Metaverse Security: Issues, Challenges and a Viable ZTA Model
Abstract
:1. Introduction
- The ability to authenticate everything;
- Repeated time/session-based authentication and identity verification;
- Access control with fine-grained privileges;
- Data validation;
- Traffic and logs validation.
- A comprehensive review of the nascent literature related to metaverse security is performed and the major issues are consolidated;
- A comprehensive model for metaverse security is formulated as a function of enabling and supporting technologies;
- A potentially viable Zero-Trust Architecture (ZTA) model to address the identified shortcomings is proposed.
2. Literature Survey
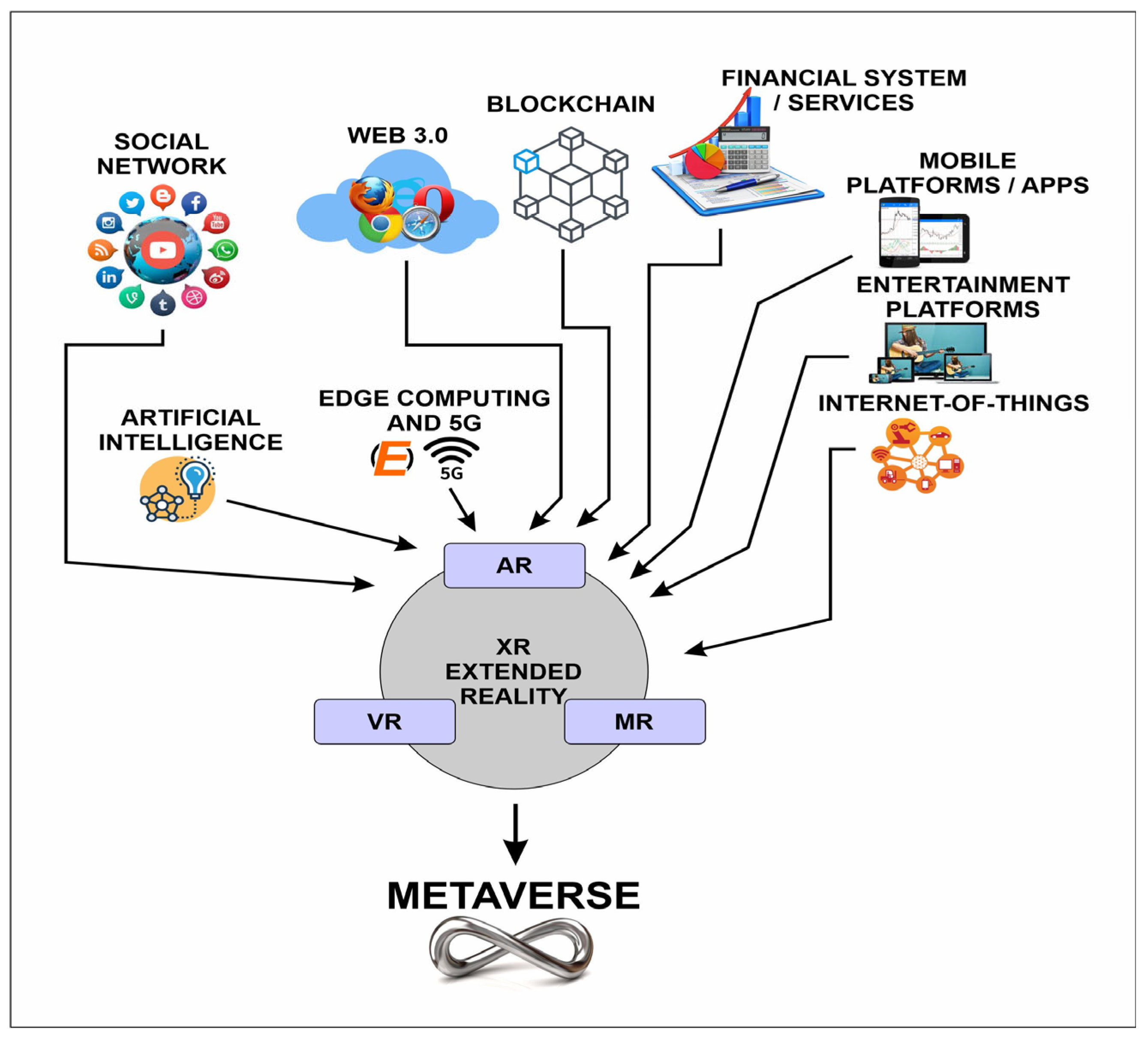
3. The Metaverse Ecosystem
- Closed Metaverse: For niche applications and use-cases limited to use by a particular community with specialized needs;
- Federated Metaverse: Managed and operated by a large corporation with an ecosystem of cooperating partners, third-party vendors and service providers delivering a unified experience to the end users;
- Open Metaverse: A non-federated metaverse controlled by no single entity with an open architecture and a developer community building applications/services for end users.
- Access: Currently only through headsets, which are not pervasive;
- Ease-of-Use: Users find the current version of headsets bulky and difficult to wear for a long time;
- Lack of Developed Ecosystem: Few Apps available on current VR Platforms;
- Security and Privacy: XR environments suffer from the security vulnerabilities of the underlying technologies, including issues regarding user privacy in virtual worlds.
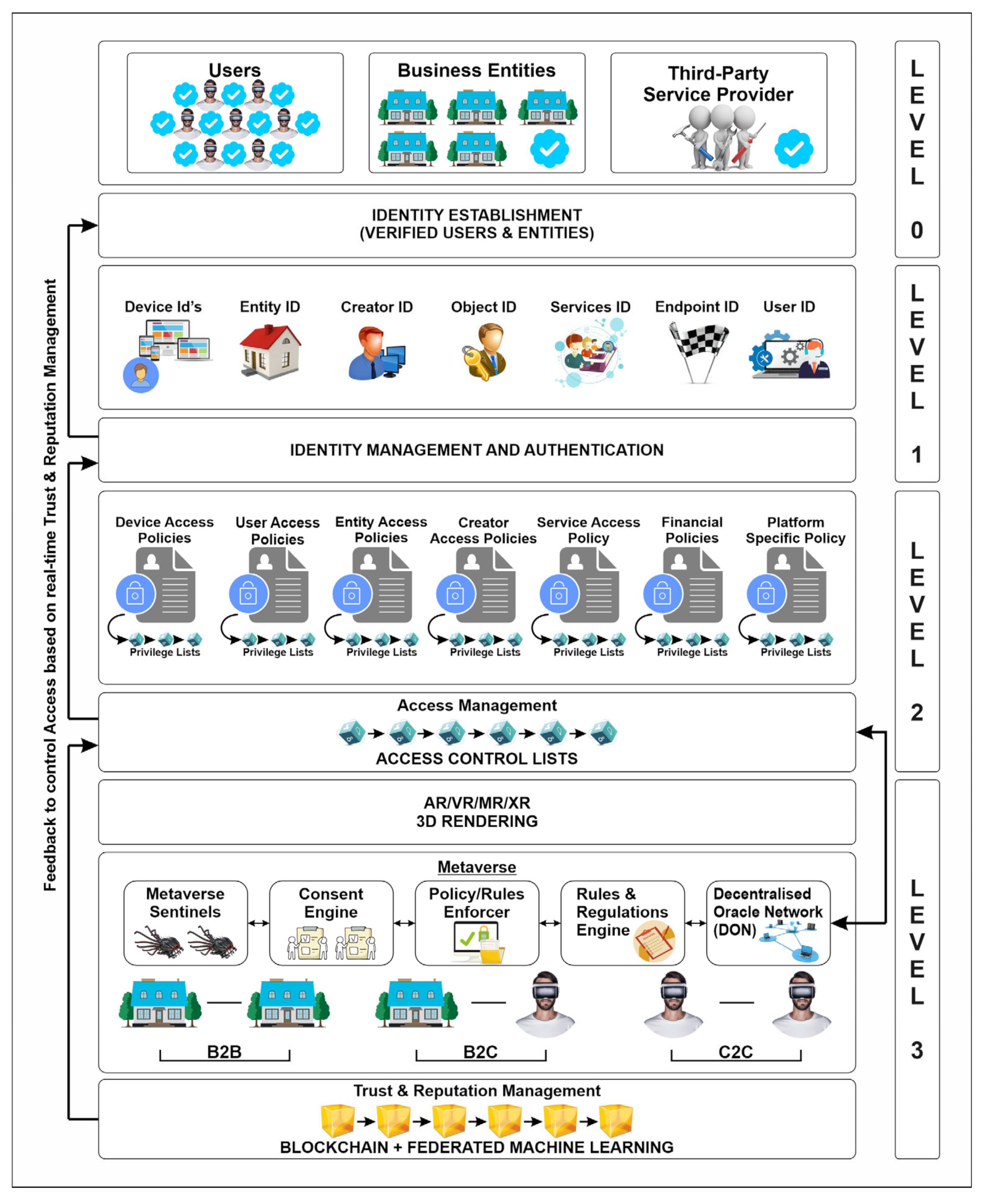
4. ZTA Model for the Metaverse
- Level 0: Verification and Registration: One of the major challenges in controlling errant user behavior on social networks is the anonymity offered by these platforms. The use of bots is also prevalent in propagating misinformation and fake news. Hence, we propose to make user/entity verification a pre-requisite for the ZTA model for the metaverse. Thus, only pre-verified users/entities shall be permitted to register for the metaverse, thereby alleviating the challenge associated with existing platforms. Twitter had recently introduced the “blue tick” symbol on select user profiles as an indication that the user identity is verified and authentic. This ensured that genuine content creators could obtain credit for their content and imposters would not gain undue benefits. Therefore, there is a case to ensure that all users and entities should have their identity and antecedents verified before being permitted to use public infrastructure and services on the metaverse [41].While the Twitter process of identity verification is manual, this task can be easily automated. In many countries, governments have built identity verification services over their citizen registries or other such databases, which can be accessed by third-party service providers for a fee [42]. In India, it is common for financial service providers to complete their KYC (Know-Your-Customer) formalities using the Aadhaar (unique ID) identity verification APIs. It can be expected that verifying user identities and allowing verified users to register on the metaverse shall prevent a large number of untoward incidents common to social networking platforms.
- Level 1: Identity Management and Authentication: This level performs the first level of authentication before permitting users access to the metaverse. In addition to performing authentication, this layer is also responsible for identity management. In the metaverse, users may want their identities to be publicly visible or they might want to use an avatar or digital twin to access various services. Hence, the identity management function is responsible for creating an avatar or digital twin for the user and storing its mapping in an encrypted database. Hence, user privacy is ensured. Another alternative to delivering trusted identity management in the metaverse is the use of a trusted third-party, which can map the real-identity of the verified user with her digital twin, such that the platform itself is not aware of the actual mapping [43]. Should the need arise, the real-identity can be deciphered using a multi-party request and consensus protocol involving the user, platform, other entities and the trusted third-party identity management service.
- Level 2: Access Management: The access management layer is responsible for ensuring seamless access to the AR/VR/XR-rendering layer and to the metaverse. The access control layer encompasses the access policies for all the entities in the metaverse to provide fine-grained access control at the level of each entity. Corresponding to the access policies for each entity are the privilege lists, which define increasing privilege levels based on the earned reputation by that entity [44]. The increasing privilege levels seek to reward good user behavior within the metaverse. The access control policies and the privilege lists feed into the level-3 metaverse sentinels, which continuously evaluate user/entity actions and take appropriate actions as per the pre-defined consent and access/privilege levels. At the platform level, access control lists are maintained to control user/entity access to specific areas within the metaverse.
- Level 3: Control, Trust and Reputation Management: The access and privilege policies, rules and regulations are codified into the rules and regulations engine, which instantiates multiple policy/rules-enforcer agents. User consent in accessing specific areas/content, as well as allowing other users access to the private space of users, is captured by the consent engine. Within the metaverse, the engagement and transactions between different entities, namely business to business, business to consumer and consumer to consumer, are continuously monitored by metaverse sentinels, which work in conjunction with the policy/rules-enforcer agents to detect any violations or unintended behavior by any of the entities. All violations are recorded on the blockchain, and trust and reputation scores are adjusted accordingly. Repeated violations may result in access privileges being revoked or demoted to lower levels. Reputation scores shall be determined for entities over a significant period of time and good scores shall unlock several higher access privileges for users/entities [45,46]. Further, federated machine learning is envisaged to be employed to determine prospective best-fit partners, violators, etc. In this layer for ensuring data validation, the use of Decentralized Oracle Networks (DONs) is also proposed, as DONs ensure credible and authentic off-chain real-world information, which can be used seamlessly with on-chain data within the metaverse. This shall enable exciting decentralized applications (dApps) to be built and deployed while ensuring data quality and security.
- Verified and authenticated identities of users and other entities, promoting greater accountability and provenance;
- Using trusted third-party identity management services, which generate virtual identities for the metaverse while keeping real identities anonymous for enhanced user privacy [47];
- Providing users complete control over their privacy settings and how others can interact with them in the metaverse, including access control to their defined private space;
- Pre-defined rules and regulations outlining acceptable behavior in the metaverse, with the ability to enforce the rules;
- Use of Decentralized Oracle Networks (DONs) as an effective data validation framework for enabling credible off-chain data to be used as part of on-chain data within the metaverse [27];
- Continuous monitoring of user interactions in the metaverse using sentinels and identifying and isolating malicious or undesirable behavior that violates the rules and regulations;
- Computing and managing trust and reputation for all entities in the metaverse on an ongoing basis to govern access rights and privileges [48];
- Ability to remove users from the metaverse based on the severity of the violation committed, leading to permanent revocation of their access [49].
5. Conclusions and Future Work
6. Future Directions for the Challenges
Research Limitations
Author Contributions
Funding
Data Availability Statement
Conflicts of Interest
References
- Sparkes, M. What Is a Metaverse; Elsevier: Amsterdam, The Netherlands, 2021. [Google Scholar]
- Mystakidis, S. Metaverse. Encyclopedia 2022, 2, 486–497. [Google Scholar] [CrossRef]
- Dionisio, J.D.N.; Iii, W.G.B.; Gilbert, R. 3D virtual worlds and the metaverse: Current status and future possibilities. ACM Comput. Surv. CSUR 2013, 45, 1–38. [Google Scholar] [CrossRef]
- Inc. Facebook Changing Its Name to Meta Is a Brilliant Business Move: FB Meta. 2021. Available online: https://www.inc.com/justin-bariso/facebook-meta-mark-zuckerberg-innovators-dilemma-why-did-facebook-change-its-name.html/ (accessed on 14 September 2022).
- Kürtünlüoğlu, P.; Akdik, B.; Karaarslan, E. Security of virtual reality authentication methods in metaverse: An overview. arXiv 2022, arXiv:2209.06447. [Google Scholar]
- Voshmgir, S. Token Economy: How the Web3 Reinvents the Internet (Vol. 2); Token Kitchen: Berlin, Germany, 2020. [Google Scholar]
- Lee, L.-H.; Braud, T.; Zhou, P.; Wang, L.; Xu, D.; Lin, Z.; Hui, P. All one needs to know about metaverse: A complete survey on technological singularity, virtual ecosystem, and research agenda. arXiv 2021, arXiv:2110.05352. [Google Scholar]
- Jeon, J.-E. The effects of user experience-based design innovativeness on user-metaverse platform channel relationships in South Korea. J. Distrib. Sci. 2021, 19, 81–90. [Google Scholar]
- Gadekallu, T.R.; Huynh-The, T.; Wang, W.; Yenduri, G.; Ranaweera, P.; Pham, Q.-V.; Liyanage, M. Blockchain for the metaverse: A review. arXiv 2022, arXiv:2203.09738. [Google Scholar]
- Khatri, M. Revamping the marketing world with metaverse–The future of marketing. Int. J. Comput. Appl. 2022, 975, 8887. [Google Scholar] [CrossRef]
- Chung, K.H.Y.; Li, D.; Adriaens, P. Technology-enabled financing of sustainable infrastructure: A case for blockchains and decentralized oracle networks. Technol. Forecast. Soc. Change 2023, 187, 122258. [Google Scholar] [CrossRef]
- Gray, M. Introducing project bletchley and elements of blockchain born in the microsoft cloud. Microsoft Dev. Blog 2016. Available online: https://azure.microsoft.com/it-it/blog/bletchley-blockchain/ (accessed on 14 September 2022).
- Rose, S.; Borchert, O.; Mitchell, S.; Connelly, S. Zero Trust Architecture; National Institute of Standards and Technology: Gaithersburg, MD, USA, 2020. [Google Scholar]
- Tang, F.; Chen, X.; Zhao, M.; Kato, N. The Roadmap of Communication and Networking in 6G for the Metaverse. IEEE Wirel. Commun. 2022, 1–15. [Google Scholar] [CrossRef]
- Evans, L.; Frith, J.; Saker, M. User Generated Worlds. In From Microverse to Metaverse; Emerald Publishing Limited: Bingley, UK, 2022; pp. 41–48. [Google Scholar]
- Seok, W.H. Analysis of metaverse business model and ecosystem. Electron. Telecommun. Trends 2021, 36, 81–91. [Google Scholar]
- Abduvahobovich, I.A. Digital Educational materials for the organization and conduct of fine arts lessons in uzbekistan. Eur. Multidiscip. J. Mod. Sci. 2022, 4, 122–132. [Google Scholar]
- Kim, J.Y. Metaverse content innovation ecosystem and conditions for sustainable growth. Sci. Technol. Policy Inst. 2021, 49, 28. [Google Scholar]
- Mollick, E.R. Containing Multitudes: The Many Impacts of Kickstarter Funding. 2016. Available online: https://ssrn.com/abstract=2808000 (accessed on 7 April 2022).
- Kiong, L.V. Metaverse Made Easy: A Beginner’s Guide to the Metaverse: Everything You Need to Know about Metaverse, NFT and GameFi; Independently Publisher: Chicago, IL, USA, 2022. [Google Scholar]
- Ryu, J.; Son, S.; Lee, J.; Park, Y.; Park, Y. Design of secure mutual authentication scheme for metaverse environments using blockchain. IEEE Access 2022, 10, 98944–98958. [Google Scholar] [CrossRef]
- Orji, J.; Hernandez, A.; Selema, B.; Orji, R. TidyHome: A Persuasive App for Supporting Victims and Survivors of Domestic Violence. In Proceedings of the International Conference on Human-Computer Interaction, Gothenburg, Sweden, 26 June–1 July 2022; Springer: Berlin/Heidelberg, Germany, 2022; pp. 400–415. [Google Scholar]
- Falchuk, B.; Loeb, S.; Neff, R. The social metaverse: Battle for privacy. IEEE Technol. Soc. Mag. 2018, 37, 52–61. [Google Scholar] [CrossRef]
- Mumtaz, S.; Huq, K.M.S.; Rodriguez, J. Direct mobile-to-mobile communication: Paradigm for 5G. IEEE Wirel. Commun. 2014, 21, 14–23. [Google Scholar] [CrossRef]
- Son, K.M.; Lee, B.R.; Shim, K.H.; Yang, K.H. Matrix world metaverse created by Web 2.0 and online games, ETRI CEO information. ETRI CEO Inf. 2006, 47, 1–26. [Google Scholar]
- Lastowka, G. User-generated content and virtual worlds. Vand. J. Ent. Tech. L. 2007, 10, 893. [Google Scholar]
- Ott, K. Virtual reality and simulations in adult and career education. In Proceedings of the Society for Information Technology & Teacher Education International Conference, Charleston, SC, USA, 2 March 2009; Association for the Advancement of Computing in Education AACE: Waynesville, NC USA, 2009; pp. 1515–1517. [Google Scholar]
- Schuemie, M.J.; Van Der Straaten, P.; Krijn, M.; Van Der, C.; Mast, A. Research on presence in virtual reality: A survey. Cyber Psychol. Behav. 2001, 4, 183–201. [Google Scholar] [CrossRef]
- Basu, T. The Metaverse has a Groping Problem Already. MIT Technology Review, 16 December 2021. [Google Scholar]
- Gupta, A.; Kumar, N.; Prabhat, P.; Gupta, R.; Tanwar, S.; Sharma, G.; Sharma, R. Combating fake news: Stakeholder interventions and potential solutions. IEEE Access 2022, 10, 78268–78289. [Google Scholar] [CrossRef]
- Ning, H.; Wang, H.; Lin, Y.; Wang, W.; Dhelim, S.; Farha, F.; Daneshmand, M. A survey on metaverse: The state-of-the-art, technologies, applications, and challenges. arXiv 2021, arXiv:2111.09673. [Google Scholar]
- Wang, Y.; Su, Z.; Zhang, N.; Liu, D.; Xing, R.; Luan, T.H.; Shen, X. A survey on metaverse: Fundamentals, security, and privacy. arXiv 2022, arXiv:2203.02662. [Google Scholar] [CrossRef]
- Di Pietro, R.; Cresci, S. Metaverse: Security and Privacy Issues. In Proceedings of the 2021 Third IEEE International Conference on Trust, Privacy and Security in Intelligent Systems and Applications (TPS-ISA), Atlanta, GA, USA, 13–15 December 2021; IEEE: Piscataway, NJ, USA, 2021; pp. 281–288. [Google Scholar]
- Zhao, R.; Zhang, Y.; Zhu, Y.; Lan, R.; Hua, Z. Metaverse: Security and Privacy Concerns. arXiv 2022, arXiv:2203.03854. [Google Scholar]
- Buck, L.; McDonnell, R. Security and privacy in the metaverse: The threat of the digital human. CHI EA 2022. [Google Scholar] [CrossRef]
- Vladimirov, I.; Nenova, M.; Nikolova, D.; Terneva, Z. Security and Privacy Protection Obstacles with 3D Reconstructed Models of People in Applications and the Metaverse: A Survey. In Proceedings of the 2022 57th International Scientific Conference on Information, Communication and Energy Systems and Technologies (ICEST), Ohrid, North Macedonia, 16–18 June 2022; IEEE: Piscataway, NJ, USA, 2022; pp. 1–4. [Google Scholar]
- Far, S.B.; Rad, A.I. Applying digital twins in metaverse: User interface, security and privacy challenges. J. Metaverse 2022, 2, 8–16. [Google Scholar]
- Dick, E. Public Policy for the Metaverse: Key Takeaways from the 2021 AR/VR Policy Conference; Information Technology and Innovation Foundation: Washington, DC, USA, 2021. [Google Scholar]
- Sultoni, K.B.; Azahra, J.M. Puspitasari The effect of cosmocracy in the metaverse world on national security (Arkycia Metaverse Case Study). Konfrontasi J. Kultural Èkon. Perubahan Sos. 2022, 9, 168–175. [Google Scholar] [CrossRef]
- Lim, W.Y.B.; Xiong, Z.; Niyato, D.; Cao, X.; Miao, C.; Sun, S.; Yang, Q. Realizing the metaverse with edge intelligence: A match made in heaven. arXiv 2022, arXiv:2201.01634. [Google Scholar] [CrossRef]
- Nguyen, C.T.; Hoang, D.T.; Nguyen, D.N.; Dutkiewicz, E. Metachain: A novel blockchain-based framework for metaverse applications. arXiv 2021, arXiv:2201.00759. [Google Scholar]
- Banciu, D.; Fodorean, D.; Cirnu, C.E. CYBER SECURITY AND HUMAN RIGHTS CONSIDERING THE METAVERSE. J. Freedom Conscienc. 2021, 9, 648–654. [Google Scholar]
- Chang, L.; Zhang, Z.; Li, P.; Xi, S.; Guo, W.; Shen, Y.; Xiong, Z.; Kang, J.; Niyato, D.; Qiao, X.; et al. 6G-enabled edge AI for metaverse: Challenges, methods, and future research directions. arXiv 2022, arXiv:2204.06192. [Google Scholar] [CrossRef]
- Zheng, J.M.; Chan, K.W.; Gibson, I. Virtual reality. IEEE Potentials 1998, 17, 20–23. [Google Scholar] [CrossRef]
- Breidenbach, L.; Cachin, C.; Chan, B.; Coventry, A.; Ellis, S.; Juels, A.; Koushanfar, F.; Miller, A.; Magauran, B.; Moroz, D.; et al. Chainlink 2.0: Next Steps in the Evolution of Decentralized Oracle Networks; Chainlink Labs: San Francisco, CA, USA, 2021. [Google Scholar]
- Jung, S.H.; Jeon, I.-O. A study on the components of the Metaverse ecosystem. J. Digit. Converg. 2022, 20, 163–174. [Google Scholar]
- Suh, S.-S. A study on metaverse development trends and prospects 2008. In Proceedings of the Korean HCI Society, Conference, Seoul, Republic of Korea, 10–12 December 2014; pp. 1450–1457. [Google Scholar]
- Han, S.; Kim, T. News big data analysis of ‘metaverse’ using topic modeling analysis. J. Digit. Contents Soc. 2021, 22, 1091–1099. [Google Scholar] [CrossRef]
- Dissanayake, V.D. A Review of Cyber Security Risks in an Augmented Reality World; Institute of Information Technology, University of Sri Lanka: Malabe, Sri Lanka, 2019. [Google Scholar]
| Research Topic | Main Features | References |
|---|---|---|
| Metaverse Concepts | Snow Crash (1992) proposed the idea of the metaverse, a web-based 3D virtual reality environment where diverse real-world activities are carried out as avatars. | Pınar, K. et al. [5] |
| Metaverse Definition | A virtual environment where users use avatars to participate in social, economic and cultural activities. | Son, K.M. et al. [25] |
| Metaverse Definition | A virtual reality setting where chances for social and economic advancement are provided, similar to actual or virtual worlds | Ryu and Ahn [21] |
| Metaverse Roadmap | Map of the Metaverse using 3D Web was announced and defined as a phenomenon where the real world and virtual world overlap, combine, converge and merge. | Lastowka, G. [26] |
| Metaverse Definition | A setting, technique and entity whereby virtual space and reality engage in active interaction | Suh, S.S. [27] |
| Metaverse Definition | A virtual space world with things, people and connections that live inside a fictitiously determined period. | Schuemie et al. [28] |
| 4th Industrial Revolution | Defined the idea as the convergence of technological revolutions, where the borders between the current digital, physical and biological worlds vanish | Kim, J.Y. [18] |
| Metaverse ecosystem | Stressed the need for metaverse ecosystem studies and characterized the metaverse as a multi-technology confluence | Seok, W.H. [16] |
| Industry | Use Cases/Application Domains |
|---|---|
| Sports/Gaming/Fitness | Virtual worlds, digital twins/avatars, immersive viewing and gaming |
| Arts and Entertainment | Virtual tours, 3D OTT and movies, NFTs |
| Decentralized Finance | Virtual trade, seamless B2B and B2C interfaces, real-time financial settlements using blockchain and Decentralized Oracle Networks (DONs) |
| Consumer Electronics | Device evolution, holographs, holograms and 3D projections, headsets, wearables and body implants |
| Communication and Collaboration | Immersive interactions, document management and sharing, business process management, virtual offices |
| Education, Training and Skilling | Immersive simulations, hands-on virtual training, 3D visualizations and remote learning |
| Computing | Personal cloud, GPU pervasiveness in mobile devices and wearables, edge computing and intelligence, AI models for 3D environments, fast 3D rendering and cybersecurity |
| E-Commerce, Fashion and Retail | Virtual stores, immersive product experience, product tryouts, creator-led products, services and economy |
| Industry 4.0 | Remote machinery and plant operations, remote troubleshooting and training |
| Healthcare | Remote robotic procedures, training, simulations, remote diagnosis and immersive tele-medicine |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2023 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).
Share and Cite
Gupta, A.; Khan, H.U.; Nazir, S.; Shafiq, M.; Shabaz, M. Metaverse Security: Issues, Challenges and a Viable ZTA Model. Electronics 2023, 12, 391. https://doi.org/10.3390/electronics12020391
Gupta A, Khan HU, Nazir S, Shafiq M, Shabaz M. Metaverse Security: Issues, Challenges and a Viable ZTA Model. Electronics. 2023; 12(2):391. https://doi.org/10.3390/electronics12020391
Chicago/Turabian StyleGupta, Ankur, Habib Ullah Khan, Shah Nazir, Muhammad Shafiq, and Mohammad Shabaz. 2023. "Metaverse Security: Issues, Challenges and a Viable ZTA Model" Electronics 12, no. 2: 391. https://doi.org/10.3390/electronics12020391
APA StyleGupta, A., Khan, H. U., Nazir, S., Shafiq, M., & Shabaz, M. (2023). Metaverse Security: Issues, Challenges and a Viable ZTA Model. Electronics, 12(2), 391. https://doi.org/10.3390/electronics12020391









