Digital Contact Tracing: Large-Scale Geolocation Data as an Alternative to Bluetooth-Based Apps Failure
Abstract
1. Introduction
- High adoption rate: We propose to use real-time location information from (literally) billions of people around the world that is already available in databases of large BigTech companies like Facebook (FB), Google, Apple, etc. We refer to these players as Location Providers (LPs) in this paper. Some of these LPs, mainly Google and Facebook, have a very large rate of active users, over 50%, in many western countries.
- Contact identification in airborne transmission range: To geolocate users at both outdoor [13] and indoor locations [14] with an accuracy of few meters, these BigTech firms use a combination of techniques that rely on multiple signals including GPS location information, WiFi SSIDs signal’s power, cellular network signals, etc.
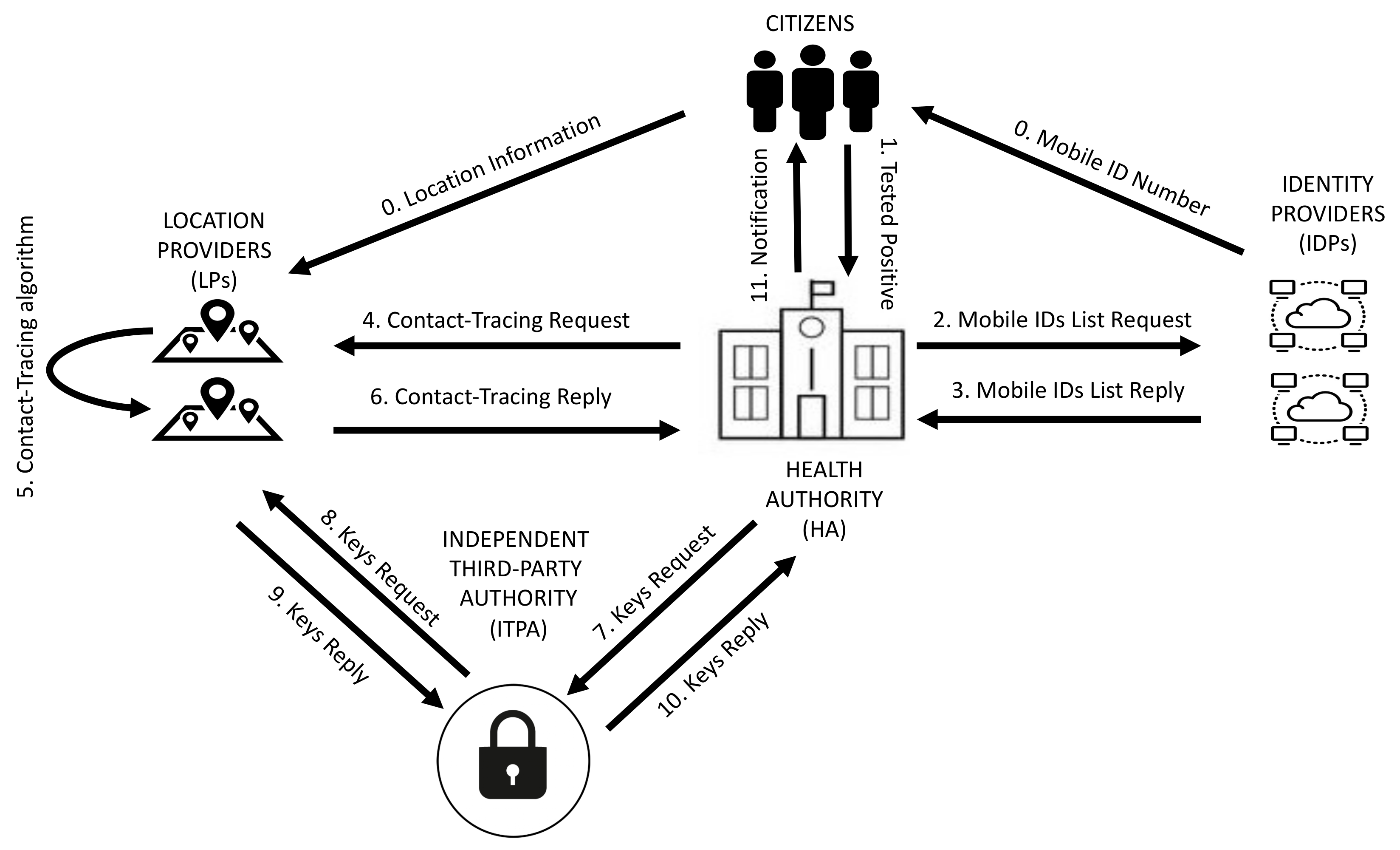
- Legal and Ethical Requirements: We are interested in performing contact-tracing just for individuals who have tested positive of COVID-19. The identity of infected individuals is sensitive information handled by the Health Authority (HA) of each country, which is also responsible for running the contact-tracing strategy. Therefore, the HA has the identity of infected individuals while the LP has the data to perform the contact-tracing for those individuals. We propose a system that allows running contact-tracing using LPs data on those individuals who tested positive as reported by HAs. Even the most restrictive data protection laws, like the GDPR [15], explicitly provision exceptions in which personal data can be used to monitor epidemics and their spread (see GDPR Article 6 Recital 46 [15]). Sustained on this legal basis an agreement to perform an exchange of data between LPs and HAs might be possible. However, to provide higher privacy guarantees, we propose a simple architecture and communication protocol that enable the exchange of information between an LP and a HA significantly limiting the ability of (1) HAs to obtain the contact graph of an individual and (2) LPs to learn the identity of infected individuals.
2. Solution Rationale
2.1. Why Using Geolocation Data?
2.2. Other Benefits
2.3. Privacy Requirements
2.4. Meeting Privacy Requirements
3. Protocol for Contact-Tracing Using Location Providers Information
- Step 0: This step refers to the basic context that our solution relies on. On the one hand, LPs record historical location information from users running their OSs, mobile apps, etc. They also store the mobile phone number for a major portion of the users. On the other hand, IDPs (i.e., mobile operators) provide users with mobile phone numbers that serve as user IDs in our solution.
- Step 1: The HA obtains the IDs of users that have been tested positive in a given time window (e.g., a day).
- Step 2: The HA triggers the contact-tracing process by requesting the IDP a list of N user IDs (i.e., real mobile phone numbers). The value of N is decided by the HA and may differ from one request to another.
- Step 3: The IDP responds to the HA request with a list of N random user IDs.
- Step 4: The HA creates K groups. As explained above, only L of these groups are infected groups and are random groups. The resulting groups are included in a Contact-Tracing Request message that is sent to the LP. It is important to note that the user IDs included in an infected group can neither be present in other infected groups in this request nor in past or future requests.
- Step 5: Upon the reception of the Contact-Tracing Request, the LP runs the contact-tracing algorithm to identify the risk contact IDs of each user ID included in the request. The risk contact IDs from all users in a group are aggregated so that any link between a user ID and a risk contact ID is eliminated.
- Step 6: Upon the reception of the Contact-Tracing Reply the HA needs to decrypt the information associated with the infected groups, i.e., the risk contacts list and the type of POIs distribution. To this end, the HA sends a Keys Request message to the ITPA that includes the total number of groups included in the Contact-Tracing Request and the identifiers of the infected groups.
- Step 7: The ITPA sends the Keys Request message to the LP but includes only the Transaction ID.
- Step 8: Upon the reception of the Keys Request message, the LP sends a Keys Reply message to the ITPA that includes the keys for all groups.
- Step 9: The ITPA checks if the number of keys in the received reply matches the actual number of groups reported by the HA. If the numbers are the same, the ITPA generates a Keys Reply message to the HA that includes only the keys of the infected groups. Otherwise, the Keys Reply message includes an error indicating that the reported number of groups does not match with the number of keys provided by the LP.
- Step 10: Upon the reception of the Keys Reply message, the HA decrypts the information about the risk contacts and the types of POIs distributions included in the Contact-Tracing Reply for the groups of infected users.
- Step 11: The HA initiates contact with the risk contacts.
4. Potential Attacks and Countermeasures
4.1. LP Inference Regarding an Infected User’s Identity
4.2. HAs Inference Regarding the Contact Graph of a User-ID
5. Conclusions
Author Contributions
Funding
Conflicts of Interest
References
- Ferretti, L.; Wymant, C.; Kendall, M.; Zhao, L.; Nurtay, A.; Abeler-Dörner, L.; Parker, M.; Bonsall, D.; Fraser, C. Quantifying SARS-CoV-2 transmission suggests epidemic control with digital contact tracing. Science 2020, 368. [Google Scholar] [CrossRef] [PubMed]
- StraitTimes. Call for More People to Use Contact-Tracing App. 2020. Available online: https://www.straitstimes.com/singapore/call-for-more-people-to-use-contact-tracing-app (accessed on 20 April 2020).
- Hinch, R.; Probert, W.; Nurtay, A.; Kendall, M.; Wymant, C.; Hall, M.; Lythgoe, K.; Cruz, A.B.; Zhao, L.; Fraser, C.; et al. Effective Configurations of a Digital Contact Tracing App: A Report to NHSX. GitHub. 2020. Available online: https://github.com/BDI-pathogens/covid-19_instant_tracing/blob/master/Report (accessed on 26 February 2021).
- Troncoso, C.; Payer, M.; Hubaux, J.; Salathé, M.; Larus, J.; Bugnion, E.; Lueks, W.; Stadler, T.; Pyrgelis, A.; Antonioli, D.; et al. Decentralized Privacy-Preserving Proximity Tracing. arXiv 2020, arXiv:2005.12273. [Google Scholar]
- White, L.; van Basshuysen, P. Without a trace: Why did corona apps fail? J. Med. Ethics 2021. [Google Scholar] [CrossRef] [PubMed]
- Apple; Google. Exposure Notifications: Using Technology to Help Public Health Authorities Fight COVID‑19. 2021. Available online: https://www.google.com/covid19/exposurenotifications/ (accessed on 26 February 2021).
- Salathé, M.; Althaus, C.L.; Anderegg, N.; Antonioli, D.; Ballouz, T.; Bugnion, E.; Čapkun, S.; Jackson, D.; Kim, S.I.; Larus, J.R.; et al. Early Evidence of Effectiveness of Digital Contact Tracing for SARS-CoV-2 in Switzerland. medRxiv 2020. [Google Scholar] [CrossRef]
- Rodríguez, P.; Graña, S.; Alvarez-León, E.E.; Battaglini, M.; Darias, F.J.; Hernán, M.A.; López, R.; Llaneza, P.; Martín, M.C.; Ramirez-Rubio, O.; et al. A population-based controlled experiment assessing the epidemiological impact of digital contact tracing. Nat. Commun. 2021, 12, 1–6. [Google Scholar] [CrossRef] [PubMed]
- Wymant, C.; Ferretti, L.; Tsallis, D.; Charalambides, M.; Abeler-Dörner, L.; Bonsall, D.; Hinch, R.; Kendall, M.; Milsom, L.; Ayres, M.; et al. The Epidemiological Impact of the NHS COVID-19 App; Alan Turing Institute: London, UK, 2021; Available online: https://github.com/BDI-pathogens/covid-19_instant_tracing/blob/master/Epidemiological_Impact_of_the_NHS_COVID_19_App_Public_Release_V1.pdf (accessed on 26 February 2021).
- Scientific Brief: SARS-CoV-2 and Potential Airborne Transmission. In Centers for Disease Control and Prevention (CDC); 2020. Available online: https://www.cdc.gov/coronavirus/2019-ncov/more/scientific-brief-sars-cov-2.html (accessed on 27 December 2020).
- Prather, K.A.; Marr, L.C.; Schooley, R.T.; McDiarmid, M.A.; Wilson, M.E.; Milton, D.K. Airborne transmission of SARS-CoV-2. Science 2020, 370, 303–304. [Google Scholar] [CrossRef] [PubMed]
- Lednicky, J.A.; Lauzardo, M.; Fan, Z.H.; Jutla, A.; Tilly, T.B.; Gangwar, M.; Usmani, M.; Shankar, S.N.; Mohamed, K.; Eiguren-Fernandez, A.; et al. Viable SARS-CoV-2 in the air of a hospital room with COVID-19 patients. medRxiv 2020. [Google Scholar] [CrossRef]
- GPS.gov. GPS Accuracy. 2017. Available online: https://www.gps.gov/systems/gps/performance/accuracy/ (accessed on 20 April 2020).
- Google. Wi-Fi Location: Ranging with RTT. 2020. Available online: https://developer.android.com/guide/topics/connectivity/wifi-rtt (accessed on 20 April 2020).
- European Union. Regulation (EU) 2016/679 of the European Parliament (General Data Protection Regulation). 2016. Available online: http://eur-lex.europa.eu/eli/reg/2016/679/oj (accessed on 22 April 2020).
- Mokbel, M.; Abbar, S.; Stanojevic, R. Contact Tracing: Beyond the Apps. SIGSPATIAL Spec. 2020, 12, 15–24. [Google Scholar] [CrossRef]
- Reichert, L.; Brack, S.; Scheuermann, B. Privacy-Preserving contact tracing of COVID-19 patients. IACR Cryptol. ePrint Arch. 2020, 2020, 375. [Google Scholar]
- Nakamoto, I.; Wang, S.; Guo, Y.; Zhuang, W. A QR Code–Based Contact Tracing Framework for Sustainable Containment of COVID-19: Evaluation of an Approach to Assist the Return to Normal Activity. JMIR mHealth uHealth 2020, 8, e22321. [Google Scholar] [CrossRef] [PubMed]
- Rahman, M.T.; Khan, R.T.; Khandaker, M.R.; Sellathurai, M.; Salan, M.S.A. An automated contact tracing approach for controlling COVID-19 spread based on geolocation data from mobile cellular networks. IEEE Access 2020, 8, 213554–213565. [Google Scholar] [CrossRef]
- Dimoco. Market Insights. 2020. Available online: https://dimoco.eu/carrierbilling/coverage/ (accessed on 27 December 2020).
- StatCounter Global Stats. Mobile Operating System Market Share Worldwide. 2020. Available online: https://gs.statcounter.com/os-market-share/mobile/ (accessed on 27 December 2020).
- Demographics of Mobile Device Ownership and Adoption in the United States. 2020. Available online: https://www.pewresearch.org/internet/fact-sheet/mobile/ (accessed on 27 December 2020).
- Facebook. Facebook Marketing API. 2020. Available online: https://developers.facebook.com/docs/marketing-apis (accessed on 27 December 2020).
- Austria: The Official Travel Portal. Austria’s “Stopp Corona” app helps your peace of mind on holiday. 2020. Available online: https://www.austria.info/en/service-and-facts/coronavirus-information/app (accessed on 27 December 2020).
- Australian Government. COVIDSafe App. 2020. Available online: https://www.covidsafe.gov.au/ (accessed on 27 December 2020).
- COSIC—ESAT KU Leuven. Coronalert: A Promising Start. 2020. Available online: https://www.esat.kuleuven.be/cosic/blog/coronalert-a-promising-start/ (accessed on 20 October 2020).
- Government of the Republic of Croatia. Stop COVID-19. 2020. Available online: https://www.koronavirus.hr/stop-covid-19-723/723 (accessed on 27 December 2020).
- eRouška. Frequently Asked Questions. 2020. Available online: https://erouska.cz/caste-dotazy#statistiky (accessed on 27 December 2020).
- Smitte|stop. Driftsstatus. 2020. Available online: https://smittestop.dk/status/ (accessed on 27 December 2020).
- Finnish Institute for Health and Welfare. Koronavilkku Has Been Downloaded More than 2.5 Million Times—Widespread Use Increases the App’s Effectiveness. 2020. Available online: https://thl.fi/en/web/thlfi-en/-/koronavilkku-has-been-downloaded-more-than-2.5-million-times-widespread-use-increases-the-app-s-effectiveness (accessed on 5 November 2020).
- Latvian Public Broadcasting. “Stop COVID” App Has Helped 110 Times Already in Latvia. 2020. Available online: https://eng.lsm.lv/article/society/health/stop-covid-app-has-helped-110-times-already-in-latvia.a379047/ (accessed on 23 October 2020).
- Overheid.nl Open Data of the Government. Dataset CoronaMelder Statistieken. 2020. Available online: https://data.overheid.nl/en/dataset/coronamelder-statistieken (accessed on 27 December 2020).
- Pickaso. Infografía: Evolución Apps Móviles de Radar COVID-19 en Europa. 2020. Available online: https://pickaso.com/2020/infografia-apps-radar-covid-europa (accessed on 31 October 2020).
- Briers, M.; Holmes, C.; Fraser, C. Demonstrating the Impact of the NHS COVID-19 App; Alan Turing Institute: London, UK, 2021; Available online: https://www.turing.ac.uk/blog/demonstrating-impact-nhs-covid-19-app (accessed on 26 February 2021).
- NBC News. Despite Promise, Few in US Adopting COVID-19 Exposure Apps. 2020. Available online: https://www.nbcnews.com/tech/tech-news/promise-us-adopting-covid-19-exposure-apps-rcna189 (accessed on 7 December 2020).
- Swiss Federal Statistical Office. Swiss Covid App Monitoring. 2020. Available online: https://www.experimental.bfs.admin.ch/expstat/en/home/innovative-methods/swisscovid-app-monitoring.assetdetail.13407769.html (accessed on 27 December 2020).
- Aleta, A.; Martín-Corral, D.; Bakker, M.A.; Piontti, A.P.Y.; Ajelli, M.; Litvinova, M.; Chinazzi, M.; Dean, N.E.; Halloran, M.E.; Longini, I.M.; et al. Quantifying the importance and location of SARS-CoV-2 transmission events in large metropolitan areas. medRxiv 2020. [Google Scholar] [CrossRef]
- The World Bank: Population, Total. 2020. Available online: https://data.worldbank.org/indicator/SP.POP.TOTL (accessed on 27 December 2020).
| Country | Smartphone | Android | BT Mobile Apps | ||
|---|---|---|---|---|---|
| Installations | Estimated Active Users | ||||
| Australia | 105 | 44 | 71.42 | 27.6 | 17.4 |
| Austria | 117 | 78 | 50.25 | 9 | 5.7 |
| Belgium | 68 | 41 | 65.00 | 12.2 | 7.7 |
| Croatia | 71 | 59 | 50.84 | 2 | 1,3 |
| Czech Rep | 84 | 66 | 53.32 | 14 | 8.8 |
| Denmark | 115 | 55 | 71.03 | 34.8 | 21.9 |
| Finland | 140 | 97 | 59.65 | 45.3 | 28.5 |
| France | 79 | 51 | 58.35 | 9.5 | 6 |
| Germany | 90 | 61 | 45.50 | 34.5 | 21.7 |
| Ireland | 78 | 42 | 65.54 | 40.5 | 25.5 |
| Italy | 84 | 62 | 57.80 | 21.1 | 13.3 |
| Latvia | 96 | 69 | 52.45 | 9.1 | 5.7 |
| Netherlands | 82 | 48 | 63.09 | 25 | 15.8 |
| Portugal | 104 | 78 | 67.47 | 1 | 0.6 |
| Spain | 90 | 71 | 62.05 | 11.5 | 7.2 |
| Switzerland | 97 | 39 | 52.38 | 33.4 | 21.1 |
| United Kingdom | 85 | 40 | 66.64 | 36.05 * | 21.7 * |
| United States | 81 | 32 | 69.90 | 2.5 | 1.6 |
Publisher’s Note: MDPI stays neutral with regard to jurisdictional claims in published maps and institutional affiliations. |
© 2021 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).
Share and Cite
González-Cabañas, J.; Cuevas, Á.; Cuevas, R.; Maier, M. Digital Contact Tracing: Large-Scale Geolocation Data as an Alternative to Bluetooth-Based Apps Failure. Electronics 2021, 10, 1093. https://doi.org/10.3390/electronics10091093
González-Cabañas J, Cuevas Á, Cuevas R, Maier M. Digital Contact Tracing: Large-Scale Geolocation Data as an Alternative to Bluetooth-Based Apps Failure. Electronics. 2021; 10(9):1093. https://doi.org/10.3390/electronics10091093
Chicago/Turabian StyleGonzález-Cabañas, José, Ángel Cuevas, Rubén Cuevas, and Martin Maier. 2021. "Digital Contact Tracing: Large-Scale Geolocation Data as an Alternative to Bluetooth-Based Apps Failure" Electronics 10, no. 9: 1093. https://doi.org/10.3390/electronics10091093
APA StyleGonzález-Cabañas, J., Cuevas, Á., Cuevas, R., & Maier, M. (2021). Digital Contact Tracing: Large-Scale Geolocation Data as an Alternative to Bluetooth-Based Apps Failure. Electronics, 10(9), 1093. https://doi.org/10.3390/electronics10091093






