysis of data. Unlike traditional cloud architectures, in fog computing, the cloud layer is accessed in a periodical and controlled manner, leading to efficient utilization of all available resources.
3.2. Fog Computing in the Healthcare
3.3. Discussion
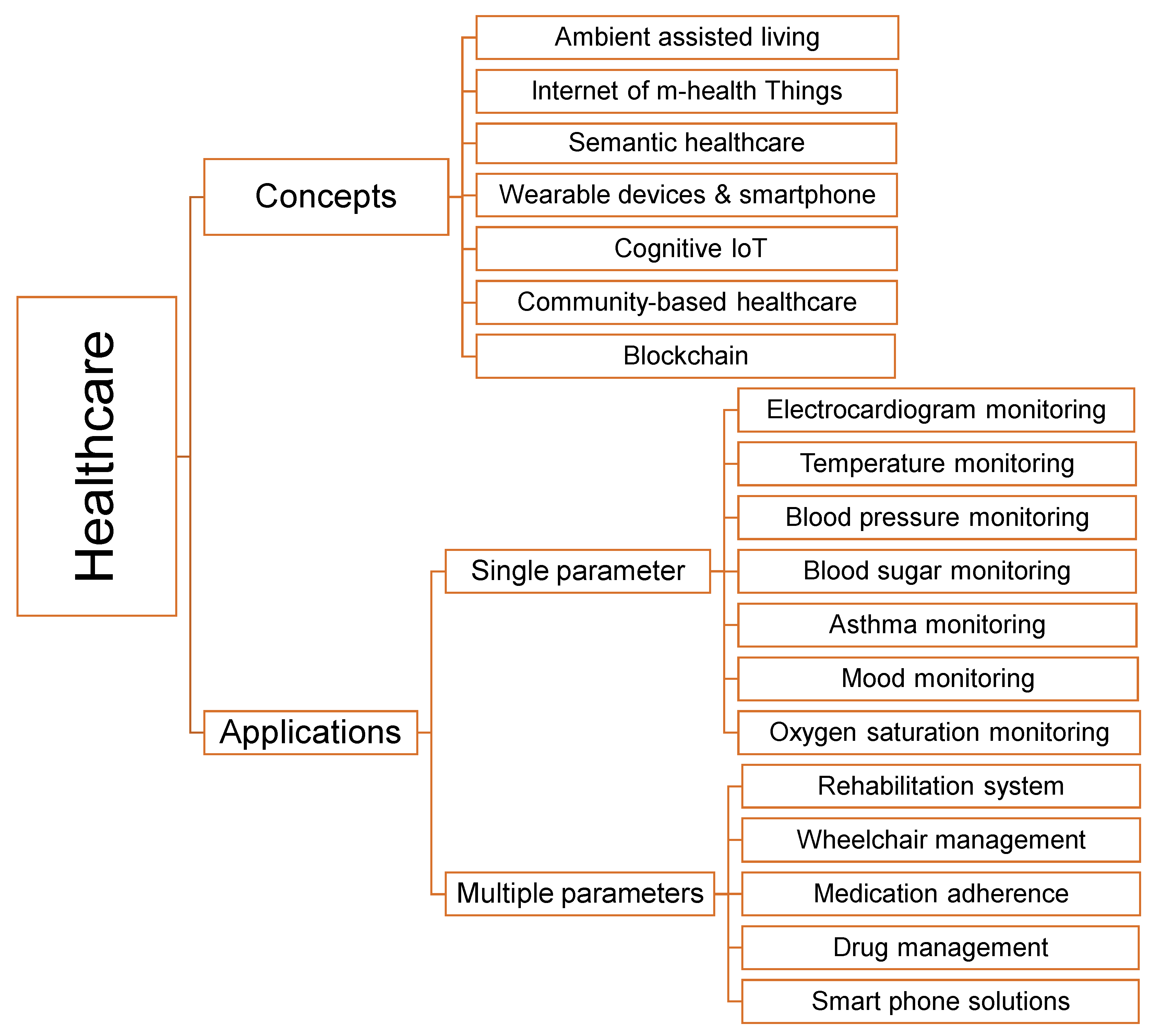
4. Heathcare Concepts and Applications
4.1. Heathcare Concepts
4.1.1. Ambient Assisted Living (AAL)
4.1.2. Internet of m-Health Things (mIoT)
4.1.3. Semantic Healthcare
4.1.4. Wearable Devices and Smart Phone
4.1.5. Cognitive IoT (CIoT)
4.1.6. Community-Based Healthcare
4.1.7. Blockchain
4.2. IoT in Heathcare Applications
4.2.1. ECG Monitoring
4.2.2. Temperature Monitoring
4.2.3. BP Monitoring
4.2.4. BG Monitoring
4.2.5. Asthma Monitoring
4.2.6. Mood Monitoring
4.2.7. Oxygen Saturation Monitoring
4.2.8. Rehabilitation System
4.2.9. Wheelchair Management
4.2.10. Medication Adherence
4.2.11. Drug Management
4.2.12. Smart Phone Solutions
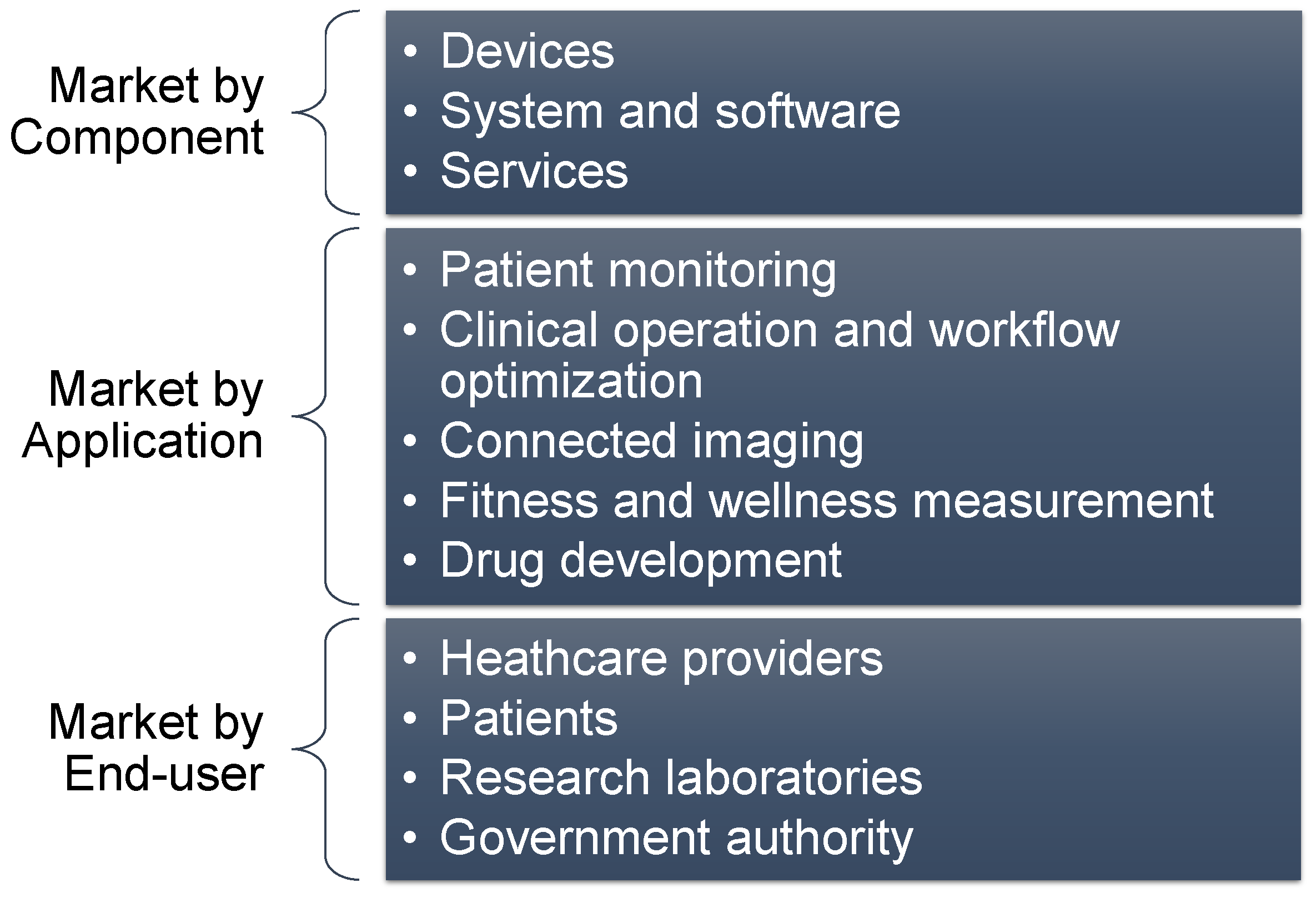
5. Latest Industry Trends in IoT and Cloud Computing in Heathcare
5.1. By Component
5.1.1. Hardware
5.1.2. Software
- Multispeciality electronic health record (EHR) solutions A multispecialty EHR brings many advantages for speciality practices expanding across many domains. It boosts the consistency and stops a patchwork approach when different EHR systems are integrated. The solution greatly reduces the extra time and cost of concatenating various groups of specialists. The multispeciality EHR solution in healthcare organizations brings higher efficiency in managing patient health record and serves various clinical requirements.
- Patient portal and self-service software Thanks to the integration of IoT and cloud computing in healthcare, patient portals are becoming the mainstream in the healthcare software market. It allows patients to interact and communicate online with responsible physicians, and the patient’s medical records are available on the internet and can be accessed at any time. Besides the patient portal, self-service software is becoming smarter, easier to use, which will eventually bring tremendous benefits to patients. Patient Kiosk software is an interesting example of self-service software because it assists patients in the identification process, hospital registration, copay payment, and paperwork.
- Blockchain solutions The role of blockchain technology in healthcare is to provide a secure mechanism for storing and sharing of medical records on the blockchain; patients and medical professionals have greater control over their information, and the sensitive data are securely protected from hackers. However, blockchain technology still needs more research and prototypes to achieve its full potential.
- Enterprise software design For years, physicians have been forced to use software that are confusing and uncomfortable. The biggest issue that leads to poor software design is the purchasing process of the enterprise. The lack of communication and market research in the developing process between developers and users.
5.2. By Application
5.2.1. Patient Monitoring
5.2.2. Telemedicine
5.2.3. Pharmaceutical Supply Chain Management
5.3. By Technology
5.3.1. Bluetooth
5.3.2. Light Fidelity (LIFI)
5.3.3. Near Field Communications (NFC)
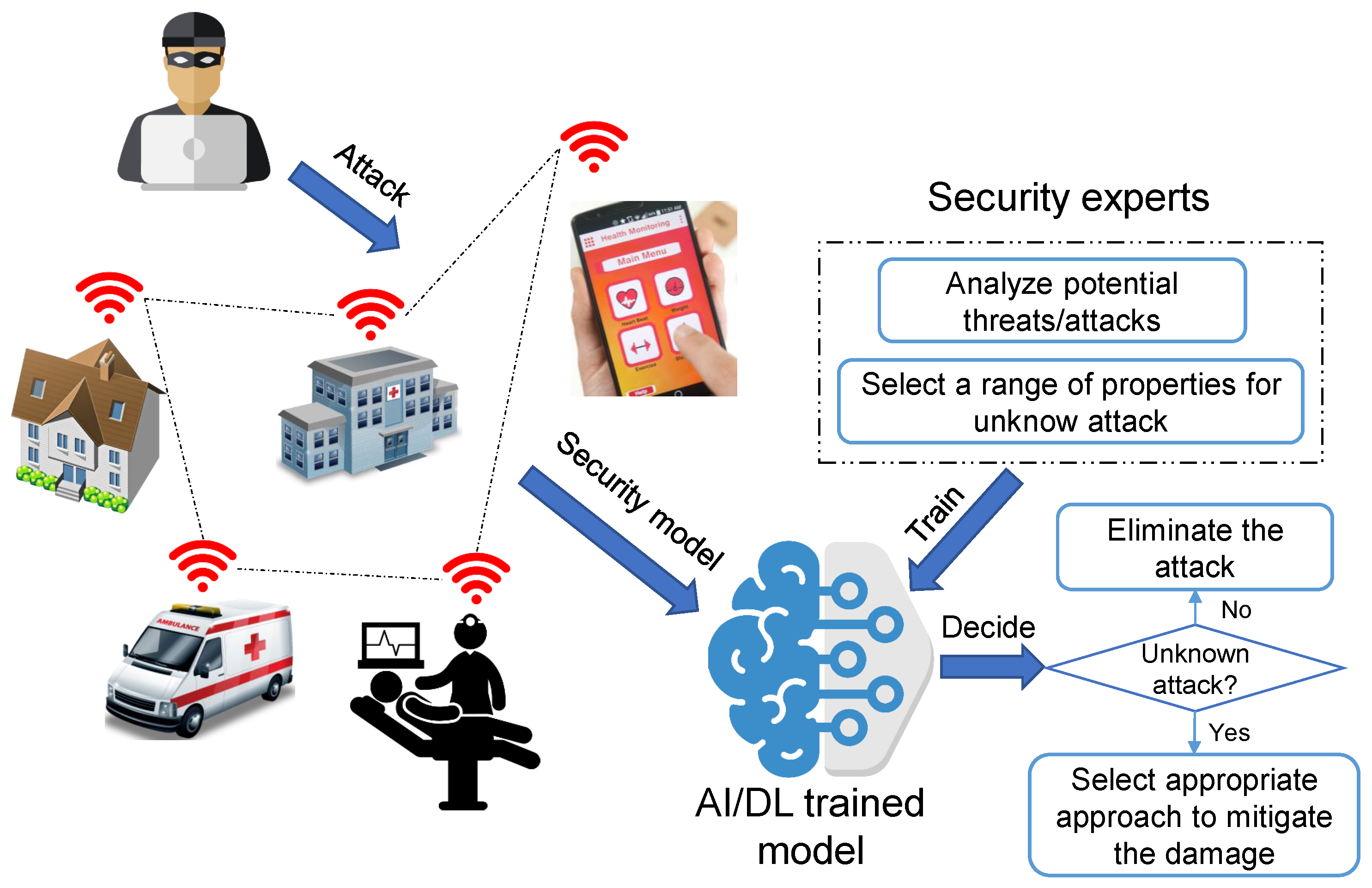
6. Security
6.1. Security Characteristics
- Authentication Authentication in the IoT network is complicated because it demands heterogeneous network authentication. Computing devices have to be recognized and validated in advance of entering the network. For the IoT network, each device has a unique identification key or a global unique identifier (UID).
- Confidentiality Confidentiality makes sure that medical information such as patient health record is protected from unauthorized users. In addition, all the confidential data must be stored safely and not be disclosed to unauthenticated identities.
- Self-Healing In case a node in an IoT network runs out of power and is broken, the remaining nodes must deliver the least security level.
- Fault tolerance If a crash happens in the network (e.g., a device failure, a software error), the system still can operate and support many security protocols.
- Resilience In case one or several points in the IoT network is damaged, the system prevents incoming attacks.
- Data freshness In a system that manages remote patient monitoring, the system has to use the latest data or information. Take an analytic of the heart functioning as an example; the system demands the most recent ECG information so it can provide the most accurate diagnostic.
- Liability For a healthcare system if any unexpected incident occurs, the system should be able to identify who will take responsibility.
- Trust In an IoT network, users or patients need to be assured that their private data will not be misused.
6.2. Security Challenges
- Memory constraints The memory of IoT devices is small, and most of the device’s memory is used to store an embedded operating system. As a result, the system that uses IoT computing devices has limited memory to perform complex security protocols.
- Speed of computation Almost all IoT computing devices have low-power processors; the processor needs to perform multiple tasks including managing, sensing, analyzing, saving, and communicating with a limited power source. Therefore, force the processor to do the security procedure is a challenging issue.
- Power consumption Most IoT devices have low battery capacity. As a result, there is a mechanism that forces them to automatically enter the power saving mode to save power at sensors’ idle time. Thus, it is difficult for IoT devices to perform security protocols all the time.
- Scalability There is a sharp rise in the number of computing devices in the IoT network. Thus, it is challenging to find the most suitable security algorithm for the growing number of devices in the IoT in the healthcare network.
- Communication channel IoT computing devices mostly participated in the network through multiple wireless communication protocols. As a result, it is challenging to find a standard security protocol that is suitable for various wireless communication protocols.
- Security updates The security framework needs to be updated frequently to minimize potential security breaches. However, automatic updates will also consume enormous power.
6.3. Threats and Attacks
6.3.1. Attack on Device (Type 1)
6.3.2. Attack on Communication Channel (Type 2)
6.3.3. Attack on Manufacturers and Cloud Providers (Type 3)
6.4. Security Model
7. IoT and Cloud Computing in Healthcare Policies
7.1. US
7.2. China
7.3. Japan
7.4. South Korea
7.5. India
7.6. Russia
7.7. Denmark
7.8. EU
8. IoT and Cloud Computing in Healthcare Challenges and Open Issues
8.1. System Development Process
8.2. Resource Management
8.3. Interoperability, Standardisation and Regulatory Issues
8.4. Data Analysis
8.4.1. Huge Volumes of Data
8.4.2. Data Complexity
8.5. Security and Privacy
8.5.1. Device Layer
8.5.2. Network Layer
8.5.3. Cloud and Fog Layers
8.6. Business Model
8.7. Transition Process
9. Conclusions
Author Contributions
Acknowledgments
Conflicts of Interest
Abbreviations
| IoT | Internet of Things |
| 6LoWPAN | IPv6 over low-power wireless personal area networks |
| AAL | Ambient assisted living |
| AES | Advanced encryption standard |
| AFE | Analog front-end |
| AI | Artificial intelligence |
| BCG | Ballistocardiography |
| BG | Blood glucose/blood sugar |
| BLE | Bluetooth low energy |
| BP | Blood pressure |
| CCTV | Closed-circuit television |
| CIoT | Cognitive IoT |
| CMRR | Common-mode rejection ratio |
| ECG | Electrocardiogram |
| EMG | Electromyography |
| EMR | Electronic medical record |
| GUI | Graphical user interface |
| HR | Heart rate |
| HTTP | Hypertext transfer protocol |
| IETF | Internet engineering task force |
| IoTHeF | IoT framework for healthcare |
| IPv4 | Internet protocol version 4 |
| IPv6 | Internet protocol version 6 |
| IR | Infrared |
| IT | Information technology |
| LIFI | Light fidelity |
| LPWAN | Low-power wide-area network |
| LTE | Long-term evolution |
| MBAN | Medical body area network |
| mIoT | Internet of m-health things |
| MIPv6 | mobile IPv6 |
| NFC | Near field communications |
| PDA | Personal digital assistants |
| PPG | Photoplethysmogram |
| RFID | Radio frequency identification |
| RR | Respiration rate |
| SIG | Bluetooth special interest group |
| SOC | Single-chip systems |
| UID | Global unique identifier |
| UTI | Urinary tract infection |
| WBAN | Wireless body area network |
| WiMAX | Microwave access |
References
- Abidi, B.; Jilbab, A.; Haziti, M.E. Wireless sensor networks in biomedical: Wireless body area networks. In Europe and MENA Cooperation Advances in Information and Communication Technologies; Springer: Berlin/Heidelberg, Germany, 2017; pp. 321–329. [Google Scholar]
- Xu, Q.; Ren, P.; Song, H.; Du, Q. Security enhancement for IoT communications exposed to eavesdroppers with uncertain locations. IEEE Access 2016, 4, 2840–2853. [Google Scholar] [CrossRef]
- Scuotto, V.; Ferraris, A.; Bresciani, S. Internet of Things: Applications and challenges in smart cities: A case study of IBM smart city projects. Bus. Process Manag. J. 2016, 22, 357–367. [Google Scholar] [CrossRef]
- Stergiou, C.; Psannis, K.E.; Kim, B.G.; Gupta, B. Secure integration of IoT and cloud computing. Future Gener. Comput. Syst. 2018, 78, 964–975. [Google Scholar] [CrossRef]
- Truong, H.L.; Dustdar, S. Principles for engineering IoT cloud systems. IEEE Cloud Comput. 2015, 2, 68–76. [Google Scholar] [CrossRef]
- Minh, D.L.; Sadeghi-Niaraki, A.; Huy, H.D.; Min, K.; Moon, H. Deep learning approach for short-term stock trends prediction based on two-stream gated recurrent unit network. IEEE Access 2018, 6, 55392–55404. [Google Scholar] [CrossRef]
- Paul, P.V.; Saraswathi, R. The Internet of Things: A comprehensive survey. In Proceedings of the 2017 International Conference on Computation of Power, Energy Information and Commuincation (ICCPEIC), Melmaruvathur, India, 22–23 March 2017; pp. 421–426. [Google Scholar]
- Chen, E.T. The Internet of Things: Opportunities, Issues, and Challenges. In The Internet of Things in the Modern Business Environment; IGI Global: Hershey, PA, USA, 2017; pp. 167–187. [Google Scholar]
- Yaqoob, I.; Ahmed, E.; Hashem, I.A.T.; Ahmed, A.I.A.; Gani, A.; Imran, M.; Guizani, M. Internet of things architecture: Recent advances, taxonomy, requirements, and open challenges. IEEE Wirel. Commun. 2017, 24, 10–16. [Google Scholar] [CrossRef]
- Lin, J.; Yu, W.; Zhang, N.; Yang, X.; Zhang, H.; Zhao, W. A survey on internet of things: Architecture, enabling technologies, security and privacy, and applications. IEEE Internet Things J. 2017, 4, 1125–1142. [Google Scholar] [CrossRef]
- Li, S.; Da Xu, L.; Zhao, S. 5G internet of things: A survey. J. Ind. Inf. Integr. 2018, 10, 1–9. [Google Scholar] [CrossRef]
- Hosseinian-Far, A.; Ramachandran, M.; Slack, C.L. Emerging Trends in Cloud Computing, Big Data, Fog Computing, IoT and Smart Living. In Technology for Smart Futures; Springer: Berlin/Heidelberg, Germany, 2018; pp. 29–40. [Google Scholar]
- Dang, L.M.; Hassan, S.I.; Im, S.; Moon, H. Face image manipulation detection based on a convolutional neural network. Expert Syst. Appl. 2019, 129, 156–168. [Google Scholar] [CrossRef]
- Nguyen, T.N.; Thai, C.H.; Luu, A.T.; Nguyen-Xuan, H.; Lee, J. NURBS-based postbuckling analysis of functionally graded carbon nanotube-reinforced composite shells. Comput. Methods Appl. Mech. Eng. 2019, 347, 983–1003. [Google Scholar] [CrossRef]
- Nguyen, T.N.; Thai, C.H.; Nguyen-Xuan, H.; Lee, J. NURBS-based analyses of functionally graded carbon nanotube-reinforced composite shells. Compos. Struct. 2018, 203, 349–360. [Google Scholar] [CrossRef]
- Nguyen, T.N.; Lee, S.; Nguyen-Xuan, H.; Lee, J. A novel analysis-prediction approach for geometrically nonlinear problems using group method of data handling. Comput. Methods Appl. Mech. Eng. 2019, 354, 506–526. [Google Scholar] [CrossRef]
- Dang, L.M.; Hassan, S.I.; Im, S.; Mehmood, I.; Moon, H. Utilizing text recognition for the defects extraction in sewers CCTV inspection videos. Comput. Ind. 2018, 99, 96–109. [Google Scholar] [CrossRef]
- Internet of Things at a Glance. Available online: https://www.cisco.com/c/dam/en/us/products/collateral/se/internet-of-things/at-a-glance-c45-731471.pdf (accessed on 23 February 2019).
- Size of the Internet of Things Market Worldwide in 2014 and 2020, by Industry. Available online: https://www.statista.com/statistics/512673/worldwide-internet-of-things-market/ (accessed on 24 February 2019).
- Islam, S.R.; Kwak, D.; Kabir, M.H.; Hossain, M.; Kwak, K.S. The internet of things for health care: A comprehensive survey. IEEE Access 2015, 3, 678–708. [Google Scholar] [CrossRef]
- Mutlag, A.A.; Ghani, M.K.A.; Arunkumar, N.; Mohamed, M.A.; Mohd, O. Enabling technologies for fog computing in healthcare IoT systems. Future Gener. Comput. Syst. 2019, 90, 62–78. [Google Scholar] [CrossRef]
- Kumari, A.; Tanwar, S.; Tyagi, S.; Kumar, N. Fog computing for Healthcare 4.0 environment: Opportunities and challenges. Comput. Electr. Eng. 2018, 72, 1–13. [Google Scholar] [CrossRef]
- García-Valls, M.; Calva-Urrego, C.; García-Fornes, A. Accelerating smart eHealth services execution at the fog computing infrastructure. Future Gener. Comput. Syst. 2018. [Google Scholar] [CrossRef]
- Kraemer, F.A.; Braten, A.E.; Tamkittikhun, N.; Palma, D. Fog computing in healthcare—A review and discussion. IEEE Access 2017, 5, 9206–9222. [Google Scholar] [CrossRef]
- Ahmadi, H.; Arji, G.; Shahmoradi, L.; Safdari, R.; Nilashi, M.; Alizadeh, M. The application of internet of things in healthcare: A systematic literature review and classification. Univer. Access Inf. Soc. 2018, 1–33. [Google Scholar] [CrossRef]
- Baker, S.B.; Xiang, W.; Atkinson, I. Internet of Things for Smart Healthcare: Technologies, Challenges, and Opportunities. IEEE Access 2017, 5, 26521–26544. [Google Scholar] [CrossRef]
- Farahani, B.; Firouzi, F.; Chang, V.; Badaroglu, M.; Constant, N.; Mankodiya, K. Towards fog-driven IoT eHealth: Promises and challenges of IoT in medicine and healthcare. Future Gener. Comput. Syst. 2018, 78, 659–676. [Google Scholar] [CrossRef]
- Yang, Z.; Zhou, Q.; Lei, L.; Zheng, K.; Xiang, W. An IoT-cloud based wearable ECG monitoring system for smart healthcare. J. Med. Syst. 2016, 40, 286. [Google Scholar] [CrossRef]
- Almotiri, S.H.; Khan, M.A.; Alghamdi, M.A. Mobile health (m-health) system in the context of IoT. In Proceedings of the IEEE International Conference on Future Internet of Things and Cloud Workshops (FiCloudW), Vienna, Austria, 22–24 August 2016; pp. 39–42. [Google Scholar]
- Oryema, B.; Kim, H.S.; Li, W.; Park, J.T. Design and implementation of an interoperable messaging system for IoT healthcare services. In Proceedings of the 2017 14th IEEE Annual Consumer Communications & Networking Conference (CCNC), Las Vegas, NV, USA, 8–11 January 2017; pp. 45–52. [Google Scholar]
- Abideen, Z.U.; Shah, M.A. An IoT based robust healthcare model for continuous health monitoring. In Proceedings of the 2017 23rd International Conference on Automation and Computing (ICAC), Huddersfield, UK, 7–8 September 2017; pp. 1–6. [Google Scholar]
- Gia, T.N.; Jiang, M.; Rahmani, A.M.; Westerlund, T.; Liljeberg, P.; Tenhunen, H. Fog computing in healthcare internet of things: A case study on ecg feature extraction. In Proceedings of the 2015 IEEE International Conference on Computer and Information Technology; Ubiquitous Computing and Communications; Dependable, Autonomic and Secure Computing; Pervasive Intelligence and Computing (CIT/IUCC/DASC/PICOM), Liverpool, UK, 26–28 October 2015; pp. 356–363. [Google Scholar]
- Rashed, A.; Ibrahim, A.; Adel, A.; Mourad, B.; Hatem, A.; Magdy, M.; Elgaml, N.; Khattab, A. Integrated IoT medical platform for remote healthcare and assisted living. In Proceedings of the 2017 Japan-Africa Conference on Electronics, Communications and Computers (JAC-ECC), Alexandria, Egypt, 18–20 December 2017; pp. 160–163. [Google Scholar]
- Rahmani, A.M.; Gia, T.N.; Negash, B.; Anzanpour, A.; Azimi, I.; Jiang, M.; Liljeberg, P. Exploiting smart e-Health gateways at the edge of healthcare Internet-of-Things: A fog computing approach. Future Gener. Comput. Syst. 2018, 78, 641–658. [Google Scholar] [CrossRef]
- Reda, R.; Piccinini, F.; Carbonaro, A. Semantic Modelling of Smart Healthcare Data. In Proceedings of SAI Intelligent Systems Conference; Springer: Berlin/Heidelberg, Germany, 2018; pp. 399–411. [Google Scholar]
- Abawajy, J.H.; Hassan, M.M. Federated internet of things and cloud computing pervasive patient health monitoring system. IEEE Commun. Mag. 2017, 55, 48–53. [Google Scholar] [CrossRef]
- Jabbar, S.; Ullah, F.; Khalid, S.; Khan, M.; Han, K. Semantic interoperability in heterogeneous IoT infrastructure for healthcare. Wirel. Commun. Mob. Comput. 2017, 2017, 9731806. [Google Scholar] [CrossRef]
- Gia, T.N.; Thanigaivelan, N.K.; Rahmani, A.M.; Westerlund, T.; Liljeberg, P.; Tenhunen, H. Customizing 6LoWPAN networks towards Internet-of-Things based ubiquitous healthcare systems. In Proceedings of the 2014 NORCHIP, Tampere, Finland, 27–28 October 2014; pp. 1–6. [Google Scholar]
- Ronen, E.; Shamir, A.; Weingarten, A.O.; O’Flynn, C. IoT goes nuclear: Creating a ZigBee chain reaction. In Proceedings of the 2017 IEEE Symposium on Security and Privacy (SP), San Jose, CA, USA, 22–26 May 2017; pp. 195–212. [Google Scholar]
- Al-Kashoash, H.; Kemp, A.H. Comparison of 6LoWPAN and LPWAN for the Internet of Things. Aust. J. Electr. Electron. Eng. 2016, 13, 268–274. [Google Scholar] [CrossRef]
- Gomes, T.; Salgado, F.; Pinto, S.; Cabral, J.; Tavares, A. A 6LoWPAN accelerator for Internet of Things endpoint devices. IEEE Internet Things J. 2018, 5, 371–377. [Google Scholar] [CrossRef]
- Lee, J.L.; Tyan, Y.Y.; Wen, M.H.; Wu, Y.W. Development of an IoT-based bridge safety monitoring system. In Proceedings of the 2017 International Conference on Applied System Innovation (ICASI), Sapporo, Japan, 13–17 May 2017; pp. 84–86. [Google Scholar]
- Arndt, J.; Krause, F.; Wunderlich, R.; Heinen, S. Development of a 6LoWPAN sensor node for IoT based home automation networks. In Proceedings of the 2017 International Conference on Research and Education in Mechatronics (REM), Wolfenbuttel, Germany, 14–15 September 2017; pp. 1–4. [Google Scholar]
- You, I.; Leu, F.Y. Comments on “SPAM: A Secure Password Authentication Mechanism for Seamless Handover in Proxy Mobile IPv6 Networks”. IEEE Syst. J. 2018, 12, 1038–1041. [Google Scholar] [CrossRef]
- Fotouhi, H.; Moreira, D.; Alves, M.; Yomsi, P.M. mRPL+: A mobility management framework in RPL/6LoWPAN. Comput. Commun. 2017, 104, 34–54. [Google Scholar] [CrossRef]
- Ha, M.; Kim, S.H.; Kim, D. Intra-MARIO: A Fast Mobility Management Protocol for 6LoWPAN. IEEE Trans. Mob. Comput. 2017, 16, 172–184. [Google Scholar] [CrossRef]
- Xiaonan, W.; Hongbin, C. Research on seamless mobility handover for 6LoWPAN wireless sensor networks. Telecommun. Syst. 2016, 61, 141–157. [Google Scholar] [CrossRef]
- Miranda, J.; Cabral, J.; Wagner, S.R.; Fischer Pedersen, C.; Ravelo, B.; Memon, M.; Mathiesen, M. An open platform for seamless sensor support in healthcare for the internet of things. Sensors 2016, 16, 2089. [Google Scholar] [CrossRef] [PubMed]
- Ali, M.; Bilal, H.S.M.; Razzaq, M.A.; Khan, J.; Lee, S.; Idris, M.; Aazam, M.; Choi, T.; Han, S.C.; Kang, B.H. IoTFLiP: IoT-based flipped learning platform for medical education. Digit. Commun. Netw. 2017, 3, 188–194. [Google Scholar] [CrossRef]
- Verma, P.; Sood, S.K.; Kalra, S. Cloud-centric IoT based student healthcare monitoring framework. J. Ambient Intell. Humaniz. Comput. 2018, 9, 1293–1309. [Google Scholar] [CrossRef]
- Manashty, A.; Light, J.; Yadav, U. Healthcare event aggregation lab (HEAL), a knowledge sharing platform for anomaly detection and prediction. In Proceedings of the 2015 17th International Conference on E-health Networking, Application & Services (HealthCom), Boston, MA, USA, 14–17 October 2015; pp. 648–652. [Google Scholar]
- Pace, P.; Aloi, G.; Gravina, R.; Fortino, G.; Larini, G.; Gulino, M. Towards interoperability of IoT-based health care platforms: The INTER-health use case. In Proceedings of the 11th EAI International Conference on Body Area Networks, Turin, Italy, 15–16 December 2016; pp. 12–18. [Google Scholar]
- Sultan, N. Making use of cloud computing for healthcare provision: Opportunities and challenges. Int. J. Inf. Manag. 2014, 34, 177–184. [Google Scholar] [CrossRef]
- Darwish, A.; Hassanien, A.E.; Elhoseny, M.; Sangaiah, A.K.; Muhammad, K. The impact of the hybrid platform of internet of things and cloud computing on healthcare systems: Opportunities, challenges, and open problems. J. Ambient Intell. Humaniz. Comput. 2017, 1–16. [Google Scholar] [CrossRef]
- Xu, B.; Xu, L.; Cai, H.; Jiang, L.; Luo, Y.; Gu, Y. The design of an m-Health monitoring system based on a cloud computing platform. Enterp. Inf. Syst. 2017, 11, 17–36. [Google Scholar] [CrossRef]
- Singh, D.; Tripathi, G.; Alberti, A.M.; Jara, A. Semantic edge computing and IoT architecture for military health services in battlefield. In Proceedings of the 2017 14th IEEE Annual Consumer Communications & Networking Conference (CCNC), Las Vegas, NV, USA, 8–11 January 2017; pp. 185–190. [Google Scholar]
- Yang, G.; Xie, L.; Mäntysalo, M.; Zhou, X.; Pang, Z.; Da Xu, L.; Kao-Walter, S.; Chen, Q.; Zheng, L.R. A health-IoT platform based on the integration of intelligent packaging, unobtrusive bio-sensor, and intelligent medicine box. IEEE Trans. Ind. Inform. 2014, 10, 2180–2191. [Google Scholar] [CrossRef]
- Corcoran, P.; Datta, S.K. Mobile-edge computing and the Internet of Things for consumers: Extending cloud computing and services to the edge of the network. IEEE Consum. Electron. Mag. 2016, 5, 73–74. [Google Scholar] [CrossRef]
- Dastjerdi, A.V.; Buyya, R. Fog computing: Helping the Internet of Things realize its potential. Computer 2016, 49, 112–116. [Google Scholar] [CrossRef]
- Solutions, C.F.C. Unleash the Power of the Internet of Things; Cisco Systems, Inc.: San Jose, CA, USA, 2015. [Google Scholar]
- Devarajan, M.; Subramaniyaswamy, V.; Vijayakumar, V.; Ravi, L. Fog-assisted personalized healthcare-support system for remote patients with diabetes. J. Ambient Intell. Humaniz. Comput. 2019, 1–14. [Google Scholar] [CrossRef]
- Sood, S.K.; Mahajan, I. IoT-Fog based Healthcare Framework to Identify and Control Hypertension Attack. IEEE Internet Things J. 2018, 6, 1920–1927. [Google Scholar] [CrossRef]
- Bhatia, M.; Sood, S.K. Exploring temporal analytics in fog-cloud architecture for Smart Office HealthCare. Mob. Netw. Appl. 2018, 1–19. [Google Scholar] [CrossRef]
- Sharma, S.; Chen, K.; Sheth, A. Toward practical privacy-preserving analytics for iot and cloud-based healthcare systems. IEEE Internet Comput. 2018, 22, 42–51. [Google Scholar] [CrossRef]
- Hu, P.; Dhelim, S.; Ning, H.; Qiu, T. Survey on fog computing: Architecture, key technologies, applications and open issues. J. Netw. Comput. Appl. 2017, 98, 27–42. [Google Scholar] [CrossRef]
- Negash, B.; Gia, T.N.; Anzanpour, A.; Azimi, I.; Jiang, M.; Westerlund, T.; Rahmani, A.M.; Liljeberg, P.; Tenhunen, H. Leveraging fog computing for healthcare iot. In Fog Computing in the Internet of Things; Springer: Berlin/Heidelberg, Germany, 2018; pp. 145–169. [Google Scholar]
- Ahmad, M.; Amin, M.B.; Hussain, S.; Kang, B.H.; Cheong, T.; Lee, S. Health Fog: A novel framework for health and wellness applications. J. Supercomput. 2016, 72, 3677–3695. [Google Scholar] [CrossRef]
- Nandyala, C.S.; Kim, H.K. From cloud to fog and IoT-based real-time U-healthcare monitoring for smart homes and hospitals. Int. J. Smart Home 2016, 10, 187–196. [Google Scholar] [CrossRef]
- Tang, W.; Zhang, K.; Zhang, D.; Ren, J.; Zhang, Y.; Shen, X.S. Fog-Enabled Smart Health: Toward Cooperative and Secure Healthcare Service Provision. IEEE Commun. Mag. 2019, 57, 42–48. [Google Scholar] [CrossRef]
- Wang, K.; Shao, Y.; Xie, L.; Wu, J.; Guo, S. Adaptive and Fault-tolerant Data Processing in Healthcare IoT Based on Fog Computing. IEEE Trans. Netw. Sci. Eng. 2018. [Google Scholar] [CrossRef]
- Sood, S.K.; Mahajan, I. A fog-based healthcare framework for chikungunya. IEEE Internet Things J. 2018, 5, 794–801. [Google Scholar] [CrossRef]
- Srinivas, J.; Das, A.K.; Kumar, N.; Rodrigues, J. Cloud centric authentication for wearable healthcare monitoring system. IEEE Trans. Depend. Secur. Comput. 2018. [Google Scholar] [CrossRef]
- Vijayakumar, V.; Malathi, D.; Subramaniyaswamy, V.; Saravanan, P.; Logesh, R. Fog computing-based intelligent healthcare system for the detection and prevention of mosquito-borne diseases. Comput. Human Behav. 2018. [Google Scholar] [CrossRef]
- Konstantinidis, E.I.; Antoniou, P.E.; Bamparopoulos, G.; Bamidis, P.D. A lightweight framework for transparent cross platform communication of controller data in ambient assisted living environments. Inf. Sci. 2015, 300, 124–139. [Google Scholar] [CrossRef]
- De Venuto, D.; Annese, V.F.; Sangiovanni-Vincentelli, A.L. The ultimate IoT application: A cyber-physical system for ambient assisted living. In Proceedings of the 2016 IEEE International Symposium on Circuits and Systems (ISCAS), Montreal, QC, Canada, 22–25 May 2016; pp. 2042–2045. [Google Scholar]
- Zgheib, R.; De Nicola, A.; Villani, M.L.; Conchon, E.; Bastide, R. A flexible architecture for cognitive sensing of activities in ambient assisted living. In Proceedings of the 2017 IEEE 26th International Conference on Enabling Technologies: Infrastructure for Collaborative Enterprises (WETICE), Poznan, Poland, 21–23 June 2017; pp. 284–289. [Google Scholar]
- Corno, F.; De Russis, L.; Roffarello, A.M. A healthcare support system for assisted living facilities: An iot solution. In Proceedings of the 2016 IEEE 40th Annual Computer Software and Applications Conference (COMPSAC), Atlanta, GA, USA, 10–14 June 2016; Volume 1, pp. 344–352. [Google Scholar]
- Tariq, M.; Majeed, H.; Beg, M.O.; Khan, F.A.; Derhab, A. Accurate detection of sitting posture activities in a secure IoT based assisted living environment. Future Gener. Comput. Syst. 2018, 92, 745–757. [Google Scholar] [CrossRef]
- Rghioui, A.; Sendra, S.; Lloret, J.; Oumnad, A. Internet of things for measuring human activities in ambient assisted living and e-health. In Network Protocols and Algorithms; Macrothink Institute: Las Vegas, NV, USA, 2016; Volume 8, pp. 15–28. [Google Scholar]
- Mainetti, L.; Manco, L.; Patrono, L.; Secco, A.; Sergi, I.; Vergallo, R. An ambient assisted living system for elderly assistance applications. In Proceedings of the 2016 IEEE 27th Annual International Symposium on Personal, Indoor, and Mobile Radio Communications (PIMRC), Valencia, Spain, 4–8 September 2016; pp. 1–6. [Google Scholar]
- Konstantinidis, E.I.; Bamparopoulos, G.; Billis, A.; Bamidis, P.D. Internet of things for an age-friendly healthcare. Stud. Health Technol. Inform. 2015, 587–591. [Google Scholar] [CrossRef]
- Marques, G.; Pitarma, R. An indoor monitoring system for ambient assisted living based on internet of things architecture. Int. J. Environ. Res. Public Health 2016, 13, 1152. [Google Scholar] [CrossRef]
- Erdeniz, S.P.; Maglogiannis, I.; Menychtas, A.; Felfernig, A.; Tran, T.N.T. Recommender Systems for IoT Enabled m-Health Applications. In Proceedings of the IFIP International Conference on Artificial Intelligence Applications and Innovations, Rhodes, Greece, 25–27 May 2018; pp. 227–237. [Google Scholar]
- Ullah, F.; Habib, M.A.; Farhan, M.; Khalid, S.; Durrani, M.Y.; Jabbar, S. Semantic interoperability for big-data in heterogeneous IoT infrastructure for healthcare. Sustain. Cities Soc. 2017, 34, 90–96. [Google Scholar] [CrossRef]
- Kelati, A.; Dhaou, I.B.; Tenhunen, H. Biosignal Monitoring Platform Using Wearable IoT. In Proceedings of the 22st Conference of Open Innovations Association FRUCT, Petrozavodsk, Russia, 9–13 April 2018; p. 47. [Google Scholar]
- Zgheib, R.; Conchon, E.; Bastide, R. Engineering IoT healthcare applications: Towards a semantic data driven sustainable architecture. In eHealth 360; Springer: Berlin/Heidelberg, Germany, 2017; pp. 407–418. [Google Scholar]
- Catherwood, P.A.; Steele, D.; Little, M.; Mccomb, S.; Mclaughlin, J. A Community-Based IoT Personalized Wireless Healthcare Solution Trial. IEEE J. Transl. Eng. Health Med. 2018, 6, 1–13. [Google Scholar] [CrossRef] [PubMed]
- Kumar, T.; Ramani, V.; Ahmad, I.; Braeken, A.; Harjula, E.; Ylianttila, M. Blockchain Utilization in Healthcare: Key Requirements and Challenges. In Proceedings of the 2018 IEEE 20th International Conference on e-Health Networking, Applications and Services (Healthcom), Ostrava, Czech Republic, 17–20 September 2018; pp. 1–7. [Google Scholar]
- Zheng, Z.; Xie, S.; Dai, H.; Chen, X.; Wang, H. An overview of blockchain technology: Architecture, consensus, and future trends. In Proceedings of the 2017 IEEE International Congress on Big Data (BigData Congress), Honolulu, HI, USA, 25–30 June 2017; pp. 557–564. [Google Scholar]
- Griggs, K.N.; Ossipova, O.; Kohlios, C.P.; Baccarini, A.N.; Howson, E.A.; Hayajneh, T. Healthcare Blockchain System Using Smart Contracts for Secure Automated Remote Patient Monitoring. J. Med. Syst. 2018, 42, 130. [Google Scholar] [CrossRef]
- Bhuiyan, M.Z.A.; Zaman, A.; Wang, T.; Wang, G.; Tao, H.; Hassan, M.M. Blockchain and Big Data to Transform the Healthcare. In Proceedings of the International Conference on Data Processing and Applications, Guangzhou, China, 12–14 May 2018; pp. 62–68. [Google Scholar]
- Gia, T.N.; Ali, M.; Dhaou, I.B.; Rahmani, A.M.; Westerlund, T.; Liljeberg, P.; Tenhunen, H. IoT-based continuous glucose monitoring system: A feasibility study. Procedia Comput. Sci. 2017, 109, 327–334. [Google Scholar] [CrossRef]
- Sunny, S.; Kumar, S.S. Optical based non invasive glucometer with IoT. In Proceedings of the 2018 International Conference on Power, Signals, Control and Computation (EPSCICON), Thrissur, India, 6–10 January 2018; pp. 1–3. [Google Scholar]
- AL-Jaf, T.G.; Al-Hemiary, E.H. Internet of Things Based Cloud Smart Monitoring for Asthma Patient. In Proceedings of the 1 st International Conference on Information Technology (ICoIT’17), Erbil, Iraq, 10 April 2017; p. 380. [Google Scholar]
- Raji, A.; Devi, P.K.; Jeyaseeli, P.G.; Balaganesh, N. Respiratory monitoring system for asthma patients based on IoT. In Proceedings of the 2016 Online International Conference on Green Engineering and Technologies (IC-GET), Coimbatore, India, 19 November 2016; pp. 1–6. [Google Scholar]
- Satija, U.; Ramkumar, B.; Manikandan, M.S. Real-time signal quality-aware ECG telemetry system for IoT-based health care monitoring. IEEE Internet Things J. 2017, 4, 815–823. [Google Scholar] [CrossRef]
- Beach, C.; Krachunov, S.; Pope, J.; Fafoutis, X.; Piechocki, R.J.; Craddock, I.; Casson, A.J. An ultra low power personalizable wrist worn ECG monitor integrated with IoT infrastructure. IEEE Access 2018, 6, 44010–44021. [Google Scholar] [CrossRef]
- Sobya, D.; Muruganandham, S.; Nallusamy, S.; Chakraborty, P. Wireless ECG Monitoring System using IoT based Signal Conditioning Module For Real Time Signal Acquisition. Indian J. Public Health Res. Dev. 2018, 9, 294–299. [Google Scholar] [CrossRef]
- He, J.; Rong, J.; Sun, L.; Wang, H.; Zhang, Y.; Ma, J. D-ECG: A Dynamic Framework for Cardiac Arrhythmia Detection from IoT-Based ECGs. In Proceedings of the International Conference on Web Information Systems Engineering, Dubai, UAE, 12–15 November 2018; pp. 85–99. [Google Scholar]
- Bansal, M.; Gandhi, B. IoT based smart health care system using CNT electrodes (for continuous ECG monitoring). In Proceedings of the 2017 International Conference on Computing, Communication and Automation (ICCCA), Greater Noida, India, 5–6 May 2017; pp. 1324–1329. [Google Scholar]
- Xin, Q.; Wu, J. A novel wearable device for continuous, non-invasion blood pressure measurement. Comput. Biol. Chem. 2017, 69, 134–137. [Google Scholar] [CrossRef] [PubMed]
- Chao, P.C.P.; Tu, T.Y. Using the Time-Domain Characterization for Estimation Continuous Blood Pressure via Neural Network Method. In Proceedings of the ASME 2017 Conference on Information Storage and Processing Systems collocated with the ASME 2017 Conference on Information Storage and Processing Systems, San Francisco, CA, USA, 29–30 August 2017; p. V001T02A003. [Google Scholar]
- Dinh, A.; Luu, L.; Cao, T. Blood Pressure Measurement Using Finger ECG and Photoplethysmogram for IoT. In Proceedings of the International Conference on the Development of Biomedical Engineering in Vietnam, Ho Chi Minh, Vietnam, 27–29 June 2017; pp. 83–89. [Google Scholar]
- Huang, M.; Tamura, T.; Tang, Z.; Chen, W.; Kanaya, S. A Wearable Thermometry for Core Body Temperature Measurement and Its Experimental Verification. IEEE J. Biomed. Health Inform. 2017, 21, 708–714. [Google Scholar] [CrossRef] [PubMed]
- Li, Q.; Zhang, L.N.; Tao, X.M.; Ding, X. Review of flexible temperature sensing networks for wearable physiological monitoring. Adv. Healthc. Mater. 2017, 6, 1601371. [Google Scholar] [CrossRef] [PubMed]
- Ota, H.; Chao, M.; Gao, Y.; Wu, E.; Tai, L.C.; Chen, K.; Matsuoka, Y.; Iwai, K.; Fahad, H.M.; Gao, W.; et al. 3d printed “earable” smart devices for real-time detection of core body temperature. ACS Sens. 2017, 2, 990–997. [Google Scholar] [CrossRef] [PubMed]
- Shabana, N.; Velmathi, G. Advanced Tele-surgery with IoT Approach. In Intelligent Embedded Systems; Springer: Berlin/Heidelberg, Germany, 2018; pp. 17–24. [Google Scholar]
- Sareen, S.; Sood, S.K.; Gupta, S.K. IoT-based cloud framework to control Ebola virus outbreak. J. Ambient Intell. Humaniz. Comput. 2016, 9, 459–476. [Google Scholar] [CrossRef]
- Ghorbel, A.; Bouguerra, S.; Amor, N.B.; Jallouli, M. Cloud based mobile application for remote control of intelligent wheelchair. In Proceedings of the 2018 14th International Wireless Communications & Mobile Computing Conference (IWCMC), Limassol, Cyprus, 25–29 June 2018; pp. 1249–1254. [Google Scholar]
- Lee, Y.K.; Lim, J.M.; Eu, K.S.; Goh, Y.H.; Tew, Y. Real time image processing based obstacle avoidance and navigation system for autonomous wheelchair application. In Proceedings of the Asia-Pacific Signal and Information Processing Association Annual Summit and Conference (APSIPA ASC), Kuala Lumpur, Malaysia, 12–15 December 2017; pp. 380–385. [Google Scholar]
- Nave, C.; Postolache, O. Smart Walker based IoT Physical Rehabilitation System. In Proceedings of the 2018 International Symposium in Sensing and Instrumentation in IoT Era (ISSI), Shanghai, China, 6–7 September 2018; pp. 1–6. [Google Scholar]
- Yang, G.; Deng, J.; Pang, G.; Zhang, H.; Li, J.; Deng, B.; Pang, Z.; Xu, J.; Jiang, M.; Liljeberg, P.; et al. An IoT-Enabled Stroke Rehabilitation System Based on Smart Wearable Armband and Machine Learning. IEEE J. Transl. Eng. Health Med. 2018, 6, 1–10. [Google Scholar] [CrossRef]
- Subhash, K.; Pournami, P.; Joseph, P.K. Census transform based feature extraction of EMG signals for neuromuscular disease classification. In Proceedings of the 2017 IEEE 15th Student Conference on Research and Development (SCOReD), Putrajaya, Malaysia, 13–14 December 2017; pp. 499–503. [Google Scholar]
- Subasi, A.; Yaman, E.; Somaily, Y.; Alynabawi, H.A.; Alobaidi, F.; Altheibani, S. Automated EMG Signal Classification for Diagnosis of Neuromuscular Disorders Using DWT and Bagging. Procedia Comput. Sci. 2018, 140, 230–237. [Google Scholar] [CrossRef]
- Fu, Y.; Liu, J. System design for wearable blood oxygen saturation and pulse measurement device. Procedia Manuf. 2015, 3, 1187–1194. [Google Scholar] [CrossRef]
- Xie, Y.; Gao, Y.; Li, Y.; Lu, Y.; Li, W. Development of Wearable Pulse Oximeter Based on Internet of Things and Signal Processing Techniques. In Proceedings of the European Modelling Symposium (EMS), Manchester, UK, 20–21 November 2017; pp. 249–254. [Google Scholar]
- Tekeste, T.; Saleh, H.; Mohammad, B.; Ismail, M. Ultra-Low Power QRS Detection and ECG Compression Architecture for IoT Healthcare Devices. IEEE Trans. Circuits Syst. I Regul. Pap. 2018, 66, 669–679. [Google Scholar] [CrossRef]
- Bathilde, J.B.; Then, Y.L.; Chameera, R.; Tay, F.S.; Zaidel, D.N.A. Continuous heart rate monitoring system as an IoT edge device. In Proceedings of the Sensors Applications Symposium (SAS), Seoul, Korea, 12–14 March 2018; pp. 1–6. [Google Scholar]
- Krachunov, S.; Beach, C.; Casson, A.J.; Pope, J.; Fafoutis, X.; Piechocki, R.J.; Craddock, I. Energy efficient heart rate sensing using a painted electrode ECG wearable. In Proceedings of the Global Internet of Things Summit (GIoTS), Geneva, Switzerland, 6–9 June 2017; pp. 1–6. [Google Scholar]
- Diabetes. Available online: https://medlineplus.gov/lab-tests/blood-glucose-test (accessed on 29 March 2019).
- Capodieci, A.; Budner, P.; Eirich, J.; Gloor, P.; Mainetti, L. Dynamically Adapting the Environment for Elderly People Through Smartwatch-Based Mood Detection. In Collaborative Innovation Networks; Springer: Berlin/Heidelberg, Germany, 2018; pp. 65–73. [Google Scholar]
- Bharadwaj, S.A.; Yarravarapu, D.; Reddy, S.C.K.; Prudhvi, T.; Sandeep, K.; Reddy, O.S.D. Enhancing healthcare using m-care box (monitoring non-compliance of medication). In Proceedings of the 2017 International Conference on I-SMAC (IoT in Social, Mobile, Analytics and Cloud)(I-SMAC), Palladam, India, 10–11 February 2017; pp. 352–356. [Google Scholar]
- Medina, J.; Espinilla, M.; García-Fernández, Á.; Martínez, L. Intelligent multi-dose medication controller for fever: From wearable devices to remote dispensers. Comput. Electr. Eng. 2018, 65, 400–412. [Google Scholar] [CrossRef]
- Gupta, K.; Rakesh, N.; Faujdar, N.; Kumari, M.; Kinger, P.; Matam, R. IOT Based Automation and Solution for Medical Drug Storage: Smart Drug Store. In Proceedings of the 2018 8th International Conference on Cloud Computing, Data Science & Engineering (Confluence), Noida, India, 11–12 January 2018; pp. 497–502. [Google Scholar]
- Monteleone, S.; Sampaio, M.; Maia, R.F. A novel deployment of smart Cold Chain system using 2G-RFID-Sys temperature monitoring in medicine Cold Chain based on Internet of Things. In Proceedings of the 2017 IEEE International Conference on Service Operations and Logistics, and Informatics (SOLI), Bari, Italy, 18–20 September 2017; pp. 205–210. [Google Scholar]
- Baig, M.M.; GholamHosseini, H.; Connolly, M.J. Mobile healthcare applications: System design review, critical issues and challenges. Australas. Phys. Eng. Sci. Med. 2015, 38, 23–38. [Google Scholar] [CrossRef] [PubMed]
- Watch Series 4, A. Apple Watch Series 4. Available online: https://www.apple.com/lae/apple-watch-series-4 (accessed on 23 February 2019).
- Thync. Available online: https://www.thync.com/ (accessed on 23 February 2019).
- Ybrain. Available online: http://www.ybrain.com (accessed on 23 February 2019).
- Quell. Available online: https://www.quellrelief.com (accessed on 23 February 2019).
- Augmedix. Available online: https://www.augmedix.com/ (accessed on 23 February 2019).
- Lumo. Available online: https://support.lumobodytech.com/hc/en-us (accessed on 23 February 2019).
- Sprouting. Available online: http://misscharmsie.com/?p=19716 (accessed on 23 February 2019).
- Nima Sensor. Available online: https://nimasensor.com (accessed on 23 February 2019).
- Beddits Sleep Monitor. Available online: https://www.beddit.com (accessed on 23 February 2019).
- Breathometer. Available online: https://www.breathometer.com (accessed on 23 February 2019).
- AURIS. Available online: https://www.aurishealth.com (accessed on 23 February 2019).
- Moxi. Available online: http://diligentrobots.com/moxi/ (accessed on 23 February 2019).
- Tugrobot. Available online: https://aethon.com/ (accessed on 23 February 2019).
- Albalawi, U.; Joshi, S. Secure and trusted telemedicine in Internet of Things IoT. In Proceedings of the 2018 IEEE 4th World Forum on Internet of Things (WF-IoT), Singapore, 5–8 February 2018; pp. 30–34. [Google Scholar]
- Galletta, A.; Carnevale, L.; Bramanti, A.; Fazio, M. An innovative methodology for Big Data Visualization for telemedicine. IEEE Trans. Ind. Inform. 2018, 15, 490–497. [Google Scholar] [CrossRef]
- Hussain, S.R.; Mehnaz, S.; Nirjon, S.; Bertino, E. Secure Seamless Bluetooth Low Energy Connection Migration for Unmodified IoT Devices. IEEE Trans. Mob. Comput. 2018, 17, 927–944. [Google Scholar] [CrossRef]
- Dimitrov, S.; Haas, H. Principles of LED Light Communications: Towards Networked Li-Fi; Cambridge University Press: Cambridge, UK, 2015. [Google Scholar]
- Albraheem, L.I.; Alhudaithy, L.H.; Aljaser, A.A.; Aldhafian, M.R.; Bahliwah, G.M. Toward Designing a Li-Fi-Based Hierarchical IoT Architecture. IEEE Access 2018, 6, 40811–40825. [Google Scholar] [CrossRef]
- Martínez Pérez, M.; Dafonte, C.; Gómez, Á. Traceability in Patient Healthcare through the Integration of RFID Technology in an ICU in a Hospital. Sensors 2018, 18, 1627. [Google Scholar] [CrossRef] [PubMed]
- Kim, Y.; Lee, W.S.; Raghunathan, V.; Jha, N.K.; Raghunathan, A. Vibration-based secure side channel for medical devices. In Proceedings of the 52nd Annual Design Automation Conference, San Francisco, CA, USA, 7–11 June 2015; p. 32. [Google Scholar]
- Al Alkeem, E.; Yeun, C.Y.; Zemerly, M.J. Security and privacy framework for ubiquitous healthcare IoT devices. In Proceedings of the 2015 10th International Conference for Internet Technology and Secured Transactions (ICITST), London, UK, 14–16 December 2015; pp. 70–75. [Google Scholar]
- Gope, P.; Hwang, T. BSN-Care: A secure IoT-based modern healthcare system using body sensor network. IEEE Sens. J. 2016, 16, 1368–1376. [Google Scholar] [CrossRef]
- Salameh, H.B.; Almajali, S.; Ayyash, M.; Elgala, H. Securing delay-sensitive cognitive radio IoT communications under reactive jamming attacks: Spectrum assignment perspective. In Proceedings of the 2018 Fifth International Conference on Software Defined Systems (SDS), Barcelona, Spain, 23–26 April 2018; pp. 20–24. [Google Scholar]
- Namvar, N.; Saad, W.; Bahadori, N.; Kelley, B. Jamming in the internet of things: A game-theoretic perspective. In Proceedings of the Global Communications Conference (GLOBECOM), 2016 IEEE, Washington, DC, USA, 4–8 December 2016; pp. 1–6. [Google Scholar]
- Abdallah, A.; Shen, X.S. Efficient prevention technique for false data injection attack in smart grid. In Proceedings of the 2016 IEEE International Conference on Communications (ICC), Kuala Lumpur, Malaysia, 22–27 May 2016; pp. 1–6. [Google Scholar]
- Amah, T.; Kamat, M.; Bakar, K.; Rahman, S.; Mohammed, M.; Abali, A.; Moreira, W.; Oliveira-Jr, A. The Impact of Message Replication on the Performance of Opportunistic Networks for Sensed Data Collection. Information 2017, 8, 143. [Google Scholar] [CrossRef]
- Singh, S.P.; Sharma, S. Secure clustering protocols in wireless sensor networks. J. Wirel. Sens. Netw. 2016, 3, 1–10. [Google Scholar]
- Adat, V.; Dahiya, A.; Gupta, B. Economic incentive based solution against distributed denial of service attacks for IoT customers. In Proceedings of the 2018 IEEE International Conference on Consumer Electronics (ICCE), Las Vegas, NV, USA, 12–14 January 2018; pp. 1–5. [Google Scholar]
- Chen, Q.; Chen, H.; Cai, Y.; Zhang, Y.; Huang, X. Denial of Service Attack on IoT System. In Proceedings of the 2018 9th International Conference on Information Technology in Medicine and Education (ITME), Hangzhou, China, 19–21 October 2018; pp. 755–758. [Google Scholar]
- Gill, R.K.; Sachdeva, M. Detection of hello flood attack on LEACH in wireless sensor networks. In Next-Generation Networks; Springer: Berlin/Heidelberg, Germany, 2018; pp. 377–387. [Google Scholar]
- Bhatia, T.; Verma, A.; Sharma, G.; Bala, S. A Novel Defense Scheme against Flooding Attack in Mobile Adhoc Networks. Recent Patents Eng. 2018, 12, 15–22. [Google Scholar] [CrossRef]
- Mohammad, S.N.; Singh, R.; Dey, A.; Ahmad, S.J. ESMBCRT: Enhance Security to MANETs Against Black Hole Attack Using MCR Technique. In Innovations in Electronics and Communication Engineering; Springer: Berlin/Heidelberg, Germany, 2019; pp. 319–326. [Google Scholar]
- Kumar, V.; Kumar, R. An adaptive approach for detection of blackhole attack in mobile ad hoc network. Procedia Comput. Sci. 2015, 48, 472–479. [Google Scholar] [CrossRef]
- Gurung, S.; Chauhan, S. A novel approach for mitigating gray hole attack in MANET. Wirel. Netw. 2018, 24, 565–579. [Google Scholar] [CrossRef]
- Schweitzer, N.; Stulman, A.; Margalit, R.D.; Shabtai, A. Contradiction based gray-hole attack minimization for ad hoc networks. IEEE Trans. Mob. Comput. 2017, 16, 2174–2183. [Google Scholar] [CrossRef]
- Pongle, P.; Chavan, G. Real time intrusion and wormhole attack detection in internet of things. Int. J. Comput. Appl. 2015, 121, 1–9. [Google Scholar] [CrossRef]
- Giri, D.; Borah, S.; Pradhan, R. Approaches and Measures to Detect Wormhole Attack in Wireless Sensor Networks: A Survey. In Advances in Communication, Devices and Networking; Springer: Berlin/Heidelberg, Germany, 2018; pp. 855–864. [Google Scholar]
- Cervantes, C.; Poplade, D.; Nogueira, M.; Santos, A. Detection of sinkhole attacks for supporting secure routing on 6LoWPAN for Internet of Things. In Proceedings of the 2015 IFIP/IEEE International Symposium on Integrated Network Management (IM), Ottawa, ON, Canada, 11–15 May 2015; pp. 606–611. [Google Scholar]
- Mishra, A.K.; Tripathy, A.K.; Puthal, D.; Yang, L.T. Analytical model for Sybil attack phases in internet of things. IEEE Internet Things J. 2019, 6, 379–387. [Google Scholar] [CrossRef]
- Jamshidi, M.; Zangeneh, E.; Esnaashari, M.; Darwesh, A.M.; Meybodi, M.R. A Novel Model of Sybil Attack in Cluster-Based Wireless Sensor Networks and Propose a Distributed Algorithm to Defend It. Wirel. Pers. Commun. 2019, 105, 145–173. [Google Scholar] [CrossRef]
- Thota, C.; Sundarasekar, R.; Manogaran, G.; Varatharajan, R.; Priyan, M. Centralized fog computing security platform for IoT and cloud in healthcare system. In Fog Computing: Breakthroughs in Research and Practice; IGI Global: Hershey, PA, USA, 2018; pp. 365–378. [Google Scholar]
- Fostering the Advancement of the Internet of Things. Available online: https://www.ntia.doc.gov/files/ntia/publications/iot_green_paper_01122017.pdf (accessed on 29 March 2019).
- CLOUD COMPUTING SECURITY REQUIREMENTS GUIDE. Available online: https://iasecontent.disa.mil/cloud/Downloads/Cloud_Computing_SRG_v1r3.pdf (accessed on 29 March 2019).
- Track the Movements of Fitness Tracker-Wearing Military Personnel. Available online: https://dod.defense.gov/News/Article/Article/1594486/new-dod-policy-prohibits-gps-enabled-devices-in-deployed-settings/ (accessed on 29 March 2019).
- Polar Fitness Suspends Its Global Activity Map after Privacy Concerns. Available online: https://www.theverge.com/2018/7/8/17546224/polar-flow-smart-fitness-company-privacy-tracking-security (accessed on 29 March 2019).
- USBan. Available online: https://dod.defense.gov/News/Article/Article/1594486/new-dod-policy-prohibits-gps-enabled-devices-in-deployed-settings/ (accessed on 29 March 2019).
- Made in China 2025. Available online: http://isdp.eu/content/uploads/2018/06/Made-in-China-Backgrounder.pdf (accessed on 29 March 2019).
- China IoT in Healthcare White Paper. Available online: http://global.chinadaily.com.cn/a/201809/14/WS5b9bb789a31033b4f465629c.html (accessed on 29 March 2019).
- EU-China Joint White Paper on the Internet of Things. Available online: http://www.eglobalmark.com/wp-content/uploads/2016/06/2016-01-EU-China-Joint-White-Paper-on-IoT.pdf (accessed on 29 March 2019).
- i-Japan Strategy 2015. Available online: https://japan.kantei.go.jp/policy/it/i-JapanStrategy2015_full.pdf (accessed on 29 March 2019).
- Smart Japan ICT Strategy. Available online: https://japan.kantei.go.jp/policy/it/i-JapanStrategy2015_full.pdf (accessed on 29 March 2019).
- General Framework for Secured IoT Systems. Available online: https://www.nisc.go.jp/active/kihon/pdf/iot_framework2016.pdf (accessed on 29 March 2019).
- Master Plan for Building the Internet of Things. Available online: http://www.iotkorea.or.kr/2013_kor/uploadFiles/board/KOREA-%20IoT%28Internet%20of%20Things%29%20Master%20Plan%20-%202014.pdf (accessed on 29 March 2019).
- Allocation of Rs. 7060 Crores for Smart Cities. Available online: https://www.thehindu.com/business/budget/rs-7060-crore-for-100-smart-cities/article6198022.ece (accessed on 29 March 2019).
- Digital India Program of the Government. Available online: https://www.digitalindia.gov.in/ (accessed on 29 March 2019).
- Russia Internet-of-Things Market 2018–2022 Forecast. Available online: https://www.idc.com/getdoc.jsp?containerId=CEMA43447018 (accessed on 29 March 2019).
- Russian Internet of Things Market. Available online: https://iot.ru/upload/Russia%20Internet%20of%20Things%20market.pdf (accessed on 29 March 2019).
- Digital Growth Strategy. Available online: https://eng.em.dk/media/10566/digital-growth-strategy-report_uk_web-2.pdf (accessed on 29 March 2019).
- Alliance for Internet of Things Innovation. Available online: https://aioti.eu/ (accessed on 29 March 2019).
- Digital Single Market Strategy. Available online: https://ec.europa.eu/commission/priorities/digital-single-market_en (accessed on 29 March 2019).
- Cisco Survey IoT Projects. Available online: https://newsroom.cisco.com/press-release-content?articleId=1847422 (accessed on 29 March 2019).
| ID | Reference | Year | IoT | Cloud | Contributions |
|---|---|---|---|---|---|
| 1 | Mutlag et al. [21] | 2019 | ✓ | ✓ |
|
| 2 | Kumari et al. [22] | 2018 | ✓ |
| |
| 3 | García et al. [23] | 2018 | ✓ |
| |
| 4 | Farahani et al. [27] | 2018 | ✓ |
| |
| 5 | Ahmadi et al. [25] | 2018 | ✓ | ✓ |
|
| 6 | Baker et al. [26] | 2017 | ✓ |
| |
| 7 | Kraemer et al. [24] | 2017 | ✓ |
| |
| 8 | Islam et al. [20] | 2015 | ✓ | ✓ |
|
| Characteristics | Bluetooth | ZigBee | Infrared |
|---|---|---|---|
| Band | 2.4 GHz | 2.4 GHz | 430 THz to 300 GHz |
| Range | 150 m | 10–100 m | Less than 1.5 m |
| Data rate | 1 Mbps | 20–250 Kbps | 9.6–115.2 Kbps |
| Topology | Star | Mesh | Point-to-point |
| Security | Secure pairing 128-AES encryption | Shared network key Optional 128-AES encryption | Line-of-sight and very low bit error rate |
| Characteristic | SigFox | LoRaWAN | 6LoWPAN |
|---|---|---|---|
| Frequency | 902 megahertz (US) 868 megahertz (Europe) | 902–928 megahertz (North America) 863–870 megahertz or 434 megahertz (Europe) 779–787 megahertz (China) | 2.4 gigahertz (Worldwide) 902–929 megahertz (North America) 868–868.6 megahertz (Europe) |
| Channel | 360 channels with 40 reserved channels | 80 channels (902–928 megahertz band) 10 channels (779–787 megahertz band and 863–870 megahertz band) | 16 channels (2.4 gigahertz band) 10 channels (915 megahertz band) 1 channel for (868.3 megahertz band) |
| Bandwidth | 100 hertz–1.2 kilohertz | 125 kilohertz and 500 kilohertz (915 megahertz band) 125 kilohertz and 250 kilohertz (868 megahertz band and 780 megahertz band) | 5 megahertz (2.4 gigahertz band) 2 megahertz (915 megahertz ban) 600 kilohertz (868.3 megahertz band) |
| Range | 10 to 50 kilometers | 5 to 15 kilometers | 10 to 100 meters |
| Data rate | 980 bit/sec to 21.9 kbit/s (915 megahertz band) | 100 to 600 bit/sec | 250 kbit/s (2.4 gigahertz band) 40 kbit/s (915 megahertz band) 20 kbit/s (868.3 megahertz band) |
| Payload | Between 0 to 12 bytes | Between 19 to 250 byte | Header (6 bytes) and session data unit (127 bytes) |
| Channel coding | Ultra narrow band coding | Chirp spread spectrum (CSS) | Direct sequence spread spectrum (DSSS) |
| Security | No encryption mechanism | Two common protection keys: NwkSKey (128 bits), AppSKey (128 bits) NwkSKey ensures data integrity AppSKey provides data confidentiality | Handled at link layer which includes secure and non-secure mode |
| Characteristics | Cloud Computing | Fog Computing |
|---|---|---|
| Node location | The internet | Local network edge |
| Number of node | Little | Large |
| Latency | High | Low |
| Delay | High | Low |
| Distance between devices and server | Multiple hops | Single hop |
| Location awareness | No | Yes |
| Distribution | Centralized | Distributed |
| Scalability | Supported (Dynamic adaptation to workload) | Limited (Fog is not as scalable as cloud) |
| Mobility support | Limited | Good |
| Real-time interaction | Supported | Supported |
| Data storage | Huge | Limit |
| Transmission | Device to cloud | Device to device |
| Data aggregation | At cloud | Partially and remaining to cloud |
| Security | No user-defined security (Carried out by cloud service providers) | User-defined security (Data is processed by a complex distributed system) |
| Ref | Year | Field | Dataset | Results | Contributions |
|---|---|---|---|---|---|
| [69] | 2019 | Smart health | Self | Efficient data sharing service with privacy preservation | ● Implement a fog-enabled smart health to improve data sharing service. ● Provide a privacy-preserving fog-assisted health data sharing case study. |
| [63] | 2018 | Dataset from other research | BBN classifer/93.6% | ● Introduce a novel Fog-Cloud framework for healthcare services in smart office. ● Propose a Severity Index to estimate the adverse effects of different activities on personal health. ● Implement an application scenario for healthcare prediction and alert generation. | |
| [70] | 2018 | Self | Reliable and faster processing speed | ● A data processing system is proposed to improve network reliability and speed. ● Introduce a self-adaptive filter to recollect missing or inaccurate data automatically. ● Propose an RVNS queue to process preprocessed data. | |
| [71] | 2018 | Self | J48 decision tree classifier/93.5% | ● Design a fog assisted cloud-based healthcare system for early detection of the virus outbreak. ● Generate alerts immediately on the user’s mobile phone in the fog layer. ● On the cloud layer, the virus outbreak is illustrated using temporal network analysis. | |
| [34] | 2018 | Acute illnesses | Self | Enhance overall system efficiency | ● Design smart e-Health gateway to provide several higher-level services. ● Use fog computing to generate a Geo-distributed intermediary layer between sensor nodes and cloud. ● Create a smart e-Health gateway prototype called UT-GATE with high-level features. |
| [61] | 2019 | Diabetes | UCI diabetes & UCI PAMAP2 | J48Graft decision tree classifer/98.56% | ● Propose a fog-based health framework to diagnose and remotely monitor diabetic patients in real-time. ● Perform risk assessment of diabetes patients at regular intervals. |
| [62] | 2018 | Hypertension attack | Self | ANN classifer/95.21% | ● Propose an IoT-fog-based healthcare system to continuous monitor patients. ● Predict the risk level of hypertension attack of users remotely. ● Data collected from patients were saved on the cloud and shared with domain experts. |
| [64] | 2018 | Healthcare system privacy | NA | Solutions for privacy issues | ● Show research challenges in developing practical privacy-preserving analytics in healthcare systems. ● Propose solutions to solve these challenges. |
| [72] | 2018 | Wearable healthcare monitoring system | NA | System is resilience against known attacks. | ● Propose a cloud-based user authentication scheme for secure authentication of medical data. ● Create a secret session key for future secure communications. ● Conduct a detailed comparative analysis on the system’s communication and computation costs. |
| [73] | 2018 | Mosquito-borne diseases | UCI Adult | FKNN classifier/95.9% | ● Introduce a fog-based system to detect and classify different mosquito-borne diseases. ● Implement Social Network Analysis to illustrate the outbreak of the mosquito-borne disease on the cloud layer. |
| [68] | 2016 | Smart homes and hospitals | NA | NA | ● Introduce a cloud to fog U-healthcare monitoring system in smart homes and hospitals. ● Investigate significant features of Fog computing and how it extends Cloud computing. |
| Domain | Types of Sensors | Main Study |
|---|---|---|
| Activity recognition | Force, button, ultrasonic, accelerometer, kinect | [74,76,77,78,79,80] |
| Vital monitoring | Heart rate, temperature, glucose meter, electromyography | [33,75,81] |
| Surrounding environment | Air temperature, moistness, carbon monoxide, carbon dioxide, glow | [82] |
| Disease/Condition | Sensors | IoT Roles/Connections |
|---|---|---|
| Diabetes [92,93] | Glucose sensor, contextual sensor, near infrared led | The sensor’s output is sent to Android gateway for local storage and data pre-processing then they are sent to the cloud for analysis and notification to the responsible person (Doctors, caregivers) if abnormalities occur. |
| Asthma [94,95] | Pulse sensor, temperature sensor | Microcontroller board processes signals, and then the data is sent through a WiFi module to the cloud for storage via hypertext transfer protocol (HTTP). |
| Heart disease [28,96,97,98,99,100,101,102,103] | Optical heart rate sensor, BP sensor, ECG sensor | The data are transmitted to a microcontroller using a wireless transmitter, and then it is sent to the servers through an appropriate smartphone gateway. |
| Hyperthermia and hypothermia [104,105,106] | Thermopile infrared (IR) sensor, wearable thermometry | wireless body area network (WBAN) connects sensors through an appropriate gateway, the raw data are sent to the server through WiFi for storage and analyzing. |
| Tele-surgery [107] | Microelectromechanical sensors (Mems sensors), robot arms, microcontroller | The sensors values are fed to a microcontroller and transmitted to 2 connected Zigbee system in realtime without delay and data loss. |
| Ebola [108] | Lightweight body sensors, radio frequency identification (RFID) reader | The sensors’ output is recorded by WBAN and is sent to mobile devices through Bluetooth connection, then finally the data is broadcast to the remote server instantly using WiFi or 4G network. |
| Wheelchair management [109,110] | Camera sensor, accelerometer sensor, force sensor | The controller integrated into the wheelchair process signals from sensors and realizes abnormality; the controller then sends data to the web server through an appropriate gateway. |
| Rehabilitation [111,112] | Force sensor, distance sensor, RFID | The controller integrated into the node processes signals and communicate with the remote system using a WiFi connection or through a smartphone gateway. |
| Medication non-compliance [111,112] | Force sensor, distance sensor, RFID | The controller integrated into the node processes signals and communicate with the remote system using a WiFi connection or through a smartphone gateway. |
| Neuromuscular diseases [113,114] | EMG sensors | The raw sensor data is sent to the controller; then, a signal classification model is performed to detect neuromuscular disorders. The classification results are sent to the cloud for storage. |
| Respiratory disease [115,116] | SpO2 sensor | The wearable devices recorded the sensor data then it connects to a wireless mesh network and sends data to the server through a personal computer connected to the internet. |
| Category |  |  | Description |
|---|---|---|---|
| Diagnosis | PEPID, UpToDate, Prognosis Your Diagnosis, Diagnosis Medical App, Quick Medical Diagnosis & Treatment, InSimu Patient-Diagnose Virtual Clinical Cases, Ada-Your Health Guide, Doctor Diagnose Symptoms Check, Cardiac diagnosis, Eye Diagnosis, Self Diagnosis, VisualDx. | PPEPID, UpToDate, Prognosis Your Diagnosis, Heart Rate Plus Pulse Monitor, Differential Diagnosis Guide, 5 Minutes Clinical Consult, Ear Age Diagnosis, Emergency Central, Dem DX Diagnostic Reasoning, Diagnosaurus DDx, mRay. | Evidence-based clinical and drug information resources for point-of-care decision making. |
| Drug references | Epocrates, Drugs.com Medication Guide, KnowDrugs Drug Checking, Drug Dictionary Offline, Drug INFO, Drugs Classifications. | Epocrates, Drugs.com Medication Guide, Medicine Dictionary, Davis’s Drug Guide. | Mobile medical reference applications, look up drug information, identify pills. |
| Education | Medscape, Muscle Trigger Point, Visual DX, PEPID. | Medscape, 3D4Medical, Muscle Trigger Point, Visual DX, PEPID. | Show practical clinical sources, including detailed guidelines on drugs, videos tutorials, and educational exercises for students. |
| Medical news | MedPage, Medscape, Newsfusion, Internal Medicine News. | MedPage, Medscape, Newsfusion, Internal Medicine News, NEJM This Week. | health apps support the flow of information in the health industry, becoming a new digital tool to help complement traditional searches for health news. |
| Telemedicine | MDLIVE, LiveHealth Online Mobile, Express Care Virtual, Amwell, Lemonaid, I Online Doctor, Ask a Doctor, Doctor’s Circle, My Live Doctors, JustDoc Online Doctor, Carrydoctor, Personal Doctor, Halodoc, MySwaath-Doctor consultation, doctor appointment. | MDLIVE, LiveHealth Online Mobile, Express Care Virtual, Amwell, First Opinion, Doctor Pocket, Ask a Doctor, iCliniq, Ask Apollo, DocOnline, Continuous Care Health, JustAnswer, OkaDoc. | These applications make connecting with a doctor fast, easy, and convenient from anywhere at any time. |
| Medical calculator | MDCalc Medical Calculator, Medical Calculators, Calculate by QxMD, Caddy, MedicALC, Medical Formulas, Mediquations Medical Calculator, IV Infusion Calculator, eGFR Calculators. | MDCalc Medical Calculator, Calculate by QxMD, MedicALC, Mediquations Medical Calculator, IV Infusion Calculator. | Receive reliable clinical solutions fast and smoothly with fundamental input values. |
| Category | Common Apps | Description |
|---|---|---|
| Workout | Fitbit, Freeletics, Sworkit, Nike+ Training Club, Daily Burn |
|
| Diet and nutrition | MyFitnessPal, FatSecret, YAZIO, Lose It!, MyPlate Calorie Tracker |
|
| Mental health | Calm, Headspace, Moodnotes, Moodpath, Pacifica |
|
| Medical records | Medical records, Patient Medical Records & Appointments for Doctors, FollowMyHealth |
|
| Type | Attacks | Description | Reference |
|---|---|---|---|
| 1 | Side-channel attack | Any attack that exploits information leaked from the deployment of a system. Power consumption, electromagnetic leaks, timing information, and even sound can reveal valuable information for hackers to attack the system. | [146,147] |
| 2 | Sniffing | Hackers take advantage of unsecured network communications to intercept data sent on a network. For network administrators, sniffers are very hard to identify since they do not intervene in the network traffic. | [2,148] |
| 2 | Radio frequency jamming | Attackers carry out this attack by intentionally jamming a target radio signal through the transmission of one or many radio signals that have similar frequency range. | [149,150] |
| 3 | Message Injection | It is a potential security vulnerability which happens when attackers attack or disrupt a network by deliberately injecting wrong messages. | [151] |
| 2 | Message Replication | Attackers conduct this attack by intercepting packets being transmitted on a network, replicating and forwarding them to other nodes on the network. | [152] |
| 1 | Node Destruction | When an IoT in healthcare network is under a node-destruction attack, attackers will try to reprogram or destroy as many nodes in the network as possible in order to cause the complete network failure. | [153] |
| 3 | Denial of service | A Denial-of-Service attack’s main goal is to damage the network connection, which makes it unavailable to users. Attackers carried out this attack by sending a large request at the same time to the target network to flood its traffic or prevent sensors from entering idle state, so they run out of battery power quickly. This attack is easy and cheap to implement and cause serious problem to a sensor network. | [154,155] |
| 1 | Hello Flooding | Attackers use some devices and deceive the target sensors network that these devices are genuine, then through these fake nodes; attackers flood the network with several hello requests and break the security link between legitimate nodes in the target sensors network. | [156,157] |
| 1 | Black Hole Attack | During the pathfinding process, a malicious node under attackers control advertises an invalid path as a good path to the source node. When the source follows the path, including the attacker node, the traffic travels through the adversary node, and this node begins to drop the packets selectively or entirely. | [158,159] |
| 1 | Gray Hole Attack | This attack is a variant of the black hole attack; in grey hole attack, only one or two nodes in the network are affected whereas the whole network is affected in black hole attack. | [160,161] |
| 1 | Wormhole Attack | Different from the black hole attack, a routing protocol is the main target of wormhole attack in which a packet or individual bits of a packet is captured at one location, transfer to another location and then replayed at another location. | [162,163] |
| 1 | Sinkhole Attack | In this attack, a region of nodes will forward packets destined for a base station through an adversary node where attackers can capture all data. The malicious node can fool the network because it provides the fastest path to the base station. | [164] |
| 1 | Sybil Attack | Attackers take multiple fake identities and use the identities of the other nodes in order to take part in distributed algorithms such as the routing table. These fake identities are known as Sybil nodes. | [165,166] |
© 2019 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Dang, L.M.; Piran, M.J.; Han, D.; Min, K.; Moon, H. A Survey on Internet of Things and Cloud Computing for Healthcare. Electronics 2019, 8, 768. https://doi.org/10.3390/electronics8070768
Dang LM, Piran MJ, Han D, Min K, Moon H. A Survey on Internet of Things and Cloud Computing for Healthcare. Electronics. 2019; 8(7):768. https://doi.org/10.3390/electronics8070768
Chicago/Turabian StyleDang, L. Minh, Md. Jalil Piran, Dongil Han, Kyungbok Min, and Hyeonjoon Moon. 2019. "A Survey on Internet of Things and Cloud Computing for Healthcare" Electronics 8, no. 7: 768. https://doi.org/10.3390/electronics8070768
APA StyleDang, L. M., Piran, M. J., Han, D., Min, K., & Moon, H. (2019). A Survey on Internet of Things and Cloud Computing for Healthcare. Electronics, 8(7), 768. https://doi.org/10.3390/electronics8070768







