A Specification-Based IDS for Detecting Attacks on RPL-Based Network Topology
Abstract
:1. Introduction
2. Topology Attacks on RPL
- The Rank attack: after the attack is triggered, the malicious node changes the way it processes the DIO messages from other neighbors so that it will get the node with the worst rank as the preferred parent. This kind of attack will create un-optimized route for all the packets that go through the malicious nodes, and it also creates more traffic to the victim.
- The Sinkhole attack: the malicious node will propagate its rank with a good value, normally the same rank of the sink. As a result, its neighbors will select it as their preferred parent and send traffic to that node. The Sinkhole attack is often combined with the Selective Forwarding attack (a performance attack which is out of scope of this paper) to drop all the traffic attracted.
- The Local repair attack: after the attack is triggered, the malicious node starts broadcasting local repair messages periodically, though there is no problem with the link quality around the node. Other node upon receiving the local repair messages will need to recalculate the route that is related to the malicious nodes. This kind of attack creates more control overhead messages, as well as some packet dropping because of temporarily unavailable route.
- The Neighbor attack: after the attack is triggered, the malicious node will replicate any DIO messages that it receives and broadcast them again. The victims who receive this type of messages may think that it has a new neighbor, which is not in range. Moreover, if the new neighbor advertises a good rank then the victims may request it as the preferred parent and change the route to the out range neighbors.
- The DIS attack: after the attack is triggered, the malicious nodes will send the DIS messages periodically to its neighbors. The DIS messages can be sent two ways, which will lead to a different response from the receivers. The first way is to broadcast DIS, the receivers upon receive will have to reset the DIO timer as they realize that there is something with the topology around. The second way is to unicast this DIS message to all nodes in the neighbor list, the receivers upon receive will unicast DIO message to the sender. Both of these ways add more control overhead on the network.
3. A specification-Based IDS for RPL to Detect the Topology Attacks
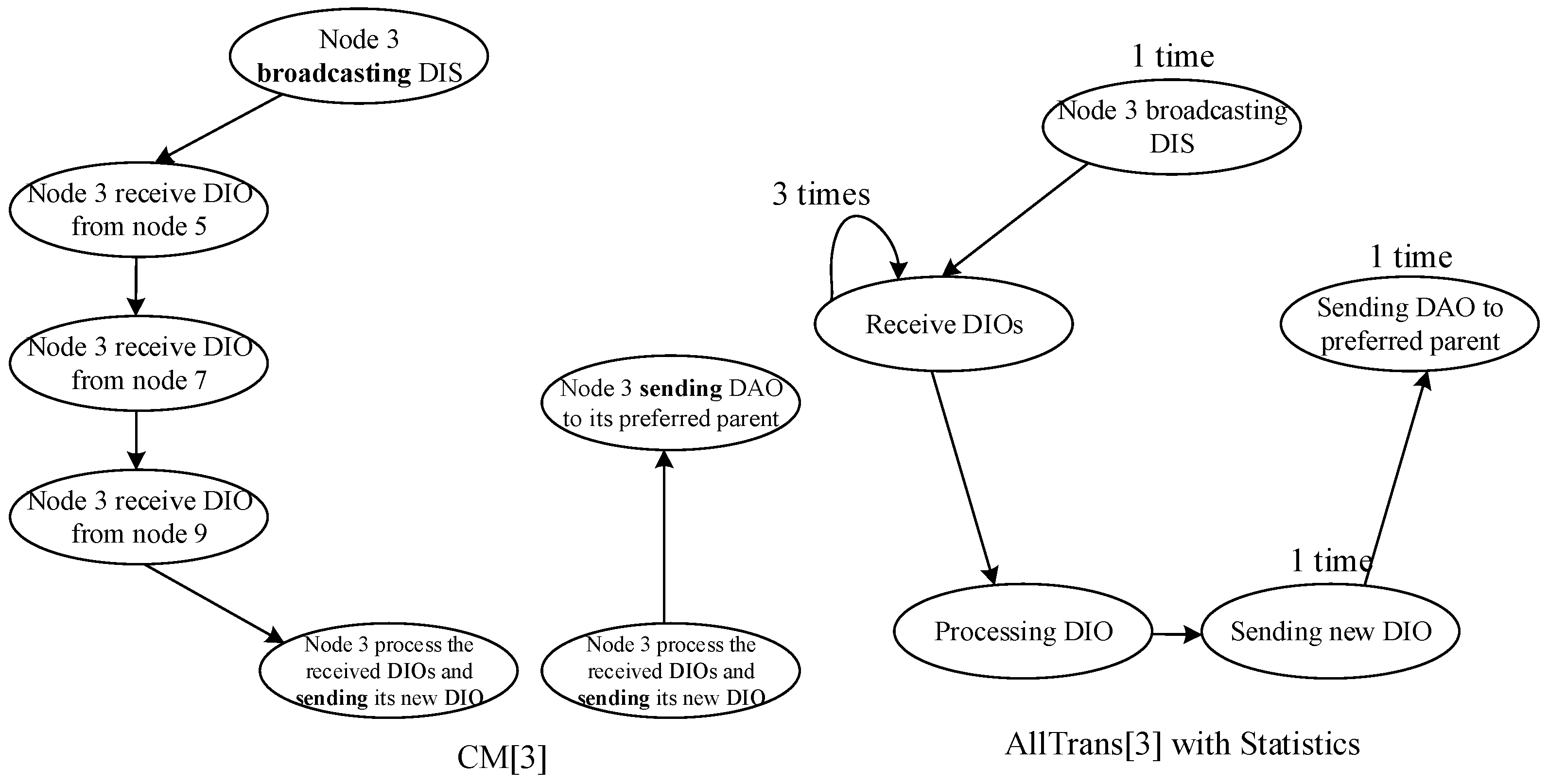
3.1. Profiling RPL
| Algorithm 1. Extracting states and transitions |
| Require: Trace file from simulation with marking relevant states |
| 1: for k = 1 to n do |
| 2: for i = 1 to Nk − 1 do |
| 3: PState = StateExtract(Ni) // Get previous state from Ni |
| 4: CState = StateExtract(Ni+1) // Get current state from Ni+1 |
| 5: CTran = NewTran(PState, CState) // Get current transition |
| 6: if CTran ∉ AllTrans[k] do |
| 7: AllTrans[k] = Add(AllTrans[k], CTran) // Add transition to list |
| 8: AllTransStatistic[k] = AddStatistic(AllTrans[k], CTran) // Add statistic |
| 9: else |
| 10: AllTransStatistic[k] = AddStatistic(AllTrans[k], CTran) // Add statistic |
| 11: end if |
| 12: end for |
| 13: end for |
| Algorithm 2. Form the specification-based IDS for RPL |
| Require: AllTrans[k], AllTransStatistic[k], k = 1,..., n |
| 1: FinalSpe = AllTrans[1] |
| 2: FinalSpeStatistic = AllTransStatistic[1] |
| 3: for k = 1 to n do |
| 4: FinalSpe = Merge(FinalSpe, AllTrans[k]) |
| 5: FinalSpeStatistic = Merge(FinalSpeStatistic, AllTransStatistic[k] |
| 6: end for |
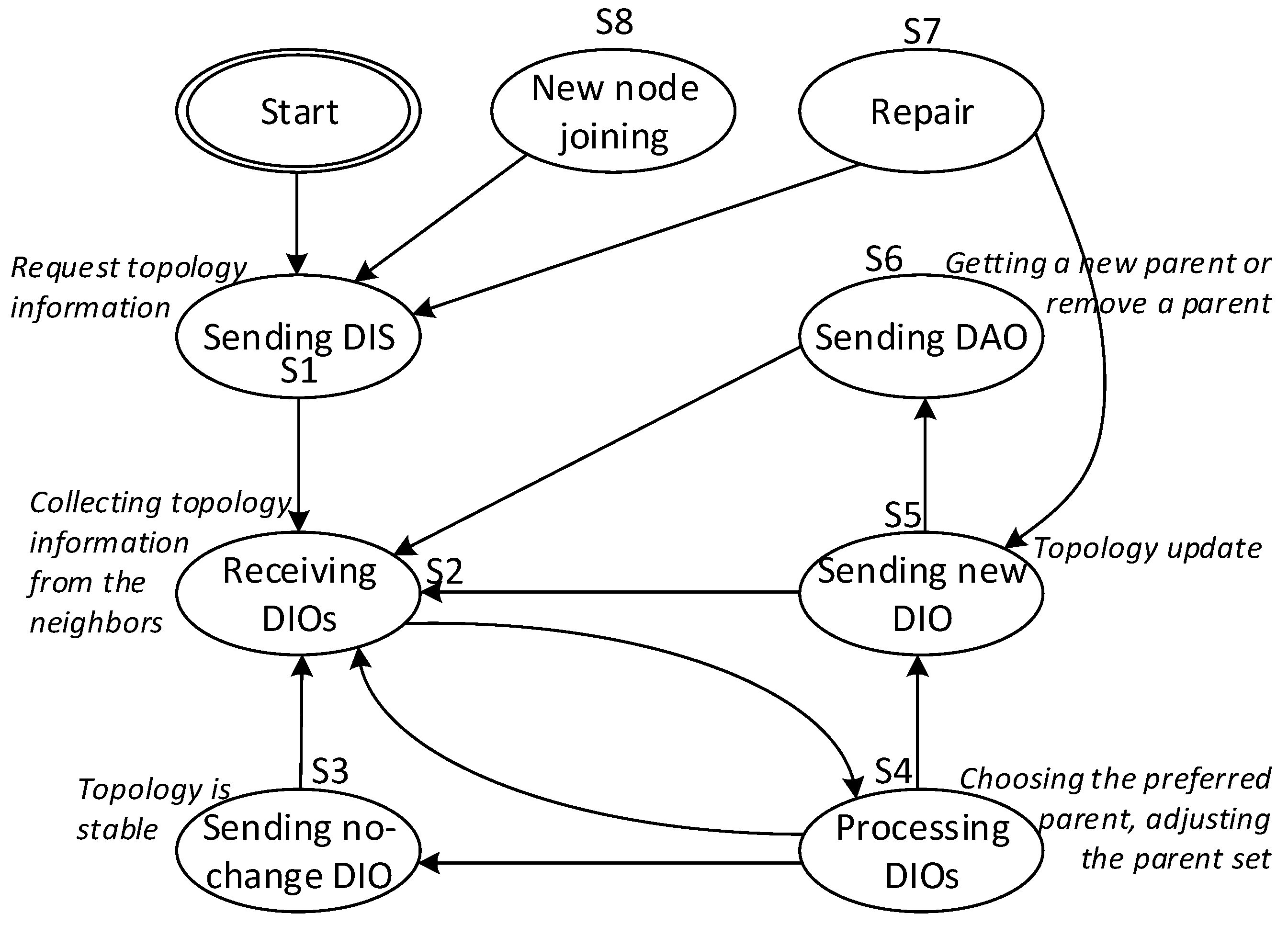
- (i)
- Nodes only move to the Sending DIS state when it first starts, joins, or involves in a link repair procedure. As a result, nodes only visit the Sending DIS state few times during the network performance.
- (ii)
- Nodes in the center tend to have more transitions to nodes in the border. The reasons are that center nodes have more neighbors than border nodes, while their neighbors are also more likely to update the routing information than the border nodes’ neighbors.
- (iii)
- In the processing DIOs state, nodes have to strictly follow the rank rule.
- (iv)
- After a long enough time of running, when the network topology becomes stable, the node will visit mostly the Sending no-change DIO state. However, such visit is not too often, because the DIO trickle time is always extended in a stable network.
- (v)
- The five states sending DIS, sending new DIO, sending DAO, repair, and new node joining indicate the instability of the network topology. When the node is in one of these states, the transitions are expected to happen more often, because the DIO trickle time is set to minimum.
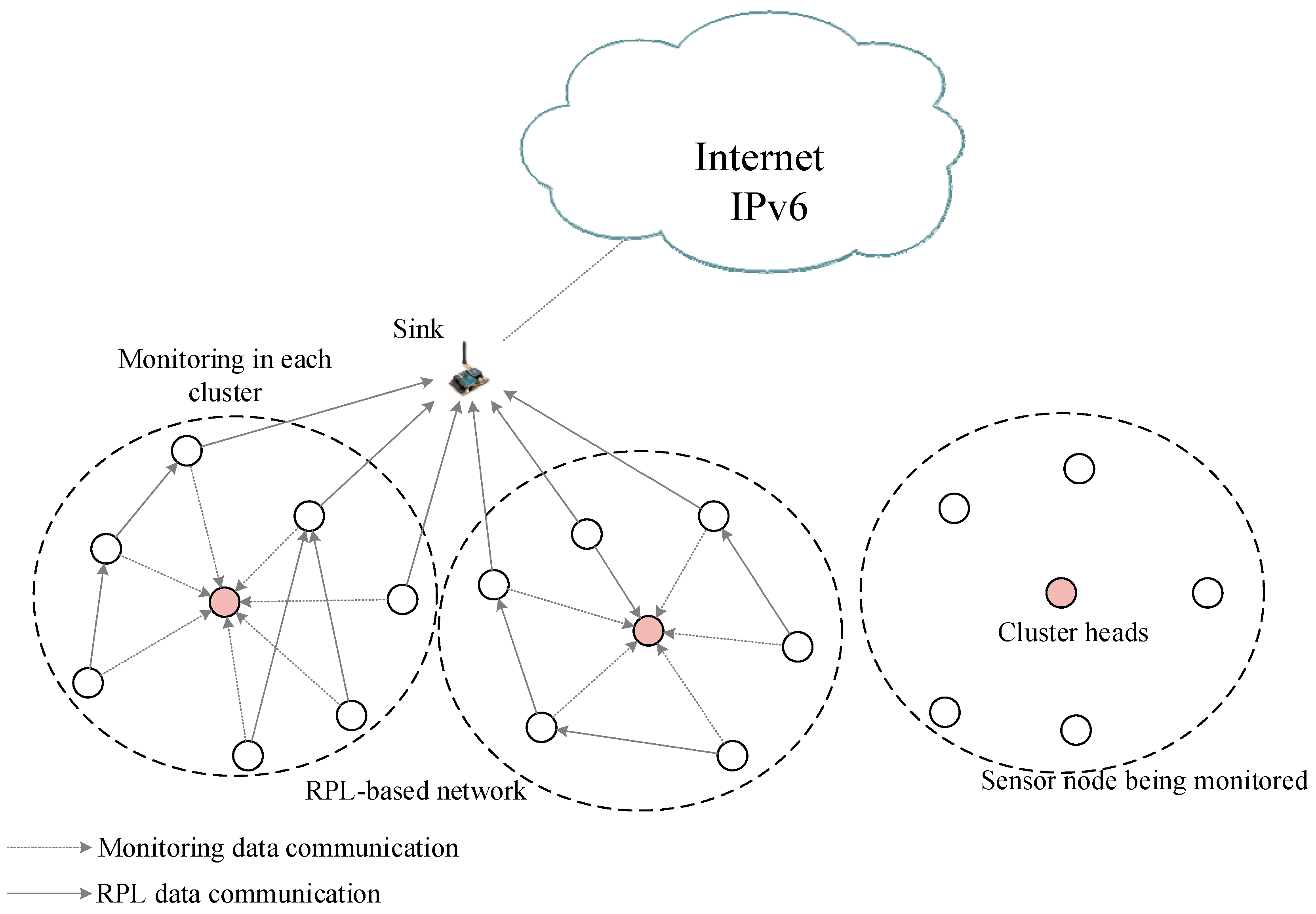
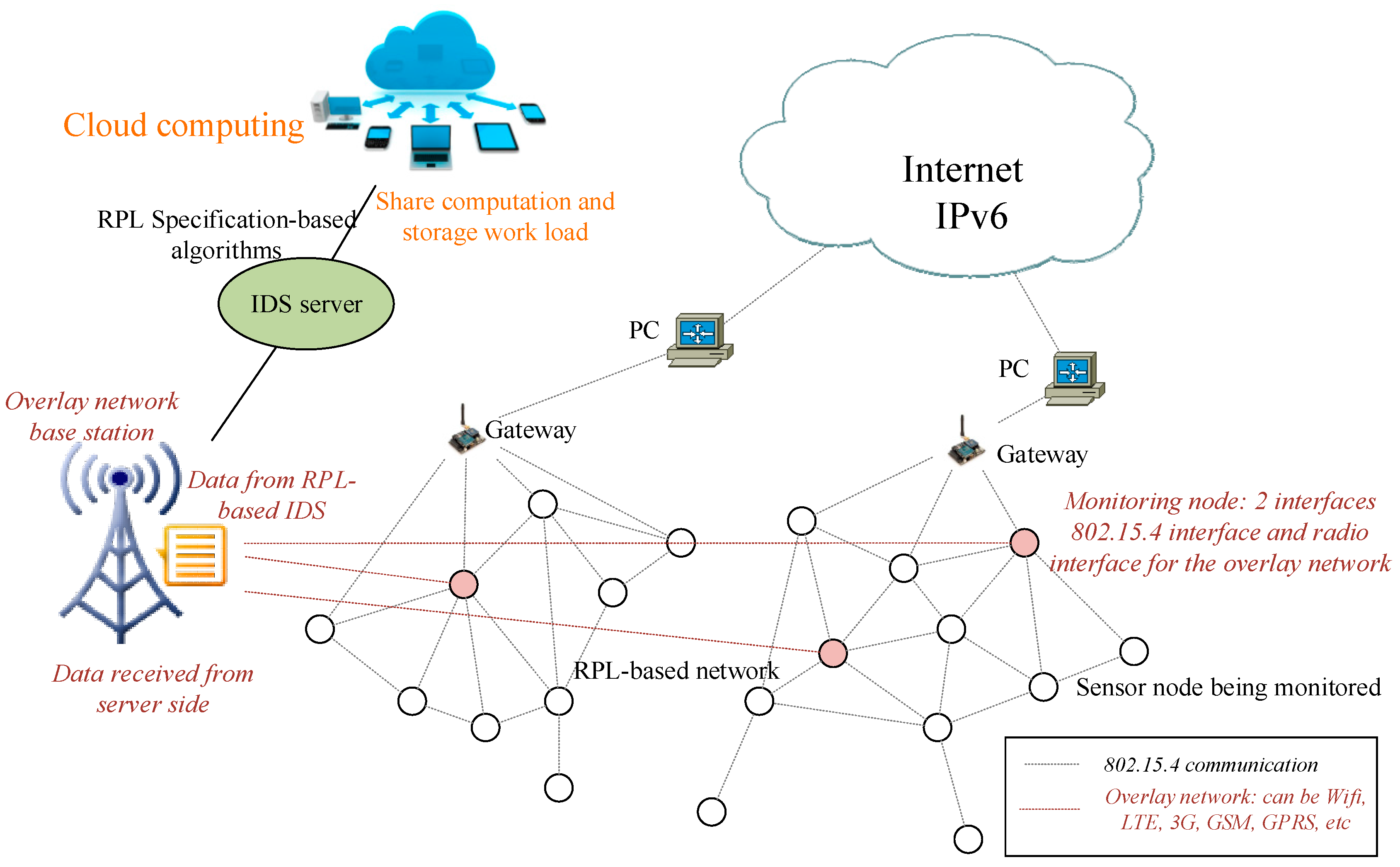
3.2. Design and Implementation of the Specification-Based IDS for RPL-Based Network
3.2.1. Placement of IDS Agents
3.2.2. IDS Data Collection
- DIS sequence, number of DIS received
- DIO sequence, number of DIO received
- List of neighbors, each neighbor has
- ○
- Node ID
- ○
- Rank
- ○
- The sequence of the DIO that provides this info
- ○
- DIS sequence, number of DIS received
- ○
- DAO sequence, number of DAO received, and a parent bit (if there is no DAO message sent, or if there is a DAO message require to remove the parent relationship, then the parent bit is 0, otherwise it will be set to 1)
- Preferred parent ID
3.2.3. Detection at the IDS Agent
- Module 1: Checking the DIS message, alarm if the received DIS is fake or sending too much.
- Module 2: Checking the sequence of DIO message, alarm if the received DIO is fake
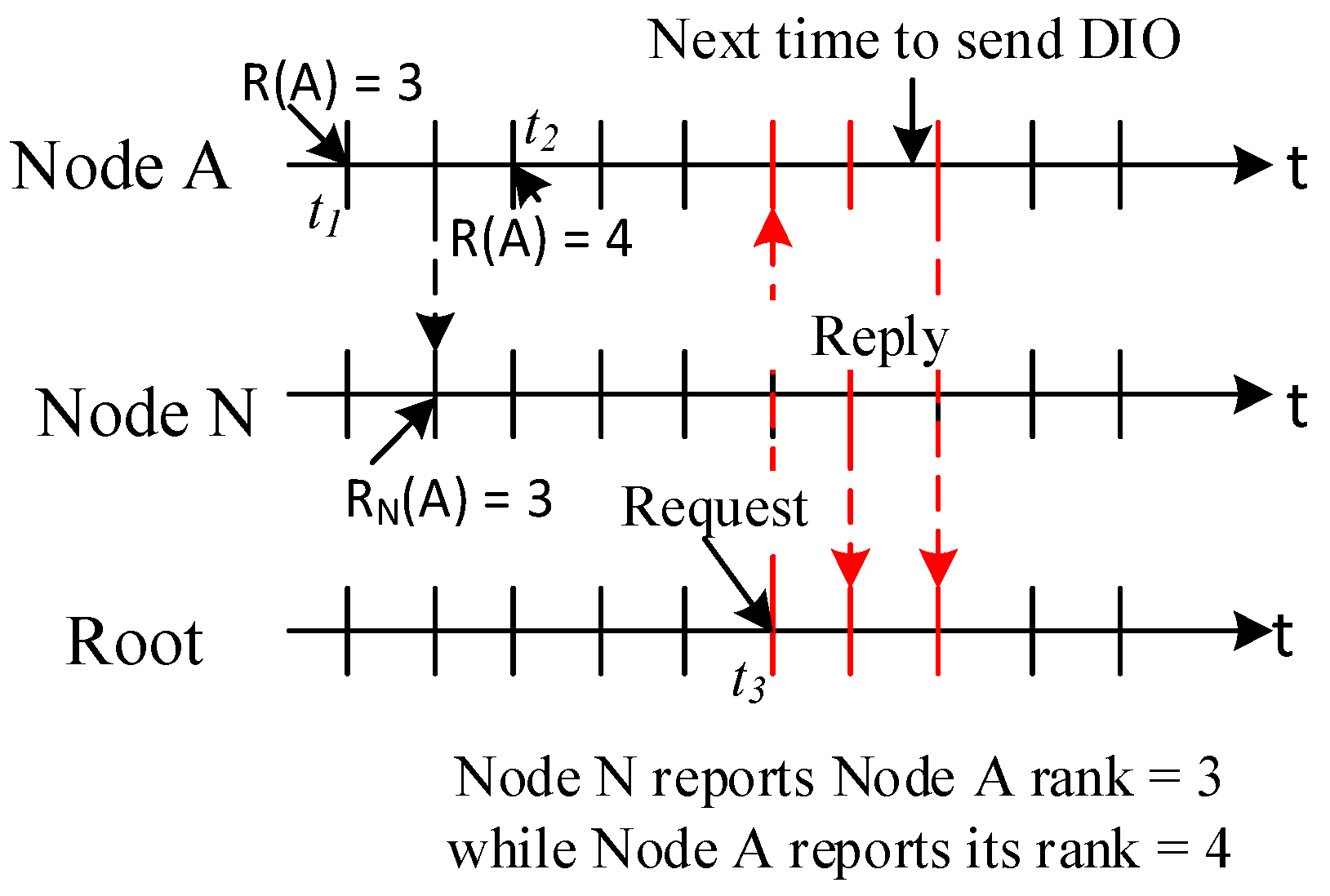
- Module 3: Checking the rank consistency, alarm if the rank of the member is different to the rank reported by its neighbors or the cluster head, given the same DIO sequence. Penalize the neighbors if they do not have the latest DIO message. Alarm if there is any DIO message reported by the neighbors or cluster head that has newer DIO sequence than the member itself
- Module 4: Check the rank rule between every pair of parent and child
- Module 5: Check the instability of the network area around a member through the relevant states and observations in Section 3.1. Penalize if there is any instability.
| Algorithm 3. Detecting topology attacks from cluster head view |
| Module 1: Check whether DIS message is illegitimate |
| 1: On receiving DIS { |
| 2: record SourceID, DIS_seq_new; |
| 3: DIS_count[SourceID]++; |
| 4: if DIS_seq_new ≤ DIS_seq_current then |
| 5: alarm fake DIS; |
| 6: else DIS_seq_current = DIS_seq_new |
| 7: end if |
| 8: if DIS_count[SourceID] > thresholdDIS_count then |
| 9: alarm DIS attack; |
| 10: end if } |
| Module 2: Check whether there is any fake DIO |
| 1: On receiving DIO { |
| 2: record SourceID, DIO_seq_new, rank; |
| 3: DIO_count[SourceID]++; |
| 4: if DIO_seq_new ≤ DIO_seq_current then |
| 5: alarm fake DIO; |
| 6: else DIO_seq_current = DIO_seq_new |
| 7: end if } |
| Module 3: Check the rank inconsistency |
| 1: After receiving reports from all of the members { |
| 2: for each Member in Cluster do { |
| 3: if Member.DIO_seq < CH.Member.DIO_seq then |
| 4: alarm fake DIO; |
| 5: end if |
| 6: for each Neighbour in Member.Neighbour do |
| 7: if Member.DIO_seq < Neighbour.Member.DIO_seq then |
| 8: alarm fake DIO; |
| 9: else if Member.DIO_seq < Neighbour.Member.DIO_seq then |
| 10: Neighbour.fault = Neighbour.fault + 0.5 //penalised |
| 11: else if Member.DIO_seq = Neighbour.Member.DIO_seq then |
| 12: if Member.rank != Neighbour.Member.Rank then |
| 13: alarm fake DIO; |
| 14: end if |
| 15: end if |
| 16: end for |
| 17: end for } } |
| Module 4: Check the rank rule |
| 1: for each Member in Cluster do |
| 2: if Member.rank + MinHopRankIncrease < Member.parent.rank then |
| 3: alarm rank attack; |
| 4: end if |
| 5: for each Neighbour in Member.Neighbour do { |
| 6: if Member.DAO.parent == 1 then |
| 7: if Member.rank – MinHopRankIncrease > Member.child.rank then |
| 8: alarm rank attack; |
| 9: end if |
| 10: end if |
| 11: end for |
| 12: end for } |
| Module 5: Check the stability of the network part which relate to a cluster member |
| //Setting the initial stability evaluation for each member in cluster |
| 1: for each Member in Cluster do |
| 2: Member.stability = thresholdstability |
| 3: end for |
| //Penalise if stability condition is observed to be not satisfied |
| 4: for each Member in Cluster { |
| 5: if IsRepairAfterPeriod then |
| 6: Member.stability -= 2 // penalised –2 on stability |
| 7: end if |
| 8: if IsChangeAfterPeriod(Member.DIO) || IsChangeAfterPeriod(Member.DAO) || IsNewNodeJoiningAfterPeriod then |
| 9: Member.stability -= 0.5 // penalised 0.5 on stability |
| 10: end if } |
| //Checking every period of time |
| 11: if IsCheckingPeriod then |
| 12: for each Member in Cluster do |
| 13: if Member.stability < 0 then |
| 14: alarm Member instability; |
| 15: end if |
| 16: if Member.fault > thresholdfault then |
| 17: alarm Member fault; // member fault is recorded in module 3 |
| 18: end if |
| 19: end for |
| 20: end if |
4. Evaluation Results and Discussion
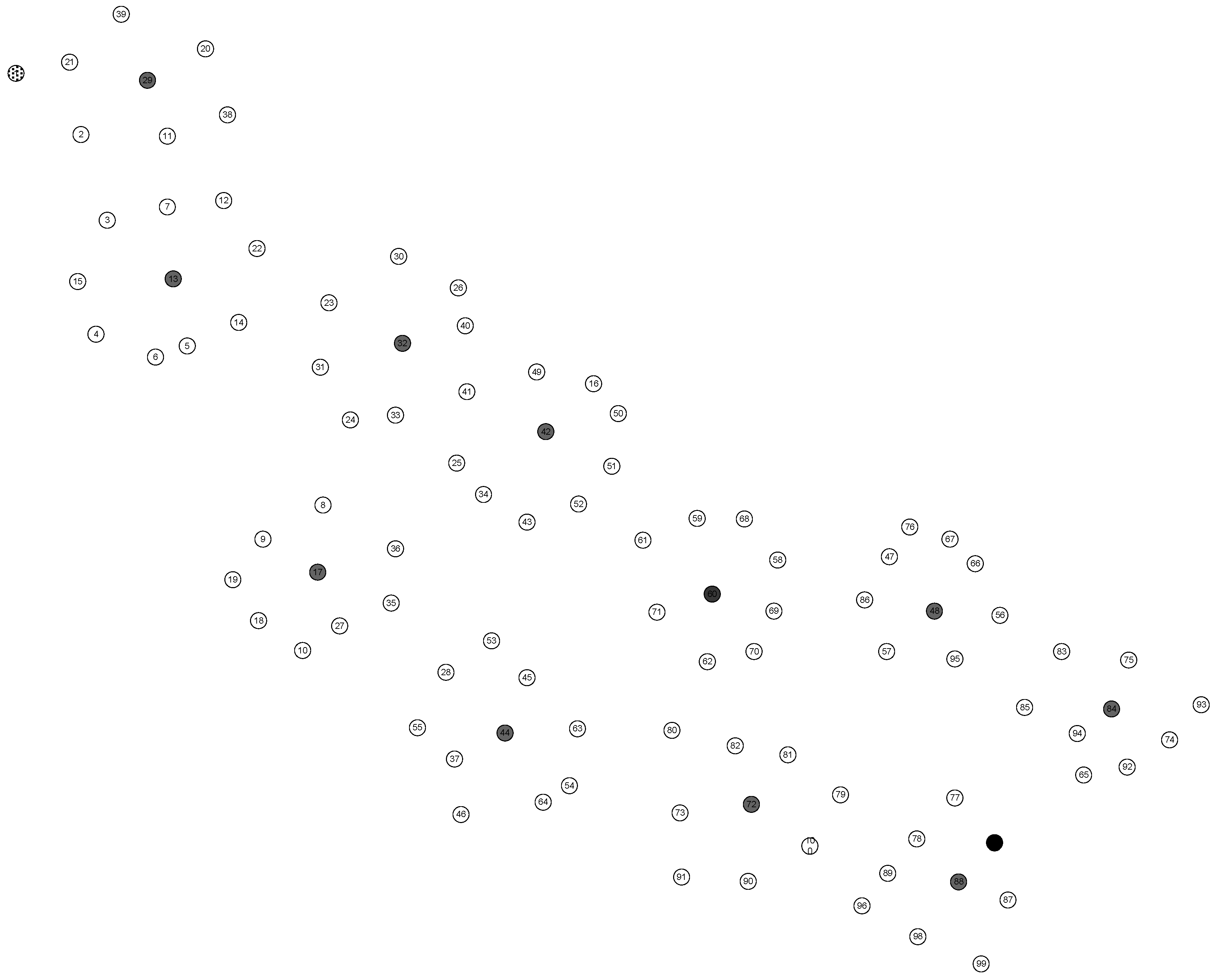
4.1. Simulation Set up
4.2. Evaluation Metrics
- True Positive (TP): is the total correctly detected malicious behaviours. This happens when the IDS correctly raise alert on a malicious event.
- False Positive (FP): happens when the IDS erroneously raises a false alarm over a legitimate behaviour in the network.
- True Negative (TN): happens when the IDS correctly judging a legitimate behaviour as normal.
- False Negative (FN): happens when the IDS erroneously judging a malicious event as normal.
4.3. Simulation Results and Discussion
4.3.1. Detection Efficency
4.3.2. Energy Efficiency
5. Further Considerations on Expanding the IDS Capability to Detect More Internal Threats
6. Conclusions
Acknowledgments
Author Contributions
Conflicts of Interest
Abbreviations
| 6LoWPAN | IPv6 over Low-power Wireless Personal Area Network |
| DAO | Destination Advertisement Object |
| DIO | Destination Oriented DAG Information Objective |
| DIS | DODAG Information Solicitation |
| FN | False Negative |
| FP | False Positive |
| FPR | False Positive Rate |
| LA | Local Repair Attack |
| LTE | Long-Term Evolution |
| NA | Neighbor Attack |
| IDS | Intrusion Detection System |
| IoT | Internet of Things |
| RA | Rank attack |
| RPL | Routing Protocol for Low Power and lossy network |
| SA | Sinkhole Attack |
| TN | True Negative |
| TP | True Positive |
| TPR | True Positive Rate |
References
- Winter, T.; Thubert, P.; Brandt, A.; Hui, J.; Kelsey, R.; Levis, P.; Pister, K.; Struik, R.; Vasseur, J.P.; Alexander, R. RPL: IPv6 Routing Protocol for Low-Power and Lossy Network; Internet Engineering Task Force (IETF): Fremont, CA, USA, 2012. [Google Scholar]
- Le, A.; Loo, J.; Lasebae, A.; Aiash, M.; Luo, Y. 6LoWPAN: A study on QoS security threats and countermeasures using intrusion detection system approach. Int. J. Commun. Syst. 2012, 25, 1189–1212. [Google Scholar] [CrossRef]
- Le, A.; Loo, J.; Lasebae, A.; Vinel, A.; Chen, Y.; Chai, M. The impact of rank attack on network topology of routing protocol for low-power and lossy networks. IEEE Sens. J. 2013, 13, 3685–3692. [Google Scholar] [CrossRef]
- Le, A.; Loo, J.; Luo, Y.; Lasebae, A. Specification-based IDS for securing RPL from topology attacks. In Proceedings of the 2011 IFIP Wireless Days (WD), Niagara Falls, ON, Canada, 10–12 October 2011; pp. 1–3.
- Le, A.; Loo, J.; Luo, Y.; Lasebae, A. The impacts of internal threats towards Routing Protocol for Low power and lossy network performance. In Proceedings of the 2013 IEEE Symposium on Computers and Communications (ISCC), Split, Croatia, 7–10 July 2013; pp. 789–794.
- Raza, S.; Wallgren, L.; Voigt, T. SVELTE: Real-time intrusion detection in the Internet of Things. Ad Hoc Netw. 2013, 11, 2661–2674. [Google Scholar] [CrossRef]
- Tang, J.; Huang, X.; Qian, J.; Viho, C. A FSM-based test sequence generation method for RPL conformance testing. In Proceedings of the Green Computing and Communications (GreenCom), 2013 IEEE and Internet of Things (iThings/CPSCom), IEEE International Conference on and IEEE Cyber, Physical and Social Computing, Beijing, China, 20–23 August 2013; pp. 591–597.
- Wallgren, L.; Raza, S.; Voigt, T. Routing attacks and countermeasures in the RPL-based Internet of Things. Int. J. Distrib. Sens. Netw. 2013, 2013, 794326. [Google Scholar] [CrossRef]
- Tsao, T.; Alexander, R.; Dohler, M.; Daza, V.; Lozano, A.; Richardson, M. A Security Threat Analysis for Routing Protocol for Low-Power and Lossy Networks (RPL). Available online: https://tools.ietf.org/html/draft-ietf-roll-security-threats-06 (accessed on 6 May 2016).
- Panos, C.; Xenakis, C.; Stavrakakis, I. A novel intrusion detection system for MANETs. In Proceedings of the 2010 International Conference on Security and Cryptography (SECRYPT), Athens, Greece, 26–28 July 2010; pp. 1–10.
- Tseng, C.-Y.; Balasubramanyam, P.; Ko, C.; Limprasittiporn, R.; Rowe, J.; Levitt, K. A specification-based intrusion detection system for AODV. In Proceedings of the 1st ACM Workshop on Security of Ad Hoc and Sensor Networks, Washington, DC, USA, 27–30 October 2003.
- Stakhanova, N.; Basu, S.; Wensheng, Z.; Wang, X.; Wong, J.S. Specification synthesis for monitoring and analysis of MANET protocols. In Proceedings of the 21st International Conference on Advanced Information Networking and Applications Workshops, AINAW ′07, Niagara Falls, ON, Canada, 21–23 May 2007; pp. 183–187.
- Contiki. Available online: http://www.contiki-os.org/ (accessed on 6 May 2016).
- Mitrokotsa, A.; Karygiannis, A. Intrusion detection techniques in sensor networks. In Wireless Sensor Network Security; Lopez, J., Zhou, J., Eds.; IOS press: Amsterdam, The Netherlands, 2008; pp. 251–272. [Google Scholar]
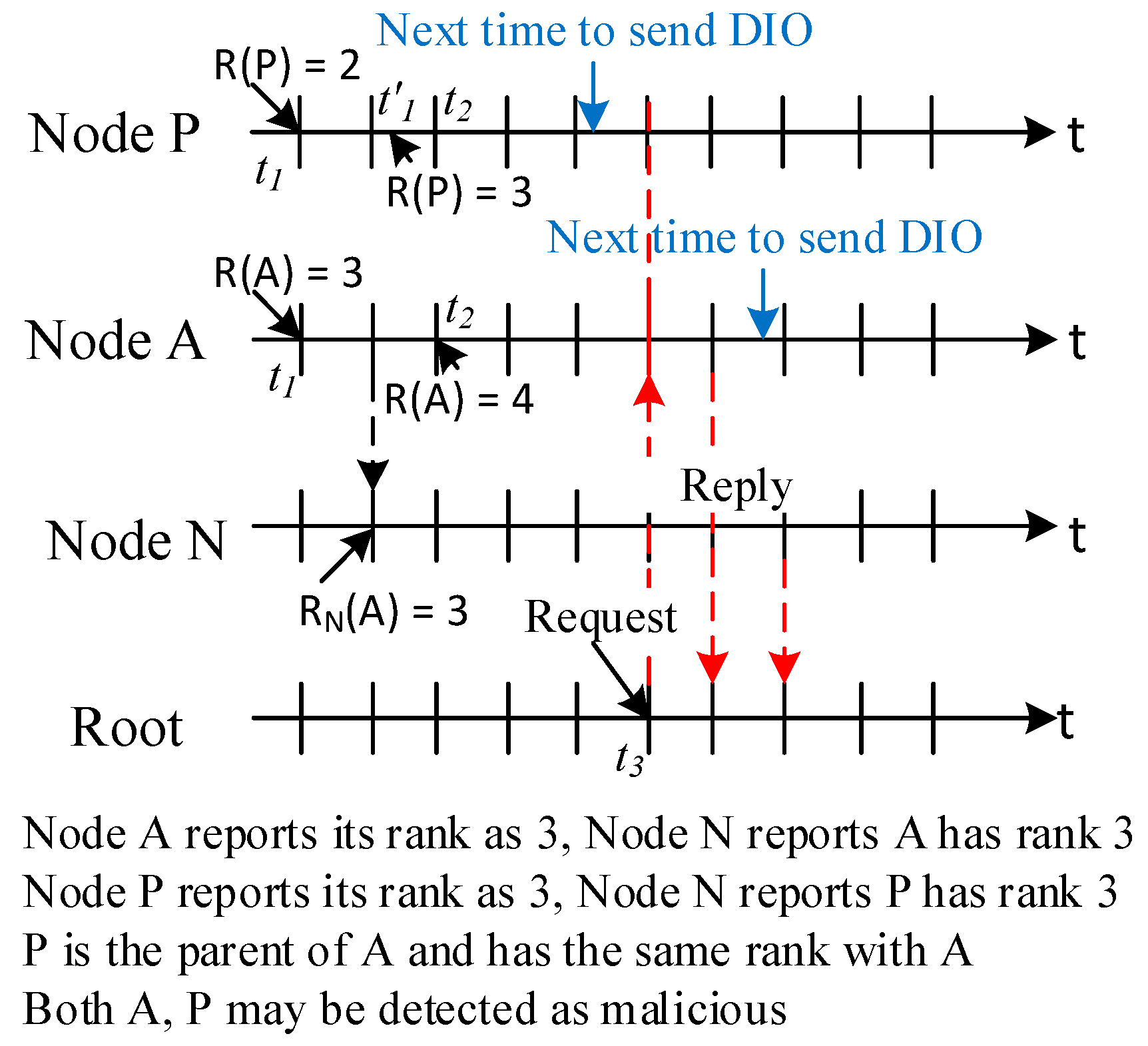
- Matsunaga, T.; Toyoda, K.; Sasase, I. Low false alarm rate RPL network monitoring system by considering timing inconstancy between the rank measurements. In Proceedings of the 2014 11th International Symposium on Wireless Communications Systems (ISWCS), Barcelona, Spain, 26–29 August 2014; pp. 427–431.
- Libelium. Wireless Interfaces Supported in Waspmote. Available online: http://www.libelium.com/products/waspmote/interfaces/ (accessed on 6 May 2016).
- Armbrust, M.; Fox, A.; Griffith, R.; Joseph, A.D.; Katz, R.; Konwinski, A.; Lee, G.; Patterson, D.; Rabkin, A.; Stoica, I.; et al. A view of cloud computing. Commun. ACM 2010, 53, 50–58. [Google Scholar] [CrossRef]
| Type of Attacks | Attack Descriptions | Misuse Goal |
|---|---|---|
| Rank attack | An attacker does not send packets to preferred parent | Route disruption—redirect traffic |
| Sinkhole attack | The attacker propagates the sink’s rank as its rank | Redirect traffic |
| Local repair | An attacker sends local repair periodically | Route disruption, resource consumption |
| Neighbor attack | An attacker forward the DIO messages to other neighbors without changing | False route, route disruption, resource consumption |
| DIS attack | The attackers send DIS messages with a fake IP address so let the other node have to generate the DIO messages so increase the overhead | Resource consumption |
| Threshold | Meaning |
|---|---|
| thresholdDIS_count | Alarm if a node visit the DIS state more than thresholdDIS_count in the monitoring time. |
| thresholdfault | Alarm if a node not updating info from the neighbours |
| thresholdinstability | Alarm if node visit the instability states S1, S5, S6, S7, S8 more than a thresholdinstability in the monitoring time |
| Parameters | Value |
|---|---|
| Simulation platform | Cooja Contiki 2.6 |
| Number of nodes | 99 senders, 1 sink |
| Number of cluster head | 11 |
| Number of attackers | 1 |
| Traffic model | Constant bit rate |
| Sending rate | 1 packet every 60 s |
| IDS require info every | 2 min |
| Simulation run time | 30 min |
| FP | TP | FN | TN | TPR (%) | FPR (%) | |
|---|---|---|---|---|---|---|
| RA | 0 | 88 | 0 | 7656 | 100 | 0 |
| SA | 0 | 88 | 0 | 7656 | 100 | 0 |
| NA | 0 | 88 | 0 | 7656 | 100 | 0 |
| FP | TP | FN | TN | TPR (%) | FPR (%) | |
|---|---|---|---|---|---|---|
| RA | 402 | 88 | 0 | 7254 | 100 | 5.25 |
| SA | 251 | 88 | 0 | 7405 | 100 | 3.28 |
| NA | 202 | 88 | 0 | 7454 | 100 | 2.64 |
| FP | TP | FN | TN | TPR (%) | FPR (%) | |
|---|---|---|---|---|---|---|
| LA | 51 | 76 | 12 | 7605 | 86.36 | 0.67 |
| DIS | 232 | 83 | 5 | 7424 | 94.32 | 3.03 |
| FP | TP | FN | TN | TPR (%) | FPR (%) | |
|---|---|---|---|---|---|---|
| LA | 519 | 88 | 0 | 7137 | 100 | 6.78 |
| DIS | 453 | 88 | 0 | 7203 | 100 | 5.92 |
© 2016 by the authors; licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC-BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Le, A.; Loo, J.; Chai, K.K.; Aiash, M. A Specification-Based IDS for Detecting Attacks on RPL-Based Network Topology. Information 2016, 7, 25. https://doi.org/10.3390/info7020025
Le A, Loo J, Chai KK, Aiash M. A Specification-Based IDS for Detecting Attacks on RPL-Based Network Topology. Information. 2016; 7(2):25. https://doi.org/10.3390/info7020025
Chicago/Turabian StyleLe, Anhtuan, Jonathan Loo, Kok Keong Chai, and Mahdi Aiash. 2016. "A Specification-Based IDS for Detecting Attacks on RPL-Based Network Topology" Information 7, no. 2: 25. https://doi.org/10.3390/info7020025
APA StyleLe, A., Loo, J., Chai, K. K., & Aiash, M. (2016). A Specification-Based IDS for Detecting Attacks on RPL-Based Network Topology. Information, 7(2), 25. https://doi.org/10.3390/info7020025






