BSP: Branch Splitting for Unsolvable Path Hybrid Fuzzing
Abstract
1. Introduction
2. Related Work
2.1. Coverage-Based Fuzzing
2.2. Concolic Execution
2.3. Hybrid Fuzzing
2.4. Program Modification
3. Motivation
3.1. Slow Concolic Execution
3.2. Unsolvable Constraints
3.3. Unsolvable and Uncovered Branches
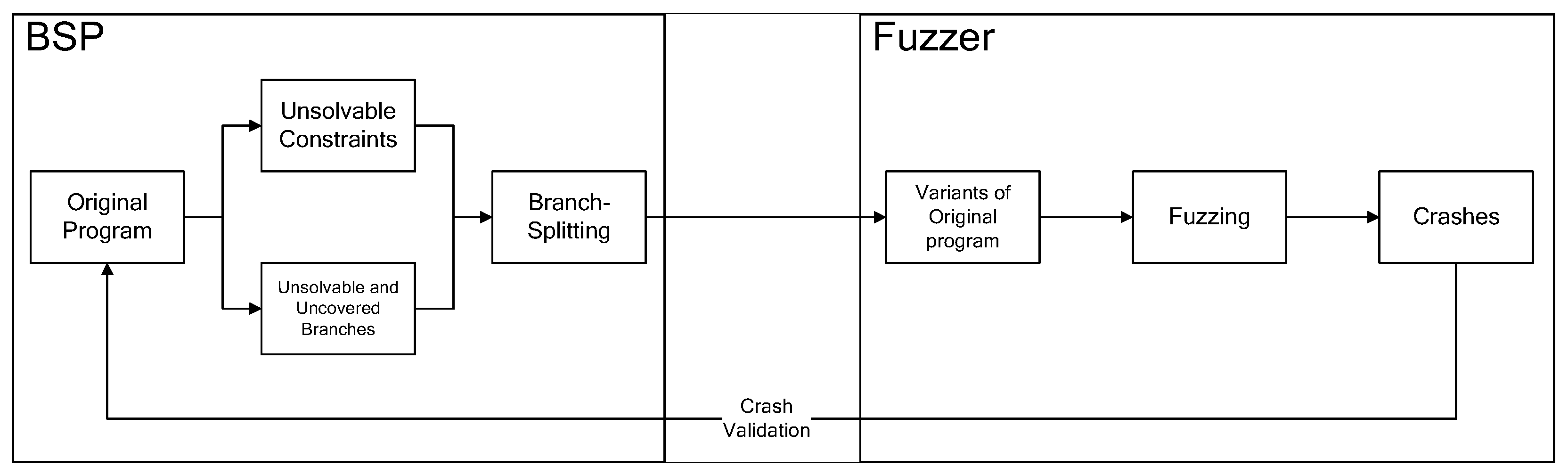
4. Design
4.1. Branch Splitting
| Algorithm 1 Branch-splitting automation. |
|
| Listing 1. An example of modifying an if statement in a file. |
 |
4.2. Filtering Out False Positives
5. Implementation and Evaluation
- RQ: Can the branch-splitting technique help the hybrid fuzzer cover more code? (Section 5)
BranchSplitting
6. Discussion
7. Conclusions
Author Contributions
Funding
Data Availability Statement
Conflicts of Interest
References
- Stephens, N.; Grosen, J.; Salls, C.; Dutcher, A.; Wang, R.; Corbetta, J.; Shoshitaishvili, Y.; Kruegel, C.; Vigna, G. Driller: Augmenting Fuzzing Through Selective Symbolic Execution. In Proceedings of the 2016 Network and Distributed System Security Symposium, San Diego, CA, USA, 21–24 February 2016. [Google Scholar] [CrossRef]
- Yun, I.; Lee, S.; Xu, M.; Jang, Y.; Kim, T. QSYM: A Practical Concolic Execution Engine Tailored for Hybrid Fuzzing. In Proceedings of the 27th USENIX Security Symposium (USENIX Security 18), Baltimore, MD, USA, 15–17 August 2018; pp. 745–761. [Google Scholar]
- Zhao, L.; Duan, Y.; Yin, H.; Xuan, J. Send Hardest Problems My Way: Probabilistic Path Prioritization for Hybrid Fuzzing. In Proceedings of the 2019 Network and Distributed System Security Symposium, San Diego, CA, USA, 24–27 February 2019. [Google Scholar] [CrossRef]
- Majumdar, R.; Sen, K. Hybrid Concolic Testing. In Proceedings of the 29th International Conference on Software Engineering (ICSE’07), Minneapolis, MN, USA, 20–26 May 2007; pp. 416–426. [Google Scholar] [CrossRef]
- Jiang, L.; Yuan, H.; Wu, M.; Zhang, L.; Zhang, Y. Evaluating and improving hybrid fuzzing. In Proceedings of the 2023 IEEE/ACM 45th International Conference on Software Engineering (ICSE), Melbourne, Australia, 14–20 May 2023; IEEE: New York, NY, USA, 2023; pp. 410–422. [Google Scholar]
- Wang, Z.; Ming, J.; Jia, C.; Gao, D. Linear Obfuscation to Combat Symbolic Execution. In Proceedings of the 16th European Symposium on Research in Computer Security(ESORICS 2011), Leuven, Belgium, 12–14 September 2011; pp. 210–226. [Google Scholar]
- Chen, Y.; Ahmadi, M.; Farkhani, R.M.; Wang, B.; Lu, L. MEUZZ: Smart Seed Scheduling for Hybrid Fuzzing. In Proceedings of the 23rd International Symposium on Research in Attacks, Intrusions and Defenses, RAID 2020, San Sebastian, Spain, 14–15 October 2020; Egele, M., Bilge, L., Eds.; USENIX Association: Berkeley, CA, USA, 2020; pp. 77–92. [Google Scholar]
- Kargén, U.; Shahmehri, N. Turning Programs against Each Other: High Coverage Fuzz-Testing Using Binary-Code Mutation and Dynamic Slicing. In Proceedings of the 2015 10th Joint Meeting on Foundations of Software Engineering, Bergamo, Italy, 30 August–4 September 2015; pp. 782–792. [Google Scholar] [CrossRef]
- Shi, J.; Wang, Z.; Feng, Z.; Lan, Y.; Qin, S.; You, W.; Zou, W.; Payer, M.; Zhang, C. {AIFORE}: Smart Fuzzing Based on Automatic Input Format Reverse Engineering. In Proceedings of the 32nd USENIX Security Symposium (USENIX Security 23), Anaheim, CA, USA, 9–11 August 2023; pp. 4967–4984. [Google Scholar]
- Fioraldi, A.; D’Elia, D.C.; Coppa, E. WEIZZ: Automatic grey-box fuzzing for structured binary formats. In Proceedings of the 29th ACM SIGSOFT International Symposium on Software Testing and Analysis, Seattle, WA, USA, 17–21 July 2020; pp. 1–13. [Google Scholar]
- Cao, S.; He, B.; Sun, X.; Ouyang, Y.; Zhang, C.; Wu, X.; Su, T.; Bo, L.; Li, B.; Ma, C.; et al. Oddfuzz: Discovering java deserialization vulnerabilities via structure-aware directed greybox fuzzing. In Proceedings of the 2023 IEEE Symposium on Security and Privacy (SP), San Francisco, CA, USA, 21–25 May 2023; IEEE: New York, NY, USA, 2023; pp. 2726–2743. [Google Scholar]
- Deng, P.; Yang, Z.; Zhang, L.; Yang, G.; Hong, W.; Zhang, Y.; Yang, M. NestFuzz: Enhancing Fuzzing with Comprehensive Understanding of Input Processing Logic. In Proceedings of the 2023 ACM SIGSAC Conference on Computer and Communications Security, Copenhagen, Denmark, 26–30 November 2023; pp. 1272–1286. [Google Scholar]
- Gan, S.; Zhang, C.; Qin, X.; Tu, X.; Li, K.; Pei, Z.; Chen, Z. CollAFL: Path Sensitive Fuzzing. In Proceedings of the 2018 IEEE Symposium on Security and Privacy (SP), San Francisco, CA, USA, 21–23 May 2018; pp. 679–696. [Google Scholar] [CrossRef]
- Chen, P.; Chen, H. Angora: Efficient Fuzzing by Principled Search. In Proceedings of the 2018 IEEE Symposium on Security and Privacy (SP), San Francisco, CA, USA, 21–23 May 2018; pp. 711–725. [Google Scholar] [CrossRef]
- Nagy, S.; Nguyen-Tuong, A.; Hiser, J.D.; Davidson, J.W.; Hicks, M. Same Coverage, Less Bloat: Accelerating Binary-only Fuzzing with Coverage-preserving Coverage-guided Tracing. In Proceedings of the 2021 ACM SIGSAC Conference on Computer and Communications Security, Virtual Event Republic of Korea, 15–19 November 2021; pp. 351–365. [Google Scholar] [CrossRef]
- Liu, Y.; Meng, W. DSFuzz: Detecting Deep State Bugs with Dependent State Exploration. In Proceedings of the 2023 ACM SIGSAC Conference on Computer and Communications Security, Copenhagen, Denmark, 26–30 November 2023; pp. 1242–1256. [Google Scholar]
- Zalewski, M. American Fuzzy Lop. 2015. Available online: https://lcamtuf.coredump.cx/afl/ (accessed on 15 August 2024).
- Luk, C.K.; Cohn, R.; Muth, R.; Patil, H.; Klauser, A.; Lowney, G.; Wallace, S.; Reddi, V.J.; Hazelwood, K. Pin: Building Customized Program Analysis Tools with Dynamic Instrumentation. SIGPLAN Not. 2005, 40, 190–200. [Google Scholar] [CrossRef]
- Google. Honggfuzz. 2010. Available online: https://honggfuzz.dev/ (accessed on 15 August 2024).
- Schumilo, S.; Aschermann, C.; Abbasi, A.; Wor-ner, S.; Holz, T. Nyx: Greybox Hypervisor Fuzzing Using Fast Snapshots and Affine Types. In Proceedings of the 30th USENIX Security Symposium (USENIX Security 21), Online, 11–13 August 2021; USENIX Association: Berkeley, CA, USA, 2021; pp. 2597–2614. [Google Scholar]
- Google. DynamoRIO. 2014. Available online: https://github.com/DynamoRIO/dynamorio (accessed on 15 August 2024).
- Fratric, I. WinAFL. 2016. Available online: https://github.com/googleprojectzero/winafl (accessed on 15 August 2024).
- Duck, G.J.; Gao, X.; Roychoudhury, A. Binary Rewriting without Control Flow Recovery. In Proceedings of the 41st ACM SIGPLAN Conference on Programming Language Design and Implementation, London, UK, 15–20 June 2020; pp. 151–163. [Google Scholar] [CrossRef]
- Dinesh, S.; Burow, N.; Xu, D.; Payer, M. RetroWrite: Statically Instrumenting COTS Binaries for Fuzzing and Sanitization. In Proceedings of the 2020 IEEE Symposium on Security and Privacy (SP), San Francisco, CA, USA, 18–21 May 2020; pp. 1497–1511. [Google Scholar] [CrossRef]
- Zhou, C.; Wang, M.; Liang, J.; Liu, Z.; Jiang, Y. Zeror: Speed Up Fuzzing with Coverage-sensitive Tracing and Scheduling. In Proceedings of the 2020 35th IEEE/ACM International Conference on Automated Software Engineering (ASE), Melbourne, Australia, 21 September 2020; pp. 858–870. [Google Scholar]
- Nagy, S.; Hicks, M. Full-Speed Fuzzing: Reducing Fuzzing Overhead through Coverage-Guided Tracing. In Proceedings of the 2019 IEEE Symposium on Security and Privacy (SP), San Francisco, CA, USA, 23 May 2019; pp. 787–802. [Google Scholar] [CrossRef]
- Wang, Y.; Jia, X.; Liu, Y.; Zeng, K.; Bao, T.; Wu, D.; Su, P. Not All Coverage Measurements Are Equal: Fuzzing by Coverage Accounting for Input Prioritization. In Proceedings of the Proceedings 2020 Network and Distributed System Security Symposium, San Diego, CA, USA, 23–26 February 2020. [Google Scholar] [CrossRef]
- Lemieux, C.; Sen, K. FairFuzz: A Targeted Mutation Strategy for Increasing Greybox Fuzz Testing Coverage. In Proceedings of the 33rd ACM/IEEE International Conference on Automated Software Engineering, Montpellier, France, 3–7 September 2018; pp. 475–485. [Google Scholar] [CrossRef]
- Yan, S.; Wu, C.; Li, H.; Shao, W.; Jia, C. PathAFL: Path-Coverage Assisted Fuzzing. In Proceedings of the 15th ACM Asia Conference on Computer and Communications Security, Taipei, Taiwan, 5–9 October 2020. [Google Scholar]
- Bohme, M.; Pham, V.T.; Roychoudhury, A. Coverage-Based Greybox Fuzzing as Markov Chain. IEEE Trans. Softw. Eng. 2019, 45, 489–506. [Google Scholar] [CrossRef]
- Yue, T.; Wang, P.; Tang, Y.; Wang, E.; Yu, B.; Lu, K.; Zhou, X. EcoFuzz: Adaptive Energy-Saving Greybox Fuzzing as a Variant of the Adversarial Multi-Armed Bandit. In Proceedings of the 29th USENIX Security Symposium (USENIX Security 20), Anaheim, CA, USA, 9–11 August 2020; USENIX Association: Berkeley, CA, USA, 2020; pp. 2307–2324. [Google Scholar]
- Shoshitaishvili, Y.; Wang, R.; Salls, C.; Stephens, N.; Polino, M.; Dutcher, A.; Grosen, J.; Feng, S.; Hauser, C.; Kruegel, C.; et al. SOK: (State of) The Art of War: Offensive Techniques in Binary Analysis. In Proceedings of the 2016 IEEE Symposium on Security and Privacy (SP), San Jose, CA, USA, 22–26 May 2016; pp. 138–157. [Google Scholar] [CrossRef]
- Cadar, C.; Dunbar, D.; Engler, D. KLEE: Unassisted and Automatic Generation of High-Coverage Tests for Complex Systems Programs. In Proceedings of the 8th USENIX Conference on Operating Systems Design and Implementation, San Diego, CA, USA, 8–10 December 2008; OSDI’08. pp. 209–224. [Google Scholar]
- Chipounov, V.; Kuznetsov, V.; Candea, G. S2E: A Platform for in-Vivo Multi-Path Analysis of Software Systems. In Proceedings of the Sixteenth International Conference on Architectural Support for Programming Languages and Operating Systems, New York, NY, USA, 5–11 May 2011; ASPLOS XVI. pp. 265–278. [Google Scholar] [CrossRef]
- Ramos, D.A.; Engler, D. Under-Constrained Symbolic Execution: Correctness Checking for Real Code. In Proceedings of the 24th USENIX Conference on Security Symposium, Washington, DC, USA, 12–14 August 2015; SEC’15. pp. 49–64. [Google Scholar]
- Neugschwandtner, M.; Milani Comparetti, P.; Haller, I.; Bos, H. The BORG: Nanoprobing Binaries for Buffer Overreads. In Proceedings of the 5th ACM Conference on Data and Application Security and Privacy, San Antonio, TX, USA, 2–4 March 2015; pp. 87–97. [Google Scholar] [CrossRef]
- Cha, S.K.; Woo, M.; Brumley, D. Program-Adaptive Mutational Fuzzing. In Proceedings of the 2015 IEEE Symposium on Security and Privacy, San Jose, CA, USA, 17–21 May 2015; pp. 725–741. [Google Scholar] [CrossRef]
- Cui, H.; Hu, G.; Wu, J.; Yang, J. Verifying Systems Rules Using Rule-Directed Symbolic Execution. In Proceedings of the Eighteenth International Conference on Architectural Support for Programming Languages and Operating Systems—ASPLOS ’13, Houston, TX, USA, 16–20 March 2013; p. 329. [Google Scholar] [CrossRef]
- Chen, P.; Liu, J.; Chen, H. Matryoshka: Fuzzing Deeply Nested Branches. In Proceedings of the 2019 ACM SIGSAC Conference on Computer and Communications Security, New York, NY, USA, 11–15 November 2019; CCS ’19. pp. 499–513. [Google Scholar] [CrossRef]
- Avgerinos, T.; Rebert, A.; Cha, S.K.; Brumley, D. Enhancing Symbolic Execution with Veritesting. Commun. ACM 2016, 59, 93–100. [Google Scholar] [CrossRef]
- Choi, J.; Jang, J.; Han, C.; Cha, S.K. Grey-Box Concolic Testing on Binary Code. In Proceedings of the 2019 IEEE/ACM 41st International Conference on Software Engineering (ICSE), Montreal, QC, Canada, 25 May 2019; pp. 736–747. [Google Scholar] [CrossRef]
- Haller, I.; Slowinska, A.; Neugschwandtner, M.; Bos, H. Dowsing for Overflows: A Guided Fuzzer to Find Buffer Boundary Violations. In Proceedings of the 22nd USENIX Conference on Security, Washington, DC, USA, 14–16 August 2013; SEC’13. pp. 49–64. [Google Scholar]
- Huang, H.; Yao, P.; Wu, R.; Shi, Q.; Zhang, C. Pangolin: Incremental Hybrid Fuzzing with Polyhedral Path Abstraction. In Proceedings of the 2020 IEEE Symposium on Security and Privacy (SP), San Francisco, CA, USA, 18–21 May 2020; pp. 1613–1627. [Google Scholar] [CrossRef]
- Zhao, Y.; Gao, L.; Wei, Q.; Zhao, L. Towards Tightly-coupled Hybrid Fuzzing via Excavating Input Specifications. IEEE Trans. Dependable Secur. Comput. 2024, 21, 4801–4814. [Google Scholar] [CrossRef]
- Yin, J.; Li, M.; Li, Y.; Yu, Y.; Lin, B.; Zou, Y.; Liu, Y.; Huo, W.; Xue, J. RSFuzzer: Discovering Deep SMI Handler Vulnerabilities in UEFI Firmware with Hybrid Fuzzing. In Proceedings of the 2023 IEEE Symposium on Security and Privacy (SP), San Francisco, CA, USA, 21–25 May 2023; IEEE: New York, NY, USA, 2023; pp. 2155–2169. [Google Scholar]
- Hu, Q.; Chen, W.; Wang, Z.; Lu, S.; Nie, Y.; Li, X.; Kuang, X. BSFuzz: Branch-State Guided Hybrid Fuzzing. Electronics 2023, 12, 4033. [Google Scholar] [CrossRef]
- Mi, X.; Wang, B.; Tang, Y.; Wang, P.; Yu, B. SHFuzz: Selective hybrid fuzzing with branch scheduling based on binary instrumentation. Appl. Sci. 2020, 10, 5449. [Google Scholar] [CrossRef]
- Lin, P.; Wang, P.; Zhou, X.; Xie, W.; Lu, K.; Zhang, G. HyperGo: Probability-based directed hybrid fuzzing. Comput. Secur. 2024, 142, 103851. [Google Scholar] [CrossRef]
- Fang, W.; Yang, X.; Guo, W.; Sun, H.; Li, Q.; Lin, Z. PBFuzz: Potential-aware Branch-oriented Hybrid Fuzzing. In Proceedings of the 2024 4th International Symposium on Computer Technology and Information Science (ISCTIS), Xi’an, China, 12–14 July 2024; IEEE: New York, NY, USA, 2024; pp. 608–614. [Google Scholar]
- Nguyen, M.D.; Bardin, S.; Bonichon, R.; Groz, R.; Lemerre, M. Binary-Level Directed Fuzzing for Use-after-Free Vulnerabilities. In Proceedings of the 23rd International Symposium on Research in Attacks, Intrusions and Defenses, RAID 2020, San Sebastian, Spain, 14–15 October 2020; Egele, M., Bilge, L., Eds.; USENIX Association: Berkeley, CA, USA, 2020; pp. 47–62. [Google Scholar]
- Gao, X.; Duck, G.J.; Roychoudhury, A. Scalable Fuzzing of Program Binaries with E9AFL. In Proceedings of the 2021 36th IEEE/ACM International Conference on Automated Software Engineering (ASE), Melbourne, Australia, 15–19 November 2021; pp. 1247–1251. [Google Scholar] [CrossRef]
- She, D.; Shah, A.; Jana, S. Effective Seed Scheduling for Fuzzing with Graph Centrality Analysis. In Proceedings of the 2022 IEEE Symposium on Security and Privacy (SP), San Francisco, CA, USA, 22–26 May 2022; pp. 2194–2211. [Google Scholar] [CrossRef]
- Lyu, C.; Ji, S.; Zhang, C.; Li, Y.; Lee, W.H.; Song, Y.; Beyah, R. MOPT: Optimized Mutation Scheduling for Fuzzers. In Proceedings of the 28th USENIX Security Symposium, USENIX Security 2019, Santa Clara, CA, USA, 14–16 August 2019; Heninger, N., Traynor, P., Eds.; USENIX Association: Berkeley, CA, USA, 2019; pp. 1949–1966. [Google Scholar]
- Pham, V.T.; Böhme, M.; Santosa, A.E.; Căciulescu, A.R.; Roychoudhury, A. Smart Greybox Fuzzing. IEEE Trans. Softw. Eng. 2021, 47, 1980–1997. [Google Scholar] [CrossRef]
- Wang, T.; Wei, T.; Gu, G.; Zou, W. TaintScope: A Checksum-Aware Directed Fuzzing Tool for Automatic Software Vulnerability Detection. In Proceedings of the 2010 IEEE Symposium on Security and Privacy, Oakland, CA, USA, 16–19 May 2010; pp. 497–512. [Google Scholar] [CrossRef]
- Peng, H.; Shoshitaishvili, Y.; Payer, M. T-Fuzz: Fuzzing by Program Transformation. In Proceedings of the 2018 IEEE Symposium on Security and Privacy (SP), San Francisco, CA, USA, 20–24 May 2018; pp. 697–710. [Google Scholar] [CrossRef]
- Aschermann, C.; Schumilo, S.; Abbasi, A.; Holz, T. Ijon: Exploring Deep State Spaces via Fuzzing. In Proceedings of the 2020 IEEE Symposium on Security and Privacy (SP), San Francisco, CA, USA, 18–21 May 2020; pp. 1597–1612. [Google Scholar] [CrossRef]
- Österlund, S.; Razavi, K.; Bos, H.; Giuffrida, C. ParmeSan: Sanitizer-guided Greybox Fuzzing. In Proceedings of the 29th USENIX Security Symposium, USENIX Security 2020, Boston, MA, USA, 12–14 August 2020; Capkun, S., Roesner, F., Eds.; USENIX Association: Berkeley, CA, USA, 2020; pp. 2289–2306. [Google Scholar]
- Huang, H.; Guo, Y.; Shi, Q.; Yao, P.; Wu, R.; Zhang, C. BEACON: Directed Grey-Box Fuzzing with Provable Path Pruning. In Proceedings of the 2022 IEEE Symposium on Security and Privacy (SP), San Francisco, CA, USA, 22–26 May 2022; pp. 36–50. [Google Scholar] [CrossRef]
- Bendersky, E. Pycparser. 2010. Available online: https://github.com/eliben/pycparser (accessed on 15 August 2024).
- Microsoft. Z3Prover. Available online: https://github.com/Z3Prover/z3 (accessed on 15 August 2024).
- Li, Y.; Ji, S.; Chen, Y.; Liang, S.; Lee, W.H.; Chen, Y.; Lyu, C.; Wu, C.; Beyah, R.; Cheng, P.; et al. UNIFUZZ: A Holistic and Pragmatic Metrics-Driven Platform for Evaluating Fuzzers. In Proceedings of the 30th USENIX Security Symposium (USENIX Security 21), Online, 11–13 August 2021; USENIX Association: Berkeley, CA, USA, 2021; pp. 2777–2794. [Google Scholar]
| Program | AFL [17] | QSYM [2] | Ratio |
|---|---|---|---|
| readelf | 13,132 | 1177 | 8.96% |
| tcpdump | 21,751 | 1165 | 5.36% |
| pdfimages | 15,521 | 880 | 5.67% |
| pdftops | 16,875 | 865 | 5.13% |
| pdftotext | 18,089 | 888 | 4.91% |
| pngfix | 3194 | 1912 | 59.86% |
| Program | Version | Input Format |
|---|---|---|
| readelf-a @@ | binutils-2.40 | elf |
| tcpdump-e-vv-nr @@ | tcpdump-4.99 | pcap |
| pdftotext @@/dev/null | xpdf-4.04 | |
| pdfimages @@/dev/null | xpdf-4.04 | |
| pdftops @@/dev/null | xpdf-4.04 | |
| pngfix @@ | libpng-1.6.40 | png |
| Program | Fuzzer | Total Branches | Unsolvable Branches | ||
|---|---|---|---|---|---|
| Num | Growth | Num | Growth | ||
| pdftotext | QSYM | 945 | - | 480 | - |
| BSP | 1338 | +41.59% | 712 | +48.33% | |
| pdftops | QSYM | 786 | - | 348 | - |
| BSP | 1283 | +63.23% | 683 | +96.26% | |
| pdfimages | QSYM | 809 | - | 380 | - |
| BSP | 1119 | +38.32% | 584 | +53.68% | |
| tcpdump | QSYM | 4254 | - | 1016 | - |
| BSP | 6570 | +54.44% | 1632 | +60.63% | |
| readelf | QSYM | 2302 | - | 299 | - |
| BSP | 3115 | +35.32% | 545 | +82.27% | |
| pngfix | QSYM | 1438 | - | 547 | - |
| BSP | 2027 | +40.96% | 595 | +8.78% | |
| Average | QSYM | 1756 | - | 512 | - |
| BSP | 2575 | +46.68% | 792 | +54.76% | |
| Program | Unsolvable and Uncovered |
|---|---|
| pdftotext | 148 |
| pdftops | 90 |
| pdfimages | 145 |
| tcpdump | 395 |
| readelf | 218 |
| pngfix | 237 |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2024 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).
Share and Cite
Qian, C.; Pang, L.; Kuang, X.; Qin, J.; Zang, Y.; Zhao, Q.; Zhang, J. BSP: Branch Splitting for Unsolvable Path Hybrid Fuzzing. Electronics 2024, 13, 4935. https://doi.org/10.3390/electronics13244935
Qian C, Pang L, Kuang X, Qin J, Zang Y, Zhao Q, Zhang J. BSP: Branch Splitting for Unsolvable Path Hybrid Fuzzing. Electronics. 2024; 13(24):4935. https://doi.org/10.3390/electronics13244935
Chicago/Turabian StyleQian, Cheng, Ling Pang, Xiaohui Kuang, Jiuren Qin, Yujie Zang, Qichao Zhao, and Jiapeng Zhang. 2024. "BSP: Branch Splitting for Unsolvable Path Hybrid Fuzzing" Electronics 13, no. 24: 4935. https://doi.org/10.3390/electronics13244935
APA StyleQian, C., Pang, L., Kuang, X., Qin, J., Zang, Y., Zhao, Q., & Zhang, J. (2024). BSP: Branch Splitting for Unsolvable Path Hybrid Fuzzing. Electronics, 13(24), 4935. https://doi.org/10.3390/electronics13244935





