Intelligent Adversary Placements for Privacy Evaluation in VANET
Abstract
1. Introduction
- A distance-based attacker placement scheme (DBAP).
- A novel speed-based attacker placement scheme (SBAP).
- A comprehensive comparative evaluation of different PMTs using the proposed schemes and random attacker placement, for different traffic conditions, using common metrics.
2. Privacy Management Techniques in VANET
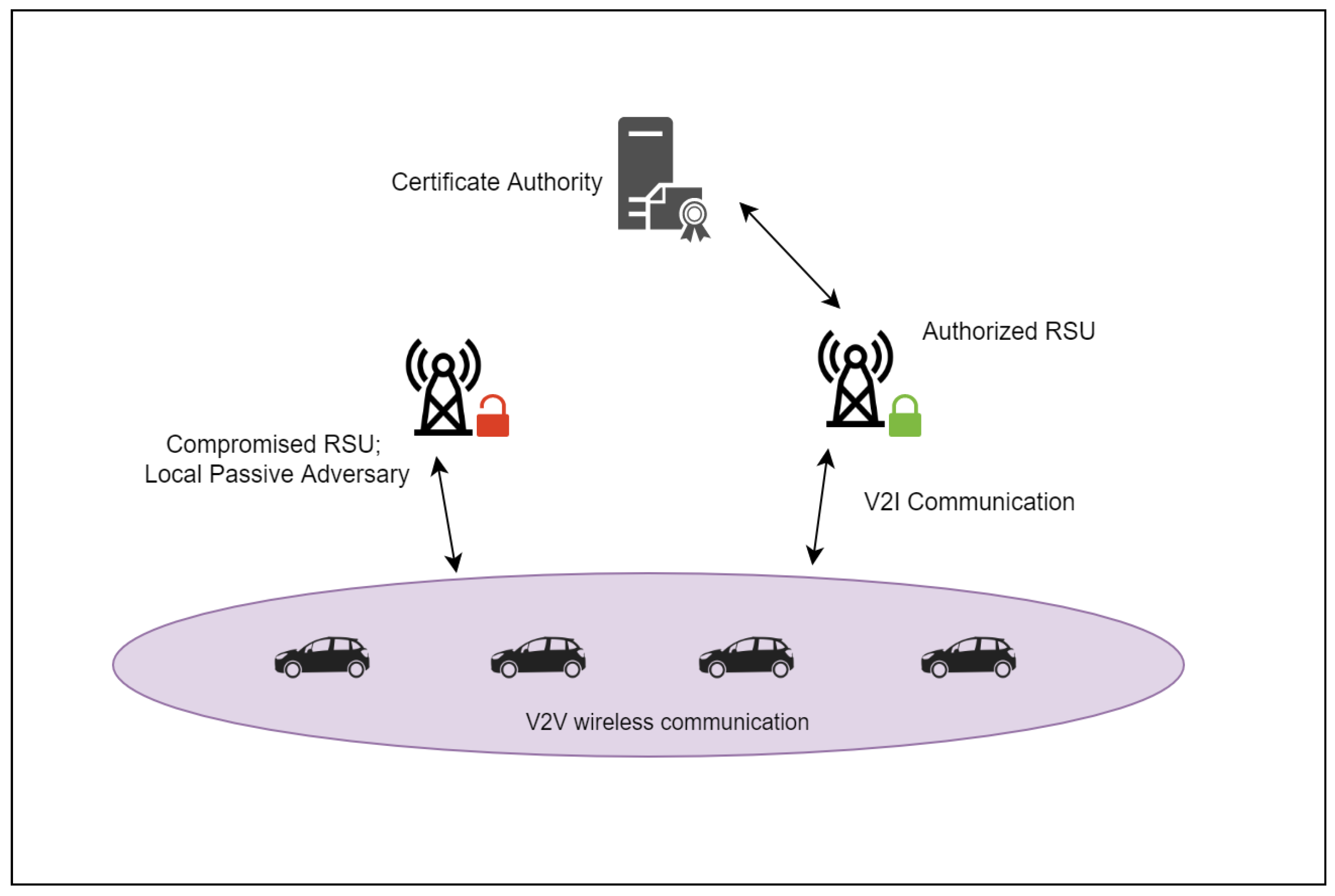
3. Network and Adversary Model
3.1. Network Model
3.2. Adversary Model
Factors Affecting Tracking Ability
- The number of vehicles changing pseudonyms simultaneously: A vehicle changing its pseudonym alone is relatively easy to recognize. Therefore, PMTs, where multiple vehicles cooperate to change pseudonyms together, tend to perform better. This depends on (i) the choice of PMT being used and (ii) the vehicle density. We have considered both factors in our simulations.
- Knowledge of PMT and traffic analysis: If the PMT is known to the attacker, the attacker can exploit this knowledge to place the listening stations strategically. In addition, stations can be placed in high-traffic areas, if traffic patterns are known, to eavesdrop on more vehicles. Certain PMTs lead to the repetition of pseudonyms, which can also be exploited by the adversary. We have compared the proposed schemes, which exploit knowledge of PMT and traffic patterns, with random placement strategy to investigate this factor.
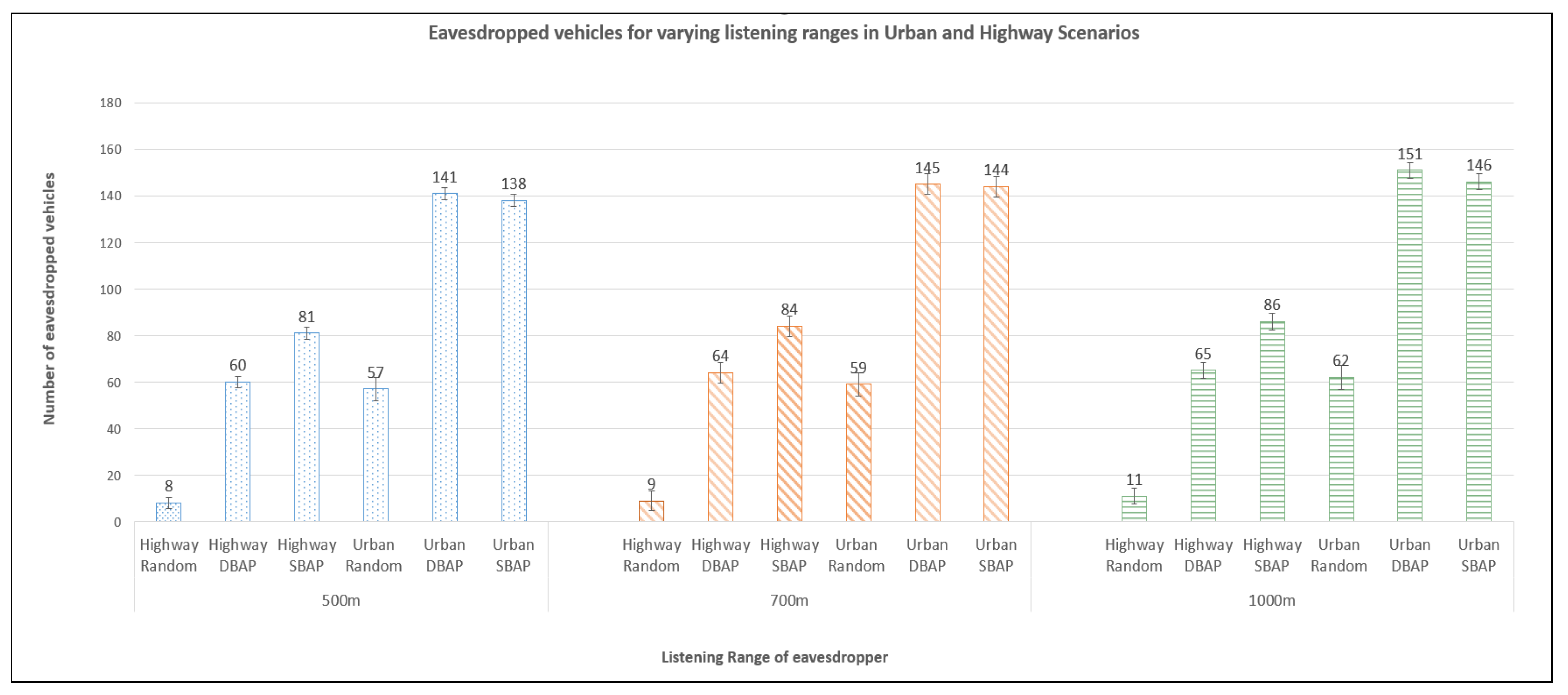
- Communication range of listening stations: Reducing the listening range of the attacking stations results in fewer BSMs reaching the eavesdropping stations and reduces successful vehicle tracking. We have considered different listening ranges to study the impact of this parameter on tracking success.
4. Intelligent Attacker Placement
- attacking stations can listen to beacons from many vehicles and
- pseudonym changes are likely to occur.
4.1. Distance-Based Attacker Placement
| Algorithm 1 Distance-based attacking algorithm |
| Input: Amount of available equipment for tracking the vehicles (n) and PN change frequency (f) |
| Output: Adversary spacing |
|
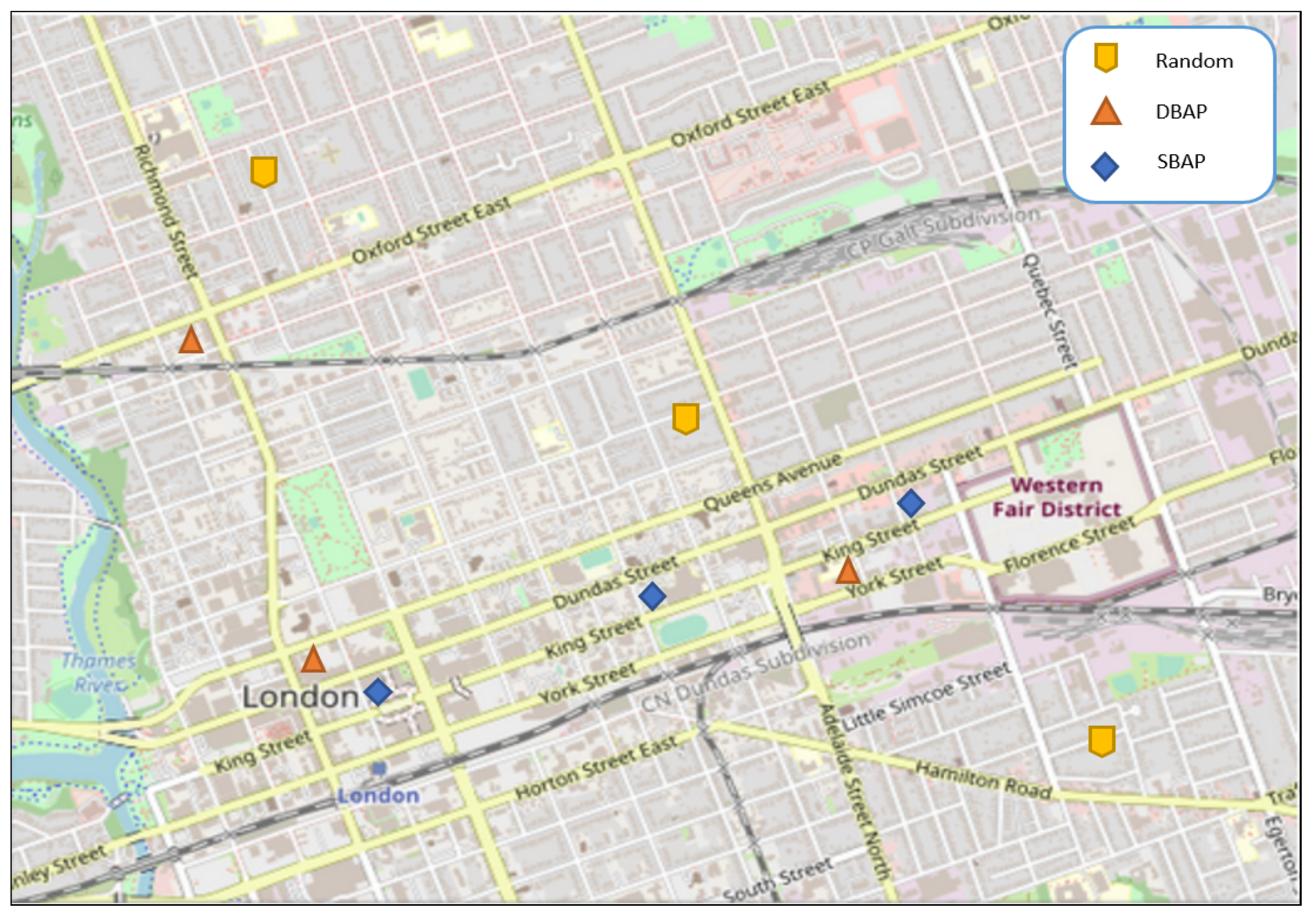
4.2. Speed-Based Attacker Placement
- A set of urban road segments where attackers will be placed based on TSI locations, where and is the ith road segment and
- a set of road segments (primarily highways, but may contain some urban roads as well), where attackers will be placed based on traffic congestion.
| Algorithm 2 Speed-based attacking algorithm |
| Input: Number (n) and communication range () of available attacking stations for vehicle tracking |
| Output: Adversary locations |
|
5. Simulation and Analysis
- Adversary model: Local passive adversary.
- Placement scheme: Random, DBAP, and SBAP.
- Road type: Urban or highway.
- Vehicle densities: 100, 200, and 300 vehicles.
- Number of attacking stations: 3.
- Listening range of attacking stations: 500 m, 700 m and 1000 m.
- Eavesdropping duration: 300 s.
Performance Metrics
- V: Set of all vehicles in the simulation.
- : Total number of vehicles in the simulation, i.e., .
- : Total number of vehicles that come within the listening range of at least one attacking station. We note that for a global adversary , while for a local adversary .
- : Set of distinct pseudonyms used by vehicle over a complete trip from source to destination.
- : Number of pseudonyms changes carried out by vehicle over a complete trip from source to destination.
- : Specific pseudonym in use by vehicle after the ith pseudonym change . corresponds to the initial pseudonym used by vehicle v. We note that if a vehicle v does not repeat any pseudonyms over its entire trip, then ; however if pseudonyms are repeated then .
- There is a total of successful tracking events associated with v and
- there are no unsuccessful tracking events associated with v.
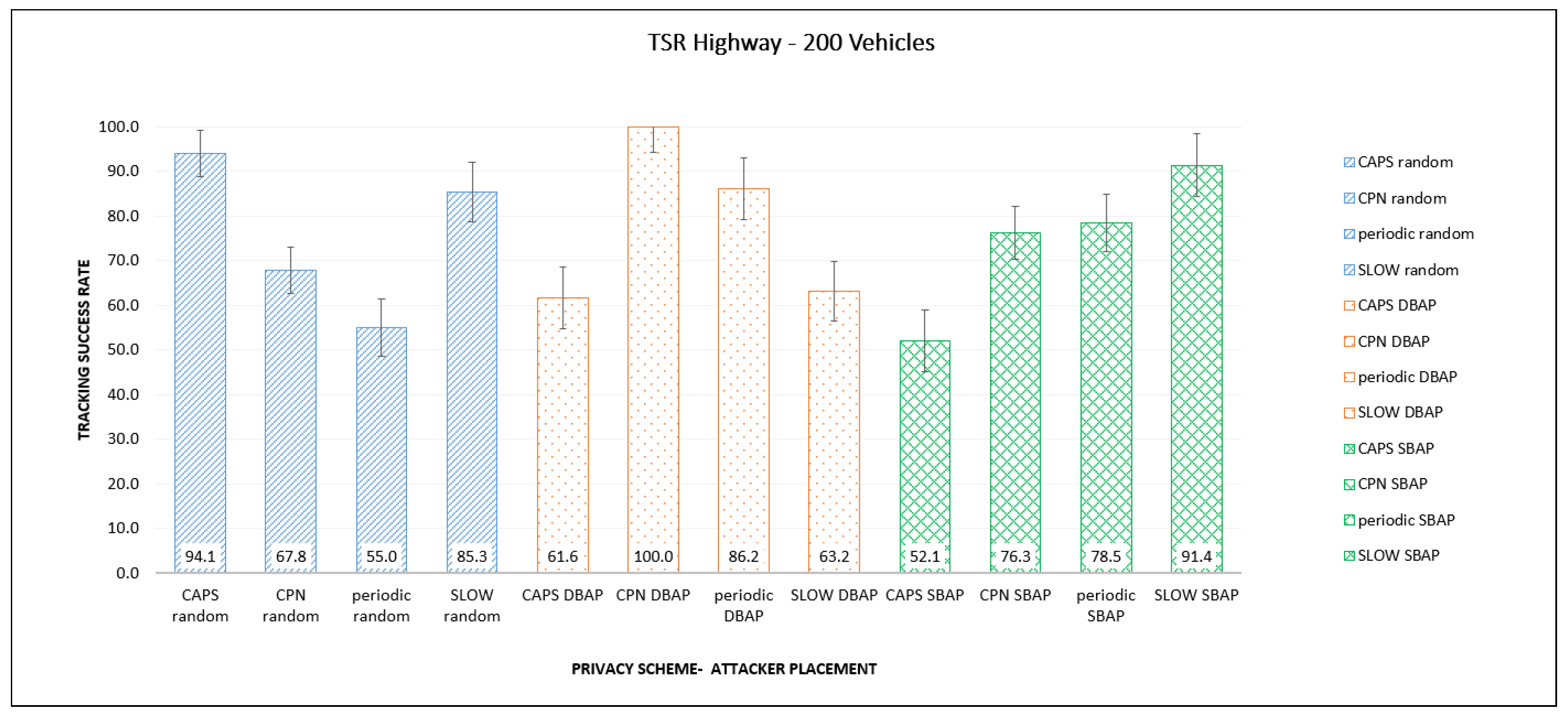
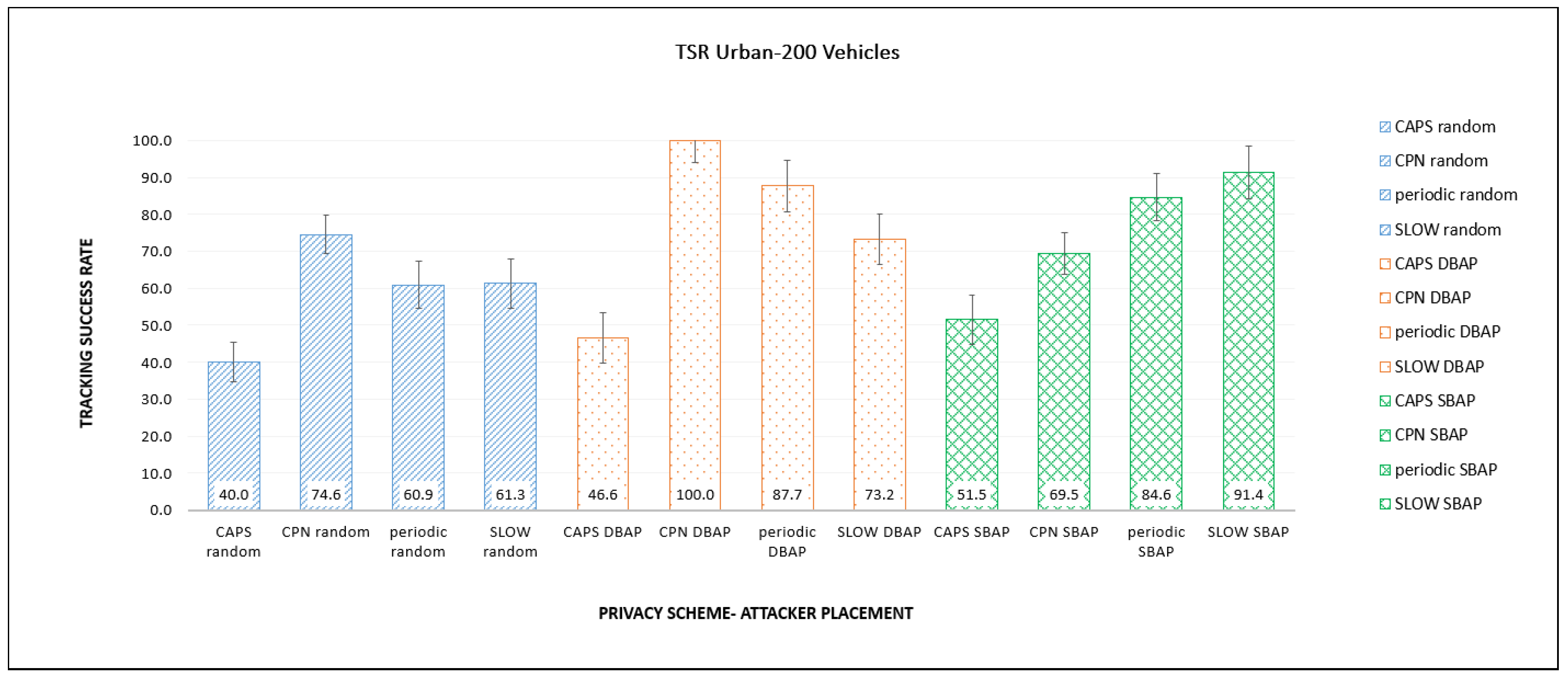
6. Results
6.1. Number of Eavesdropped Vehicles
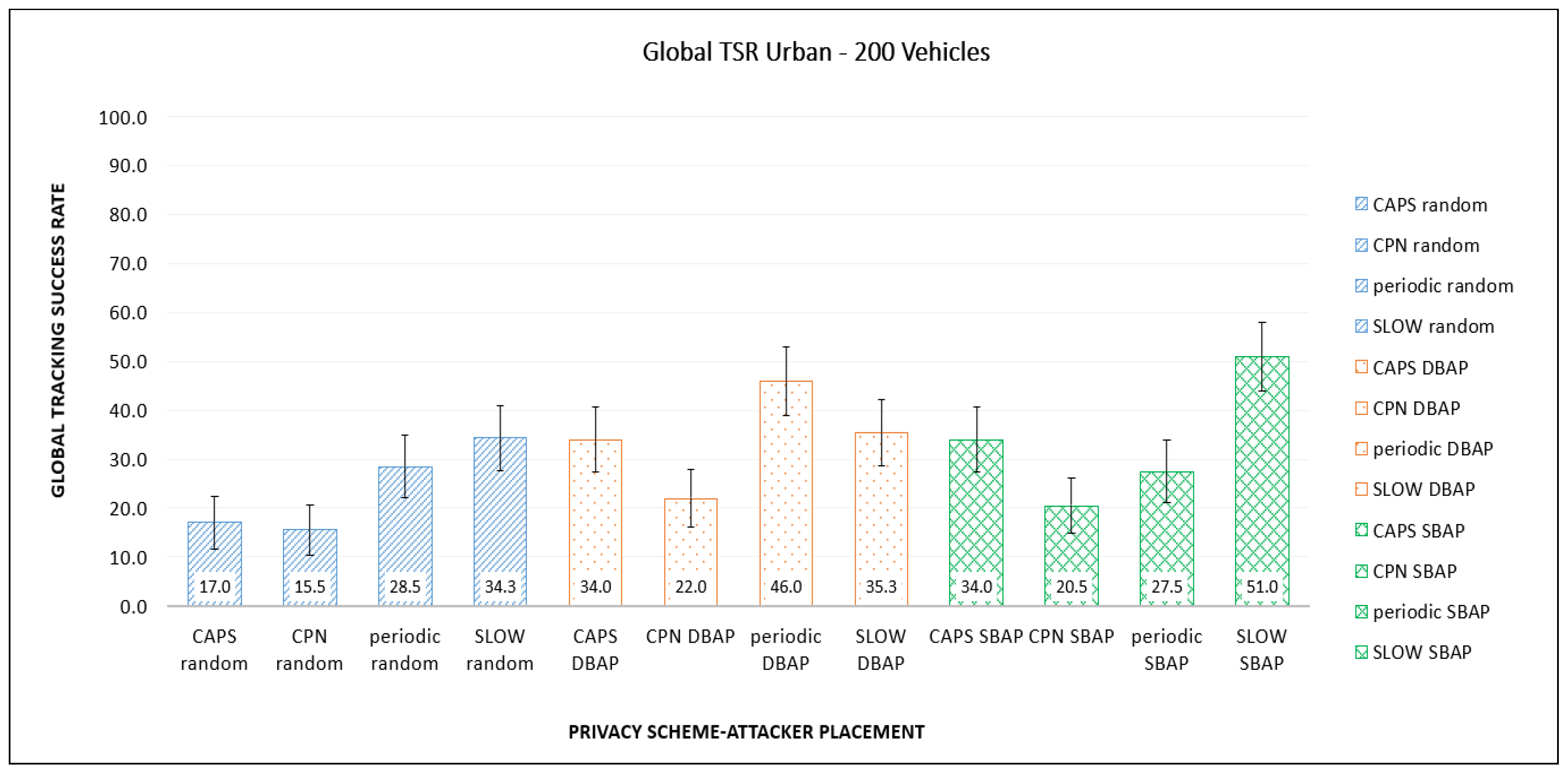
6.2. Results for the Base Case
6.3. Vehicle Density
- Different PMTs have different vulnerabilities and these can be exploited by the adversary by placing eavesdropping stations accordingly if the PMT being used is known.
- Intelligent adversary placement consistently results in more vehicles being eavesdropped and consequently higher tracking success rates by the adversary, compared to random placement.
- The effect of vehicle speed and vehicle density depend heavily on the PMT and the placement scheme being used. For example, SBAP is very effective with SLOW (which uses a speed-based trigger), since it was designed to target such PMTs.
7. Conclusions
Author Contributions
Funding
Acknowledgments
Conflicts of Interest
Abbreviations
| BSM | Basic Safety Message |
| CAPS | Context-Aware Pseudonym Scheme |
| CPN | Cooperative Pseudonym scheme based on number of Neighbors |
| DSRC | Dedicated Short Range Communication |
| DBAP | Distance-Based Attacker Placement |
| GTSR | Global Tracking Success Rate |
| HTS | High Traffic Section |
| OBU | On-Board Unit |
| PMT | Pseudonym Management Technique |
| PRD | Periodic pseudonym scheme |
| RSU | Roadside Unit |
| SBAP | Speed-based attacker placement |
| SCMS | Security Credential Management System |
| SLOW | Silence at LOW speeds |
| TSI | Traffic/Stop Intersection |
| TSR | Tracking success rate |
| VANET | Vehicular Ad-hoc Network |
| VIN | Vehicle identification number |
| V2V | Vehicle-to-Vehicle Communication |
| V2I | Vehicle-to-Infrastructure Communication |
References
- Harnstein, H.; Laberteaux, L.P. A tutorial survey on vehicular ad hoc networks. IEEE Commun. Mag. 2008, 46, 164–171. [Google Scholar] [CrossRef]
- IEEE Standard for Wireless Access in Vehicular Environments (WAVE)–Multi-Channel Operation. IEEE Std 1609.4-2016 (Revision of IEEE Std 1609.4-2006). Available online: https://standards.ieee.org/standard/1609_4-2016.html (accessed on 10 September 2020).
- Kenney, J. Dedicated Short-Range Communciations (DSRC) Standards in the United States. Proc. IEEE 2011, 99, 1162–1182. [Google Scholar] [CrossRef]
- DSRC Committee. Dedicated Short Range Communications (DSRC) Message Set Dictionary; SAE Std. J2735; SAE Int.: Warrendale PA, USA, 2009. [Google Scholar]
- Golle, P.A. On the anonymity of home/work location pairs. In Proceedings of the International Conference on the Pervasive Computing, Nara, Japan, 9–13 March 2009; Springer: Berlin/Heidelberg, Germany, 2009. [Google Scholar]
- Duckham, M.; Kulik, L. Location Privacy and Location-Aware Computing in Dynamic & Mobile GIS: Investigating Change in Space and Time; Drummond, J., Ed.; CRC Press: Boca Raton, FL, USA, 2006; pp. 34–51. [Google Scholar]
- Emara, K.; Woerndl, W.; Schlichter, J. Beacon-Based Vehicle Tracking in Vehicular Ad-Hoc Networks; Technical Report; Technische Universitat Munchen: Munchen, Germany, 2013. [Google Scholar]
- Gerlach, M. Assessing and improving privacy in VANETs. In Proceedings of the 4th Workshop ESCAR, Berlin, Germany, 14–15 November 2006; pp. 1–9. [Google Scholar]
- 1609.2-2016-IEEE Standard for Wireless Access in Vehicular Environments—Security Services for Applications and Management Messages. Available online: https://standards.ieee.org/standard/1609.2-2016.html (accessed on 10 February 2020).
- Buttyan, L.; Holczer, T.; Vajda, I. On the effectiveness of changing pseudonyms to provide location privacy in vanets. In European Workshop on Security in Ad-Hoc and Sensor Networks; Springer: Berlin/Heidelberg, Germany, 2007; pp. 129–141. [Google Scholar]
- Li, M.; Sampigethaya, K.; Huang, L.; Poovendran, R. Swing & swap: User-centric approaches towards maximizing location privacy. In Proceedings of the 5th ACM Workshop on Privacy in Electronic Society, Alexandria, VA, USA, 30 October 2006; pp. 19–28. [Google Scholar]
- Freudiger, J.; Raya, M.; Felegyhazi, P.P.; Papadimitratos, P.; Hubaux, J.P. Mix-zones for location privacy in vehicular networks. In Proceedings of the ACM Workshop on Wireless Networking for Intelligent Transportation Systems (WiNITS), Vancouver, BC, Canada, 14 August 2007; ACM: New York, NY, USA, 2007. [Google Scholar]
- Brecht, B.; Therriault, D.; Weimerskirch, A.; Whyte, W.; Kumar, V.; Hehn, T.; Goudy, R. A Security Credential Management System for V2X Communications. IEEE Trans. Intell. Transp. Syst. 2018, 19, 3850–3871. [Google Scholar] [CrossRef]
- Buttyan, L.; Holczer, T.; Weimerskirch, A.; Whyte, W. SLOW: A Practical pseudonym changing scheme for location privacy in VANETs. In Proceedings of the 2009 IEEE Vehicular Networking Conference (VNC), Tokyo, Japan, 28–30 October 2009; pp. 1–8. [Google Scholar]
- Song, J.-H.; Wong, V.W.; Leung, V.C. Wireless location privacy protection in vehicular ad-hoc networks. Mob. Netw. Appl. 2010, 15, 160–171. [Google Scholar] [CrossRef]
- Pan, Y.; Li, J. Cooperative pseudonym change scheme based on the number of neighbors in vanets. J. Netw. Comput. Appl. 2013, 36, 1599–1609. [Google Scholar] [CrossRef]
- Emara, K.; Wolfgang, W.; Johann, S. CAPS: Context-aware privacy scheme for VANET safety applications. In Proceedings of the 8th ACM Conference on Security & Privacy in Wireless and Mobile Networks, New York, NY, USA, 22 June 2015. [Google Scholar]
- Liao, J.; Li, J. Effectively changing pseudonyms for privacy protection in vanets. In Proceedings of the 10th International Symposium on Pervasive Systems, Algorithms, and Networks (ISPAN), Kaohsiung, Taiwan, 14–16 December 2009; pp. 648–652. [Google Scholar]
- Wasef, A.; Shen, X. Rep: Location privacy for vanets using random encryption periods. Mob. Netw. Appl. 2010, 15, 172–185. [Google Scholar] [CrossRef]
- Weerasinghe, H.; Fu, H.; Leng, S.; Zhu, Y. Enhancing unlinkability in vehicular ad hoc networks. In Proceedings of the 2011 IEEE International Conference on Intelligence and Security Informatics (ISI), Beijing, China, 10–12 July 2011; pp. 161–166. [Google Scholar]
- Ullah, I.; Wahid, A.; Shah, M.A.; Waheed, A. VBPC: Velocity based pseudonym changing strategy to protect location privacy of vehicles in VANET. In Proceedings of the 2017 International Conference on Communication Technologies (ComTech), Rawalpindi, Pakistan, 19–21 April 2017; pp. 132–137. [Google Scholar]
- Scheuer, F.; Fuchs, K.-P.; Federrath, H. A safety-preserving mix zone for vanets. In Proceedings of the International Conference on Trust, Privacy and Security in Digital Business, Toulouse, France, 29 August–2 September 2011; Springer: Berlin/Heidelberg, Germany, 2011; pp. 37–48. [Google Scholar]
- Eckhoff, D.; Sommer, C.; Gansen, T.; German, R.; Dressler, F. Strong and affordable location privacy invanets: Identity diffusion using time-slots and swapping. In Proceedings of the 2010 IEEE Vehicular Networking Conference (VNC), Jersey City, NJ, USA, 13–15 December 2010; pp. 174–181. [Google Scholar]
- Benarous, L.; Kadri, B.; Boudjit, S. Alloyed Pseudonym Change Strategy for Location Privacy in VANETs. In Proceedings of the 2020 IEEE 17th Annual Consumer Communications & Networking Conference (CCNC), Las Vegas, NV, USA, 11–14 January 2020; pp. 1–6. [Google Scholar] [CrossRef]
- Santos-Jaimes, L.M.; dos Santos Moreira, E. Pseudonym change strategy based on the reputation of neighboring vehicles in VANETs. DYNA 2019, 86, 157–166. [Google Scholar] [CrossRef]
- Liu, Z.; Zhang, L.; Ni, W.; Collings, I. Uncoordinated Pseudonym Changes for Privacy Preserving in Distributed Networks. IEEE Trans. Mob. Comput. 2019, 19, 1465–1477. [Google Scholar] [CrossRef]
- Boualouache, A.; Moussaoui, S. Tapcs: Traffic-awarepseudonym changing strategy for vanets. Peer-to-Peer Netw. Appl. 2017, 10, 1008–1020. [Google Scholar] [CrossRef]
- Singh, P.K.; Chourasiya, D.; Singh, A.; Nandi, S.K.; Nandi, S. CCAPS: Cooperative Context Aware Privacy Scheme for VANETs. In Proceedings of the 2019 IEEE 90th Vehicular Technology Conference (VTC2019-Fall), Honolulu, HI, USA, 22–25 September 2019; pp. 1–5. [Google Scholar]
- Zeng, M.; Xu, H. Mix-Context-Based Pseudonym Changing Privacy Preserving Authentication in VANETs. Mob. Inf. Syst. 2019, 2019, 3109238. [Google Scholar] [CrossRef]
- Zhao, Z.; Ye, A.; Meng, L.; Zhang, Q. Pseudonym Changing for Vehicles in VANETs: A Game-Theoretic Analysis Based Approach. In Proceedings of the 2019 International Conference on Networking and Network Applications (NaNA), Daegu, Korea, 10–13 October 2019; pp. 70–74. [Google Scholar] [CrossRef]
- Yang, M.; Feng, Y.; Fu, X.; Qian, Q. Location privacy preserving scheme based on dynamic pseudonym swap zone for Internet of Vehicles. Int. J. Distrib. Sens. Netw. 2019. [Google Scholar] [CrossRef]
- Li, W.; Song, H. ART: An attack-resistant trust management scheme for securing vehicular ad hoc networks. IEEE Trans. Intell. Transp. Syst. 2015, 17, 960–969. [Google Scholar] [CrossRef]
- Wang, J.; Hari, S. Detecting Compromised Certificate Authority. U.S. Patent No. 9,686,081, 20 January 2017. [Google Scholar]
- Emara, K. Poster: “Prext: Privacy extension for veins vanet simulator”. In Proceedings of the Vehicular Networking Conference (VNC), Columbus, OH, USA, 8–10 December 2016. [Google Scholar]
- Saini, I.; Saad, S.; Jaekel, A. Attacker Placement for Detecting Vulnerabilities of Pseudonym Change Strategies in VANET. In Proceedings of the 1st International Workshop on Dependable Wireless Communications (DEWCOM), Chicago, IL, USA, 27–30 August 2018. [Google Scholar]
- Saini, I.; Saad, S.; Jaekel, A. Speed Based Attacker Placement for Evaluating Location Privacy in VANET. In Ad Hoc Networks ADHOCNETS 2018; Springer: Cham, Switzerland, 2018. [Google Scholar]
- Wiedersheim, B.; Ma, Z.; Kargl, F.; Papadimitratos, P. Privacy in inter-vehicular networks: Why simple pseudonym change is not enough. In Proceedings of the 2010 Seventh International Conference on Wireless On-Demand Network Systems and Services (WONS), Kranjska Gora, Slovenia, 3–5 February 2010; pp. 176–183. [Google Scholar]
- Kalman, R. A new approach to linear filtering and prediction problems. Trans. ASME J. Basic Eng. 1960, 82, 35–45. [Google Scholar] [CrossRef]
- Fitzgerald, R.J. Development of practical pda logic for multitarget tracking by microprocessor. In Proceedings of the American Control Conference, Seattle, WA, USA, 18–20 June 1986; pp. 889–898. [Google Scholar]
- Google Maps Platform—Traffic Layer. Available online: https://developers.google.com/maps/documentation/javascript/examples/layer-traffic (accessed on 8 May 2020).
- Sommer, C.; German, R.; Dressler, F. Bidirectionally coupled network and road traffic simulation for improved IVC analysis. IEEE Trans. Mob. Comput. 2011, 10, 3–15. [Google Scholar] [CrossRef]
- Varga, A.; Rudolf, H. An overview of the OMNeT++ simulation environment. In Proceedings of the 1st Inter-National Conference on Simulation Tools and Techniques for Communications, Networks and Systems and Workshops, Marseille, France, 3–7 March 2008; ICST(Institute for Computer Sciences, Social-Informatics and Telecommunications Engineering): Brussels, Belgium, 2008. [Google Scholar]
- Krajzewicz, D.; Erdmann, J.; Behrisch, M.; Bieker, L. Recent development and applications of SUMO-Simulation of Urban MObility. Int. J. Adv. Syst. Meas. 2012, 5, 55031451. [Google Scholar]
- OpenStreetMap. Available online: https://www.openstreetmap.org/copyright (accessed on 6 June 2019).


| PMTs/Triggers | Time-Based | Speed-Based | Traffic-Based | Context-Based |
|---|---|---|---|---|
| Periodical [13] | ✓ | |||
| SLOW [14] | ✓ | |||
| Cooperative [16] | ✓ | |||
| Dynamic Zone based [31] | ✓ | |||
| Jaimes et al. [25] | ✓ | |||
| Liu et al. [26] | ✓ | |||
| CAPS [17] | ✓ | |||
| Swing and Swap [11] | ✓ | |||
| Song et al. [15] | ✓ | |||
| Boualouache et al. [27] | ✓ | |||
| CCAPS [28] | ✓ | ✓ | ||
| Mix-Context based [29] | ✓ | |||
| Zhao et al. [30] | ✓ | |||
| Benarous et al. [24] | ✓ |
| Number of Vehicles | Random | DBAP | SBAP | |||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|
| CAPS | CPN | PRD | SLOW | CAPS | CPN | PRD | SLOW | CAPS | CPN | PRD | SLOW | |
| 100 | 17 | 20 | 30.5 | 11.3 | 25 | 48 | 45.5 | 32.7 | 25 | 20 | 38.5 | 45.7 |
| 200 | 17 | 15.5 | 28.5 | 34.3 | 34 | 22 | 46 | 35.3 | 34 | 20.5 | 27.5 | 51 |
| 300 | 30 | 15.5 | 11.3 | 34.7 | 48 | 17 | 47 | 25.3 | 39 | 17.5 | 27 | 51.3 |
| Number of Vehicles | Random | DBAP | SBAP | |||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|
| CAPS | CPN | PRD | SLOW | CAPS | CPN | PRD | SLOW | CAPS | CPN | PRD | SLOW | |
| 100 | 16 | 18 | 33 | 11 | 24 | 46.5 | 42.5 | 36 | 24 | 25 | 36 | 49.33 |
| 200 | 16 | 15.5 | 25.5 | 33 | 40 | 20 | 41 | 35.3 | 38 | 22.5 | 28 | 44 |
| 300 | 37 | 15.5 | 10.7 | 33.7 | 54 | 18 | 47 | 25.7 | 38 | 21 | 25.3 | 43.3 |
© 2020 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Saini, I.; St. Amour, B.; Jaekel, A. Intelligent Adversary Placements for Privacy Evaluation in VANET. Information 2020, 11, 443. https://doi.org/10.3390/info11090443
Saini I, St. Amour B, Jaekel A. Intelligent Adversary Placements for Privacy Evaluation in VANET. Information. 2020; 11(9):443. https://doi.org/10.3390/info11090443
Chicago/Turabian StyleSaini, Ikjot, Benjamin St. Amour, and Arunita Jaekel. 2020. "Intelligent Adversary Placements for Privacy Evaluation in VANET" Information 11, no. 9: 443. https://doi.org/10.3390/info11090443
APA StyleSaini, I., St. Amour, B., & Jaekel, A. (2020). Intelligent Adversary Placements for Privacy Evaluation in VANET. Information, 11(9), 443. https://doi.org/10.3390/info11090443






