Harris-Hawk-Optimization-Based Deep Recurrent Neural Network for Securing the Internet of Medical Things
Abstract
:1. Introduction
- This research proposed a new technique that constructs machine learning and deep learning techniques in combination with the HHO algorithm for detecting cyber-attacks in IoMT.
- HHO is used for feature selection due to its quick coverage ability; it also hardly gets stuck in local minima. It improves the model performance compared with other optimizers.
- Results reveal that the proposed approach attains an accuracy of 99.85%, outperforming other techniques and existing studies, and provides an efficient model for detecting cyber-attacks in IoMT devices, preventing serious issues between end-users.
2. Literature Review
2.1. Machine Learning Techniques
2.2. Deep Learning Techniques
3. Proposed Methodology
3.1. Experimental Dataset
3.2. Dataset Preprocessing
3.3. Harris-Hawk-Optimization-Based Feature Selection
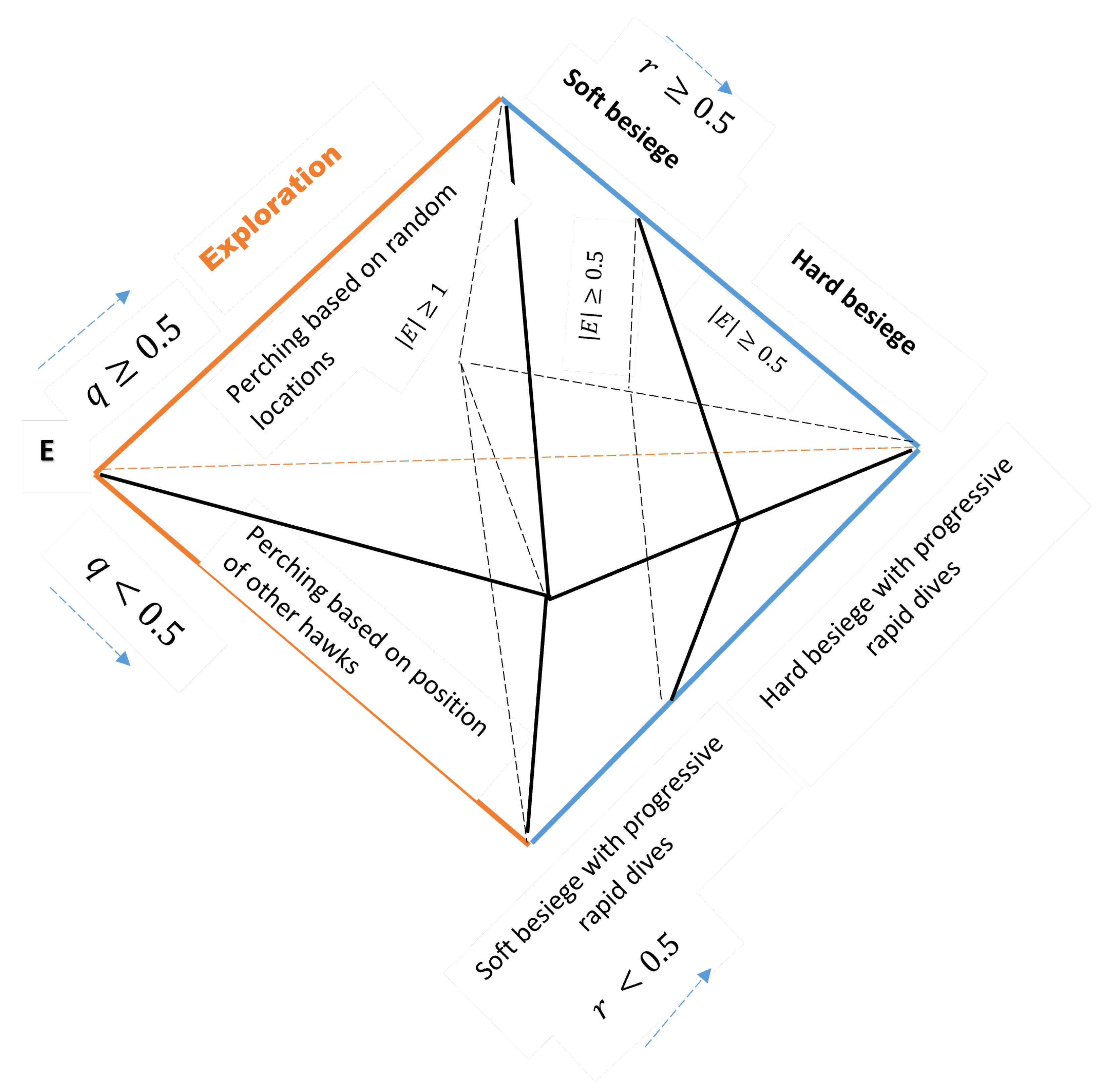
3.3.1. Exploration Phase
3.3.2. Exploitation Phase
| Algorithm 1 HHO’s pseudo code. |
|
3.4. Classification Algorithms
3.4.1. Recurrent Neural Network (RNN)
3.4.2. Random Forest
3.4.3. Support Vector Machine
3.4.4. Bagging
3.4.5. Boosting
4. Result and Discussion
4.1. Evaluation Measurements
4.2. Result and Analysis of the Experiment
4.3. Comparison of Proposed Approach with Exiting Studies
5. Conclusions
Author Contributions
Funding
Data Availability Statement
Conflicts of Interest
References
- Dhasarathan, C.; Hasan, M.K.; Islam, S.; Abdullah, S.; Mokhtar, U.A.; Javed, A.R.; Goundar, S. COVID-19 health data analysis and personal data preserving: A homomorphic privacy enforcement approach. Comput. Commun. 2023, 199, 87–97. [Google Scholar] [CrossRef]
- Pradhan, B.; Bhattacharyya, S.; Pal, K. IoT-based applications in healthcare devices. J. Healthc. Eng. 2021, 2021, 6632599. [Google Scholar] [CrossRef]
- Akhras, K.S.; Alsheikh-Ali, A.A.; Kabbani, S. Use of real-world evidence for healthcare decision-making in the Middle East: Practical considerations and future directions. Expert Rev. Pharmacoecon. Outcomes Res. 2019, 19, 245–250. [Google Scholar] [CrossRef]
- Javed, A.R.; Khan, H.U.; Alomari, M.K.B.; Sarwar, M.U.; Asim, M.; Almadhor, A.S.; Khan, M.Z. Toward explainable AI-empowered cognitive health assessment. Front. Public Health 2023, 11, 1024195. [Google Scholar] [CrossRef]
- Saheed, Y.K.; Arowolo, M.O. Efficient cyber attack detection on the internet of medical things-smart environment based on deep recurrent neural network and machine learning algorithms. IEEE Access 2021, 9, 161546–161554. [Google Scholar] [CrossRef]
- Safa, M.; Pandian, A.; Gururaj, H.; Ravi, V.; Krichen, M. Real time health care big data analytics model for improved QoS in cardiac disease prediction with IoT devices. Health Technol. 2023, 1–11. [Google Scholar] [CrossRef]
- Akram, F.; Liu, D.; Zhao, P.; Kryvinska, N.; Abbas, S.; Rizwan, M. Trustworthy Intrusion Detection in E-Healthcare Systems. Front. Public Health 2021, 9, 1800. [Google Scholar] [CrossRef] [PubMed]
- Rahman, H.; Naik Bukht, T.F.; Ahmad, R.; Almadhor, A.; Javed, A.R. Efficient Breast Cancer Diagnosis from Complex Mammographic Images Using Deep Convolutional Neural Network. Comput. Intell. Neurosci. 2023, 2023, 7717712. [Google Scholar] [CrossRef] [PubMed]
- Bharadwaj, H.K.; Agarwal, A.; Chamola, V.; Lakkaniga, N.R.; Hassija, V.; Guizani, M.; Sikdar, B. A review on the role of machine learning in enabling IoT based healthcare applications. IEEE Access 2021, 9, 38859–38890. [Google Scholar] [CrossRef]
- Javed, A.R.; Shahzad, F.; ur Rehman, S.; Zikria, Y.B.; Razzak, I.; Jalil, Z.; Xu, G. Future smart cities requirements, emerging technologies, applications, challenges, and future aspects. Cities 2022, 129, 103794. [Google Scholar] [CrossRef]
- Lian, Z.; Zeng, Q.; Wang, W.; Gadekallu, T.R.; Su, C. Blockchain-Based Two-Stage Federated Learning with Non-IID Data in IoMT System. IEEE Trans. Comput. Soc. Syst. 2022. [Google Scholar] [CrossRef]
- Yenduri, G.; Kaluri, R.; Gadekallu, T.R.; Mahmud, M.; Brown, D.J. Blockchain for Software Maintainability in Healthcare. In Proceedings of the 24th International Conference on Distributed Computing and Networking, Kharagpur, India, 4–7 January 2023; pp. 420–424. [Google Scholar]
- Rbah, Y.; Mahfoudi, M.; Balboul, Y.; Fattah, M.; Mazer, S.; Elbekkali, M.; Bernoussi, B. Machine Learning and Deep Learning Methods for Intrusion Detection Systems in IoMT: A survey. In Proceedings of the 2022 2nd International Conference on Innovative Research in Applied Science, Engineering and Technology (IRASET), Meknes, Morocco, 3–4 March 2022; pp. 1–9. [Google Scholar]
- Mohiyuddin, A.; Chakraborty, C.; Rizwan, M.; Shabbir, M. Secure cloud storage for medical IoT data using adaptive neuro-fuzzy inference system. Int. J. Fuzzy Syst. 2022, 24, 1203–1215. [Google Scholar] [CrossRef]
- Mehmood, M.; Rizwan, M.; Gregus ml, M.; Abbas, S. Machine learning assisted cervical cancer detection. Front. Public Health 2021, 9, 788376. [Google Scholar] [CrossRef] [PubMed]
- Haraty, R.A.; Boukhari, B.; Kaddoura, S. An Effective Hash-Based Assessment and Recovery Algorithm for Healthcare Systems. Arab. J. Sci. Eng. 2021, 47, 1523–1536. [Google Scholar] [CrossRef]
- El Zarif, O.; Haraty, R.A. Toward information preservation in healthcare systems. In Innovation in Health Informatics; Elsevier: Amsterdam, The Netherlands, 2020; pp. 163–185. [Google Scholar]
- Kaddoura, S.; Haraty, R.A.; Al Kontar, K.; Alfandi, O. A parallelized database damage assessment approach after cyberattack for healthcare systems. Future Internet 2021, 13, 90. [Google Scholar] [CrossRef]
- Chehab, M.; Mourad, A. Towards a lightweight policy-based privacy enforcing approach for IoT. In Proceedings of the 2018 International Conference on Computational Science and Computational Intelligence (CSCI), Las Vegas, NV, USA, 12–14 December 2018; pp. 984–989. [Google Scholar]
- Khan, S.; Akhunzada, A. A hybrid DL-driven intelligent SDN-enabled malware detection framework for Internet of Medical Things (IoMT). Comput. Commun. 2021, 170, 209–216. [Google Scholar] [CrossRef]
- Wahab, O.A.; Mourad, A.; Otrok, H.; Taleb, T. Federated machine learning: Survey, multi-level classification, desirable criteria and future directions in communication and networking systems. IEEE Commun. Surv. Tutorials 2021, 23, 1342–1397. [Google Scholar] [CrossRef]
- AbdulRahman, S.; Tout, H.; Ould-Slimane, H.; Mourad, A.; Talhi, C.; Guizani, M. A survey on federated learning: The journey from centralized to distributed on-site learning and beyond. IEEE Internet Things J. 2020, 8, 5476–5497. [Google Scholar] [CrossRef]
- AbdulRahman, S.; Tout, H.; Mourad, A.; Talhi, C. FedMCCS: Multicriteria client selection model for optimal IoT federated learning. IEEE Internet Things J. 2020, 8, 4723–4735. [Google Scholar] [CrossRef]
- Dasaradharami Reddy, K.; Gadekallu, T.R. A Comprehensive Survey on Federated Learning Techniques for Healthcare Informatics. Comput. Intell. Neurosci. 2023, 2023, 8393990. [Google Scholar] [CrossRef]
- Xue, B.; Warkentin, M.; Mutchler, L.A.; Balozian, P. Self-efficacy in information security: A replication study. J. Comput. Inf. Syst. 2023, 63, 1–10. [Google Scholar] [CrossRef]
- Yunis, M.M.; El-Khalil, R.; Ghanem, M. Towards a Conceptual Framework on the Importance of Privacy and Security Concerns in Audit Data Analytics. In Proceedings of the International Conference on Industrial Engineering and Operations Management, Sao Paulo, Brazil, 5–8 April 2021. [Google Scholar]
- Hady, A.A.; Ghubaish, A.; Salman, T.; Unal, D.; Jain, R. Intrusion detection system for healthcare systems using medical and network data: A comparison study. IEEE Access 2020, 8, 106576–106584. [Google Scholar] [CrossRef]
- Abbas, N.; Nasser, Y.; Shehab, M.; Sharafeddine, S. Attack-specific feature selection for anomaly detection in software-defined networks. In Proceedings of the 2021 3rd IEEE Middle East and North Africa COMMunications Conference (MENACOMM), Agadir, Morocco, 3–5 December 2021; pp. 142–146. [Google Scholar]
- Wahab, O.A.; Bentahar, J.; Otrok, H.; Mourad, A. Resource-aware detection and defense system against multi-type attacks in the cloud: Repeated bayesian stackelberg game. IEEE Trans. Dependable Secur. Comput. 2019, 18, 605–622. [Google Scholar] [CrossRef]
- Nayak, J.; Meher, S.K.; Souri, A.; Naik, B.; Vimal, S. Extreme learning machine and bayesian optimization-driven intelligent framework for IoMT cyber-attack detection. J. Supercomput. 2022, 78, 14866–14891. [Google Scholar] [CrossRef]
- Kumar, P.; Gupta, G.P.; Tripathi, R. An ensemble learning and fog-cloud architecture-driven cyber-attack detection framework for IoMT networks. Comput. Commun. 2021, 166, 110–124. [Google Scholar] [CrossRef]
- Moukafih, N.; Orhanou, G.; El Hajji, S. Neural network-based voting system with high capacity and low computation for intrusion detection in SIEM/IDS systems. Secur. Commun. Netw. 2020, 2020, 3512737. [Google Scholar] [CrossRef]
- Saheed, Y.K.; Abiodun, A.I.; Misra, S.; Holone, M.K.; Colomo-Palacios, R. A machine learning-based intrusion detection for detecting internet of things network attacks. Alex. Eng. J. 2022, 61, 9395–9409. [Google Scholar] [CrossRef]
- Radoglou-Grammatikis, P.; Sarigiannidis, P.; Efstathopoulos, G.; Lagkas, T.; Fragulis, G.; Sarigiannidis, A. A self-learning approach for detecting intrusions in healthcare systems. In Proceedings of the ICC 2021-IEEE International Conference on Communications, Montreal, QC, Canada, 14–23 June 2021; pp. 1–6. [Google Scholar]
- Rahman, S.A.; Tout, H.; Talhi, C.; Mourad, A. Internet of things intrusion detection: Centralized, on-device, or federated learning? IEEE Netw. 2020, 34, 310–317. [Google Scholar] [CrossRef]
- Gautam, S.; Henry, A.; Zuhair, M.; Rashid, M.; Javed, A.R.; Maddikunta, P.K.R. A Composite Approach of Intrusion Detection Systems: Hybrid RNN and Correlation-Based Feature Optimization. Electronics 2022, 11, 3529. [Google Scholar] [CrossRef]
- Haque, N.I.; Rahman, M.A.; Shahriar, M.H.; Khalil, A.A.; Uluagac, S. A novel framework for threat analysis of machine learning-based smart healthcare systems. arXiv 2021, arXiv:2103.03472. [Google Scholar]
- Aleesa, A.; Younis, M.; Mohammed, A.A.; Sahar, N. Deep-intrusion detection system with enhanced UNSW-NB15 dataset based on deep learning techniques. J. Eng. Sci. Technol. 2021, 16, 711–727. [Google Scholar]
- Hammoud, A.; Mourad, A.; Otrok, H.; Wahab, O.A.; Harmanani, H. Cloud federation formation using genetic and evolutionary game theoretical models. Future Gener. Comput. Syst. 2020, 104, 92–104. [Google Scholar] [CrossRef]
- Shamseddine, H.; Nizam, J.; Hammoud, A.; Mourad, A.; Otrok, H.; Harmanani, H.; Dziong, Z. A novel federated fog architecture embedding intelligent formation. IEEE Netw. 2020, 35, 198–204. [Google Scholar] [CrossRef]
- Kuppusamy, P.; Kumari, N.M.J.; Alghamdi, W.Y.; Alyami, H.; Ramalingam, R.; Javed, A.R.; Rashid, M. Job scheduling problem in fog-cloud-based environment using reinforced social spider optimization. J. Cloud Comput. 2022, 11, 99. [Google Scholar] [CrossRef]
- Wahab, O.A.; Bentahar, J.; Otrok, H.; Mourad, A. Optimal load distribution for the detection of VM-based DDoS attacks in the cloud. IEEE Trans. Serv. Comput. 2017, 13, 114–129. [Google Scholar] [CrossRef]
- Kilincer, I.F.; Ertam, F.; Sengur, A.; Tan, R.S.; Acharya, U.R. Automated detection of cybersecurity attacks in healthcare systems with recursive feature elimination and multilayer perceptron optimization. Biocybern. Biomed. Eng. 2023, 43, 30–41. [Google Scholar] [CrossRef]
- Khan, F.; Jan, M.A.; Alturki, R.; Alshehri, M.D.; Shah, S.T.; ur Rehman, A. A Secure Ensemble Learning-Based Fog-Cloud Approach for Cyberattack Detection in IoMT. IEEE Trans. Ind. Inform. 2023. [Google Scholar] [CrossRef]
- RM, S.P.; Maddikunta, P.K.R.; Parimala, M.; Koppu, S.; Gadekallu, T.R.; Chowdhary, C.L.; Alazab, M. An effective feature engineering for DNN using hybrid PCA-GWO for intrusion detection in IoMT architecture. Comput. Commun. 2020, 160, 139–149. [Google Scholar]
- Aswad, F.M.; Ahmed, A.M.S.; Alhammadi, N.A.M.; Khalaf, B.A.; Mostafa, S.A. Deep learning in distributed denial-of-service attacks detection method for Internet of Things networks. J. Intell. Syst. 2023, 32. [Google Scholar] [CrossRef]
- Hnamte, V.; Hussain, J. DCNNBiLSTM: An efficient hybrid deep learning-based intrusion detection system. Telemat. Inform. Rep. 2023, 10, 100053. [Google Scholar] [CrossRef]
- Yazdinejad, A.; Kazemi, M.; Parizi, R.M.; Dehghantanha, A.; Karimipour, H. An ensemble deep learning model for cyber threat hunting in industrial internet of things. Digit. Commun. Netw. 2023, 9, 101–110. [Google Scholar] [CrossRef]
- Tavallaee, M.; Bagheri, E.; Lu, W.; Ghorbani, A.A. A detailed analysis of the KDD CUP 99 data set. In Proceedings of the 22009 IEEE Symposium on Computational Intelligence for Security and Defense Applications, Ottawa, ON, Canada, 8–10 July 2009; pp. 1–6. [Google Scholar]
- Farahnakian, F.; Heikkonen, J. A deep auto-encoder based approach for intrusion detection system. In Proceedings of the 2018 20th International Conference on Advanced Communication Technology (ICACT), Chuncheon, Korea, 11–14 February 2018; pp. 178–183. [Google Scholar]
- Wang, W.; Zhang, X.; Gombault, S.; Knapskog, S.J. Attribute normalization in network intrusion detection. In Proceedings of the 2009 10th International Symposium on Pervasive Systems, Algorithms, and Networks, Kaoshiung, Taiwan, 14–16 December 2009; pp. 448–453. [Google Scholar]
- Shakya, V.; Makwana, R.R.S. Feature selection based intrusion detection system using the combination of DBSCAN, K-Mean++ and SMO algorithms. In Proceedings of the 2017 international conference on trends in electronics and informatics (ICEI), Tirunelveli, India, 11–12 May 2017; pp. 928–932. [Google Scholar]
- Saheed, Y.K.; Hamza-Usman, F.E. Feature selection with IG-R for improving performance of intrusion detection system. Int. J. Commun. Netw. Inf. Secur. 2020, 12, 338–344. [Google Scholar] [CrossRef]
- Deka, R.K.; Bhattacharyya, D.K.; Kalita, J.K. Active learning to detect DDoS attack using ranked features. Comput. Commun. 2019, 145, 203–222. [Google Scholar] [CrossRef]
- Heidari, A.A.; Mirjalili, S.; Faris, H.; Aljarah, I.; Mafarja, M.; Chen, H. Harris hawks optimization: Algorithm and applications. Future Gener. Comput. Syst. 2019, 97, 849–872. [Google Scholar] [CrossRef]
- Abdel-Basset, M.; Ding, W.; El-Shahat, D. A hybrid Harris Hawks optimization algorithm with simulated annealing for feature selection. Artif. Intell. Rev. 2021, 54, 593–637. [Google Scholar] [CrossRef]
- Dokeroglu, T.; Deniz, A.; Kiziloz, H.E. A robust multiobjective Harris’ Hawks Optimization algorithm for the binary classification problem. Knowl.-Based Syst. 2021, 227, 107219. [Google Scholar] [CrossRef]
- Tang, T.A.; Mhamdi, L.; McLernon, D.; Zaidi, S.A.R.; Ghogho, M. Deep recurrent neural network for intrusion detection in sdn-based networks. In Proceedings of the 2018 4th IEEE Conference on Network Softwarization and Workshops (NetSoft), Montreal, QC, Canada, 25–29 June 2018; pp. 202–206. [Google Scholar]
- Zhang, H.; Dai, S.; Li, Y.; Zhang, W. Real-time distributed-random-forest-based network intrusion detection system using Apache spark. In Proceedings of the 2018 IEEE 37th international performance computing and communications conference (IPCCC), Orlando, FL, USA, 17–19 November 2018; pp. 1–7. [Google Scholar]
- Rani, D.; Gill, N.S.; Gulia, P.; Chatterjee, J.M. An Ensemble-Based Multiclass Classifier for Intrusion Detection Using Internet of Things. Comput. Intell. Neurosci. 2022, 2022, 1668676. [Google Scholar] [CrossRef] [PubMed]
- Odegua, R. An empirical study of ensemble techniques (bagging boosting and stacking). Deep Learn. IndabaXAt 2019. [Google Scholar] [CrossRef]
- Nguyen, H.T.; Ngo, Q.D.; Le, V.H. IoT botnet detection approach based on PSI graph and DGCNN classifier. In Proceedings of the 2018 IEEE international conference on information communication and signal processing (ICICSP), Singapore, 28–30 September 2018; pp. 118–122. [Google Scholar]




| Algorithms | AC% | PR% | RE% | F1% |
|---|---|---|---|---|
| HHO-RNN | 99.8 | 98.3 | 98.7 | 97.6 |
| HHO-RF | 97.5 | 98.2 | 98.7 | 98.5 |
| HHO-SVM | 96.8 | 99.7 | 97.2 | 98.7 |
| HHO-Bagging | 97.5 | 97.9 | 98.5 | 98.2 |
| HHO-Boosting | 98.1 | 96.1 | 97.9 | 97.0 |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2023 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).
Share and Cite
Abbas, S.; Sampedro, G.A.; Abisado, M.; Almadhor, A.; Yousaf, I.; Hong, S.-P. Harris-Hawk-Optimization-Based Deep Recurrent Neural Network for Securing the Internet of Medical Things. Electronics 2023, 12, 2612. https://doi.org/10.3390/electronics12122612
Abbas S, Sampedro GA, Abisado M, Almadhor A, Yousaf I, Hong S-P. Harris-Hawk-Optimization-Based Deep Recurrent Neural Network for Securing the Internet of Medical Things. Electronics. 2023; 12(12):2612. https://doi.org/10.3390/electronics12122612
Chicago/Turabian StyleAbbas, Sidra, Gabriel Avelino Sampedro, Mideth Abisado, Ahmad Almadhor, Iqra Yousaf, and Seng-Phil Hong. 2023. "Harris-Hawk-Optimization-Based Deep Recurrent Neural Network for Securing the Internet of Medical Things" Electronics 12, no. 12: 2612. https://doi.org/10.3390/electronics12122612
APA StyleAbbas, S., Sampedro, G. A., Abisado, M., Almadhor, A., Yousaf, I., & Hong, S.-P. (2023). Harris-Hawk-Optimization-Based Deep Recurrent Neural Network for Securing the Internet of Medical Things. Electronics, 12(12), 2612. https://doi.org/10.3390/electronics12122612








