Machine-Learning-Based Vulnerability Detection and Classification in Internet of Things Device Security
Abstract
:1. Introduction
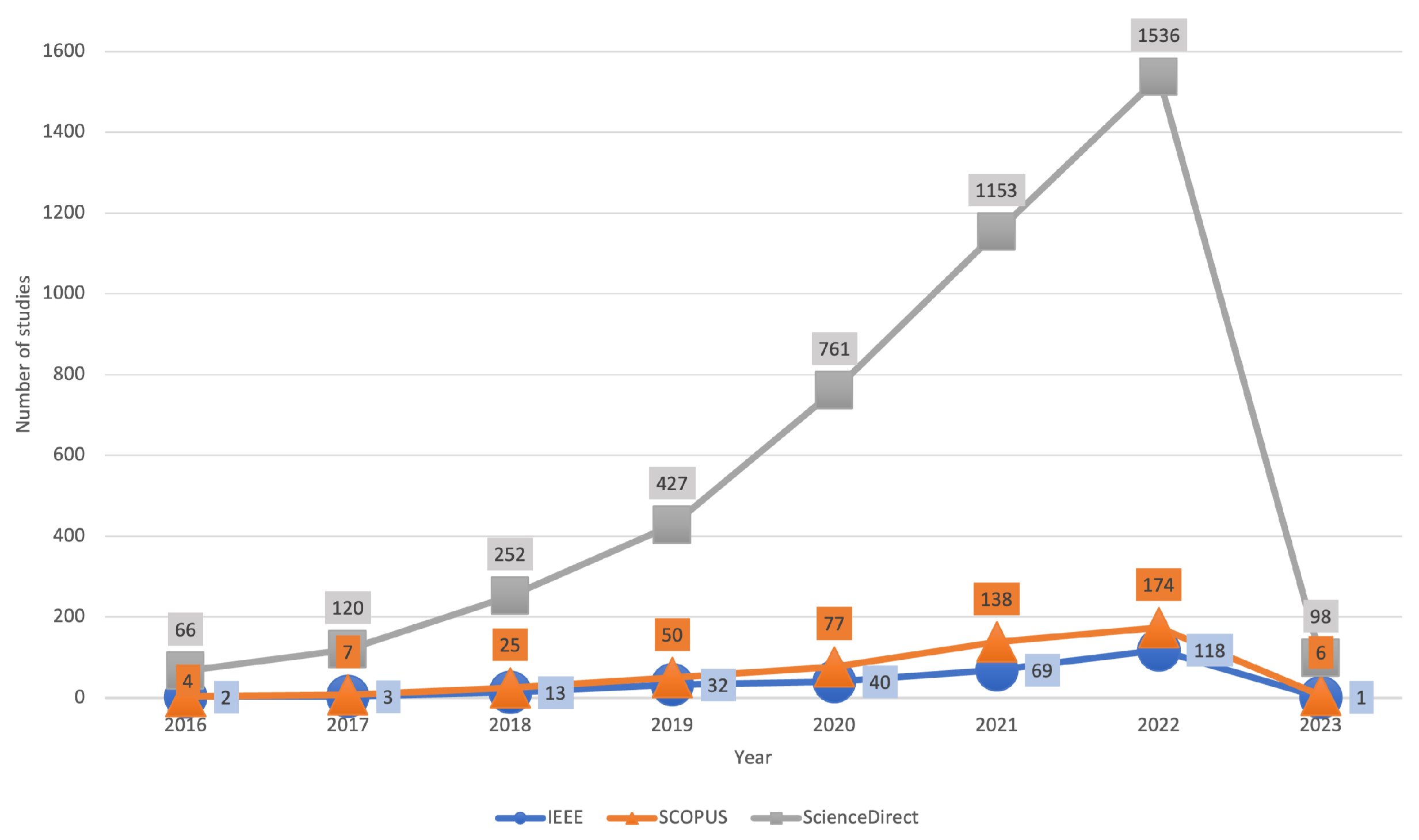
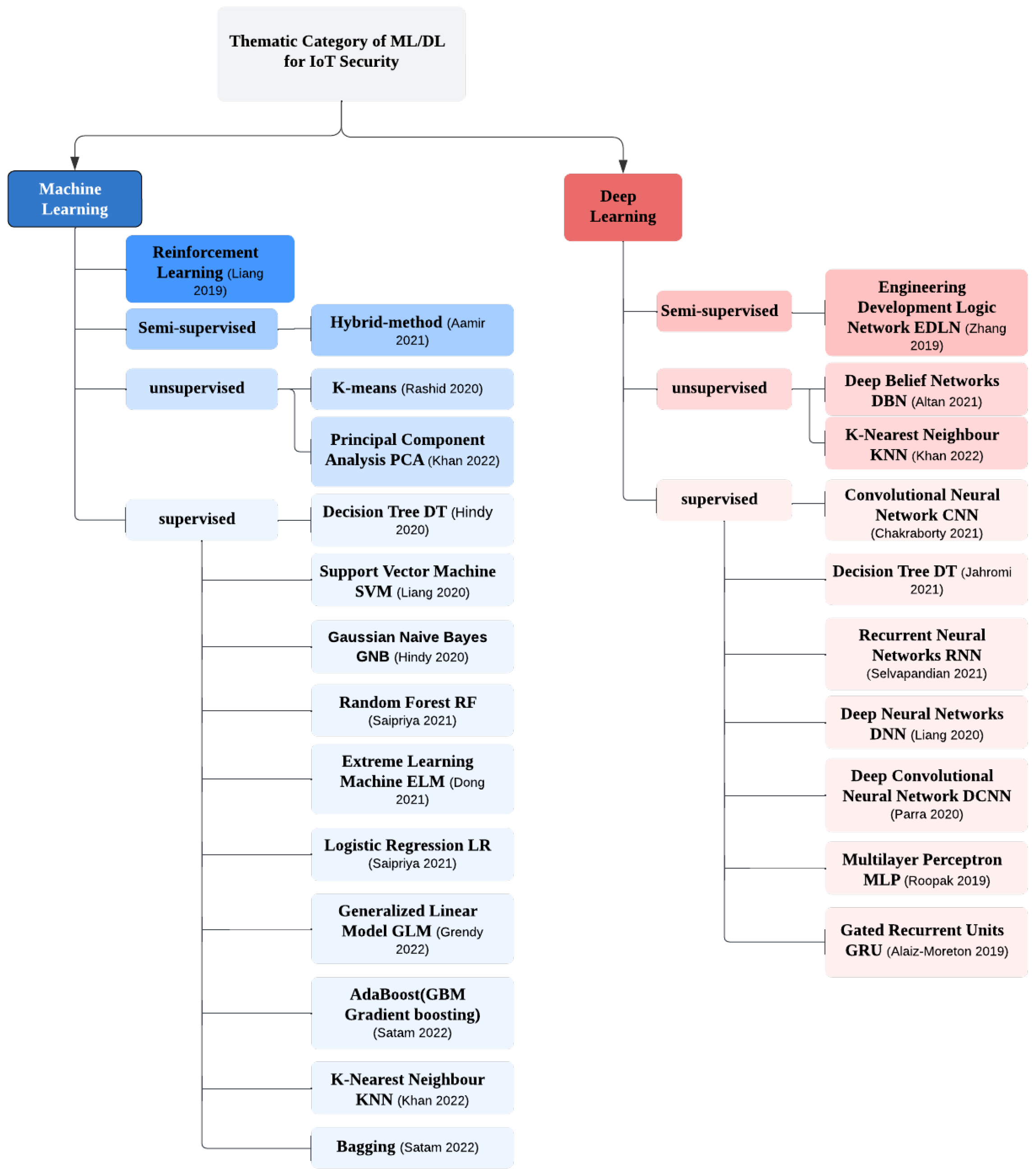
- A comprehensive survey has been undertaken to focus on recent research studies using ML and DL to detect and classify vulnerabilities and attacks in IoT ecosystems.
- This work investigates the common potential vulnerabilities at each layer in the IoT architecture and summarises ML workflow to detect vulnerabilities in IoT devices.
- A framework is proposed to detect and mitigate the vulnerabilities in IoT environments, and recent research trends on machine-learning-based vulnerability detection are summarized.
2. Related Works
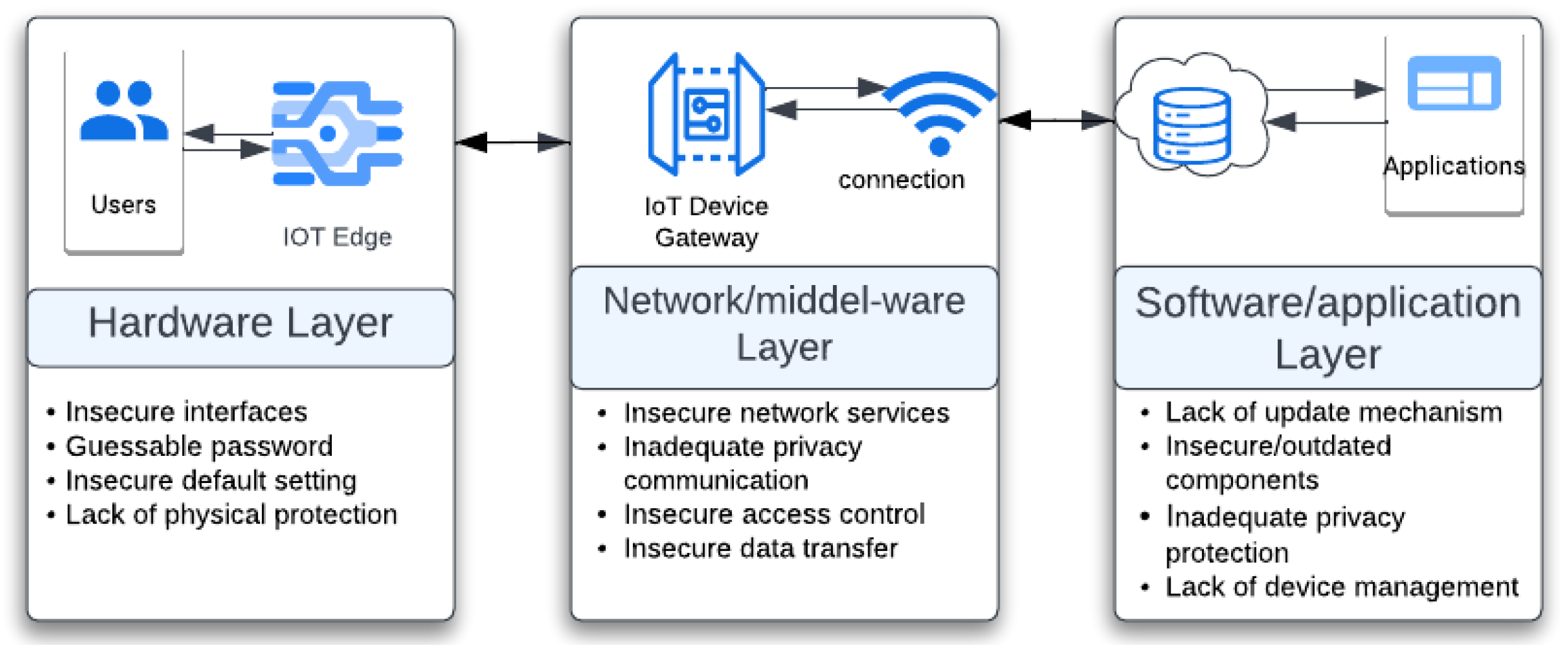
3. Vulnerabilities in IoT Environments
- CVE-2020-11896 could be triggered by sending multiple malformed IPv4 packets to a device supporting IPv4 tunneling to cause a Denial of Service (DoS) attack.
- CVE-2020-11897 can be prompted by sending multiple malformed IPv6 packets to a device that supports IPv6 to enable the execution of remote code.
- CVE-2020-11901 allows remote code execution by answering a single DNS request made from the device, so it allows an attacker to gain control of the device via DNS cache poisoning.
- CVE-2020-11898 could expose sensitive information when an unauthorized network attacker send a handling packet.
3.1. Vulnerabilities in the IoT Hardware Layer
- De-authentication attack on the smart plug. It points to making a DoS attack on the communication between the Wi-Fi access point and the targeted device and aims to disconnect the device from the network, even if the network password is unknown.
- TCP SYN flooding–DoS attack. This involves sending a lot of lawful SYN requests to the targeted IP address, and the victim’s system will never receive the final ACK message; as is known, the TCP protocol uses a three-way handshake mechanism. Therefore, the number of open connections will increase, causing the targeted machine to break down. It could be conducted by sending the SYN packets from one specific IP or from random IPs.
3.2. Vulnerabilities and Attacks in the IoT Network Layer/Middle-Layer
3.3. Vulnerabilities and Attacks in the IoT Application Layer
4. Vulnerability Analysis Using ML and DL
4.1. Machine Learning Techniques in Detecting Attacks in the IoT Hardware Layer
4.2. Machine Learning and Deep Learning in Detecting Attacks in the Middle Layer
4.3. Machine Learning and Deep Learning in Detecting Attacks in the Software Application Layer
4.4. Machine Learning and Deep Learning in Detecting Threats and Vulnerabilities across All Layers
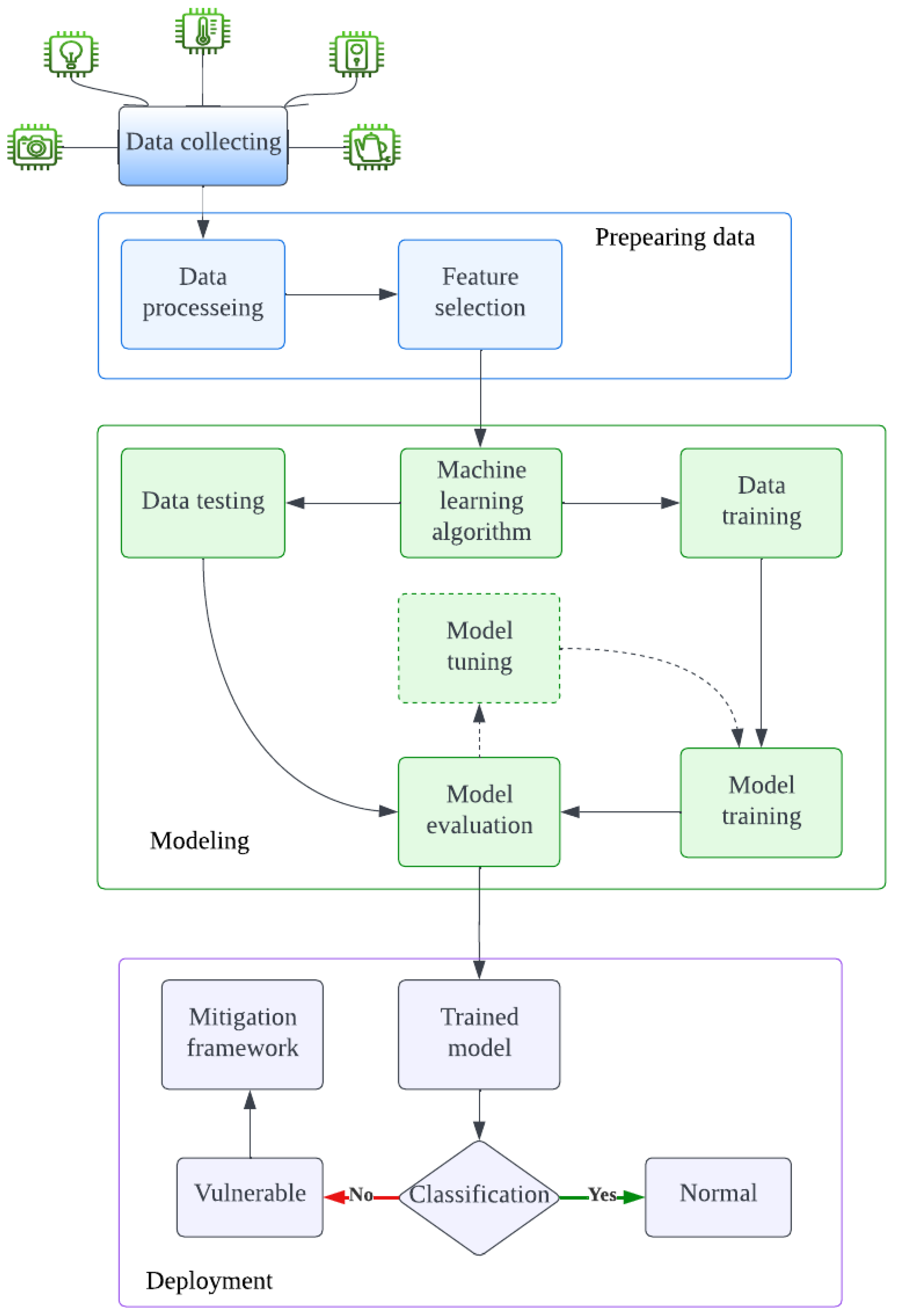
5. Vulnerability Detection and Classification
5.1. Procedure
- -
- Data collection: collected data from real-life scenarios from IoT networks which connect to other devices such as mobiles and computers; it consists of normal use traffic and suspected traffic trying to conduct some attacks. The data type could be network traffic, logs, or other related data.
- -
- Data preparation: data cleaning or data preparation acts as a critical step in ML methods, especially when the data is collected from heterogeneous sources. It aims to identify errors and correct them by using different types of ML algorithms. In some complex cases, the data need to be cleaned and transformed. This stage could affect the result of the whole procedure. The quality of data can be measured in terms of its accuracy, balance, and completeness [93]. Any errors in this stage could result in enormous mistakes in the predictive models. The problems with the data could be simple, such as empty columns and duplicate rows or, in some cases, different types of data. In this stage, there are many sub-steps that should be followed, such as cleaning data, which focuses on identifying and correcting the faults in the dataset. Then, it is necessary to select features which aim to find the most important inputs. Next, transform data, which aims to change the size or allocate the variables. Then, the features that work to use the existing data are engineered to gain new variables. Finally, reduce the dimensional, which aims to generate the compacted predictions of the data [94].
- -
- Feature extraction: It aims to identify the most useful features in the data to feed the model, which could be conducted using a DL technique and creating some useful features which help the classifying model to make a decision. In some cases, in a DL model, this step does not need to be performed manually due to the DL model’s ability to learn to extract them during the training phase, which is the biggest advantage of DL [95].
- -
- Model training: A model can be trained to learn (define) the best values for all the weights and the bias from trained data. It could differ depending on the type of algorithms; for example, in supervised learning, an ML algorithm builds a model by investigating many examples and attempting to find a good model which reduces cost; this method is called practical risk minimization [94]. The model is usually trained in part of the main dataset by splitting them into training data and excused (tested) data which will be training them in the predictive model.
- -
- Model evaluation: This aims to evaluate the trained model using various metrics with predicted models to assess the quality of the ML model, such as calculating the accuracy, precision, recall, and F1 in these algorithms to ensure the effectiveness [96].
- -
- Tuning/hyperparameterizing the model: This is an optional step for some algorithms, such as DT and SVM. The tuning of hyperparameters is the process of selecting the best hyperparameters for an algorithm with the aim of increasing the effectiveness of its task [97].
- -
- Detection: This stage aims to detect vulnerabilities, attacks, or threats in the IoT ecosystems; it uses the tested data from the main dataset. The result from this step differs depending on the dataset and algorithms used; it could be supervised, unsupervised or semi-supervised. In addition, this step may utilize another dataset to approve the performance of the detection model. The output from this step is forwarded to the classification step to determine the type of detected data.
- -
- Classification: This is the final stage which is deployed in order to classify and analyze the upcoming data to determine whether or not they are normal using various types of ML algorithms and classifiers. In some cases, these data are categorized into numerous types of non-normal data, which is called multi-classification. If the data is non-normal, it will be passed to the mitigation framework.
5.2. Research Challenges
- Incomplete data can bias the detection result of machine learning models or compromise the accuracy of the model. Missing certain details may make it difficult for a classifier to learn representative vulnerability features.
- Most existing works focused on detecting attacks as soon as they start to be implemented; actually, a previously undiscovered vulnerability can be triggered by specific events or conditions, which makes it challenging to predict.
- Resource issues in IoT devices, which are memory and time issues, play an important role in implementing ML and DL models in IoT systems. In addition, implementing these models usually occurs offline, and applying these techniques in real life remains an issue.
- Another challenge is found that the IoT ecosystems work in different ways. For example, some of them work with Bluetooth and others work with sensors which results in different types of data, which means no one method is generally better than others. Therefore, standardization of the IoT ecosystems is important to make improvements in IoT security easier and more effective. In addition, secure by design could also be beneficial for IoT device security.
- IoT devices deal with various types of data with different scales. In addition, all previous research studies were implemented with different datasets. Some of them are collected from wired networks and others from wireless networks. As a result, the accuracy of implementing ML and DL methods is different depending on the type of the datasets and their features.
6. Vulnerability Mitigation
6.1. Vulnerability Mitigation Strategies in IoT
- Avoid: Avoid mitigation strategies allow a vulnerable node to be protected permanently by patching its weaknesses or using a secure protocol and encryption.
- Reduce: Reduce mitigation strategies stop the spread of weaknesses or stop these vulnerabilities from being used as a privilege to deep with more attacks. Due to the limitation of processing power and remote location in IoT environments, reduction strategies are considered safe for IoT devices.
- Manage: Manage strategies involve accepting the risk and implementing another solution for the device, such as setting the access control or allowing trusted communication within the system.
- Mitigate: Risk mitigate involves the mitigation of responsibility to a third party who is willing to take on the risk. In order to minimize the organization’s exposure to that risk, this procedure is undertaken. External entities that specialize in certain areas of risk management can be delegated certain responsibilities and aspects of risk management.
6.2. Vulnerability Mitigation Frameworks
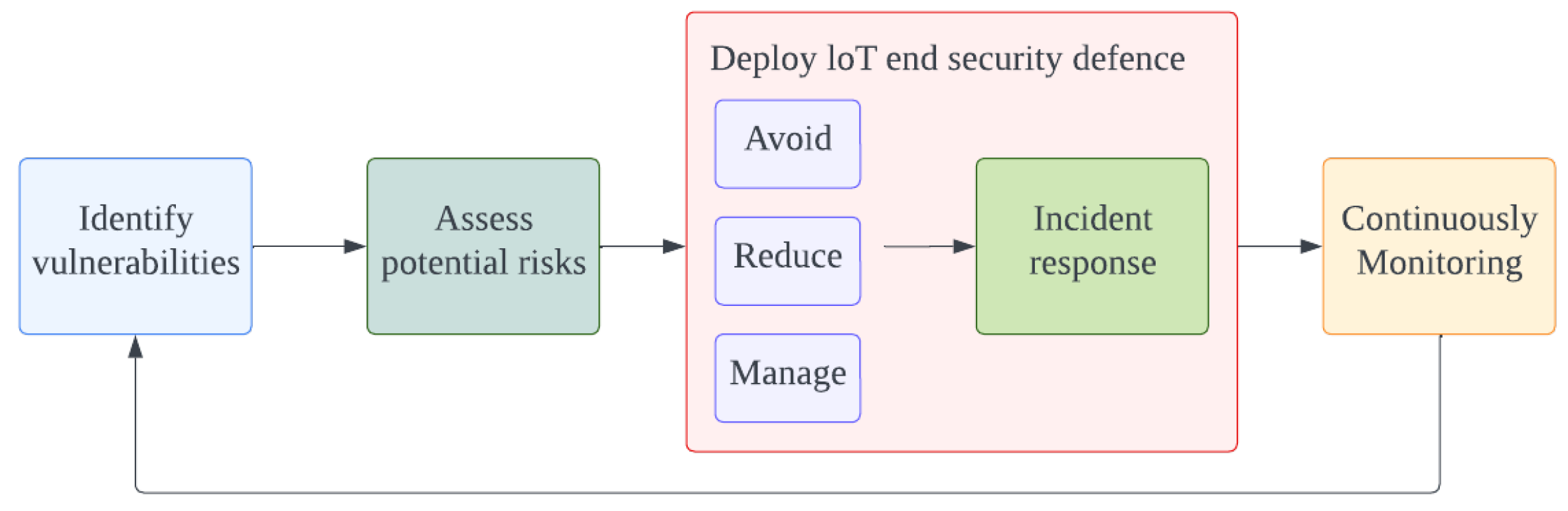
6.3. The Proposed Vulnerability Mitigation Framework
- (1)
- Identify vulnerabilities. Scanning the network to identify the vulnerabilities in the whole IoT ecosystem using the developed ML and DL-based model to detect the vulnerable points such as the proposed model in [90] based on LGBM algorithm which produced an excellent detection model. Then, using an ML-based model to classify these vulnerabilities to determine the threats level and layer(place) of them such as feed-forward neural network (FNN), which is a combined model used for classification and achieves great classification results [109].
- (2)
- Assess potential risks. Assess the risk level of the detected vulnerabilities to choose the mitigation strategies depending on the risk rate and move the output to the next stage. The risk rate could be predicted by a training-based learning model depending on the previous dataset attacks, such as IoT23.
- (3)
- Deploy the security defense. Deploy the defense by determining the type of incident response, such as performing security controls—access control, procedure controls, technical controls, compliance controls, etc.
- If the mitigation strategy is ’Avoid’, implement the security defense and the incident response immediately, such as isolating the device and then patching the system or implementing encryption protocol.
- If the strategy is ’Reduce’, reduce the risk by performing the security control, such as updating the system and re-configuring the security control.
- If the strategy is ’Manage’, accept the incident and then make updates for the security control and security configuration.
- (4)
- Continuous Monitoring. Monitoring the traffic in the whole system by using certain techniques and procedures to prevent security issues and reduce the risk in IoT environments.
6.4. Mitigating Exploitation of Vulnerability in IoT
- Memory management vulnerability. Managing the memory and controlling the followed traffic and allocation present the critical resources in the IoT environment, so any vulnerabilities in memory management could significantly affect the entire system. These vulnerabilities could be exploited to evade security controls in order to inject malicious code and smash an IoT system.As exploiting these vulnerabilities could cause critical potential risks for the IoT ecosystem, the potential threats must be avoided by immediately patching and updating the system. However, patching IoT devices may be complex, so if the device cannot be patched, it could be worthwhile applying a different strategy, such as reducing the exploitation impacts by keeping vulnerable devices off of the internet in order to reduce attack sides and then monitor the system to reveal any behavioral signs of compromise. Moreover, it is necessary to ensure that critical assets are protected by network segmentation. Another study that proposed a framework to detect memory corruption, named FIoT, which works using code execution and fuzzing, resulted in defining 35 IoT devices that have a zero-day vulnerability [114,115].
- API vulnerability. The Application Programming Interface (API) is a set of functions and procedures which are used to build and integrate by other software applications usually based on web service applications, with roles for the important platform that collects input from users and connects with the backend services. The security of IoT applications is compromised by several security vulnerabilities, including weak or hardcoded passwords, such as using guessable passwords or using the default manufacturing passwords. Therefore, the most important procedure in IoT security is confirming that only the authorized users can communicate with APIs [116,117].Mitigating the exploitation of API vulnerability could be resolved by using many procedures that could be implemented to ensure the security of APIs. Mitigating the insecure backend API requires strong authentication and authorization methods. ML and DL could be used to detect and determine potential threats in API along with a strong encryption infrastructure and access controls such as using a robust primary key on the IoT infrastructure [118].
- Side channel vulnerability. This is a type of security attack which targets the indirect effects of a system’s hardware or software rather than directly targeting the code to gather sensitive data such as cryptography keys. It could be exploited by computing or investigating several parameters from a chip or a system, such as execution time and electromagnetic radiation, which are commonly used in IoT environments. It can be categorized into three types: memory cache attacks, which use a shared physical system to monitor the cache accesses.; timing attacks aim to establish patterns by observing the computing time; and power-monitoring attacks aim to track the hardware’s power consumption during computation [119,120].
7. Research Trends and Directions
- Making IoT systems more intelligent to detect their vulnerabilities by using ML and DL techniques could be more efficient to enhance security. Many studies focused on detecting attacks and malicious data, but detecting the vulnerabilities would be more efficient. Making the IoT device detect known and unknown vulnerabilities in their environment and sending alerts to the consumer would improve the whole IoT ecosystem’s security.
- Time consumption and memory capacity in IoT devices pose the biggest challenge as has been noticed from the previous sections; most of the proposed solutions take time to process these huge data starting with analysis the incoming traffic then decide whether a malicious or not. However, they could be addressed by utilizing compression ML and DL models and reducing the use of cache memory by sharing the data with other devices such as external tools or resources, as well as avoiding unnecessary computations.
- Standardization of the IoT structure, infrastructure, and scale of the data used is a significant issue regarding developing techniques for improving security in IoT environments due to the diversity of the IoT and its data. However, it could be addressed by using algorithms in IoT devices to transform and standardize the data before processing them. However, it leads to the challenges associated with IoT ecosystems which are memory and time consumption.
- Creating cyber resilience in IoT involves not only preventing cyber attacks, but also managing adaptability, recovery, and preserving critical functions even in the face of difficulty. Although the best efforts are made, breaches may occur, so the key is to ensure that the IoT ecosystem can recover and remain to deliver essential functions while saving its critical assets.
8. Conclusions
Author Contributions
Funding
Conflicts of Interest
References
- Li, S.; Zhao, S.; Min, G.; Qi, L.; Liu, G. Lightweight privacy-preserving scheme using homomorphic encryption in industrial Internet of Things. IEEE Internet Things J. 2021, 9, 14542–14550. [Google Scholar] [CrossRef]
- Zhao, S.; Li, S.; Qi, L.; Xu, L.D. Computational Intelligence Enabled Cybersecurity for the Internet of Things. IEEE Trans. Emerg. Top. Comput. Intell. 2020, 4, 666–674. [Google Scholar] [CrossRef]
- Arshad, J.; Azad, M.A.; Amad, R.; Salah, K.; Alazab, M.; Iqbal, R. A review of performance, energy and privacy of intrusion detection systems for IoT. Electronics 2020, 9, 629. [Google Scholar] [CrossRef]
- Mercer, D. Smart Home Will Drive Internet of Things To 50 Billion Devices. Available online: https://www.strategyanalytics.com/strategy-analytics/news/strategy-analytics-press-releases/strategy-analytics-press-release/2017/10/26/smart-home-will-drive-Internet-of-things-to-50-billion-devices-says-strategy-analytics (accessed on 1 January 2023).
- Ashton, K. Making sense of IoT. In How the Internet of Things Became Humanity’s Nervous System; Hewlett Packard Enterprise: Spring, TX, USA, 2017. [Google Scholar]
- Jabraeil Jamali, M.A.; Bahrami, B.; Heidari, A.; Allahverdizadeh, P.; Norouzi, F. IoT architecture. In Towards the Internet of Things; Springer: Berlin/Heidelberg, Germany, 2020; pp. 9–31. [Google Scholar]
- Honar Pajooh, H.; Rashid, M.; Alam, F.; Demidenko, S. Multi-layer blockchain-based security architecture for internet of things. Sensors 2021, 21, 772. [Google Scholar] [CrossRef] [PubMed]
- Rana, M.; Shafiq, A.; Altaf, I.; Alazab, M.; Mahmood, K.; Chaudhry, S.A.; Zikria, Y.B. A secure and lightweight authentication scheme for next generation IoT infrastructure. Comput. Commun. 2021, 165, 85–96. [Google Scholar] [CrossRef]
- Azrour, M.; Mabrouki, J.; Guezzaz, A.; Kanwal, A. Internet of things security: Challenges and key issues. Secur. Commun. Netw. 2021, 2021, 5533843. [Google Scholar] [CrossRef]
- Wang, C.; Dong, S.; Zhao, X.; Papanastasiou, G.; Zhang, H.; Yang, G. SaliencyGAN: Deep learning semisupervised salient object detection in the fog of IoT. IEEE Trans. Ind. Inform. 2019, 16, 2667–2676. [Google Scholar] [CrossRef]
- Zhou, Y.; Han, M.; Liu, L.; He, J.S.; Wang, Y. Deep learning approach for cyberattack detection. In Proceedings of the IEEE INFOCOM 2018-IEEE Conference on Computer Communications Workshops (INFOCOM WKSHPS), Honolulu, HI, USA, 15–19 April 2018; IEEE: New York, NY, USA, 2018; pp. 262–267. [Google Scholar]
- Neshenko, N.; Bou-Harb, E.; Crichigno, J.; Kaddoum, G.; Ghani, N. Demystifying IoT security: An exhaustive survey on IoT vulnerabilities and a first empirical look on Internet-scale IoT exploitations. IEEE Commun. Surv. Tutor. 2019, 21, 2702–2733. [Google Scholar] [CrossRef]
- Xie, W.; Jiang, Y.; Tang, Y.; Ding, N.; Gao, Y. Vulnerability detection in iot firmware: A survey. In Proceedings of the 2017 IEEE 23rd International Conference on Parallel and dIstributed Systems (ICPADS), Shenzhen, China, 15–17 December 2017; IEEE: New York, NY, USA, 2017; pp. 769–772. [Google Scholar]
- Feng, X.; Zhu, X.; Han, Q.L.; Zhou, W.; Wen, S.; Xiang, Y. Detecting vulnerability on IoT device firmware: A survey. IEEE/CAA J. Autom. Sin. 2022, 10, 25–41. [Google Scholar] [CrossRef]
- Meneghello, F.; Calore, M.; Zucchetto, D.; Polese, M.; Zanella, A. IoT: Internet of threats? A survey of practical security vulnerabilities in real IoT devices. IEEE Internet Things J. 2019, 6, 8182–8201. [Google Scholar] [CrossRef]
- Yu, M.; Zhuge, J.; Cao, M.; Shi, Z.; Jiang, L. A survey of security vulnerability analysis, discovery, detection, and mitigation on IoT devices. Future Internet 2020, 12, 27. [Google Scholar] [CrossRef]
- Ahanger, T.A.; Aljumah, A.; Atiquzzaman, M. State-of-the-art survey of artificial intelligent techniques for IoT security. Comput. Netw. 2022, 206, 108771. [Google Scholar] [CrossRef]
- OWASP. Internet of Things; OWASP Foundation: Bel Air, MA, USA, 2022. [Google Scholar]
- Qu, J. Research on Password Detection Technology of IoT Equipment Based on Wide Area Network. ICT Express 2021, 8, 213–219. [Google Scholar] [CrossRef]
- Verma, R.S.; Chandavarkar, B.R.; Nazareth, P. Mitigation of hard-coded credentials related attacks using QR code and secured web service for IoT. In Proceedings of the 2019 10th International Conference on Computing, Communication and Networking Technologies (ICCCNT), Kanpur, India, 6–8 July 2019; IEEE: New York, NY, USA, 2019; pp. 1–5. [Google Scholar]
- Sun, H.M.; Chen, Y.H.; Lin, Y.H. oPass: A User Authentication Protocol Resistant to Password Stealing and Password Reuse Attacks. IEEE Trans. Inf. Forensics Secur. 2012, 7, 651–663. [Google Scholar] [CrossRef]
- Mouris, D.; Tsoutsos, N.G. Zilch: A Framework for Deploying Transparent Zero-Knowledge Proofs. IEEE Trans. Inf. Forensics Secur. 2021, 16, 3269–3284. [Google Scholar] [CrossRef]
- Erendor, M.E.; Yildirim, M. Cybersecurity Awareness in Online Education: A Case Study Analysis. IEEE Access 2022, 10, 52319–52335. [Google Scholar] [CrossRef]
- Alladi, T.; Chamola, V.; Sikdar, B.; Choo, K.K.R. Consumer IoT: Security vulnerability case studies and solutions. IEEE Consum. Electron. Mag. 2020, 9, 17–25. [Google Scholar] [CrossRef]
- Chatterjee, D.; Boyapally, H.; Patranabis, S.; Chatterjee, U.; Hazra, A.; Mukhopadhyay, D. Physically Related Functions: Exploiting Related Inputs of PUFs for Authenticated-Key Exchange. IEEE Trans. Inf. Forensics Secur. 2022, 17, 3847–3862. [Google Scholar] [CrossRef]
- Meng, Q.; Nian, X.; Chen, Y.; Chen, Z. Attack-Resilient Distributed Nash Equilibrium Seeking of Uncertain Multiagent Systems Over Unreliable Communication Networks. In IEEE Transactions on Neural Networks and Learning Systems; IEEE: New York, NY, USA, 2022; pp. 1–15. [Google Scholar] [CrossRef]
- Nadir, I.; Mahmood, H.; Asadullah, G. A taxonomy of IoT firmware security and principal firmware analysis techniques. Int. J. Crit. Infrastruct. Prot. 2022, 38, 100552. [Google Scholar] [CrossRef]
- Morgner, P.; Mai, C.; Koschate-Fischer, N.; Freiling, F.; Benenson, Z. Security Update Labels: Establishing Economic Incentives for Security Patching of IoT Consumer Products. In Proceedings of the 2020 IEEE Symposium on Security and Privacy (SP), San Francisco, CA, USA, 18–21 May 2020; pp. 429–446. [Google Scholar] [CrossRef]
- Li, S. Zero trust based internet of things. EAI Endorsed Trans. Internet Things 2019, 5, e1. [Google Scholar]
- Arthi, R.; Krishnaveni, S. Design and Development of IOT Testbed with DDoS Attack for Cyber Security Research. In Proceedings of the 2021 3rd International Conference on Signal Processing and Communication (ICPSC), Coimbatore, India, 13–14 May 2021; pp. 586–590. [Google Scholar] [CrossRef]
- Cao, H.; Brown, M.; Chen, L.; Smith, R.; Wachowicz, M. Lessons Learned from Integrating Batch and Stream Processing using IoT Data. In Proceedings of the 2019 Sixth International Conference on Internet of Things: Systems, Management and Security (IOTSMS), Granada, Spain, 22–25 October 2019; pp. 32–34. [Google Scholar] [CrossRef]
- Alrawi, O. Security Evaluation of Home-Based IoT Deployments. In Proceedings of the 2019 IEEE Symposium on Security and Privacy (SP), San Francisco, CA, USA, 19–23 May 2019. [Google Scholar]
- Thapaliya, B.; Mursi, K.T.; Zhuang, Y. Machine Learning-based Vulnerability Study of Interpose PUFs as Security Primitives for IoT Networks. In Proceedings of the 2021 IEEE International Conference on Networking, Architecture and Storage (NAS), Riverside, CA, USA, 24–26 October 2021; pp. 1–7. [Google Scholar] [CrossRef]
- Islam, M.J.; Rahman, A.; Kabir, S.; Karim, M.R.; Acharjee, U.K.; Nasir, M.K.; Band, S.S.; Sookhak, M.; Wu, S. Blockchain-SDN-Based Energy-Aware and Distributed Secure Architecture for IoT in Smart Cities. IEEE Internet Things J. 2022, 9, 3850–3864. [Google Scholar] [CrossRef]
- Chandavarkar, B. Hardcoded credentials and insecure data transfer in IoT: National and international status. In Proceedings of the 2020 11th International Conference on Computing, Communication and Networking Technologies (ICCCNT), Kharagpur, India, 1–3 July 2020; IEEE: New York, NY, USA, 2020; pp. 1–7. [Google Scholar]
- Shin, S.; Seto, Y. Development of iot security exercise contents for cyber security exercise system. In Proceedings of the 2020 13th International Conference on Human System Interaction (HSI), Tokyo, Japan, 6–8 June 2020; IEEE: New York, NY, USA, 2020; pp. 1–6. [Google Scholar]
- Singh, S.K.; Park, J.H. TaLWaR: Blockchain-Based Trust Management Scheme for Smart Enterprises With Augmented Intelligence. IEEE Trans. Ind. Inform. 2023, 19, 626–634. [Google Scholar] [CrossRef]
- Kotenko, I.; Doynikova, E.; Fedorchenko, A.; Desnitsky, V. Automation of Asset Inventory for Cyber Security: Investigation of Event Correlation-Based Technique. Electronics 2022, 11, 2368. [Google Scholar] [CrossRef]
- Asef, P.; Taheri, R.; Shojafar, M.; Mporas, I.; Tafazolli, R. SIEMS: A Secure Intelligent Energy Management System for Industrial IoT Applications. IEEE Trans. Ind. Inform. 2023, 19, 1039–1050. [Google Scholar] [CrossRef]
- Adil, M.; Jan, M.A.; Liu, Y.; Abulkasim, H.; Farouk, A.; Song, H. A Systematic Survey: Security Threats to UAV-Aided IoT Applications, Taxonomy, Current Challenges and Requirements With Future Research Directions. In IEEE Transactions on Intelligent Transportation Systems; IEEE: New York, NY, USA, 2022; pp. 1–19. [Google Scholar] [CrossRef]
- Choudhary, Y.; Umamaheswari, B.; Kumawat, V. A Study of Threats, Vulnerabilities and Countermeasures: An IoT Perspective. Humanities 2021, 8, 39–45. [Google Scholar] [CrossRef]
- Pal, R.; Huang, Z.; Yin, X.; Lototsky, S.; De, S.; Tarkoma, S.; Liu, M.; Crowcroft, J.; Sastry, N. Aggregate Cyber-Risk Management in the IoT Age: Cautionary Statistics for (Re)Insurers and Likes. IEEE Internet Things J. 2021, 8, 7360–7371. [Google Scholar] [CrossRef]
- Wang, H.; Barriga, L.; Vahidi, A.; Raza, S. Machine Learning for Security at the IoT Edge—A Feasibility Study. In Proceedings of the 2019 IEEE 16th International Conference on Mobile Ad Hoc and Sensor Systems Workshops (MASSW), Monterey, CA, USA, 4–7 November 2019; pp. 7–12. [Google Scholar] [CrossRef]
- Tao, M.; Ota, K.; Dong, M. Locating compromised data sources in IoT-enabled smart cities: A great-alternative-region-based approach. IEEE Trans. Ind. Inform. 2018, 14, 2579–2587. [Google Scholar] [CrossRef]
- Chen, L.; Xue, L.; Huang, H.; Wang, W.; Cao, M.; Xiao, F. Double Rainbows: A Promising Distributed Data Sharing in Augmented Intelligence of Things. IEEE Trans. Ind. Inform. 2023, 19, 653–661. [Google Scholar] [CrossRef]
- Ryon, L.; Martintoni, D. Field Loadable Software Confidentiality Protection. In Proceedings of the 2022 IEEE/AIAA 41st Digital Avionics Systems Conference (DASC), Portsmouth, VA, USA, 18–22 September 2022; pp. 1–6. [Google Scholar] [CrossRef]
- Tong, F.; Chen, X.; Wang, K.; Zhang, Y. CCAP: A Complete Cross-Domain Authentication Based on Blockchain for Internet of Things. IEEE Trans. Inf. Forensics Secur. 2022, 17, 3789–3800. [Google Scholar] [CrossRef]
- Dofe, J. Thermal Side-channel Leakage Protection in Monolithic Three Dimensional Integrated Circuits. In Proceedings of the 2022 IEEE 35th International System-on-Chip Conference (SOCC), Belfast, UK, 5–8 September 2022; pp. 1–2. [Google Scholar] [CrossRef]
- Gourisetti, S.N.G.; Mylrea, M.; Patangia, H. Cybersecurity Vulnerability Mitigation Framework Through Empirical Paradigm (CyFEr): Prioritized Gap Analysis. IEEE Syst. J. 2020, 14, 1897–1908. [Google Scholar] [CrossRef]
- Kol, M. JSOF Research Lab. 2020. Available online: https://www.jsof-tech.com/wp-content/uploads/2020/08/Ripple20CVE-2020-11901-August20.pdf (accessed on 3 February 2023).
- Dong, C.; He, G.; Liu, X.; Yang, Y.; Guo, W. A multi-layer hardware trojan protection framework for IoT chips. IEEE Access 2019, 7, 23628–23639. [Google Scholar] [CrossRef]
- Adina, P.; Shahzad, M. A Distributed & Lightweight Framework to Secure IoT Networks Against Network Layer Attacks. In Proceedings of the 2022 International Conference on Computer Communications and Networks (ICCCN), Honolulu, HI, USA, 25–28 July 2022; IEEE: New York, NY, USA, 2022; pp. 1–9. [Google Scholar]
- Nebbione, G.; Calzarossa, M.C. Security of IoT application layer protocols: Challenges and findings. Future Internet 2020, 12, 55. [Google Scholar] [CrossRef]
- Mocrii, D.; Chen, Y.; Musilek, P. IoT-based smart homes: A review of system architecture, software, communications, privacy and security. Internet Things 2018, 1, 81–98. [Google Scholar] [CrossRef]
- Burhan, M.; Rehman, R.A.; Khan, B.; Kim, B.S. IoT elements, layered architectures and security issues: A comprehensive survey. Sensors 2018, 18, 2796. [Google Scholar] [CrossRef]
- Meng, H.; Thing, V.L.; Cheng, Y.; Dai, Z.; Zhang, L. A survey of Android exploits in the wild. Comput. Secur. 2018, 76, 71–91. [Google Scholar] [CrossRef]
- Hosmer, C. IoT vulnerabilities. In Defending IoT Infrastructures with the Raspberry Pi; Springer: Berlin/Heidelberg, Germany, 2018; pp. 1–15. [Google Scholar]
- Chakraborty, S.; Krishna, R.; Ding, Y.; Ray, B. Deep learning based vulnerability detection: Are we there yet. IEEE Trans. Softw. Eng. 2021, 48, 9. [Google Scholar] [CrossRef]
- Selvapandian, D.; Santhosh, R. Deep learning approach for intrusion detection in IoT-multi cloud environment. Autom. Softw. Eng. 2021, 28, 19. [Google Scholar] [CrossRef]
- Liang, C.; Shanmugam, B.; Azam, S.; Jonkman, M.; De Boer, F.; Narayansamy, G. Intrusion detection system for Internet of Things based on a machine learning approach. In Proceedings of the 2019 International Conference on Vision Towards Emerging Trends in Communication and Networking (ViTECoN), Vellore, India, 30–31 March 2019; IEEE: New York, NY, USA, 2019; pp. 1–6. [Google Scholar]
- Liang, C.; Shanmugam, B.; Azam, S.; Karim, A.; Islam, A.; Zamani, M.; Kavianpour, S.; Idris, N.B. Intrusion detection system for the internet of things based on blockchain and multi-agent systems. Electronics 2020, 9, 1120. [Google Scholar] [CrossRef]
- Hindy, H.; Bayne, E.; Bures, M.; Atkinson, R.; Tachtatzis, C.; Bellekens, X. Machine learning based IoT intrusion detection system: An MQTT case study (MQTT-IoT-IDS2020 dataset). In Selected Papers from the 12th International Networking Conference, 16 November 2020; Springer: Berlin/Heidelberg, Germany, 2020; pp. 73–84. [Google Scholar]
- Alaiz-Moreton, H.; Aveleira-Mata, J.; Ondicol-Garcia, J.; Muñoz-Castañeda, A.L.; García, I.; Benavides, C. Multiclass classification procedure for detecting attacks on MQTT-IoT protocol. Complexity 2019, 2019, 6516253. [Google Scholar] [CrossRef]
- Saipriya, T.; Anand, M. To Secure IoT sensor nodes through Fog computing. In Proceedings of the 2021 Second International Conference on Electronics and Sustainable Communication Systems (ICESC), Coimbatore, India, 4–6 August 2021; IEEE: New York, NY, USA, 2021; pp. 836–844. [Google Scholar]
- Grendy, E.; Aliandy, R.J. Denial of Service Classification on Message Queueing Telemetry Transport Protocol at Indonesia Oil Services Company. J. Theor. Appl. Inf. Technol. 2022, 100, 2289–2299. [Google Scholar]
- Satam, S.; Satam, P.; Pacheco, J.; Hariri, S. Security framework for smart cyber infrastructure. Clust. Comput. 2022, 25, 2767–2778. [Google Scholar] [CrossRef]
- Roopak, M.; Tian, G.Y.; Chambers, J. Deep learning models for cyber security in IoT networks. In Proceedings of the 2019 IEEE 9th Annual Computing and Communication Workshop and Conference (CCWC), Las Vegas, NV, USA, 7–9 January 2019; IEEE: New York, NY, USA, 2019; pp. 452–457. [Google Scholar]
- Dong, X.; Dong, C.; Chen, Z.; Cheng, Y.; Chen, B. BotDetector: An extreme learning machine-based Internet of Things botnet detection model. Trans. Emerg. Telecommun. Technol. 2021, 32, e3999. [Google Scholar] [CrossRef]
- Parra, G.D.L.T.; Rad, P.; Choo, K.K.R.; Beebe, N. Detecting Internet of Things attacks using distributed deep learning. J. Netw. Comput. Appl. 2020, 163, 102662. [Google Scholar] [CrossRef]
- Aamir, M.; Zaidi, S.M.A. Clustering based semi-supervised machine learning for DDoS attack classification. J. King Saud Univ. Comput. Inf. Sci. 2021, 33, 436–446. [Google Scholar] [CrossRef]
- Khan, S.H.; Arko, A.R.; Chakrabarty, A. Anomaly Detection in IoT Using Machine Learning. In Artificial Intelligence for Cloud and Edge Computing; Springer: Berlin/Heidelberg, Germany, 2022; pp. 237–254. [Google Scholar]
- Jahromi, A.N.; Karimipour, H.; Dehghantanha, A.; Choo, K.K.R. Toward Detection and Attribution of Cyber-Attacks in IoT-Enabled Cyber–Physical Systems. IEEE Internet Things J. 2021, 8, 13712–13722. [Google Scholar] [CrossRef]
- Altan, G. SecureDeepNet-IoT: A deep learning application for invasion detection in industrial Internet of things sensing systems. Trans. Emerg. Telecommun. Technol. 2021, 32, e4228. [Google Scholar] [CrossRef]
- Rashid, M.M.; Kamruzzaman, J.; Hassan, M.M.; Imam, T.; Gordon, S. Cyberattacks detection in iot-based smart city applications using machine learning techniques. Int. J. Environ. Res. Public Health 2020, 17, 9347. [Google Scholar] [CrossRef]
- Zhang, Y.; Dukkipati, C.; Cheng, L.C. Clustering Methods for Identification of Attacks in IoT Based Traffic Signal System. In Proceedings of the 2019 International Conference on Sensing, Diagnostics, Prognostics, and Control (SDPC), Beijing, China, 15–17 August 2019; IEEE: New York, NY, USA, 2019; pp. 24–28. [Google Scholar]
- Ferrag, M.A.; Friha, O.; Maglaras, L.; Janicke, H.; Shu, L. Federated deep learning for cyber security in the internet of things: Concepts, applications, and experimental analysis. IEEE Access 2021, 9, 138509–138542. [Google Scholar] [CrossRef]
- Jain, A.; Singh, T.; Sharma, S.K. Security as a solution: An intrusion detection system using a neural network for IoT enabled healthcare ecosystem. Interdiscip. J. Inf. Knowl. Manag. 2021, 16, 331–369. [Google Scholar] [CrossRef]
- Gao, H.; Qiu, B.; Barroso, R.J.D.; Hussain, W.; Xu, Y.; Wang, X. TSMAE: A novel anomaly detection approach for internet of things time series data using memory-augmented autoencoder. In IEEE Transactions on Network Science and Engineering; IEEE: New York, NY, USA, 2022. [Google Scholar]
- Toğaçar, M. Detecting attacks on IoT devices with probabilistic Bayesian neural networks and hunger games search optimization approaches. Trans. Emerg. Telecommun. Technol. 2022, 33, e4418. [Google Scholar] [CrossRef]
- Khempetch, T.; Wuttidittachotti, P. DDoS attack detection using deep learning. IAES Int. J. Artif. Intell. 2021, 10, 382. [Google Scholar] [CrossRef]
- Brun, O.; Yin, Y.; Gelenbe, E.; Kadioglu, Y.M.; Augusto-Gonzalez, J.; Ramos, M. Deep learning with dense random neural networks for detecting attacks against IoT-connected home environments. In Proceedings of the International ISCIS Security Workshop, London, UK, 26–27 February 2018; Springer: Cham, Switzerland, 2018; pp. 79–89. [Google Scholar]
- Li, Z.; Zou, D.; Xu, S.; Chen, Z.; Zhu, Y.; Jin, H. VulDeeLocator: A Deep Learning-Based Fine-Grained Vulnerability Detector. IEEE Trans. Dependable Secur. Comput. 2022, 19, 2821–2837. [Google Scholar] [CrossRef]
- Roy, S.; Li, J.; Bai, Y. A Two-layer Fog-Cloud Intrusion Detection Model for IoT Networks. Internet Things 2022, 19, 100557. [Google Scholar] [CrossRef]
- Khan, S.; Akhunzada, A. A hybrid DL-driven intelligent SDN-enabled malware detection framework for Internet of Medical Things (IoMT). Comput. Commun. 2021, 170, 209–216. [Google Scholar] [CrossRef]
- Kozik, R.; Pawlicki, M.; Choraś, M. A new method of hybrid time window embedding with transformer-based traffic data classification in IoT-networked environment. Pattern Anal. Appl. 2021, 24, 1441–1449. [Google Scholar] [CrossRef]
- Gao, H.; Xiao, J.; Yin, Y.; Liu, T.; Shi, J. A Mutually Supervised Graph Attention Network for Few-Shot Segmentation: The Perspective of Fully Utilizing Limited Samples. In IEEE Transactions on Neural Networks and Learning Systems; IEEE: New York, NY, USA, 2022. [Google Scholar]
- Gao, H.; Huang, W.; Liu, T.; Yin, Y.; Li, Y. PPO2: Location Privacy-Oriented Task Offloading to Edge Computing Using Reinforcement Learning for Intelligent Autonomous Transport Systems. IEEE Trans. Intell. Transp. Syst. 2022, 24, 7. [Google Scholar] [CrossRef]
- Blanco-Medina, P.; Fidalgo, E.; Alegre, E.; Vasco-Carofilis, R.A.; Jañez-Martino, F.; Villar, V.F. Detecting vulnerabilities in critical infrastructures by classifying exposed industrial control systems using deep learning. Appl. Sci. 2021, 11, 367. [Google Scholar] [CrossRef]
- Naeem, H.; Alalfi, M.H. Identifying vulnerable IoT applications using deep learning. In Proceedings of the 2020 IEEE 27th International Conference on Software Analysis, Evolution and Reengineering (SANER), London, ON, Canada, 18–21 February 2020; IEEE: New York, NY, USA, 2020; pp. 582–586. [Google Scholar]
- Meidan, Y.; Sachidananda, V.; Peng, H.; Sagron, R.; Elovici, Y.; Shabtai, A. A novel approach for detecting vulnerable IoT devices connected behind a home NAT. Comput. Secur. 2020, 97, 101968. [Google Scholar] [CrossRef]
- Ullah, F.; Naeem, H.; Jabbar, S.; Khalid, S.; Latif, M.A.; Al-Turjman, F.; Mostarda, L. Cyber security threats detection in internet of things using deep learning approach. IEEE Access 2019, 7, 124379–124389. [Google Scholar] [CrossRef]
- Li, Z.; Zou, D.; Xu, S.; Ou, X.; Jin, H.; Wang, S.; Deng, Z.; Zhong, Y. Vuldeepecker: A deep learning-based system for vulnerability detection. arXiv 2018, arXiv:1801.01681. [Google Scholar]
- Jesmeen, M.; Hossen, J.; Sayeed, S.; Ho, C.; Tawsif, K.; Rahman, A.; Arif, E. A survey on cleaning dirty data using machine learning paradigm for big data analytics. Indones. J. Electr. Eng. Comput. Sci. 2018, 10, 1234–1243. [Google Scholar]
- Brownlee, J. Data Preparation for Machine Learning: Data Cleaning, Feature Selection, and Data Transforms in Python; Machine Learning Mastery: Vermont, Australia, 2020. [Google Scholar]
- Kasongo, S.M.; Sun, Y. A deep learning method with wrapper based feature extraction for wireless intrusion detection system. Comput. Secur. 2020, 92, 101752. [Google Scholar] [CrossRef]
- Zhou, J.; Gandomi, A.H.; Chen, F.; Holzinger, A. Evaluating the quality of machine learning explanations: A survey on methods and metrics. Electronics 2021, 10, 593. [Google Scholar] [CrossRef]
- Tune Model Hyperparameters—Azure Machine Learning|Microsoft Learn. 2021. Available online: https://learn.microsoft.com/en-us/azure/machine-learning/component-reference/tune-model-hyperparameters?view=azureml-api-2 (accessed on 14 February 2023).
- Booij, T.M.; Chiscop, I.; Meeuwissen, E.; Moustafa, N.; den Hartog, F.T. ToN_IoT: The role of heterogeneity and the need for standardization of features and attack types in IoT network intrusion data sets. IEEE Internet Things J. 2021, 9, 485–496. [Google Scholar] [CrossRef]
- Liang, Y.; Vankayalapati, N. Machine Learning and Deep Learning Methods for Better Anomaly Detection in IoT-23 Dataset Cybersecurity. 2021. Available online: https://github.com/yliang725/Anomaly-Detection-IoT23 (accessed on 10 January 2023).
- Khan, A.; Cotton, C. Detecting attacks on IoT devices using featureless 1D-CNN. In Proceedings of the 2021 IEEE International Conference on Cyber Security and Resilience (CSR), Rhodes, Greece, 26–28 July 2021; IEEE: New York, NY, USA, 2021; pp. 461–466. [Google Scholar]
- Seong, T.B.; Ponnusamy, V.; Jhanjhi, N.; Annur, R.; Talib, M. A comparative analysis on traditional wired datasets and the need for wireless datasets for IoT wireless intrusion detection. Indones. J. Electr. Eng. Comput. Sci. 2021, 22, 1165–1176. [Google Scholar] [CrossRef]
- Rajagopal, S.; Kundapur, P.P.; Hareesha, K.S. A stacking ensemble for network intrusion detection using heterogeneous datasets. Secur. Commun. Netw. 2020, 2020, 4586875. [Google Scholar] [CrossRef]
- Lonzetta, A.M.; Cope, P.; Campbell, J.; Mohd, B.J.; Hayajneh, T. Security vulnerabilities in Bluetooth technology as used in IoT. J. Sens. Actuator Netw. 2018, 7, 28. [Google Scholar] [CrossRef]
- Hadar, N.; Siboni, S.; Elovici, Y. A lightweight vulnerability mitigation framework for IoT devices. In Proceedings of the 2017 Workshop on Internet of Things Security and Privacy, Dallas, TX, USA, 3 November 2017; pp. 71–75. [Google Scholar]
- Adat, V.; Gupta, B. A DDoS attack mitigation framework for internet of things. In Proceedings of the 2017 International Conference on Communication and Signal Processing (ICCSP), Chennai, India, 6–8 April 2017; IEEE: New York, NY, USA, 2017; pp. 2036–2041. [Google Scholar]
- Yin, D.; Zhang, L.; Yang, K. A DDoS attack detection and mitigation with software-defined Internet of Things framework. IEEE Access 2018, 6, 24694–24705. [Google Scholar] [CrossRef]
- Yan, Q.; Huang, W.; Luo, X.; Gong, Q.; Yu, F.R. A multi-level DDoS mitigation framework for the industrial Internet of Things. IEEE Commun. Mag. 2018, 56, 30–36. [Google Scholar] [CrossRef]
- Nobakht, M.; Sivaraman, V.; Boreli, R. A host-based intrusion detection and mitigation framework for smart home IoT using OpenFlow. In Proceedings of the 2016 11th International Conference on Availability, Reliability and Security (ARES), Salzburg, Austria, 31 August–2 September 2016; IEEE: New York, NY, USA, 2016; pp. 147–156. [Google Scholar]
- Ibitoye, O.; Shafiq, O.; Matrawy, A. Analyzing adversarial attacks against deep learning for intrusion detection in IoT networks. In Proceedings of the 2019 IEEE Global Communications Conference (GLOBECOM), Waikoloa, HI, USA, 9–13 December 2019; IEEE: New York, NY, USA, 2019; pp. 1–6. [Google Scholar]
- Wang, J.; Chen, Y.; Hao, S.; Peng, X.; Hu, L. Deep learning for sensor-based activity recognition: A survey. Pattern Recognit. Lett. 2019, 119, 3–11. [Google Scholar] [CrossRef]
- Hore, S.; Moomtaheen, F.; Shah, A.; Ou, X. Towards Optimal Triage and Mitigation of Context-sensitive Cyber Vulnerabilities. IEEE Trans. Dependable Secur. Comput. 2022, 20, 1270–1285. [Google Scholar] [CrossRef]
- IEEE P11073-40101/D5, July 2020; IEEE Approved Draft Standard—Health Informatics—Device Interoperability— Part 40101: Cybersecurity—Processes for Vulnerability Assessment. IEEE: New York, NY, USA, 2020; pp. 1–46.
- Aurisch, T.; Jacke, A. Replication Strategies of Mobile Agents for Autonomous Vulnerability Mitigation. In Proceedings of the 2019 International Conference on Military Communications and Information Systems (ICMCIS), Budva, Montenegro, 14–15 May 2019; pp. 1–6. [Google Scholar] [CrossRef]
- Zhu, L.; Fu, X.; Yao, Y.; Zhang, Y.; Wang, H. FIoT: Detecting the memory corruption in lightweight IoT device firmware. In Proceedings of the 2019 18th IEEE International Conference On Trust, Security and Privacy in Computing and Communications/13th IEEE International Conference on Big Data Science and Engineering (TrustCom/BigDataSE), Rotorua, New Zealand, 5–8 August 2019; IEEE: New York, NY, USA, 2019; pp. 248–255. [Google Scholar]
- Nelson, C.; Izraelevitz, J.; Bahar, R.I.; Lehman, T.S. Eliminating Micro-Architectural Side-Channel Attacks using Near Memory Processing. In Proceedings of the 2022 IEEE International Symposium on Secure and Private Execution Environment Design (SEED), Storrs, CT, USA, 26-27 September 2022; pp. 179–189. [Google Scholar] [CrossRef]
- Education, I.C. What is an Application Programming Interface (API)? IBM: Armonk, NY, USA, 2020. [Google Scholar]
- Lee, J.; Jung, S.; Suh, T.; Oh, Y.; Yoon, M.K.; Koo, G. GhostLeg: Selective Memory Coalescing for Secure GPU Architecture. IEEE Access 2022, 10, 111449–111462. [Google Scholar] [CrossRef]
- Siriwardena, P. Advanced API Security: OAuth 2.0 and Beyond; Springer: Berlin/Heidelberg, Germany, 2020. [Google Scholar]
- Bhunia, S.; Tehranipoor, M. Hardware Security: A Hands-On Learning Approach; Morgan Kaufmann: Burlington, MA, USA, 2018. [Google Scholar]
- Chen, Z.; Zhang, Q.; Wu, J.; Yan, J.; Xue, J. A Source-Level Instrumentation Framework for the Dynamic Analysis of Memory Safety. IEEE Trans. Softw. Eng. 2022, 49, 2107–2127. [Google Scholar] [CrossRef]
- Gavin Wright, A.S.G. What Is a Side-Channel Attack? 2021. Available online: https://www.techtarget.com/searchsecurity/definition/side-channel-attack (accessed on 10 March 2023).
- Lyerly, R.; Wang, X.; Ravindran, B. Dynamic and Secure Memory Transformation in Userspace. In Proceedings of the European Symposium on Research in Computer Security, Guildford, UK, 14–18 September 2020; Springer: Berlin/Heidelberg, Germany, 2020; pp. 237–256. [Google Scholar]
| Vulnerabilities | Impact (Consequences) |
|---|---|
| Weak password | This vulnerability usually was performed to carry out attacks against the authorization of the IoT devices which allows the attacker to gain permission to control and access its ecosystem [19,20,21,22,23]. |
| Insecure network services | Hampers both the confidentiality, integrity, and availability of the system [24,25,26]. |
| Insecure Interfaces | Alteration and injection could be implemented against authorization and authentication. The authentication process identifies the device, whereas authorization grants permissions and both of these must exist in IoT devices to perform their roles. The result of these types of attacks could be unauthorized access and access to the network boundaries that connect within the device [27,28,29]. |
| Lack of update mechanism | Consists of unconfigured firmware, unencrypted delivery, no anti-rollback mechanisms, and no notifications of security updates, which leads to exploit the threat on the IoT software. For instance, the software updates can be replaced with malicious code by an attacker if there is an unsecured update mechanism [27,30,31]. |
| Insecure/outdated components | Using insecure components such as operating system platforms or third-party hardware could compromise the device, such as using hardware, like a server, which needs to be secured to prevent an attacker from gaining access to it or to the network for launching an attack or using it to initiate a botnet attack [32,33,34]. |
| Inadequate privacy protection | Most of the IoT ecosystems store personal information for their users and any failure to protect these data could lead to this information being stolen or compromised. In addition, the users must be aware of the privacy methods that are used in their devices, such as where and how their data will be stored using the regulation to protect their privacy [35,36]. |
| Insecure data transfer/storage | It is necessary to protect the data in the whole IoT for both transferred data and saved data in order to protect the consumers’ privacy. As the IoT ecosystem uses sensitive data in transit and storage or when processing, these data must be protected by using an efficient technique such as encryption to ensure the integrity and confidentiality of the ecosystem [20,35,37]. |
| Lack of device management | IoT device management issues occur when a company fails to adequately protect and secure connected devices. In an IoT environment, IoT device management is responsible for configuring, monitoring, and maintaining connected devices. Keeping the system updated and monitored, asset management, and updating the response capabilities protect the system against cyber attacks and data breaches [38,39,40]. |
| Insecure default setting | By restricting operators from altering configurations, the system cannot be secured, such as a lack of file system permissions could be exploited by running the services as root. It is possible to interrupt secret keys that are utilized to launch connections within a restricted network during the on-boarding process for an IoT device, thereby allowing the attackers to initiate an attack from the deepest physical layer such as the motherboard [41,42,43]. |
| Lack of physical protection | Poor physical hardening could make the IoT-connected network vulnerable. It may allow attackers to gain sensitive information that can be used in future remote attacks or to gain control of the device [44,45,46,47,48]. |
| Works | Attacks | Methods and Algorithms | Dataset and Results |
|---|---|---|---|
| Aliandy et al. [65] | DoS in MQTT-based IoT systems | Generalized linear model (GLM), RF, GBM, DL, Stack Ensemble | Data from Indonesia oil services company and the result was that the Stack Ensemble offers the best prediction accuracy and achieved the best results, followed by RF technique. |
| Satam et al. [66] | DoS attacks, Random Signal Attacks, and Replay Attacks | DT, AdaBoost, SVM, Naive Bayes, Ripper, and Bagging | Two datasets: the first was collected from Bluetooth traffic and the second from three temperature sensors. In the sensor datasets, the best performing technique was AdaBoost, whereas the bagging-based model was the best on the Bluetooth dataset. |
| Touga et al. [79] | DDoS attacks, Botnet | Probabilistic (BNN) Bayesian neural networks and normal Bayesian neural networks | Two datasets: Botnet-IoT and UNSWNB-15; accuracy on Botnet-IoT accuracy on UNSWNB-15. |
| Khempetch et al. [80] | DDoS attack (Syn Flood, UDP, and UDP-Lag) | DNN and long short-term memory (LSTM) algorithm | CICDDoS2019 dataset and the results indicate that 99.90–9.97% of all three types of DDoS attacks were identified. |
| Roopak et al. [67] | DDoS attack | Four different DL models: multilayer perceptron (MLP), 1d-CNN, Long Short-Term Memory (LSTM), CNN + LSTM | CICIDS2017 dataset and the highest accuracy was 97.16% using the CNN + LSTN model, whereas the lowest accuracy was with the MLP. |
| Brun et al. [81] | TCP, SYN attacks on IoT gateways | Dense RNN | Used a constructed dataset and it was able to predict with high-performance. |
| Dong et al. [68] | Botnet detection | Classify Botnet traffic and normal traffic based on ELM algorithm | ISCX-Bot-2014 dataset and the accuracy of ELM model was . |
| Parra et al. [69] | Phishing and Botnet attack | Using both methods: DCNN with cloud-based LSTM | Two data sets: created a dataset and N_BaIoT. CNN models are efficient at detecting phishing attacks with an accuracy of 94.3% and detect Botnet attacks with an accuracy of 94.80%. |
| Li et al. [82] | Vulnerability detection | Automatically VulDeeLocator | An automatic software vulnerability detector was developed using deep learning techniques, with accuracy up to 80.0%. |
| Aamir et al. [70] | DDoS attack | It provides a clustering-based approach for identifying network traffic flows, including normal and DDoS traffic by using kNN, SVM and RF models | OPNET Modeler 14.5 simulator resulted in an accuracy of 95% in kNN, 92% in SVM and 96.66% in RF. |
| Roy et al. [83] | Network attacks | Proposed a two-layer hierarchical approach using fog layer resources by employing a multi-layered feedforward NNs | The proposed approach for both datasets CICIDS2017 and NSL-KD showed better result than existing IDs and using the fog-cloud design reduced power and time consumption. |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2023 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).
Share and Cite
Hulayyil, S.B.; Li, S.; Xu, L. Machine-Learning-Based Vulnerability Detection and Classification in Internet of Things Device Security. Electronics 2023, 12, 3927. https://doi.org/10.3390/electronics12183927
Hulayyil SB, Li S, Xu L. Machine-Learning-Based Vulnerability Detection and Classification in Internet of Things Device Security. Electronics. 2023; 12(18):3927. https://doi.org/10.3390/electronics12183927
Chicago/Turabian StyleHulayyil, Sarah Bin, Shancang Li, and Lida Xu. 2023. "Machine-Learning-Based Vulnerability Detection and Classification in Internet of Things Device Security" Electronics 12, no. 18: 3927. https://doi.org/10.3390/electronics12183927
APA StyleHulayyil, S. B., Li, S., & Xu, L. (2023). Machine-Learning-Based Vulnerability Detection and Classification in Internet of Things Device Security. Electronics, 12(18), 3927. https://doi.org/10.3390/electronics12183927






