A Perfect Security Key Management Method for Hierarchical Wireless Sensor Networks in Medical Environments
Abstract
1. Introduction
1.1. Major Contributions
1.2. Research Organization
2. Schemes Related to the Security of WSN Key Management
3. Introductory Details of the Proposed Techniques for the Security of WSN Key Management
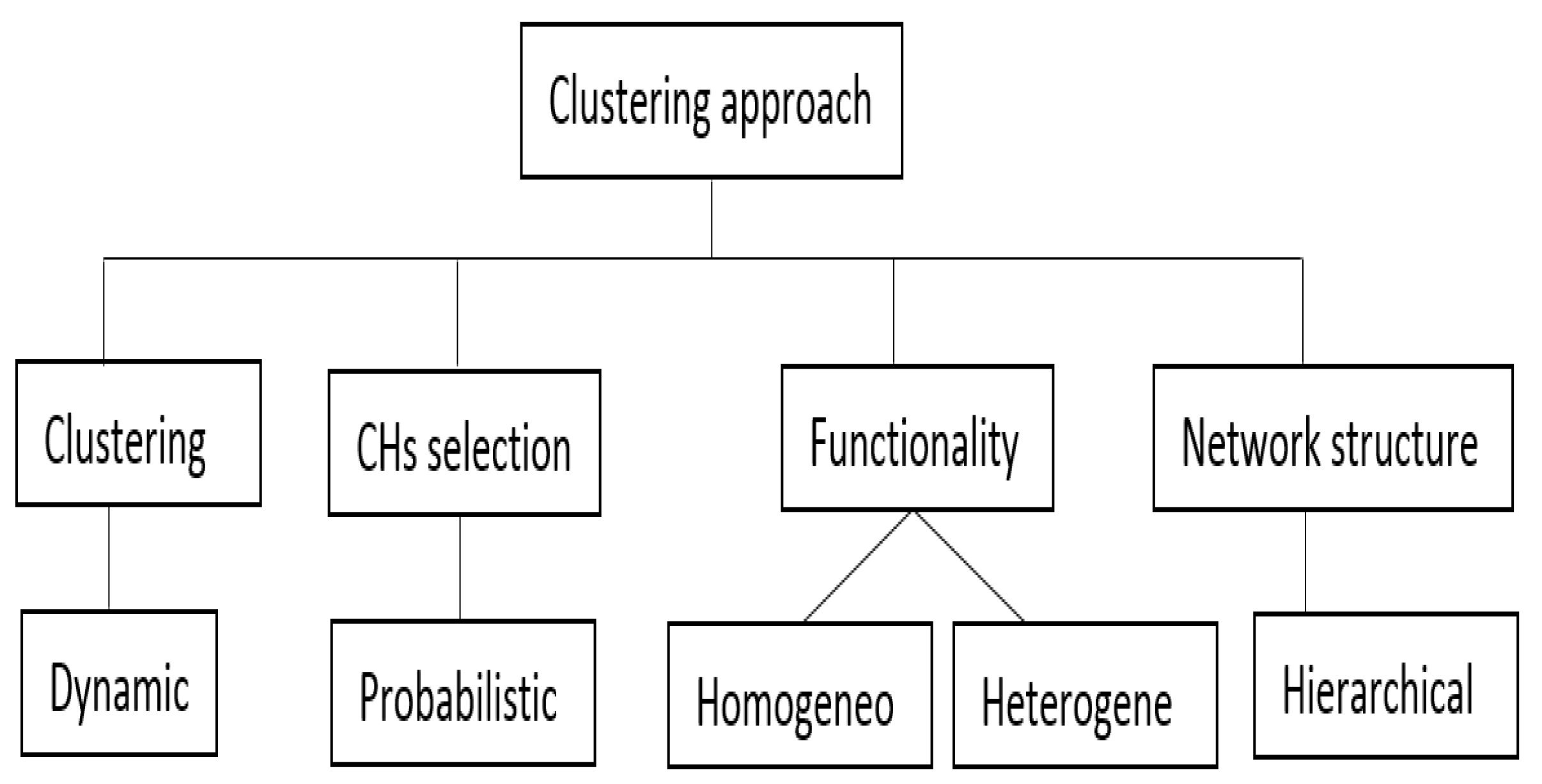
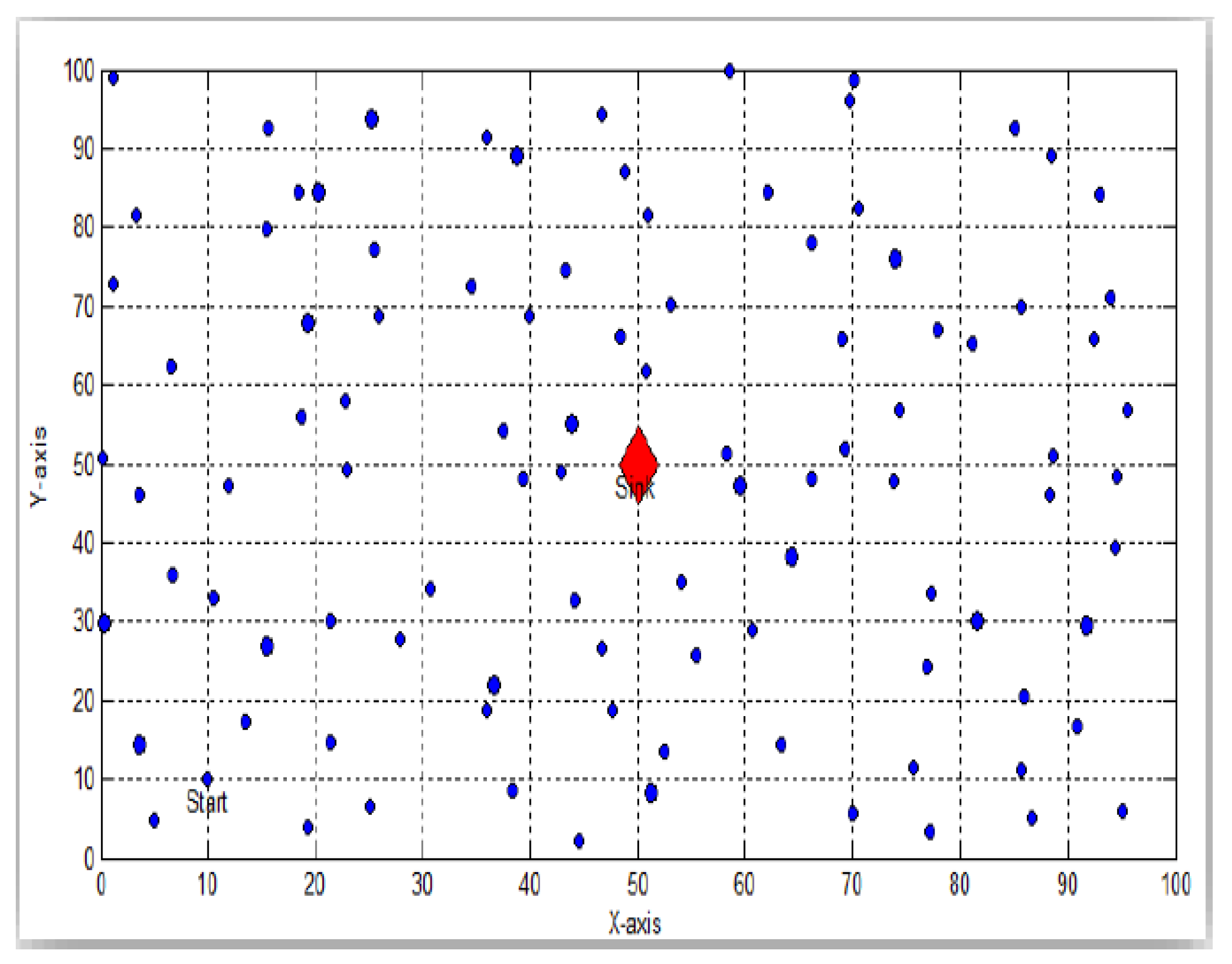
3.1. Hybrid Energy-Efficient Distributed Clustering Protocol
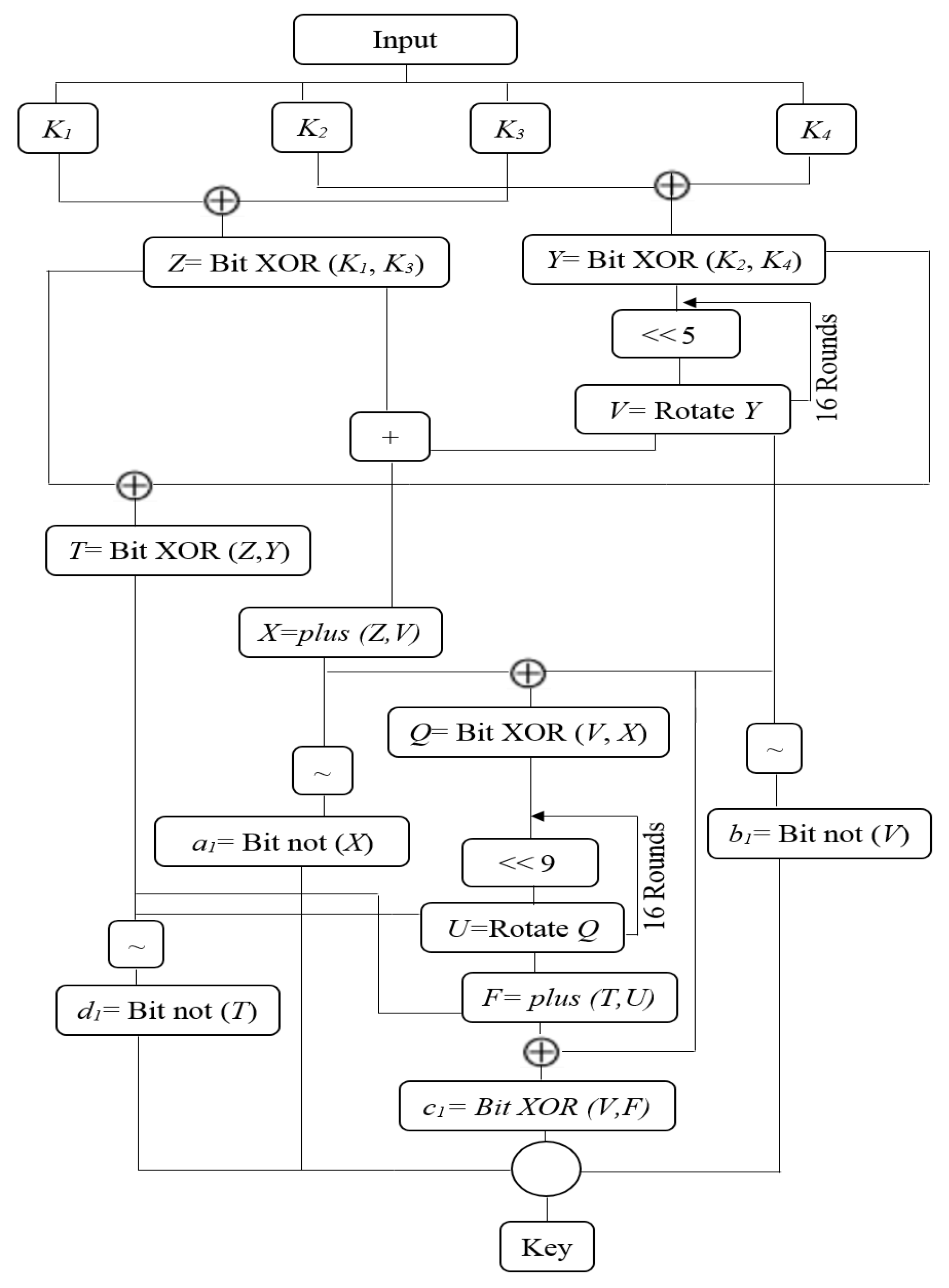
3.2. Rivest Cipher 5
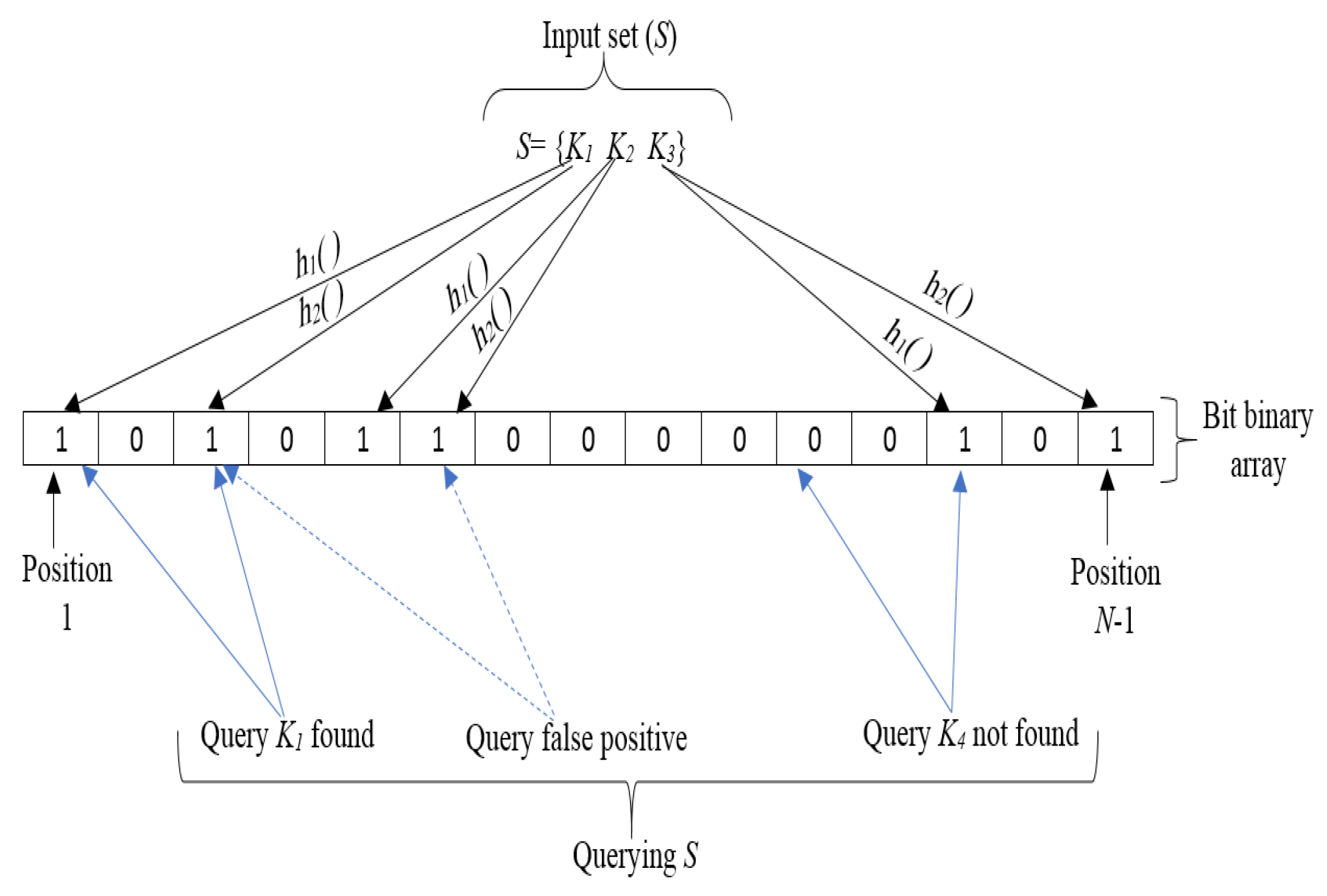
3.3. Bloom Scheme
3.4. Pseudorandom Number Generator
4. The Proposed Method
4.1. Key Generation
4.1.1. Key Generation between CH-CH and CH-BS
- First step: We select a prime element from the field GF(q), where q is bigger than the key length and q > N. Next, our method constructs a public matrix G based on the sensor neighbors that is N × N in size relying on the , value a number of rows with N columns.
- Second step: The BS produces a D symmetric matrix of size ( + 1) × ( + 1). Then, it computes matrix A by .
- Third step: All rows of matrix A stored in a memory of the sensors. When sensor i wishes to connect with sensor j, sensor i multiplies the row with the column . Then the result is a secret key. To demonstrate the operation of the modified Bloom’s method using an adjacency matrix. For example, the network has 6 sensors, for instance, N = 6, = 3 (secure parameter), and q = 29 (prime numbers).Modified adjacency matrix:Public matrix (G):Secret semantic matrix (D):A= :
- Shared key = Row of Node i * Public column of Node j;
- Shared key = Row of Node j * Public column of Node i.
4.1.2. Key Generation between CH-Sensors
- Step1: The initial key has been split into four parts , and
- 1.
- For j from 1 to 32
- -
- Z [Bit XOR()]
- -
- Y [Bit XOR()]
- -
- For u from 1 to 16
- -
- V [swapping(Y) 5]
- -
- End
- -
- X addition(Z,V) module
- -
- T [Bit XOR(Z,Y)]
- -
- Q [Bit XOR(V,X)]
- -
- For i from 1 to 16
- -
- U [swapping(Q) 9]
- -
- end
- -
- F addition(T, U) module
- -
- [Bit not(X)]
- -
- end
- 2.
- For j from 1 to 16
- -
- For s from 1 to 16
- -
- [Bit not(V)]
- -
- end
- -
- [Bit XOR(V, F)]
- -
- For n from 1 to 16
- -
- [Bit not(F)]
- -
- end
- end
- A - [binary Vector to Hex()]
- B - [binary Vector to Hex()]
- C - [binary Vector to Hex()]
- D - [binary Vector to Hex()]
- Step2: The four registers [A,B,C,D] combine to form the final key (shared key-64 bit).
4.2. Encryption and Decryption Procedures
4.3. Key-Updating
Sensor Add and Delete
5. Results
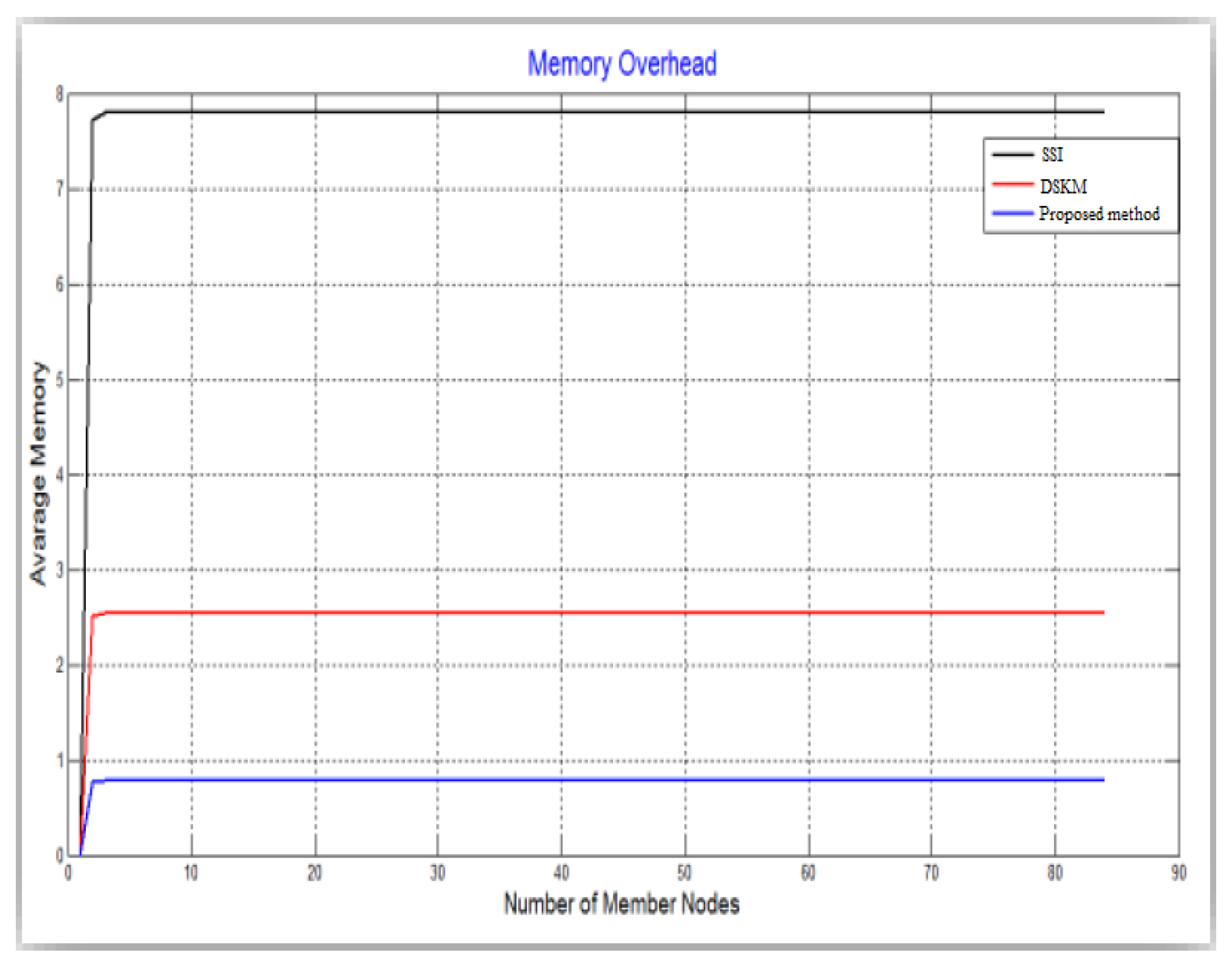
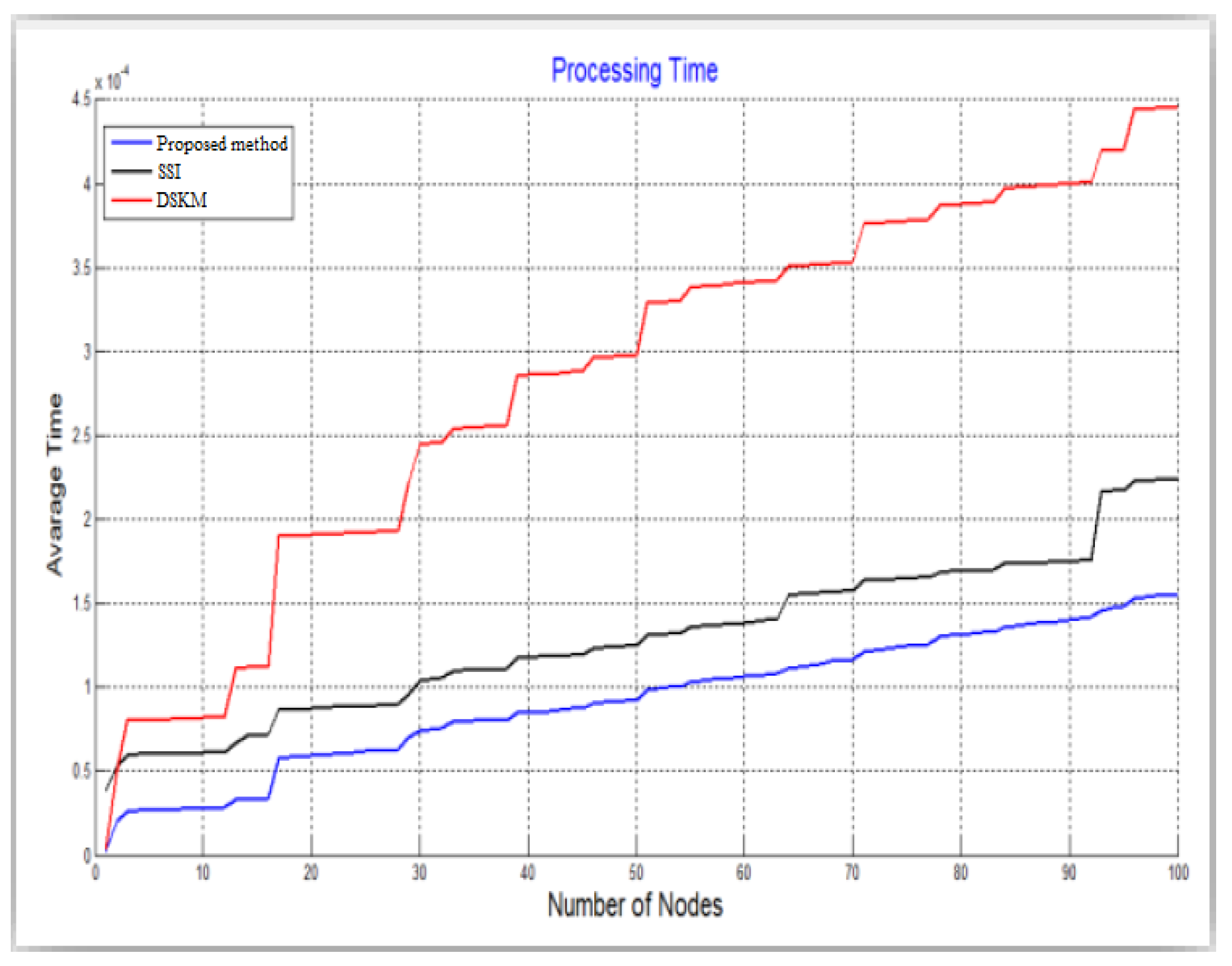
5.1. Performance Results
5.2. Security Results
- Sensor node capture attack: When the attacker compromises a sensor and obtains some previous parameters such as SK-K, they try to use that key in future sessions of the WSN. In our proposed method, all sensors use new SH-K for each session. Therefore, when a hacker performs a sensor node capture attack on our WSN it will not affect the confidential information of other sensors.
- Sensor CH capture attack: When the hacker succeeds in executing this attack on CH. It tries to use the previous Auth-K to make all its sensors trust it and send all data and information to that hacker in that session. In our proposed method, the sensors within the cluster do not handle the old Auth-K. Thus, this attack cannot compromise WSN information by relying on a single CH, namely, our proposed method resists the CH capture attack.
- BS capture attack: We assume that BS is safe against capture attacks. However, assuming that the hacker was able to penetrate the BS either remotely or by stealing the BS device. The hacker will not benefit from the previous information of sensors or CHs because all security parameters (such as SH-K and Auth-K) in our proposed method are generated instantly/unique by PRNG and Bloom and are hidden by RC5. However, the hacker may find some data collected by sensors. First, we assume that the data is transferred periodically to a central server so that even if the hacker tampered with this data, the original copy will be safe. Second, our research focuses on security key management and not the data collected. Therefore, our method is able to block BS capture attacks.
- A capture attack of more than one sensor node: If the hacker was able to compromise two or three sensors. Then he tried to analyze the obtained security parameters (such as Auth-Ks) for these sensors. The hacker cannot use these current parameters to hack network information in the current session. Because our method uses the RC5 algorithm, which has the advantage of preventing analysis and differential risks. Therefore, our method prevents this attack from extracting security parameters from Auth-Ks.
- A capture attack of more than one CH: When a hacker can compromise two CHs or three CHs. It tries to use the security parameters available from the compromised CHs. However, our proposed method uses a Bloom filter between BS and CHs to manage and verify the exchanged keys. The hacker cannot use the old parameters to communicate with the BS because these parameters will be rejected by the BS. Therefore, our proposed method is able to prevent this attack.
6. Conclusions and Future Trends
Author Contributions
Funding
Conflicts of Interest
Abbreviations
| Auth-K | Authentication key |
| BS | Base station |
| CBC-RC5 | Cipher block chaining-Rivest cipher 5 |
| CH | Cluster head |
| HEED | Hybrid energy efficient distributed |
| ID | Identifier |
| PRNG | Pseudo-random number generator |
| SH-K | Shared key |
| Sym/Asym | Symmetric/Asymmetric |
References
- Patil, H.K.; Szygenda, S.A.; Szygenda, S.A. Security for Wireless Sensor Networks Using Identity-Based Cryptography; CRC Press: Boca Raton, FL, USA, 2013. [Google Scholar]
- Huanan, Z.; Suping, X.; Jiannan, W. Security and application of wireless sensor network. Procedia Comput. Sci. 2021, 183, 486–492. [Google Scholar] [CrossRef]
- Awaad, M.H.; Jebbar, W.A. Study to analyze and compare the LEACH protocol with three methods to improve it and determine the best choice. J. Comput. Sci. Control. Syst. 2014, 7, 5. [Google Scholar]
- Al-Zubaidie, M.; Zhang, Z.; Zhang, J. REISCH: Incorporating lightweight and reliable algorithms into healthcare applications of WSNs. Appl. Sci. 2020, 10, 2007. [Google Scholar] [CrossRef]
- Banerjee, A.; De, S.K.; Majumder, K.; Das, V.; Giri, D.; Shaw, R.N.; Ghosh, A. Construction of effective wireless sensor network for smart communication using modified ant colony optimization technique. In Advanced Computing and Intelligent Technologies; Springer: Singapore, 2022; pp. 269–278. [Google Scholar]
- Khalaf, O.I.; Romero, C.A.T.; Hassan, S.; Iqbal, M.T. Mitigating hotspot issues in heterogeneous wireless sensor networks. J. Sens. 2022, 2022, 7909472. [Google Scholar] [CrossRef]
- Al-Zubaidie, M.; Zhang, Z.; Zhang, J. RAMHU: A new robust lightweight scheme for mutual users authentication in healthcare applications. Secur. Commun. Netw. 2019, 2019, 3263902. [Google Scholar] [CrossRef]
- Majid, M.; Habib, S.; Javed, A.R.; Rizwan, M.; Srivastava, G.; Gadekallu, T.R.; Lin, J.C.W. Applications of wireless sensor networks and internet of things frameworks in the industry revolution 4.0: A systematic literature review. Sensors 2022, 22, 2087. [Google Scholar] [CrossRef]
- Al-Zubaidie, M. Implication of lightweight and robust hash function to support key exchange in health sensor networks. Symmetry 2023, 15, 152. [Google Scholar] [CrossRef]
- Sastry, A.S.; Sulthana, S.; Vagdevi, S. Security threats in wireless sensor networks in each layer. Int. J. Adv. Netw. Appl. 2013, 4, 1657. [Google Scholar]
- Lee, C.-C. Security and privacy in wireless sensor networks: Advances and challenges. Sensors 2020, 20, 744. [Google Scholar] [CrossRef]
- Barati, H. A hierarchical key management method for wireless sensor networks. Microprocess. Microsyst. 2022, 90, 04489. [Google Scholar]
- Al-Zubaidie, M.; Zhang, Z.; Zhang, J. PAX: Using pseudonymization and anonymization to protect patients’ identities and data in the healthcare system. Int. J. Environ. Res. Public Health 2019, 16, 1490. [Google Scholar] [CrossRef] [PubMed]
- Al-Zubaidie, M.H.A. Incorporating Security into Electronic Health Records Based Healthcare Systems with Wireless Sensor Networks. Ph.D. Dissertation, University of Southern Queensland, Darling Heights, QLD, Australia, 2020. [Google Scholar]
- Ghosal, A.; Conti, M. Key management systems for smart grid advanced metering infrastructure: A survey. IEEE Commun. Surv. Tutor. 2019, 21, 2831–2848. [Google Scholar] [CrossRef]
- Zhou, H.; Lv, K.; Huang, L.; Ma, X. Security assessment and key management in a quantum network. arXiv 2019, arXiv:1907.08963. [Google Scholar] [CrossRef]
- Al-Zubaidie, M.; Zhang, Z.; Zhang, J. User authentication into electronic health record based on reliable lightweight algorithms. In Handbook of Research on Cyber Crime and Information Privacy; IGI Global: Hershey, PA, USA, 2021; pp. 700–738. [Google Scholar]
- Shahzadi, R.; Anwar, S.M.; Qamar, F.; Ali, M.; Rodrigues, J.J. Chaos based enhanced RC5 algorithm for security and integrity of clinical images in remote health monitoring. IEEE Access 2019, 7, 52858–52870. [Google Scholar] [CrossRef]
- Li, L.; Wang, X. A high security dynamic secret key management scheme for wireless sensor networks. In Proceedings of the Third International Symposium on Intelligent Information Technology and Security Informatics, Jinan, China, 2–4 April 2010; pp. 507–510. [Google Scholar]
- Iwendi, C.; Allen, A.; Offor, K. Smart security implementation for wireless sensor network nodes. J. Wirel. Sens. Netw. 2015, 1, 1. [Google Scholar]
- Zhang, Y.; Pengfei, J. An efficient and hybrid key management for heterogeneous wireless sensor networks. In Proceedings of the 26th Chinese Control and Decision Conference (2014 CCDC), Changsha, China, 31 May 2014–2 June 2014; pp. 1881–1885. [Google Scholar]
- Zhang, X.; Wang, J. An efficient key management scheme in hierarchical wireless sensor networks. In Proceedings of the 2015 International Conference on Computing, Communication and Security (ICCCS), Pointe aux Piments, Mauritius, 4–5 December 2015; pp. 1–7. [Google Scholar]
- Qin, D.; Jia, S.; Yang, S.; Wang, E.; Ding, Q. A lightweight authentication and key management scheme for wireless sensor networks. J. Sens. 2016, 2016, 1547963. [Google Scholar] [CrossRef]
- Moara-Nkwe, K.; Shi, Q.; Lee, G.M.; Eiza, M.H. A novel physical layer secure key generation and refreshment scheme for wireless sensor networks. IEEE Access 2018, 6, 11374–11387. [Google Scholar] [CrossRef]
- Chanda, A.; Sadhukhan, P.; Mukherjee, N. Key management for hierarchical wireless sensor networks: A robust scheme. EAI Endorsed Trans. Internet Things 2020, 6, 23. [Google Scholar] [CrossRef]
- Jia, C.; Ding, H.; Zhang, C.; Zhang, X. Design of a dynamic key management plan for intelligent building energy management system based on wireless sensor network and blockchain technology. Alex. Eng. J. 2021, 60, 337–346. [Google Scholar] [CrossRef]
- Ahlawat, P.; Dave, M. An attack resistant key predistribution scheme for wireless sensor networks. J. King Saud Univ.-Comput. Inf. Sci. 2021, 33, 268–280. [Google Scholar] [CrossRef]
- Kumar, V.; Malik, N. Enhancing the connectivity and resiliency of random key pre-distribution schemes for wireless sensor network. Int. J. Syst. Assur. Eng. Manag. 2022, 13, 92–99. [Google Scholar] [CrossRef]
- Tyagi, P.; Kumari, S.; Alzahrani, B.A.; Gupta, A.; Yang, M.H. An enhanced user authentication and key agreement scheme for wireless sensor networks tailored for IoT. Sensors 2022, 22, 8793. [Google Scholar] [CrossRef]
- Liu, J.; Liu, L.; Liu, Z.; Lai, Y.; Qin, H.; Luo, S. WSN node access authentication protocol based on trusted computing. Simul. Model. Pract. Theory 2022, 117, 102522. [Google Scholar] [CrossRef]
- Wang, C.; Wang, D.; Tu, Y.; Xu, G.; Wang, H. Understanding node capture attacks in user authentication schemes for wireless sensor networks. IEEE Trans. Dependable Secur. Comput. 2020, 19, 507–523. [Google Scholar] [CrossRef]
- Ullah, Z. A survey on hybrid, energy efficient and distributed (HEED) based energy efficient clustering protocols for wireless sensor networks. Wirel. Pers. Commun. 2020, 112, 2685–2713. [Google Scholar] [CrossRef]
- Gupta, P.; Sharma, A.K. Clustering-based optimized HEED protocols for WSNs using bacterial foraging optimization and fuzzy logic system. Soft Comput. 2019, 23, 507–526. [Google Scholar] [CrossRef]
- Awaad, M.H.; Jebbar, W.A. Prolong the lifetime of WSN by determining a correlation nodes in the same zone and searching for the best not the closest CH. Int. J. Mod. Educ. Comput. Sci. 2014, 6, 31. [Google Scholar] [CrossRef]
- Mishall Hammed, A. Improve the effectiveness of sensor networks and extend the network lifetime using 2BSs and determination of area of CHs choice. J. Comput. Sci. Control. Syst. 2014, 7, 15. [Google Scholar]
- Anitha, G.; Vijayakumari, V.; Thangavelu, S. A comprehensive study and analysis of LEACH and HEED routing protocols for wireless sensor networks—With suggestion for improvements. Indones. J. Electr. Eng. Comput. Sci. 2018, 9, 778–783. [Google Scholar] [CrossRef]
- Boudhiafi, W.; Ezzedine, T. Optimization of multi-level HEED protocol in wireless sensor networks. In Communications in Computer and Information Science: International Conference on Applied Informatics; Springer: Cham, Swidzerland, 2021; pp. 407–418. [Google Scholar]
- Jamil, A.S.; Rahma, A.M.S. Image encryption based on multi-level keys on RC5 algorithm. iJIM 2022, 16, 101. [Google Scholar]
- Raj, K.V.; Ankitha, H.; Ankitha, N.G.; Hegde, L.K. Honey encryption based hybrid cryptographic algorithm: A fusion ensuring enhanced security. In Proceedings of the 2020 5th International Conference on Communication and Electronics Systems (ICCES), Coimbatore, India, 10–12 June 2020; pp. 490–494. [Google Scholar]
- Alenezi, M.N.; Alabdulrazzaq, H.; Mohammad, N.Q. Symmetric encryption algorithms: Review and evaluation study. Int. J. Commun. Netw. Inf. Secur. 2020, 12, 256–272. [Google Scholar]
- Sadhya, D.; Sing, S.K. Providing robust security measures to bloom filter based biometric template protection schemes. Comput. Secur. 2017, 67, 59–72. [Google Scholar] [CrossRef]
- Lim, K.; Liu, W.; Wang, X.; Joung, J. SSKM: Scalable and secure key management scheme for group signature based authentication and CRL in VANET. Electronics 2019, 8, 1330. [Google Scholar] [CrossRef]
- Sampangi, R.V.; Sampalli, S. Metamorphic framework for key management and authentication in resource-constrained wireless networks. Int. J. Netw. Secur. 2017, 19, 430–442. [Google Scholar]
- Ghorpade, S.; Zennaro, M.; Chaudhari, B.S. Towards green computing: Intelligent bio-inspired agent for IoT-enabled wireless sensor networks. Int. J. Sens. Netw. 2021, 35, 121–131. [Google Scholar] [CrossRef]
- Mcginthy, J.M.; Michaels, A.J. Further analysis of prng-based key derivation functions. IEEE Access 2019, 7, 978–995. [Google Scholar] [CrossRef]





| Properties | HEED | LEACH |
|---|---|---|
| Balanced clustering | Good | Moderate |
| Balanced loading | High | Moderate |
| CH capability | Data aggregation, homogeneous | Data aggregation, homogeneous |
| Clustering process execution | Iterative | Probabilistic |
| Cluster overlapping | No | No |
| Cluster stability | High | Moderate |
| Delay | Moderate | Very small |
| Energy efficiency | Moderate | Low |
| Mobility | Stationary | Stationary |
| Routing between clusters | Single hop and Multi hop | Single hop |
| Routing within a cluster | Single hop | Single hop |
| Scalability | Moderate | Low |
| Security Feature | Qin et al. [23] | Ahlawat and Dave [27] | Liu et al. [30] | Wang et al. [31] | Proposed Method |
|---|---|---|---|---|---|
| Anti node capture attacks | One | One | One | Many | Many |
| Encryption type | Sym | Sym/Asym | Sym | Sym | |
| Flexibility | Yes | ||||
| Forward secrecy | Yes | Yes | Yes | Yes | |
| Info. hiding | Yes | Yes | Yes | ||
| Keys randomness | Low | Medium | Low | Medium | High |
| Scalability | Low | Low | Medium | Low | High |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2023 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).
Share and Cite
Muhajjar, R.A.; Flayh, N.A.; Al-Zubaidie, M. A Perfect Security Key Management Method for Hierarchical Wireless Sensor Networks in Medical Environments. Electronics 2023, 12, 1011. https://doi.org/10.3390/electronics12041011
Muhajjar RA, Flayh NA, Al-Zubaidie M. A Perfect Security Key Management Method for Hierarchical Wireless Sensor Networks in Medical Environments. Electronics. 2023; 12(4):1011. https://doi.org/10.3390/electronics12041011
Chicago/Turabian StyleMuhajjar, Raad A., Nahla A. Flayh, and Mishall Al-Zubaidie. 2023. "A Perfect Security Key Management Method for Hierarchical Wireless Sensor Networks in Medical Environments" Electronics 12, no. 4: 1011. https://doi.org/10.3390/electronics12041011
APA StyleMuhajjar, R. A., Flayh, N. A., & Al-Zubaidie, M. (2023). A Perfect Security Key Management Method for Hierarchical Wireless Sensor Networks in Medical Environments. Electronics, 12(4), 1011. https://doi.org/10.3390/electronics12041011







