1. Introduction
Driven by the rapid proliferation of smart home devices, the global smart home market reached an estimated valuation of
$183.2 billion in 2024, with the United States accounting for approximately
$50.6 billion [
1]. As the market expands, industry stakeholders are increasingly adopting the Matter standard to ensure interoperability across leading platforms, including Google Home, Amazon Alexa, Apple Home, and Samsung SmartThings. Since its official launch, the ecosystem has grown to encompass more than 1400 certified devices, enabling broad compatibility across devices and platforms [
2]. Internet of Things (IoT) devices, with capabilities such as voice assistants, security cameras, and environmental sensors, have been deployed in hundreds of millions of households worldwide, continuously collecting daily data that can serve as “silent witnesses” in criminal investigations. For example, in 2022, investigators in Kansas City sought, pursuant to a warrant, to obtain audio logs stored in the cloud from an Amazon Echo device recovered at a homicide scene. In the same year, Ring disclosed that it had provided video to law enforcement on at least eleven occasions without user consent, thereby underscoring the legal and investigative value of data generated by smart home devices [
3,
4]. Accordingly, automatically generated voice recordings, video footage, sensor logs, and control records from smart home devices are increasingly being used for crime scene reconstruction, alibi verification, and suspect tracking, heightening the importance of smart home forensics. However, the field faces several challenges. Devices are becoming increasingly miniaturized and engineered with greater complexity, making access to internal storage difficult. Manufacturers adopt divergent hardware and firmware architectures, as well as interface designs, which require acquisition and analysis techniques tailored to specific devices. Additionally, approaches that rely on serial debug interfaces, such as the Universal Asynchronous Receiver-Transmitter (UART) and Joint Test Action Group (JTAG) port or chip-off carry the risk of device damage or destruction, and device-to-device communications are typically encrypted; thus, decryption is required before packet analysis. To address these challenges, new acquisition methods that can be applied across smart home devices and platforms are required to extract data reliably [
5,
6,
7].
The Matter standard, which is being adopted rapidly in the smart home domain, is supported by major platforms such as Google Home, Amazon Alexa, and Samsung SmartThings, and many IoT manufacturers are introducing devices that support Matter. By contrast, as the range of device types and functions supported by Matter grows, the attack surface expands and smart home security risks increase. Therefore, researchers have been conducting security analyses of Matter. Moreover, as smart home devices are increasingly misused as tools of crime and used as evidence in domestic cases, the technical features of newly released devices remain insufficiently reflected in existing smart home forensics research, which can hinder their use in real investigations. Accordingly, this study proposes a Matter-based smart home forensic approach that can be applied across devices and platforms and evaluates its effectiveness experimentally.
The main contributions of this study are as follows:
Proposal of an IoT forensic acquisition approach based on Matter Multi-Admin: This study proposes a digital evidence acquisition approach that can be applied to most devices that support Matter, regardless of the manufacturer or platform. By providing a Matter standard-based solution for smart home forensics, which has traditionally relied on extraction methods tailored to specific devices, this approach enables the efficient acquisition of diverse digital evidence.
Implementation and validation of a nondestructive data acquisition technique: The feasibility of extracting forensic data stored on IoT devices without disassembly or direct access to on-device storage was experimentally verified on a smart home testbed. Using a smart bulb paired with SmartThings, the device was added to a secondary Matter fabric implemented with chip-tool, and the data generated in the primary SmartThings fabric were extracted without damaging the device.
A novel acquisition approach for smart home forensics: A new approach is proposed that applies Matter features to forensic acquisition in smart home environments and provides foundational insights for future research on smart home forensics.
The remainder of this paper is organized as follows:
Section 2 introduces Matter and chip-tool;
Section 3 reviews related works on Matter and smart home forensics;
Section 4 presents a smart home forensic approach based on Matter;
Section 5 describes the experimental validation for the proposed approach on a smart home testbed;
Section 6 discusses the proposed approach and experiments; and
Section 7 concludes the paper.
3. Related Works
A broad range of evidence acquisition and analysis techniques for heterogeneous devices and ecosystems have been developed for smart home and IoT forensics. The studies cited in this section were selected to represent recurring acquisition paradigms in smart home IoT forensics and to capture early security insights on multi controller behaviors in Matter, such that the practical limitations motivating a standardized, nondestructive acquisition path can be clearly contextualized. Proposed DEF-IoTF for smart bulbs demonstrated that artifacts stored on the device, including network related traces and application logs, could be recovered through a combination of software level and hardware level acquisition [
11]. Although this study highlighted the evidentiary value of internal artifacts, its applicability is constrained by a strong dependence on a specific device category and partial reliance on a particular weakness, which limits portability across vendors and IoT classes. Shin et al. presented an integrated methodology that combines open-source intelligence with application, network, and hardware analyses to investigate heterogeneous smart home incidents across multiple platforms [
12]. This approach improves the investigative completeness but still requires investigators to tailor the acquisition steps to each platform and device combination, reflecting persistent fragmentation in smart home ecosystems.
Beyond platform level heterogeneity, prior studies have examined artifacts and acquisition constraints that are specific to device categories. Kim et al. studied intelligent and smart IoT devices in the wearable domain and showed that considering both logical and physical extraction can reveal rich personal artifacts from sensor-driven devices [
13]. However, procedures and storage patterns centered on wearables cannot be readily generalized to nonwearable smart home devices, which expose different interfaces and artifact structures. Kim et al. also analyzed smart wallpad control panels and demonstrated that abundant evidentiary data could be obtained through a combination of network capture, software exploitation, serial access, and storage imaging [
14]. This line of work underscores the value of hub like components but also illustrates common limitations of invasive or vendor-specific techniques, including an increased risk of device damage and reduced repeatability across vendors.
Other studies have pursued generalized frameworks and network centric approaches. Mazhar et al. proposed an M2M-based framework that uses centralized logging and machine learning to detect and analyze attacks, demonstrating that network layer traces can support IoT forensic analysis at scale [
15]. Such approaches can preserve volatile event evidence and interaction patterns observed in the communication layer; however, they remain limited when investigators must interpret device resident state, histories, and on-device configurations as primary evidence. In addition, network centric monitoring alone often cannot substitute for standardized acquisition of device resident artifacts when device side state and histories must be interpreted for evidential purposes. To address cross platform investigations, Kim et al. proposed a common architecture-based framework that analyzes application functionality, extracts data from interconnected devices, and identifies evidentiary artifacts across multiple smart home platforms [
16]. Although this approach improves scalability at the investigation level, it still depends on platform-specific interfaces and does not provide a broadly reusable, nondestructive acquisition channel on the device side. Collectively, these limitations indicate the need for a standardized device side acquisition path, rather than relying primarily on platform-dependent interfaces or invasive access methods.
Recent research has further emphasized the need for generalizable data acquisition and systematic evidence handling. Kaushik et al. summarized the challenges in smart home IoT forensics and stressed that heterogeneity in storage, protocols, and companion-app designs complicates consistent acquisition and analysis across devices [
17]. Mahmood et al. comparatively evaluated IoT forensic frameworks and reported that many approaches fail to satisfy the heterogeneity, scalability, and evidence preservation requirements simultaneously, suggesting gaps in end-to-end applicability [
18]. Eichhorn et al. examined smart relays and their companion apps and observed that relevant artifacts can be distributed across the device, mobile application, and cloud layers, while noting that artifact locations and semantics remain vendor- and app-dependent [
19]. This distribution complicates repeatable acquisition and interpretation, because investigators must reconcile multiple evidence layers and their timelines under differing access controls and data formats. Ruiz-Villafranca et al. proposed a tool-assisted procedure to identify, acquire, and analyze IoT evidence sources, particularly network traffic, via near real-time monitoring, which helps to preserve volatile traces. However, this method remains centered on network layer artifacts rather than standardized acquisition of device resident evidence across heterogeneous platforms [
20].
As smart home ecosystems evolve toward standardized interoperability, the evidence surface increasingly includes protocol level interactions and multi controller behaviors that cross vendor boundaries. Matter has emerged as a unifying standard in this direction, and early security analyses have provided important insights into how commissioning, controller trust, and delegation can affect the security and integrity of device states. Shafqat et al. demonstrated outsider access risks in Matter devices controlled by third party applications, in which incomplete onboarding allowed an external party to recommission and control a device without user consent [
21]. Shashwat et al. analyzed the trust model of Matter controllers and identified a weakness in which a device could be commissioned by an arbitrary controller without verifying the controller trustworthiness, enabling stealth fabric enrollment and abnormal cross fabric interactions [
22]. Liao et al. investigated pairing and delegation in commercial Matter ecosystems and reported a hidden hub eavesdropping scenario in which a secondary user can add a concealed hub and continuously receive device state updates without clear visibility in the owner application [
23]. These findings collectively suggest that although multi-controller capabilities can be exploited, they also represent a critical locus where visibility, accountability, and reliability become central requirements if additional controllers are introduced for legitimate purposes, including evidence acquisition and interpretation. Complementary theory oriented work on reliable global diagnosis based on self-comparative models and the g-good-neighbor property further reinforces the importance of reliable state assessment in complex networks, where not all nodes can be assumed to be trustworthy [
24]. The limitations observed in device-specific and invasive acquisition approaches, together with the growing importance of standardized multi controller semantics, motivate acquisition strategies that operate consistently across vendors while minimizing device disruption and maintaining interpretable and diagnosable device states under Multi-Admin conditions. In this context, our study demonstrates that leveraging Matter Multi-Admin can provide a standardized and nondestructive acquisition path, enabling evidence extraction across heterogeneous smart home deployments while improving repeatability and preserving interpretability under Multi-Admin conditions.
4. Smart Home Forensic Method Using Matter Multi-Admin
Major smart home platforms such as Amazon Alexa, Google Home, and Apple Home now support the Matter standard to improve interoperability. A forensic approach is proposed for smart home platforms that use Matter by leveraging its Multi-Admin capability. As shown in
Figure 1, the main concept consists of three steps.
Identify the target smart home environment. The target device is determined by examining the connected devices and selecting those that support Matter.
Using chip-tool, configure an independent Matter controller as a forensic controller and commission the target Matter IoT device to it. The device can then interact with two Matter controllers.
Interact with the device through chip-tool and extract the device data via the chip-tool CLI.
For smart home devices that are already linked to a platform, the detailed procedure for extracting forensic data by constructing a Multi-Admin Matter environment is as follows.
4.1. Step 1: Forensic Readiness and Target Device Identification
To conduct smart home forensics, the target environment must first be identified. A smart home environment includes multiple components; therefore, the investigator should identify the smart home platform (e.g., Google Home and SmartThings), types of connected IoT devices, and whether each device supports Matter. If IoT devices that support Matter are identified, one of them is designated as the target device. When such devices are identified, devices with broader functionality, such as smart speakers, or those that generate data relevant to an investigation, such as door locks, are prioritized. This forensic readiness phase is essential because identifying the environment and selecting a target device in advance reduces costs and enables a more efficient investigation when an incident occurs.
4.2. Step 2: Joining Matter Device to Secondary Fabric
Subsequently, the Matter device is added to a second fabric for forensic purposes. Specifically, the smart home platform app that performed the initial commissioning is used to generate a QR code via a feature such as “Share with other services,” and chip-tool is then used to commission the IoT device into the second fabric. Consequently, the device belongs to the two fabrics simultaneously, and the controllers of both fabrics can access the device.
4.3. Step 3: Data Extraction Using Chip-Tool
The internal state and log data of the device are collected using the chip-tool controller that has joined the forensic fabric. The chip-tool CLI provides commands to enumerate the endpoints and clusters of the device. Because Matter clusters group the specific capabilities supported by the device, the types of data maintained by the device can be inferred. Accordingly, the attributes of clusters that are likely to contain forensically relevant information are read, and the data that exist on the smart home platform are extracted.
As this Matter-based forensic approach operates through the device-implemented Matter clusters, it enables standardized evidence collection without disassembling the device or relying on the manufacturer. Additionally, because it uses the chip-tool CLI, the workflow can be automated to extract data from IoT devices in a smart home environment.
5. Experiment
In
Section 4, a forensic method was proposed that uses Multi-Admin in Matter to extract data from Matter IoT devices connected to smart home platforms via chip-tool. To validate the methodology, an experiment was conducted by following the three-step procedure and demonstrating data extraction from a Matter IoT device that was already linked to a smart home platform. Access to the user’s smartphone was assumed, and the devices used in the experiment are listed in
Table 1. As shown in
Figure 2, the smart home hub was a Samsung SmartThings Station, which is a TP-Link Tapo Smart Wi-Fi Multicolor Bulb (L535E, Product ID 769), and the forensic controller was chip-tool from the Matter SDK installed on Linux.
For the testbed setup, the bulb was first powered on, and the SmartThings Station was connected to the Wi-Fi network. The SmartThings mobile app was then used to scan the QR code of the bulb and add the bulb to SmartThings. During this process, SmartThings automatically created the first fabric, which included the bulb. Approximately 3 min after powering on the bulb, the bulb was connected to chip-tool. Approximately 4 min after the connection, which was approximately 7 min after power-on, data were acquired from the smart bulb. This timing offset allowed us to determine whether chip-tool could extract data that existed before the chip-tool connection. When the acquired data includes time-related fields, the offsets make it possible to infer when the data were generated.
5.1. Forensic Readiness and Target Device Identification
First, the smart home platform and connected IoT devices were identified. Access to a smartphone, which could be used to determine the devices linked to the smart home platform, was assumed. The smartphone ran the SmartThings app and the connected devices could be viewed in the app, as shown in
Figure 3. In this environment, Samsung SmartThings was linked to a SmartThings Station and a TP-Link smart bulb (L535E). After confirming that the smart bulb supported Matter, it was designated as the target device.
5.2. Joining Matter Device to Secondary Fabric
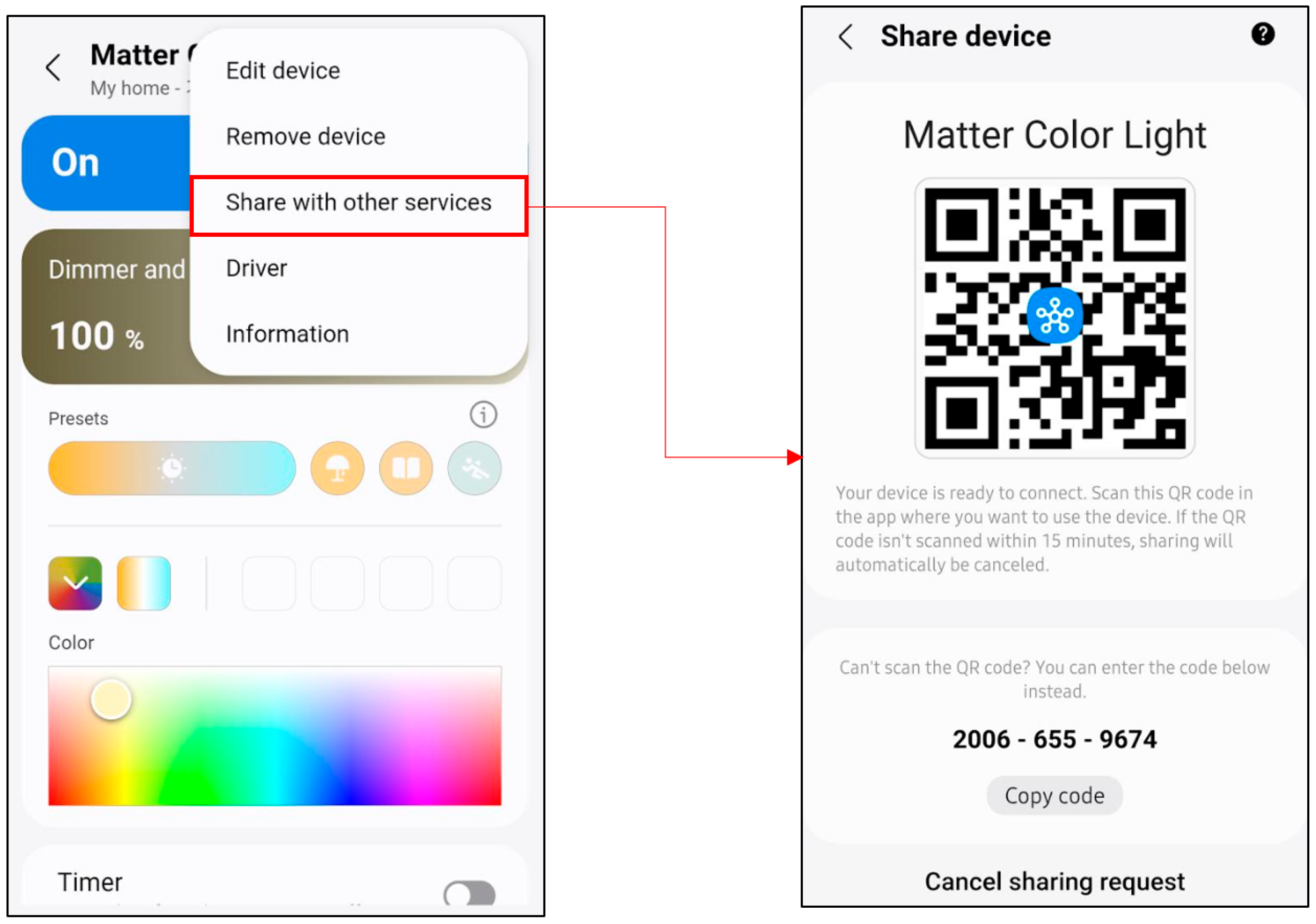
After identifying the target device, as shown in
Figure 4, the “Share with other services” feature of the SmartThings app was used to generate a QR code and commission the smart bulb to chip-tool.
To confirm that chip-tool could extract the data generated in the primary fabric (SmartThings), the bulb was kept running for approximately 3 min and then commissioned into a secondary fabric using the chip-tool pairing command, thereby establishing a Multi-Admin environment. Thus, the bulb belonged to both the SmartThings fabric and the forensic fabric simultaneously, and interaction with the device was possible from both fabrics.
5.3. Data Extraction Using Chip-Tool
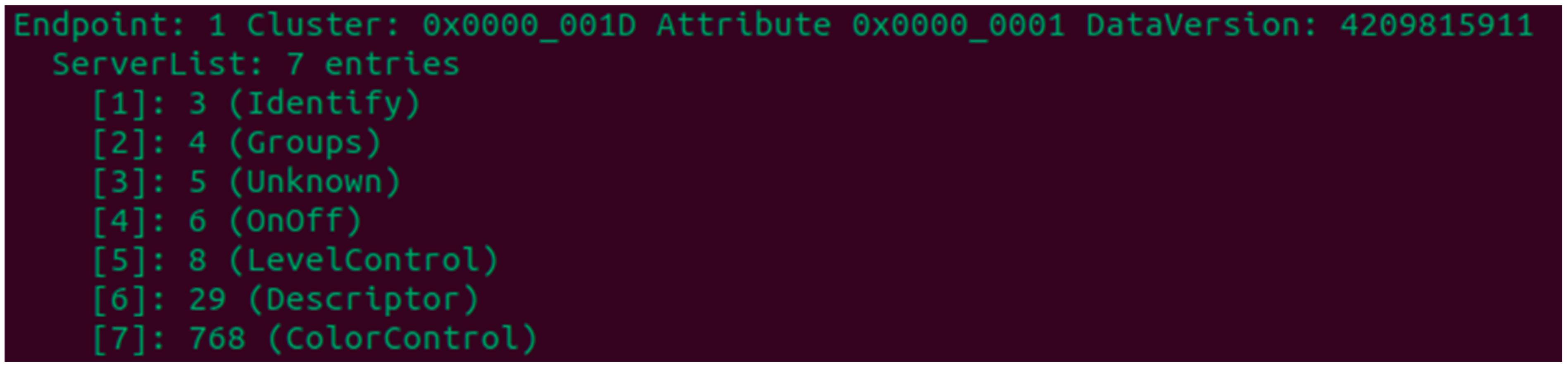
After completing the Multi-Admin setup, chip-tool was used to list the clusters by endpoint. On Endpoint 0, the clusters included Descriptor, AccessControl, BasicInformation, OtaSoftwareUpdateRequestor, and General Diagnostics, as shown in
Figure 5. On Endpoint 1, the clusters included Identify, OnOff, LevelControl, Descriptor, and ColorControl, as shown in
Figure 6. The role, functions, attributes, commands, and events of each cluster are defined in detail in the official Matter documentation [
9,
25].
Table 2 and
Table 3 summarize these cluster functions.
Endpoint 0 is defined as a mandatory reserved endpoint that must exist on every node for device management, commissioning, security, and diagnostics clusters. As shown in
Table 2, Endpoint 0 includes clusters required for management and operation, such as Network Commissioning 0x0031 for configuring network interfaces, Access Control 0x001F and Operational Credentials 0x003E for access control and operational credential management, and General Diagnostics 0x0033 for device status reporting. Endpoint 1 is populated with clusters according to the device functionality. In our experiment, the smart bulb exposed the clusters listed in
Table 3. The presence of OnOff 0x0006, Level Control 0x0008, and Color Control 0x0300 indicates that this endpoint was responsible for lighting control. The Identify 0x0003 cluster supports device identification during installation and maintenance, and the Groups 0x0004 cluster enables group-based control. The cluster at 0x0005 was not labeled in our controller output; however, it is inferred to correspond to the Scenes cluster because the Matter cluster identifier mapping assigns 0x0005 to Scenes in the Matter Application Cluster Specification [
25].
At Endpoint 0, the Basic Information cluster included attributes such as VendorName and ProductName. Reading these attributes using chip-tool confirmed that the connected device was a Tapo Smart Multicolor Bulb, as shown in
Figure 7 and
Figure 8.
Additionally, querying the UpTime attribute in the General Diagnostics cluster on Endpoint 0 returned 454 s, as shown in
Figure 9. This indicates that the forensic controller implemented using chip-tool can extract the device’s operating time from before commissioning.
6. Discussion
A forensic methodology has been proposed that uses the Multi-Admin capability in Matter to extract data from Matter IoT devices that connected to smart home platforms, and it was validated on Samsung SmartThings with a TP-Link Tapo smart bulb. The methodology consists of three steps. First, identify the platform and the IoT devices in the target smart home environment that support Matter. Second, connect the target device to chip-tool so that the device can receive commands from two Matter controllers. Third, use the controller implemented with chip-tool to extract data via clusters. This approach overcomes the difficulty of physically accessing increasingly miniaturized IoT devices, and enables the acquisition of diverse data in real investigations.
The methodology was verified using a smart bulb commissioned to the SmartThings fabric. In our setup, a SmartThings Station and the bulb were paired in the SmartThings app, and the bulb (a Matter-enabled device) was then commissioned into a secondary fabric using the “Share with other services” feature of the app to connect chip-tool as an additional controller. Through chip-tool, attribute reads were performed on the relevant Matter clusters. In the experiment, the bulb was powered on, commissioned to chip-tool after approximately 3 min, and queried at approximately 7 min by reading the UpTime attribute in the General Diagnostics cluster, which returned 454, indicating that the bulb had been on for 454 s. This demonstrates that chip-tool can extract a device-reported state that predates the chip-tool commissioning, that is, data generated during the prior interaction of the bulb with SmartThings. Additionally, reading VendorName from the Basic Information cluster confirmed that the manufacturer was Tapo, which was not displayedin the SmartThings app. This suggests that platform apps may not expose all data available through Matter. Overall, the proposed method enables nondestructive and efficient evidence acquisition from smart home IoT devices and can yield a broader range of data than those available solely on smartphones. Specifically, chip-tool acquires device-reported artifacts by reading cluster attributes and returning structured values that consist of standardized cluster and attribute identifiers and strictly typed values(e.g., Unsigned Integer, UTF-8 String). In our experiment, these artifacts included the temporal diagnostic state, such as UpTime, and device identity metadata, such as VendorName. These values provide a direct evidentiary source that can support timeline reconstruction and corroborate records from the primary platform, particularly in forensic scenarios where the platform application masks or omits granular device details.
Prior smart home IoT forensic studies have demonstrated valuable artifact recovery; however, many approaches remain constrained by acquisition paths that are specific to particular devices or vendors and, in some cases, require invasive access, which can be difficult to generalize across device classes [
11,
14]. More scalable investigation frameworks can correlate evidence across different smart home platforms; however, they typically depend on platform-specific interfaces and do not provide a reusable device side acquisition channel [
16]. Although network and logging centric methods can support large-scale monitoring and behavioral analysis, they may be insufficient when investigators must directly interpret device resident states, histories, and configurations as evidential artifacts [
15]. By contrast, our methodology leverages the standardized Multi-Admin capability in Matter together with chip-tool to enable a reusable and nondestructive device side acquisition path. This indicates that the approach can retrieve device-reported information that is not surfaced by the platform application, as shown by the UpTime and VendorName reads under SmartThings.
The proposed methodology has four limitations and considerations for practical deployment. First, during Multi-Admin enrollment, opening a commissioning window in the existing fabric typically requires operating the smartphone app. When the smartphone is available to investigators, substantial data can already be acquired; however, as platform apps do not necessarily persist in every Matter field in app storage, our method remains valuable for accessing additional device-reported data. The Matter ecosystem is also trending toward simpler and more automated Multi-Admin, such as the “Fabric Synchronization” introduced in Matter 1.4. If future platforms such as smart TVs or specialized hubs permit the addition of an additional forensic fabric through centralized synchronization without direct smartphone interaction, the forensic applicability and accessibility of the method will be enhanced significantly.
Second, this study’s validation is limited to a single device type (a smart bulb), which constrains the empirical demonstration of the methodology’s generalizability across diverse IoT device categories. While the smart bulb effectively demonstrates the feasibility of Multi-Admin-based data extraction through standardized Matter clusters, real-world smart home environments typically contain heterogeneous devices such as smart locks, security cameras, environmental sensors, and thermostats, each implementing different cluster sets with varying forensic relevance [
8]. The evidentiary scope and data richness may vary substantially across device categories. For instance, smart locks implement the Door Lock cluster (0x0101), which provides access to lock state, user management attributes, and control commands, and may expose lock operation events when supported by the device [
25]. Environmental sensors utilize Temperature Measurement (0x0402) and Relative Humidity Measurement (0x0405) clusters to provide current measurement values, which can be periodically collected by the forensic controller to reconstruct environmental conditions over time. Smart plugs provide On/Off state and control via cluster 0x0006, and expose power measurement values such as voltage, current, and active power through the Electrical Power Measurement cluster (0x0090), enabling investigators to establish device usage patterns through controller side data collection. However, without empirical validation on these device types, practical challenges remain uncertain. For example, security sensitive devices such as smart locks may implement more restrictive Access Control Lists, resource constrained sensors may maintain limited event histories, and certain device categories may expose only minimal metadata rather than detailed forensic artifacts due to privacy concerns, vendor-specific implementations, or resource constraints. Although the Matter specification mandates Multi-Admin support for all certified devices, suggesting architectural compatibility across categories, future work must validate the methodology across diverse device types from multiple manufacturers to confirm its practical applicability and establish category-specific acquisition techniques.
Third, the technical constraints in real-world environments must be considered. To conserve hardware resources, some manufacturers may employ nonstandard Matter implementations or firmware level restrictions that limit the number of active fabrics. If a device has already reached its maximum fabric capacity (typically a minimum of five), investigators should first prioritize other devices that have available fabric slots. If investigating a specific device with full fabric capacity is necessary and multiple users have commissioned the device to different fabrics in a shared living environment, investigators may seek cooperation from fabric administrators who are not subjects of the investigation. These individuals may voluntarily remove their fabrics through their respective platform applications to temporarily accommodate the forensic controller. While this action temporarily disrupts their access to the device, it is not expected to cause substantial evidence tampering or data loss that would compromise the forensic investigation. When such cooperation cannot be obtained, investigators should document the fabric capacity limitation as a constraint on evidence acquisition. Additionally, scalability constraints arise when investigating environments with numerous IoT devices, as manually commissioning each device becomes time intensive. Since chip-tool is a command line interface, automated acquisition scripts could be developed to programmatically discover devices and iterate through extraction workflows, potentially streamlining the process. Prior to deploying the methodology in active investigations, forensic teams should establish testbeds that replicate target environments to identify potential compatibility issues and verify device behavior across different manufacturers and firmware versions.
Finally, the addition of a forensic administrator inevitably leaves a forensic footprint because it updates the fabric list and access control rules of the device. Because commissioning and multi controller behaviors can also be abused in practice, investigators should record why and how the additional controller was authorized and preserve the resulting fabric and access control changes as part of the case record so that the acquisition remains auditable and clearly separable from adversarial misuse [
21,
22,
23]. However, this state change also provides a transparent and repeatable audit trail for the investigation process. From a forensic standpoint, this method offers a justifiable balance between the integrity of evidence and need for acquisition.