Attacker Behaviour Forecasting Using Methods of Intelligent Data Analysis: A Comparative Review and Prospects
Abstract
1. Introduction
- Techniques based on attack graph analysis.
- Techniques based on hidden Markov model.
- Techniques based on fuzzy inference.
- Techniques based on attributing cyber attacks using intelligent data mining techniques including neural networks, statistics, and so on.
- Seven works explicitly use different attacker profiles, seventeen define dimensions, and the vast majority use actions to characterize the attacker. Just two works define a system model and perform risk analysis without explicitly considering an attacker model. This shows the trend of defining an attacker model to perform security analysis of CPS and, at the same time, there exist various ways to model the attacker.
- All the papers share the same actions or the same intuitions on the attackers, but they apply those actions to different definitions of attacker models.
- Different works propose different attacker profiles. The boundaries between the different attacker profiles are not well defined, thus it is hard to classify a specific attacker as one specific profile. The authors outline the following six types of attackers based on related research: (1) a basic user [10,11] (also known as script kiddie, unstructured hacker, hobbyist, or cracker) uses already established and potentially automated techniques to attack a system, and has average access to hardware, software, and Internet connectivity; (2) an insider [11,12,13,14] (disgruntled employees or social engineering victims) can cause damage to the target depending on the employment position or the system privileges he/she owns (e.g., user, supervisor, administrator)—this type is of high importance for systems that are mainly protected through air-gaps between the system network and the outside world (often used in CPS); (3) a hacktivist [10,11,12] aims to promote a political agenda, often related to freedom of information (e.g., Anonymous); (4) a terrorist [11,12,13], also known as cyber-terrorist, is a politically motivated attacker who uses information technology to cause severe disruption or widespread fear [15,16]; (5) a cybercriminal [10,11,12,13,14] (sometimes called black hat hacker or structured hacker) is an attacker with extensive security knowledge and skills, he/she takes advantage of known vulnerabilities, and potentially has the knowledge and intention of finding new zero-day vulnerabilities, his/her goals can range from blackmailing to espionage (industrial, foreign) or sabotage; (6) a nation-state [10,11,12,13] is an attacker sponsored by a nation/state, and his/her targets are usually public infrastructure systems, mass transit, power or water systems, and general intelligence.
- Finally, the authors outlined nine common parameters that are used to generate metrics. Examples of metrics are as follows:
- tools (resources) available, also known as attacklets, or actions in the abstract definition of the attacker model—these define which types of tools are available to the attacker;
- camouflage or preference to stay hidden—expresses the aim and/or the ability of the attacker to not be tracked down after or while performing an attack;
- distance to the CPS—an attacker can be located in another country, within WiFi range, or possibly have direct access to the system.
- Comparative analysis and classification of existing techniques for attackers’ behaviour forecasting and used characteristics of attackers.
- Existing challenges and solutions in the considered area.
- A common approach to attack forecasting task implementation that specifies further research steps and is the basis for the development of an attacker behaviour forecasting technique.
2. The Comparative Analysis of the Approaches to the Attacker’s Profile Specification and Attack Forecasting
- (1)
- the results of the attack prediction depend strongly on the attacker’s model, and it is required to define the attacker’s model explicitly;
- (2)
- the attack forecasting is based on data analysis without explicit attacker’s model specification, and the attacker’s behaviour is constructed implicitly on the basis of the sequence of the security events.
2.1. Attacker Behaviour Prediction Based on Attack Graphs
2.2. Attacker Behaviour Prediction Based on Hidden Markov Model
- Glastopf (https://github.com/mushorg/glastopf)—a honeypot that emulates vulnerabilities that are relevant to web applications;
- Kippo (https://github.com/desaster/kippo)—a medium-interaction SSH honeypot;
- Honeytrap (https://www.honeynet.org/projects/active/honeytrap/)—a low-interaction honeypot that aims at collecting malware in an automated way;
- Dinoaea (https://www.div0.sg/single-post/dionaea-malware-honeypot)—malware capturing a honeypot that emulates several well-known protocols.
2.3. Attacker Behaviour Pattern Discovery Using Fuzzy Inference
2.4. Attributing Cyber Attacks
3. Challenges, Possible Solutions, and Common Approaches
- Lack of uniformity in the classification of attackers, distinguished metrics, and attributes, as well as the definition of the same classes and metrics.
- The gap between the raw data (such as network traffic and events logs), attacker profile, and forecasting of the attacker behaviour, as well as the methods for the determination of relationships between them.
- Lack of datasets suitable for research of the relationships between attacker steps and his/her goals.
- Absence of the research that demonstrates if there is an influence of the attacker profiling and attributing on the attack forecasting.
- Use existing datasets with specific attacks’ data.
- Use honeypots to generate real data.
- Use normal data and add data on attacks intentionally (use attack generators).
- First of all, we suppose to outline possible raw data sources. There are two types of sources: structured data and unspecified data. In [58], we outlined the following open sources of structured data considering objects of information security assessments: vulnerability databases, attack patterns databases, weaknesses databases, software and hardware databases, and so on. For accurate attack forecasting in real time, it is required to add another type of source data, network traffic, and event logs (which is unspecified). From the analyzed events datasets, the most interesting is the one provided in [56]. The dataset should contain data on various attacks with different goals implemented by attackers of different classes. From our point of view, the most complete classification from those reviewed was proposed in [40]. It incorporates the following classes: guest, external employee, internal employee, activists, state-sponsored, ethical hacker, criminals, cracker, and hobby hacker.
- Extract features from the events dataset that can characterize different classes of attackers with different goals. While there are rather detailed sets of features from the network traffic (such as source IP address, operating system, user–agent (protocol), and {cookies} in [40]), the events features should be researched in more detail. In [41], the following set is proposed: destination port, alert signature, alert category, alert severity, proto, source port, and host. We can use this as the basis for future research.
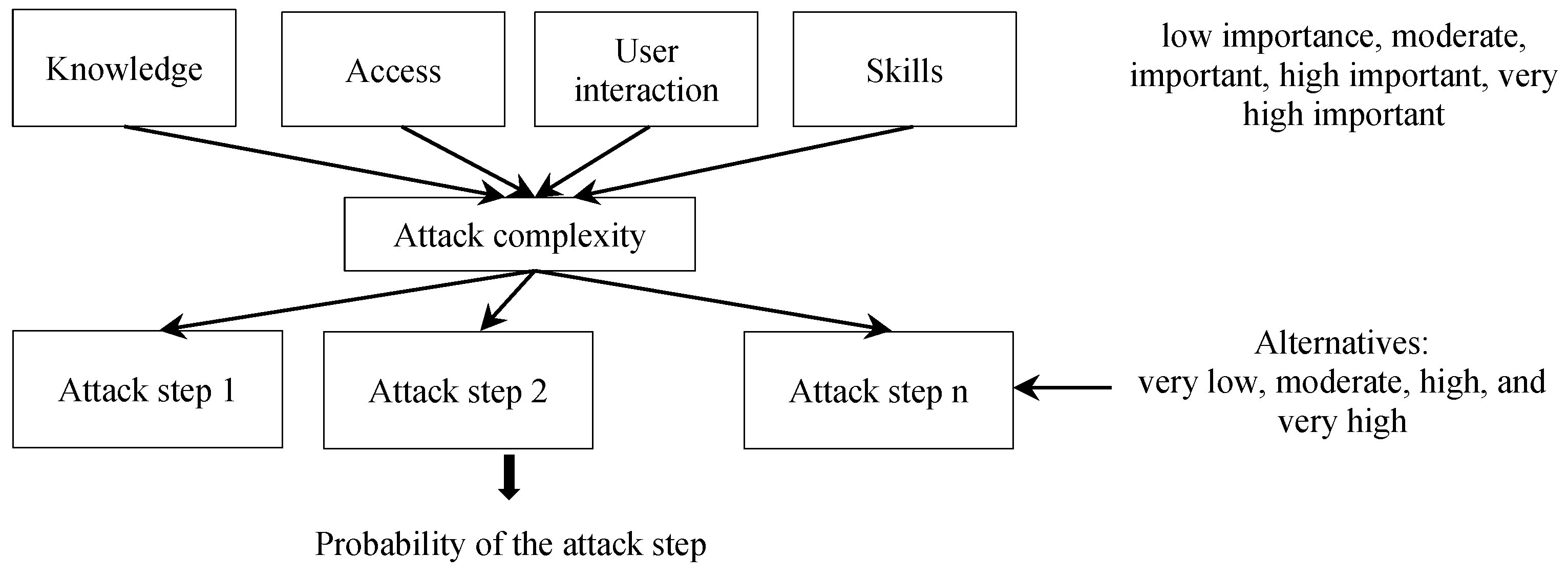
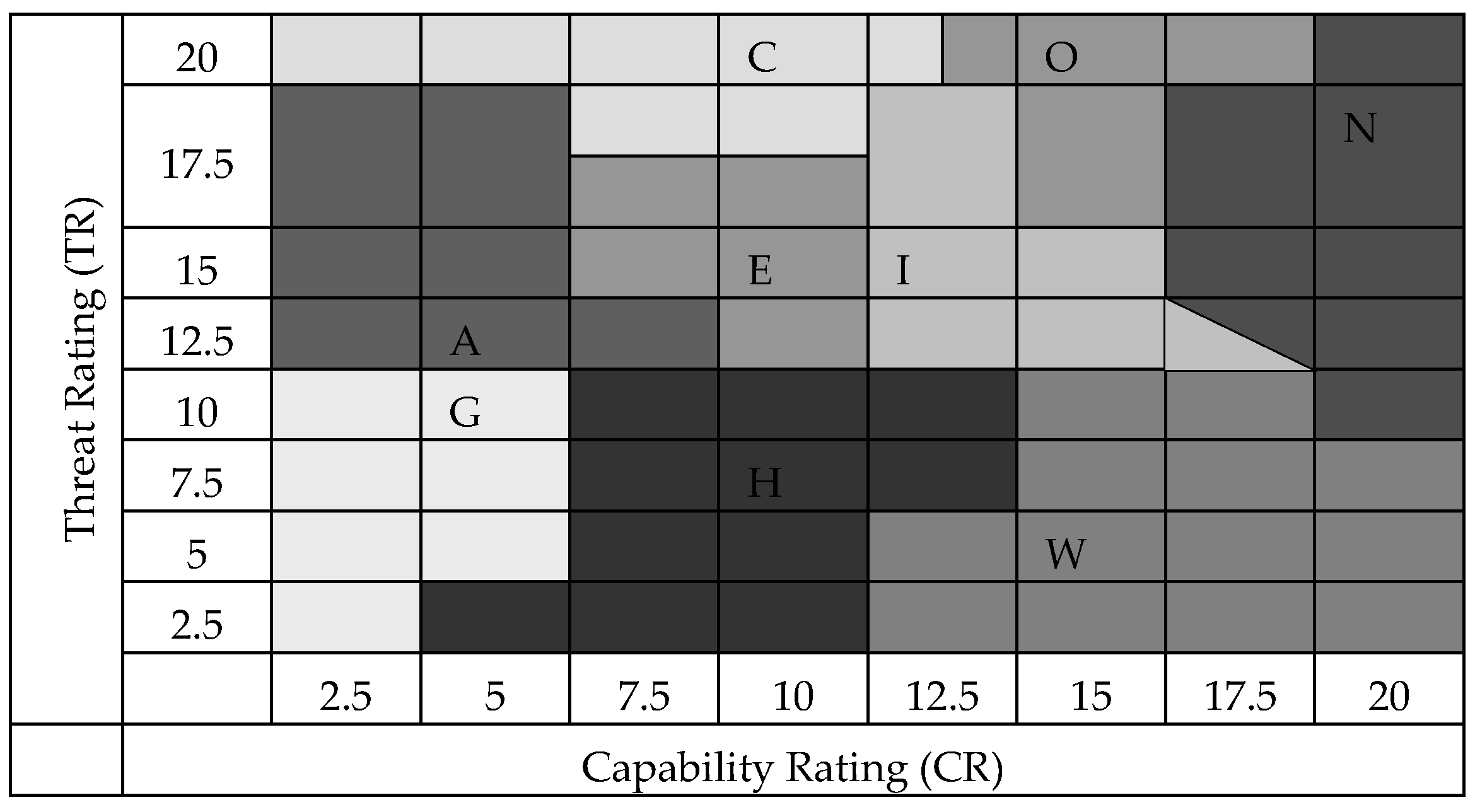
- Then, we suppose to outline and classify high level metrics that form the attacker profile, on the basis of the following metrics, proposed in [59]: attacker skill level, attacker knowledge, tools complexity, attack steps complexity, steps success rate, trace coverage rate, and so on.
- Then, we propose to find out structural and semantic relations between data sources, objects of the attacker behaviour forecasting subject area, and metrics (from features extracted from the raw data to high level metrics of attackers and attacks). To implement these, we plan to extend an ontology provided in [59] and determine transitional metrics.
- Then, we propose to use the outlined characteristics and relationships to do the following:
- develop algorithms for metrics calculation;
- train a neuro-fuzzy network for attackers’ behaviour forecasting.
4. Conclusions
Author Contributions
Funding
Conflicts of Interest
References
- Howard, J.D.; Longstaff, T.A. A Common Language for Computer Security Incidents; Sandia National Labs.: Albuquerque, NM, USA; Livermore, CA, USA, 1998. [Google Scholar]
- Abomhara, M.; Køien, G.M. Cyber security and the Internet of Things: Vulnerabilities, threats, intruders and attacks. J. Cyber Secur. Mob. 2015, 4, 65–88. [Google Scholar] [CrossRef]
- Aliyev, V. Using Honeypots to Study Skill Level of Attackers Based on the Exploited Vulnerabilities in the Network. Ph.D. Thesis, Chalmers University of technology, Göteborg, Sweden, 2010. [Google Scholar]
- Gheyas, I.A.; Abdallah, A.E. Detection and prediction of insider threats to cyber security: A systematic literature review and metaanalysis. Big Data Anal. 2016, 1, 6. [Google Scholar] [CrossRef]
- Husák, M.; Komárková, J.; Bou-Harb, E.; Čeleda, P. Survey of Attack Projection, Prediction, and Forecasting in Cyber Security. IEEE Commun. Surv. Tutor. 2019, 21, 640–660. [Google Scholar] [CrossRef]
- Yang, S.J.; Du, H.; Holsopple, J.; Sudit, M. Attack Projection. In Cyber Defense and Situational Awareness; Springer: Cham, Switzerland, 2014; pp. 239–261. [Google Scholar]
- Ahmed, A.A.; Zaman, N.A.K. Attack intention recognition: A review. IJ Netw. Secur. 2017, 244–250. [Google Scholar]
- Abdlhamed, M.; Kifayat, K.; Shi, Q.; Hurst, W. Intrusion Prediction Systems. In Information Fusion for Cyber-Security Analytics; Springer: Cham, Switzerland, 2017; pp. 155–174. [Google Scholar]
- Rocchetto, M.; Tippenhauer, N.O. On Attacker Models and Profiles for Cyber-Physical Systems. In Lecture Notes in Computer Science, Proceedings of the ESORICS, 2016; Askoxylakis, I., Ioannidis, S., Katsikas, S., Meadows, C., Eds.; Springer: Cham, Switzerland, 2016. [Google Scholar]
- Corman, J.; Etue, D. Adversary ROI: Evaluating Security from the Threat Actor’s Perspective. In Proceedings of the RSA Conference Europe 2012, San Francisco, CA, USA, 9–11 October 2012. [Google Scholar]
- Heckman, R.M. Attacker Classification to Aid Targeting Critical Systems for Threat Modelling and Security Review. 2005. Available online: www.rockyh.net/papers/AttackerClassification.pdf (accessed on 22 January 2020).
- Cardenas, A.A.; Amin, S.M.; Sinopoli, B.; Giani, A.; Perrig, A.; Sastry, S.S. Challenges for Securing Cyber Physical Systems. In Workshop on Future Directions in Cyber-physical Systems Security; DHS: Newark, NJ, USA, 2009. [Google Scholar]
- LeMay, E.; Ford, M.D.; Keefe, K.; Sanders, W.H.; Muehrcke, C. Model-Based Security Metrics Using Adversary View Security Evaluation (ADVISE). In Proceedings of the 2011 Eighth International Conference on Quantitative Evaluation of Systems, Aachen, Germany, 5–8 September 2011. [Google Scholar]
- Cardenas, A.A.; Roosta, T.; Sastry, S. Rethinking security properties, threat models, and the design space in sensor networks: A case study in SCADA systems. Ad Hoc Netw. 2009, 7, 1434–1447. [Google Scholar] [CrossRef]
- Matusitz, J. Cyberterrorism: Postmodern state of chaos. Inf. Secur. J. 2008, 17, 179–187. [Google Scholar] [CrossRef]
- Denning, D.E. Activism, hacktivism, and cyberterrorism: The internet as a tool for influencing foreign policy. Netw. Netwars Future Terror Crime Militancy 2001, 239, 288. [Google Scholar]
- Schneier, B. Attack Trees—Modeling Security Threats. Dr. Dobb’s J. 1999, 24, 12. [Google Scholar]
- Hariri, S.; Qu, G.; Dharmagadda, T.; Ramkishore, M.; Raghavendra, C.S. Impact Analysis of Faults and Attacks in Large-Scale Networks. IEEE Secur. Priv. 2003, 1, 49–54. [Google Scholar] [CrossRef]
- Ingols, K.; Chu, M.; Lippmann, R.; Webster, S.; Boyer, S. Modeling Modern Network Attacks and Countermeasures Using Attack Graphs. In Proceedings of the 2009 Annual Computer Security Applications Conference (ACSAC’09), Honolulu, HI, USA, 7–11 December 2009. [Google Scholar]
- Kheir, N.; Cuppens-Boulahia, N.; Cuppens, F.; Debar, H. A Service Dependency Model for Cost-Sensitive Intrusion Response. In Proceedings of the 15th European Symposium on Research in Computer Security (ESORICS), Athens, Greece, 20–22 September 2010. [Google Scholar]
- Kotenko, I.; Stepashkin, M. Attack Graph based Evaluation of Network Security. Lect. Notes Comput. Sci. 2006, 4237, 216–227. [Google Scholar]
- Kotenko, I.; Stepashkin, M.; Doynikova, E. Security Analysis of Computer-aided Systems Taking into Account Social Engineering Attacks. In Proceedings of the 19th Euromicro International Conference on Parallel, Distributed and Network-Based Processing (PDP 2011), Los Alamitos, CA, USA, 9–11 February 2011; pp. 611–618. [Google Scholar]
- Noel, S.; Jajodia, S.; O’Berry, B.; Jacobs, M. Efficient minimum-cost network hardening via exploit dependency graphs. In Proceedings of the 19th Annual Computer Security Applications Conference (ACSAC’03), Las Vegas, NV, USA, 8–12 December 2003. [Google Scholar]
- Wang, L.; Jajodia, S.; Singhal, A.; Noel, S. k-Zero Day Safety: Measuring the Security Risk of Networks against Unknown Attacks. In Proceedings of the 15th European Conference on Research in Computer Security; Springer: Berlin/Heidelberg, Germany, 2010; pp. 573–587. [Google Scholar]
- GhasemiGol, M.; Ghaemi-Bafghi, A.; Takabi, H. A comprehensive approach for network attack forecasting. Comput. Secur. 2016, 58, 83–105. [Google Scholar] [CrossRef]
- Wang, L.; Islam, T.; Long, T.; Singhal, A.; Jajodia, S. An Attack Graph-Based Probabilistic Security Metric. In Lecture Notes in Computer Science 5094, Proceedings of the Data and Applications Security XXII (DBSec 2008); Atluri, V., Ed.; Springer: Berlin/Heidelberg, Germany, 2008. [Google Scholar]
- Kotenko, I.; Doynikova, E. Improvement of attack graphs for cybersecurity monitoring: Handling of inaccuracies, processing of cycles, mapping of incidents and automatic countermeasure selection. SPIIRAS Proc. 2018, 57, 211–240. [Google Scholar]
- An, S.; Eom, T.; Park, J.S.; Hong, J.B.; Nhlabatsi, A.; Fetais, N.; Khan, K.M.; Kim, D.S. CloudSafe: A Tool for an Automated Security Analysis for Cloud Computing. Available online: https://arxiv.org/abs/1903.04271v1 (accessed on 25 January 2020).
- Rashid, T.; Agrafiotis, I.; Nurse, J.R.C. A New Take on Detecting Insider Threats: Exploring the Use of Hidden Markov Mode. In Proceedings of the 8th ACM CCS International Workshop on Managing Insider Security Threats, Vienna, Austria, 28 October 2016; ACM: New York, NY, USA, 2016; pp. 47–56. [Google Scholar]
- Bar, A.; Shapira, B.; Rokach, L.; Unger, M. Identifying Attack Propagation Patterns in Honeypots Using Markov Chains Modeling and Complex Networks Analysis. In Proceedings of the IEEE International Conference on Software Science, Technology and Engineering (SWSTE), Beer Sheva, Israel, 23–24 June 2016; pp. 28–36. [Google Scholar]
- Deshmukh, S.; Rade, R.; Kazi, F. Attacker Behaviour Profiling Using Stochastic Ensemble of Hidden Markov Models. 2019. Available online: https://arxiv.org/abs/1905.11824 (accessed on 25 January 2020).
- Oosterhof, G.M. Cowrie—Medium-Interaction Honeypot. Available online: https://github.com/micheloosterhof/cowrie (accessed on 25 January 2020).
- Jhawar, R.; Lounis, K.; Mauw, S. A Stochastic Framework for Quantitative Analysis of Attack-Defense Trees. In Lecture Notes in Computer Science 9871, Proceedings of the Security and Trust Management (STM 2016); Barthe, G., Markatos, E., Samarati, P., Eds.; Springer: Cham, Switzerland, 2016. [Google Scholar]
- Katipally, R.; Yang, L.; Liu, A. Attacker Behavior Analysis in Multi-stage Attack Detection System. In Proceedings of the Cyber Security and Information Intelligence Research (CSIIRW’11), Oak Ridge, TN, USA, 12–14 October 2011; ACM: New York, NY, USA, 2011. Available online: https://www.utc.edu/center-academic-excellence-cyber-defense/pdfs/paper-csiirw-2011-attacker-behavior.pdf (accessed on 25 January 2020).
- Pricop, E.; Mihalache, S.F. Fuzzy approach on modelling cyber attacks patterns on data transfer in industrial control systems. In Proceedings of the 7th International Conference on Electronics, Computers and Artificial Intelligence (ECAI 2015), Bucharest, Romania, 25–27 June 2015. [Google Scholar]
- Mallikarjunan, K.N.; Shalinie, S.M.; Preetha, G. Real Time Attacker Behavior Pattern Discovery and Profiling Using Fuzzy Rules. J. Internet Technol. 2018, 19, 1567–1575. [Google Scholar]
- Kudłacik, P.; Porwik, P.; Wesołowski, T. Fuzzy approach for intrusion detection based on user’s commands. Soft Comput. 2016, 20, 10–16. [Google Scholar] [CrossRef]
- Rid, T.; Buchanan, B. Attributing Cyber Attacks. J. Strateg. Stud. 2015, 38, 4–37. [Google Scholar] [CrossRef]
- Watters, P.A.; McCombie, S.; Layton, R.; Pieprzyk, J. Characterising and Predicting Cyber Attacks Using the Cyber Attacker Model Profile (CAMP). J. Money Laund. Control 2012, 15, 430–441. [Google Scholar] [CrossRef]
- Fraunholz, D.; Krohmer, D.; Duque Antón, S.; Schotten, H.D. YAAS—On the Attribution of Honeypot Data. Int. J. Cyber Situat. Aware. 2017, 2, 31–48. [Google Scholar] [CrossRef]
- Perry, I.; Li, L.; Sweet, C.; Su, S.H.; Cheng, F.-Y.; Yang, S.J.; Okutan, A. Differentiating and Predicting Cyberattack Behaviors Using LSTM. In Proceedings of the 2018 IEEE Conference on Dependable and Secure Computing (DSC), Kaohsiung, Taiwan, 10–13 December 2018. [Google Scholar]
- Çayirci, E.; Rong, C. Security in Wireless Ad Hoc and Sensor Networks; John Wiley & Sons: Hoboken, NJ, USA, 2009. [Google Scholar]
- Kdd Cup 1999 Data. UCI KDD Archive. 1999. Available online: http://kdd.ics.uci.edu/databases/kddcup99/kddcup99.html (accessed on 25 January 2020).
- The CAIDA DDoS Attack 2007 Dataset. 2007. Available online: http://www.caida.org/data/passive/ddos-20070804_dataset.xml (accessed on 25 January 2020).
- Shyla, S.; Sujatha, S. Cloud Security: LKM and Optimal Fuzzy System for Intrusion Detection in Cloud Environment. J. Intell. Syst. 2019, 29, 1626–1642. [Google Scholar] [CrossRef]
- Orojloo, H.; Abdollahi Azgomi, M. Predicting the behavior of attackers and the consequences of attacks against cyber-physical systems. Secur. Commun. Netw. 2016, 9, 6111–6136. [Google Scholar] [CrossRef]
- MASSIF FP7 Project. MASSIF Architecture. 2011–2013. Available online: https://rieke.link/MASSIF_Architecture_document.pdf (accessed on 22 January 2020).
- Casey, T. Threat Agent Library Helps Identify Information Security Risks. Intel. Technical Report. 2007. Available online: https://www.sbs.ox.ac.uk/cybersecurity-capacity/system/files/Intel%20-%20Threat%20Agent%20Library%20Helps%20Identify%20Information%20Security%20Risks.pdf (accessed on 22 January 2020).
- Shanmugam, B.; Idris, N.B. Hybrid Intrusion Detection Systems (HIDS) Using Fuzzy Logic. 2011. Available online: https://www.intechopen.com/books/intrusion-detection-systems/hybrid-intrusion-detection-systems-hids-using-fuzzy-logic (accessed on 22 January 2020).
- Dickerson, J.E.; Dickerson, J.A. Fuzzy Network Profiling for Intrusion Detection. In Proceedings of the 19th International Conference of the North American Fuzzy Information Processing Society—NAFIPS (Cat. No.00TH8500), PeachFuzz 2000, Atlanta, GA, USA, 13–15 July 2000; pp. 301–306. [Google Scholar]
- Shanmugam, B.; Idris, N.B. Improved Intrusion Detection System Using Fuzzy Logic for Detecting Anamoly and Misuse Type of Attacks. In Proceedings of the 2009 International Conference of Soft Computing and Pattern Recognition, Malacca, Malaysia, 4–7 December 2009; pp. 212–217. [Google Scholar]
- Chen, C.T. Extensions of the TOPSIS for group decision-making under fuzzy environment. Fuzzy Sets Syst. 2000, 114, 1–9. [Google Scholar] [CrossRef]
- Structured Threat Information eXpression (STIX™) 1.x Archive Website. Available online: https://stixproject.github.io/ (accessed on 25 January 2020).
- About STIX. Available online: https://stixproject.github.io/about/ (accessed on 25 January 2020).
- Rade, R.; Deshmukh, S.; Nene, R.; Wadekar, A.S.; Unny, A. Temporal and Stochastic Modelling of Attacker Behaviour. In Advances in Data Science 941, Proceedings of the Communications in Computer and Information Science (ICIIT 2018); Akoglu, L., Ferrara, E., Deivamani, M., Baeza-Yates, R., Yogesh, P., Eds.; Springer: Singapore, 2019. [Google Scholar]
- Singapore University of Technology and Design Official Web Site. iTrust. Dataset Characteristics. Available online: https://itrust.sutd.edu.sg/itrust-labs_datasets/dataset_info/ (accessed on 25 January 2020).
- Kotenko, I.; Chechulin, A.; Branitskiy, A. Generation of Source Data for Experiments with Network Attack Detection Software. J. Phys. Conf. Ser. 2017, 820, 012033. [Google Scholar] [CrossRef]
- Kotenko, I.; Fedorchenko, A.; Doynikova, E.; Chechulin, A. An Ontology-based Hybrid Storage of Security Information. Inf. Technol. Control 2018, 47, 655–667. [Google Scholar]
- Doynikova, E.; Kotenko, I. Approach for determination of cyber attack goals based on the ontology of security metrics. In IOP Conference Series: Materials Science and Engineering (MSE) 450, Proceedings of the International Workshop “Advanced Technologies in Aerospace, Mechanical and Automation Engineering” (MIST: Aerospace-2018), Krasnoyarsk, Russia, 20 October 2018; IOP Publishing: Bristol, UK, 2018. [Google Scholar]
| Method | Related Research | Datasets and Features | Attacker Classification | Characteristics | Description and Advantages | Limitations |
|---|---|---|---|---|---|---|
| Attack graph analysis based on the analysis of network topology, software and hardware configuration, relationships between users and services, and vulnerabilities | Schneier, B., 1999 [17]; Ingols, K. et al., 2009 [19]; Kheir, N. et al., 2010 [20]; Kotenko, I. and Stepashkin, M., 2006 [21]; GhasemiGol, M. et al., 2016 [25]; Wang, L. et al., 2008 [26]; Kotenko, I. and Doynikova, E., 2018 [27] | – |
|
|
|
|
| HMM-based approach | Rashid, T. et al., 2016 [29]; Bar, A. et al., 2016 [30]; Deshmukh, S. et al., 2019 [31]; Jhawar, R. et al., 2016 [33] | events generated by honeypots | - | – |
|
|
| Katipally, R. et al., 2011 [34] | network traffic with emulated attacks |
|
|
|
| |
| Fuzzy inference-based approach | Çayirci, E., Rong, C., 2009 [42] |
| - | - |
|
|
| Pricop, E. and Mihalache, S.F., 2015 [35]. Mallikarjunan, K.N. et al., 2018 [36] | high level abstract variables | 6–9 profiles, e.g.,
| No unified set of attributes to define attacker’s profile. example:
|
|
| |
| Fuzzy inference and attack graphs | Orojloo and Abdollahi Azgomi, 2016 [46] | high level abstract data and use case |
|
|
| |
| Fuzzy inference based on statistical user profiles | Kudłacik, P. et al., 2016 [37] | qualitative attributes of the log events such as keyboard keys’ sequences, characteristic data sequences retrieved from pointing device, chosen options, and so on. | - | - |
|
|
| Attack attributing | Rid, T. and Buchanan, B., 2015 [38] | behavioural indicators, including atomic indicators (IP addresses, email addresses, domain names, and small pieces of text) and computed indicators (‘hash’) | - | - | behavioural indicators allow pointing a specific adversary who has employed similar behaviours in the past |
|
| Attribution of honeypot data | Fraunholz, D. et al., 2017 [40] |
|
|
| attempt to link raw data and high-level metrics |
|
| RNN | Perry, I. et al., 2018 [41] |
| – | – |
|
|
| Origin | Temporal | ||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|
| Port | IP address | User agent | URL | Domain | User ID | OS | Inter-Arrival Time | ||||
| Protocol | Service | Autonomous system | Country | Standard deviation | Average | ||||||
© 2020 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Doynikova, E.; Novikova, E.; Kotenko, I. Attacker Behaviour Forecasting Using Methods of Intelligent Data Analysis: A Comparative Review and Prospects. Information 2020, 11, 168. https://doi.org/10.3390/info11030168
Doynikova E, Novikova E, Kotenko I. Attacker Behaviour Forecasting Using Methods of Intelligent Data Analysis: A Comparative Review and Prospects. Information. 2020; 11(3):168. https://doi.org/10.3390/info11030168
Chicago/Turabian StyleDoynikova, Elena, Evgenia Novikova, and Igor Kotenko. 2020. "Attacker Behaviour Forecasting Using Methods of Intelligent Data Analysis: A Comparative Review and Prospects" Information 11, no. 3: 168. https://doi.org/10.3390/info11030168
APA StyleDoynikova, E., Novikova, E., & Kotenko, I. (2020). Attacker Behaviour Forecasting Using Methods of Intelligent Data Analysis: A Comparative Review and Prospects. Information, 11(3), 168. https://doi.org/10.3390/info11030168






